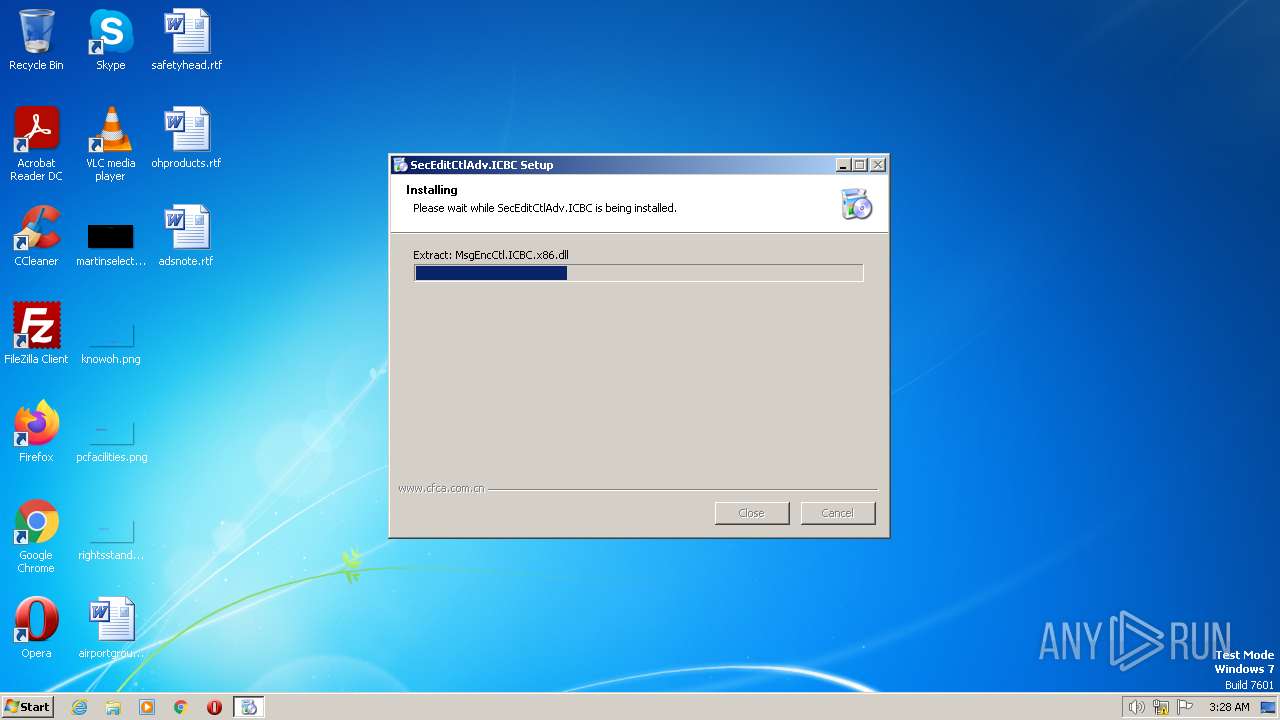
| File name: | SecEditCtlHostAdv.ICBC.Setup.All.exe |
| Full analysis: | https://app.any.run/tasks/2e6e65b7-5b15-4878-b1b0-c7db0b19fbcc |
| Verdict: | Malicious activity |
| Analysis date: | July 09, 2023, 02:28:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 4C5E4F626EB198DA64CC5F73A0C03D73 |
| SHA1: | 1A3601A8340E2993404BE01984413FC7F1B2871B |
| SHA256: | EA5A2B824E333944606CCB3798D9EA59228CA12EB13BFFB9C3F4F027E5CFF6C5 |
| SSDEEP: | 98304:CKNDfDZodL7S3DCahvuS/aK1+lBMAKtfQkzUuBGptOAc7nsbHFnBkaSGRB1csYuM:CIDr6m3DruAt+fE5UwGbKLeFBkDGn1cP |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- SecEditCtlHostAdv.ICBC.Setup.All.exe (PID: 3444)
Actions looks like stealing of personal data
- SecEditCtlHostAdv.ICBC.Setup.All.exe (PID: 3444)
Creates a writable file the system directory
- SecEditCtlHostAdv.ICBC.Setup.All.exe (PID: 3444)
Loads dropped or rewritten executable
- SecEditCtlHostAdv.ICBC.Setup.All.exe (PID: 3444)
- regsvr32.exe (PID: 3456)
- regsvr32.exe (PID: 3976)
- opera.exe (PID: 1248)
SUSPICIOUS
The process creates files with name similar to system file names
- SecEditCtlHostAdv.ICBC.Setup.All.exe (PID: 3444)
Reads the Internet Settings
- regsvr32.exe (PID: 3976)
Executable content was dropped or overwritten
- SecEditCtlHostAdv.ICBC.Setup.All.exe (PID: 3444)
Changes internet zones settings
- regsvr32.exe (PID: 3976)
INFO
Reads the computer name
- SecEditCtlHostAdv.ICBC.Setup.All.exe (PID: 3444)
The process checks LSA protection
