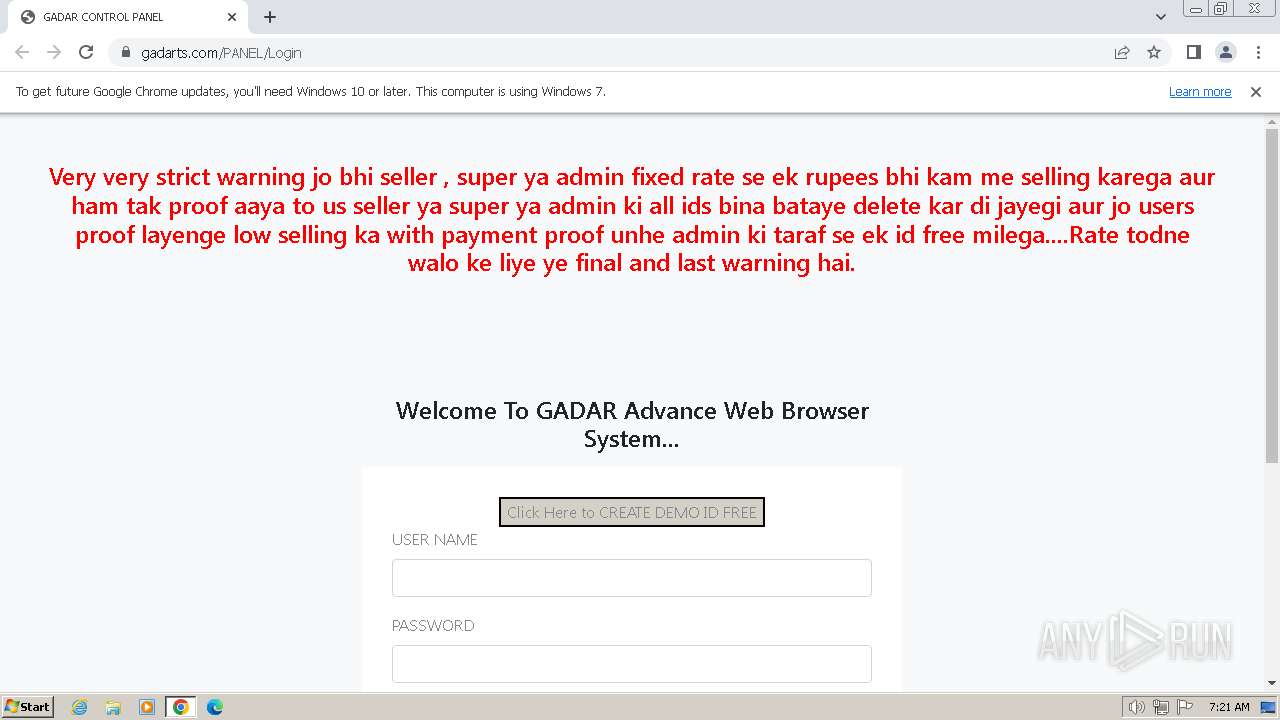
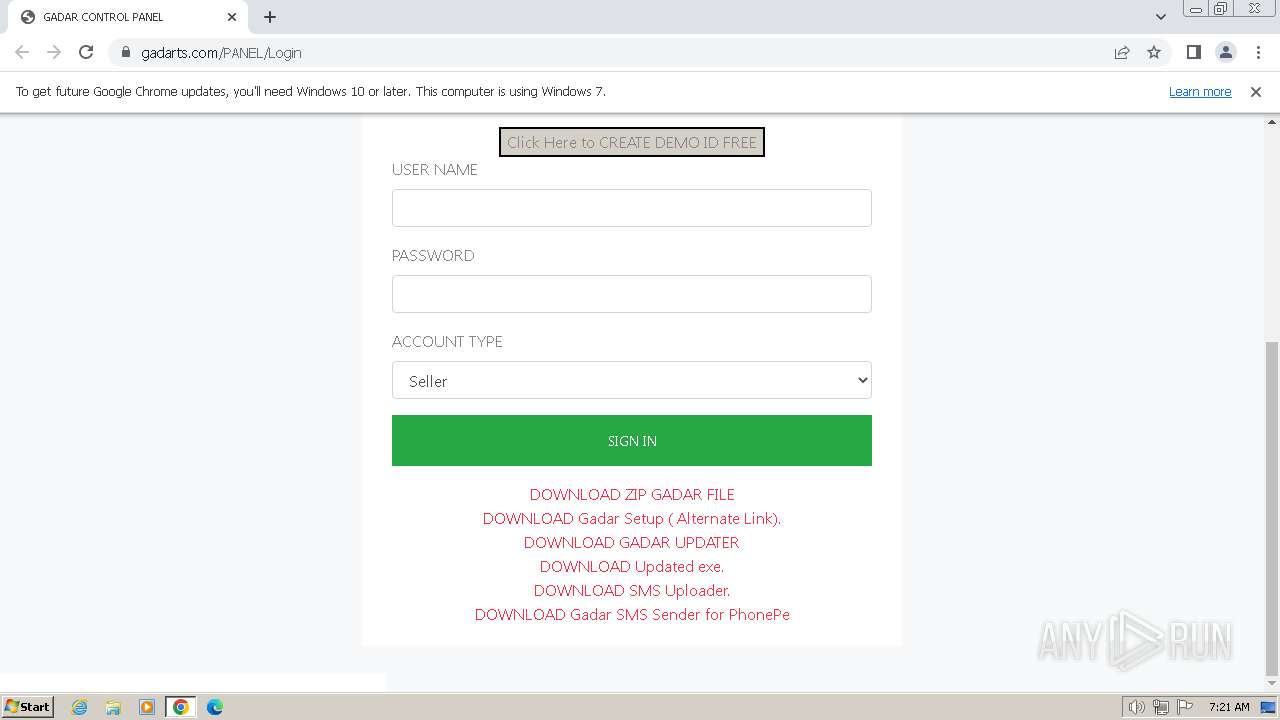
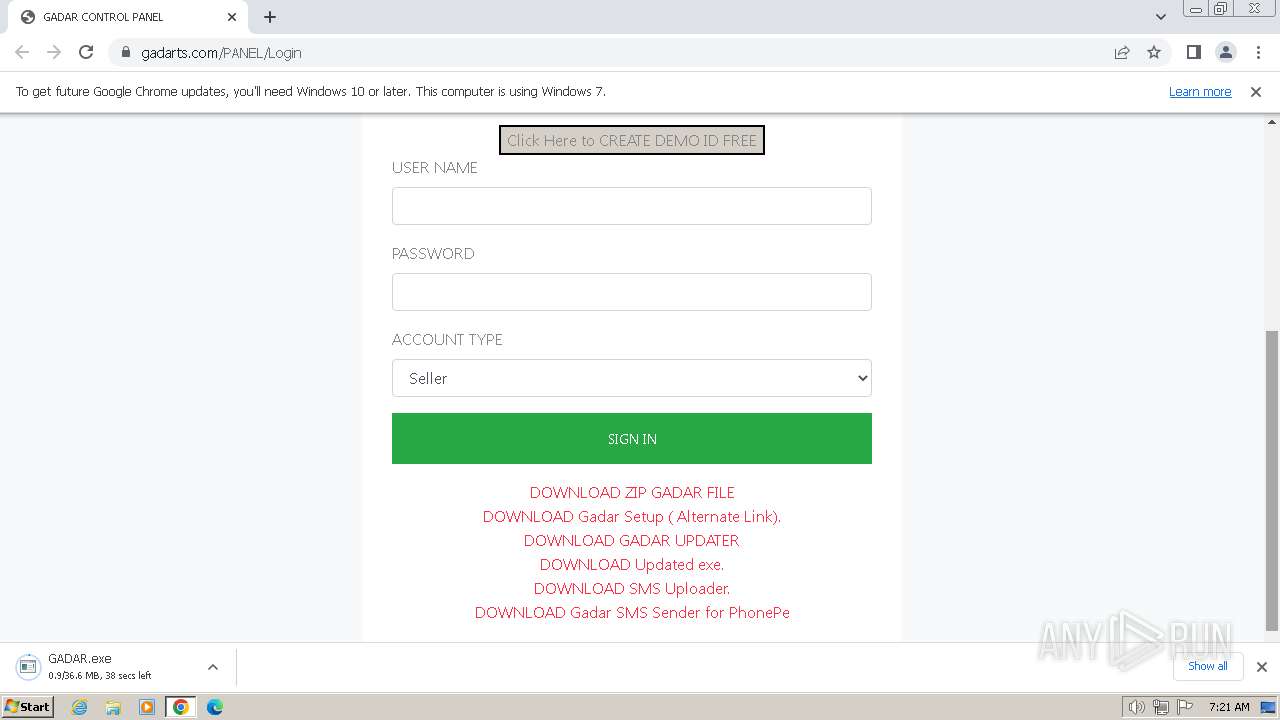
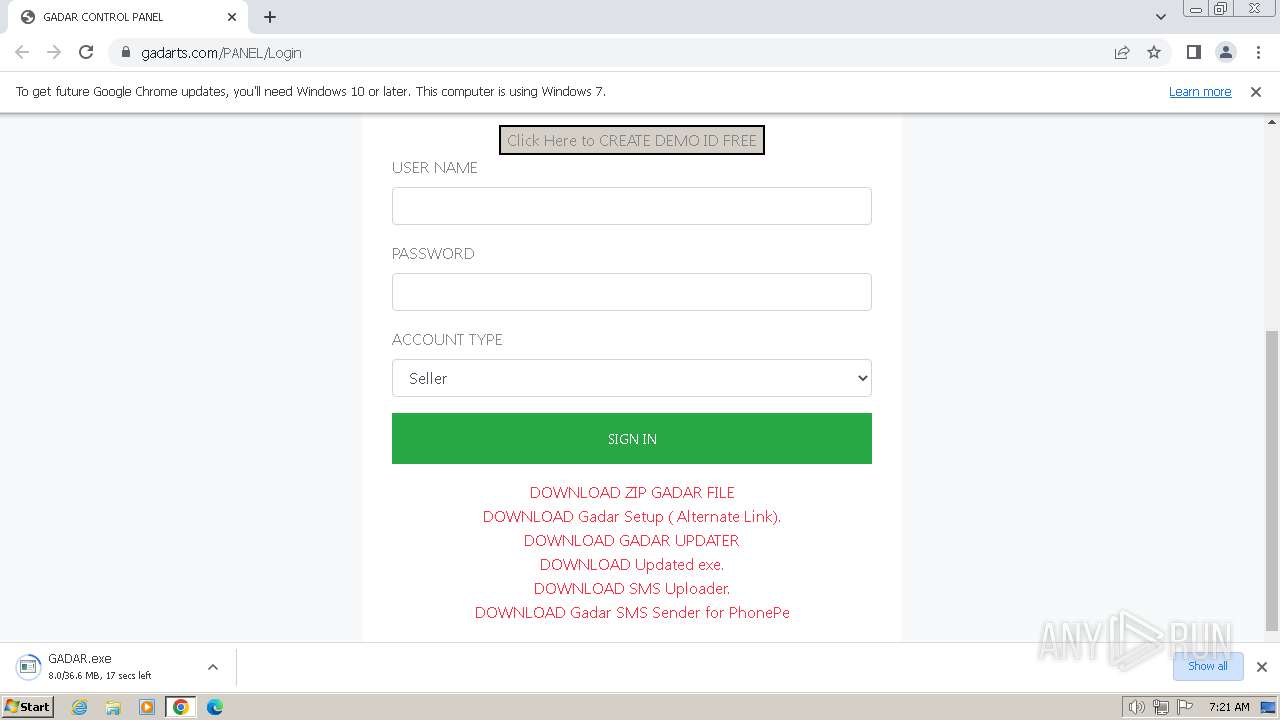
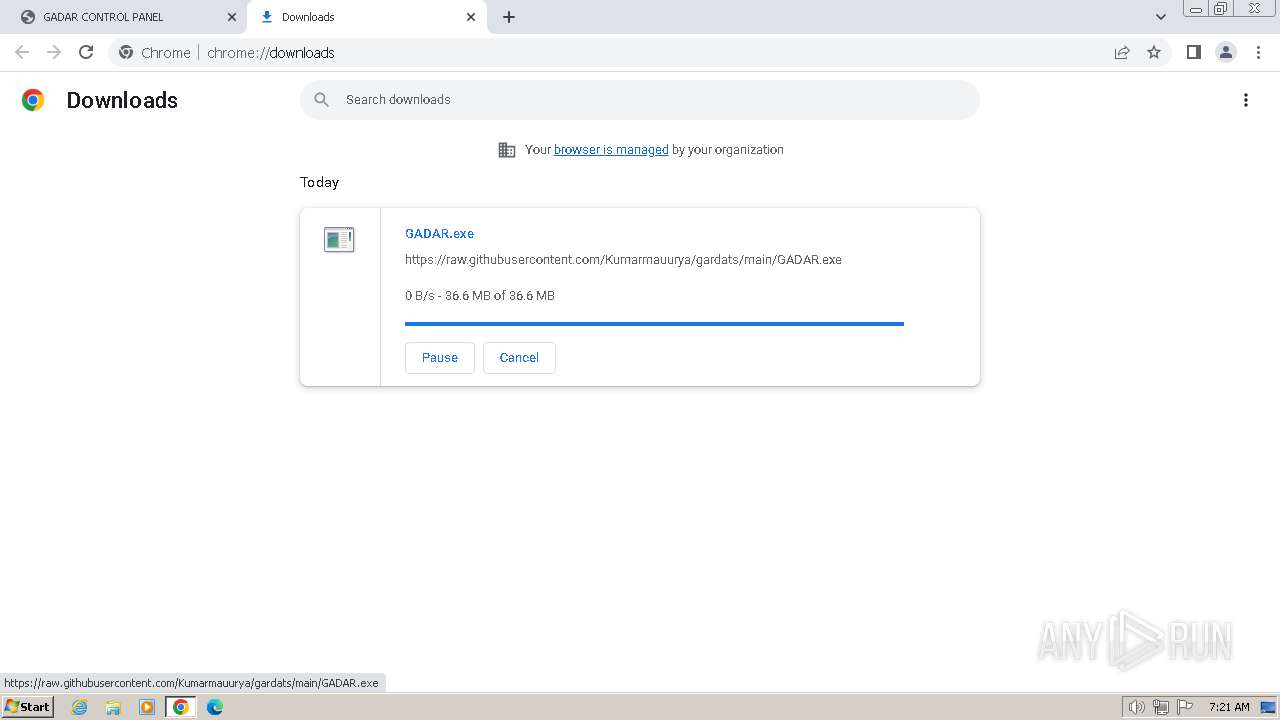
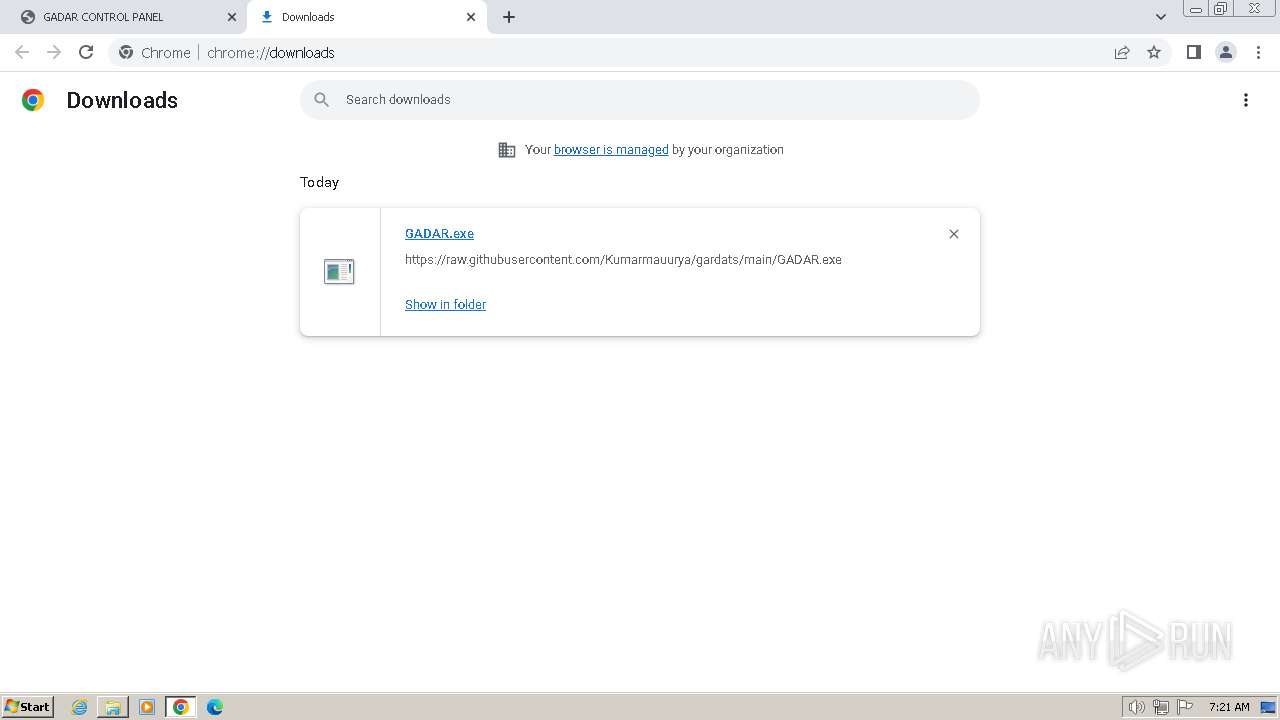
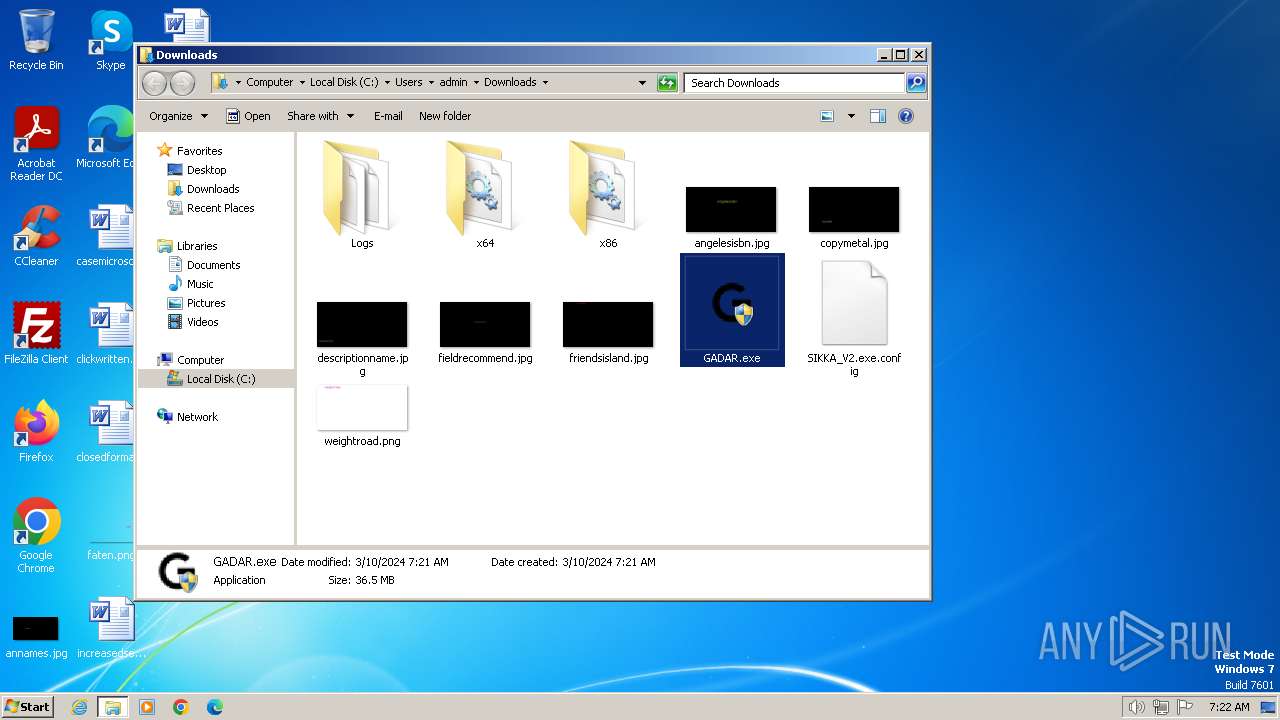
| URL: | gadarts.com |
| Full analysis: | https://app.any.run/tasks/72fce855-79cd-4d95-bbdf-6b682bbdd914 |
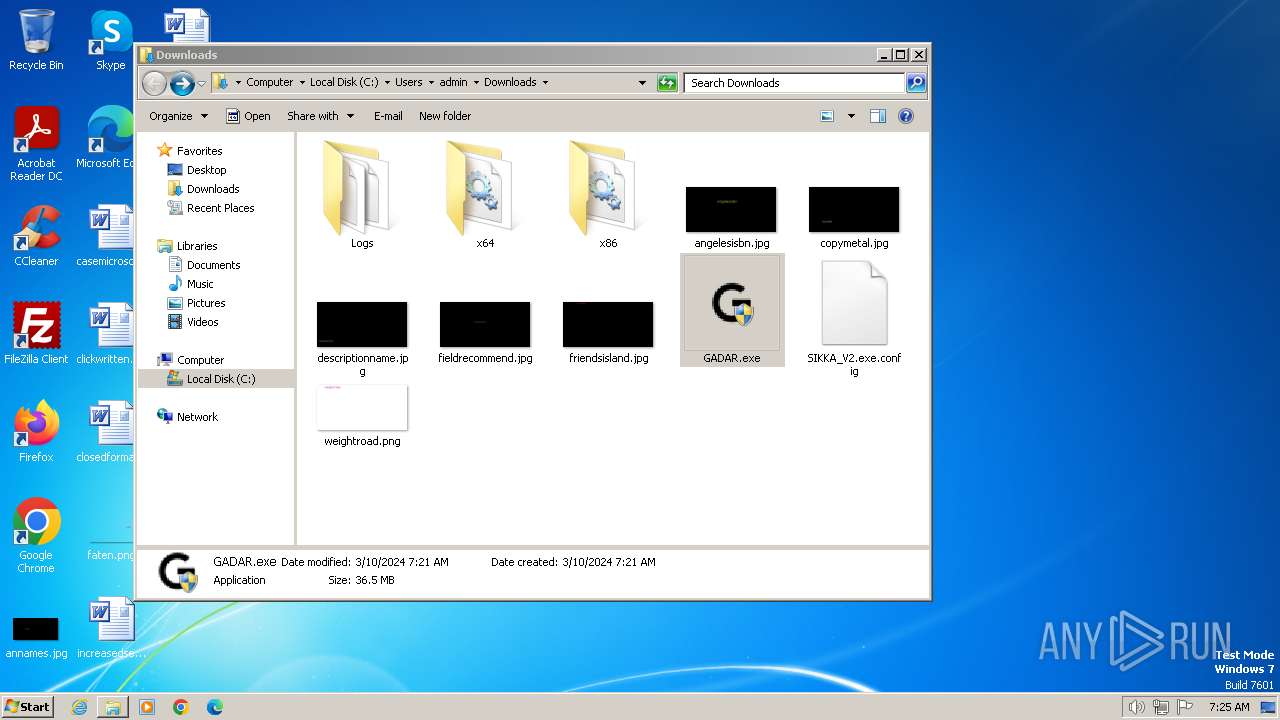
| Verdict: | Malicious activity |
| Analysis date: | March 10, 2024, 07:20:54 |
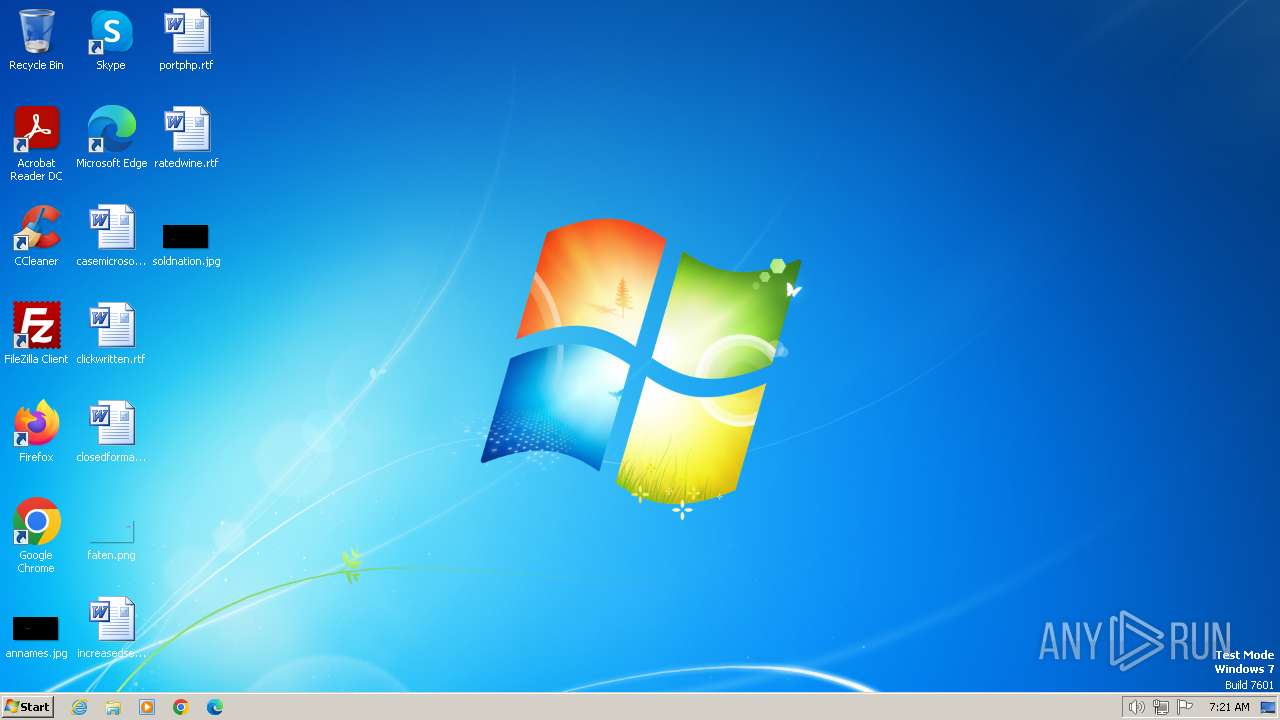
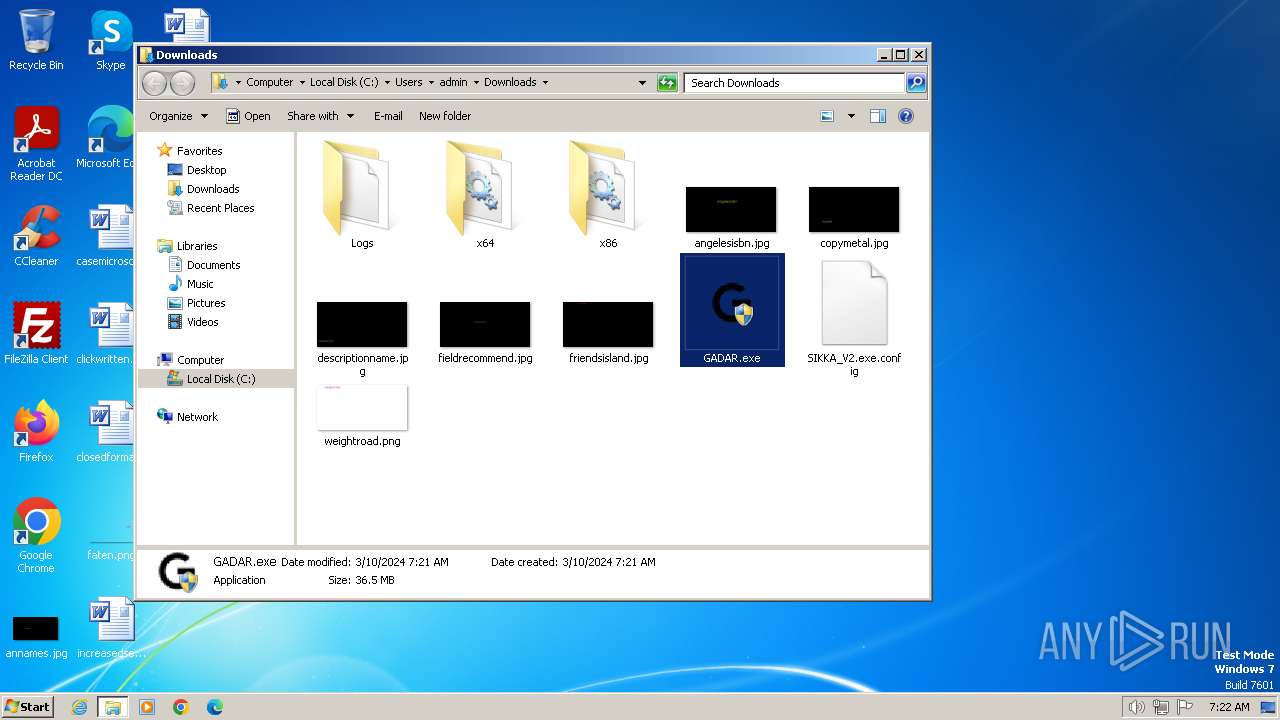
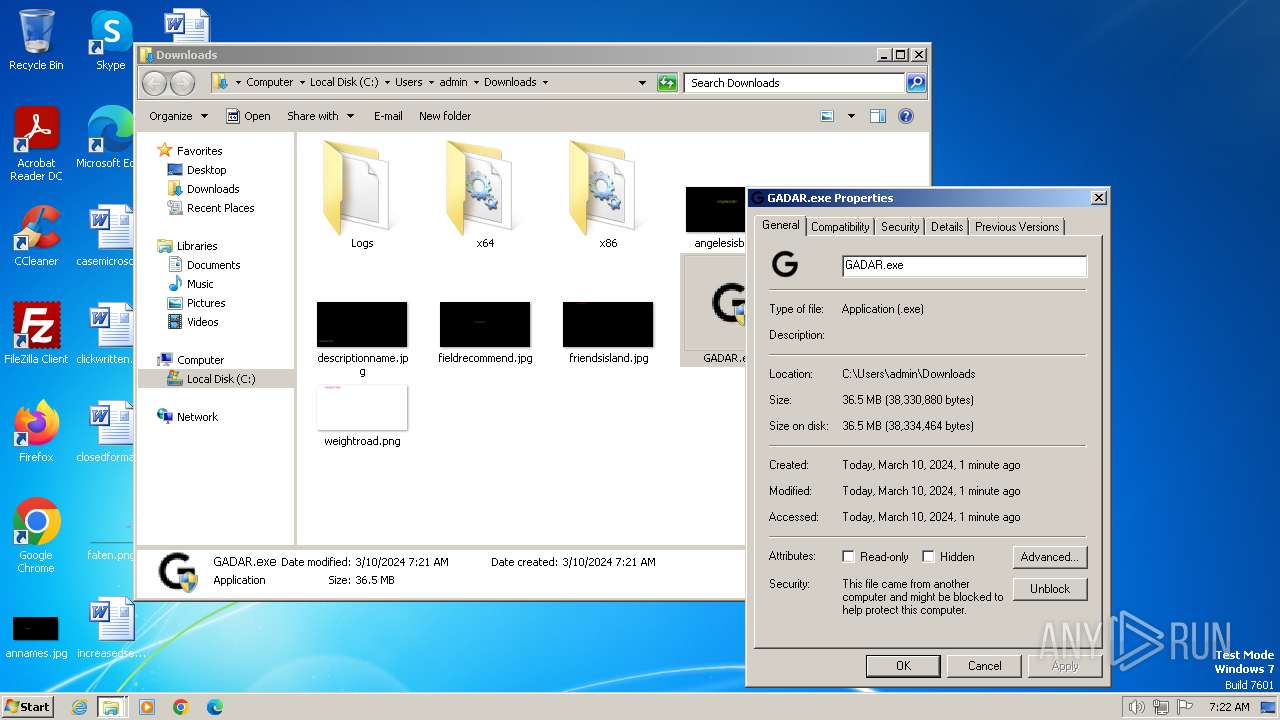
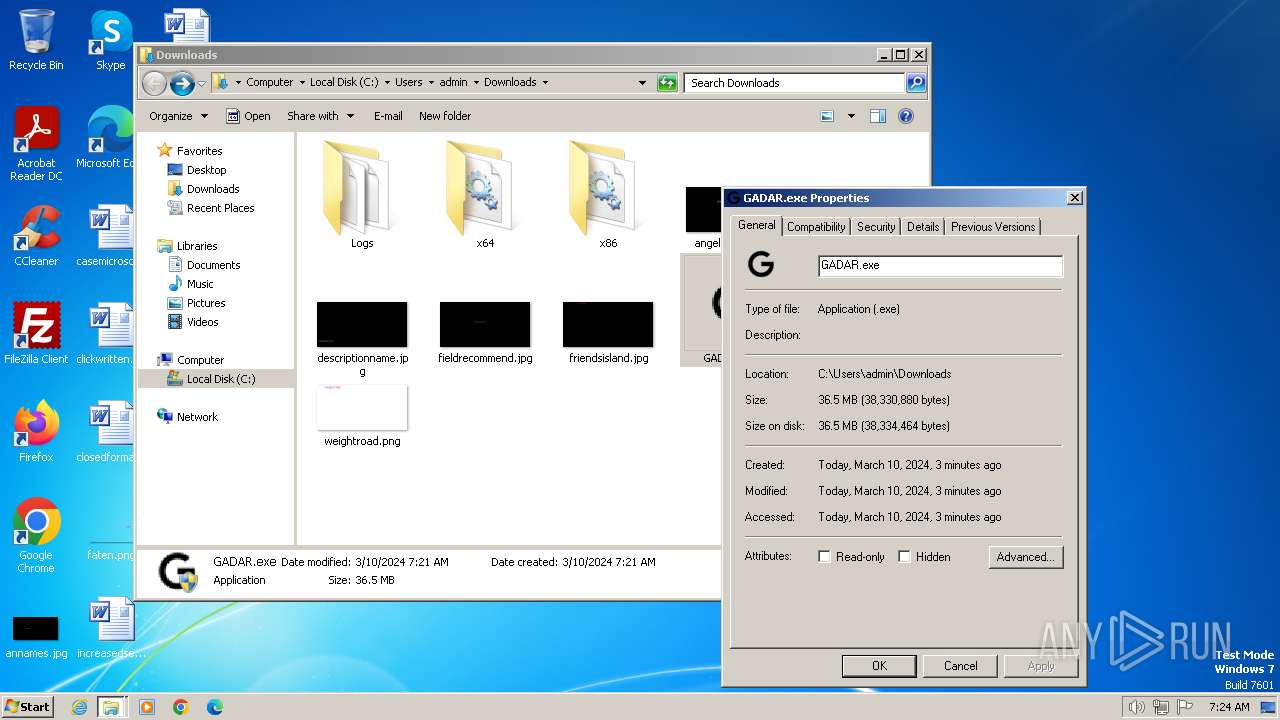
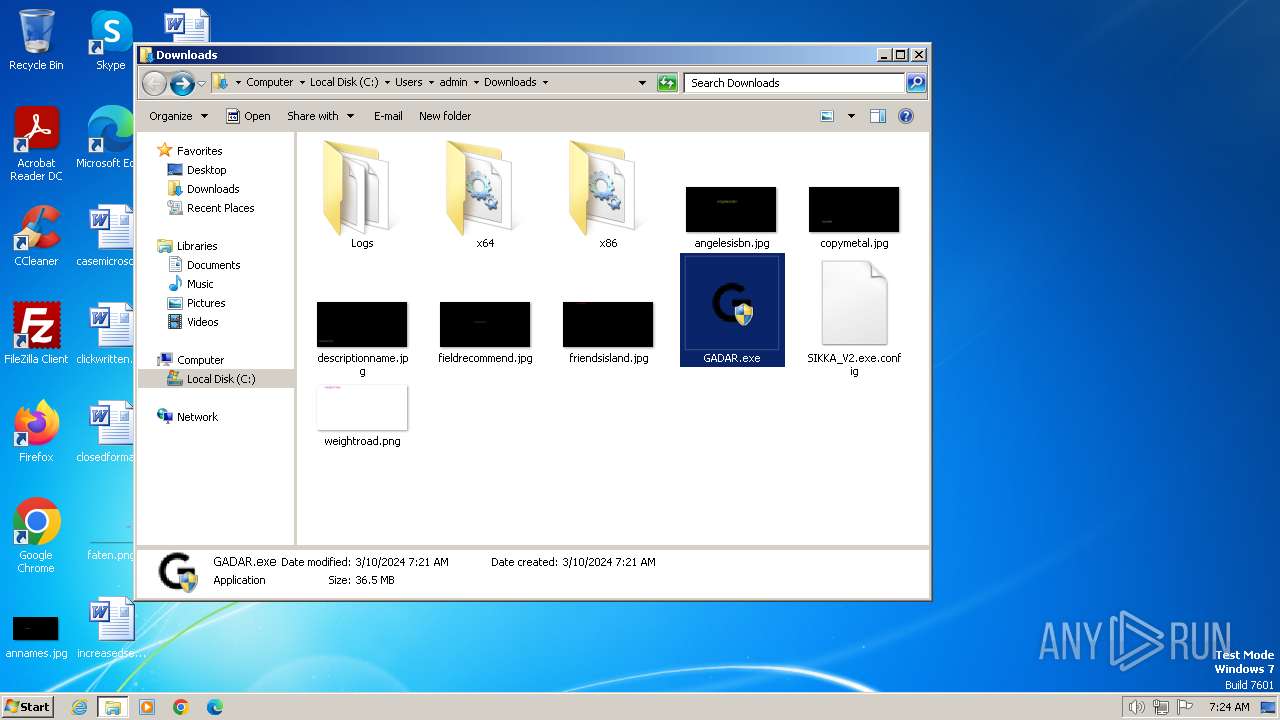
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C33120F61F8199908E6F1B15DE30CEA4 |
| SHA1: | 58DE9E06CE735FF007434B7CD76AA42E7BE76204 |
| SHA256: | EA565B0F92CB9F965308701F4619254125802D9EA4E49C36D9DFB2D14F033369 |
| SSDEEP: | 3:k+K:PK |
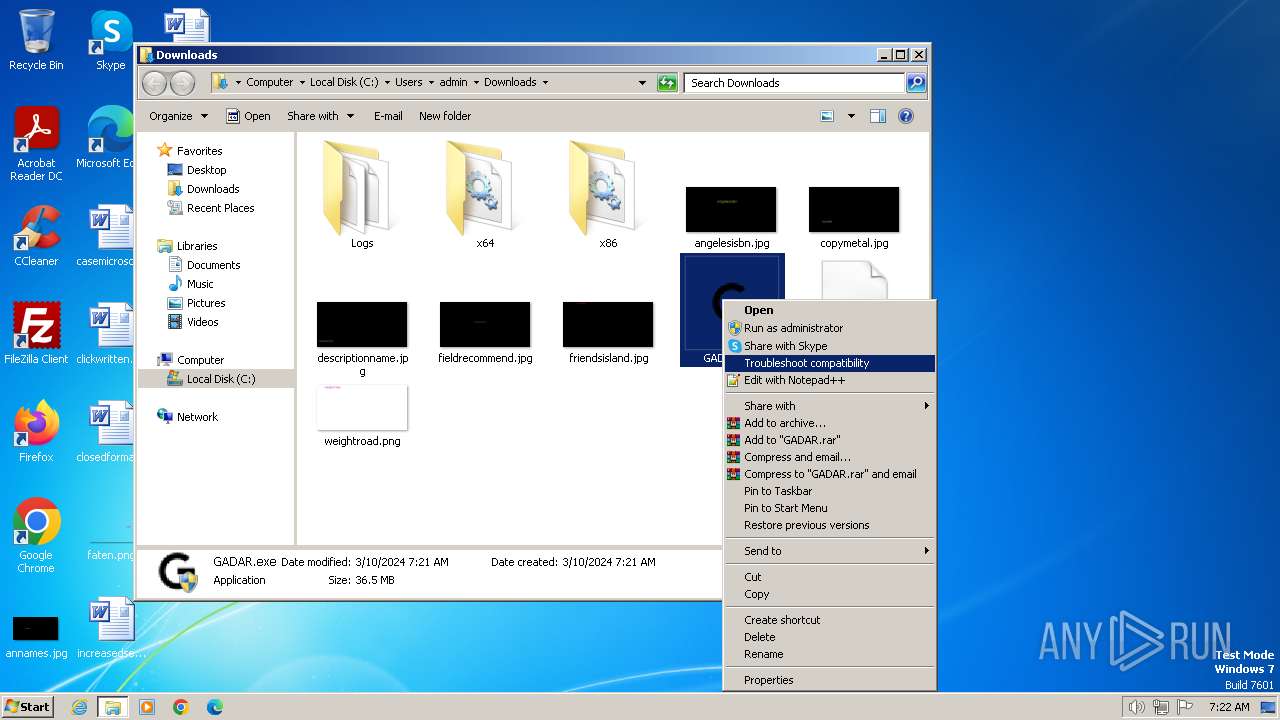
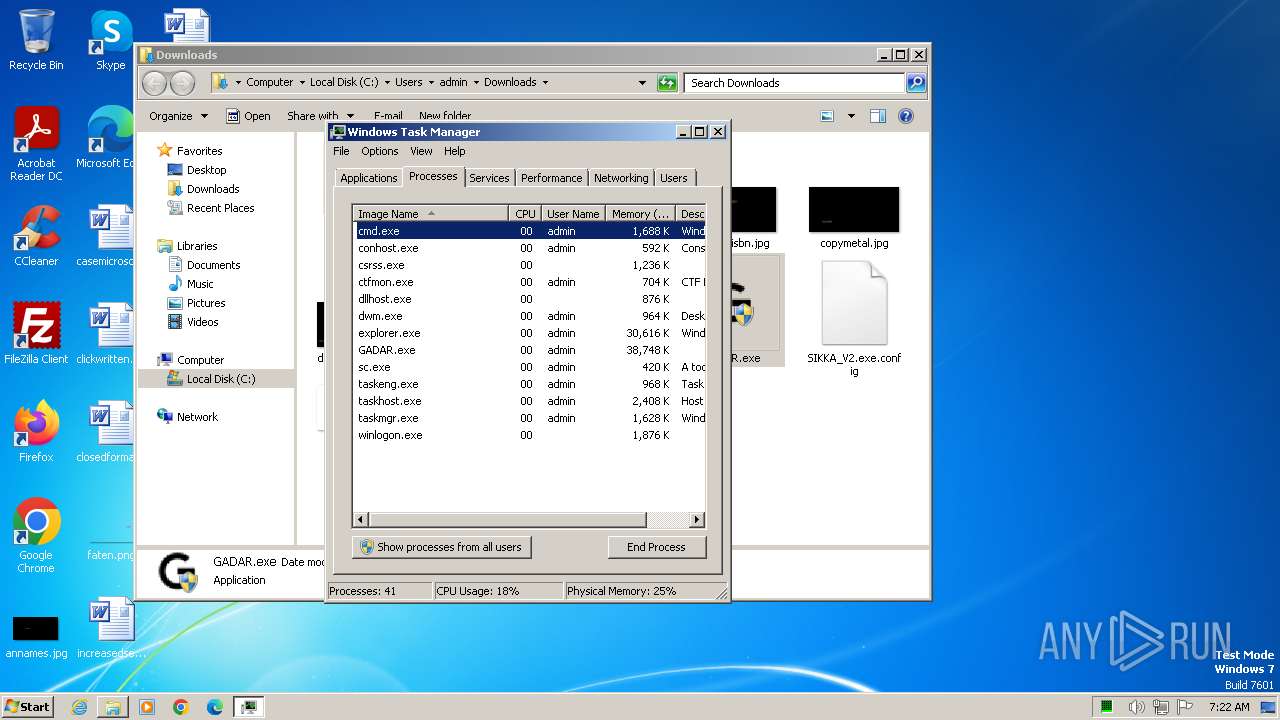
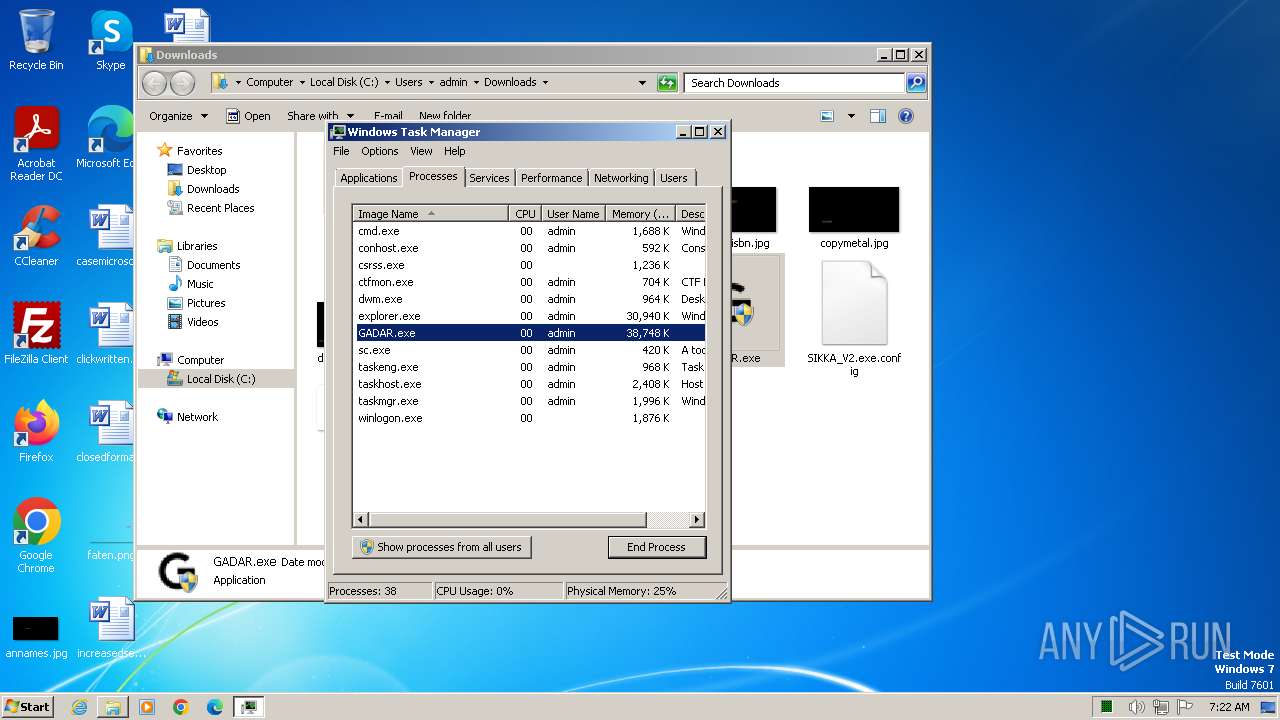
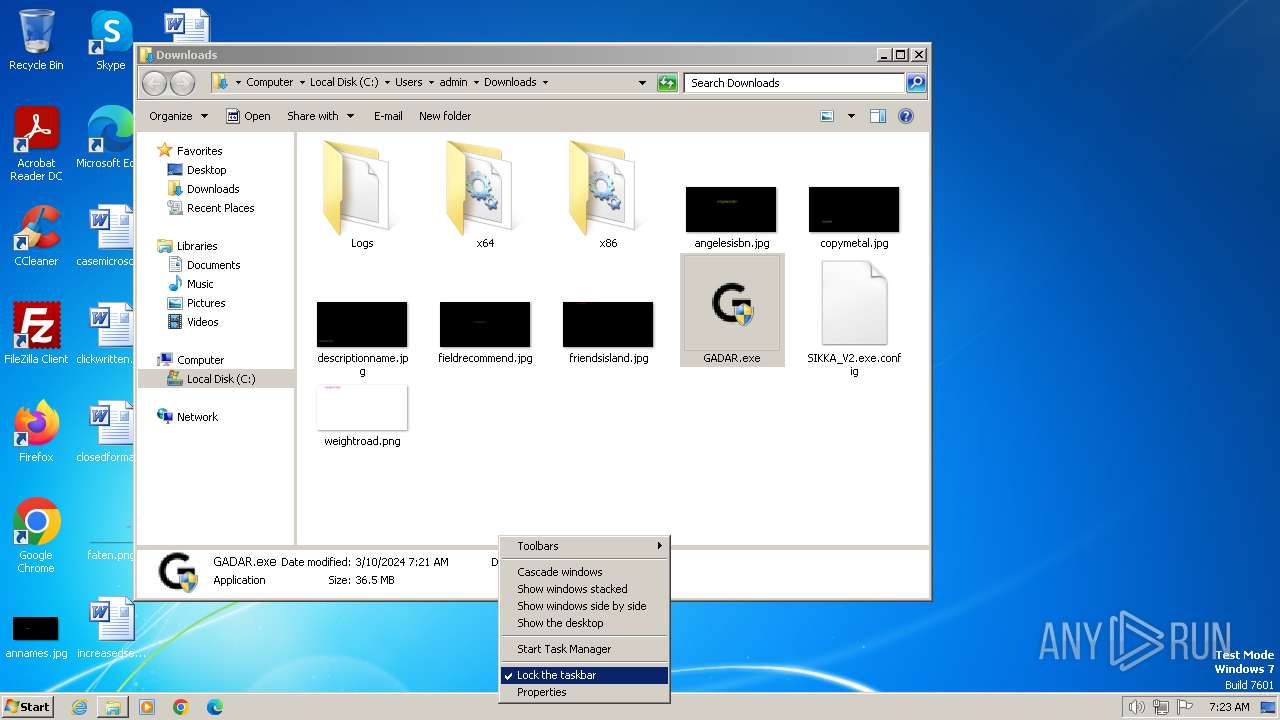
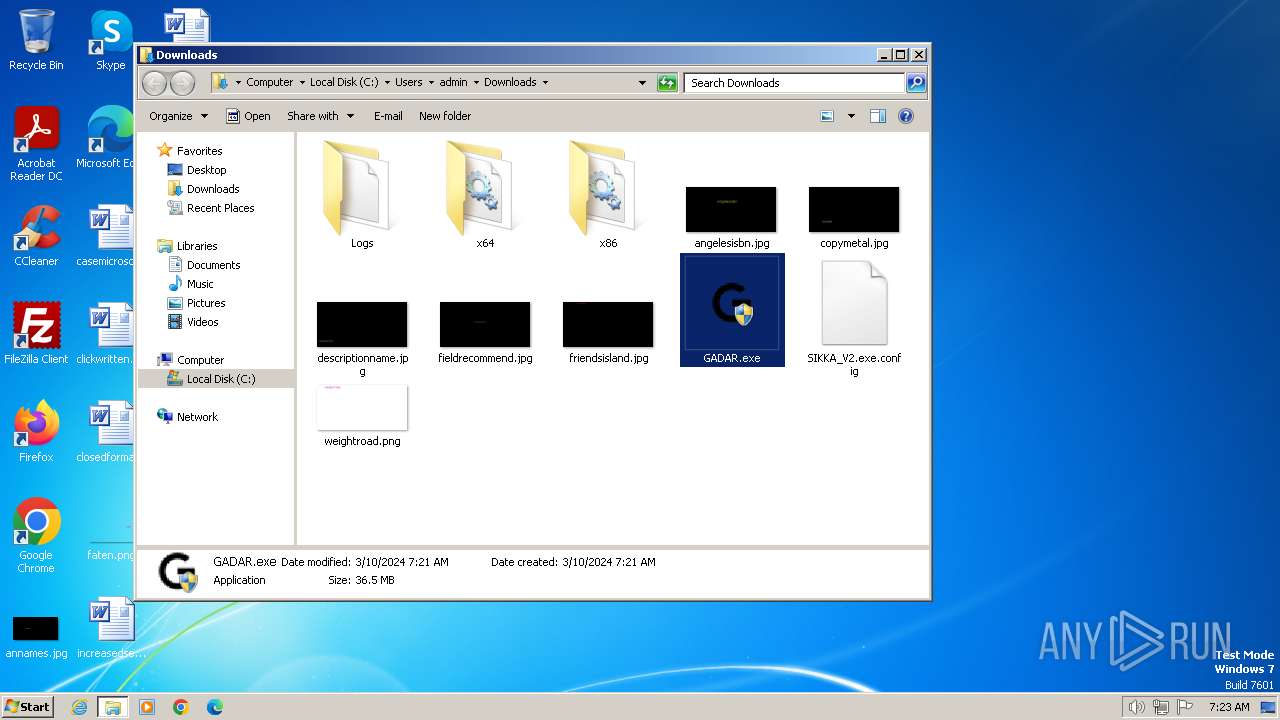
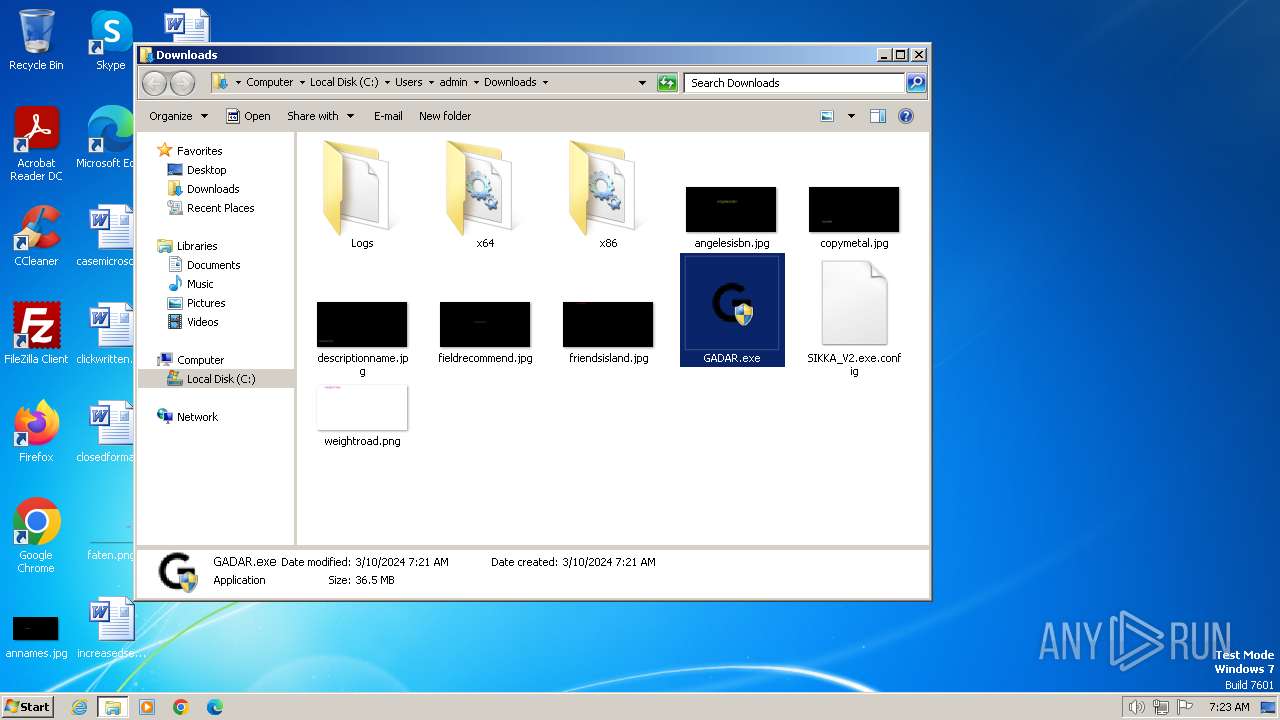
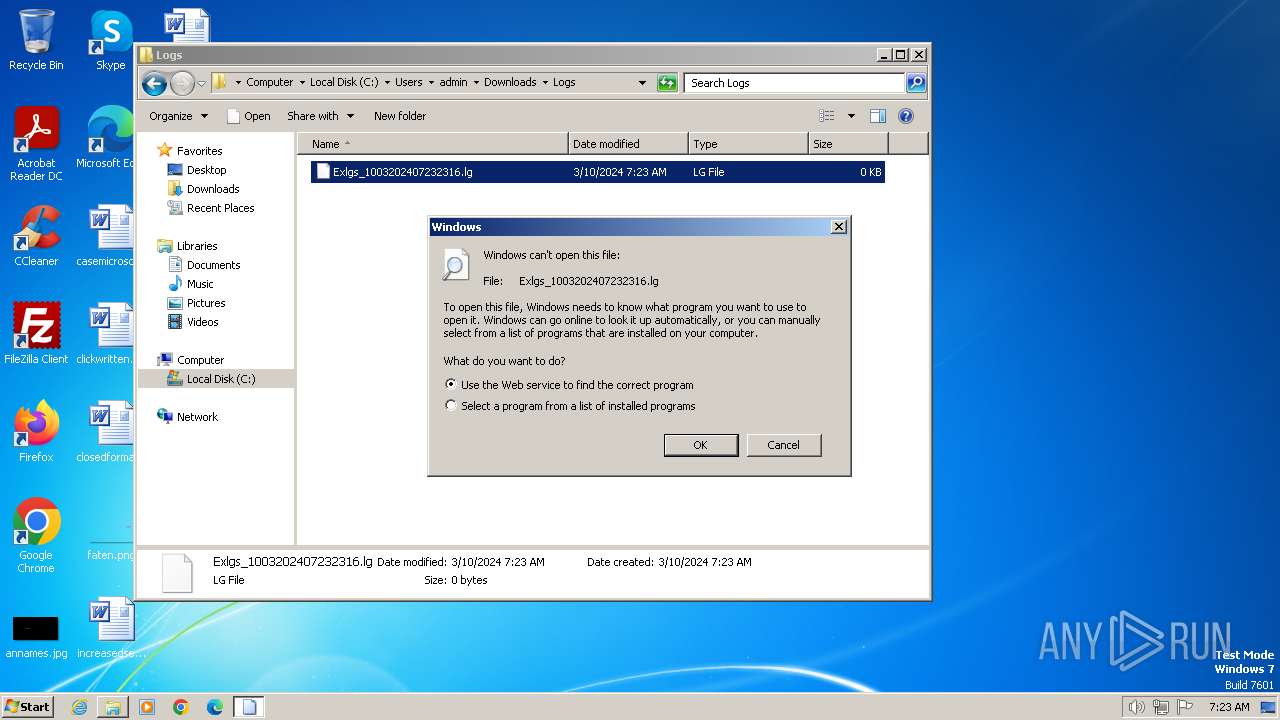
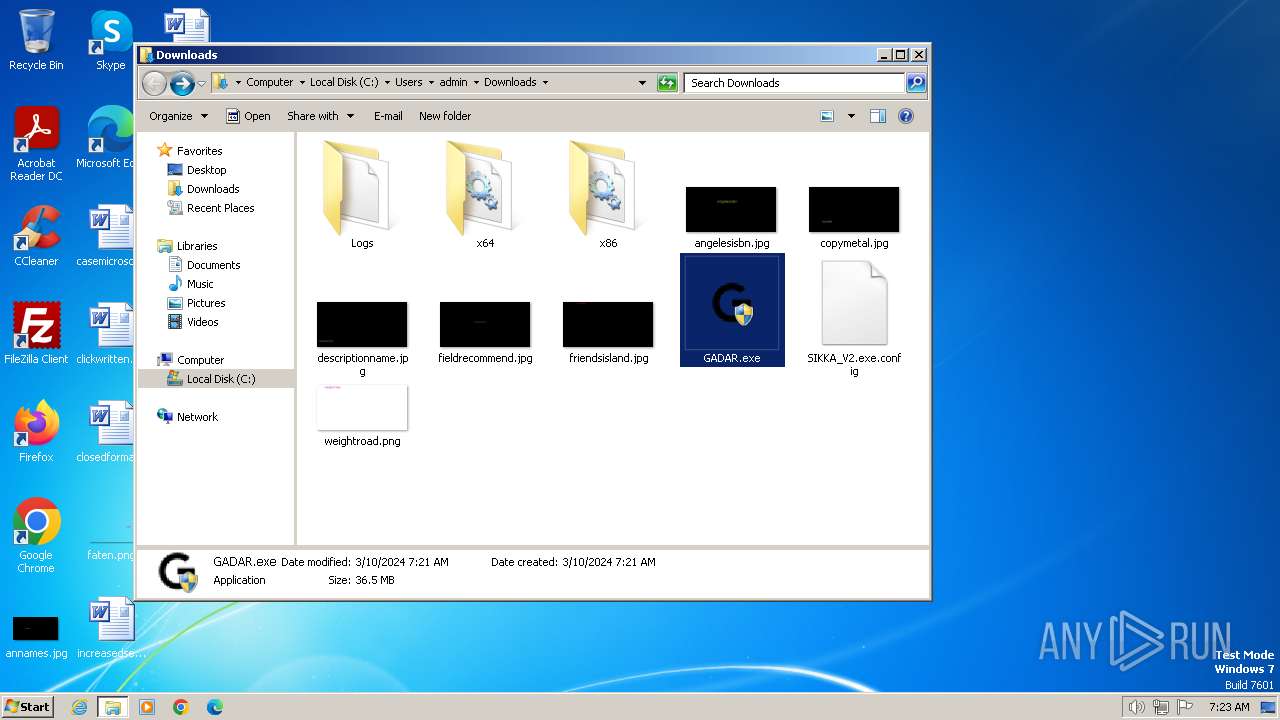
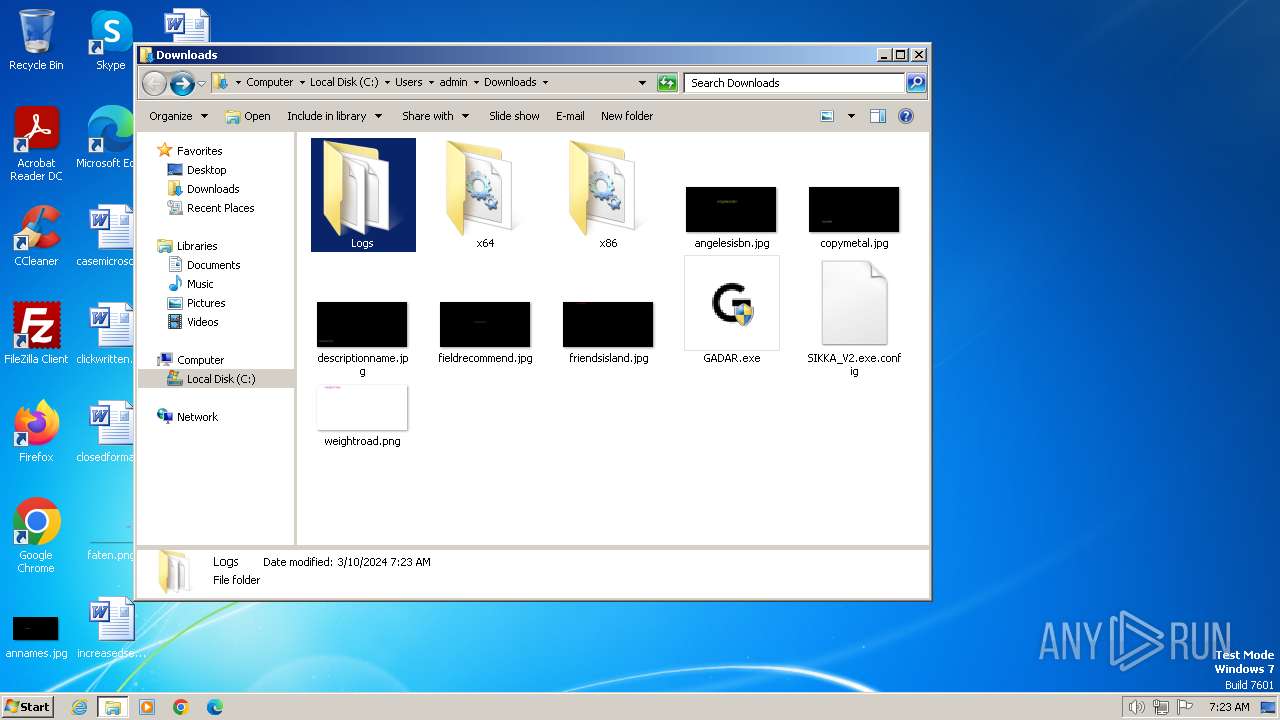
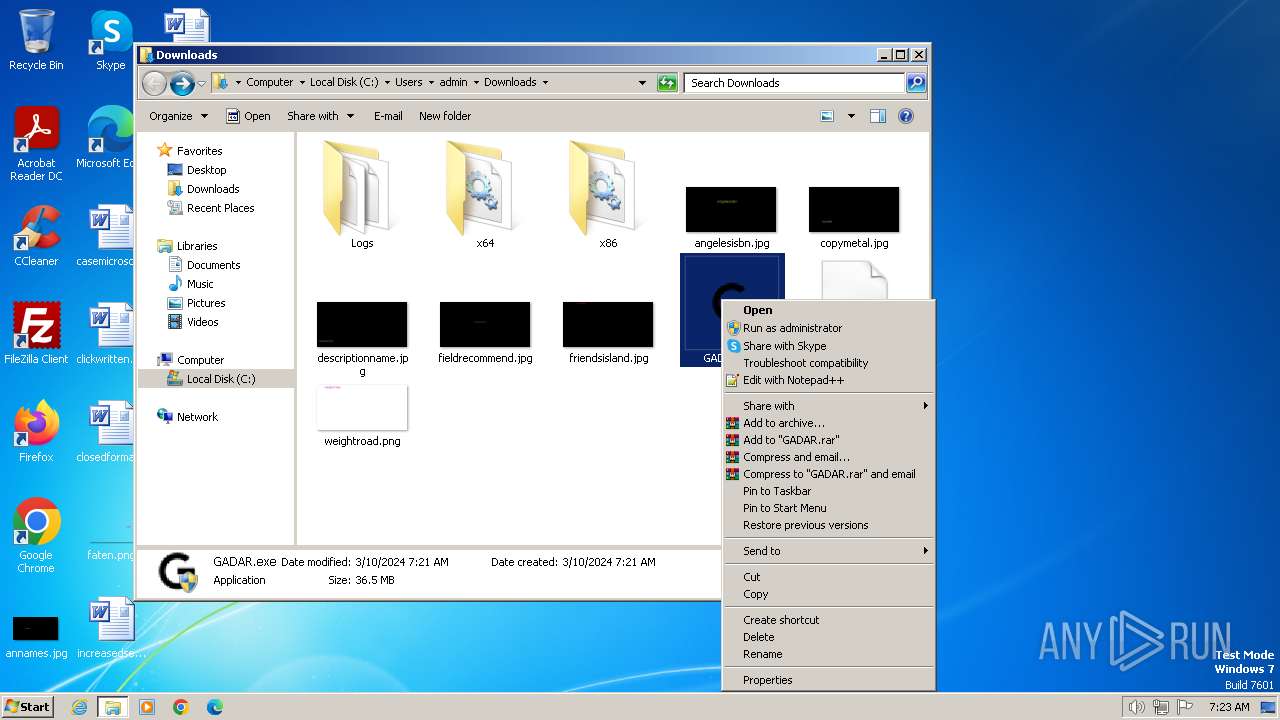
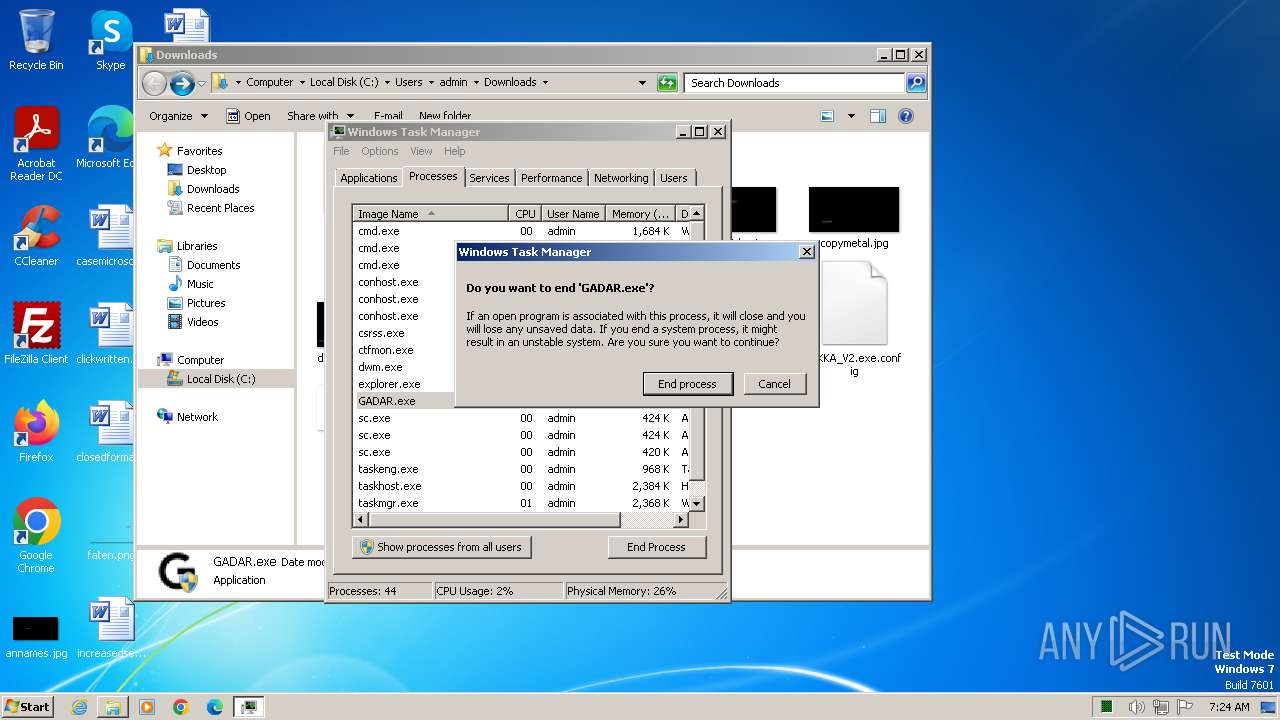
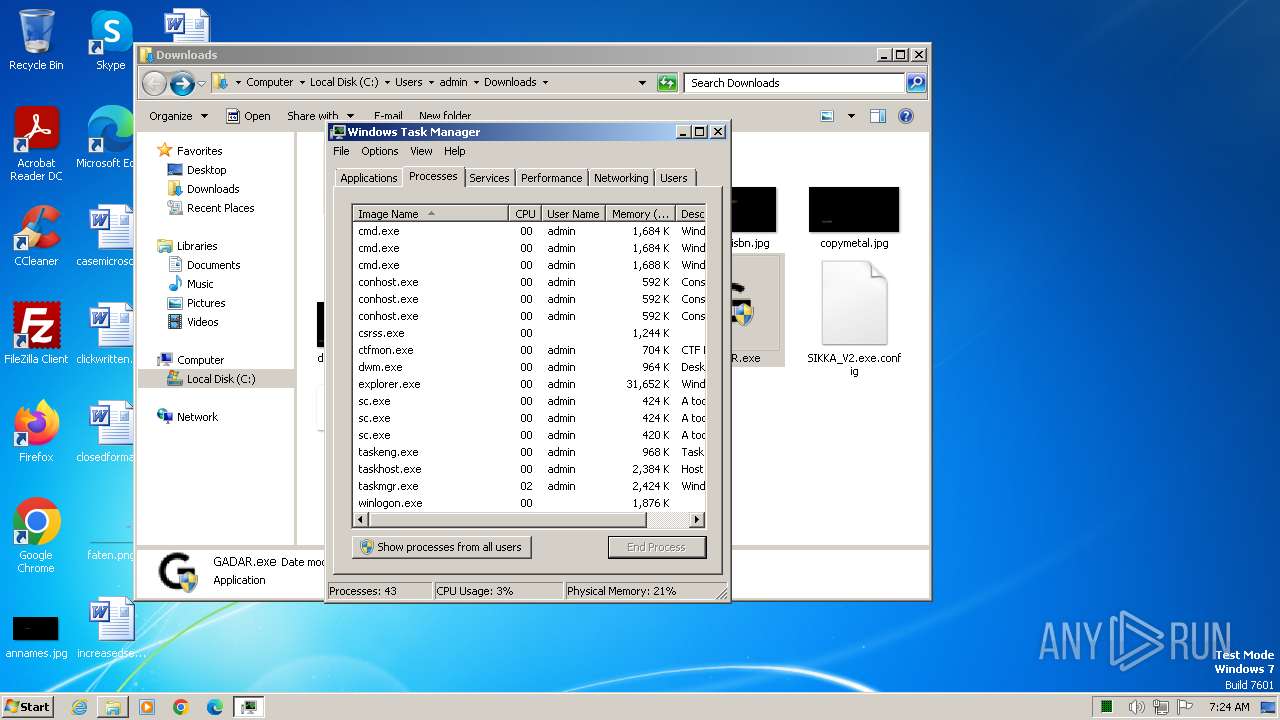
MALICIOUS
