| File name: | Teleport_external.exe |
| Full analysis: | https://app.any.run/tasks/017cf819-d97e-4a7d-a320-13cc10c16ffd |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 00:48:45 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 6 sections |
| MD5: | B3AEF8D48BBB9E6DE7C0E852063F1A03 |
| SHA1: | 5186FDA2EE8A50B7651E5EBCAE041F45820A4C33 |
| SHA256: | EA274E4C736937FF88714604C2ECB9CD4BE65058468E2C6AF6771EC6DAB4479F |
| SSDEEP: | 24576:cAaGzRHX9CyFsgjDBUsr7fnFqS2UnV4jAk:xdzRHX9CyFsgXBUu7fYSZn/k |
MALICIOUS
Uses TASKKILL.EXE to kill security tools
- cmd.exe (PID: 5332)
- cmd.exe (PID: 536)
- cmd.exe (PID: 6744)
- cmd.exe (PID: 5640)
- cmd.exe (PID: 6644)
- cmd.exe (PID: 2108)
- cmd.exe (PID: 7384)
- cmd.exe (PID: 7604)
- cmd.exe (PID: 6040)
- cmd.exe (PID: 7840)
- cmd.exe (PID: 8112)
- cmd.exe (PID: 7820)
- cmd.exe (PID: 7880)
- cmd.exe (PID: 8116)
- cmd.exe (PID: 7432)
- cmd.exe (PID: 7300)
- cmd.exe (PID: 8172)
- cmd.exe (PID: 7956)
Starts NET.EXE for service management
- cmd.exe (PID: 1812)
- cmd.exe (PID: 5640)
- net.exe (PID: 2564)
- net.exe (PID: 1188)
- net.exe (PID: 4408)
- cmd.exe (PID: 2384)
- cmd.exe (PID: 7148)
- net.exe (PID: 7152)
- net.exe (PID: 7292)
- cmd.exe (PID: 7296)
- net.exe (PID: 7376)
- cmd.exe (PID: 5204)
- cmd.exe (PID: 6272)
- net.exe (PID: 7756)
- cmd.exe (PID: 7532)
- net.exe (PID: 7440)
- cmd.exe (PID: 7460)
- net.exe (PID: 7544)
- cmd.exe (PID: 7228)
- net.exe (PID: 8136)
SUSPICIOUS
Hides command output
- cmd.exe (PID: 536)
- cmd.exe (PID: 5640)
- cmd.exe (PID: 5332)
- cmd.exe (PID: 1812)
- cmd.exe (PID: 5608)
- cmd.exe (PID: 1228)
- cmd.exe (PID: 7148)
- cmd.exe (PID: 2384)
- cmd.exe (PID: 2152)
- cmd.exe (PID: 5072)
- cmd.exe (PID: 2384)
- cmd.exe (PID: 5892)
- cmd.exe (PID: 6272)
- cmd.exe (PID: 5640)
- cmd.exe (PID: 2152)
- cmd.exe (PID: 5344)
- cmd.exe (PID: 3100)
- cmd.exe (PID: 5640)
- cmd.exe (PID: 1072)
- cmd.exe (PID: 6744)
- cmd.exe (PID: 7848)
- cmd.exe (PID: 5640)
- cmd.exe (PID: 7184)
- cmd.exe (PID: 7180)
- cmd.exe (PID: 7280)
