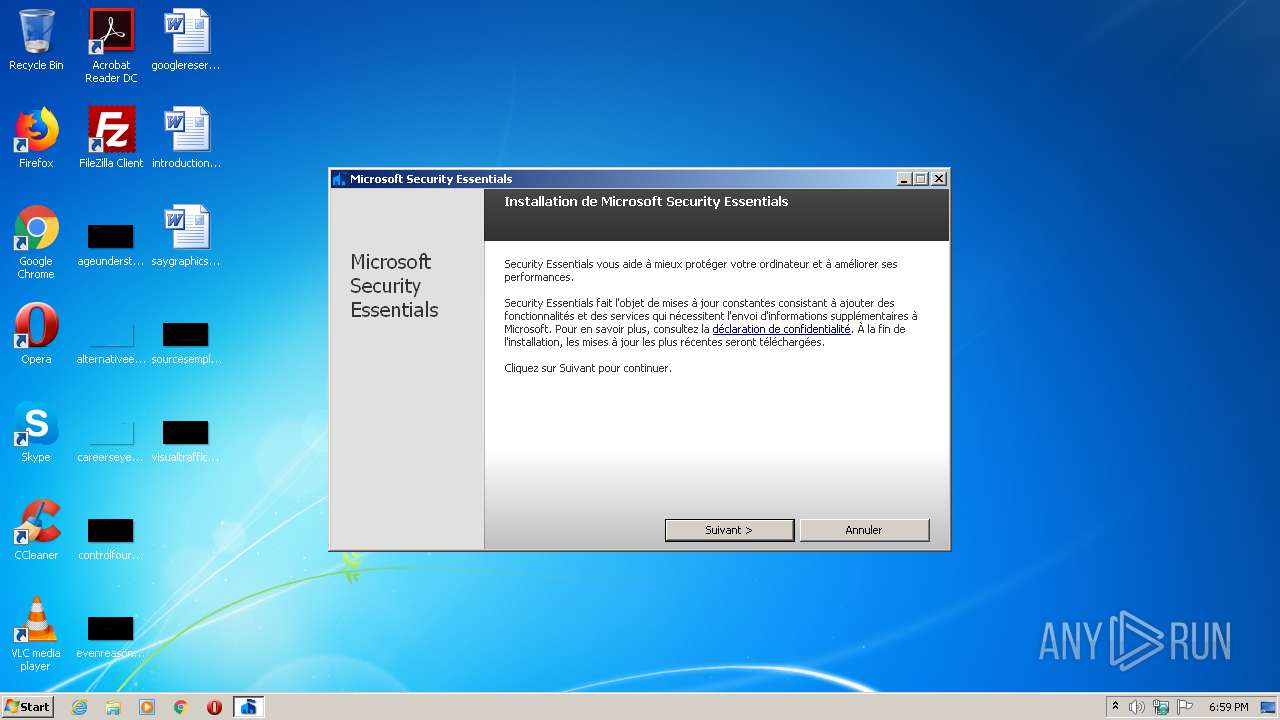
| File name: | MSEInstall.exe |
| Full analysis: | https://app.any.run/tasks/d07b9fd8-64d7-45bb-8669-e7c25c4442e4 |
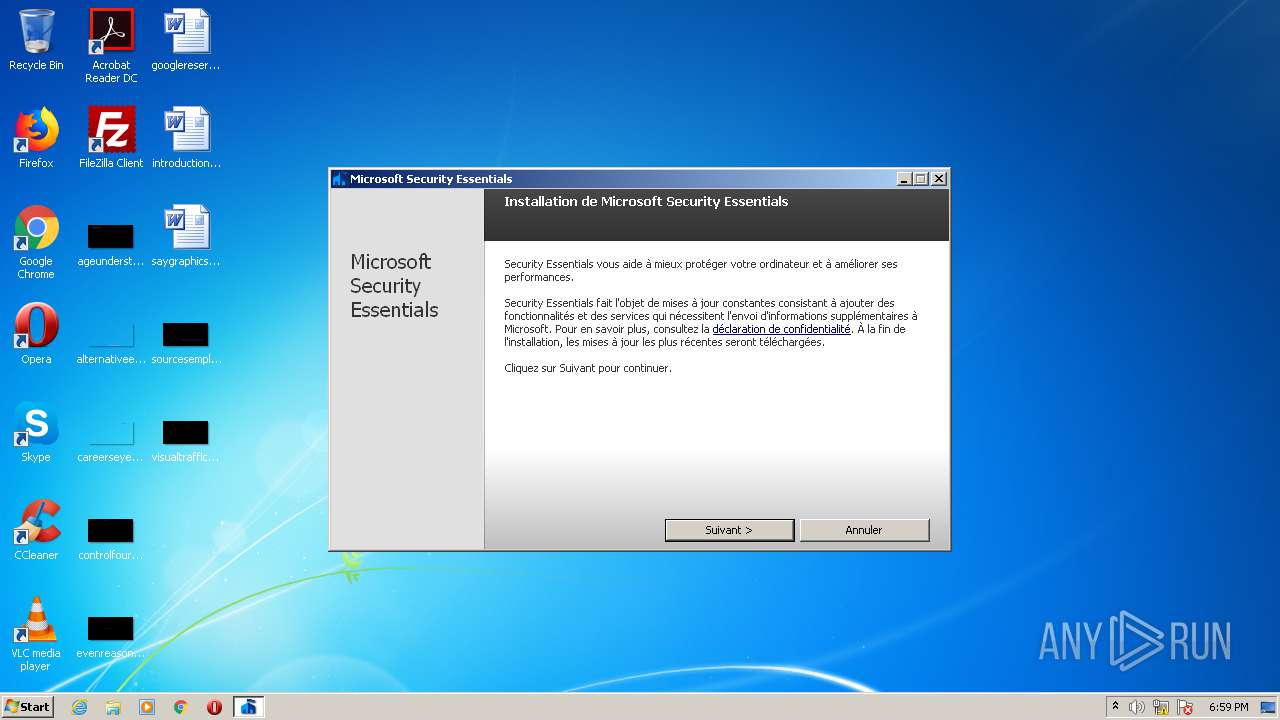
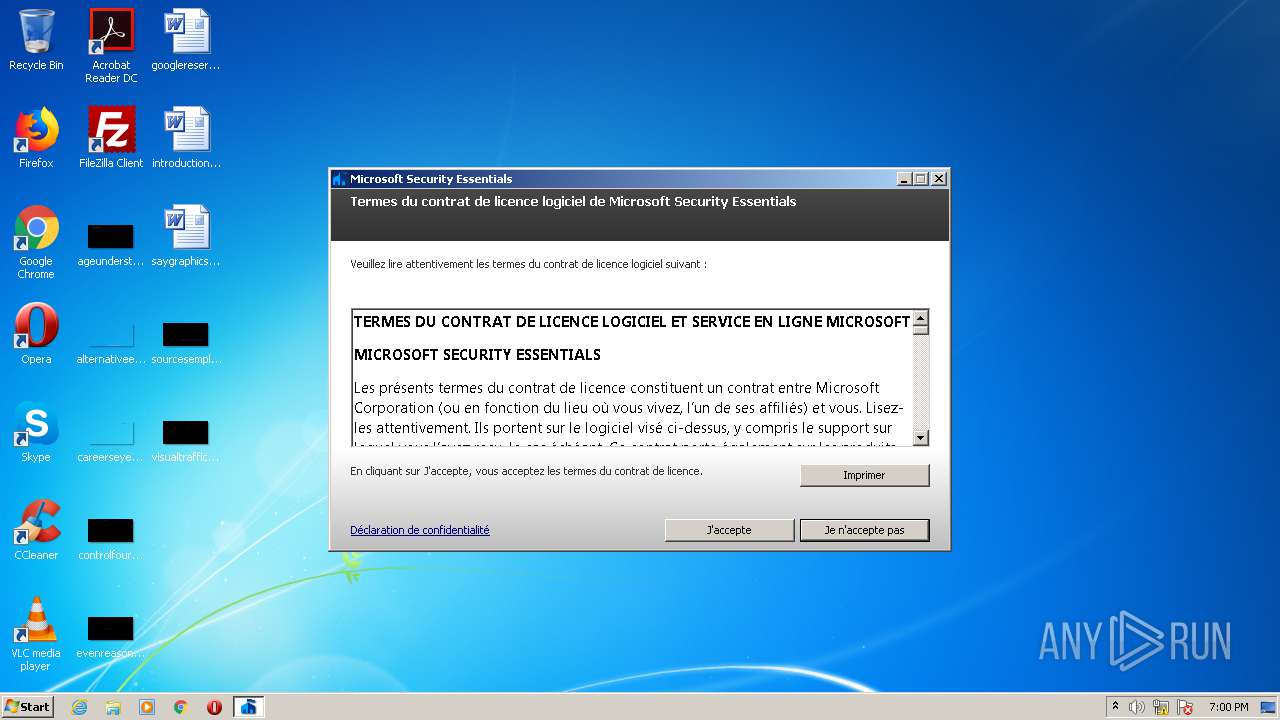
| Verdict: | Malicious activity |
| Analysis date: | April 03, 2021, 17:58:46 |
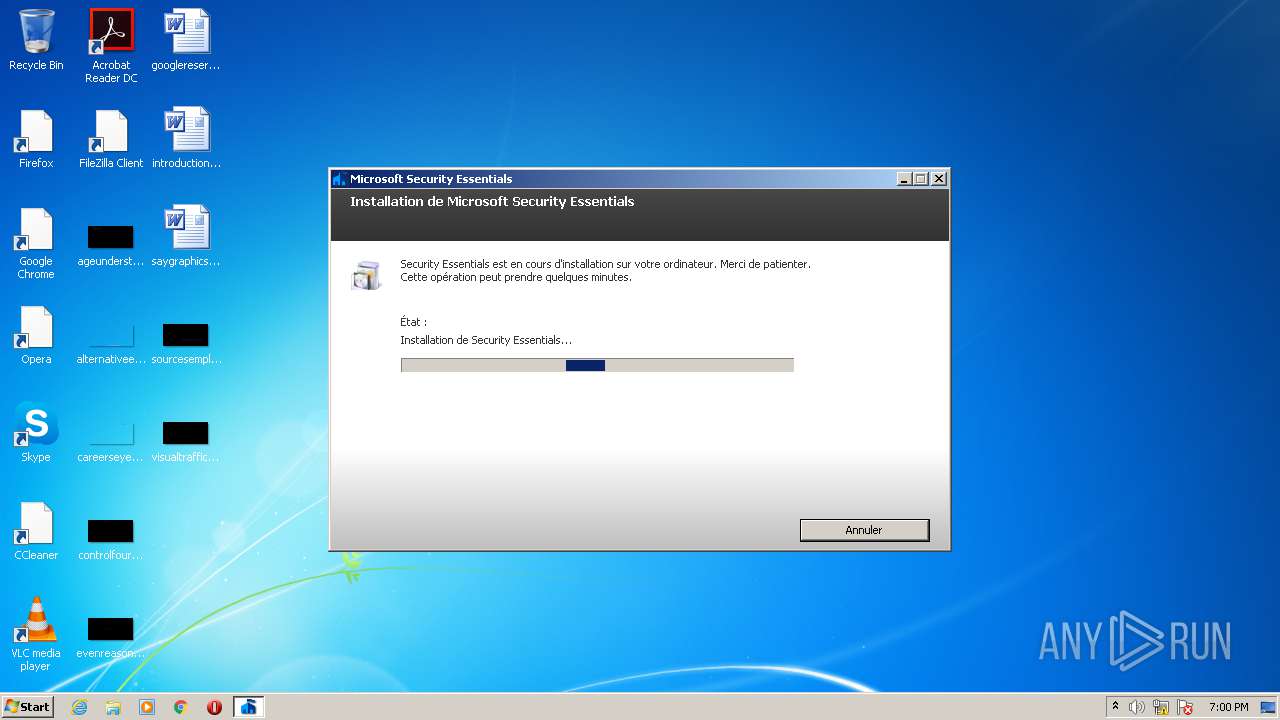
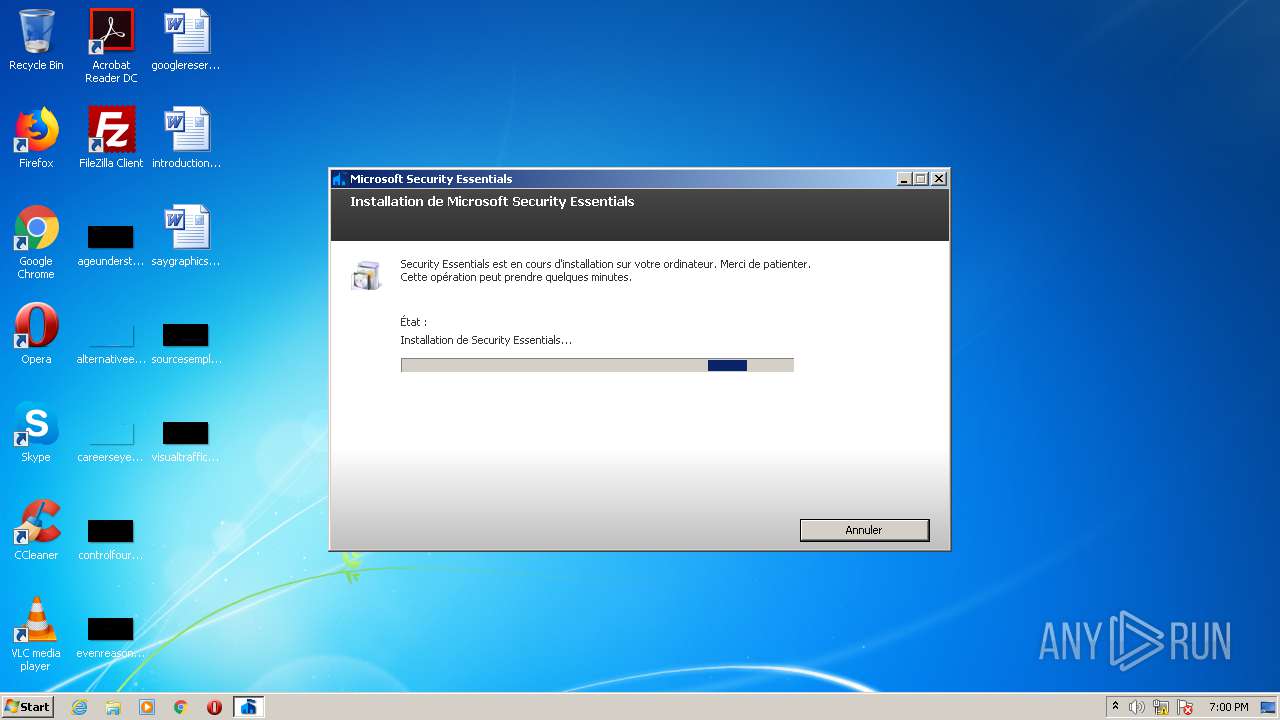
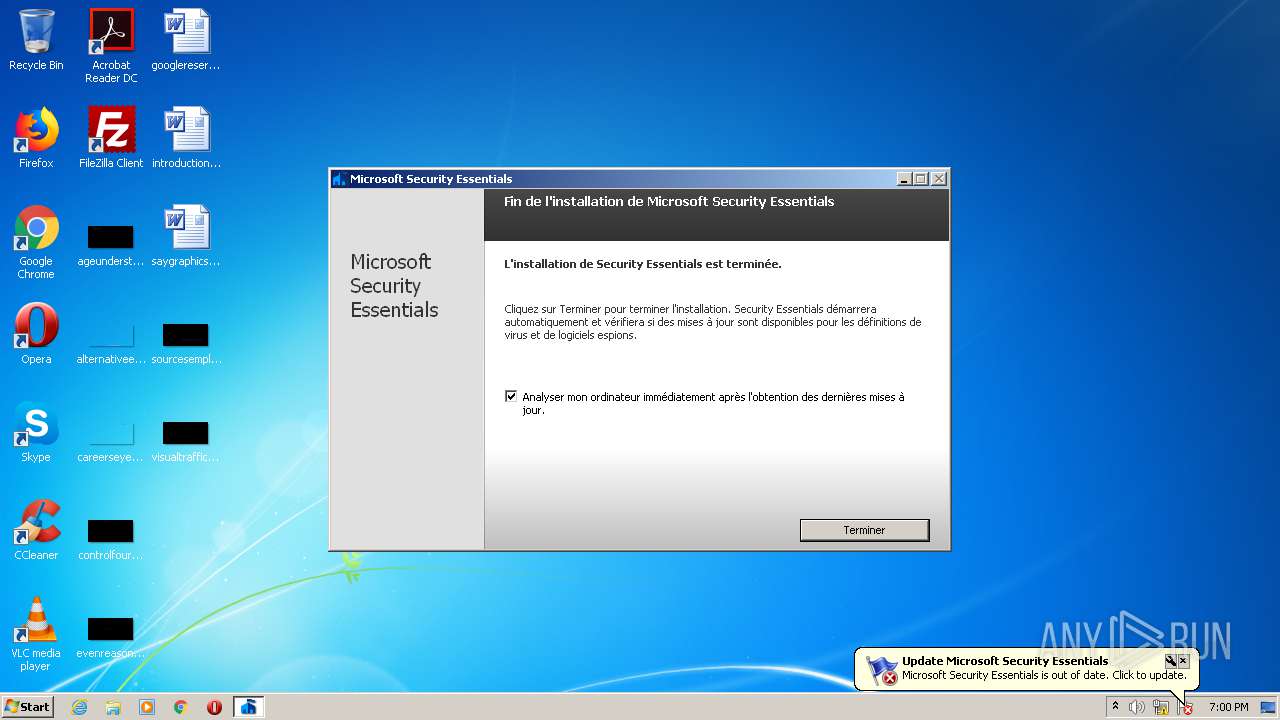
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, InstallShield self-extracting archive |
| MD5: | 2819435A97EB2A8691C2AF5344A5BD5C |
| SHA1: | E2851DBD248980569E46CE1E8F21D2ACFF759ADF |
| SHA256: | EA424A1EE2219BC61ACC2877B0C1DAE2C96B30BDD3B9322915F3DC60456E8E00 |
| SSDEEP: | 196608:ByLHbnHLu/LXuyrY39I4yD0cPaxah+31vaKDqw2vldbDb1AQ/0HgamIM1p:BubnHKy1IRgiM0KDRWdHCQ/eQIG |
MALICIOUS
Actions looks like stealing of personal data
- epplauncher.exe (PID: 3624)
Loads dropped or rewritten executable
- Setup.exe (PID: 2400)
- svchost.exe (PID: 856)
- services.exe (PID: 476)
- MsMpEng.exe (PID: 3384)
- msseces.exe (PID: 2700)
- MpCmdRun.exe (PID: 2172)
- MpCmdRun.exe (PID: 1532)
- MpCmdRun.exe (PID: 2148)
- MpCmdRun.exe (PID: 1756)
- NisSrv.exe (PID: 2412)
- mpsigstub.exe (PID: 3132)
- mpsigstub.exe (PID: 2128)
- NisSrv.exe (PID: 3560)
Drops executable file immediately after starts
- MSEInstall.exe (PID: 344)
- mpsigstub.exe (PID: 3132)
- mpam-3caa2efd.exe (PID: 3436)
Application was dropped or rewritten from another process
- epplauncher.exe (PID: 3624)
- Setup.exe (PID: 2400)
- MsMpEng.exe (PID: 3384)
- msseces.exe (PID: 2700)
- MpCmdRun.exe (PID: 2172)
- MpCmdRun.exe (PID: 1532)
- MpCmdRun.exe (PID: 2148)
- MpCmdRun.exe (PID: 1756)
- NisSrv.exe (PID: 2412)
- mpsigstub.exe (PID: 3132)
- mpam-b563e0b4.exe (PID: 3584)
- mpam-3caa2efd.exe (PID: 3436)
- mpsigstub.exe (PID: 2128)
- NisSrv.exe (PID: 3560)
Loads the Task Scheduler COM API
- MsiExec.exe (PID: 1736)
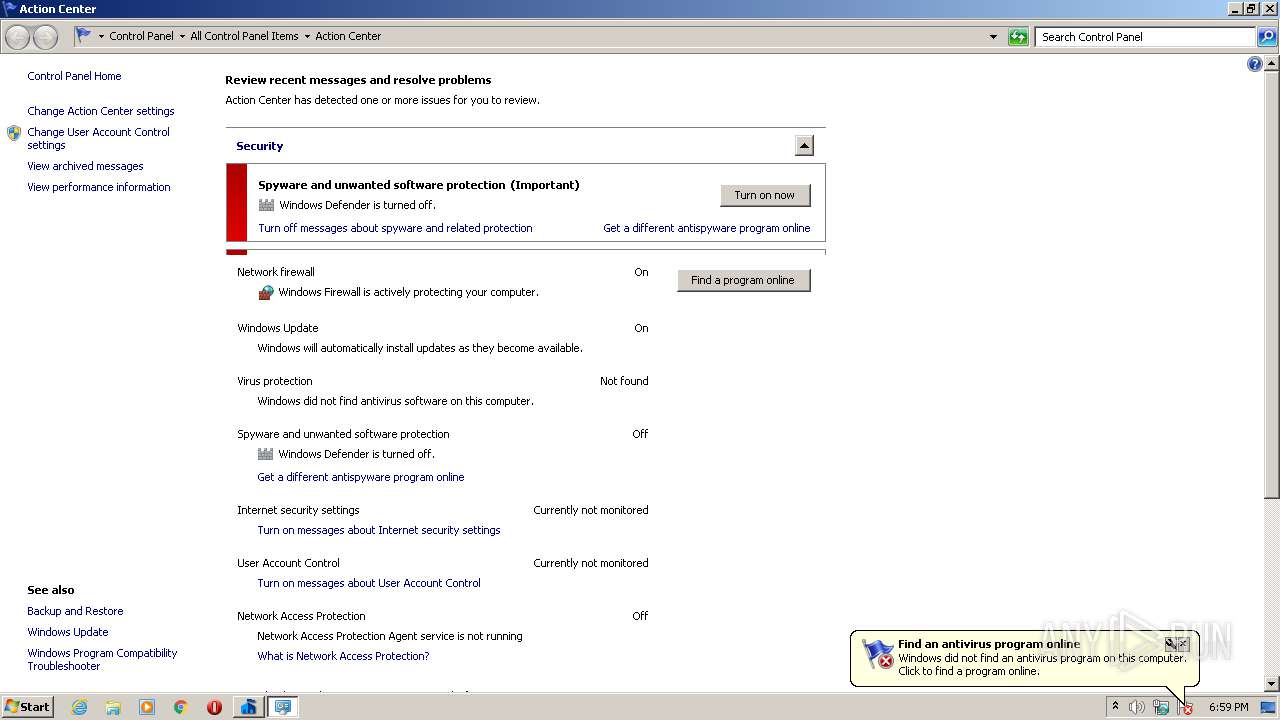
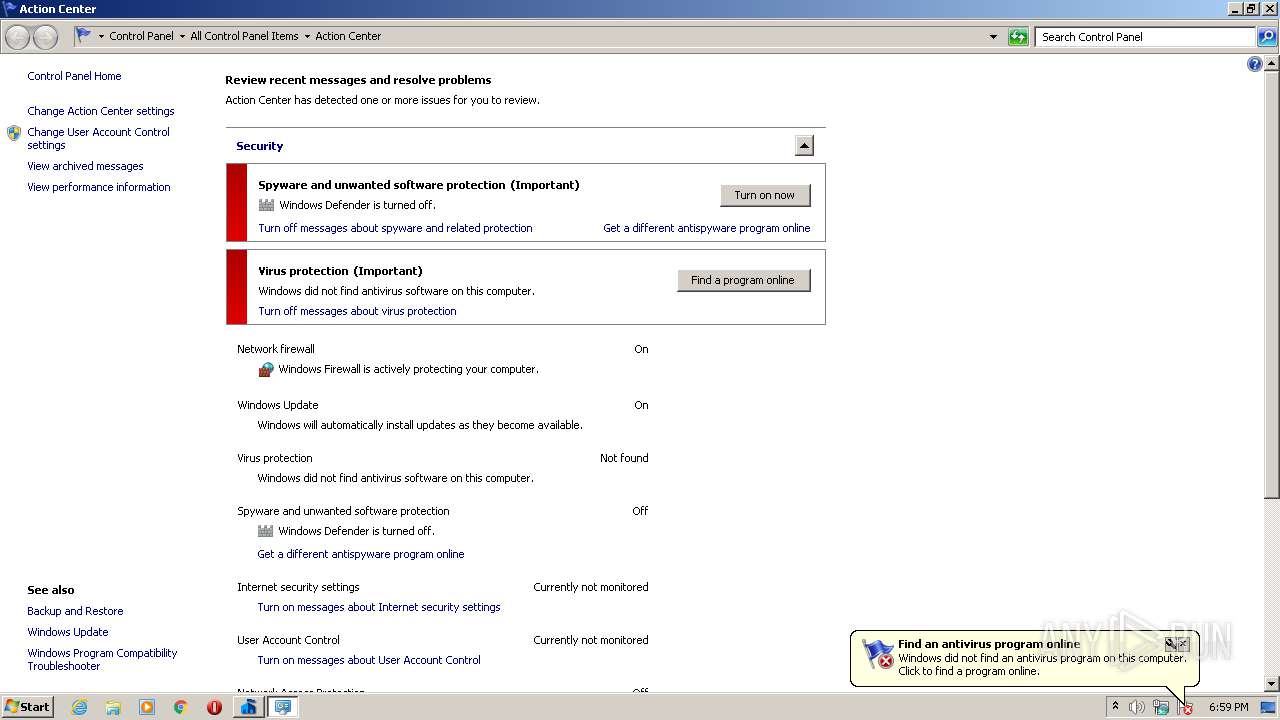
Modifies Windows Defender service settings
- services.exe (PID: 476)
SUSPICIOUS
Executable content was dropped or overwritten
- MSEInstall.exe (PID: 344)
- Setup.exe (PID: 2400)
- msseces.exe (PID: 2700)