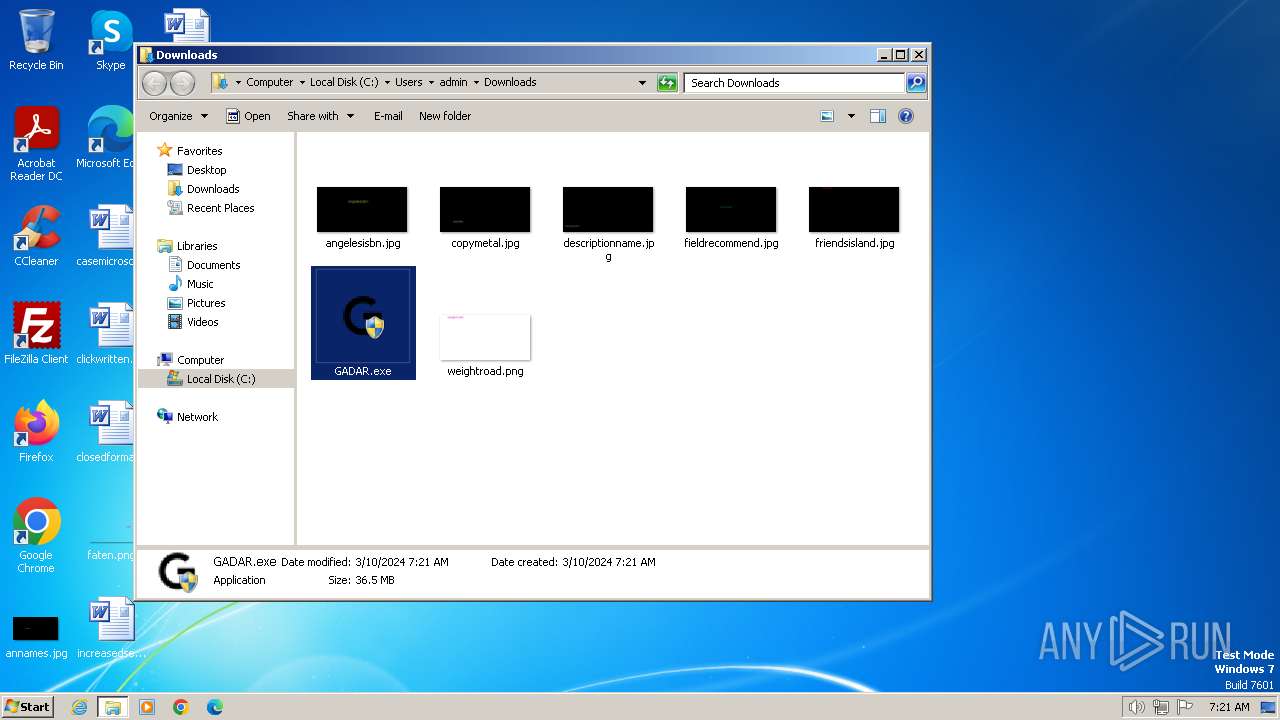
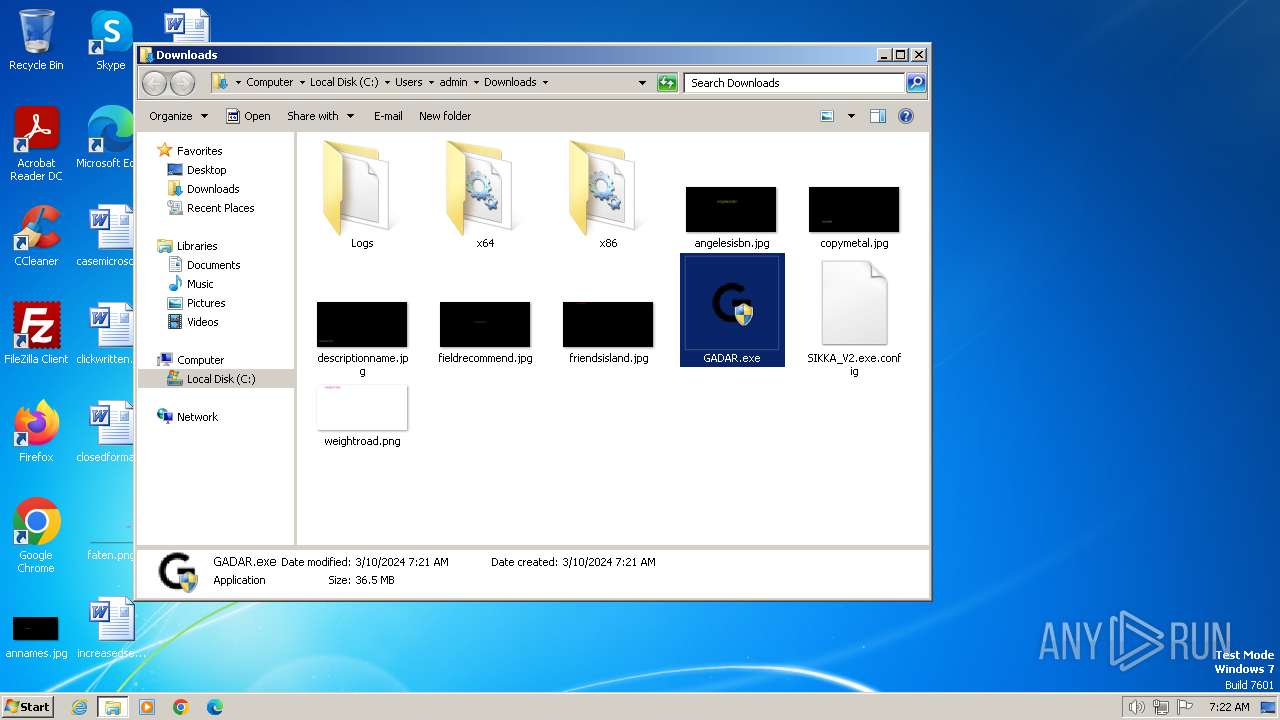
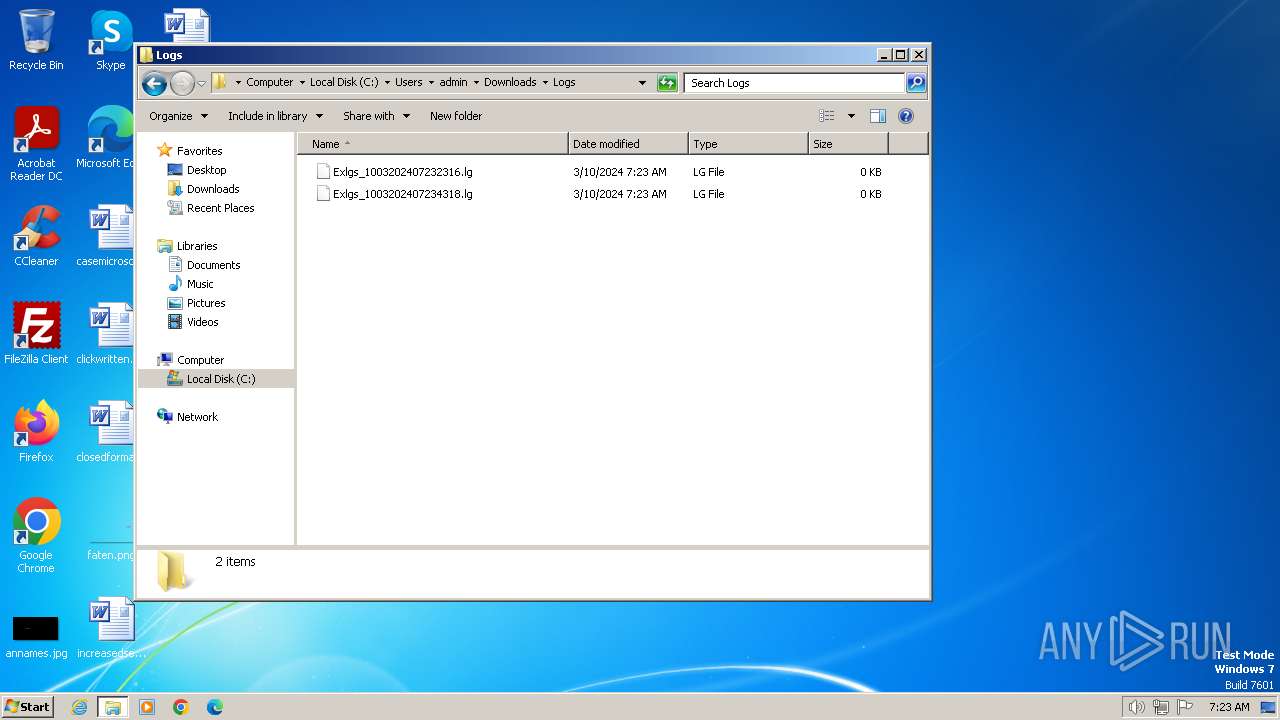
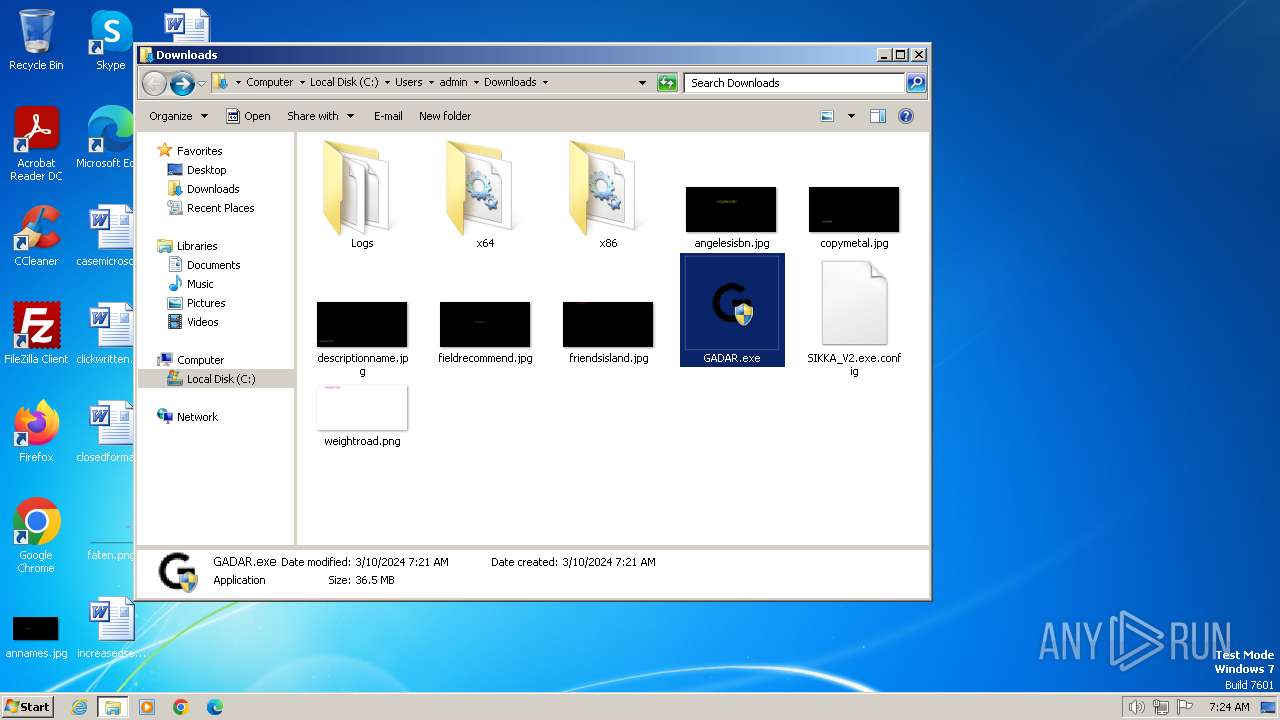
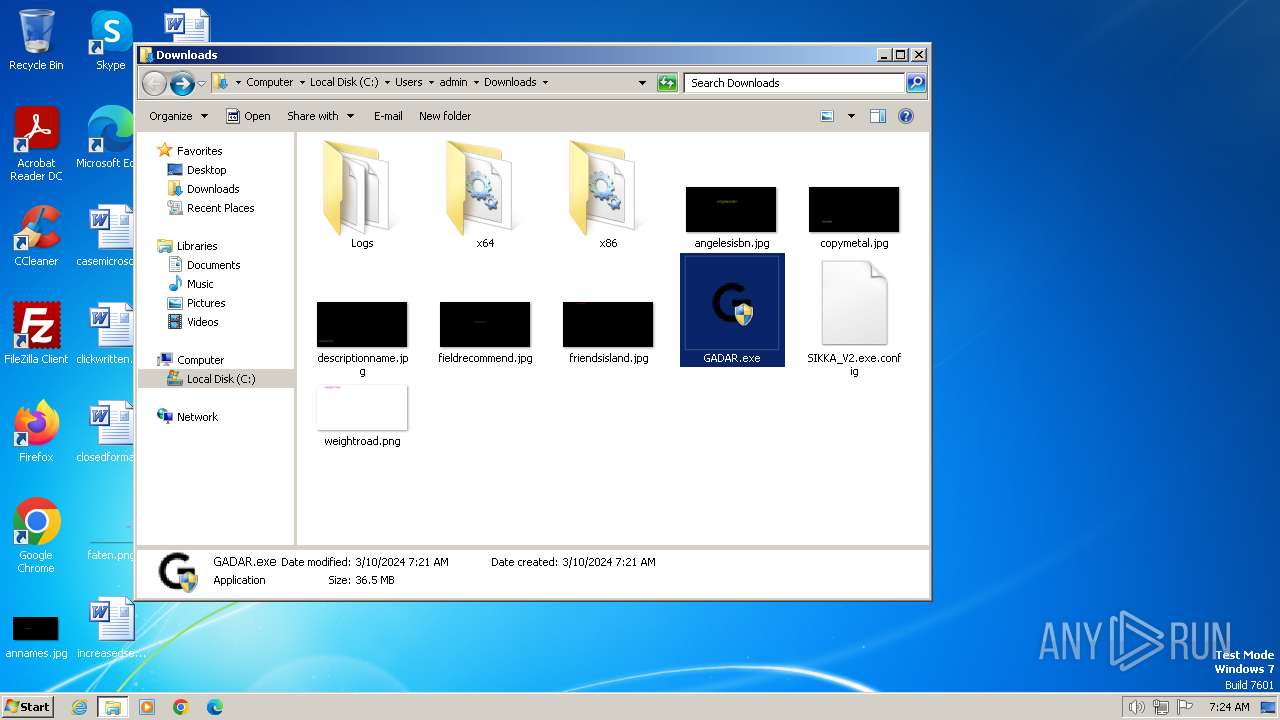
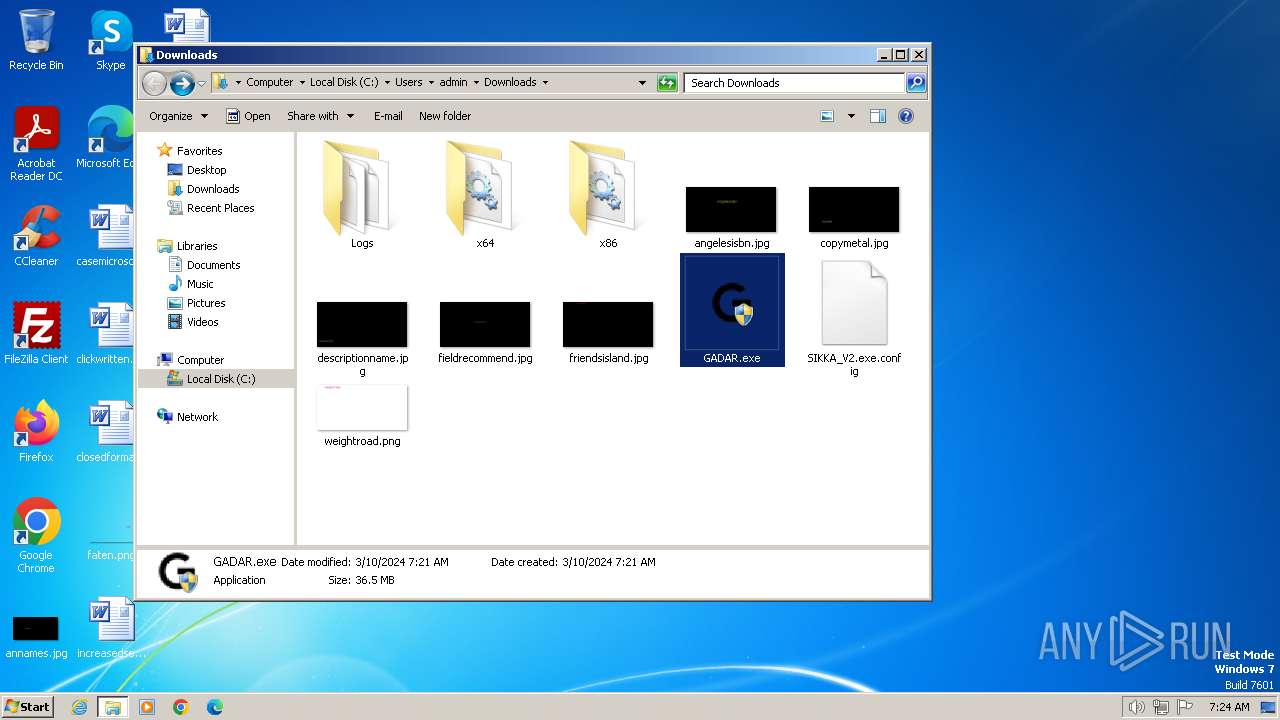
Drops the executable file immediately after the start
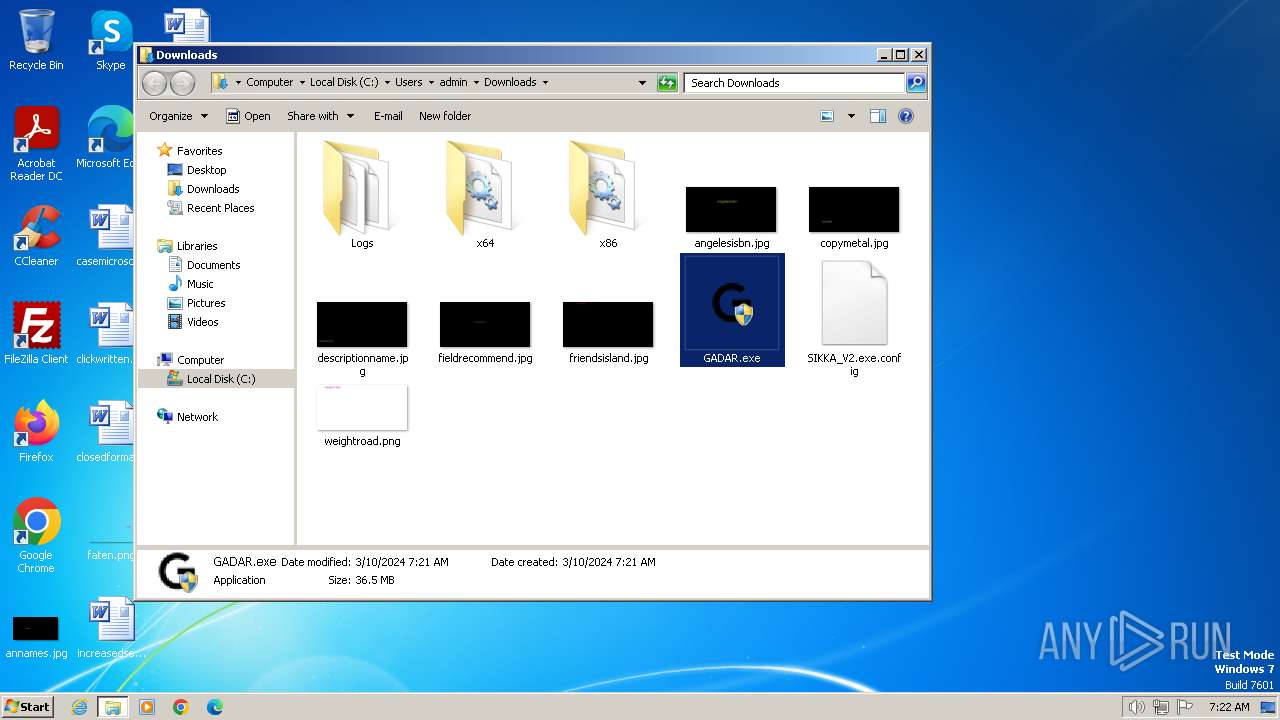
- GADAR.exe (PID: 2736)
- GADAR.exe (PID: 560)
- GADAR.exe (PID: 2064)
- GADAR.exe (PID: 1832)
- GADAR.exe (PID: 2508)
- GADAR.exe (PID: 2728)
- GADAR.exe (PID: 3376)
- GADAR.exe (PID: 3068)
- GADAR.exe (PID: 968)
- GADAR.exe (PID: 2244)
- GADAR.exe (PID: 984)
- GADAR.exe (PID: 2548)
- GADAR.exe (PID: 4000)
SUSPICIOUS
Executable content was dropped or overwritten
- GADAR.exe (PID: 2736)
- GADAR.exe (PID: 560)
- GADAR.exe (PID: 2064)
- GADAR.exe (PID: 1832)
- GADAR.exe (PID: 2508)
- GADAR.exe (PID: 2728)
- GADAR.exe (PID: 3376)
- GADAR.exe (PID: 3068)
- GADAR.exe (PID: 968)
- GADAR.exe (PID: 2244)
- GADAR.exe (PID: 984)
- GADAR.exe (PID: 4000)
- GADAR.exe (PID: 2548)
Reads the BIOS version
- GADAR.exe (PID: 2736)
- GADAR.exe (PID: 560)
- GADAR.exe (PID: 2064)
- GADAR.exe (PID: 1832)
- GADAR.exe (PID: 2508)
- GADAR.exe (PID: 2728)
- GADAR.exe (PID: 3376)
- GADAR.exe (PID: 3068)
- GADAR.exe (PID: 968)
- GADAR.exe (PID: 2244)
- GADAR.exe (PID: 984)
- GADAR.exe (PID: 2548)
- GADAR.exe (PID: 4000)
Reads the Internet Settings
- GADAR.exe (PID: 2736)
- GADAR.exe (PID: 560)
- GADAR.exe (PID: 1832)
- GADAR.exe (PID: 2064)
- GADAR.exe (PID: 2508)