- cmd.exe (PID: 1672)
- cmd.exe (PID: 7296)
- cmd.exe (PID: 7200)
- cmd.exe (PID: 2108)
- cmd.exe (PID: 6644)
- cmd.exe (PID: 8144)
- cmd.exe (PID: 7472)
- cmd.exe (PID: 7672)
- cmd.exe (PID: 7452)
- cmd.exe (PID: 7792)
- cmd.exe (PID: 7956)
- cmd.exe (PID: 7924)
- cmd.exe (PID: 7652)
- cmd.exe (PID: 7692)
- cmd.exe (PID: 7992)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 8088)
- cmd.exe (PID: 7724)
- cmd.exe (PID: 7920)
- cmd.exe (PID: 7608)
- cmd.exe (PID: 7600)
- cmd.exe (PID: 7384)
- cmd.exe (PID: 5204)
- cmd.exe (PID: 7296)
- cmd.exe (PID: 7740)
- cmd.exe (PID: 7568)
- cmd.exe (PID: 7520)
- cmd.exe (PID: 7536)
- cmd.exe (PID: 7604)
- cmd.exe (PID: 7452)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 6040)
- cmd.exe (PID: 7260)
- cmd.exe (PID: 7692)
- cmd.exe (PID: 3768)
- cmd.exe (PID: 7880)
- cmd.exe (PID: 5352)
- cmd.exe (PID: 3900)
- cmd.exe (PID: 7840)
- cmd.exe (PID: 7684)
- cmd.exe (PID: 8116)
- cmd.exe (PID: 744)
- cmd.exe (PID: 4464)
- cmd.exe (PID: 6228)
- cmd.exe (PID: 6468)
- cmd.exe (PID: 7368)
- cmd.exe (PID: 7196)
- cmd.exe (PID: 8056)
- cmd.exe (PID: 8076)
- cmd.exe (PID: 7500)
- cmd.exe (PID: 5116)
- cmd.exe (PID: 7288)
- cmd.exe (PID: 4528)
- cmd.exe (PID: 3956)
- cmd.exe (PID: 7532)
- cmd.exe (PID: 7224)
- cmd.exe (PID: 7404)
- cmd.exe (PID: 7820)
- cmd.exe (PID: 6272)
- cmd.exe (PID: 8112)
- cmd.exe (PID: 7460)
- cmd.exe (PID: 7928)
- cmd.exe (PID: 8116)
- cmd.exe (PID: 7868)
- cmd.exe (PID: 7880)
- cmd.exe (PID: 7228)
- cmd.exe (PID: 7876)
- cmd.exe (PID: 8156)
- cmd.exe (PID: 6676)
- cmd.exe (PID: 4068)
- cmd.exe (PID: 736)
- cmd.exe (PID: 5228)
- cmd.exe (PID: 6540)
- cmd.exe (PID: 3900)
- cmd.exe (PID: 1240)
- cmd.exe (PID: 7316)
- cmd.exe (PID: 1052)
- cmd.exe (PID: 3176)
- cmd.exe (PID: 5744)
- cmd.exe (PID: 5968)
- cmd.exe (PID: 8176)
- cmd.exe (PID: 8024)
- cmd.exe (PID: 7336)
- cmd.exe (PID: 7300)
- cmd.exe (PID: 4200)
- cmd.exe (PID: 6156)
- cmd.exe (PID: 728)
- cmd.exe (PID: 7628)
- cmd.exe (PID: 7812)