- mpam-b563e0b4.exe (PID: 3584)
- MsMpEng.exe (PID: 3384)
- MpCmdRun.exe (PID: 1756)
- mpam-3caa2efd.exe (PID: 3436)
Drops a file that was compiled in debug mode
- MSEInstall.exe (PID: 344)
- MsiExec.exe (PID: 1736)
- Setup.exe (PID: 2400)
- msseces.exe (PID: 2700)
- mpam-b563e0b4.exe (PID: 3584)
- MsMpEng.exe (PID: 3384)
- MpCmdRun.exe (PID: 1756)
- mpam-3caa2efd.exe (PID: 3436)
Drops a file with too old compile date
- MSEInstall.exe (PID: 344)
- Setup.exe (PID: 2400)
- mpam-b563e0b4.exe (PID: 3584)
- MsMpEng.exe (PID: 3384)
- mpam-3caa2efd.exe (PID: 3436)
Creates files in the program directory
- epplauncher.exe (PID: 3624)
- Setup.exe (PID: 2400)
- MsMpEng.exe (PID: 3384)
- wermgr.exe (PID: 960)
- wermgr.exe (PID: 2596)
- wermgr.exe (PID: 2184)
- NisSrv.exe (PID: 2412)
Executed via COM
- DllHost.exe (PID: 4072)
- DllHost.exe (PID: 1004)
Creates files in the Windows directory
- svchost.exe (PID: 856)
- MsiExec.exe (PID: 1736)
- Setup.exe (PID: 2400)
- MpCmdRun.exe (PID: 2172)
- MpCmdRun.exe (PID: 1756)
- mpam-3caa2efd.exe (PID: 3436)
- mpsigstub.exe (PID: 2128)
Creates a directory in Program Files
- Setup.exe (PID: 2400)
Removes files from Windows directory
- svchost.exe (PID: 856)
- MsiExec.exe (PID: 1736)
- wermgr.exe (PID: 960)
- wermgr.exe (PID: 2184)
- MpCmdRun.exe (PID: 1756)
- mpam-3caa2efd.exe (PID: 3436)
- mpsigstub.exe (PID: 2128)
Creates or modifies windows services
- services.exe (PID: 476)
Creates files in the driver directory
- MsiExec.exe (PID: 1736)
Creates files in the user directory
- Setup.exe (PID: 2400)
Creates a software uninstall entry
- Setup.exe (PID: 2400)
Application launched itself
- MpCmdRun.exe (PID: 2148)
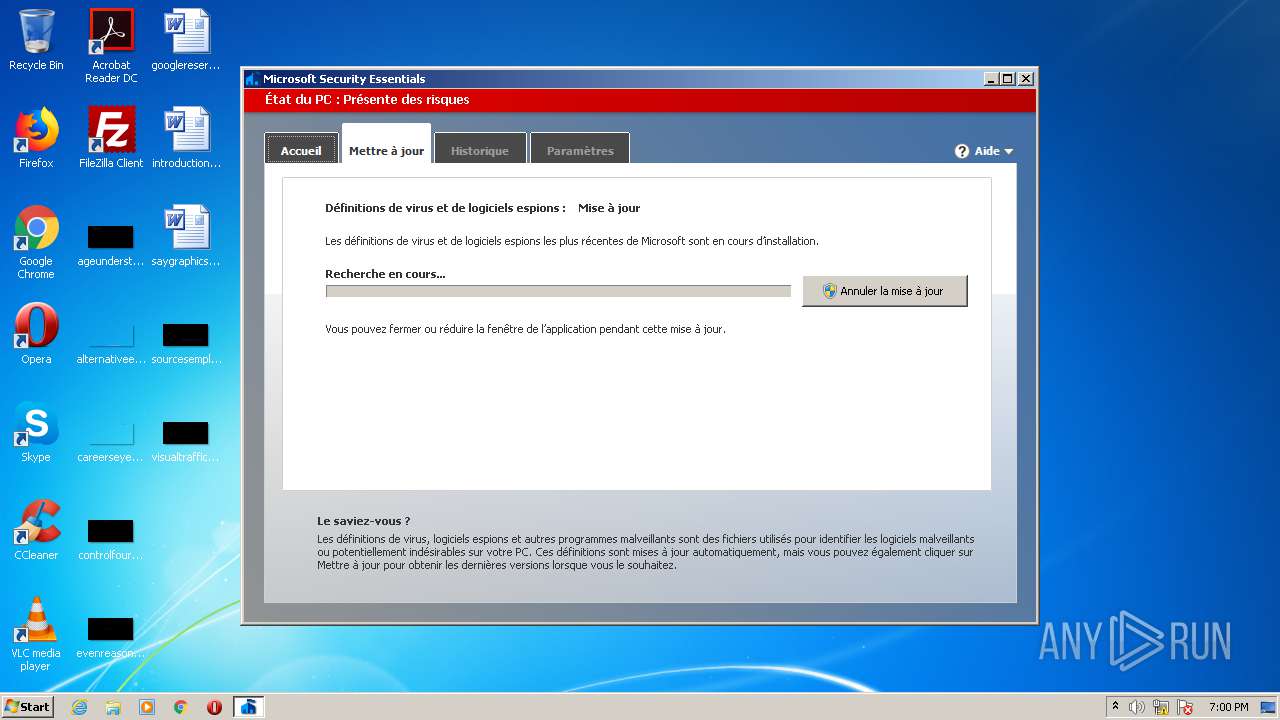
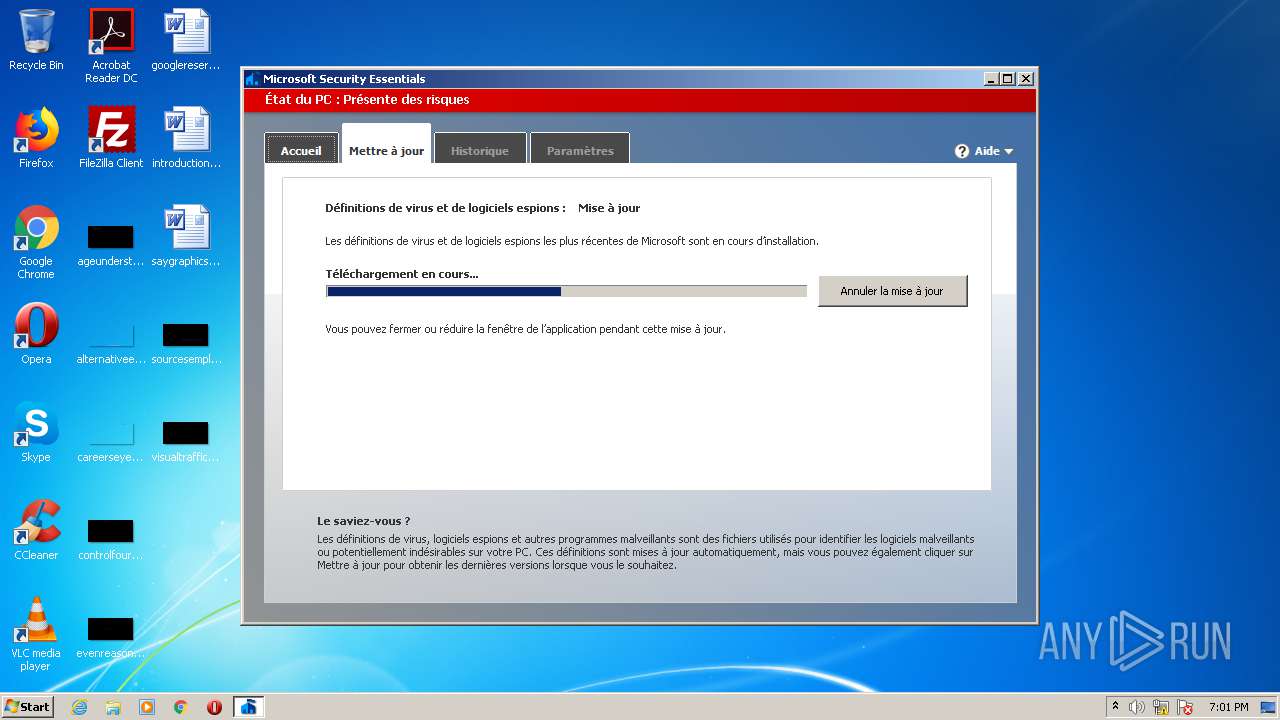
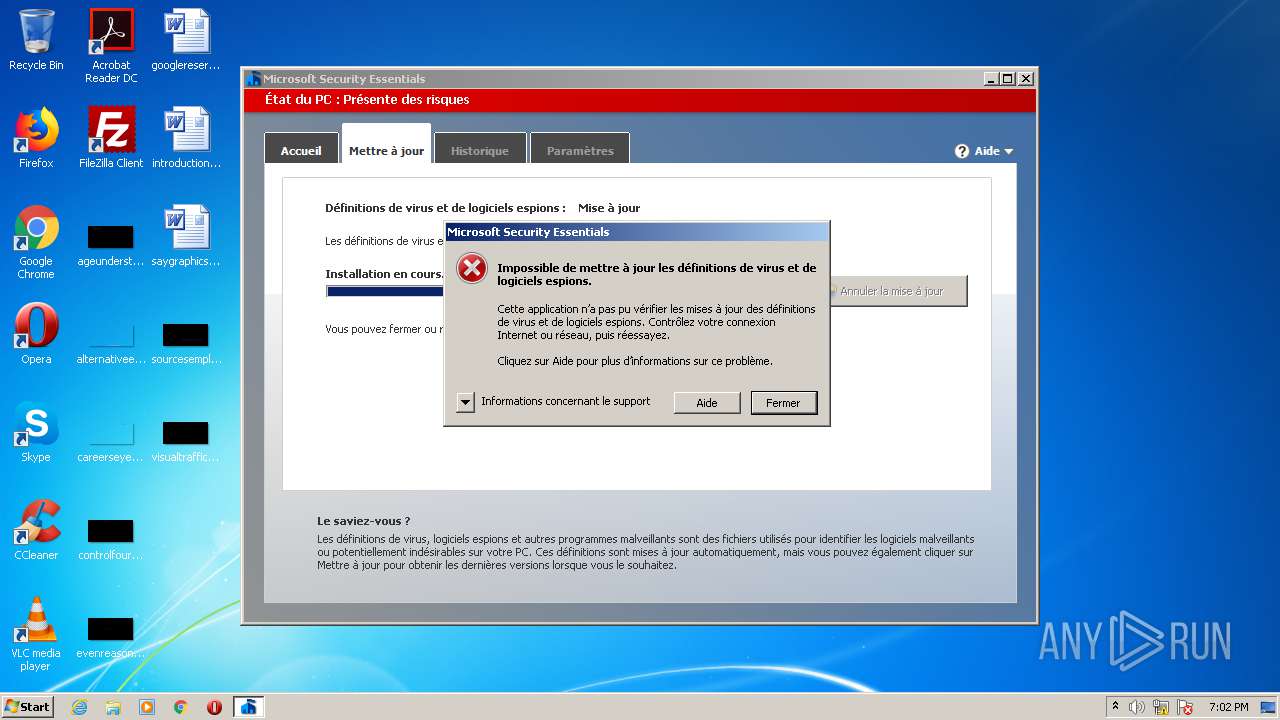
Starts Internet Explorer
- msseces.exe (PID: 2700)
INFO
Reads settings of System Certificates
- svchost.exe (PID: 856)
- iexplore.exe (PID: 3360)
- iexplore.exe (PID: 2256)
Creates or modifies windows services
- MsiExec.exe (PID: 1736)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 1888)
- MsiExec.exe (PID: 1736)
Creates files in the user directory
- iexplore.exe (PID: 3360)
Application launched itself
