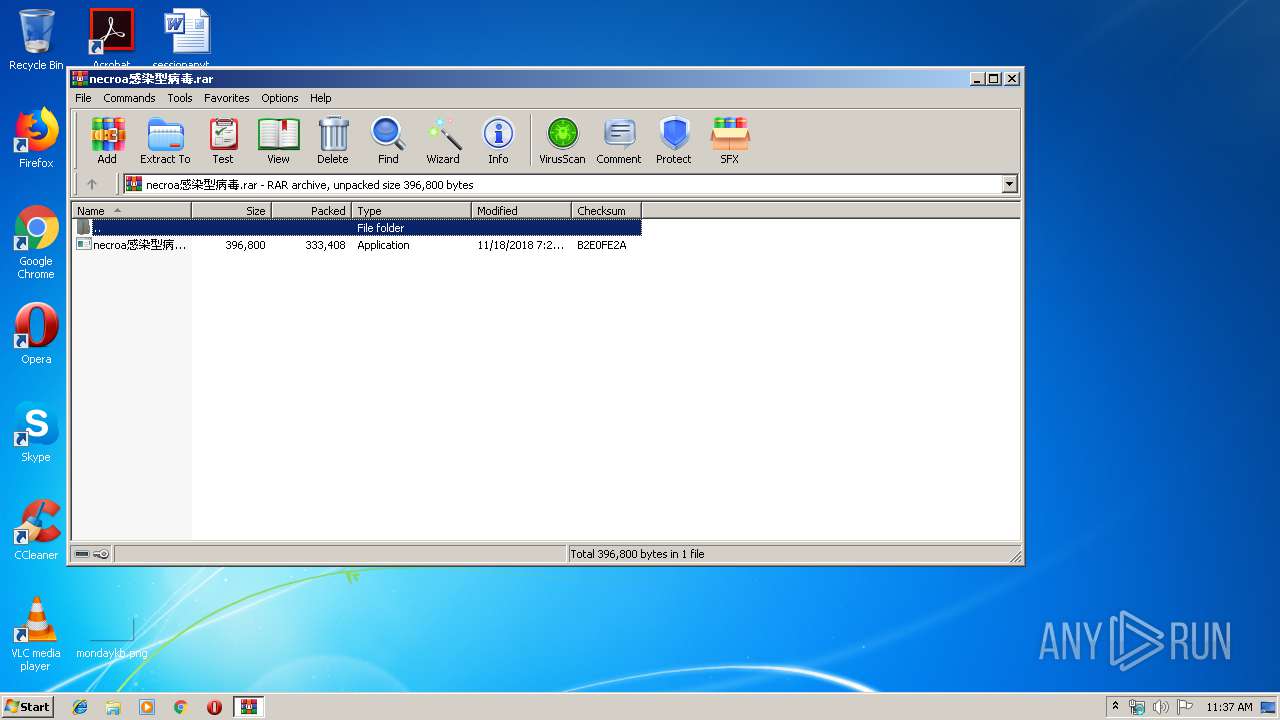
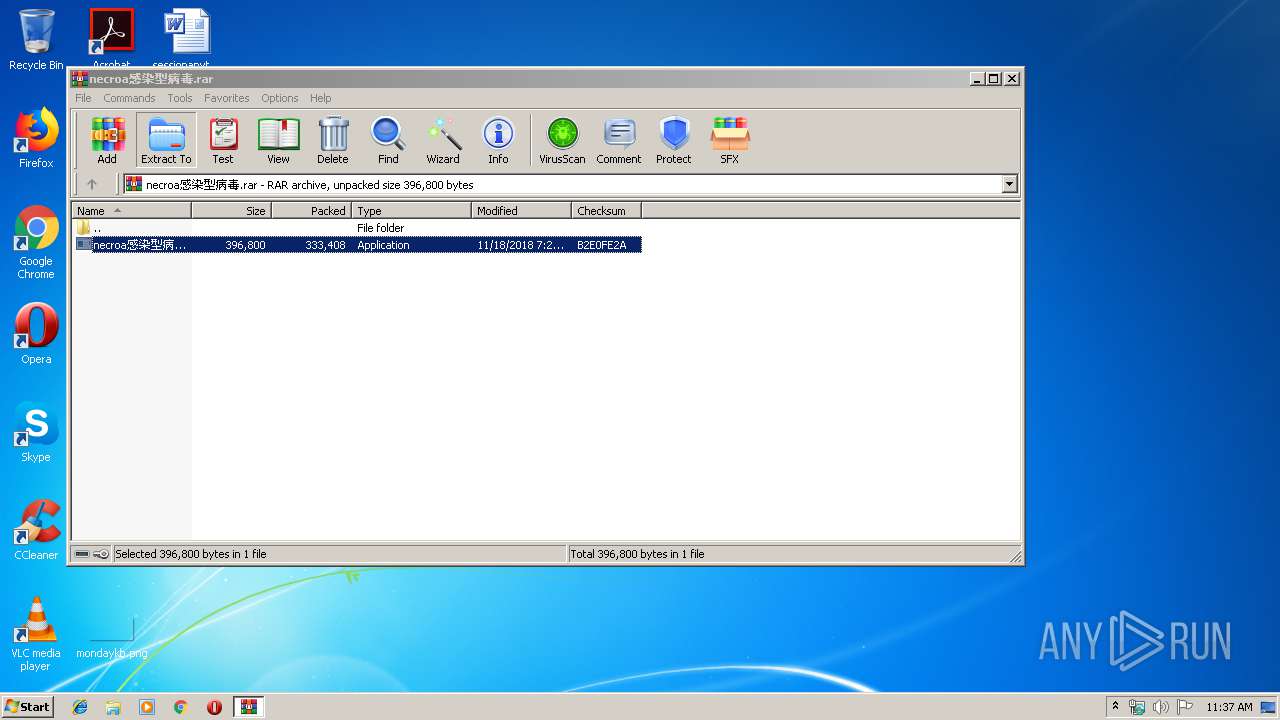
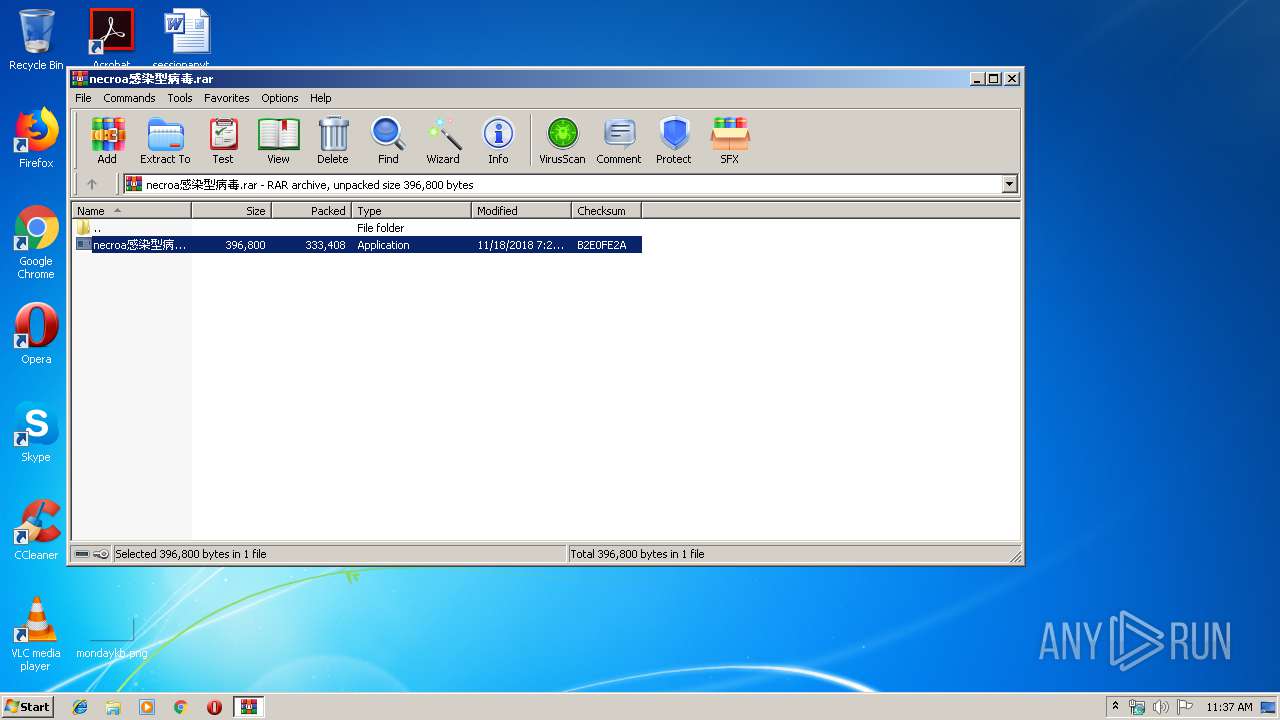
| File name: | necroa感染型病毒.rar |
| Full analysis: | https://app.any.run/tasks/705b1670-2d73-4bbe-bed8-829b2b6e40b7 |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 10:37:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 37B705C2B628CE6008CAC1D01125D4D8 |
| SHA1: | 89243D34A2B32C802431EEA2AD273D8BA3AD1696 |
| SHA256: | EA425F0499137D848FEBC53FB6925BFFC929DC819530E8D3853BA1184A44B464 |
| SSDEEP: | 6144:G+cn+FuKzLDDYJOlS2+Cfkj5ME1Jggl6q4hW8BrPob+Xory:G+c+AALDDlSXjK6ggl5SrPob+ |
MALICIOUS
Starts NET.EXE for service management
- cmd.exe (PID: 2328)
Application was dropped or rewritten from another process