- SecEditCtlHostAdv.ICBC.Setup.All.exe (PID: 3444)
Checks supported languages
- SecEditCtlHostAdv.ICBC.Setup.All.exe (PID: 3444)
Creates files in the program directory
- SecEditCtlHostAdv.ICBC.Setup.All.exe (PID: 3444)
Create files in a temporary directory
- SecEditCtlHostAdv.ICBC.Setup.All.exe (PID: 3444)
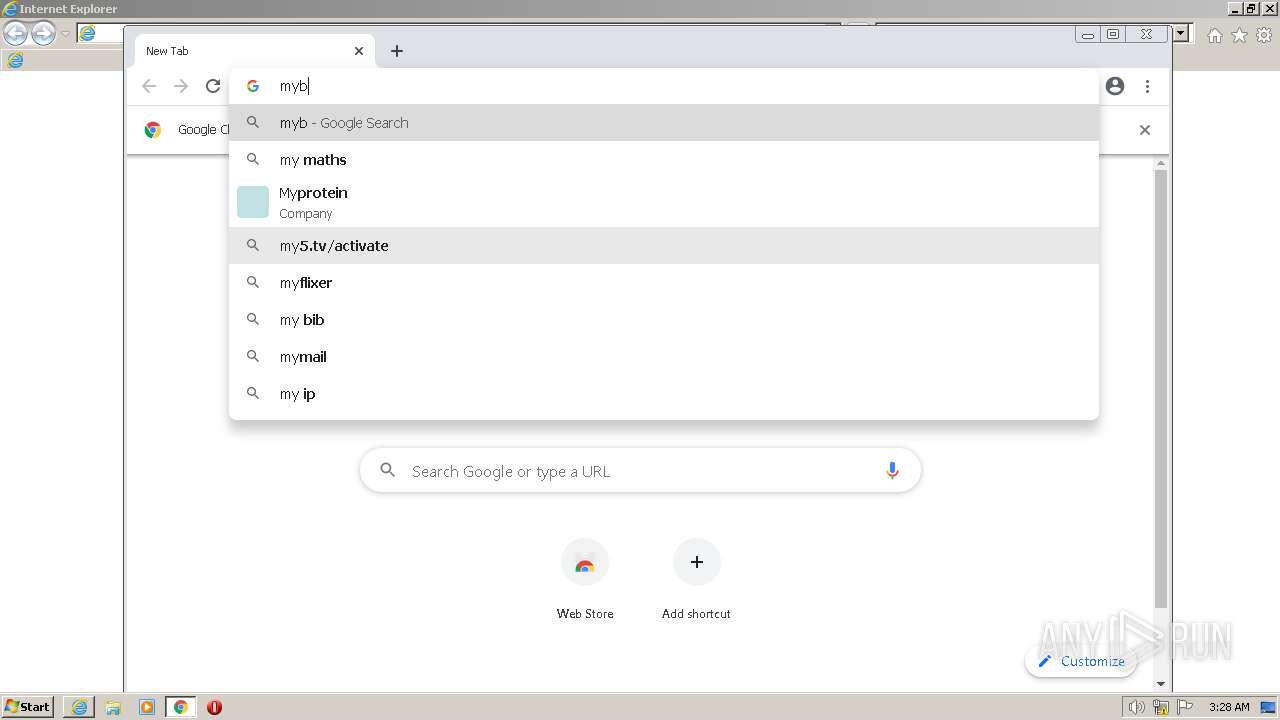
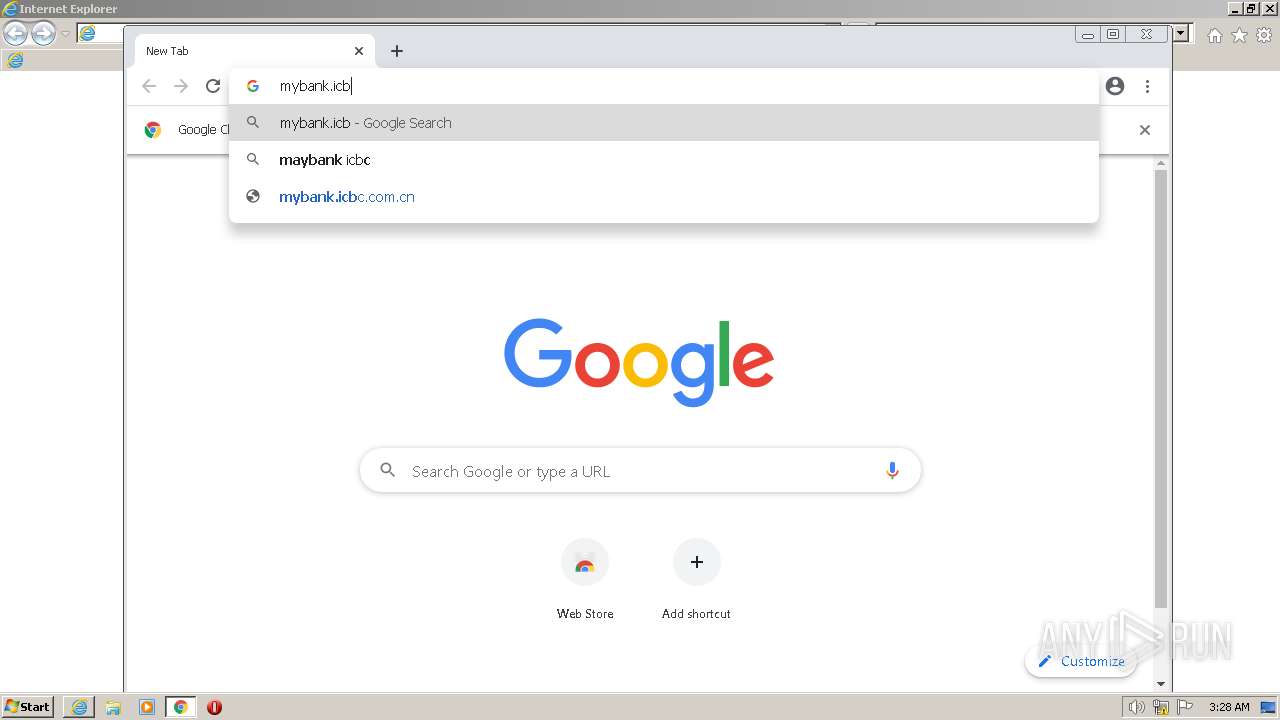
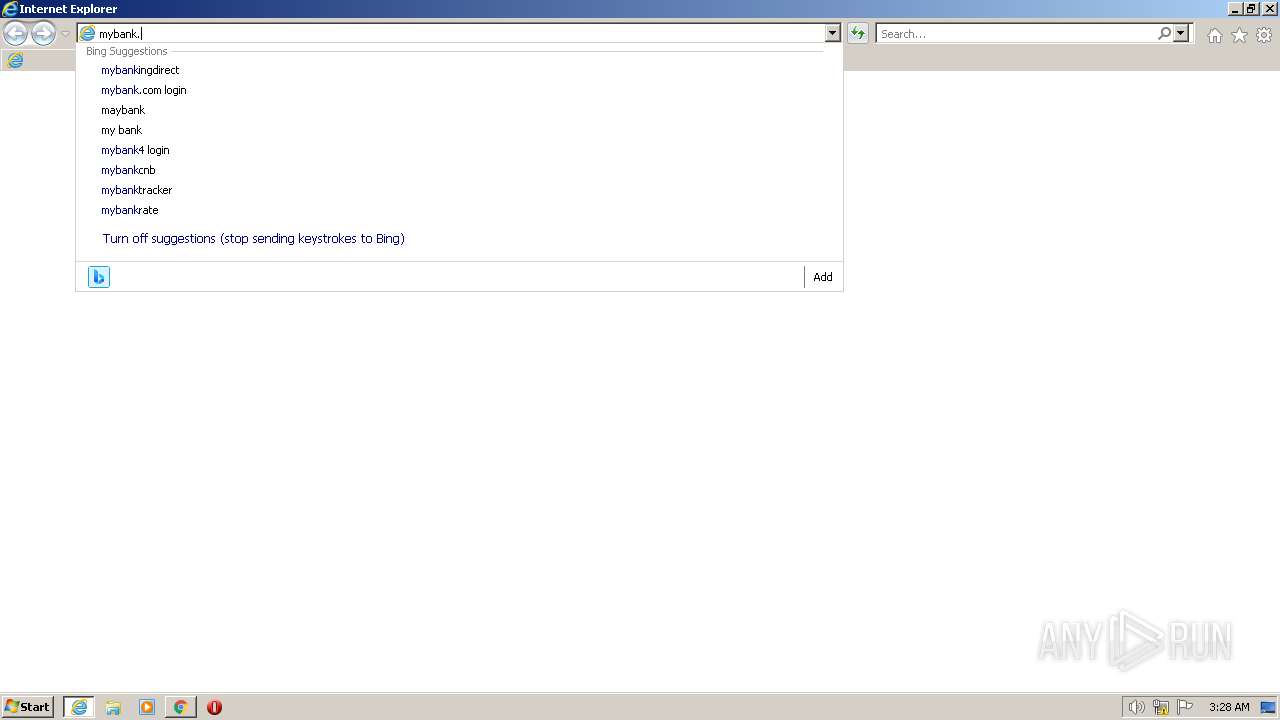
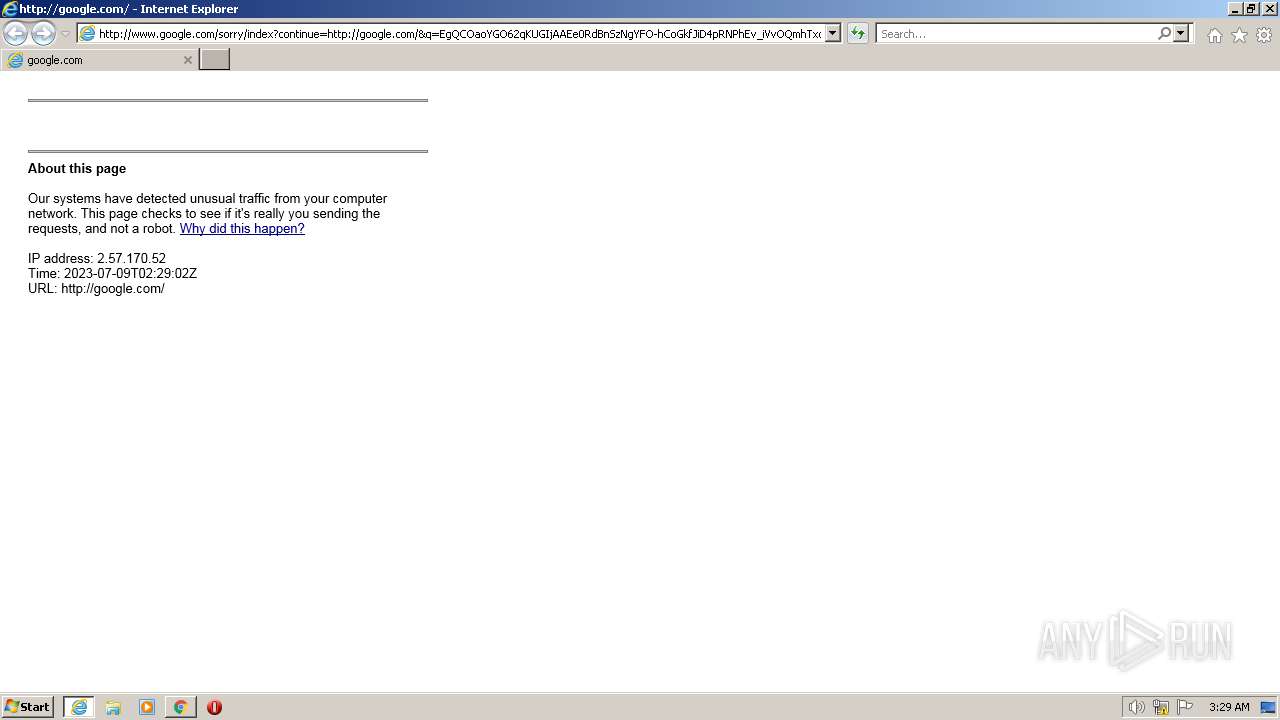
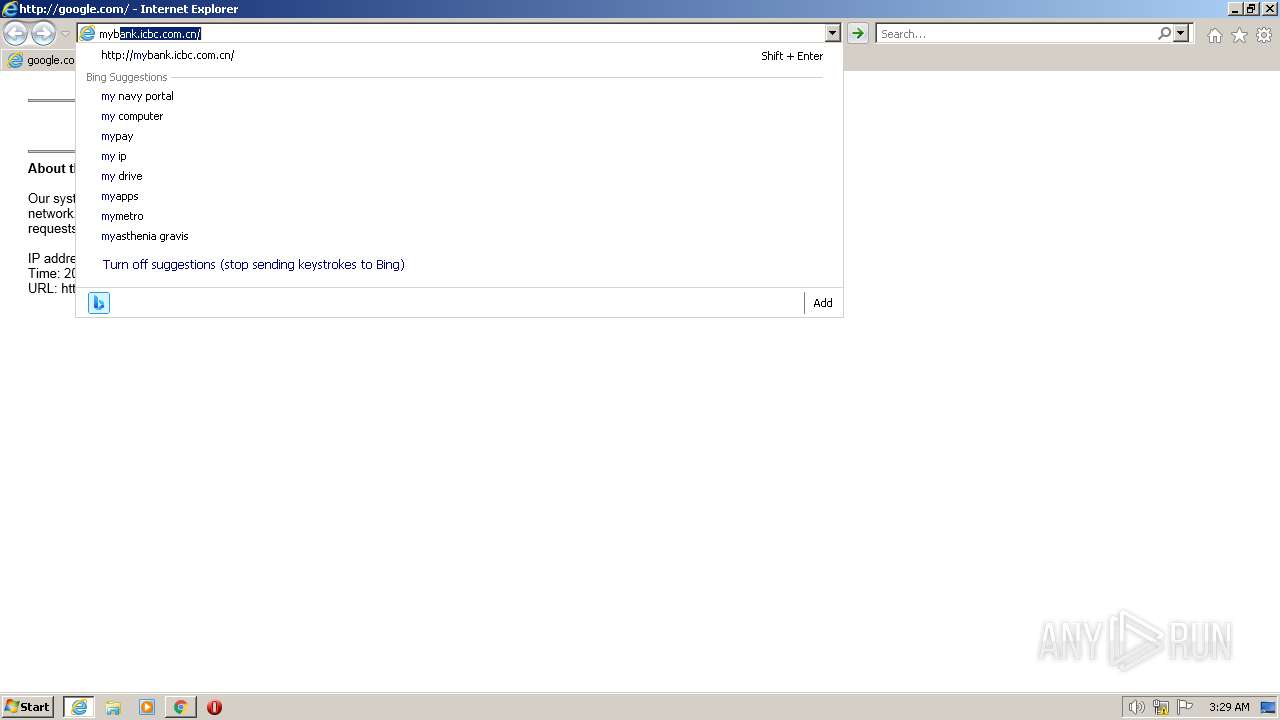
Manual execution by a user
- iexplore.exe (PID: 2212)
- chrome.exe (PID: 3500)
- iexplore.exe (PID: 2052)
- opera.exe (PID: 1248)
Application launched itself
- iexplore.exe (PID: 2212)
- chrome.exe (PID: 3500)
- iexplore.exe (PID: 2052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| ProductVersion: | 3.2.2.2 |
|---|---|
| ProductName: | SecEditCtlHostAdv.ICBC.Setup |
| LegalCopyright: | Copyright(C) 2023 CFCA |
| FileVersion: | 3.2.2.2 |
| FileDescription: | CFCA SecEditCtlAdv |
| CompanyName: | CFCA |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 3.2.2.2 |
| FileVersionNumber: | 3.2.2.2 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x352d |
| UninitializedDataSize: | 2048 |
| InitializedDataSize: | 186880 |
| CodeSize: | 27136 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| TimeStamp: | 2021:09:25 21:57:46+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Sep-2021 21:57:46 |
| Detected languages: |
|
| CompanyName: | CFCA |
