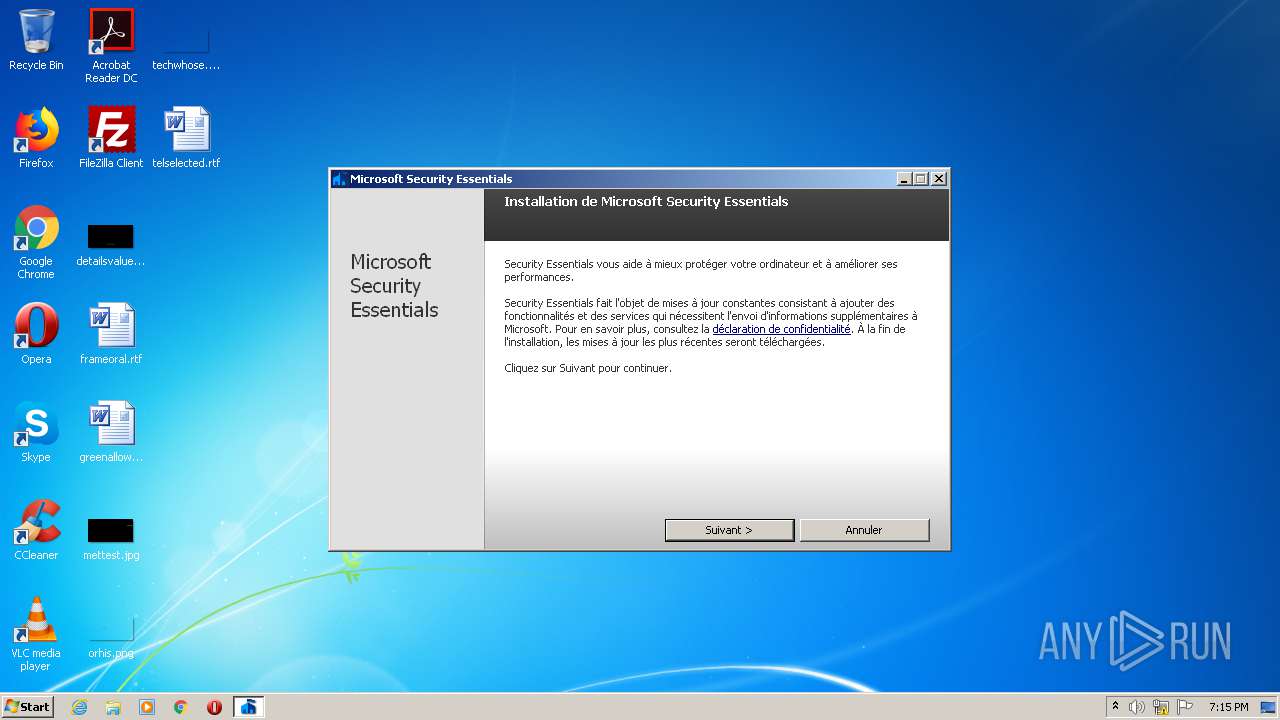
| File name: | MSEInstall.exe |
| Full analysis: | https://app.any.run/tasks/535ca0a2-3dde-483b-91ce-8f754fdb1cdb |
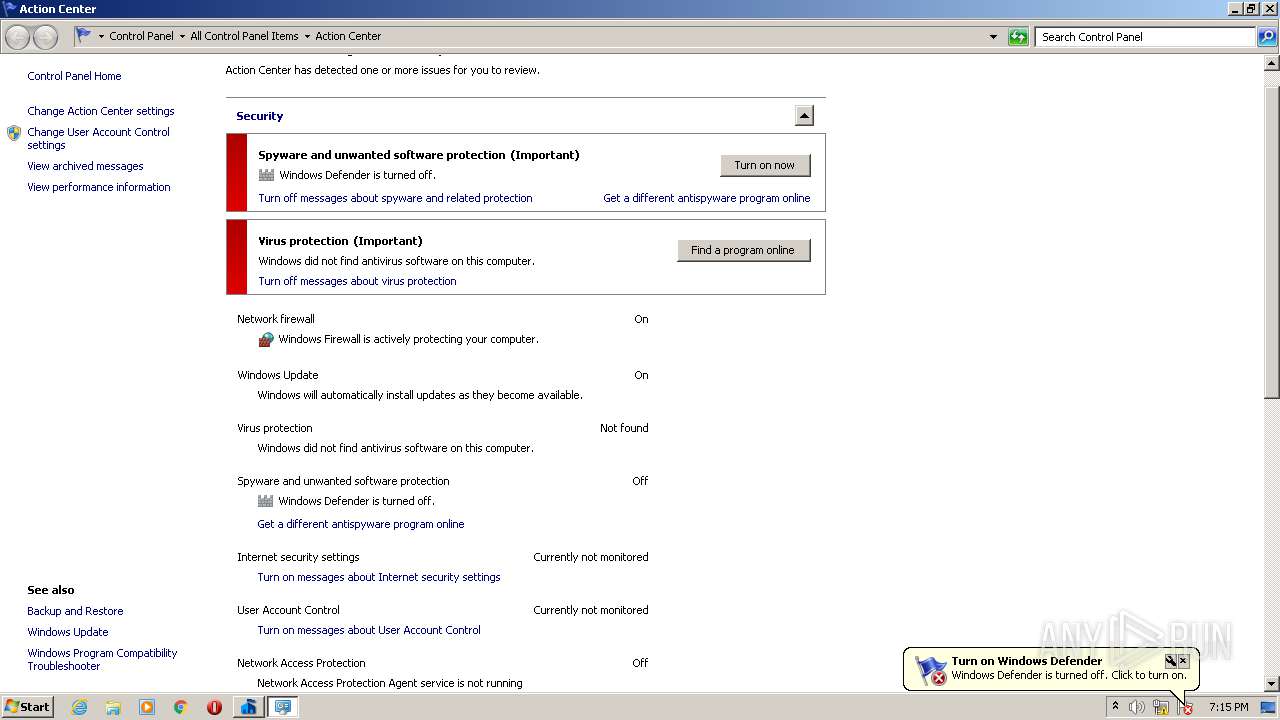
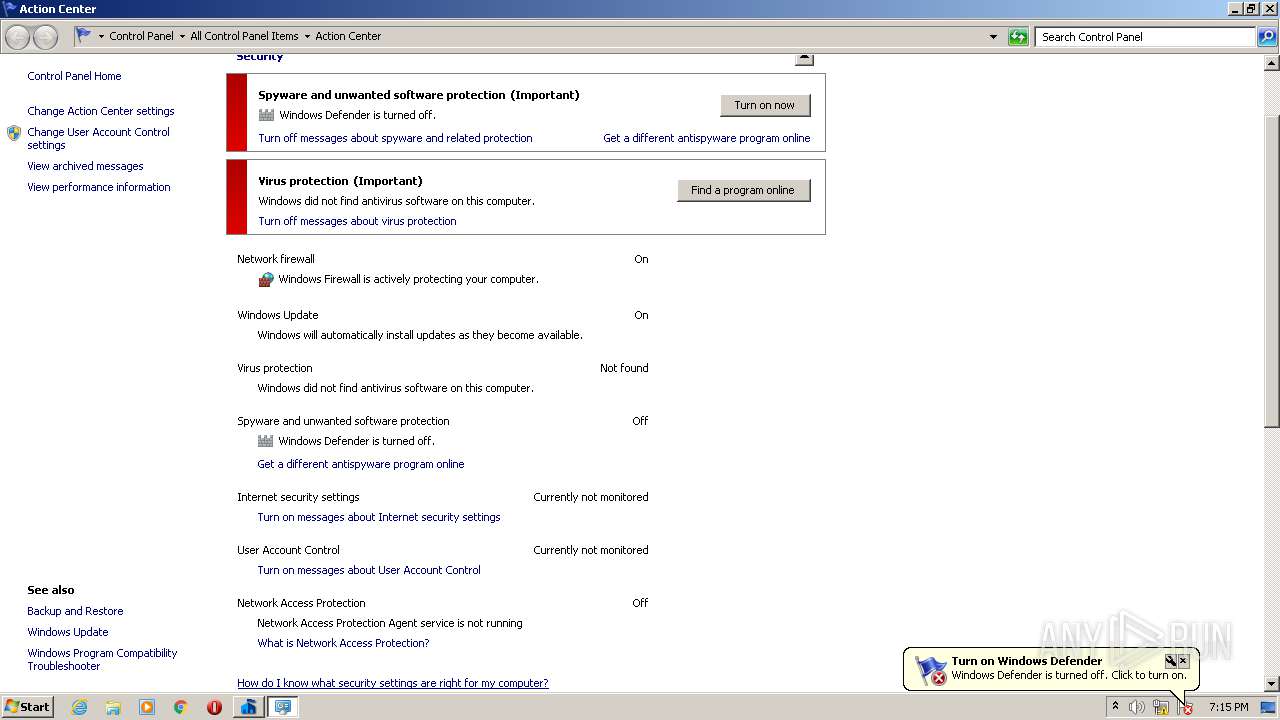
| Verdict: | Malicious activity |
| Analysis date: | April 03, 2021, 18:14:41 |
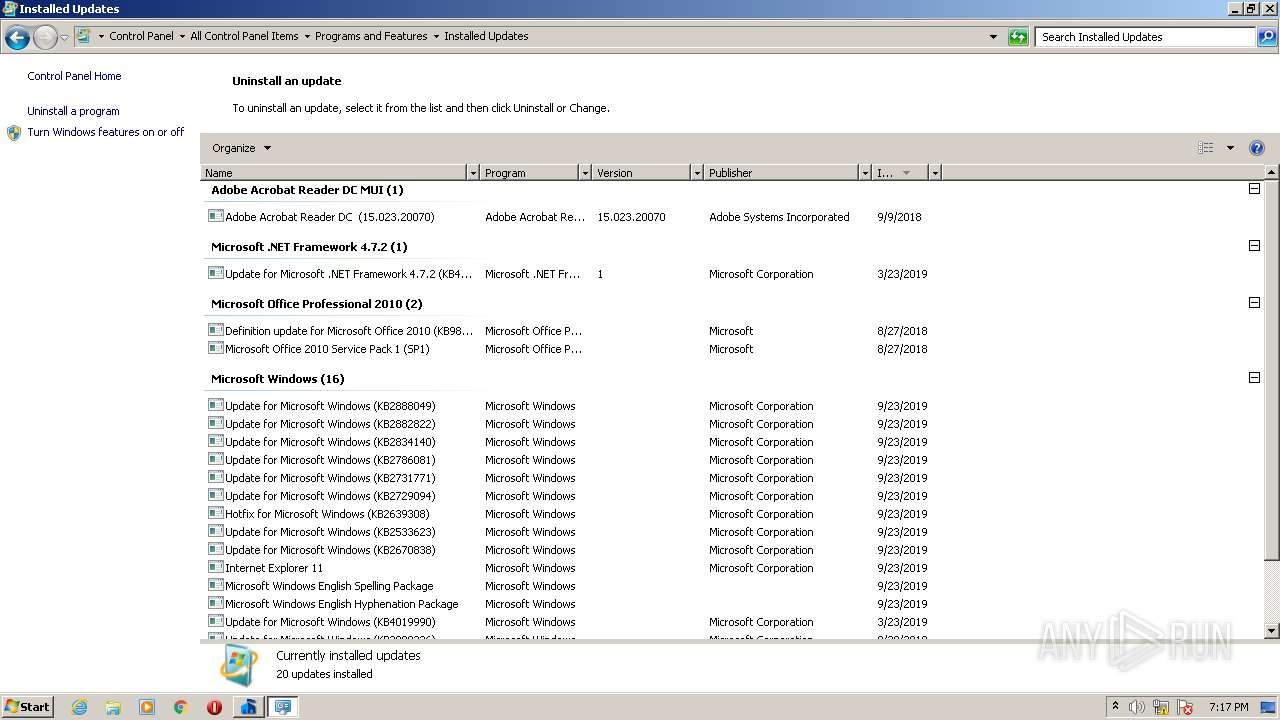
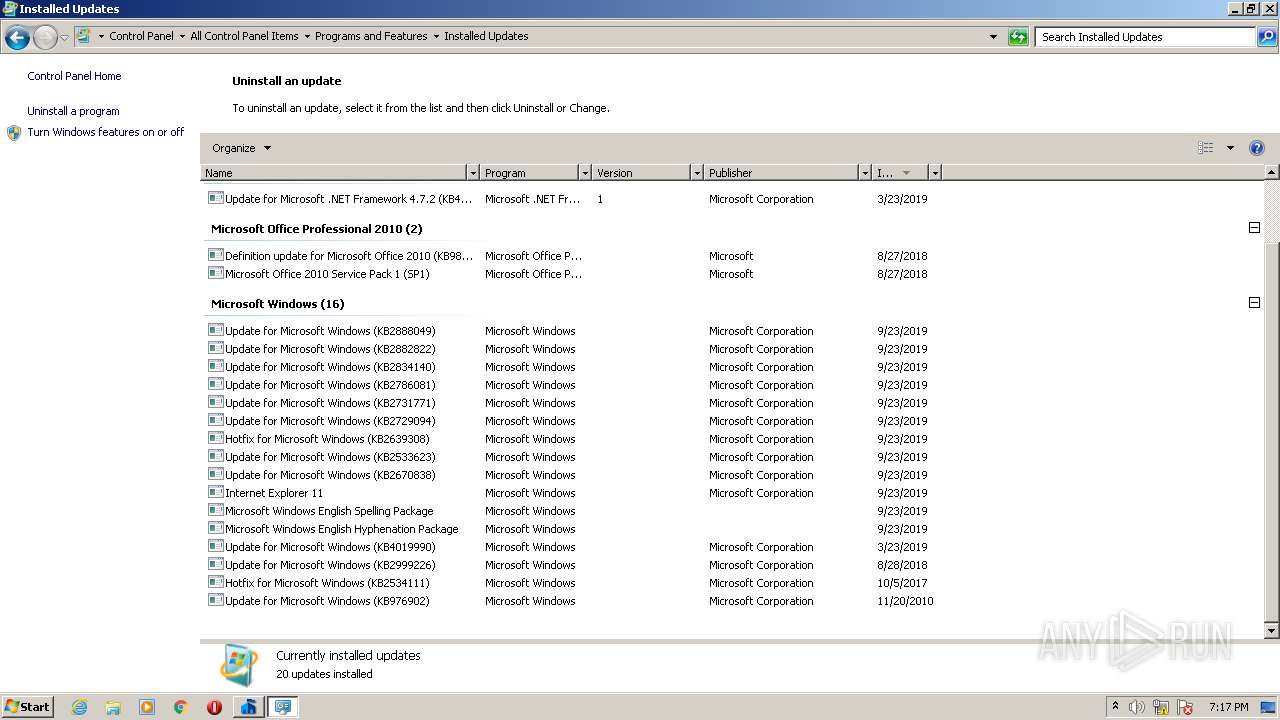
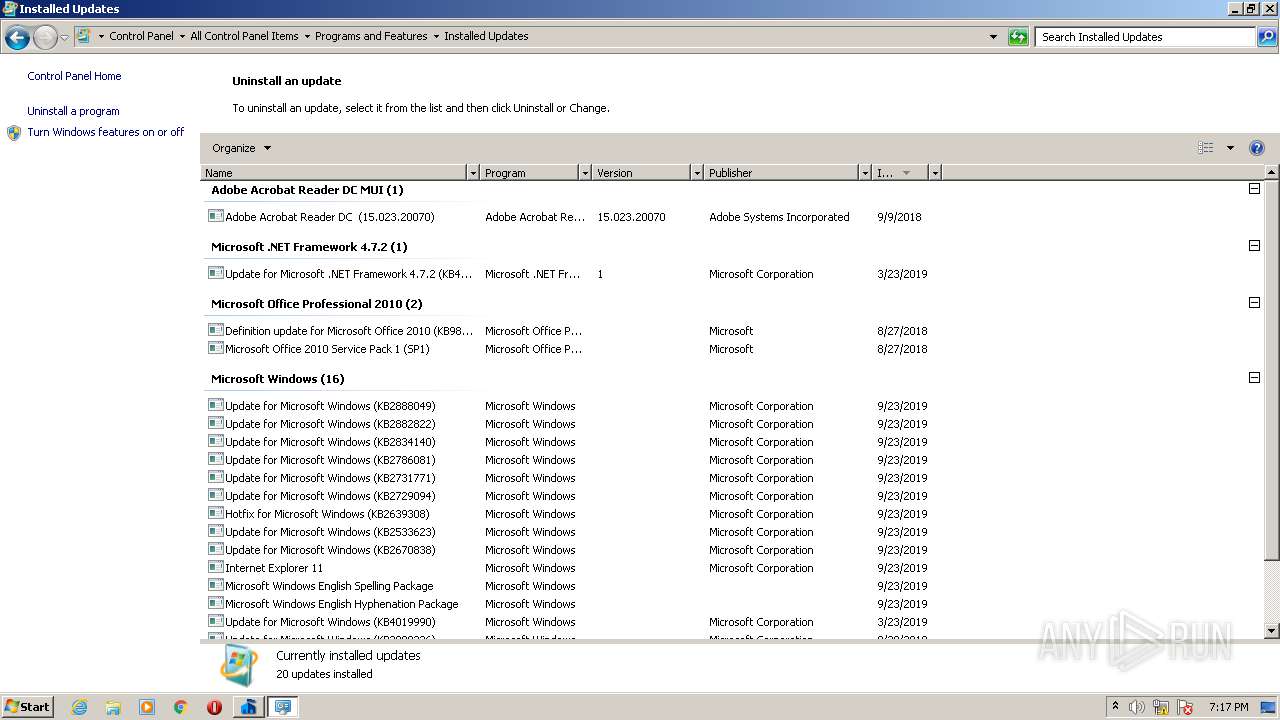
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, InstallShield self-extracting archive |
| MD5: | 2819435A97EB2A8691C2AF5344A5BD5C |
| SHA1: | E2851DBD248980569E46CE1E8F21D2ACFF759ADF |
| SHA256: | EA424A1EE2219BC61ACC2877B0C1DAE2C96B30BDD3B9322915F3DC60456E8E00 |
| SSDEEP: | 196608:ByLHbnHLu/LXuyrY39I4yD0cPaxah+31vaKDqw2vldbDb1AQ/0HgamIM1p:BubnHKy1IRgiM0KDRWdHCQ/eQIG |
MALICIOUS
Drops executable file immediately after starts
- MSEInstall.exe (PID: 4076)
- msdt.exe (PID: 3692)
Loads dropped or rewritten executable
- Setup.exe (PID: 3520)
Application was dropped or rewritten from another process
- Setup.exe (PID: 3520)
- epplauncher.exe (PID: 2396)
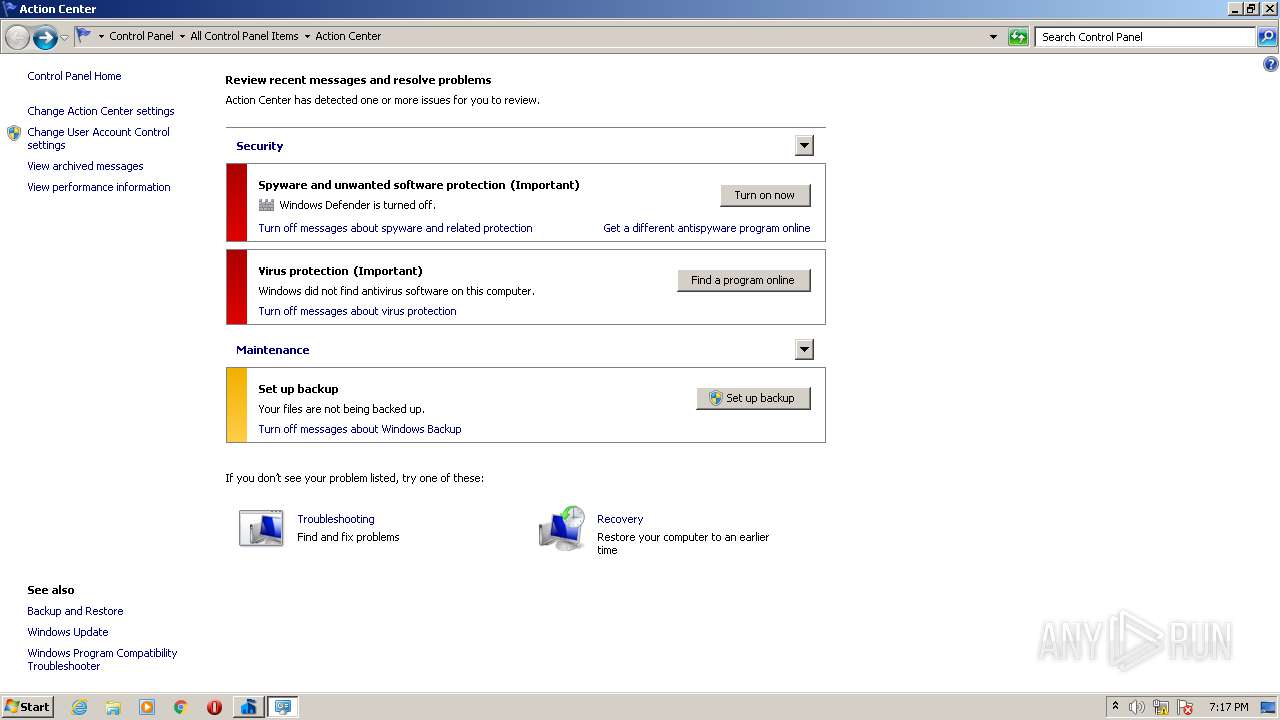
Actions looks like stealing of personal data
- epplauncher.exe (PID: 2396)
SUSPICIOUS
Executable content was dropped or overwritten
- MSEInstall.exe (PID: 4076)
- msdt.exe (PID: 3692)
Executed via COM
- DllHost.exe (PID: 1752)
- DllHost.exe (PID: 3148)
- sdiagnhost.exe (PID: 2516)
- sdiagnhost.exe (PID: 1360)