- cmd.exe (PID: 7432)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 7508)
- cmd.exe (PID: 2096)
- cmd.exe (PID: 6712)
- cmd.exe (PID: 8172)
- cmd.exe (PID: 7956)
- cmd.exe (PID: 6272)
- cmd.exe (PID: 7532)
- cmd.exe (PID: 6036)
- cmd.exe (PID: 7888)
- cmd.exe (PID: 2284)
- cmd.exe (PID: 7640)
- cmd.exe (PID: 7788)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 7228)
- cmd.exe (PID: 5228)
- cmd.exe (PID: 2644)
- cmd.exe (PID: 2852)
- cmd.exe (PID: 7428)
- cmd.exe (PID: 7000)
- cmd.exe (PID: 7824)
- cmd.exe (PID: 7828)
- cmd.exe (PID: 3268)
- cmd.exe (PID: 728)
- cmd.exe (PID: 780)
- cmd.exe (PID: 7916)
- cmd.exe (PID: 7312)
- cmd.exe (PID: 5744)
- cmd.exe (PID: 7396)
- cmd.exe (PID: 4844)
- cmd.exe (PID: 7440)
- cmd.exe (PID: 8184)
- cmd.exe (PID: 7768)
- cmd.exe (PID: 7260)
- cmd.exe (PID: 7476)
- cmd.exe (PID: 8160)
- cmd.exe (PID: 7580)
- cmd.exe (PID: 7764)
- cmd.exe (PID: 5436)
- cmd.exe (PID: 2040)
- cmd.exe (PID: 3008)
- cmd.exe (PID: 6272)
- cmd.exe (PID: 720)
- cmd.exe (PID: 7708)
- cmd.exe (PID: 1676)
- cmd.exe (PID: 6032)
- cmd.exe (PID: 5352)
- cmd.exe (PID: 8048)
- cmd.exe (PID: 2092)
- cmd.exe (PID: 7304)
- cmd.exe (PID: 8144)
- cmd.exe (PID: 1240)
- cmd.exe (PID: 7388)
- cmd.exe (PID: 1132)
- cmd.exe (PID: 5324)
- cmd.exe (PID: 1300)
- cmd.exe (PID: 1672)
Starts SC.EXE for service management
- cmd.exe (PID: 2152)
- cmd.exe (PID: 5608)
- cmd.exe (PID: 5072)
- cmd.exe (PID: 5892)
- cmd.exe (PID: 1228)
- cmd.exe (PID: 5640)
- cmd.exe (PID: 2384)
- cmd.exe (PID: 6272)
- cmd.exe (PID: 1072)
- cmd.exe (PID: 3100)
- cmd.exe (PID: 2152)
- cmd.exe (PID: 5344)
- cmd.exe (PID: 7924)
- cmd.exe (PID: 7452)
- cmd.exe (PID: 7792)
- cmd.exe (PID: 7652)
- cmd.exe (PID: 7692)
- cmd.exe (PID: 7992)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 7608)
- cmd.exe (PID: 7600)
- cmd.exe (PID: 7724)
- cmd.exe (PID: 7920)
- cmd.exe (PID: 8088)
- cmd.exe (PID: 7568)
- cmd.exe (PID: 7740)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 7260)
- cmd.exe (PID: 7520)
- cmd.exe (PID: 7536)