| FileDescription: | CFCA SecEditCtlAdv |
| FileVersion: | 3.2.2.2 |
| LegalCopyright: | Copyright(C) 2023 CFCA |
| ProductName: | SecEditCtlHostAdv.ICBC.Setup |
| ProductVersion: | 3.2.2.2 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 25-Sep-2021 21:57:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006897 | 0x00006A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4584 |
.rdata | 0x00008000 | 0x000014A6 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.02411 |
.data | 0x0000A000 | 0x0002B018 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.15458 |
.ndata | 0x00036000 | 0x0001A000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00050000 | 0x000074A0 | 0x00007600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.72541 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28834 | 1070 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.6303 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 6.5168 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 6.72637 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 3.68656 | 1640 | UNKNOWN | English - United States | RT_ICON |
6 | 5.62942 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 6.07002 | 1128 | UNKNOWN | English - United States | RT_ICON |
8 | 3.89724 | 744 | UNKNOWN | English - United States | RT_ICON |
9 | 3.70745 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.89097 | 132 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
91
Monitored processes
46
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1020,11443568050120207866,2234940553166159469,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3452 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 548 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2212 CREDAT:78850 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1020,11443568050120207866,2234940553166159469,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3376 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,11443568050120207866,2234940553166159469,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2280 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1020,11443568050120207866,2234940553166159469,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1176 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1020,11443568050120207866,2234940553166159469,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3676 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1020,11443568050120207866,2234940553166159469,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1796 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,11443568050120207866,2234940553166159469,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1032 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 1284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1020,11443568050120207866,2234940553166159469,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1880 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
49 651
Read events
47 841