Drops a file with too old compile date
- MSEInstall.exe (PID: 4076)
- msdt.exe (PID: 3692)
Drops a file that was compiled in debug mode
- MSEInstall.exe (PID: 4076)
Creates files in the program directory
- Setup.exe (PID: 3520)
- epplauncher.exe (PID: 2396)
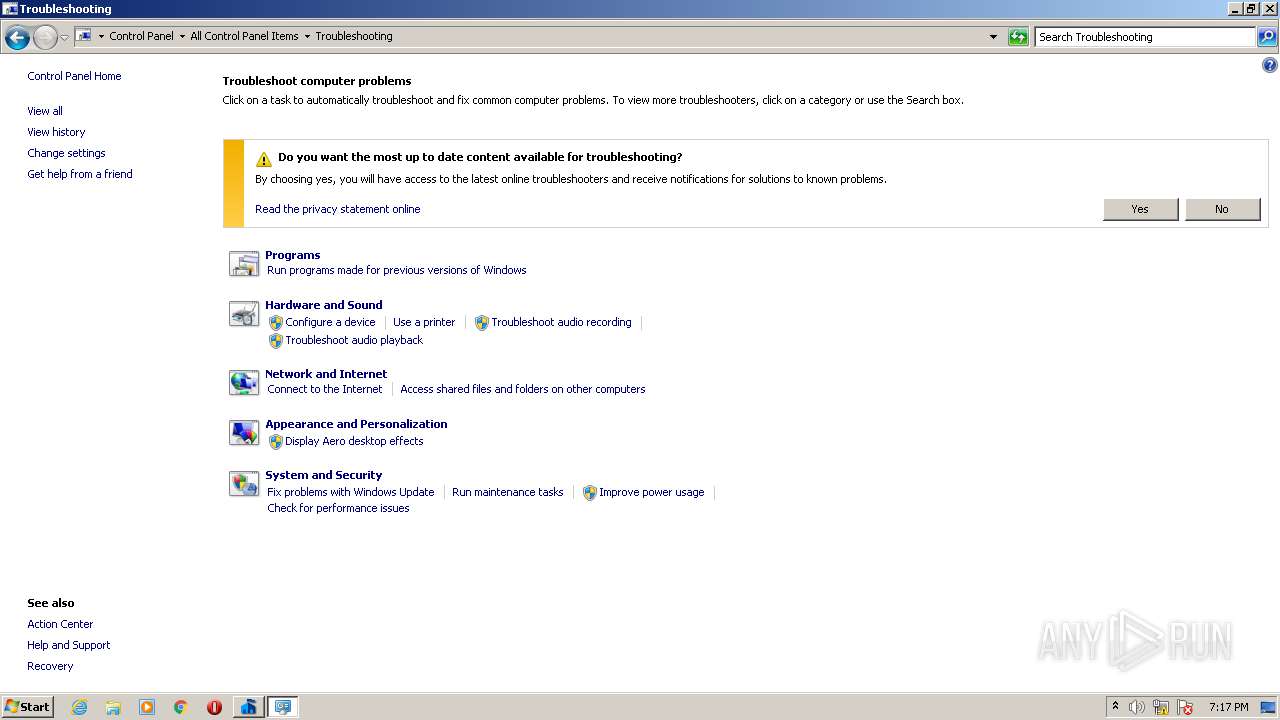
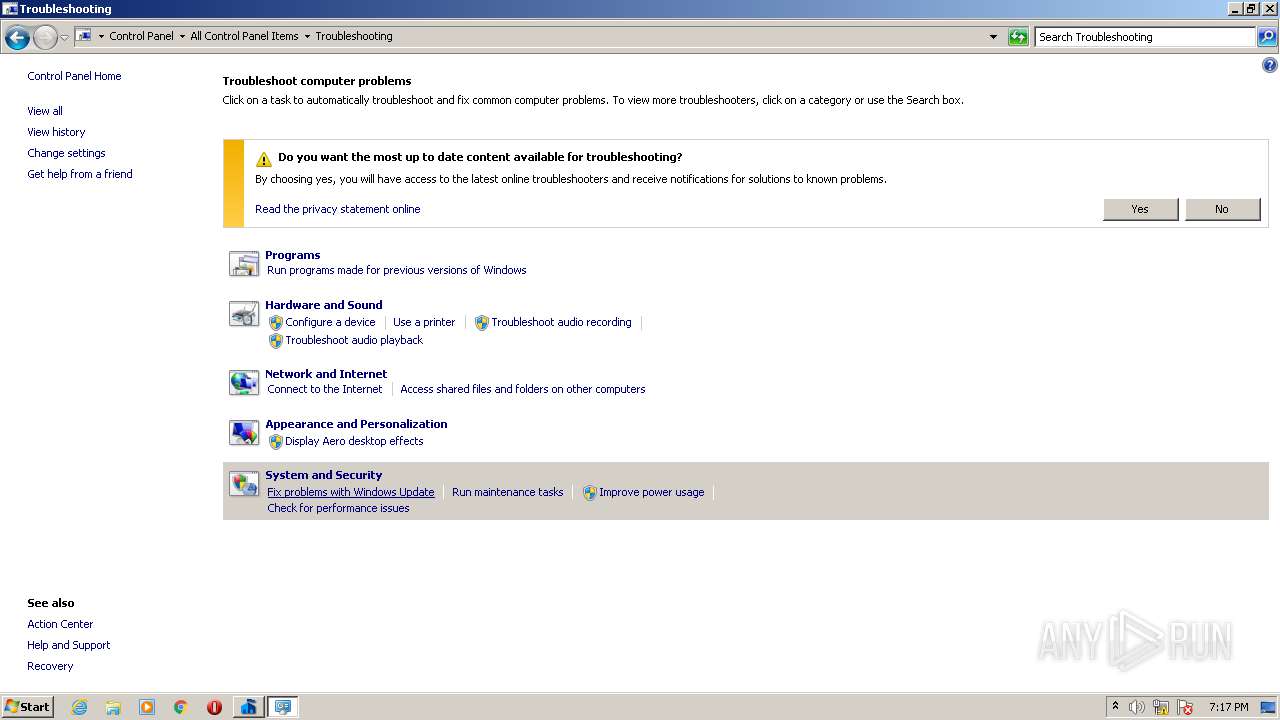
Uses IPCONFIG.EXE to discover IP address
- sdiagnhost.exe (PID: 2516)
Executed as Windows Service
- vssvc.exe (PID: 2148)
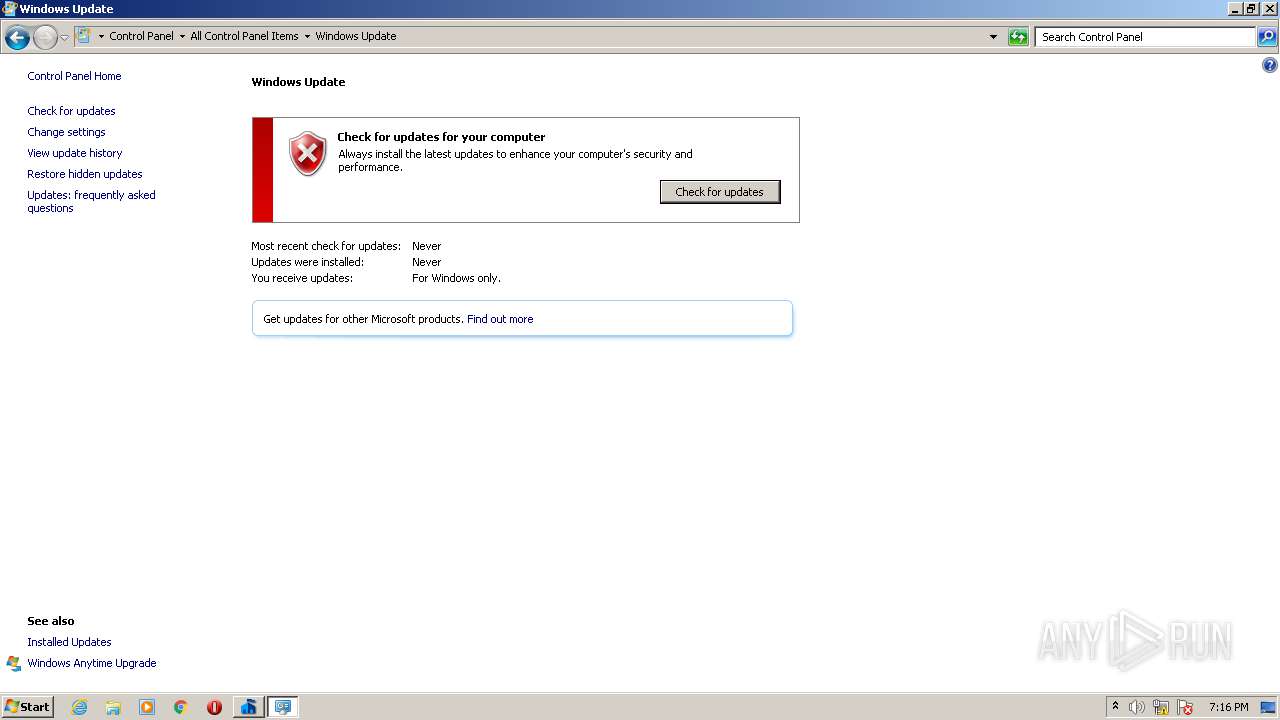
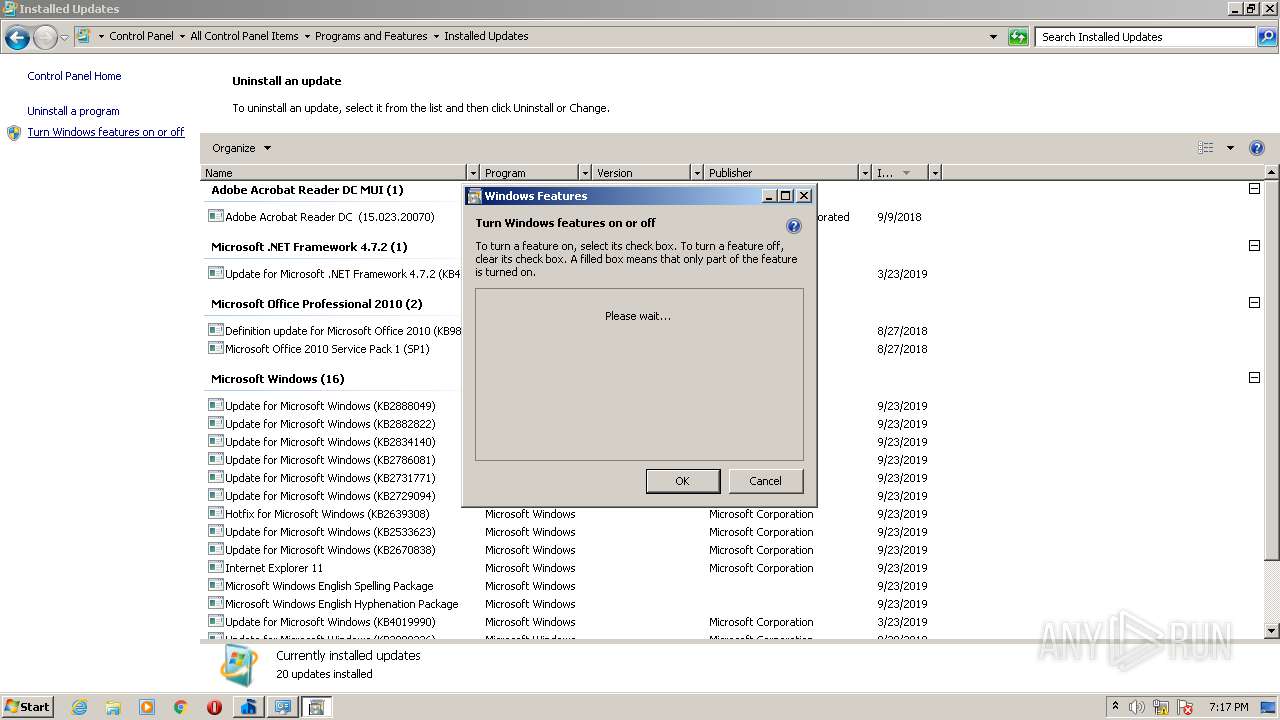
INFO
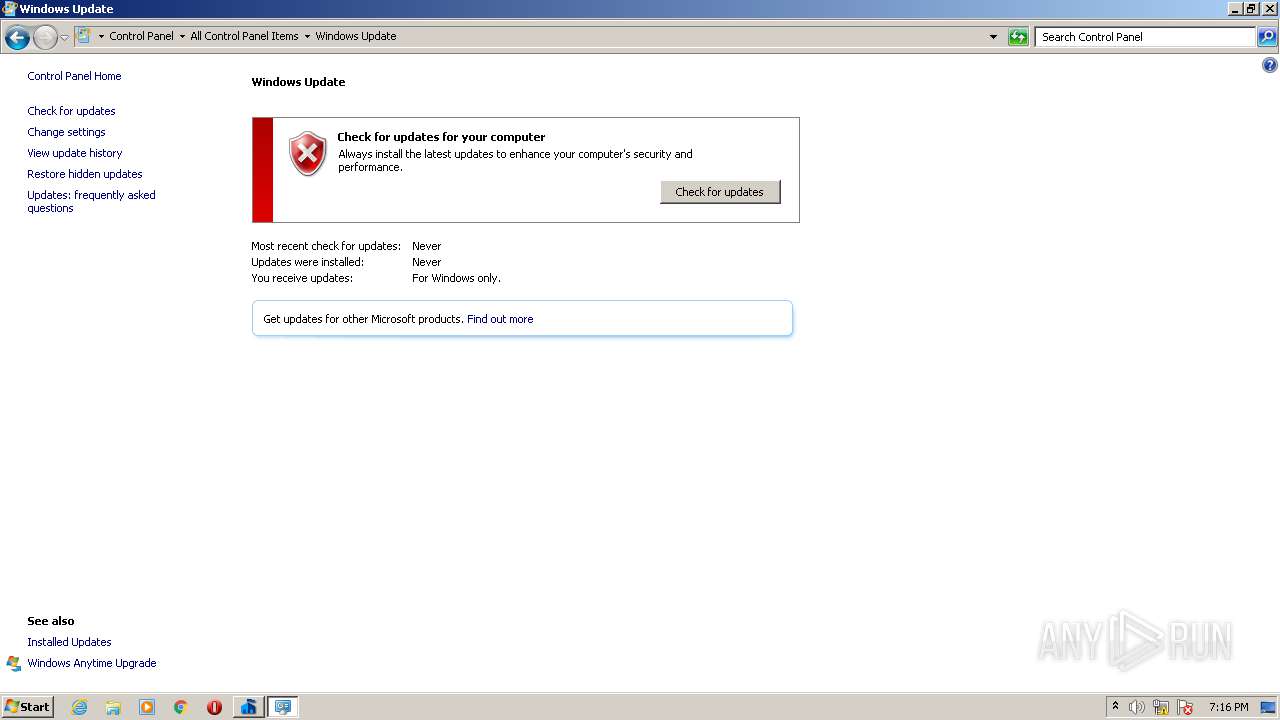
Application launched itself
- iexplore.exe (PID: 1516)
Changes internet zones settings
- iexplore.exe (PID: 1516)
Manual execution by user
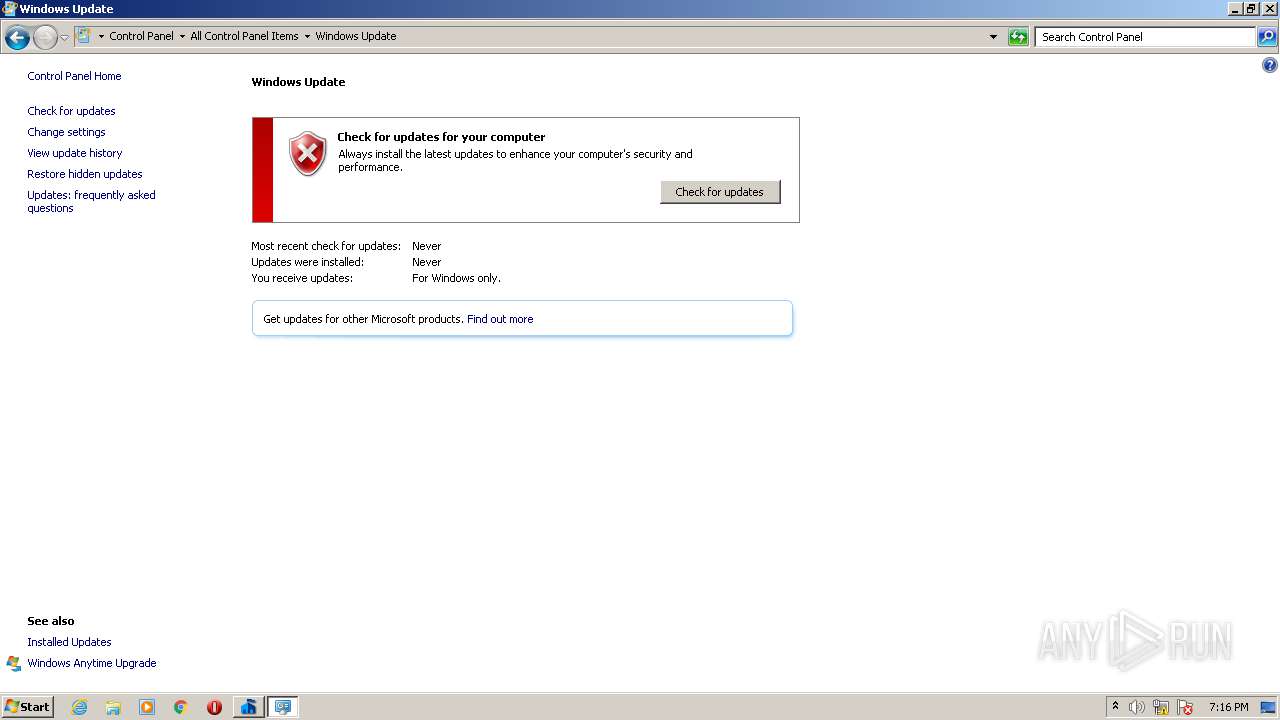
- iexplore.exe (PID: 1516)
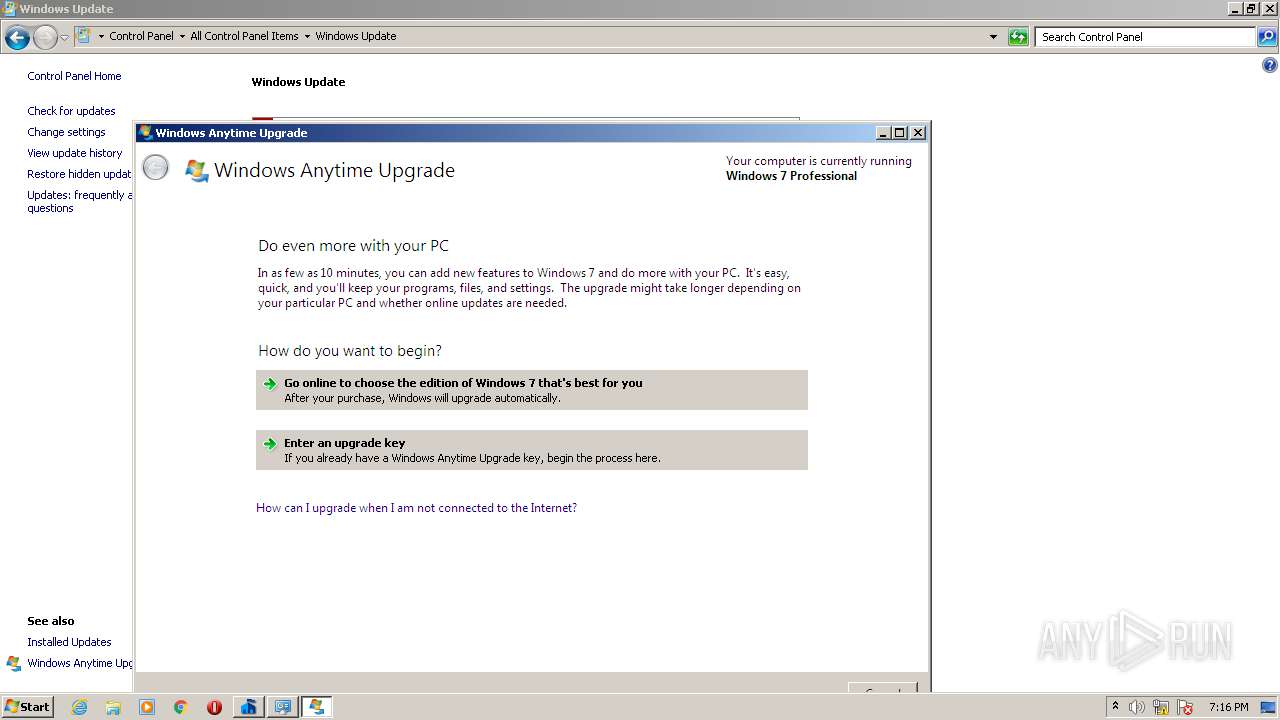
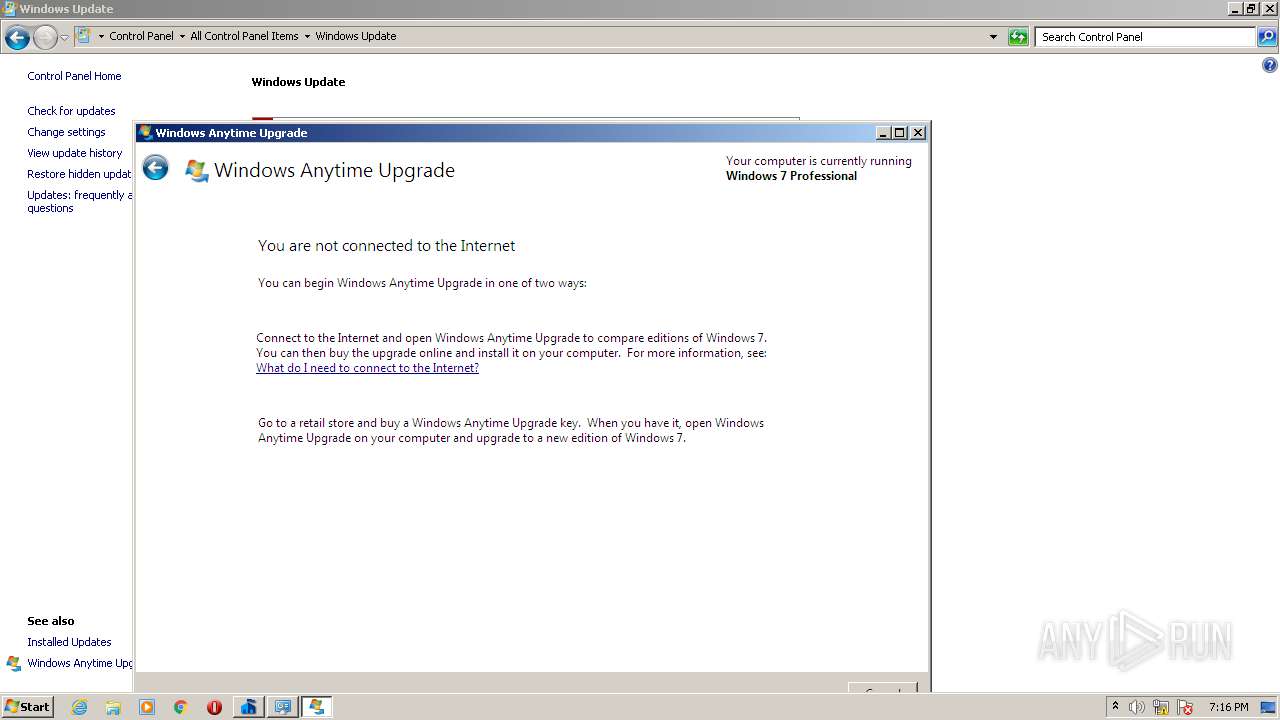
- windowsanytimeupgradeui.exe (PID: 3136)
- rundll32.exe (PID: 3544)
- msdt.exe (PID: 3692)
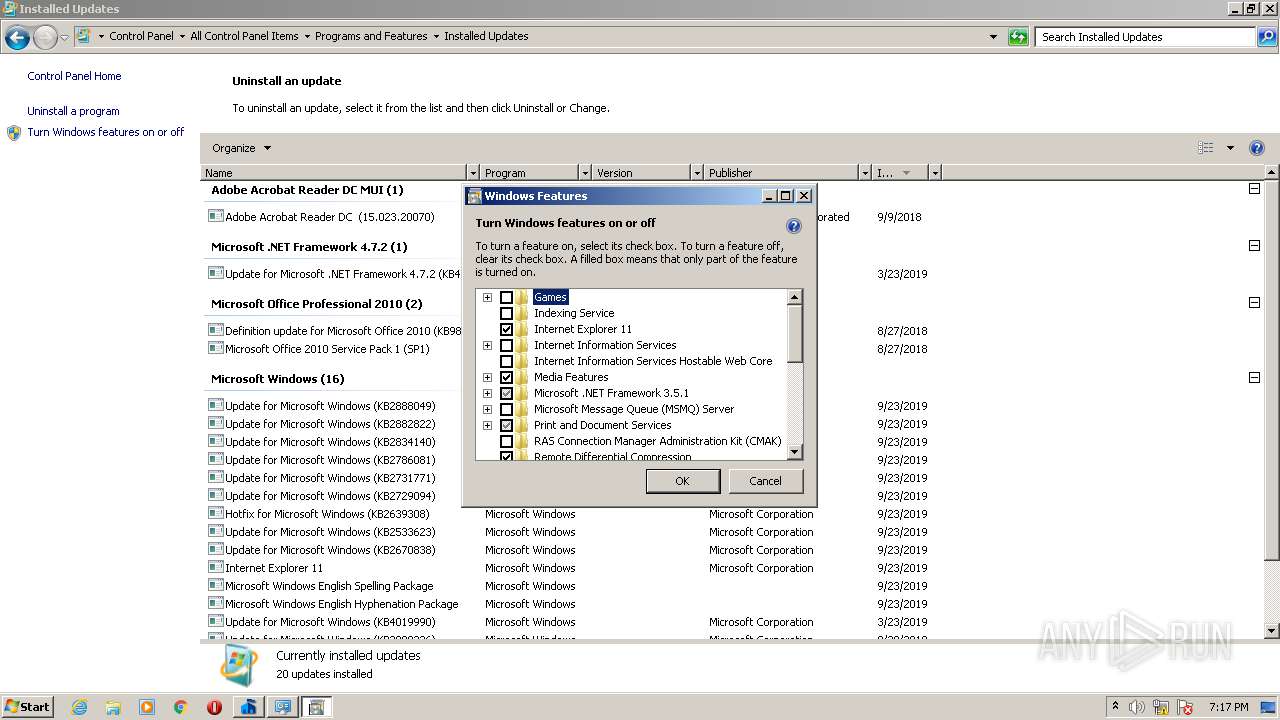
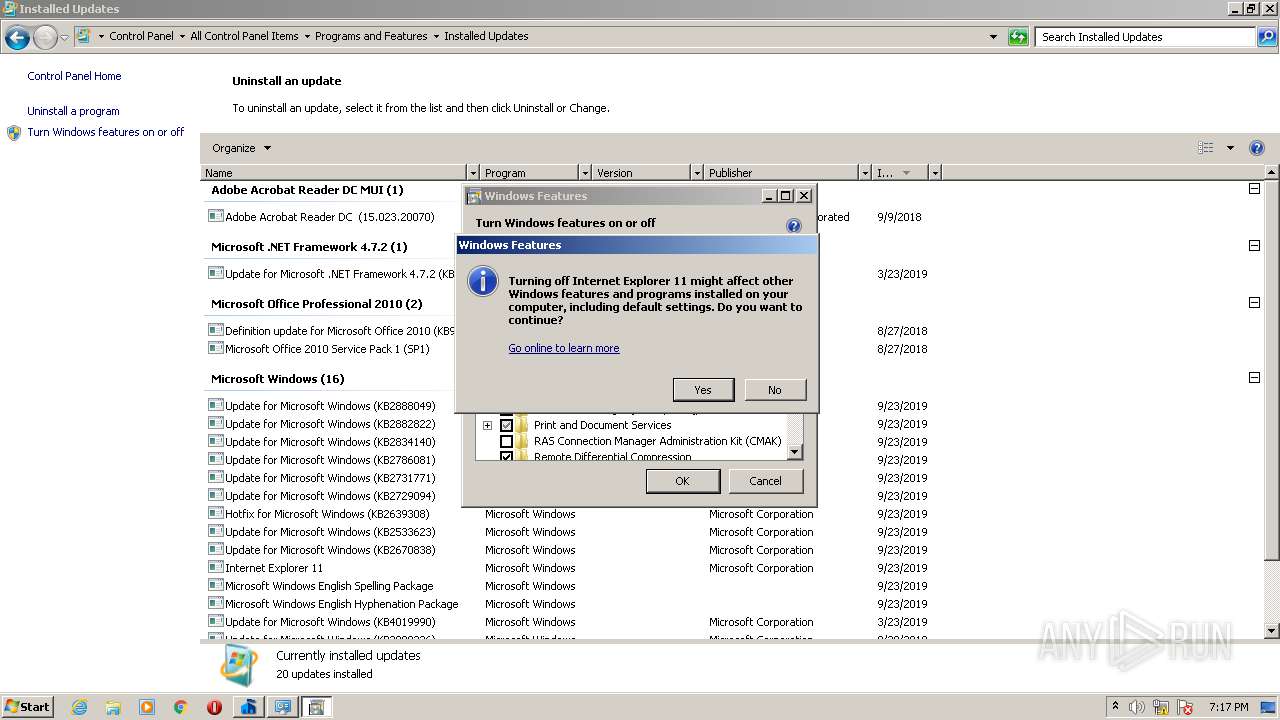
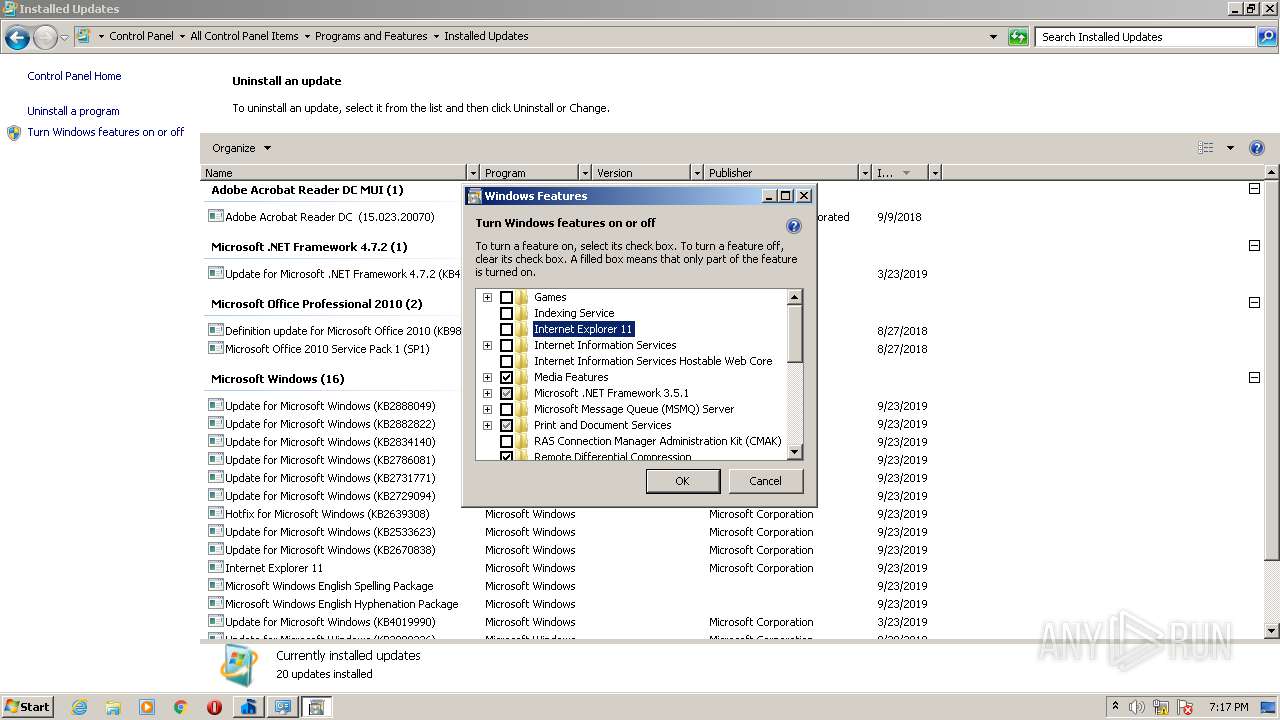
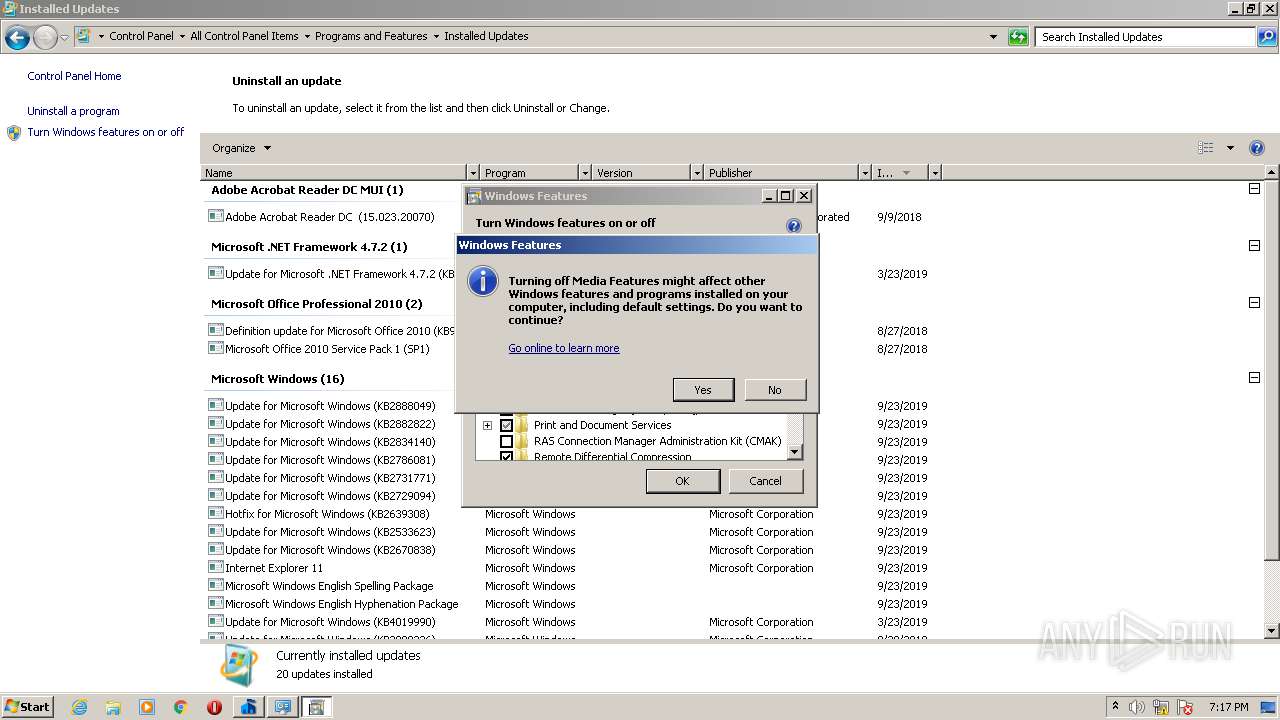
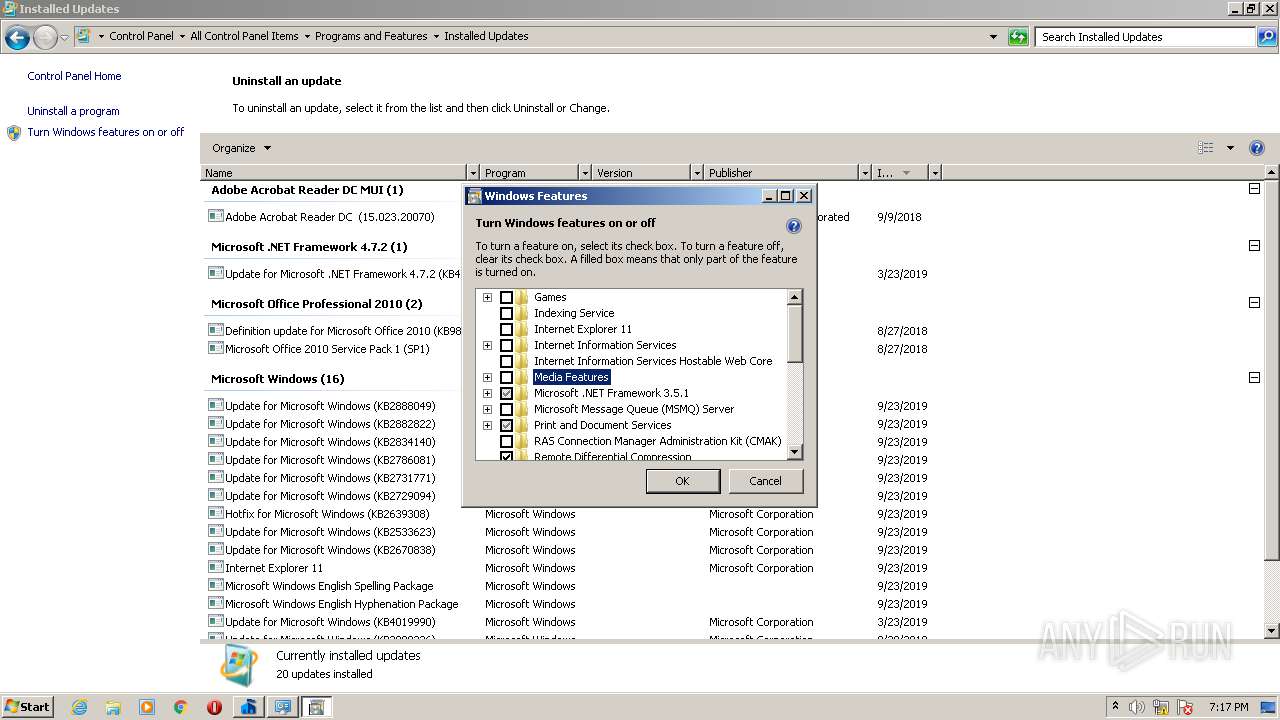
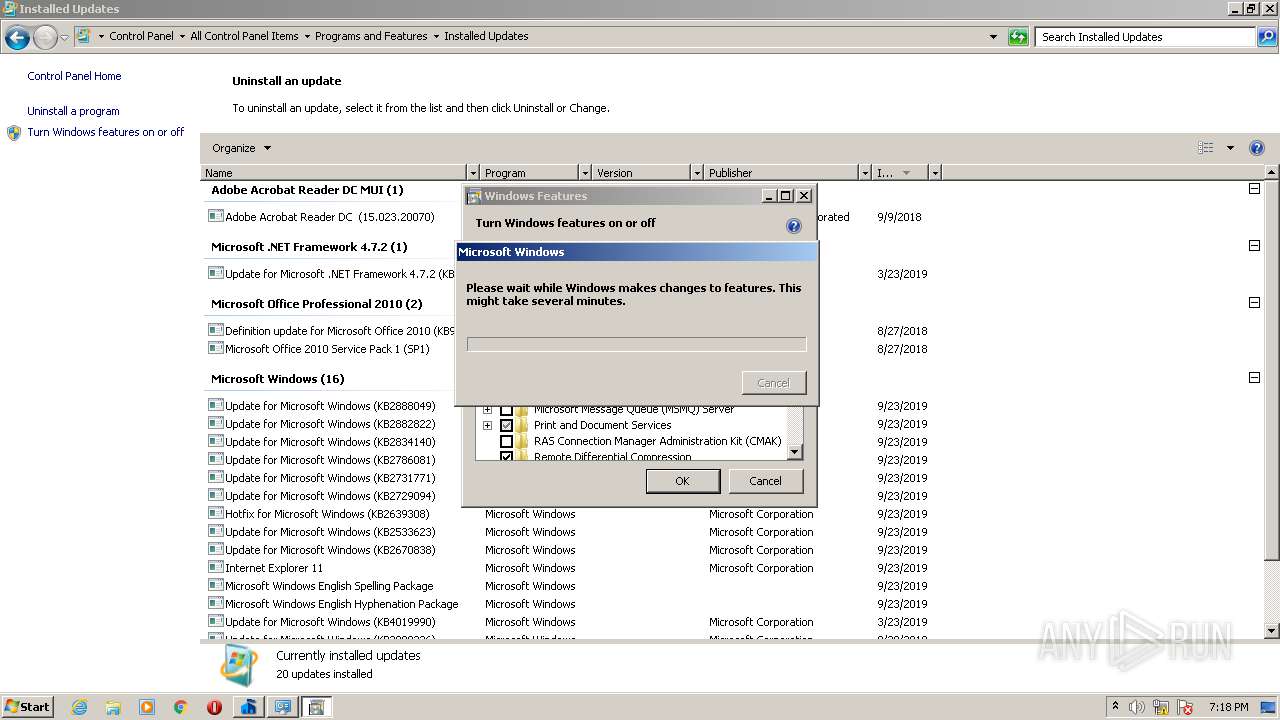
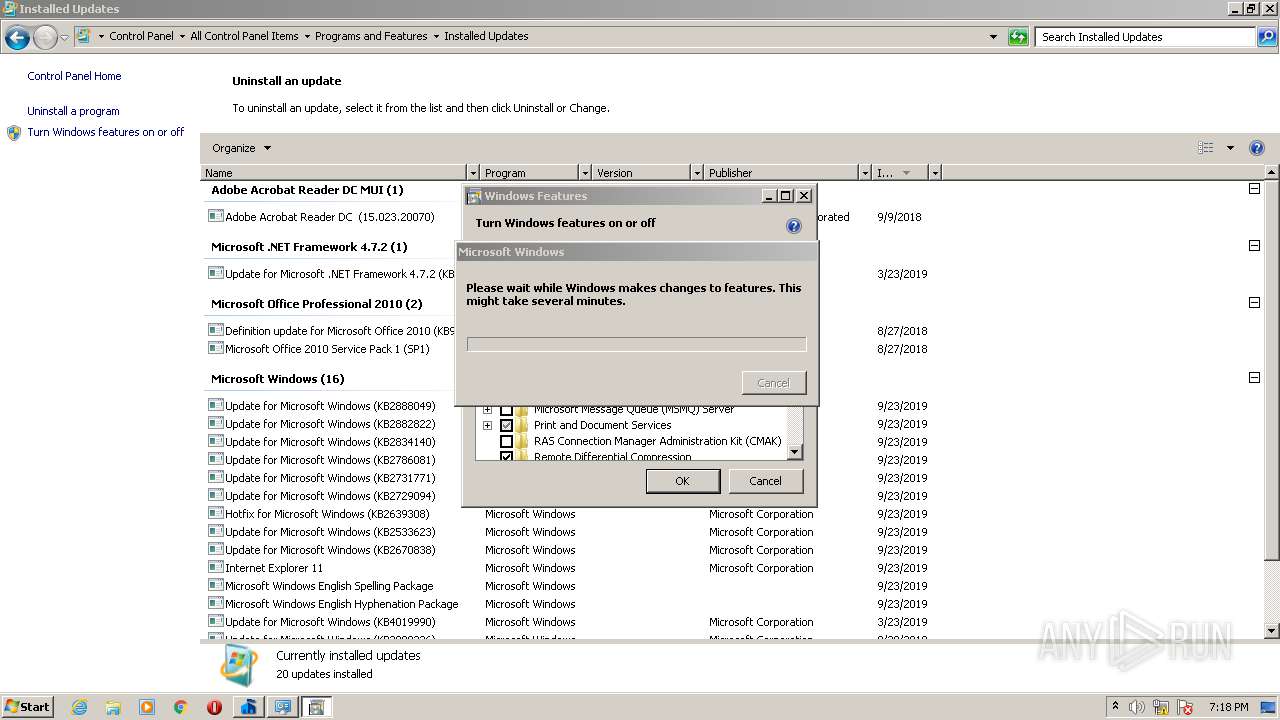
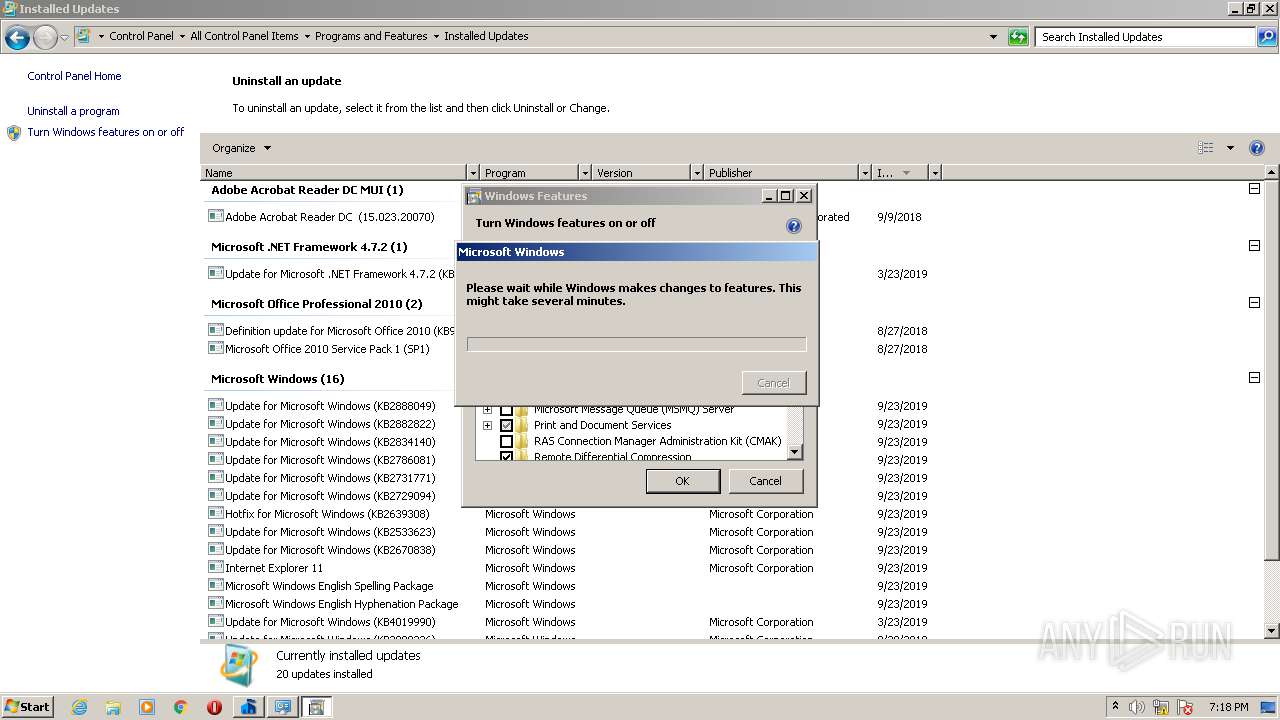
- OptionalFeatures.exe (PID: 548)
- OptionalFeatures.exe (PID: 2596)
Changes settings of System certificates
- iexplore.exe (PID: 1516)