- cmd.exe (PID: 7452)
- cmd.exe (PID: 3768)
- cmd.exe (PID: 7868)
- cmd.exe (PID: 7876)
- cmd.exe (PID: 8156)
- cmd.exe (PID: 4068)
- cmd.exe (PID: 1240)
- cmd.exe (PID: 3900)
- cmd.exe (PID: 6676)
- cmd.exe (PID: 736)
- cmd.exe (PID: 6540)
- cmd.exe (PID: 1052)
- cmd.exe (PID: 7316)
- cmd.exe (PID: 5228)
- cmd.exe (PID: 8024)
- cmd.exe (PID: 8176)
- cmd.exe (PID: 7336)
- cmd.exe (PID: 5968)
- cmd.exe (PID: 5744)
- cmd.exe (PID: 4200)
- cmd.exe (PID: 728)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 7508)
- cmd.exe (PID: 6712)
- cmd.exe (PID: 5352)
- cmd.exe (PID: 7304)
- cmd.exe (PID: 2092)
- cmd.exe (PID: 1240)
- cmd.exe (PID: 1132)
- cmd.exe (PID: 8048)
- cmd.exe (PID: 5324)
- cmd.exe (PID: 6032)
- cmd.exe (PID: 8144)
- cmd.exe (PID: 1300)
- cmd.exe (PID: 1672)
- cmd.exe (PID: 7388)
Stops a currently running service
- sc.exe (PID: 4724)
- sc.exe (PID: 6712)
- sc.exe (PID: 6388)
- sc.exe (PID: 516)
- sc.exe (PID: 6184)
- sc.exe (PID: 2800)
- sc.exe (PID: 664)
- sc.exe (PID: 1180)
- sc.exe (PID: 6476)
- sc.exe (PID: 864)
- sc.exe (PID: 660)
- sc.exe (PID: 5280)
- sc.exe (PID: 7424)
- sc.exe (PID: 7488)
- sc.exe (PID: 7700)
- sc.exe (PID: 7508)
- sc.exe (PID: 7544)
- sc.exe (PID: 7928)
- sc.exe (PID: 920)
- sc.exe (PID: 7624)
- sc.exe (PID: 8140)
- sc.exe (PID: 7648)
- sc.exe (PID: 7788)
- sc.exe (PID: 8120)
- sc.exe (PID: 7408)
- sc.exe (PID: 5548)
- sc.exe (PID: 7404)
- sc.exe (PID: 7696)
- sc.exe (PID: 7784)
- sc.exe (PID: 7580)
- sc.exe (PID: 7904)
- sc.exe (PID: 5720)
- sc.exe (PID: 8084)
- sc.exe (PID: 7888)
- sc.exe (PID: 5400)
- sc.exe (PID: 5360)
- sc.exe (PID: 1040)
- sc.exe (PID: 6668)
- sc.exe (PID: 6736)
- sc.exe (PID: 7204)
- sc.exe (PID: 6192)
- sc.exe (PID: 5588)
- sc.exe (PID: 672)
- sc.exe (PID: 2656)
- sc.exe (PID: 7280)
- sc.exe (PID: 7400)
- sc.exe (PID: 2192)
- sc.exe (PID: 2616)
- sc.exe (PID: 2152)
- sc.exe (PID: 7328)
- sc.exe (PID: 7916)
- sc.exe (PID: 5640)
- sc.exe (PID: 7816)
- sc.exe (PID: 7768)
- sc.exe (PID: 632)
- sc.exe (PID: 744)