- iexplore.exe (PID: 2256)
Changes internet zones settings
- iexplore.exe (PID: 2256)
Reads internet explorer settings
- iexplore.exe (PID: 3360)
Changes settings of System certificates
- iexplore.exe (PID: 2256)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2256)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | MS generic-sfx Cabinet File Unpacker (32/64bit MSCFU) (82.5) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (7.3) |
| .exe | | | Win64 Executable (generic) (6.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.5) |
| .exe | | | Win32 Executable (generic) (1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:03:13 07:51:25+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 7.1 |
| CodeSize: | 35840 |
| InitializedDataSize: | 300032 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6b23 |
| OSVersion: | 5.2 |
| ImageVersion: | 5.2 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.10.209.0 |
| ProductVersionNumber: | 4.10.209.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | MSEInstall Package |
| FileVersion: | 4.10.0209.0 |
| InternalName: | MSEInstall.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | MSEInstall.exe |
| ProductName: | Microsoft Security Client |
| ProductVersion: | 4.10.0209.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Mar-2009 06:51:25 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | MSEInstall Package |
| FileVersion: | 4.10.0209.0 |
| InternalName: | MSEInstall.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | MSEInstall.exe |
| ProductName: | Microsoft Security Client |
| ProductVersion: | 4.10.0209.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 13-Mar-2009 06:51:25 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00008B08 | 0x00008C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.53364 |
.data | 0x0000C000 | 0x00011438 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.519063 |
.rsrc | 0x0001E000 | 0x000491D4 | 0x00049200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.03435 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 1.5 | 4 | Latin 1 / Western European | English - United States | UNKNOWN |