- GADAR.exe (PID: 2728)
- GADAR.exe (PID: 3376)
- GADAR.exe (PID: 3068)
- GADAR.exe (PID: 968)
- GADAR.exe (PID: 2244)
- GADAR.exe (PID: 984)
- GADAR.exe (PID: 2548)
- GADAR.exe (PID: 4000)
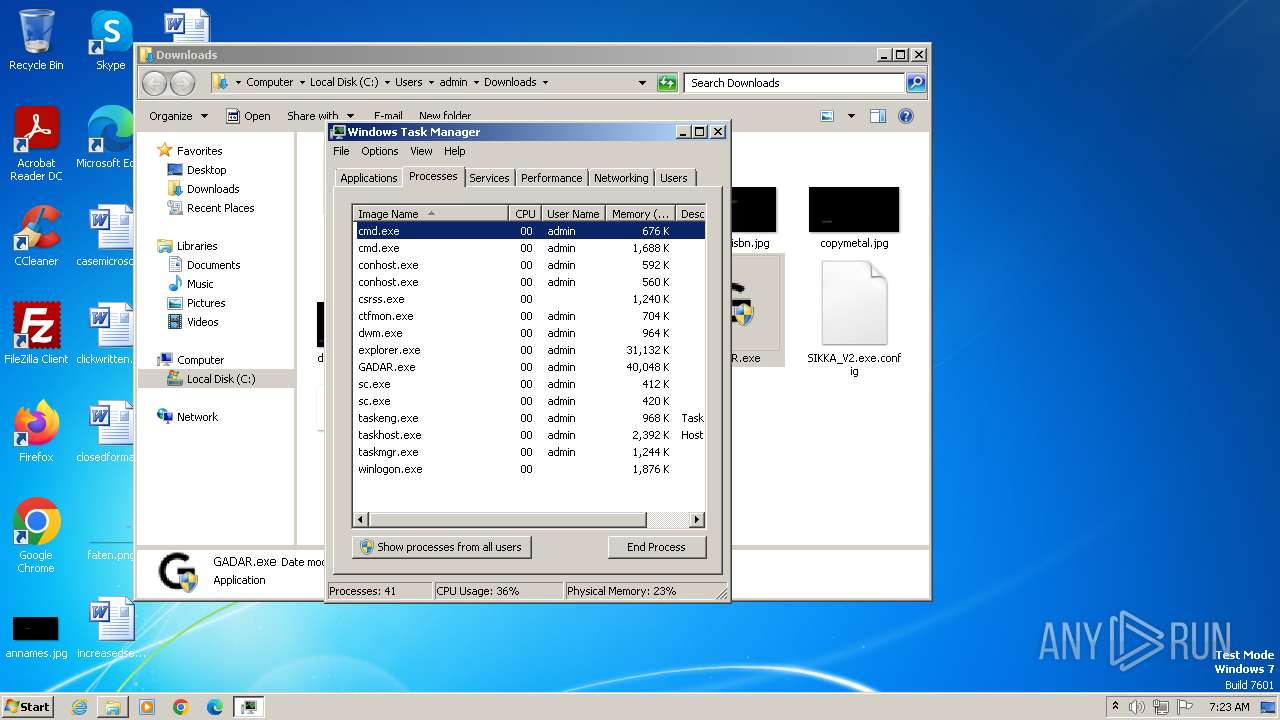
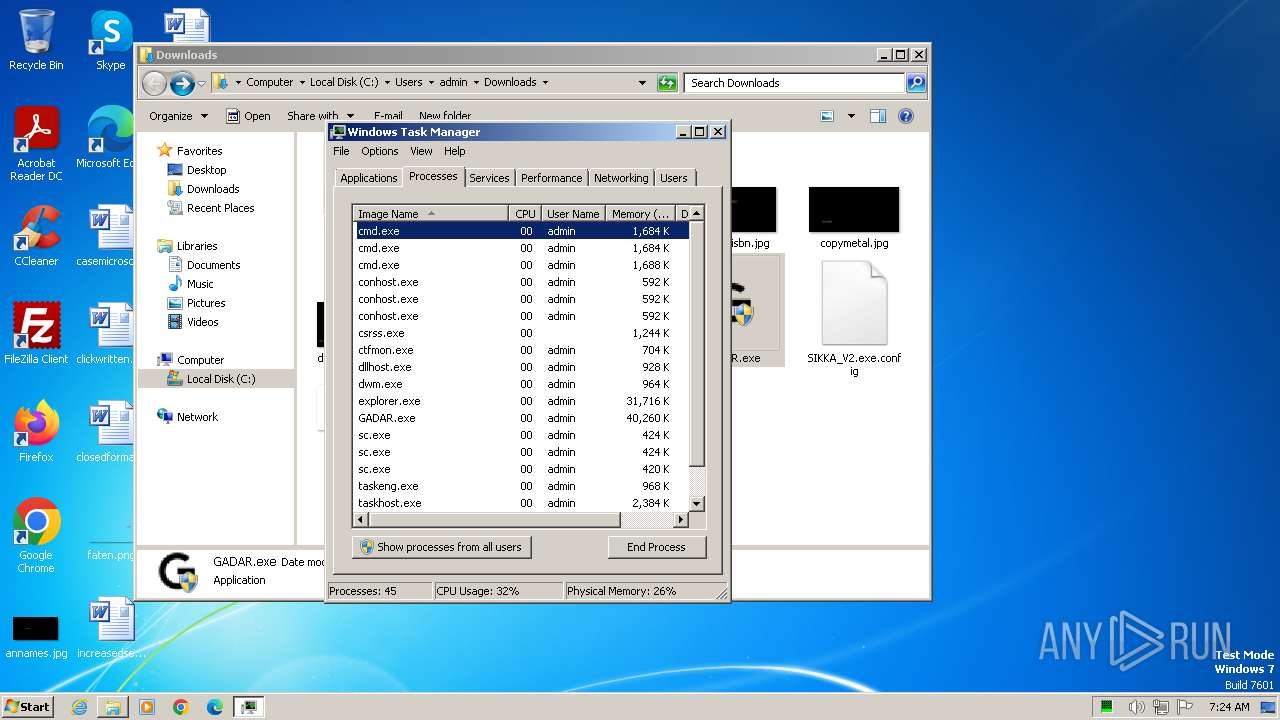
Starts CMD.EXE for commands execution
- GADAR.exe (PID: 2736)
- GADAR.exe (PID: 1832)
- GADAR.exe (PID: 2508)
- GADAR.exe (PID: 3068)
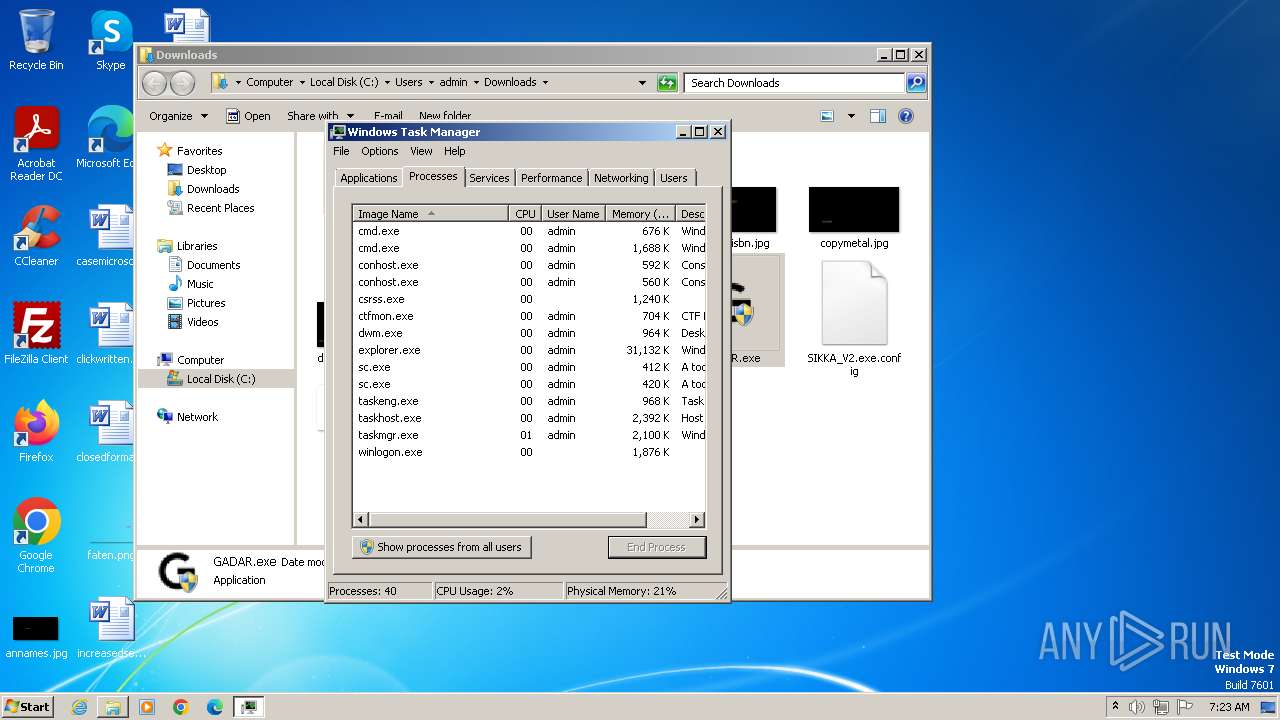
Starts SC.EXE for service management
- cmd.exe (PID: 3048)
- cmd.exe (PID: 2568)
- cmd.exe (PID: 844)
- cmd.exe (PID: 2256)
Reads settings of System Certificates
- GADAR.exe (PID: 1832)
- GADAR.exe (PID: 2508)
- GADAR.exe (PID: 3068)
INFO
Application launched itself
- chrome.exe (PID: 3700)
Checks supported languages
- GADAR.exe (PID: 2736)
- GADAR.exe (PID: 560)
- GADAR.exe (PID: 2064)
- GADAR.exe (PID: 1832)
- GADAR.exe (PID: 2508)
- GADAR.exe (PID: 2728)
- GADAR.exe (PID: 3376)
- GADAR.exe (PID: 3068)
- GADAR.exe (PID: 968)
- GADAR.exe (PID: 2244)
- GADAR.exe (PID: 2548)
- GADAR.exe (PID: 984)
- GADAR.exe (PID: 4000)
Reads the computer name
- GADAR.exe (PID: 2736)
- GADAR.exe (PID: 560)
- GADAR.exe (PID: 2064)
- GADAR.exe (PID: 1832)
- GADAR.exe (PID: 2508)
- GADAR.exe (PID: 2728)
- GADAR.exe (PID: 3376)
- GADAR.exe (PID: 3068)
- GADAR.exe (PID: 968)
- GADAR.exe (PID: 2244)
- GADAR.exe (PID: 984)
- GADAR.exe (PID: 2548)
- GADAR.exe (PID: 4000)
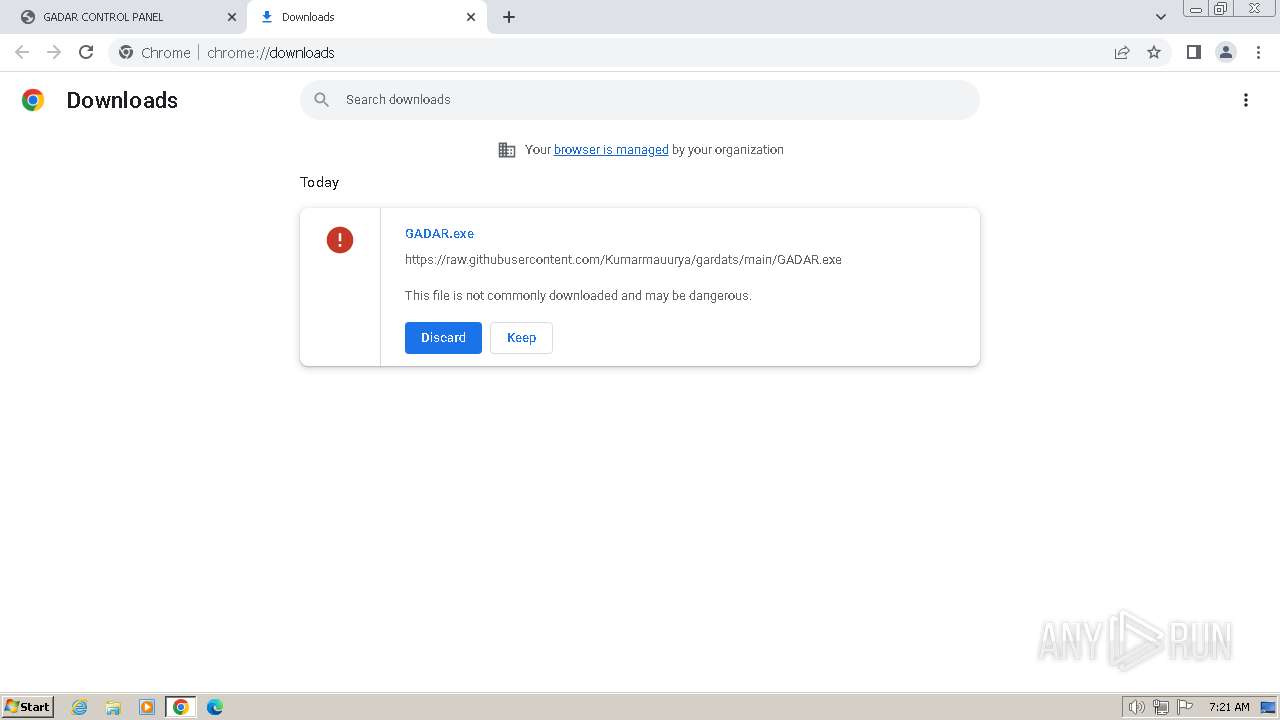