- sc.exe (PID: 3268)
- sc.exe (PID: 7052)
- sc.exe (PID: 2904)
- sc.exe (PID: 6576)
- sc.exe (PID: 7824)
- sc.exe (PID: 5364)
- sc.exe (PID: 2616)
- sc.exe (PID: 7392)
- sc.exe (PID: 7492)
- sc.exe (PID: 7336)
Starts CMD.EXE for commands execution
- Teleport_external.exe (PID: 4180)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 7184)
- cmd.exe (PID: 7180)
- cmd.exe (PID: 7280)
- cmd.exe (PID: 7296)
- cmd.exe (PID: 1672)
- cmd.exe (PID: 7472)
- cmd.exe (PID: 7672)
- cmd.exe (PID: 7956)
- cmd.exe (PID: 7200)
- cmd.exe (PID: 7684)
- cmd.exe (PID: 7692)
- cmd.exe (PID: 8116)
- cmd.exe (PID: 5352)
- cmd.exe (PID: 7880)
- cmd.exe (PID: 8076)
- cmd.exe (PID: 4464)
- cmd.exe (PID: 6228)
- cmd.exe (PID: 6468)
- cmd.exe (PID: 3900)
- cmd.exe (PID: 7196)
- cmd.exe (PID: 8056)
- cmd.exe (PID: 744)
- cmd.exe (PID: 5116)
- cmd.exe (PID: 7500)
- cmd.exe (PID: 7368)
- cmd.exe (PID: 4528)
- cmd.exe (PID: 3956)
- cmd.exe (PID: 7288)
- cmd.exe (PID: 7224)
- cmd.exe (PID: 7404)
- cmd.exe (PID: 7928)
- cmd.exe (PID: 6156)
- cmd.exe (PID: 3176)
- cmd.exe (PID: 7628)
- cmd.exe (PID: 7812)
- cmd.exe (PID: 2096)
- cmd.exe (PID: 6272)
- cmd.exe (PID: 7532)
- cmd.exe (PID: 7788)
- cmd.exe (PID: 7228)
- cmd.exe (PID: 2284)
- cmd.exe (PID: 6036)
- cmd.exe (PID: 7640)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 7888)
- cmd.exe (PID: 7824)
- cmd.exe (PID: 2852)
- cmd.exe (PID: 7000)
- cmd.exe (PID: 3268)
- cmd.exe (PID: 7828)
- cmd.exe (PID: 2644)
- cmd.exe (PID: 4844)
- cmd.exe (PID: 780)
- cmd.exe (PID: 728)
- cmd.exe (PID: 7916)
- cmd.exe (PID: 7428)
- cmd.exe (PID: 5228)
- cmd.exe (PID: 5744)
- cmd.exe (PID: 7396)
- cmd.exe (PID: 7440)
- cmd.exe (PID: 8160)
- cmd.exe (PID: 7768)
- cmd.exe (PID: 8184)
- cmd.exe (PID: 7312)
- cmd.exe (PID: 7260)
- cmd.exe (PID: 7476)
- cmd.exe (PID: 7708)
- cmd.exe (PID: 1676)
- cmd.exe (PID: 6272)
- cmd.exe (PID: 7580)
- cmd.exe (PID: 720)
- cmd.exe (PID: 7764)
- cmd.exe (PID: 5436)
- cmd.exe (PID: 2040)
- cmd.exe (PID: 3008)
INFO
Reads the computer name