Write events
1 799
Delete events
11
Modification events
| (PID) Process: | (3976) regsvr32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3976) regsvr32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3976) regsvr32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3976) regsvr32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3976) regsvr32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\2 |
| Operation: | write | Name: | DisplayName |
Value: Trusted sites | |||
| (PID) Process: | (3976) regsvr32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\2 |
| Operation: | write | Name: | Description |
Value: This zone contains websites that you trust not to damage your computer or data. | |||
| (PID) Process: | (3976) regsvr32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\2 |
| Operation: | write | Name: | Icon |
Value: inetcpl.cpl#00004480 | |||
| (PID) Process: | (3976) regsvr32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\2 |
| Operation: | write | Name: | 1001 |
Value: 1 | |||
| (PID) Process: | (3976) regsvr32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\2 |
| Operation: | write | Name: | 1004 |
Value: 3 | |||
| (PID) Process: | (3976) regsvr32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\2 |
| Operation: | write | Name: | 1200 |
Value: 0 | |||
Executable files
20
Suspicious files
174
Text files
221
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3444 | SecEditCtlHostAdv.ICBC.Setup.All.exe | C:\Program Files\CFCA\SecEditCtlHostAdv.ICBC.Setup\com.cfca.SecEditCtlAdv.ICBC-win.json | text | |