Drops the executable file immediately after the start
- chrome.exe (PID: 3700)
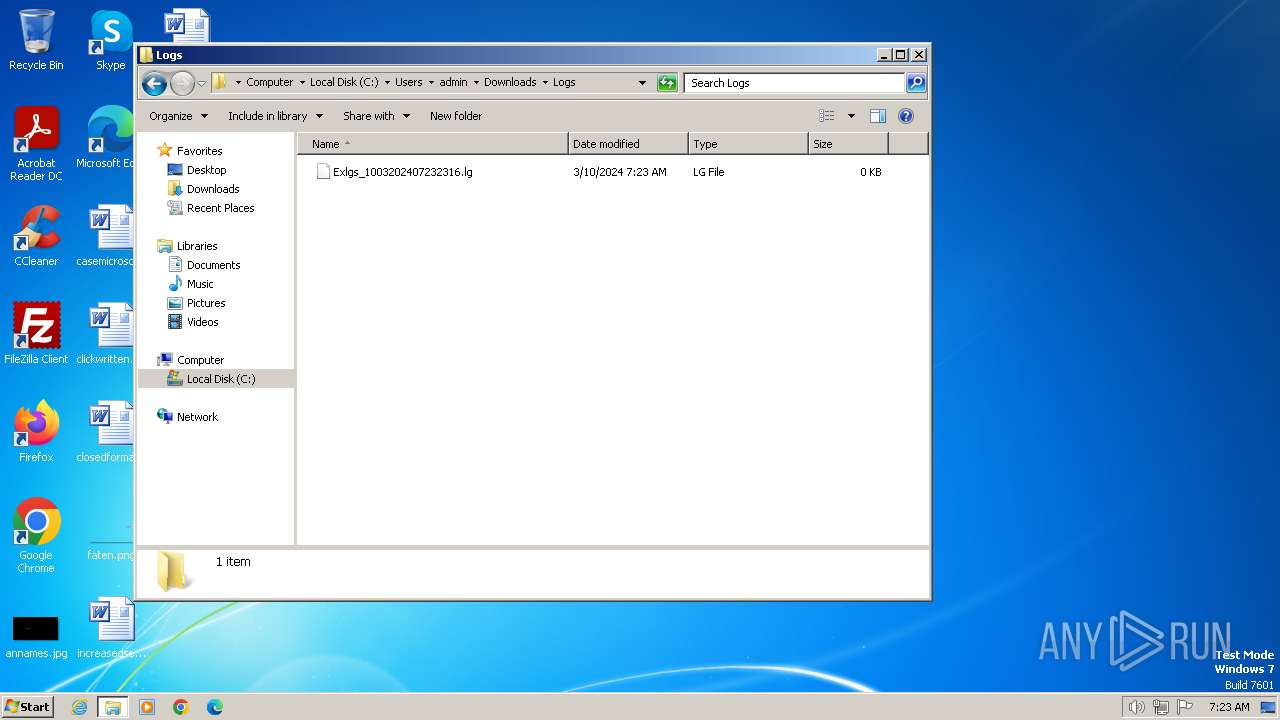
Create files in a temporary directory
- GADAR.exe (PID: 2736)
- GADAR.exe (PID: 560)
- GADAR.exe (PID: 2064)
- GADAR.exe (PID: 1832)
- GADAR.exe (PID: 2508)
- GADAR.exe (PID: 3376)
- GADAR.exe (PID: 2728)
- GADAR.exe (PID: 3068)
- GADAR.exe (PID: 968)
- GADAR.exe (PID: 2244)
- GADAR.exe (PID: 984)
- GADAR.exe (PID: 2548)
- GADAR.exe (PID: 4000)
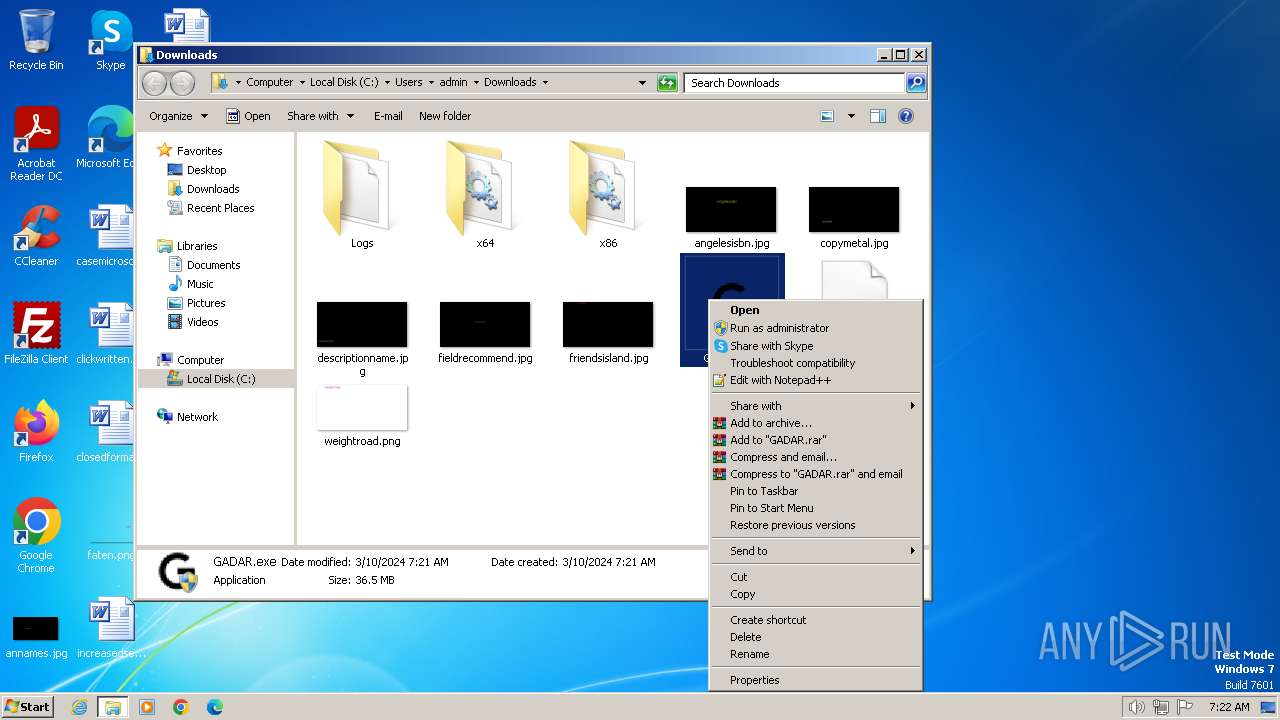
Process checks whether UAC notifications are on
- GADAR.exe (PID: 2736)
- GADAR.exe (PID: 560)
- GADAR.exe (PID: 2064)
- GADAR.exe (PID: 1832)
- GADAR.exe (PID: 2508)
- GADAR.exe (PID: 2728)
- GADAR.exe (PID: 3376)
- GADAR.exe (PID: 3068)
- GADAR.exe (PID: 968)
- GADAR.exe (PID: 2244)
- GADAR.exe (PID: 984)
- GADAR.exe (PID: 4000)
- GADAR.exe (PID: 2548)
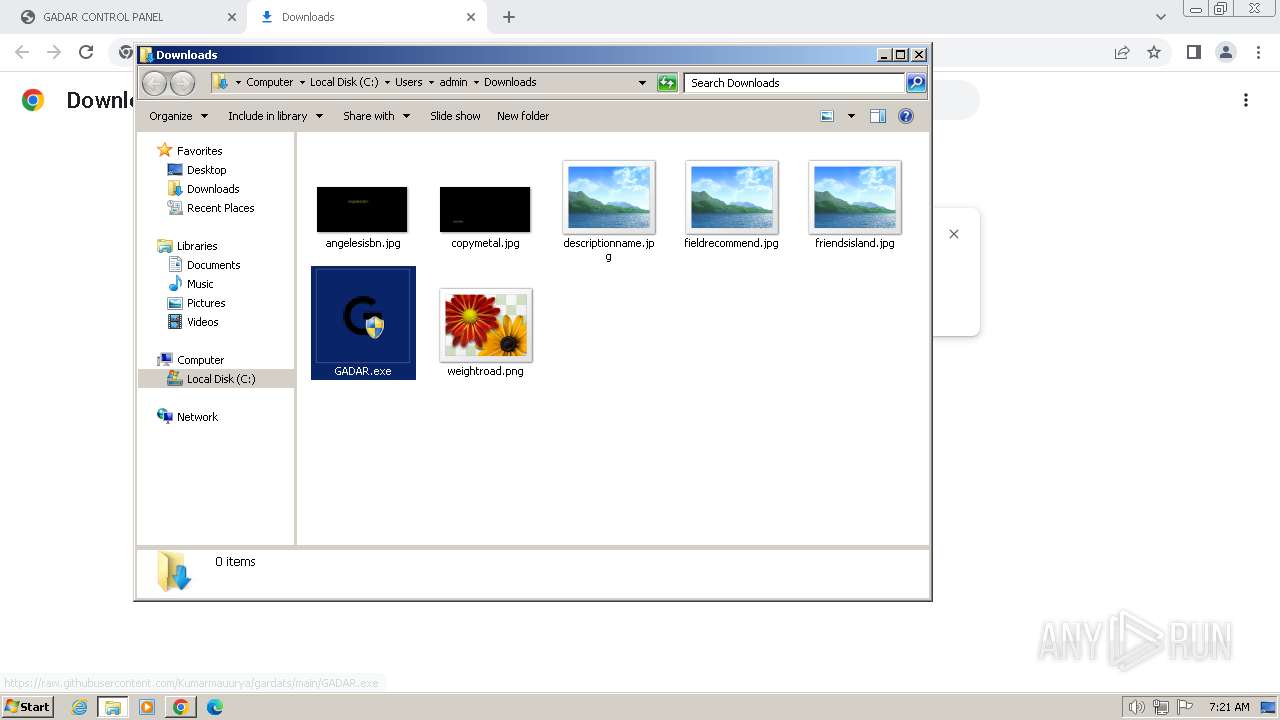
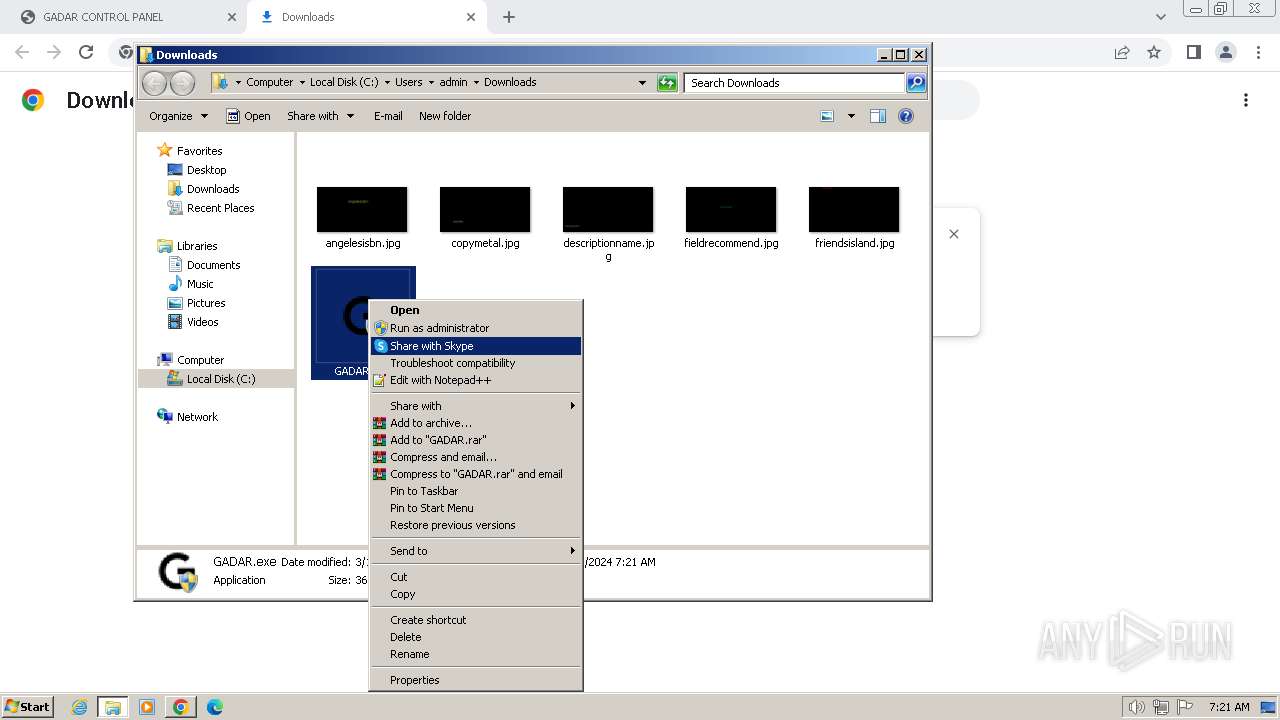
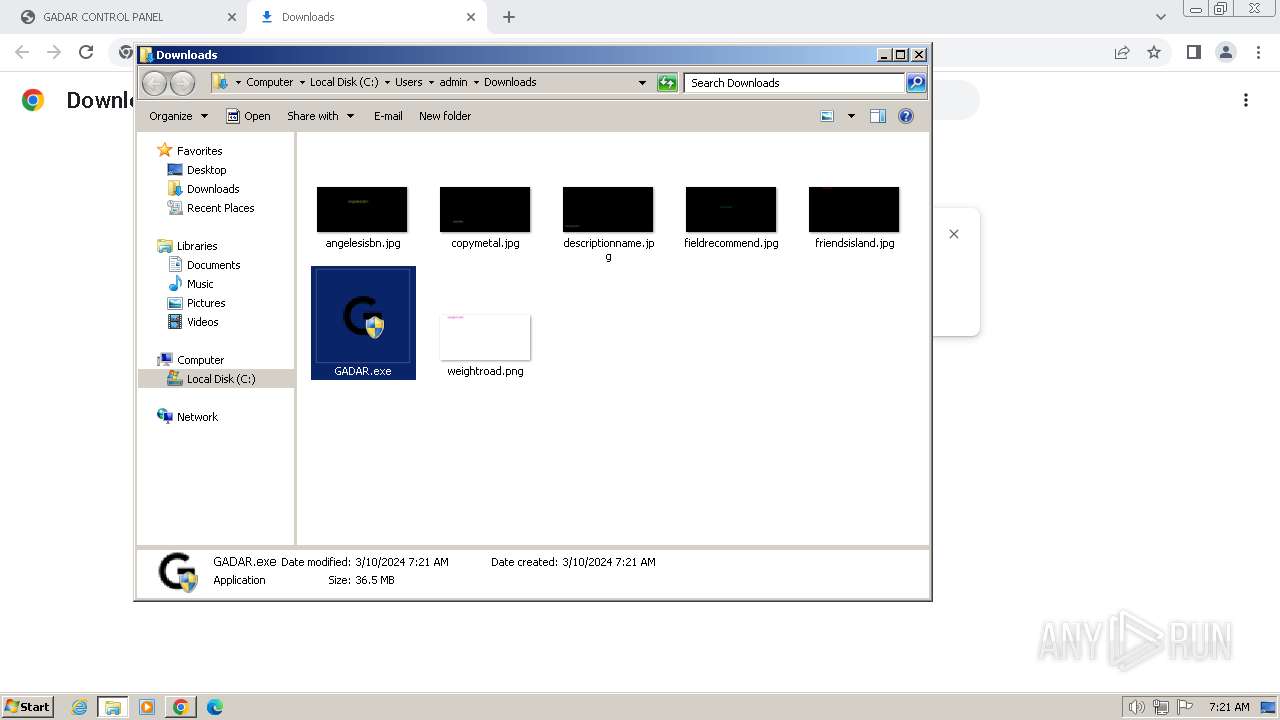
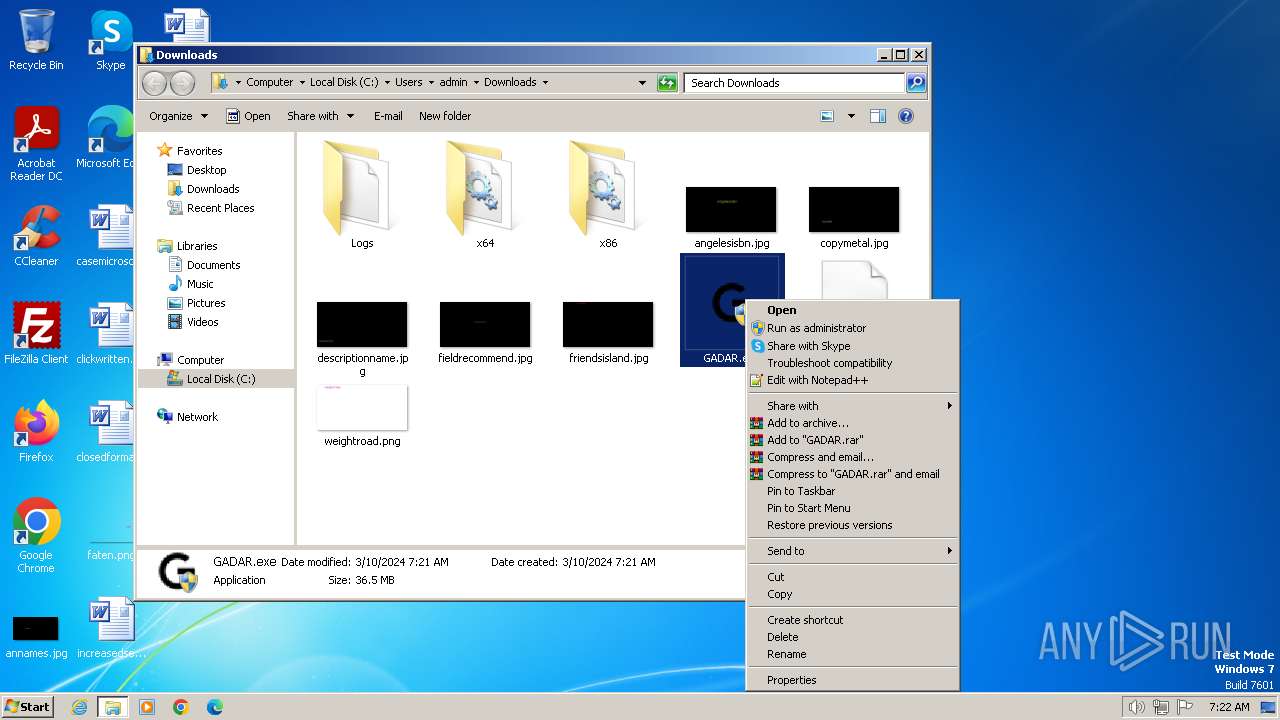
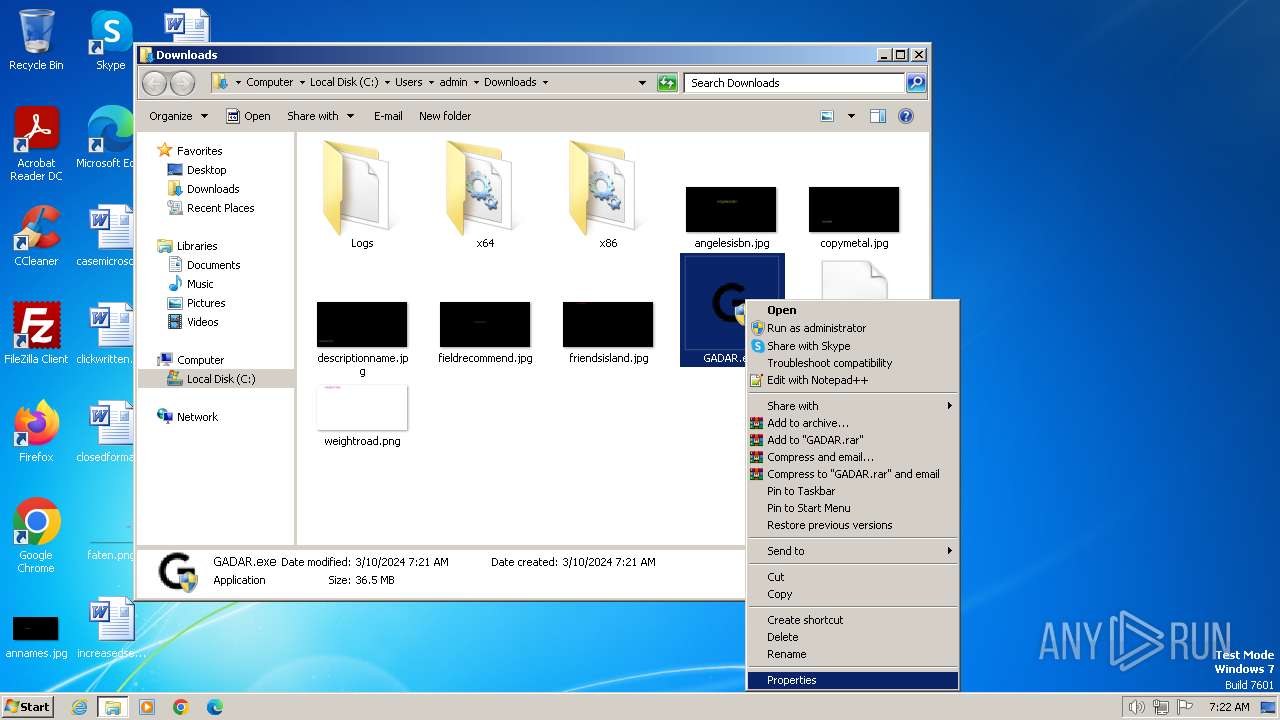
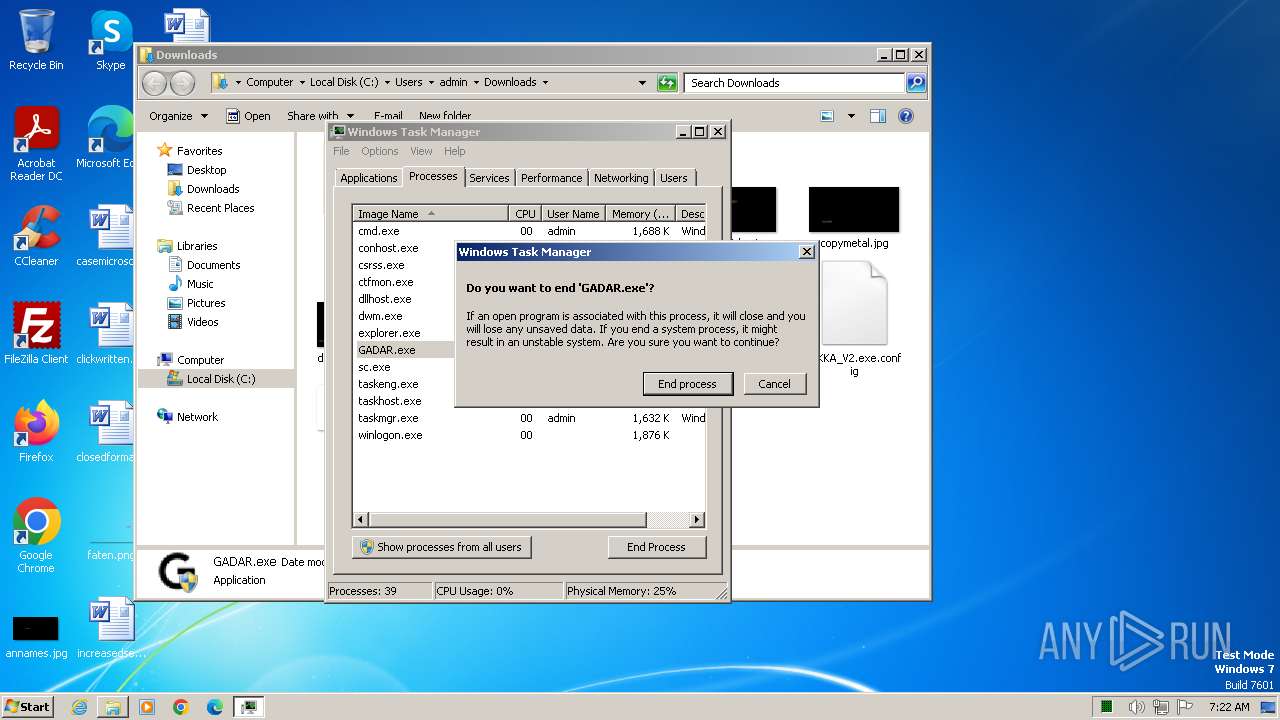
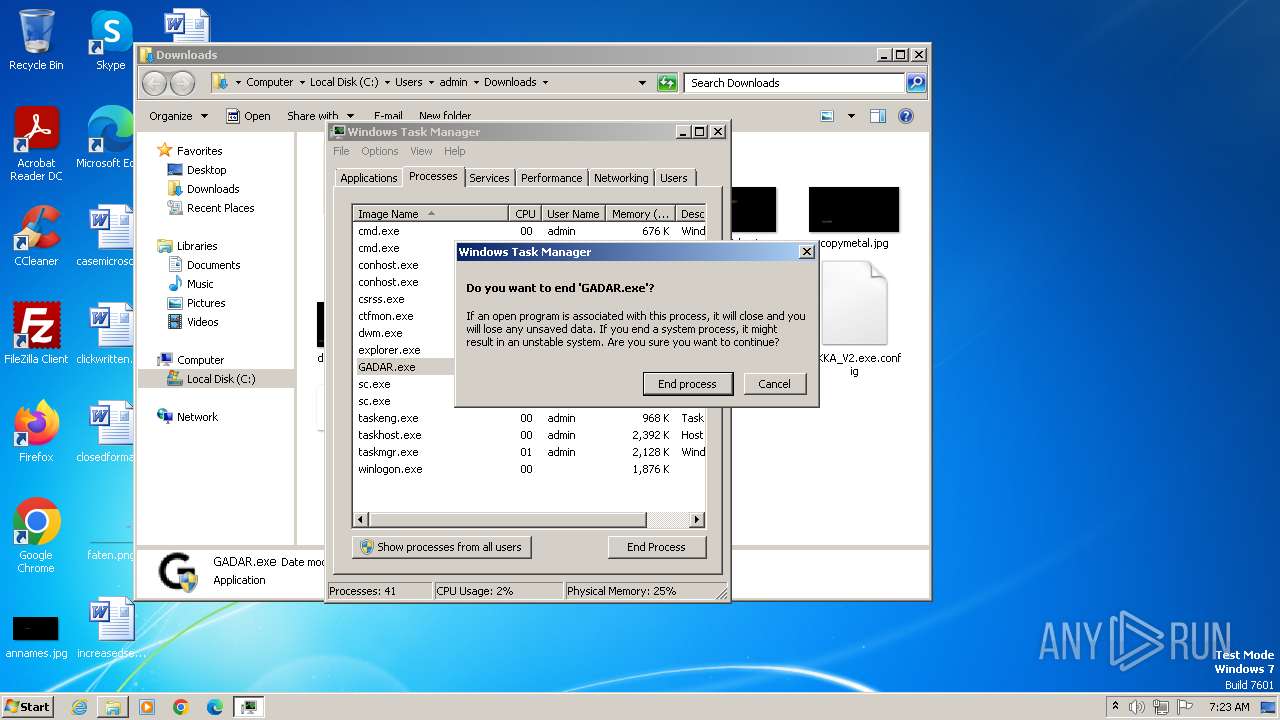
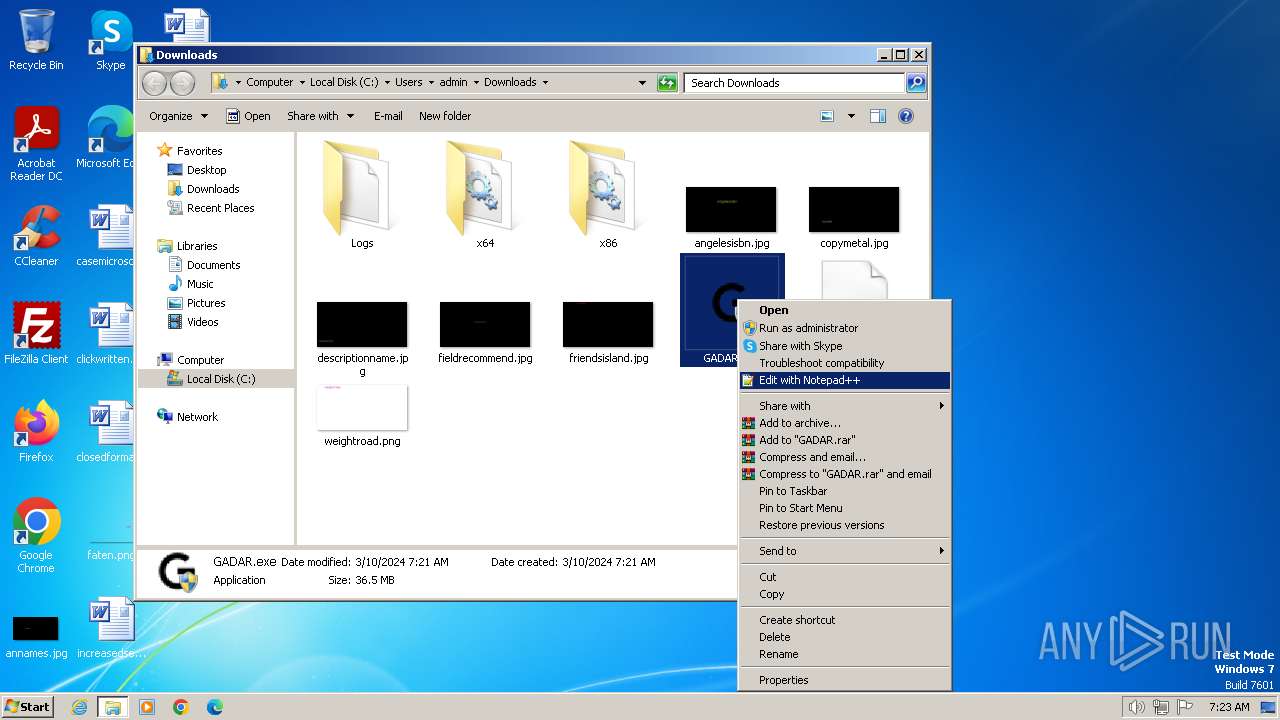
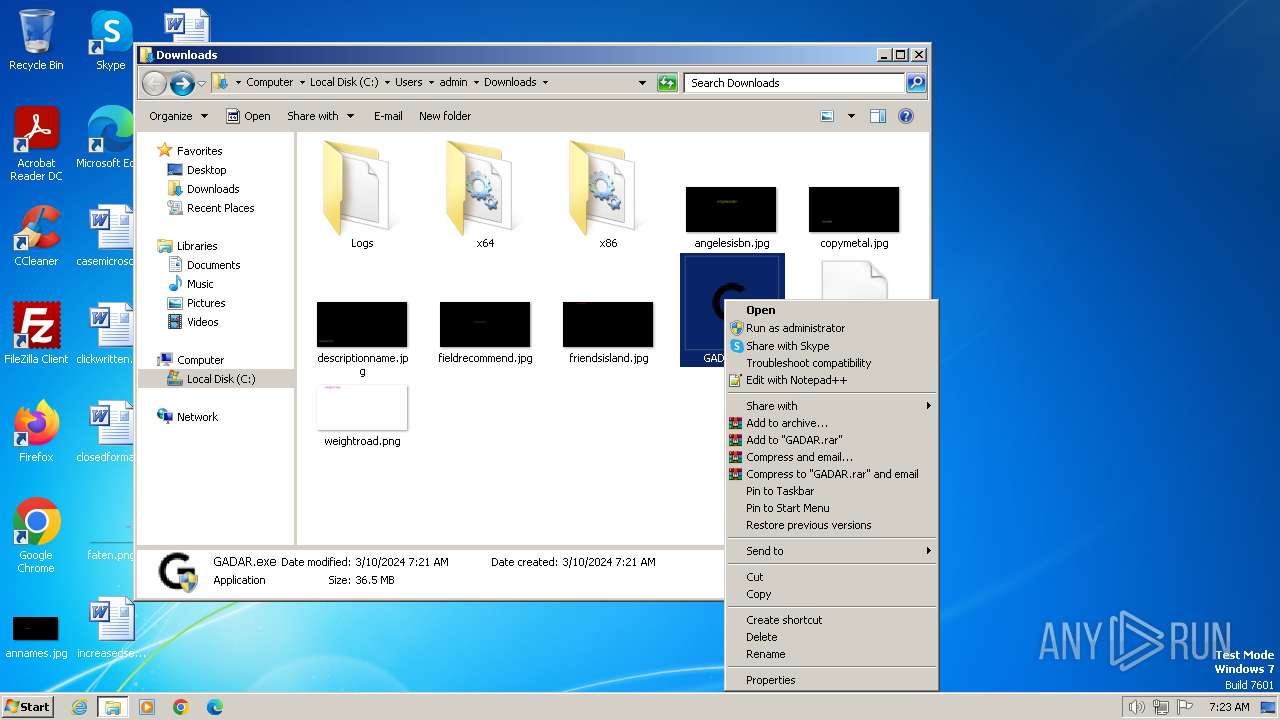
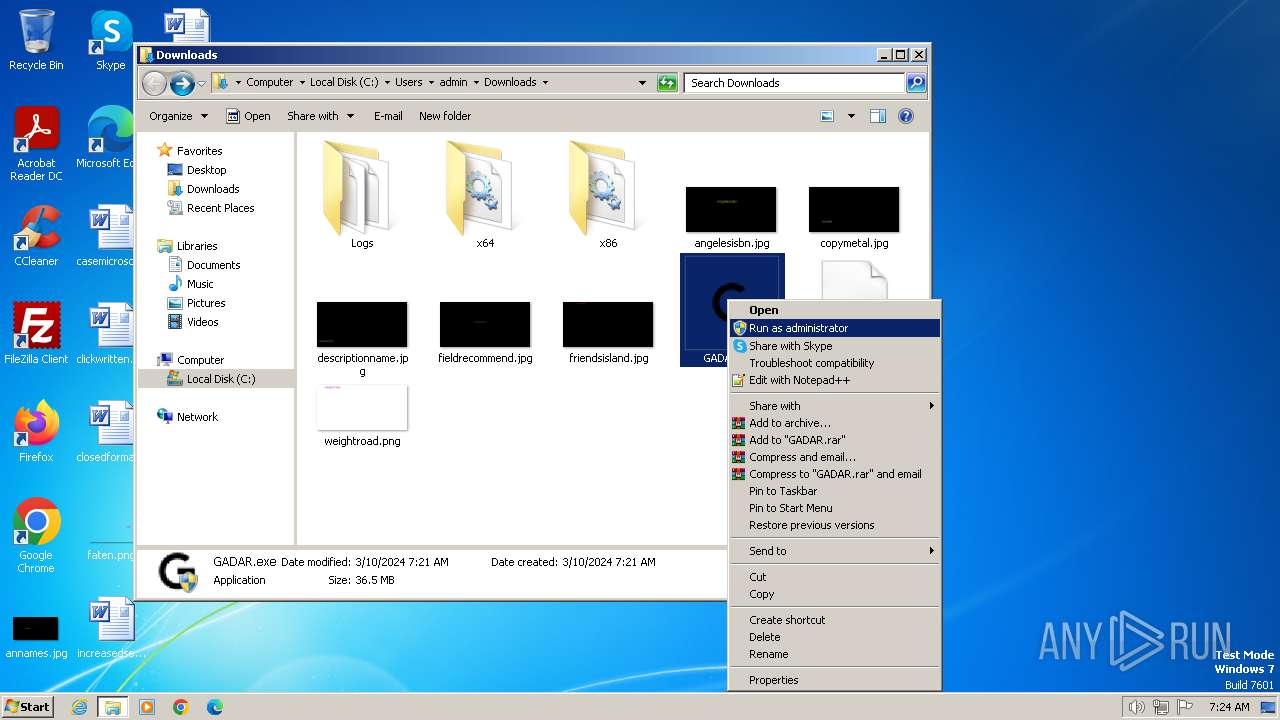
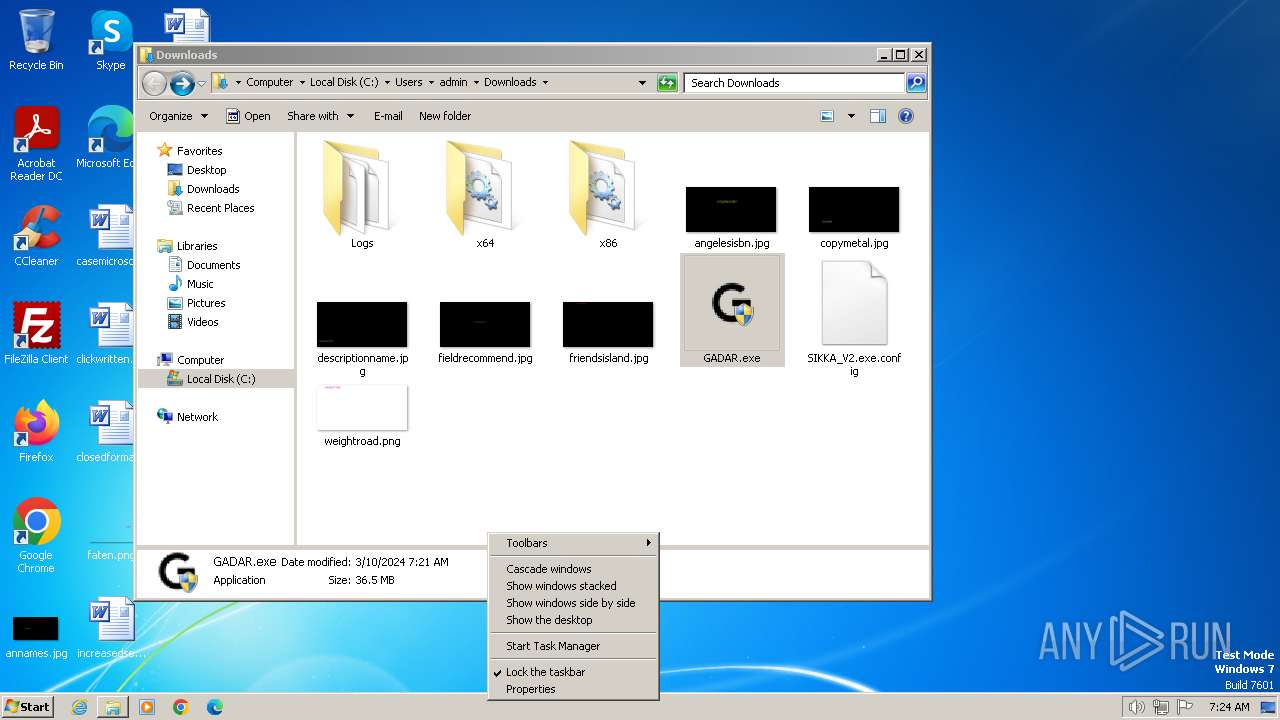
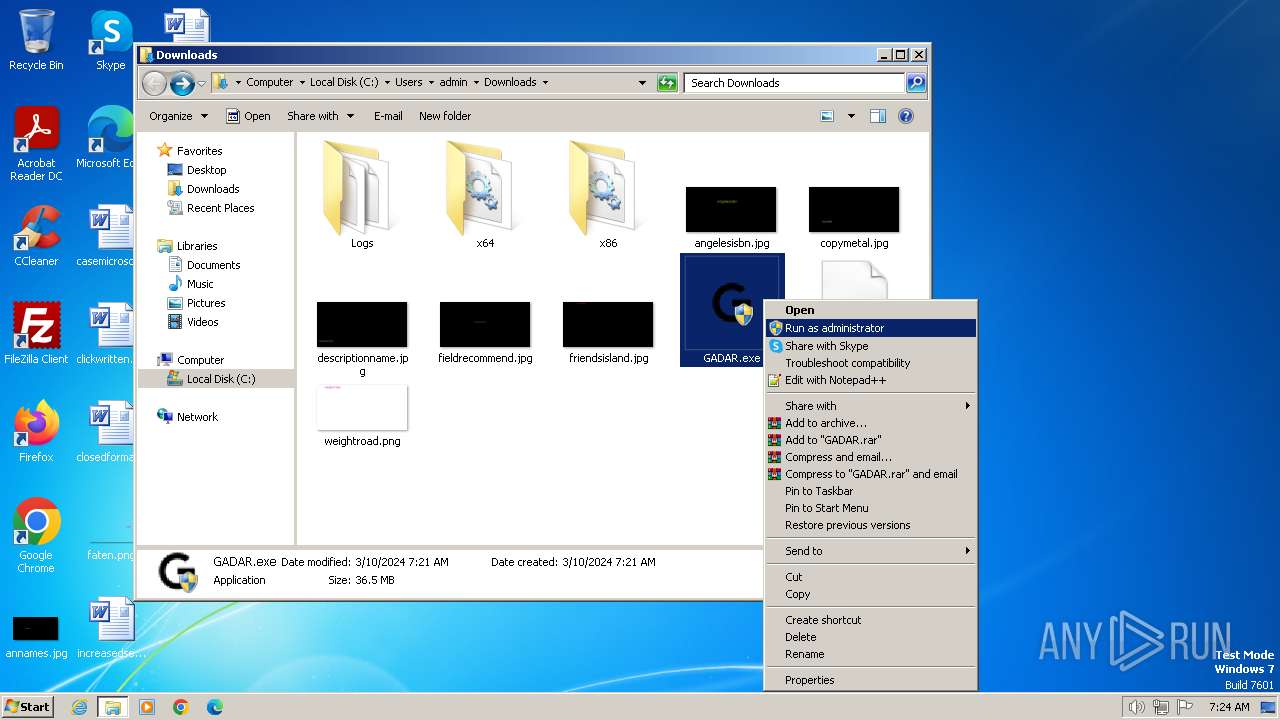
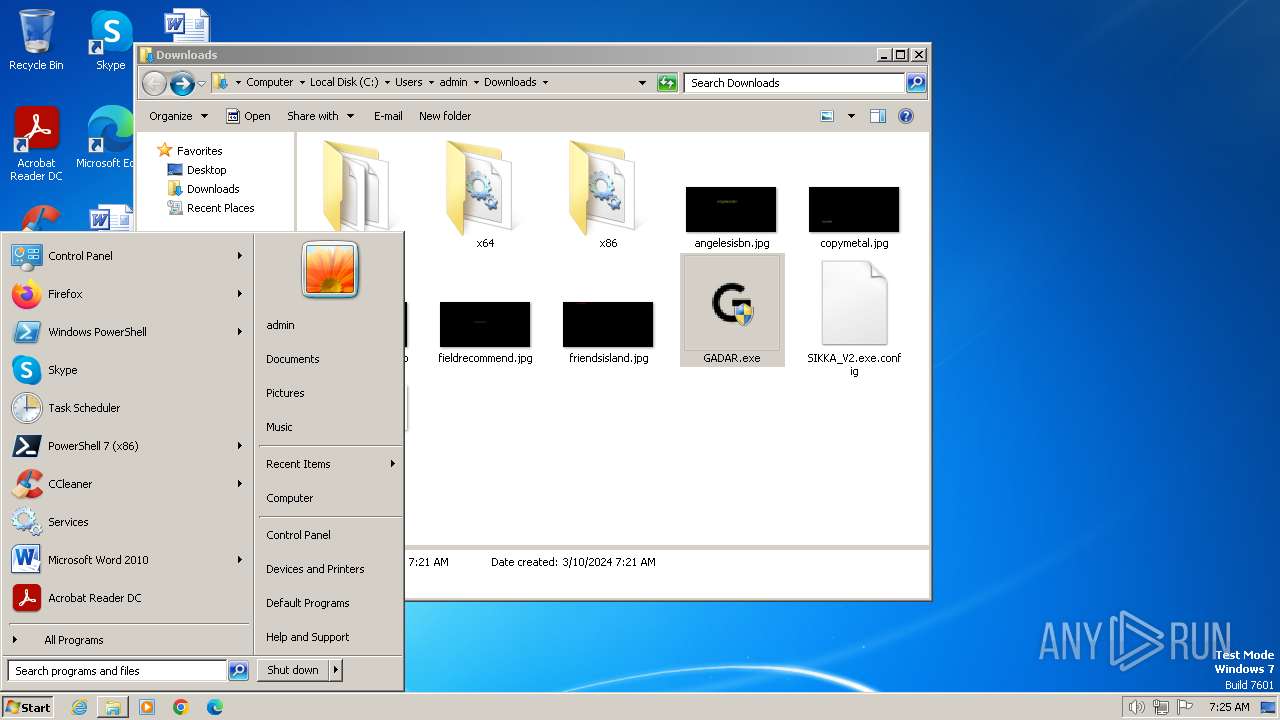
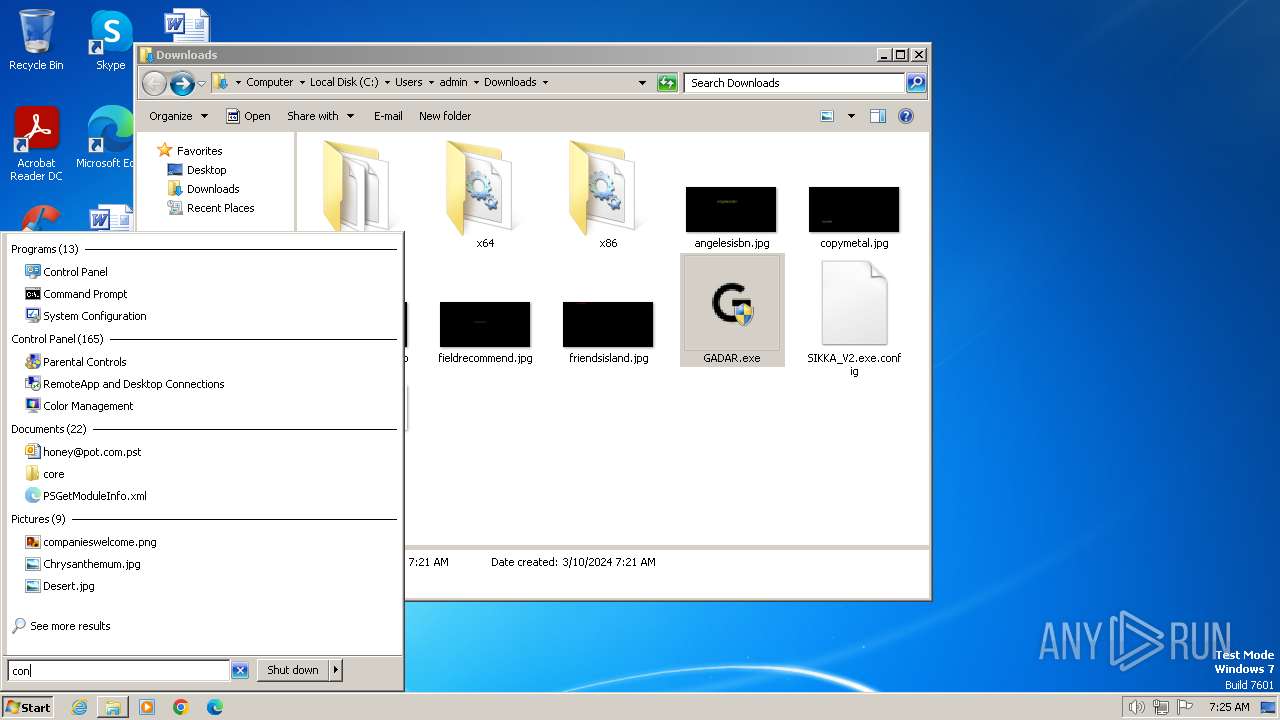
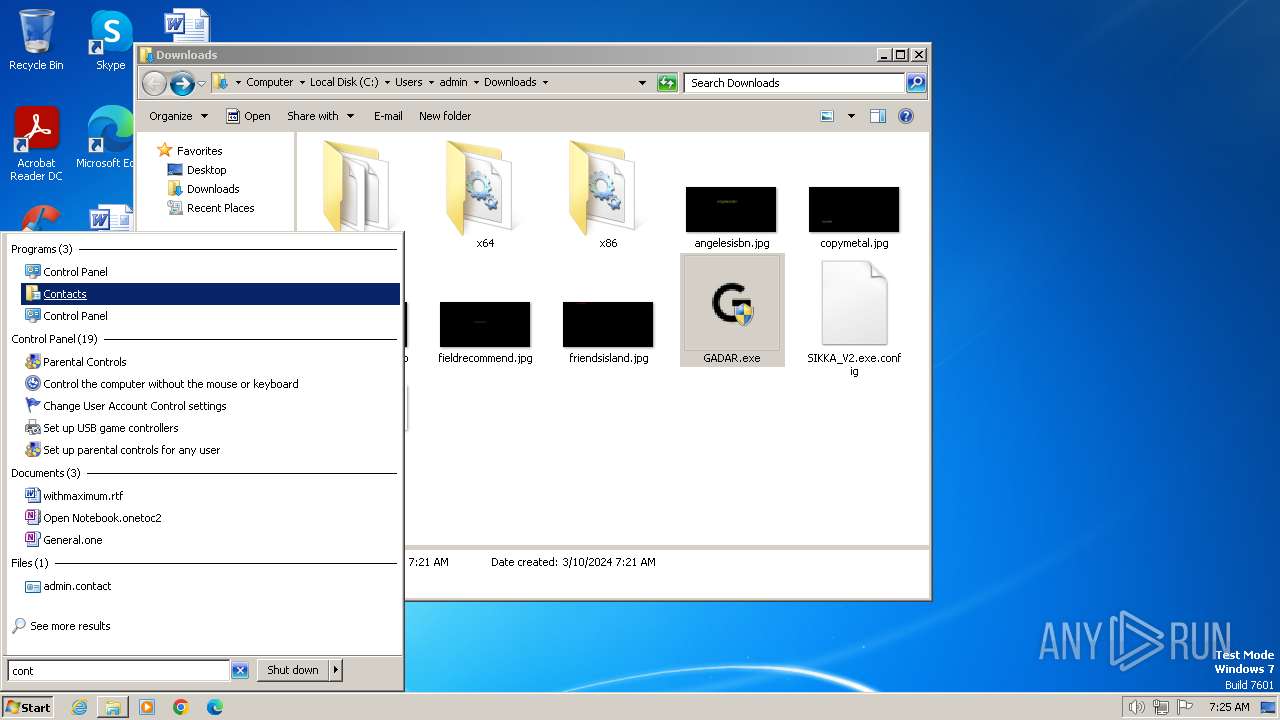
Manual execution by a user