- Teleport_external.exe (PID: 4180)
Checks supported languages
- Teleport_external.exe (PID: 4180)
- mode.com (PID: 6620)
- mode.com (PID: 2152)
Starts MODE.COM to configure console settings
- mode.com (PID: 6620)
- mode.com (PID: 2152)
Gets the hash of the file via CERTUTIL.EXE
- certutil.exe (PID: 720)
- certutil.exe (PID: 7420)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:08:10 05:57:33+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.39 |
| CodeSize: | 645632 |
| InitializedDataSize: | 183808 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9c7c4 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
501
Monitored processes
372
Malicious processes
2
Suspicious processes
76
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | taskkill /FI "IMAGENAME eq httpdebugger*" /IM * /F /T | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | sc stop KProcessHacker2 | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | C:\WINDOWS\system32\cmd.exe /c taskkill /f /im HTTPDebuggerUI.exe >nul 2>&1 | C:\Windows\System32\cmd.exe | — | Teleport_external.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | taskkill /f /im HTTPDebuggerSvc.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | sc stop HTTPDebuggerPro | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | C:\WINDOWS\system32\net1 stop ESEADriver2 | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | sc stop KProcessHacker1 | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | C:\WINDOWS\system32\net1 stop ESEADriver2 | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | sc stop KProcessHacker3 | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) | |||||||||||||||
Total events
13 017
Read events
13 013
Write events
4
Delete events
0
Modification events
| (PID) Process: | (2196) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\Dnscache\Parameters\DnsPolicyConfig\DNS_RESILIENCY_fe3cr.delivery.mp.microsoft.com |
| Operation: | write | Name: | Name |
Value: fe3cr.delivery.mp.microsoft.com | |||