- necroa感染型病毒.exe (PID: 3760)
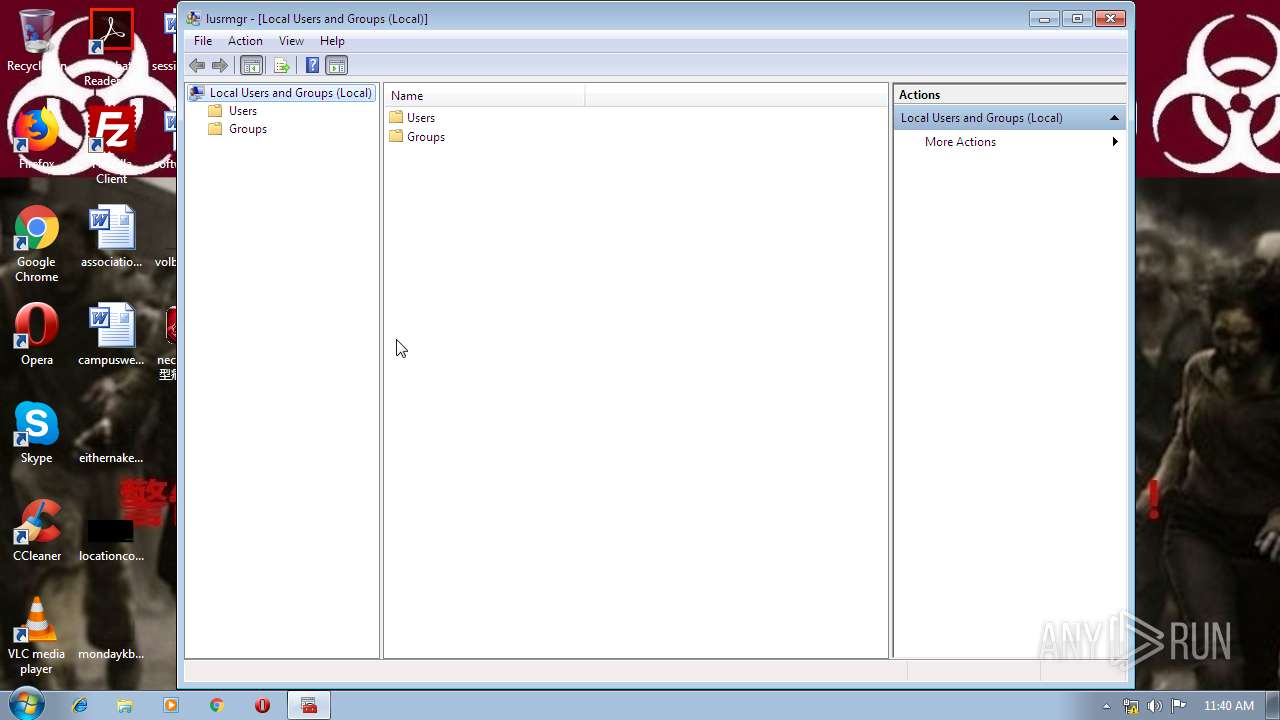
Starts NET.EXE to view/change users group
- cmd.exe (PID: 2328)
Changes the autorun value in the registry
- regedit.exe (PID: 2348)
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 2328)
SUSPICIOUS
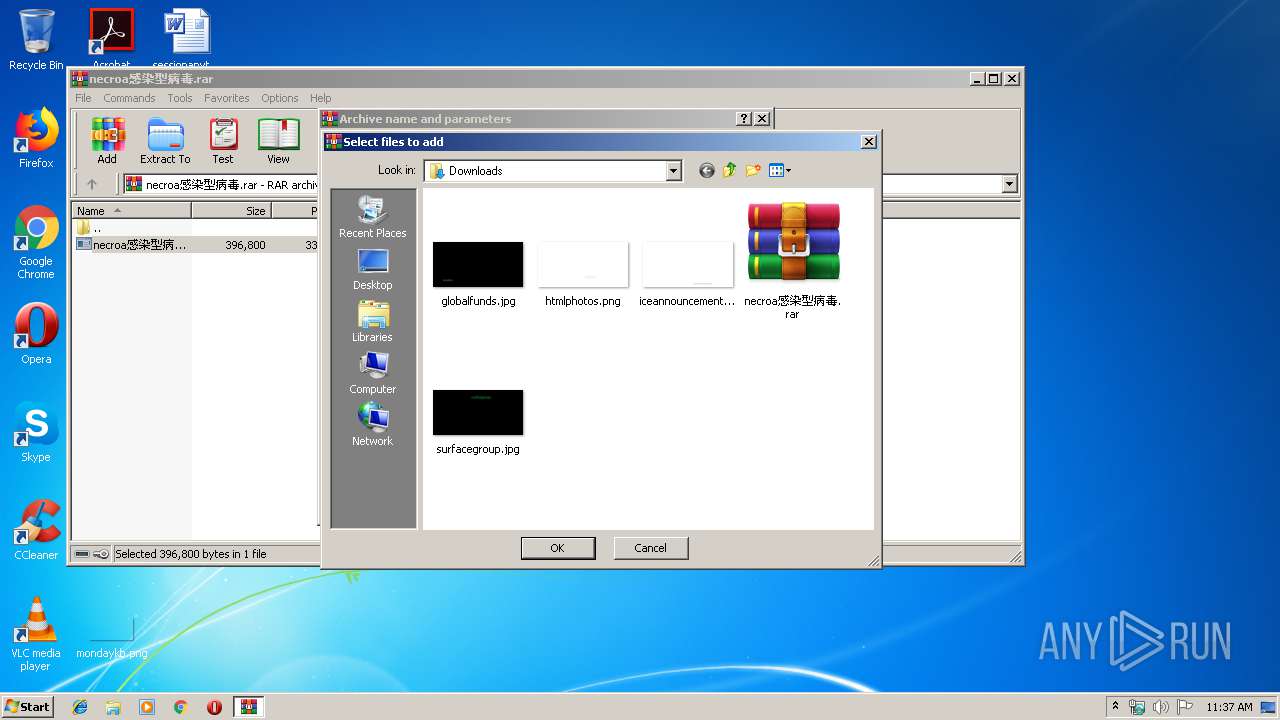
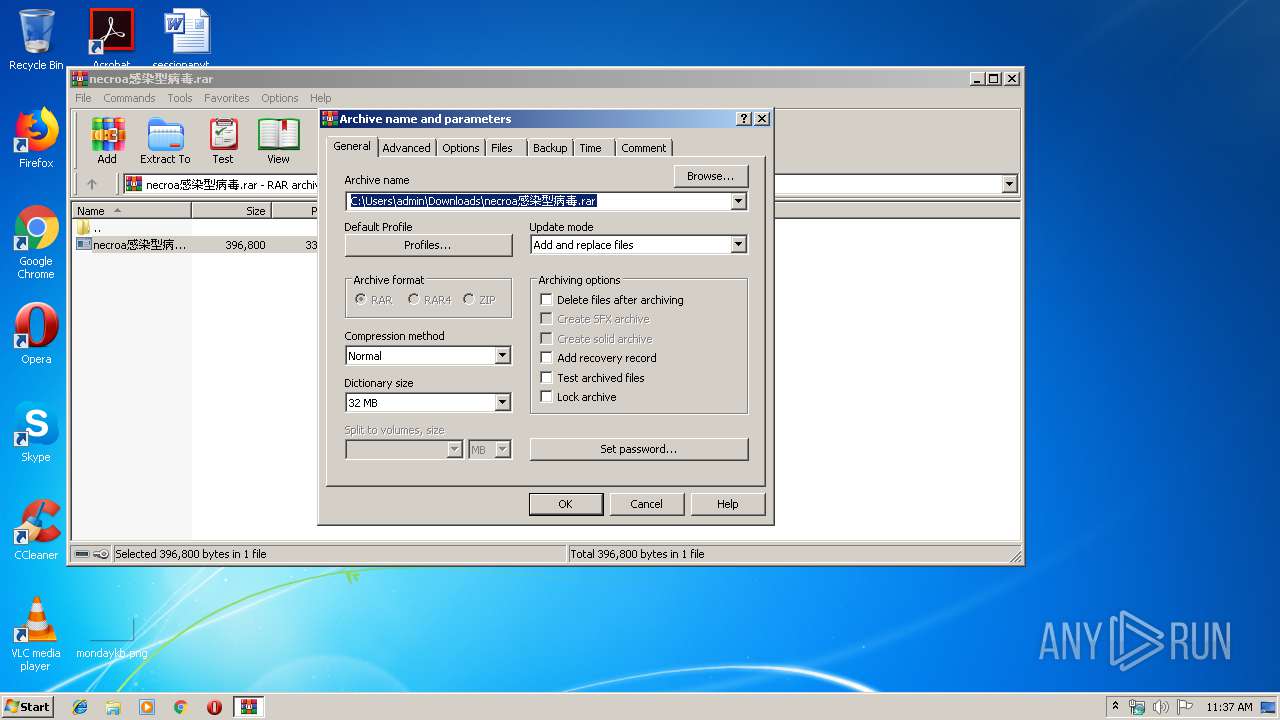
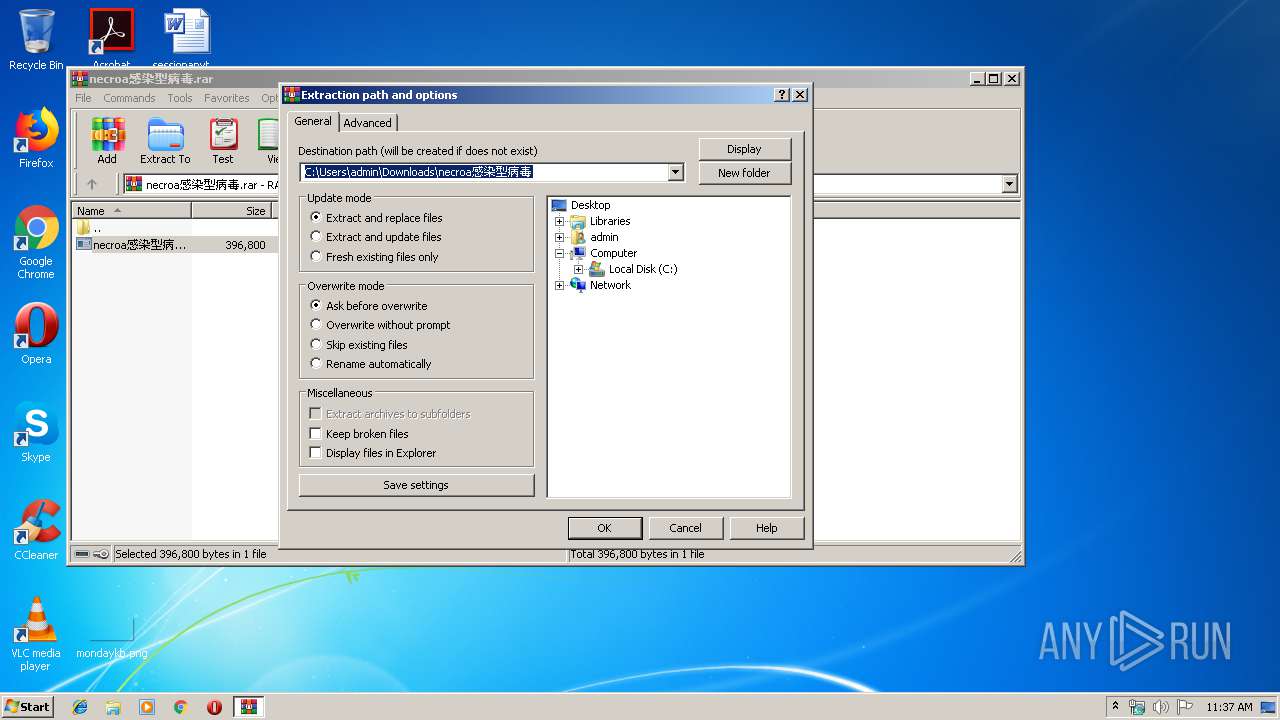
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3516)
- cmd.exe (PID: 2328)
Starts CMD.EXE for commands execution
- necroa感染型病毒.exe (PID: 3760)
Starts SC.EXE for service management
- cmd.exe (PID: 2328)
Creates files in the Windows directory
- cmd.exe (PID: 2328)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 2328)