- GADAR.exe (PID: 2736)
- GADAR.exe (PID: 560)
- GADAR.exe (PID: 2064)
- taskmgr.exe (PID: 3724)
- GADAR.exe (PID: 1832)
- taskmgr.exe (PID: 1592)
- GADAR.exe (PID: 2728)
- rundll32.exe (PID: 2668)
- GADAR.exe (PID: 2508)
- GADAR.exe (PID: 3376)
- taskmgr.exe (PID: 3576)
- GADAR.exe (PID: 3068)
- GADAR.exe (PID: 968)
- GADAR.exe (PID: 880)
- GADAR.exe (PID: 1740)
- GADAR.exe (PID: 2244)
- GADAR.exe (PID: 1844)
- GADAR.exe (PID: 2152)
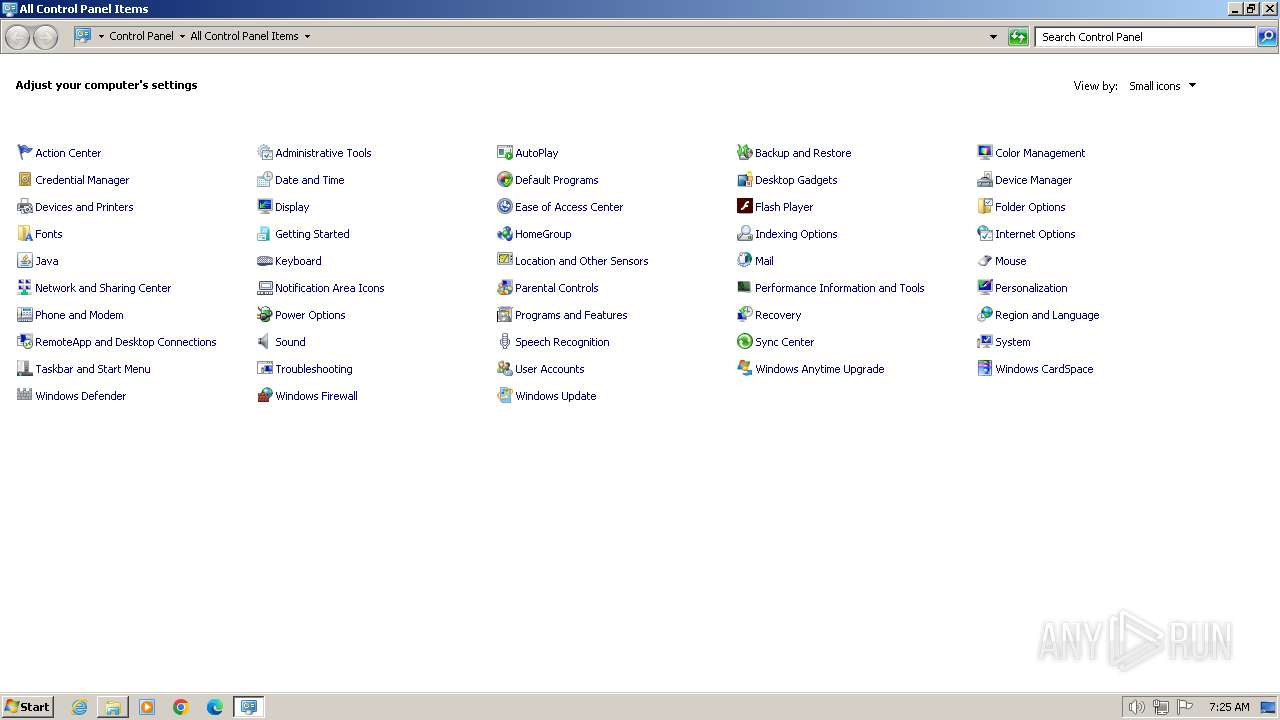
- control.exe (PID: 2956)
- GADAR.exe (PID: 2548)
- GADAR.exe (PID: 984)
- GADAR.exe (PID: 2740)
- GADAR.exe (PID: 4000)
Executable content was dropped or overwritten
- chrome.exe (PID: 3700)
The process uses the downloaded file
- chrome.exe (PID: 992)
Checks proxy server information
- GADAR.exe (PID: 2736)
- GADAR.exe (PID: 560)
- GADAR.exe (PID: 1832)
- GADAR.exe (PID: 2064)
- GADAR.exe (PID: 2508)
- GADAR.exe (PID: 2728)
- GADAR.exe (PID: 3376)
- GADAR.exe (PID: 3068)
- GADAR.exe (PID: 2244)
- GADAR.exe (PID: 968)
- GADAR.exe (PID: 984)
- GADAR.exe (PID: 2548)
- GADAR.exe (PID: 4000)
Reads Environment values
- GADAR.exe (PID: 2736)
- GADAR.exe (PID: 1832)
- GADAR.exe (PID: 2508)
- GADAR.exe (PID: 3068)
Reads the machine GUID from the registry
- GADAR.exe (PID: 2736)
- GADAR.exe (PID: 560)
- GADAR.exe (PID: 2064)
- GADAR.exe (PID: 1832)
- GADAR.exe (PID: 2508)
- GADAR.exe (PID: 2728)
- GADAR.exe (PID: 3376)
- GADAR.exe (PID: 3068)
- GADAR.exe (PID: 2244)
- GADAR.exe (PID: 968)