2 | 3.84176 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.96352 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.48788 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.99442 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.58633 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 4.94629 | 270376 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 5.41932 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 5.4847 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 4.86767 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
msvcrt.dll |
ntdll.dll |
Total processes
81
Monitored processes
28
Malicious processes
18
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 344 | "C:\Users\admin\AppData\Local\Temp\MSEInstall.exe" | C:\Users\admin\AppData\Local\Temp\MSEInstall.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: MSEInstall Package Exit code: 0 Version: 4.10.0209.0 Modules
| |||||||||||||||
| 476 | C:\Windows\system32\services.exe | C:\Windows\System32\services.exe | — | wininit.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Services and Controller app Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 856 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 960 | "C:\Windows\system32\wermgr.exe" "-outproc" "856" "4136" | C:\Windows\system32\wermgr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1004 | C:\Windows\system32\DllHost.exe /Processid:{E9495B87-D950-4AB5-87A5-FF6D70BF3E90} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1532 | "c:\Program Files\Microsoft Security Client\\MpCmdRun.exe" SignaturesUpdateService -ScheduleJob -UnmanagedUpdate | c:\Program Files\Microsoft Security Client\MpCmdRun.exe | — | MsMpEng.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Malware Protection Command Line Utility Exit code: 0 Version: 4.10.0209.0 Modules
| |||||||||||||||
| 1736 | c:\Windows\system32\MsiExec.exe -Embedding 6F0F4D81CF564EA446C1F59F5E7612F4 M Global\MSI0000 | c:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1756 | "c:\Program Files\Microsoft Security Client\\MpCmdRun.exe" SignaturesUpdateService -ScheduleJob -HttpDownload -RestrictPrivileges -Reinvoke | c:\Program Files\Microsoft Security Client\MpCmdRun.exe | MpCmdRun.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Malware Protection Command Line Utility Exit code: 0 Version: 4.10.0209.0 Modules