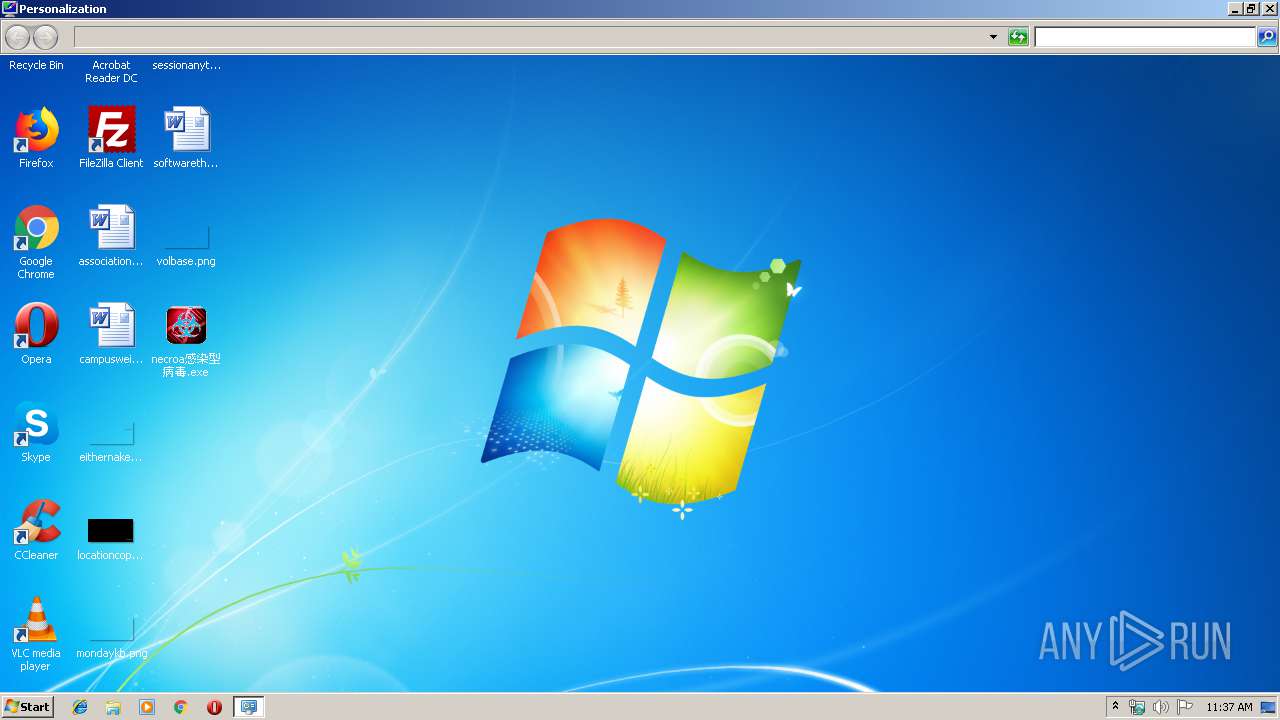
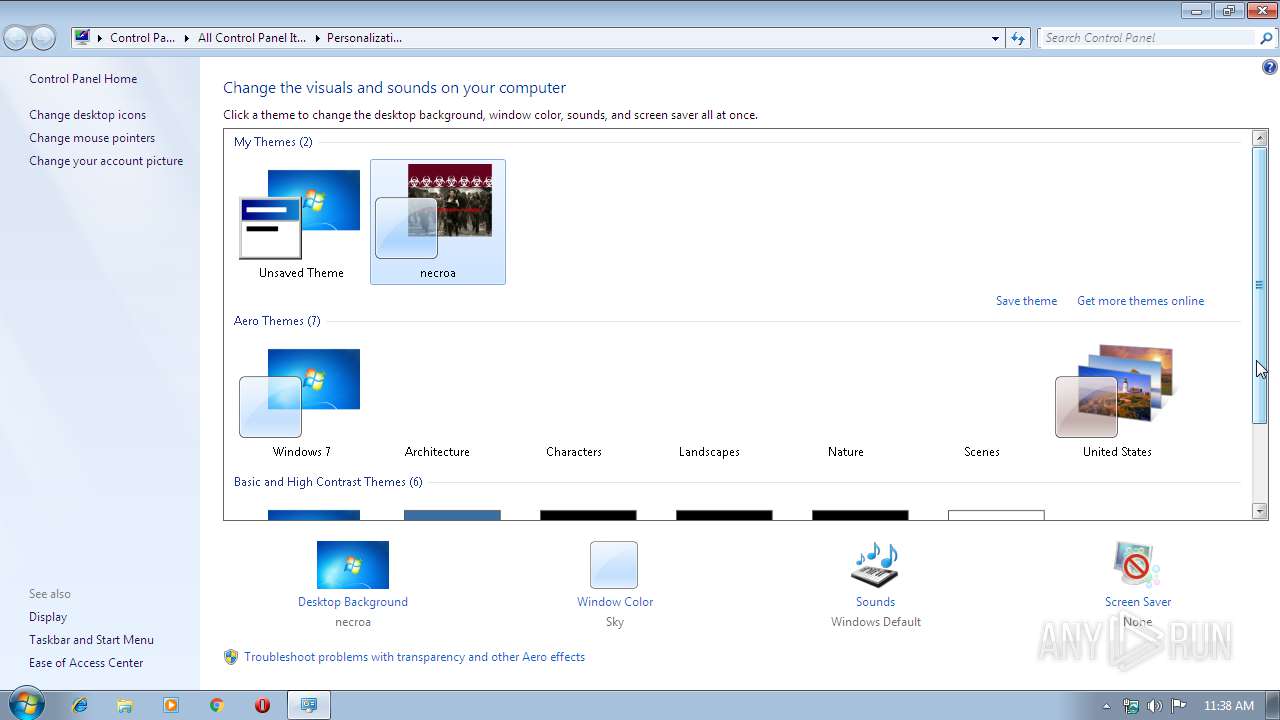
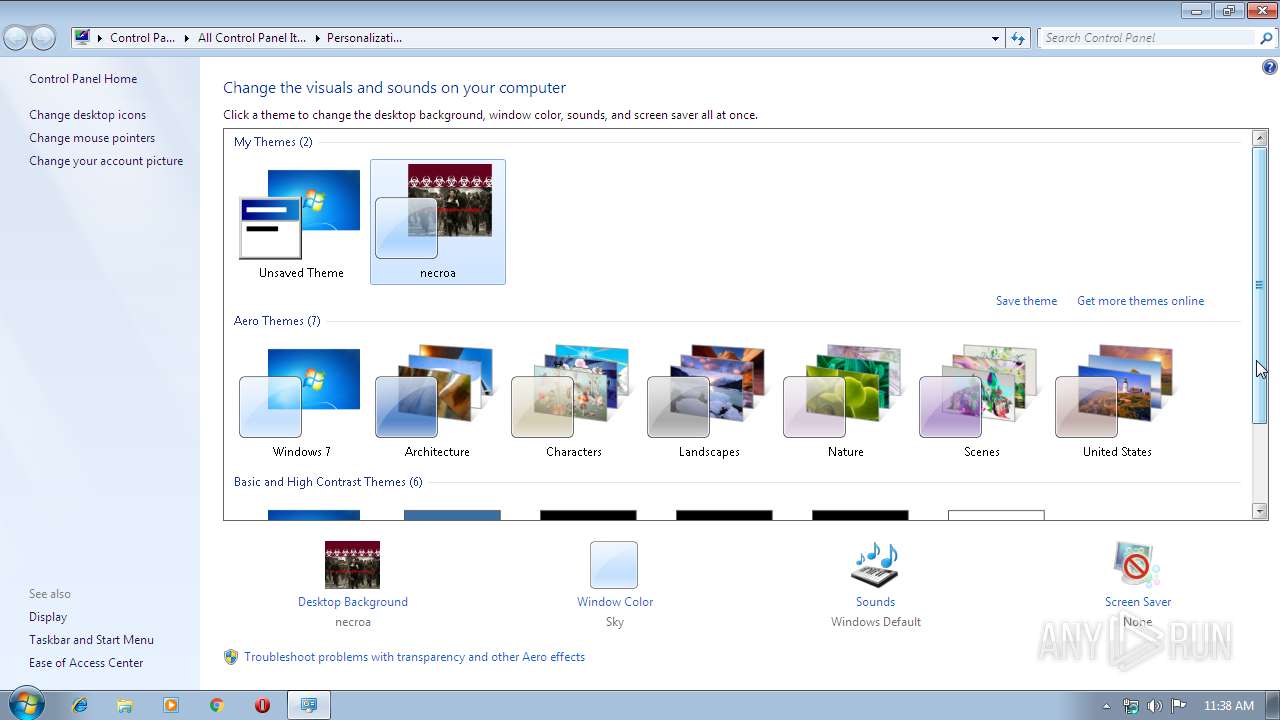
Modifies the open verb of a shell class
- regedit.exe (PID: 2348)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 2328)
INFO
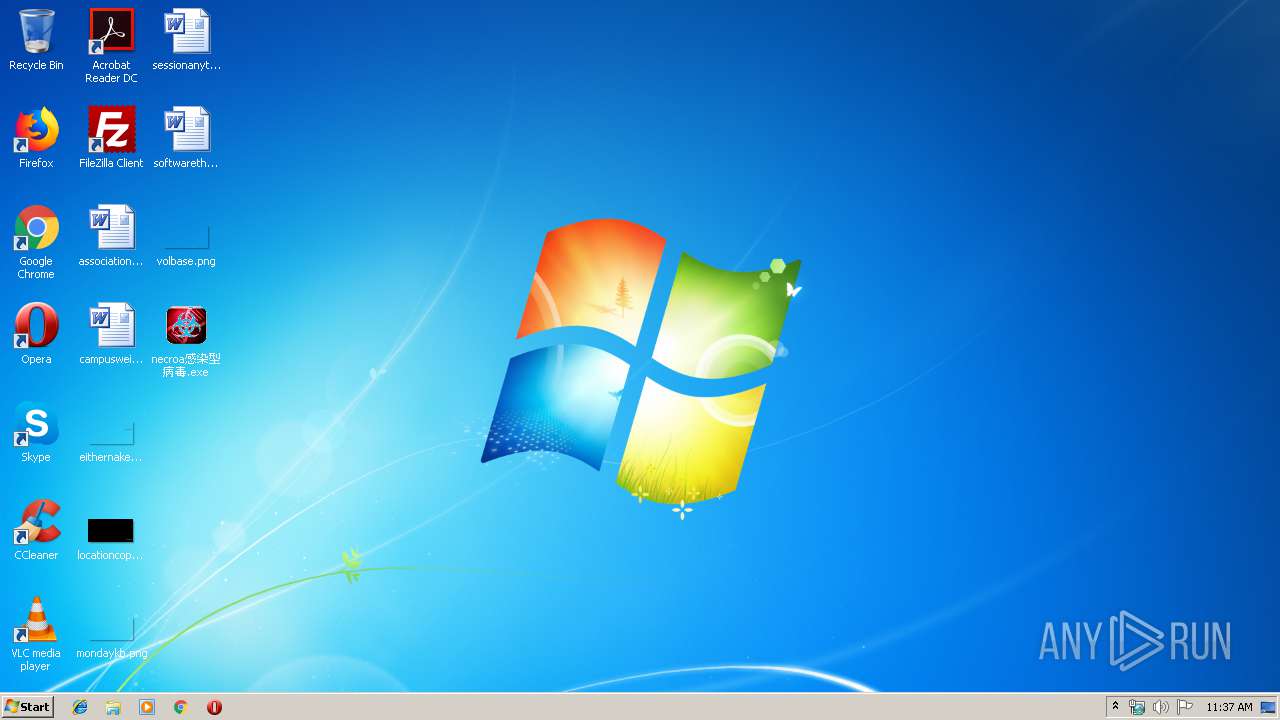
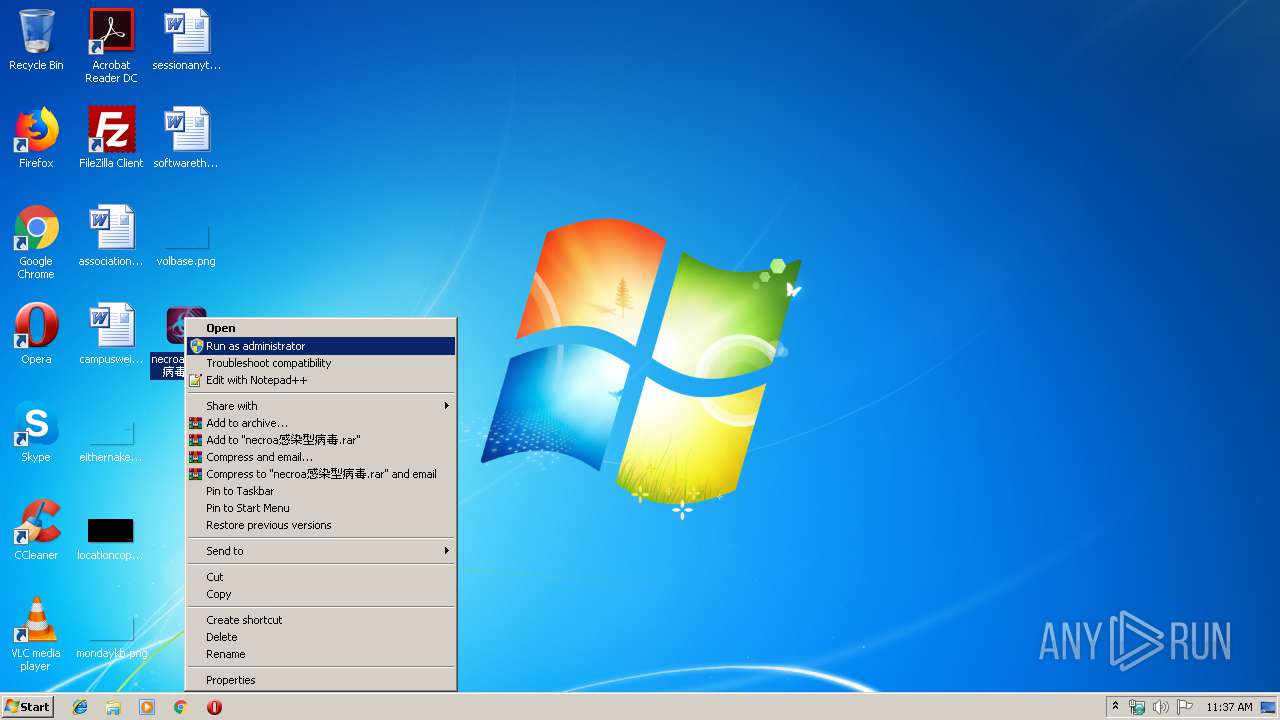
Manual execution by user
- necroa感染型病毒.exe (PID: 3760)
- mmc.exe (PID: 3676)
- mmc.exe (PID: 2280)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
75
Monitored processes
29
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1688 | SC config LanmanServer START= AUTO | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2116 | C:\Windows\system32\net1 start ShellHWDetection | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