MD5:FFF429802F91E849A5C0DF1EB5092BCF | SHA256:795013B2A39AE5E6A2038996150B0E17D2934A5870D012E76A8966A6B658000E | |||
| 3444 | SecEditCtlHostAdv.ICBC.Setup.All.exe | C:\Program Files\CFCA\SecEditCtlHostAdv.ICBC.Setup\ldeoacaiflgllkpappifbdcimcklcfec.zip | compressed | |
MD5:85557F376EAFAD7CE96BBABD490851D8 | SHA256:988CF71BD038CCDEA4A7EB2CAECBD915DE1D9A64FA420415927971B60AEE7CA1 | |||
| 3444 | SecEditCtlHostAdv.ICBC.Setup.All.exe | C:\Windows\System32\npSecEditCtlAdv.ICBC.x86.dll | executable | |
MD5:C14FE17F9177577317D9AA17E22E3F8A | SHA256:1DF74079A769D34D0DA482C1BC2930EB9F4567DB9899B4709478D537AC79E7E5 | |||
| 3444 | SecEditCtlHostAdv.ICBC.Setup.All.exe | C:\Windows\System32\MsgEncCtl.ICBC.x86.dll | executable | |
MD5:A5FF0F0E7045801C2CE26652F3EF4019 | SHA256:78E696A78DCB59B36344B2DF1892BF78CFDCC19BD9148CCFB1DDC1AB17745928 | |||
| 3500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-64AA1B51-DAC.pma | — | |
MD5:— | SHA256:— | |||
| 3444 | SecEditCtlHostAdv.ICBC.Setup.All.exe | C:\Program Files\CFCA\SecEditCtlHostAdv.ICBC.Setup\ldeoacaiflgllkpappifbdcimcklcfec.json | text | |
MD5:BDBEEE962FEB7AB7FAE4F7F38A3ED144 | SHA256:C6624D1CA448F736FC3D344666E23C3634BD73ECF4BC86844713876E638E8A7B | |||
| 3444 | SecEditCtlHostAdv.ICBC.Setup.All.exe | C:\Program Files\CFCA\SecEditCtlHostAdv.ICBC.Setup\uninst.exe | executable | |
MD5:16182A2A78F831A01F8D536E9E279DA5 | SHA256:CC2D10B8FEB1DFACAA56DC4FF5C36985BF4ADBB614E1263FA039DA312663F5F7 | |||