- GADAR.exe (PID: 984)
- GADAR.exe (PID: 2548)
- GADAR.exe (PID: 4000)
Reads the software policy settings
- GADAR.exe (PID: 1832)
- GADAR.exe (PID: 2508)
- GADAR.exe (PID: 3068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
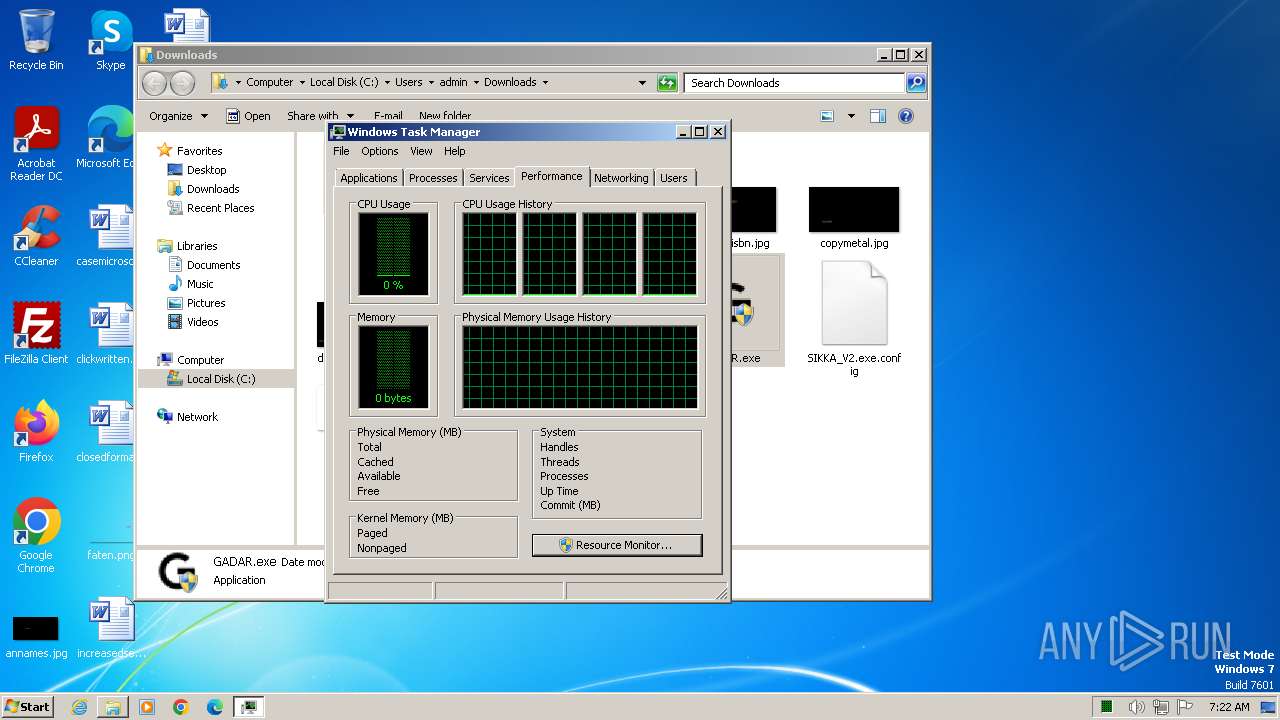
Total processes
141
Monitored processes
49
Malicious processes
13
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
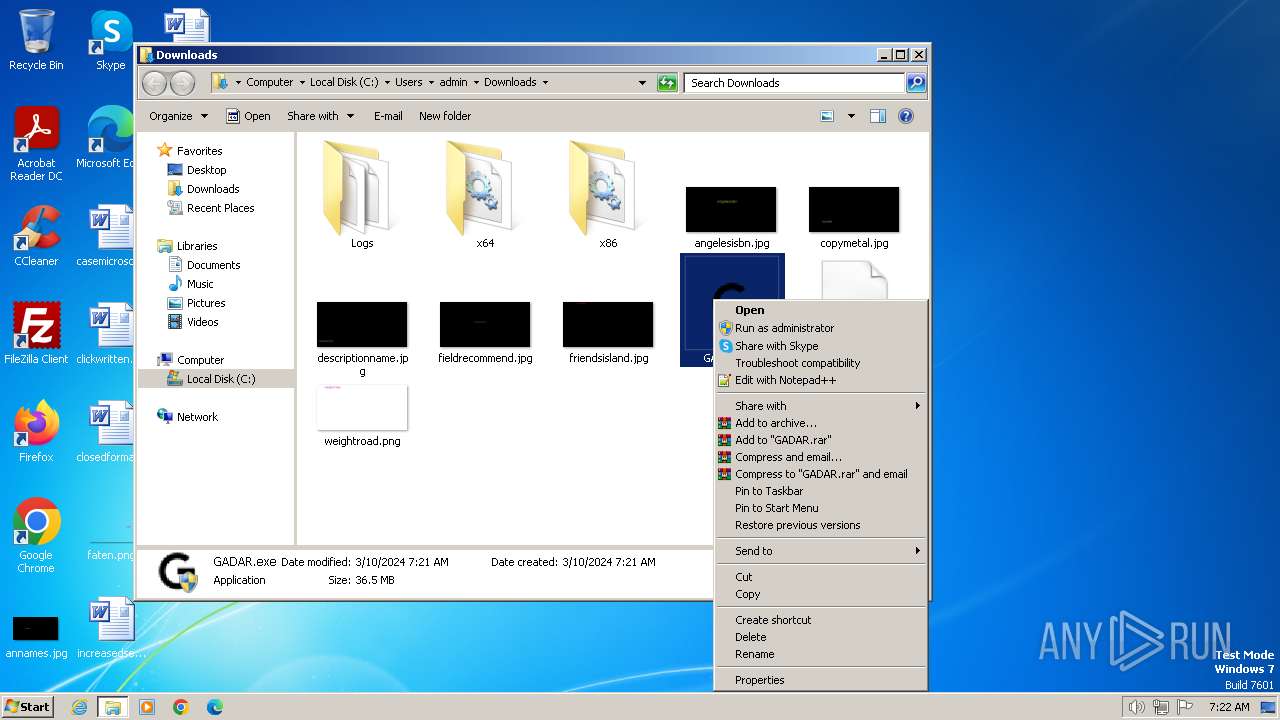
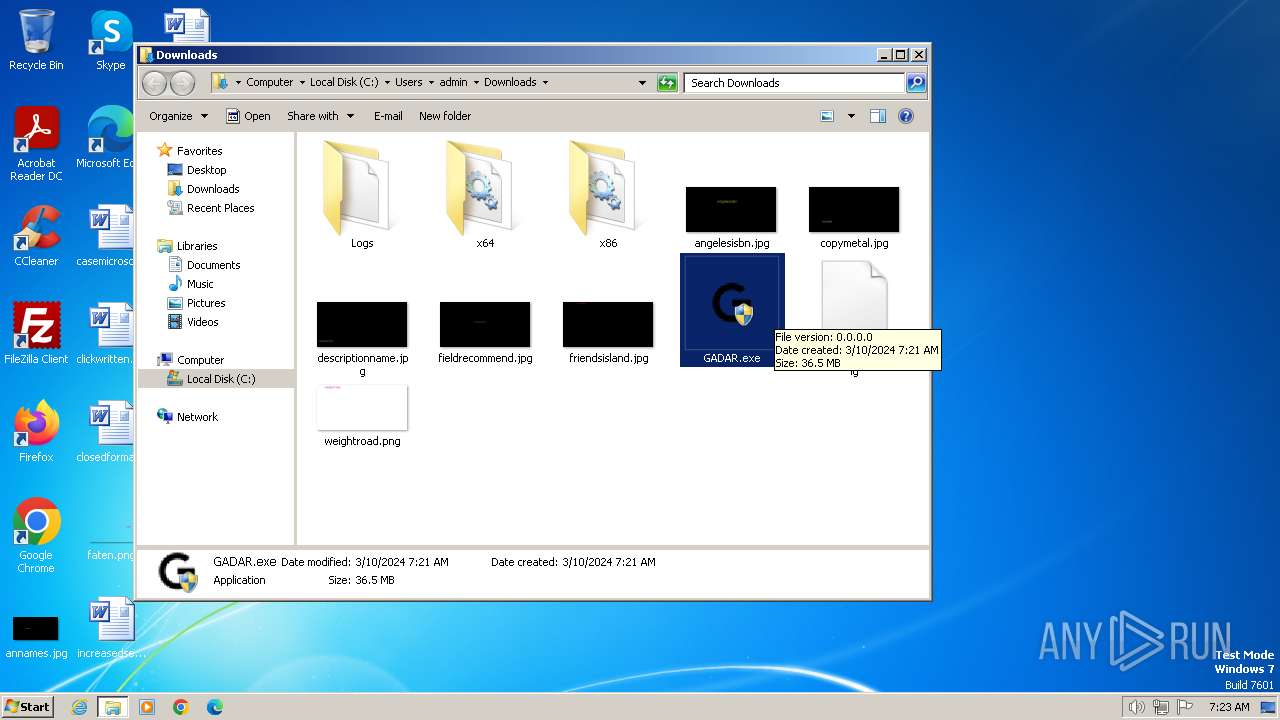
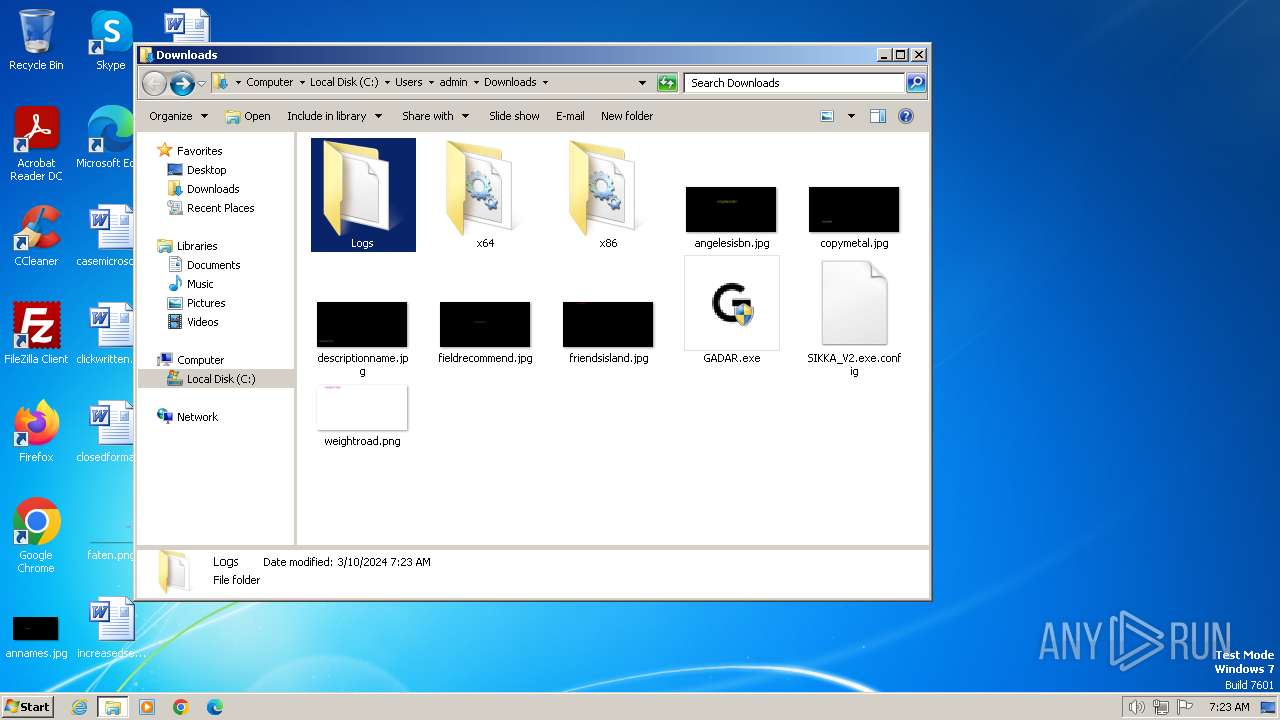
| 560 | "C:\Users\admin\Downloads\GADAR.exe" | C:\Users\admin\Downloads\GADAR.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 844 | "cmd.exe" | C:\Windows\System32\cmd.exe | — | GADAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 880 | "C:\Users\admin\Downloads\GADAR.exe" | C:\Users\admin\Downloads\GADAR.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 3221226540 Version: 0.0.0.0 Modules
| |||||||||||||||
| 920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3716 --field-trial-handle=1180,i,15158571087109355954,2540731932785975767,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 968 | "C:\Users\admin\Downloads\GADAR.exe" | C:\Users\admin\Downloads\GADAR.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 984 | "C:\Users\admin\Downloads\GADAR.exe" | C:\Users\admin\Downloads\GADAR.