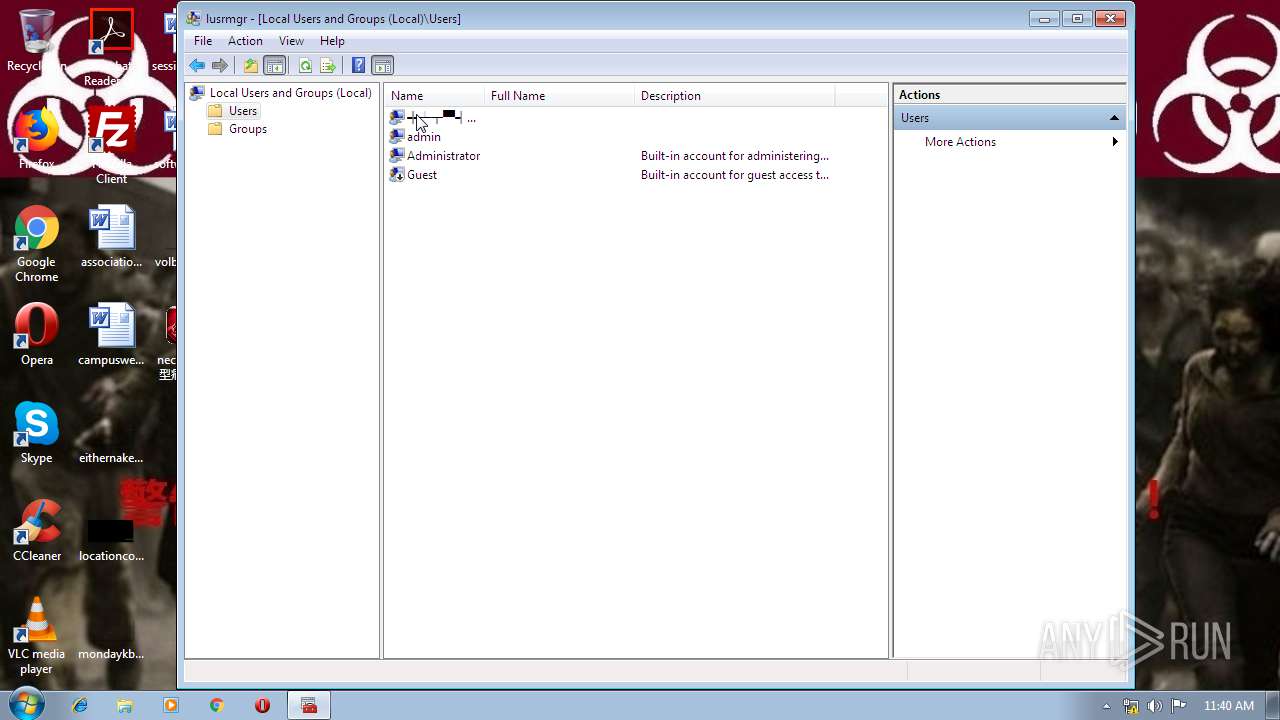
| 2280 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\lusrmgr.msc" | C:\Windows\system32\mmc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2328 | cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\0PVN636D.bat" "C:\Users\admin\Desktop\necroa?????.exe" " | C:\Windows\system32\cmd.exe | necroa感染型病毒.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2348 | regedit.exe /s C:\Users\admin\AppData\Local\qb114EF8.BB\necroa.reg | C:\Windows\regedit.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2436 | SC config DHCP START= AUTO | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2472 | net start DHCP | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2556 | SC config server START= AUTO | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2564 | NET USER ╬┴╥▀╣½╦╛ neurax /ADD | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2608 | NET LOCALGROUP TelnetClients ╬┴╥▀╣½╦╛ /add | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 261
Read events
1 114
Write events
146
Delete events
1
Modification events
| (PID) Process: | (3516) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3516) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3516) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3516) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\necroa感染型病毒.rar | |||
| (PID) Process: | (3516) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3516) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3516) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3516) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3516) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | 0 |
Value: 43003A005C00500072006F006700720061006D002000460069006C00650073005C00570069006E005200410052005C00570069006E005200410052002E00650078006500000043003A005C00550073006500720073005C00610064006D0069006E005C0044006F0077006E006C006F006100640073000000 | |||
| (PID) Process: | (3516) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
Executable files
6
Suspicious files
0
Text files
8
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4084 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\TP_5503.tmp | — | |
MD5:— | SHA256:— | |||
| 3516 | WinRAR.exe | C:\Users\admin\Desktop\necroa感染型病毒.exe | executable | |
MD5:— | SHA256:— | |||
| 3760 | necroa感染型病毒.exe | C:\Users\admin\AppData\Local\qb114EF8.BB\autorun.inf | inf | |
MD5:— | SHA256:— | |||
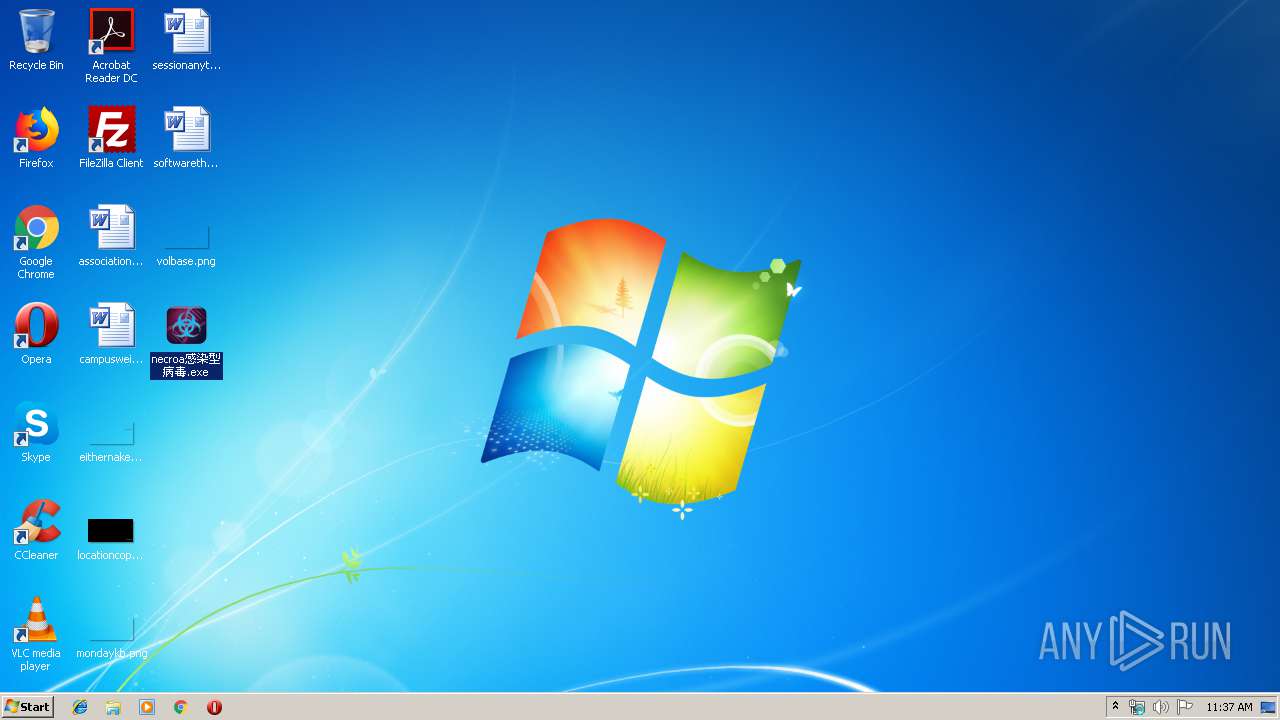
| 3760 | necroa感染型病毒.exe | C:\Users\admin\AppData\Local\qb114EF8.BB\necroa.themepack | themepack | |
MD5:— | SHA256:— | |||
| 2328 | cmd.exe | C:\windows\necroa.exe | executable | |
MD5:— | SHA256:— | |||
| 2328 | cmd.exe | C:\windows\neurax.exe | executable | |
MD5:— | SHA256:— | |||
| 3760 | necroa感染型病毒.exe | C:\Users\admin\AppData\Local\qb114EF8.BB\necroa.reg | text | |
MD5:— | SHA256:— | |||
| 3760 | necroa感染型病毒.exe | C:\Users\admin\AppData\Local\qb114EF8.BB\super.bat | text | |
MD5:— | SHA256:— | |||
| 4084 | rundll32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Themes\necroa\necroa.theme | text | |
MD5:— | SHA256:— | |||
| 4084 | rundll32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Themes\necroa\DesktopBackground\necroa.jpg | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
0
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3504 | WMIC.exe | GET | 404 | 149.28.76.165:80 | http://149.28.76.165/host.xsl | US | xml | 345 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3504 | WMIC.exe | 149.28.76.165:80 | — | — | US | unknown |