| 3444 | SecEditCtlHostAdv.ICBC.Setup.All.exe | C:\Users\admin\AppData\Local\Temp\nscBB3F.tmp\System.dll | executable | |
MD5:CFF85C549D536F651D4FB8387F1976F2 | SHA256:8DC562CDA7217A3A52DB898243DE3E2ED68B80E62DDCB8619545ED0B4E7F65A8 | |||
| 3444 | SecEditCtlHostAdv.ICBC.Setup.All.exe | C:\Windows\System32\npMsgEncCtl.ICBC.x86.dll | executable | |
MD5:725070834E62B268E69E652D7A06191F | SHA256:DE595E5A4D295539F78565D831BDB77042E1DC05ECB3BF09AF1467013F77C494 | |||
| 3444 | SecEditCtlHostAdv.ICBC.Setup.All.exe | C:\Users\admin\AppData\Local\Temp\nscBB3F.tmp\CrxInstaller.dll | executable | |
MD5:B9086DFA9511196D59814B0FB377B09A | SHA256:A804304DBBEECB815A9B8B90F071FE50CCEC50502EB367F86BFC575DB1102E85 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
44
TCP/UDP connections
104
DNS requests
38
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
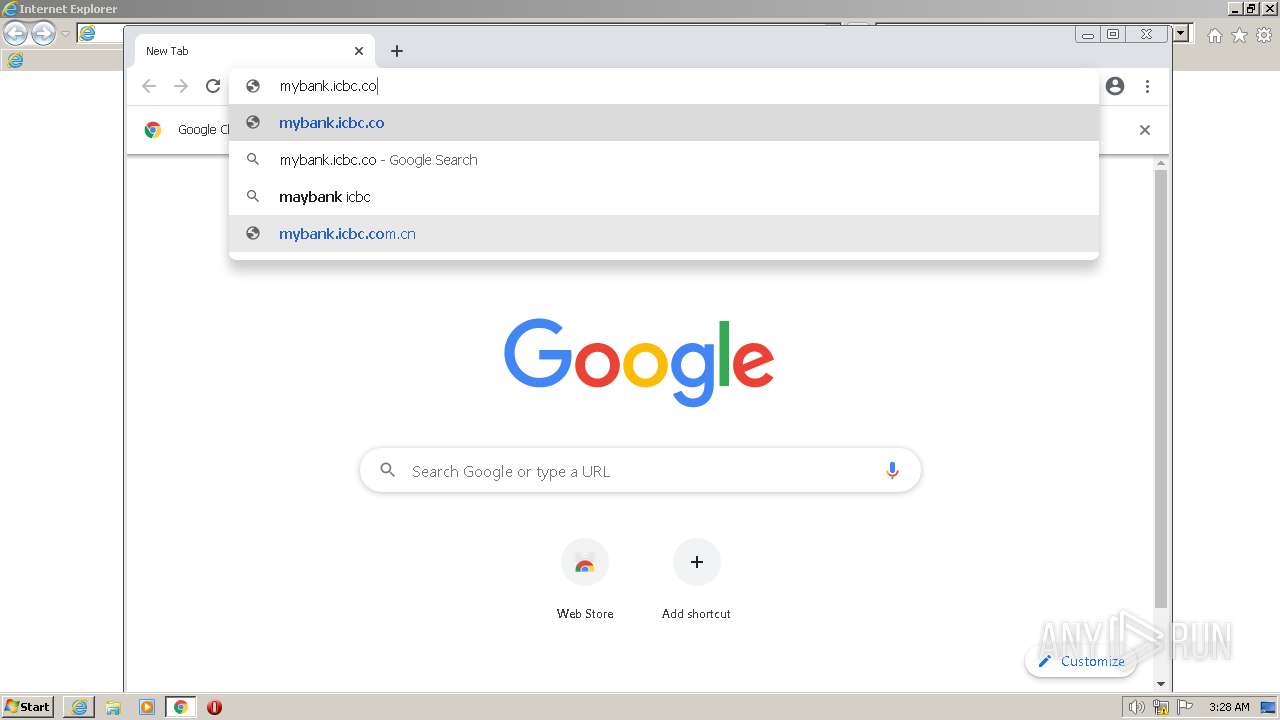
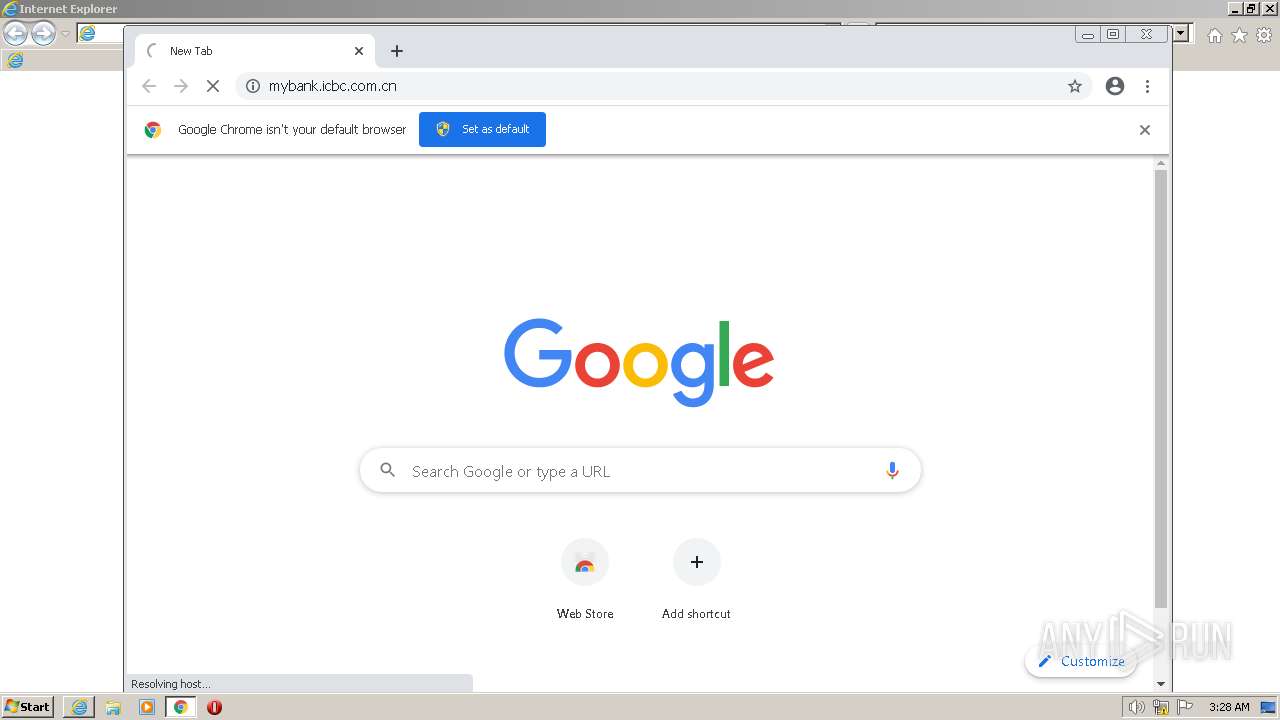
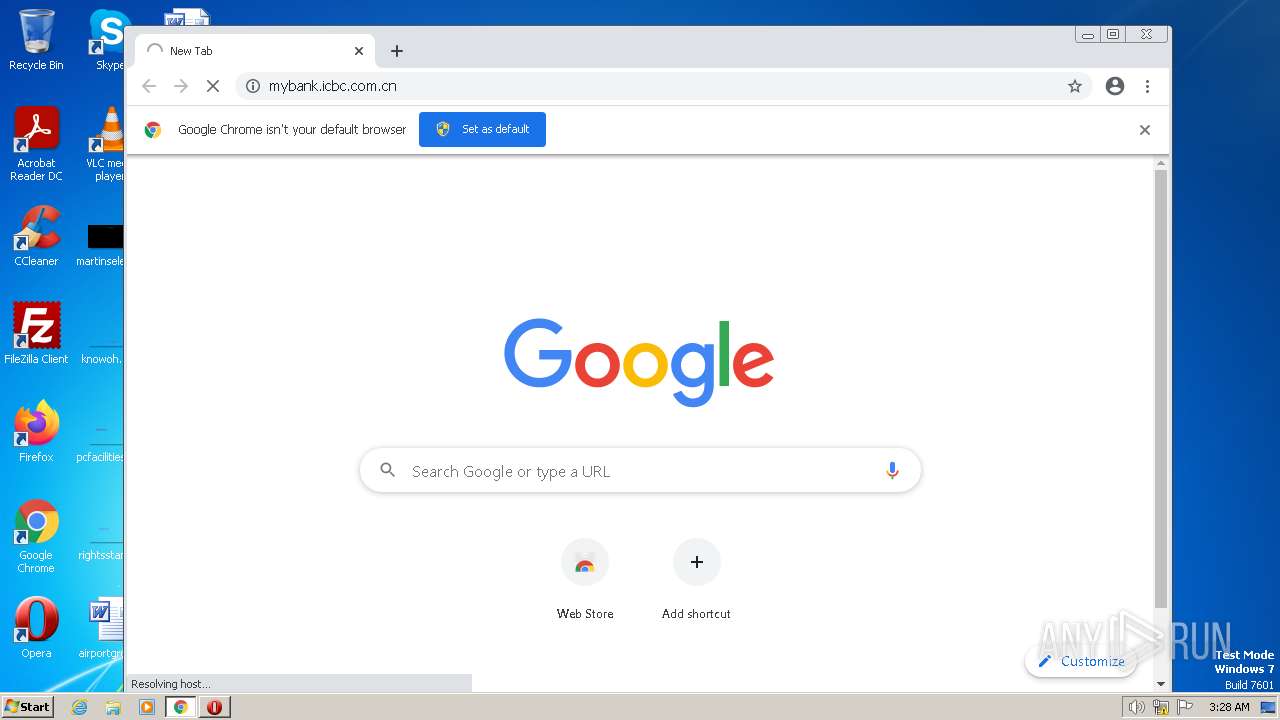
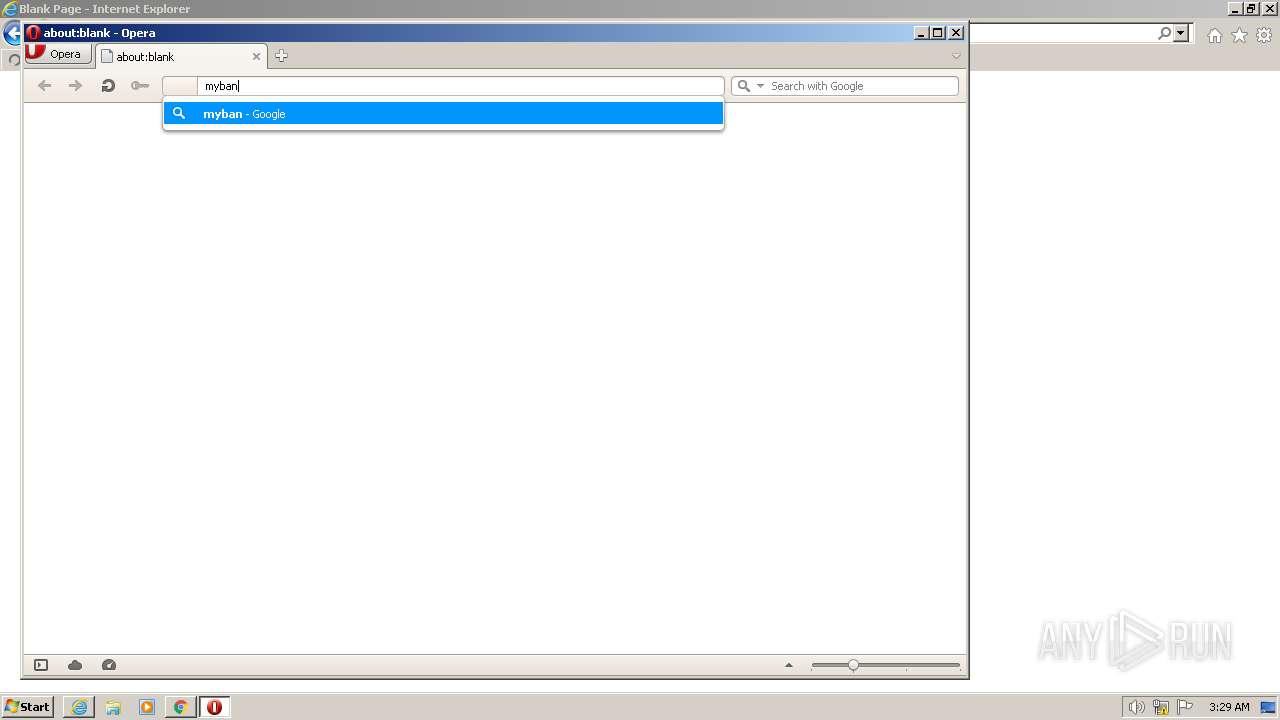
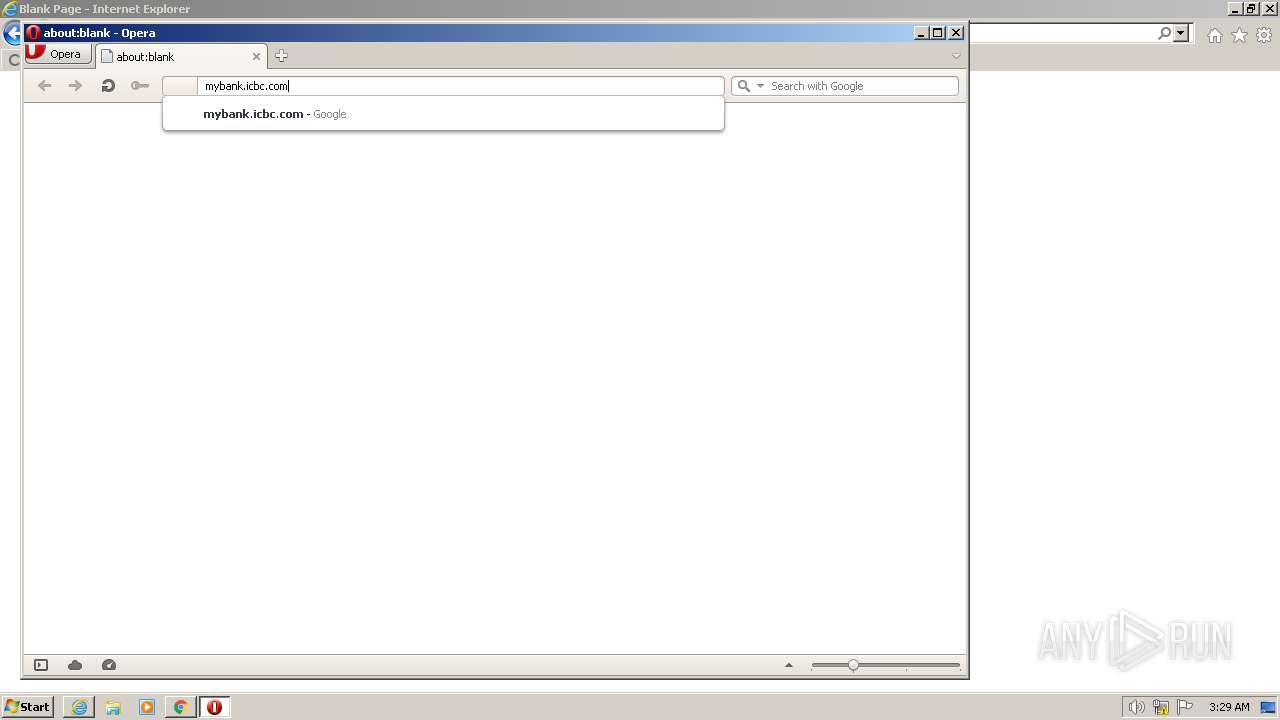
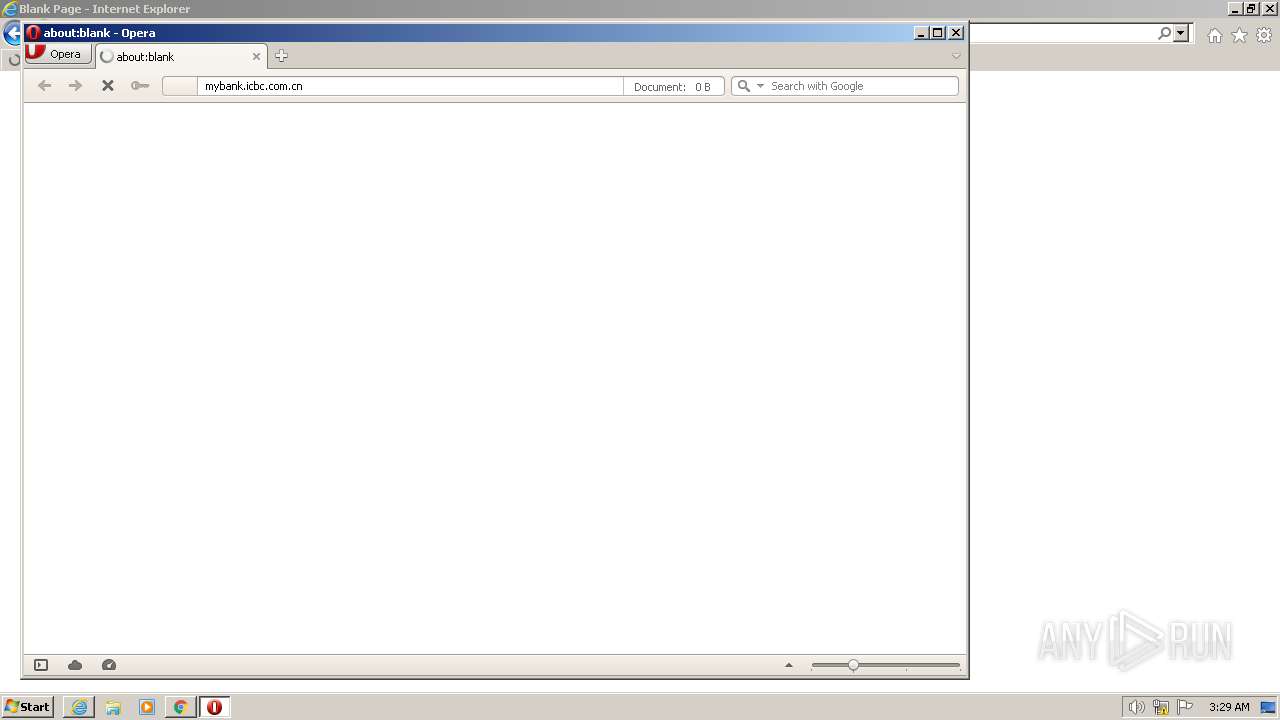
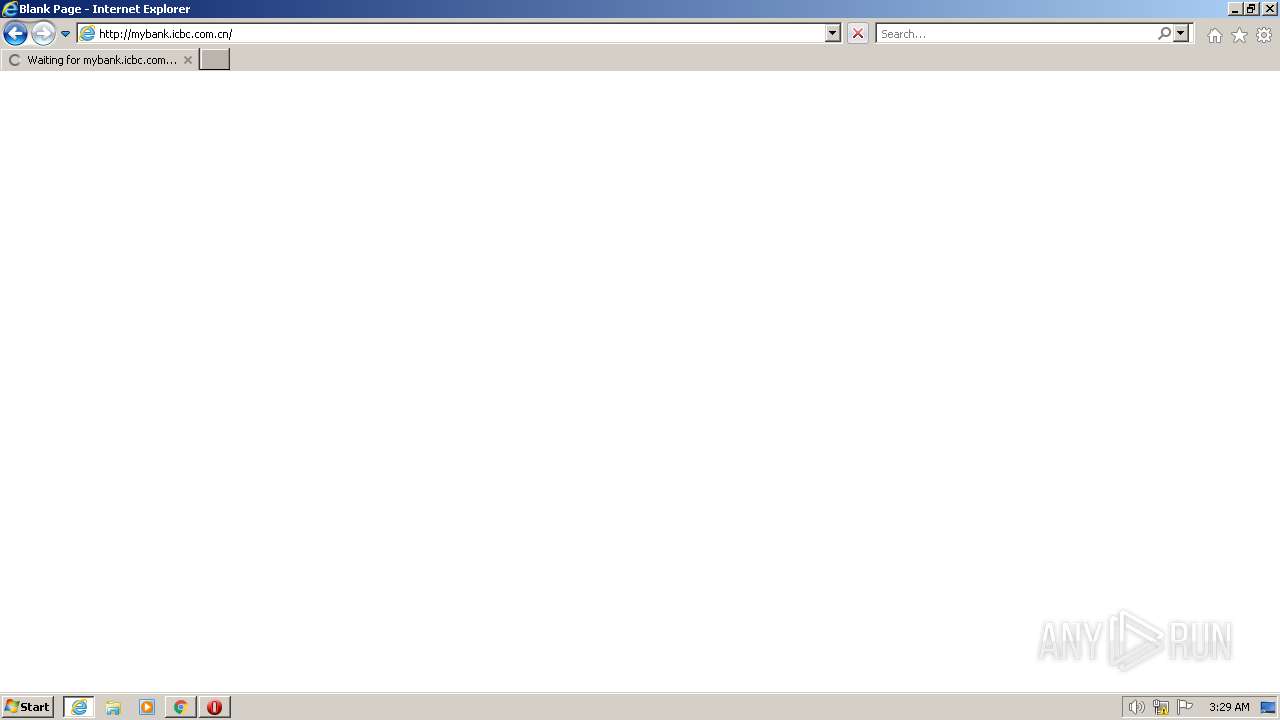
4084 | chrome.exe | GET | — | 103.126.1.226:80 | http://mybank.icbc.com.cn/ | CN | — | — | unknown |
1476 | iexplore.exe | GET | — | 103.126.1.226:80 | http://mybank.icbc.com.cn/ | CN | — | — | unknown |
1248 | opera.exe | GET | — | 103.126.1.226:80 | http://mybank.icbc.com.cn/ | CN | — | — | unknown |