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=956 --field-trial-handle=1180,i,15158571087109355954,2540731932785975767,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1516 --field-trial-handle=1180,i,15158571087109355954,2540731932785975767,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1324 --field-trial-handle=1180,i,15158571087109355954,2540731932785975767,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1592 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\System32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
34 320
Read events
34 166
Write events
144
Delete events
10
Modification events
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
53
Suspicious files
35
Text files
58
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF17fa5d.TMP | — | |
MD5:— | SHA256:— | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF17fa6d.TMP | text | |
MD5:05CF4C3C5148DA6355D3561A9EAA5E8A | SHA256:8D720243F6876898E4F197C8867C4CEE69F1C7335C55B8A29C120B1028D93E41 | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:65239F35CB63C76EA1F59EF64F7AAFF4 | SHA256:252EF82CC03FDE4BEF13CF81CD1AC5CE45854212D1A7359035E7A5D6BEDBE229 | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF17ffcc.TMP | — | |
MD5:— | SHA256:— | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | text | |
MD5:4E2B7997F4C3647F8D1ADA88339BBBA5 | SHA256:C33226C460208AA10537A23CB5128FD887DCBAA335C7DC8BFFBE08A607CCFDF5 | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RF180e05.TMP | — | |
MD5:— | SHA256:— | |||
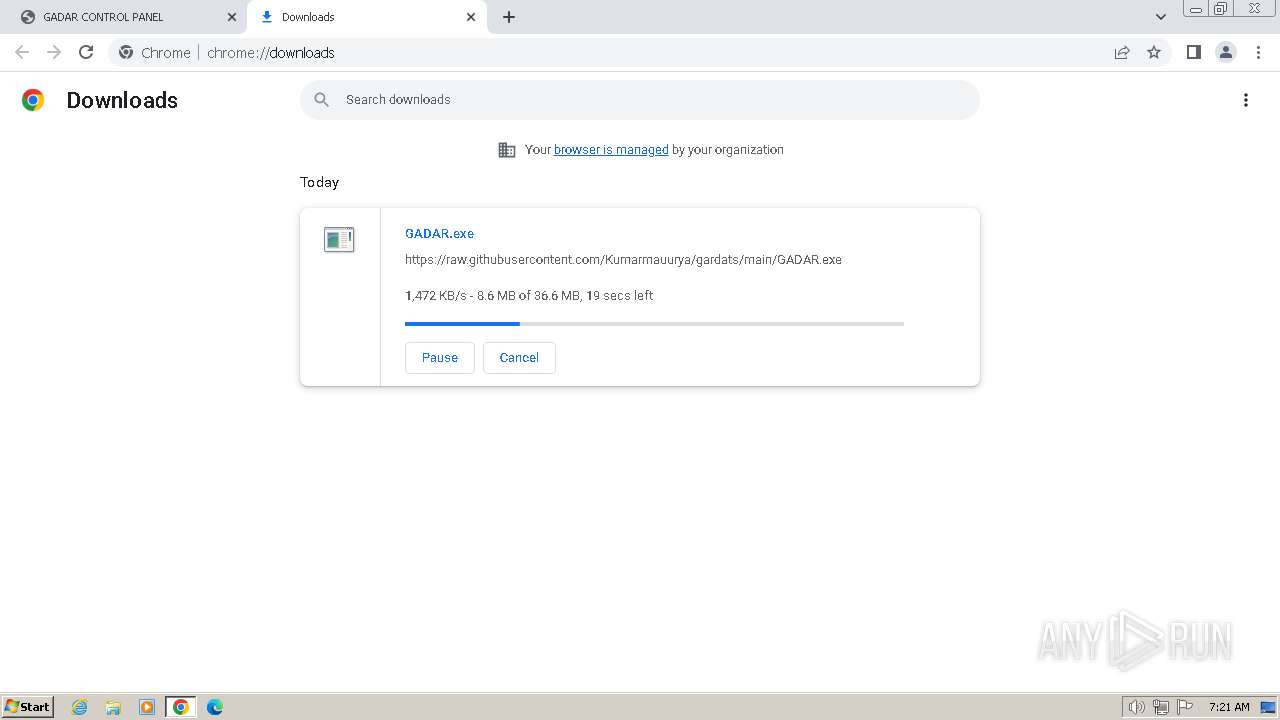
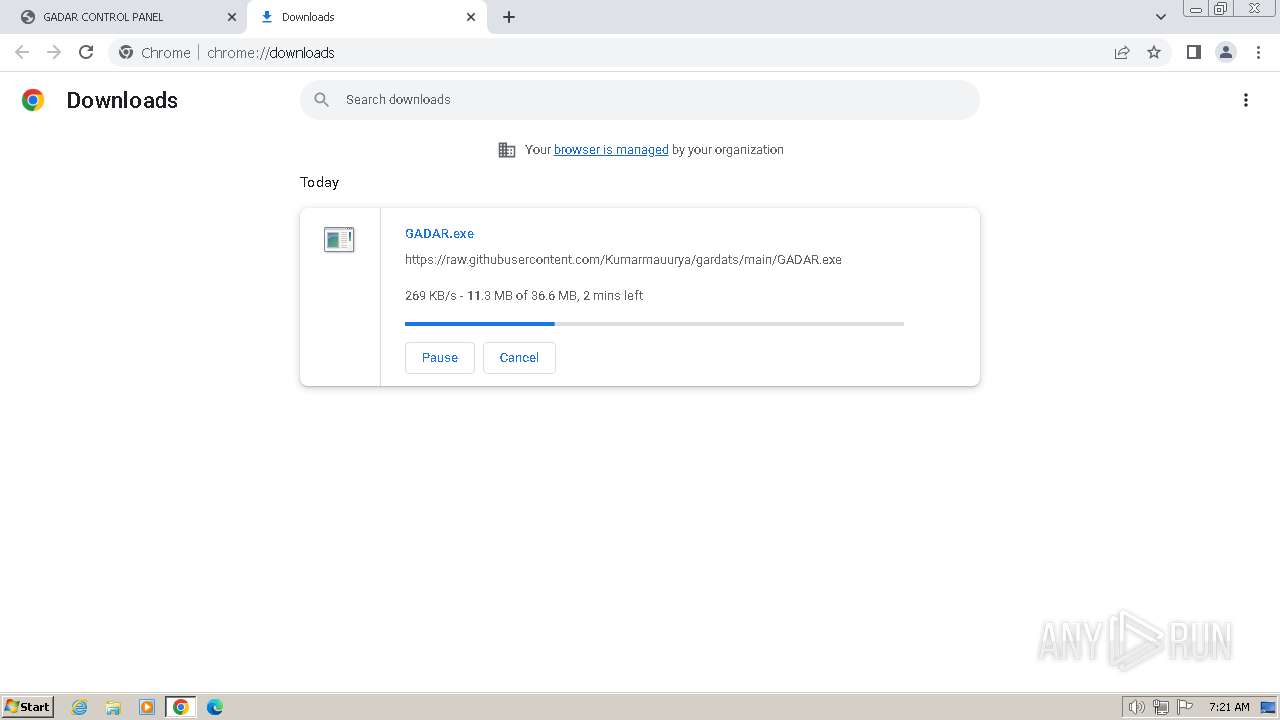
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
21
DNS requests
29
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
3460 | chrome.exe | 108.177.15.84:443 | accounts.google.com | GOOGLE | US | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3700 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
3460 | chrome.exe | 104.21.9.60:443 | gadarts.com | CLOUDFLARENET | — | unknown |
3460 | chrome.exe | 142.250.185.202:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
3460 | chrome.exe | 142.250.186.163:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
3460 | chrome.exe | 35.190.80.1:443 | a.nel.cloudflare.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
gadarts.com |
| unknown |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
a.nel.cloudflare.com |
| whitelisted |
www.google.com |
| whitelisted |
raw.githubusercontent.com |
| shared |
www.googleapis.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
GADAR.exe | FTH: (3376): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
GADAR.exe | FTH: (3068): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
GADAR.exe | FTH: (968): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
GADAR.exe | FTH: (2244): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
GADAR.exe | FTH: (984): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
GADAR.exe | FTH: (2548): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
GADAR.exe | FTH: (4000): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|