Reads settings of System Certificates
- iexplore.exe (PID: 856)
- iexplore.exe (PID: 1516)
- msdt.exe (PID: 3692)
Reads internet explorer settings
- iexplore.exe (PID: 856)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1516)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | MS generic-sfx Cabinet File Unpacker (32/64bit MSCFU) (82.5) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (7.3) |
| .exe | | | Win64 Executable (generic) (6.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.5) |
| .exe | | | Win32 Executable (generic) (1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:03:13 07:51:25+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 7.1 |
| CodeSize: | 35840 |
| InitializedDataSize: | 300032 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6b23 |
| OSVersion: | 5.2 |
| ImageVersion: | 5.2 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.10.209.0 |
| ProductVersionNumber: | 4.10.209.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | MSEInstall Package |
| FileVersion: | 4.10.0209.0 |
| InternalName: | MSEInstall.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | MSEInstall.exe |
| ProductName: | Microsoft Security Client |
| ProductVersion: | 4.10.0209.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Mar-2009 06:51:25 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | MSEInstall Package |
| FileVersion: | 4.10.0209.0 |
| InternalName: | MSEInstall.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | MSEInstall.exe |
| ProductName: | Microsoft Security Client |
| ProductVersion: | 4.10.0209.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 13-Mar-2009 06:51:25 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00008B08 | 0x00008C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.53364 |
.data | 0x0000C000 | 0x00011438 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.519063 |
.rsrc | 0x0001E000 | 0x000491D4 | 0x00049200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.03435 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 1.5 | 4 | Latin 1 / Western European | English - United States | UNKNOWN |
2 | 3.84176 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.96352 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.48788 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.99442 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.58633 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 4.94629 | 270376 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 5.41932 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 5.4847 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 4.86767 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
msvcrt.dll |
ntdll.dll |
Total processes
72
Monitored processes
19