852 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjg0QUFYSnN4MFUtaEQwNDZqVGRkVkFmZw/1.0.6.0_aemomkdncapdnfajjbbcbdebjljbpmpj.crx | US | — | — | whitelisted |
2212 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2212 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?5dcec47cb040d223 | US | compressed | 4.70 Kb | whitelisted |
1248 | opera.exe | GET | 400 | 82.145.216.15:80 | http://sitecheck2.opera.com/?host=mybank.icbc.com.cn&hdn=kishCOp93KCAxa%2BALlq8NA== | unknown | html | 150 b | whitelisted |
2424 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
2052 | iexplore.exe | GET | 200 | 142.250.185.228:80 | http://www.google.com/favicon.ico | US | image | 1.46 Kb | malicious |
852 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjg0QUFYSnN4MFUtaEQwNDZqVGRkVkFmZw/1.0.6.0_aemomkdncapdnfajjbbcbdebjljbpmpj.crx | US | binary | 6.20 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
820 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3500 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4084 | chrome.exe | 142.250.185.228:443 | www.google.com | GOOGLE | US | whitelisted |
4084 | chrome.exe | 142.250.186.142:443 | clients2.google.com | GOOGLE | US | whitelisted |
4084 | chrome.exe | 142.250.184.193:443 | clients2.googleusercontent.com | GOOGLE | US | whitelisted |
4084 | chrome.exe | 142.250.186.141:443 | accounts.google.com | GOOGLE | US | whitelisted |
3500 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
update.googleapis.com |
| whitelisted |