| |||||||||||||||
| 1888 | c:\Windows\system32\MsiExec.exe -Embedding AAC4890042DFD791BBB203A847D95243 | c:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2128 | C:\Windows\SERVIC~2\NETWOR~1\AppData\Local\Temp\{4D51910D-A473-47EA-8A98-26EF0BE2B1EF}\mpsigstub.exe /stub 1.1.14500.5 /payload 119.0.0.0 /program C:\Windows\SERVIC~2\NETWOR~1\AppData\Local\Temp\mpam-3caa2efd.exe /q /ProductGUID EDB4FA23-53B8-4AFA-8C5D-99752CCA7094 | C:\Windows\SERVIC~2\NETWOR~1\AppData\Local\Temp\{4D51910D-A473-47EA-8A98-26EF0BE2B1EF}\mpsigstub.exe | — | mpam-3caa2efd.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Malware Protection Signature Update Stub Exit code: 0 Version: 1.1.14500.5 (5ed17a8d71195f7dd09ac85d18671d0876764dd1) Modules
| |||||||||||||||
Total events
5 049
Read events
4 704
Write events
326
Delete events
19
Modification events
| (PID) Process: | (856) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\CoDeviceInstallers |
| Operation: | write | Name: | _ObjectId_ |
Value: F000000000000000 | |||
| (PID) Process: | (856) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Enum |
| Operation: | write | Name: | ObjectId |
Value: F000000000000000 | |||
| (PID) Process: | (856) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Enum |
| Operation: | write | Name: | ObjectLru |
Value: 0804000000000000 | |||
| (PID) Process: | (856) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\CoDeviceInstallers |
| Operation: | write | Name: | _ObjectLru_ |
Value: 0804000000000000 | |||
| (PID) Process: | (856) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\CoDeviceInstallers |
| Operation: | write | Name: | _FileId_ |
Value: 29C2000000000400 | |||
| (PID) Process: | (856) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\CoDeviceInstallers |
| Operation: | write | Name: | _Usn_ |
Value: 78EF0C0500000000 | |||
| (PID) Process: | (856) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\CoDeviceInstallers |
| Operation: | write | Name: | _UsnJournalId_ |
Value: CAF752A8FD3DD301 | |||
| (PID) Process: | (856) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services |