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 548 | "C:\Windows\system32\OptionalFeatures.exe" | C:\Windows\system32\OptionalFeatures.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Features Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 856 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1516 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1360 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1516 | "C:\Program Files\Internet Explorer\iexplore.exe" http://go.microsoft.com/fwlink/?LinkId=70156 | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1752 | C:\Windows\system32\DllHost.exe /Processid:{E9495B87-D950-4AB5-87A5-FF6D70BF3E90} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2148 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2396 | c:\0bd122434cc3ccfb7bd3512d\epplauncher.exe | c:\0bd122434cc3ccfb7bd3512d\epplauncher.exe | MSEInstall.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Security Client Launcher Exit code: 0 Version: 4.10.0209.0 Modules
| |||||||||||||||
| 2516 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2596 | "C:\Windows\system32\OptionalFeatures.exe" | C:\Windows\system32\OptionalFeatures.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Features Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2880 | "C:\Users\admin\AppData\Local\Temp\MSEInstall.exe" | C:\Users\admin\AppData\Local\Temp\MSEInstall.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSEInstall Package Exit code: 3221226540 Version: 4.10.0209.0 Modules
| |||||||||||||||
Total events
1 132
Read events
908
Write events
221
Delete events
3
Modification events
| (PID) Process: | (2396) epplauncher.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3520) Setup.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2201137845 | |||
| (PID) Process: | (1516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30877877 | |||
| (PID) Process: | (1516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
Executable files
17
Suspicious files
25
Text files
65
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4076 | MSEInstall.exe | C:\0bd122434cc3ccfb7bd3512d\x86\epp.msi | — | |
MD5:— | SHA256:— | |||
| 4076 | MSEInstall.exe | C:\0bd122434cc3ccfb7bd3512d\epplauncher.exe | executable | |
MD5:C9E82C0B2083B76AD7F5631E4A52609C | SHA256:482DA7FFC6AD64B0307E6A7B0C1D77A60BC07ECA878E663F42ABCF4D02A51C63 | |||
| 4076 | MSEInstall.exe | C:\0bd122434cc3ccfb7bd3512d\x86\dw20shared.msi | executable | |
MD5:77FF64A620134E5FF8D36FD660E990D2 | SHA256:4BB16ECA7DD0BDDA7148D336F9739B8FD4CABF7D68E4086F36607952BC2931B6 | |||
| 856 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab3282.tmp | — | |
MD5:— | SHA256:— | |||
| 856 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar3283.tmp | — | |
MD5:— | SHA256:— | |||
| 3520 | Setup.exe | C:\ProgramData\Microsoft\Microsoft Security Client\Support\EppSetupResult.ini | text | |
MD5:— | SHA256:— | |||
| 856 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\696F3DE637E6DE85B458996D49D759AD | binary | |