| (PID) Process: | (2196) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\Dnscache\Parameters\DnsPolicyConfig\DNS_RESILIENCY_fe3cr.delivery.mp.microsoft.com |
| Operation: | write | Name: | ConfigOptions |
Value: 8 | |||
| (PID) Process: | (2196) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\Dnscache\Parameters\DnsPolicyConfig\DNS_RESILIENCY_fe3cr.delivery.mp.microsoft.com |
| Operation: | write | Name: | Version |
Value: 2 | |||
| (PID) Process: | (2196) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\Dnscache\Parameters\DnsPolicyConfig\DNS_RESILIENCY_fe3cr.delivery.mp.microsoft.com |
| Operation: | write | Name: | GenericDNSServers |
Value: 162.159.36.2 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
23
DNS requests
19
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
756 | lsass.exe | GET | 200 | 2.18.161.41:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1228 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1228 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4180 | Teleport_external.exe | 104.26.1.5:443 | keyauth.win | CLOUDFLARENET | US | malicious |
756 | lsass.exe | 2.18.161.41:80 | x1.c.lencr.org | AKAMAI-AS | DE | whitelisted |
— | — | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
keyauth.win |
| malicious |
x1.c.lencr.org |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
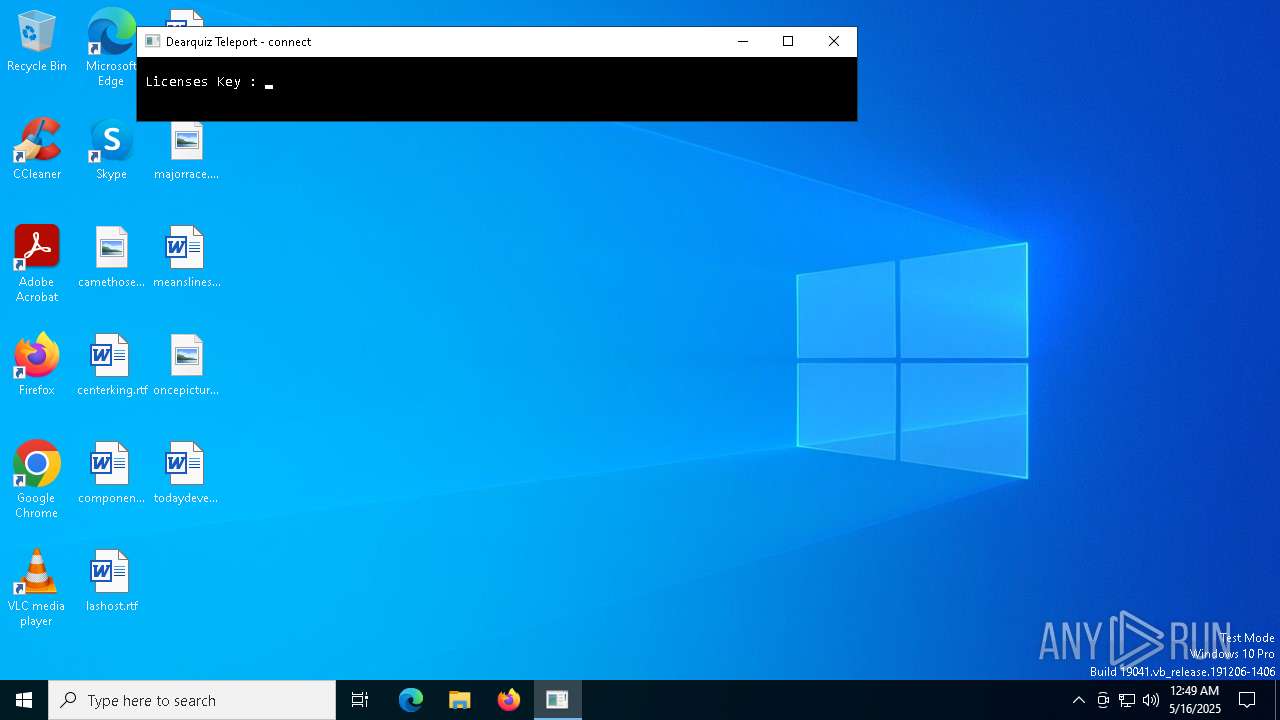
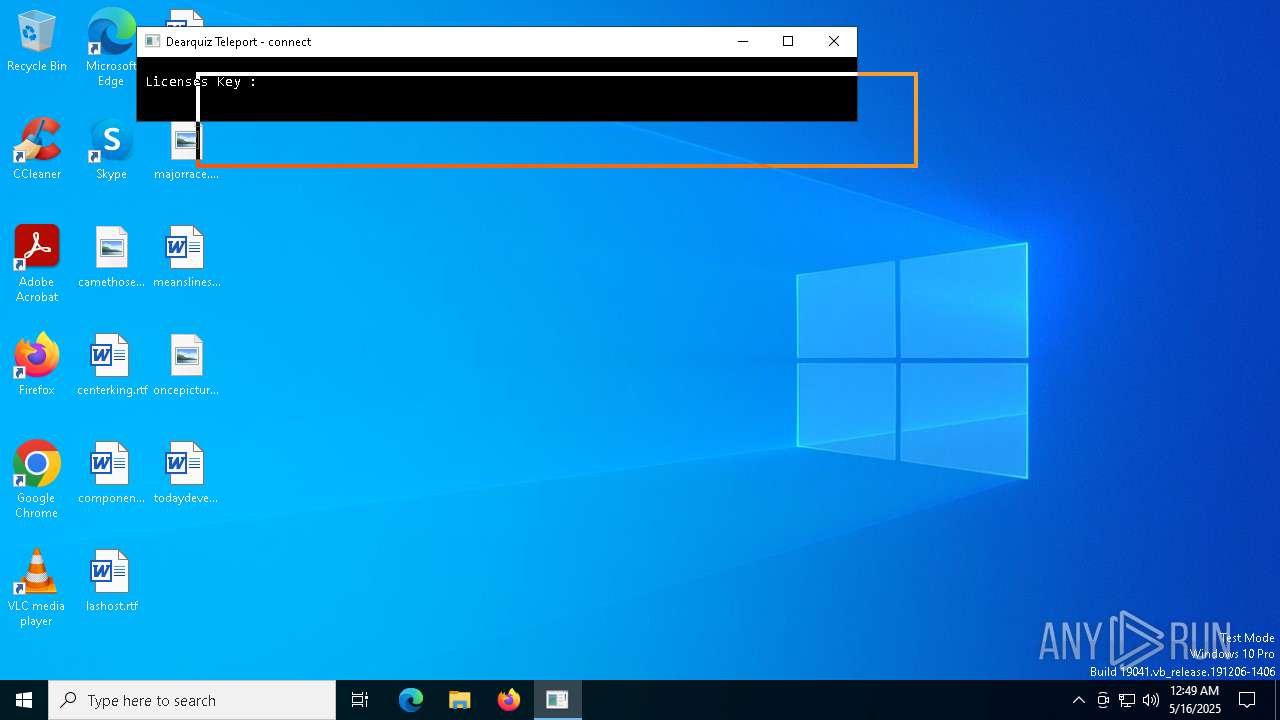
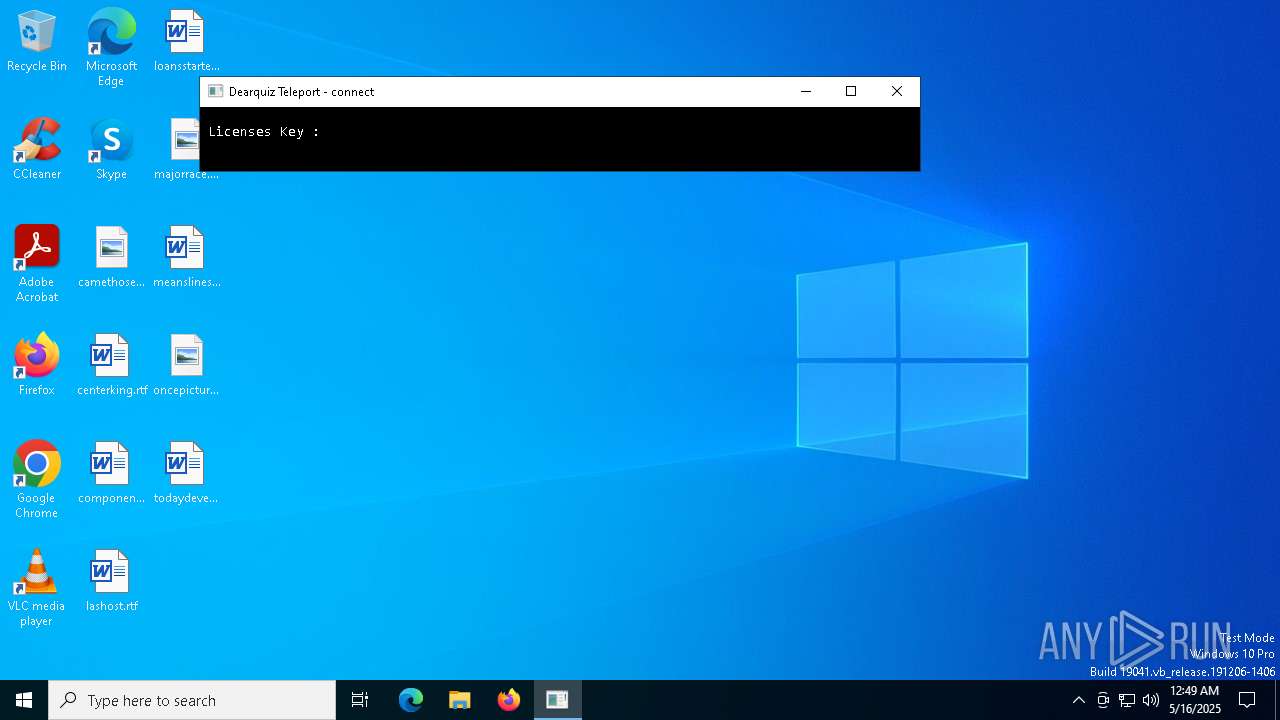
2196 | svchost.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain in DNS Lookup (keyauth .win) |
4180 | Teleport_external.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain (keyauth .win) in TLS SNI |
2196 | svchost.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain in DNS Lookup (keyauth .win) |
4180 | Teleport_external.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain (keyauth .win) in TLS SNI |
4180 | Teleport_external.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain (keyauth .win) in TLS SNI |