| Operation: | write | Name: | 400000000C229 |
Value: 29C2000000000400 | |||
| (PID) Process: | (856) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Class |
| Operation: | write | Name: | F0 |
Value: F000000000000000 | |||
| (PID) Process: | (856) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\CoDeviceInstallers |
| Operation: | write | Name: | AeFileID |
Value: 300030003000300037003900370065006500350033006600340039003700330062003400330035003900330032006300350037003300660030003400310033006100660064003500390037003700620061006600300065000000 | |||
Executable files
30
Suspicious files
57
Text files
76
Unknown types
40
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 344 | MSEInstall.exe | C:\062b149833893f6f17f2fd6dc8b3f0\x86\epp.msi | — | |
MD5:— | SHA256:— | |||
| 856 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:6534F5B88C7C04BDAF5C8EA10E166F82 | SHA256:4F771DBD2CAD230E51CDAFC9AEC8909916160651EC8176C5AA8E19F1EDD28685 | |||
| 344 | MSEInstall.exe | C:\062b149833893f6f17f2fd6dc8b3f0\epplauncher.exe | executable | |
MD5:C9E82C0B2083B76AD7F5631E4A52609C | SHA256:482DA7FFC6AD64B0307E6A7B0C1D77A60BC07ECA878E663F42ABCF4D02A51C63 | |||
| 2400 | Setup.exe | C:\ProgramData\Microsoft\Microsoft Security Client\Support\EppSetupResult.ini | text | |
MD5:7CB36E99703C598A3F4005508FF64AB0 | SHA256:89650298914A4E6C615A9B23494CB63FA93C29D3DA321410AC55BBAAE427E199 | |||
| 344 | MSEInstall.exe | C:\062b149833893f6f17f2fd6dc8b3f0\EN-US\setupres.dll.mui | executable | |
MD5:7E8248F70361DF527F6F195C3616EFF6 | SHA256:596348E1160D0DA943704968AF54978955C8C0443D02BDBC255F80F3CDADB49E | |||
| 344 | MSEInstall.exe | C:\062b149833893f6f17f2fd6dc8b3f0\FR-FR\setupres.dll.mui | executable | |
MD5:79C414318BFED727024C80FB46AA3C57 | SHA256:9D3BA7821A11B3129F47AD3B4F8FB6A26290A0CE2180A7C8FBBAEA6F8DD1164F | |||
| 344 | MSEInstall.exe | C:\062b149833893f6f17f2fd6dc8b3f0\setupres.dll | executable | |
MD5:ACFB50A5F7DD8106B3A510BCC2161FBD | SHA256:F926C5DCADC292DBB138AF95AFF1E2C11FA2CDA70EC81E66A93F540A29E27B25 | |||
| 1736 | MsiExec.exe | C:\Windows\system32\DRIVERS\SETACC6.tmp | — | |
MD5:— | SHA256:— | |||
| 344 | MSEInstall.exe | C:\062b149833893f6f17f2fd6dc8b3f0\x86\sqmapi.dll | executable | |