MD5:— | SHA256:— | |||
| 856 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\696F3DE637E6DE85B458996D49D759AD | der | |
MD5:— | SHA256:— | |||
| 856 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\3CBD32CA8C115321DC0C0A19D8C07886 | der | |
MD5:— | SHA256:— | |||
| 4076 | MSEInstall.exe | C:\0bd122434cc3ccfb7bd3512d\EN-US\EULA.RTF | text | |
MD5:740190A5BBE59302CE8C02858FE384CC | SHA256:D0A2577D3BB5E38A8EBBF028E20030D8D4314CEF9E7388D6FE048B38A173E94D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
35
DNS requests
17
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | iexplore.exe | GET | 302 | 104.111.242.51:80 | http://go.microsoft.com/fwlink/?LinkId=70156 | NL | — | — | whitelisted |
— | — | HEAD | 200 | 93.184.221.240:80 | http://download.windowsupdate.com/v9/windowsupdate/redir/muv4wuredir.cab?2104031815 | US | — | — | whitelisted |
856 | iexplore.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | der | 781 b | whitelisted |
856 | iexplore.exe | GET | 200 | 2.18.233.62:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Secure%20Server%20CA%201.crl | unknown | der | 818 b | whitelisted |
1516 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
856 | iexplore.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | der | 781 b | whitelisted |
1516 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
856 | iexplore.exe | GET | 200 | 2.18.233.62:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Secure%20Server%20CA%201.crl | unknown | der | 818 b | whitelisted |
1516 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
1516 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQQX6Z6gAidtSefNc6DC0OInqPHDQQUD4BhHIIxYdUvKOeNRji0LOHG2eICEA8aVkWYLIkXQFXHYN8Oxso%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 93.184.221.240:80 | download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
856 | iexplore.exe | 104.111.242.51:80 | go.microsoft.com | Akamai International B.V. | NL | unknown |
— | — | 40.70.224.146:443 | www.update.microsoft.com | Microsoft Corporation | US | malicious |
856 | iexplore.exe | 2.16.186.74:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
856 | iexplore.exe | 40.70.224.146:443 | www.update.microsoft.com | Microsoft Corporation | US | malicious |
856 | iexplore.exe | 2.18.233.62:80 | www.microsoft.com | Akamai International B.V. | — | whitelisted |
1516 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1516 | iexplore.exe | 40.70.224.146:443 | www.update.microsoft.com | Microsoft Corporation | US | malicious |
1516 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
832 | svchost.exe | 104.79.89.142:80 | www.microsoft.com | Time Warner Cable Internet LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.windowsupdate.com |
| whitelisted |
www.update.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
update.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report