MD5:D475BBD6FEF8DB2DDE0DA7CCFD2C9042 | SHA256:8E9D77A216D8DD2BE2B304E60EDF85CE825309E67262FCFF1891AEDE63909599 | |||
| 1736 | MsiExec.exe | C:\Windows\system32\DRIVERS\SETACF6.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
77
DNS requests
36
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2596 | wermgr.exe | GET | — | 104.42.151.234:80 | http://watson.microsoft.com/StageOne/Generic/MSSecurityClient/Setup_exe/4_10_209_0/0x80070003/MorroBootstraper__CInstallFlow__InternalRunEpp%20-%20GetBackupAction/MorroBootstraper__CFlow__ProcessFlowActionResult/0/Security%20Essentials.htm?LCID=1033&OS=6.1.7601.2.00010100.1.0.48.17514&SM=DELL&SPN=DELL&BV=DELL | US | — | — | whitelisted |
— | — | HEAD | 200 | 8.248.113.254:80 | http://download.windowsupdate.com/v9/windowsupdate/redir/muv4wuredir.cab?2104031800 | US | — | — | whitelisted |
— | — | GET | 200 | 2.16.107.82:80 | http://ds.download.windowsupdate.com/v11/2/microsoftupdate/redir/v6-legacy-muauth.cab?2104031800 | unknown | compressed | 23.3 Kb | whitelisted |
— | — | HEAD | 200 | 2.16.107.82:80 | http://ds.download.windowsupdate.com/v11/2/microsoftupdate/redir/v6-legacy-muauth.cab?2104031800 | unknown | — | — | whitelisted |
— | — | HEAD | 200 | 2.16.107.82:80 | http://ds.download.windowsupdate.com/v11/2/microsoftupdate/redir/v6-legacy-muredir.cab?2104031800 | unknown | compressed | 23.3 Kb | whitelisted |
— | — | GET | 200 | 2.16.107.82:80 | http://ds.download.windowsupdate.com/v11/2/microsoftupdate/redir/v6-legacy-muredir.cab?2104031800 | unknown | compressed | 22.9 Kb | whitelisted |
2700 | msseces.exe | GET | 302 | 104.111.242.51:80 | http://go.microsoft.com/fwlink/?LinkID=121721&clcid=0x409&arch=x86&eng=0.0.0.0&avdelta=0.0.0.0&asdelta=0.0.0.0&prod=EDB4FA23-53B8-4AFA-8C5D-99752CCA7094 | NL | — | — | whitelisted |
— | — | HEAD | 200 | 8.248.113.254:80 | http://download.windowsupdate.com/v9/windowsupdate/redir/muv4wuredir.cab?2104031801 | US | — | — | whitelisted |
— | — | HEAD | 200 | 2.16.107.82:80 | http://ds.download.windowsupdate.com/v11/2/microsoftupdate/redir/v6-legacy-muauth.cab?2104031801 | unknown | compressed | 22.9 Kb | whitelisted |
1756 | MpCmdRun.exe | GET | 302 | 104.111.242.51:80 | http://go.microsoft.com/fwlink/?LinkID=121721&clcid=0x409&arch=x86&eng=0.0.0.0&avdelta=0.0.0.0&asdelta=0.0.0.0&prod=EDB4FA23-53B8-4AFA-8C5D-99752CCA7094 | NL | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.70.224.146:443 | www.update.microsoft.com | Microsoft Corporation | US | malicious |
2596 | wermgr.exe | 104.42.151.234:80 | watson.microsoft.com | Microsoft Corporation | US | suspicious |
— | — | 2.16.107.82:80 | ds.download.windowsupdate.com | Akamai International B.V. | — | suspicious |
2700 | msseces.exe | 104.111.242.51:80 | go.microsoft.com | Akamai International B.V. | NL | unknown |
2700 | msseces.exe | 184.30.21.171:443 | www.microsoft.com | GTT Communications Inc. | US | suspicious |
2700 | msseces.exe | 2.18.233.19:443 | definitionupdates.microsoft.com | Akamai International B.V. | — | whitelisted |
1756 | MpCmdRun.exe | 104.111.242.51:80 | go.microsoft.com | Akamai International B.V. | NL | unknown |
1756 | MpCmdRun.exe | 2.18.233.19:443 | definitionupdates.microsoft.com | Akamai International B.V. | — | whitelisted |
1756 | MpCmdRun.exe | 23.210.253.93:443 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2700 | msseces.exe | 104.79.89.142:443 | www.microsoft.com | Time Warner Cable Internet LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.windowsupdate.com |
| whitelisted |
www.update.microsoft.com |
| whitelisted |
watson.microsoft.com |
| whitelisted |
sqm.microsoft.com |
| unknown |
ds.download.windowsupdate.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
definitionupdates.microsoft.com |
| whitelisted |
support.microsoft.com |
| malicious |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2596 | wermgr.exe | Potential Corporate Privacy Violation | ET POLICY Application Crash Report Sent to Microsoft |
2596 | wermgr.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
Process | Message |
|---|---|
Setup.exe | Invalid parameter passed to C runtime function.
|
Setup.exe | Invalid parameter passed to C runtime function.
|
wermgr.exe | Error - |
wermgr.exe | |
wermgr.exe | |
wermgr.exe | Failed to read the peb from the process |
wermgr.exe | Failed to read the peb from the process |
wermgr.exe |