analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
| download: | download |
| Full analysis: | https://app.any.run/tasks/9ead3ae4-8cec-47a1-bd92-8ebff0494326 |
| Verdict: | Malicious activity |
| Analysis date: | August 09, 2020, 02:46:30 |
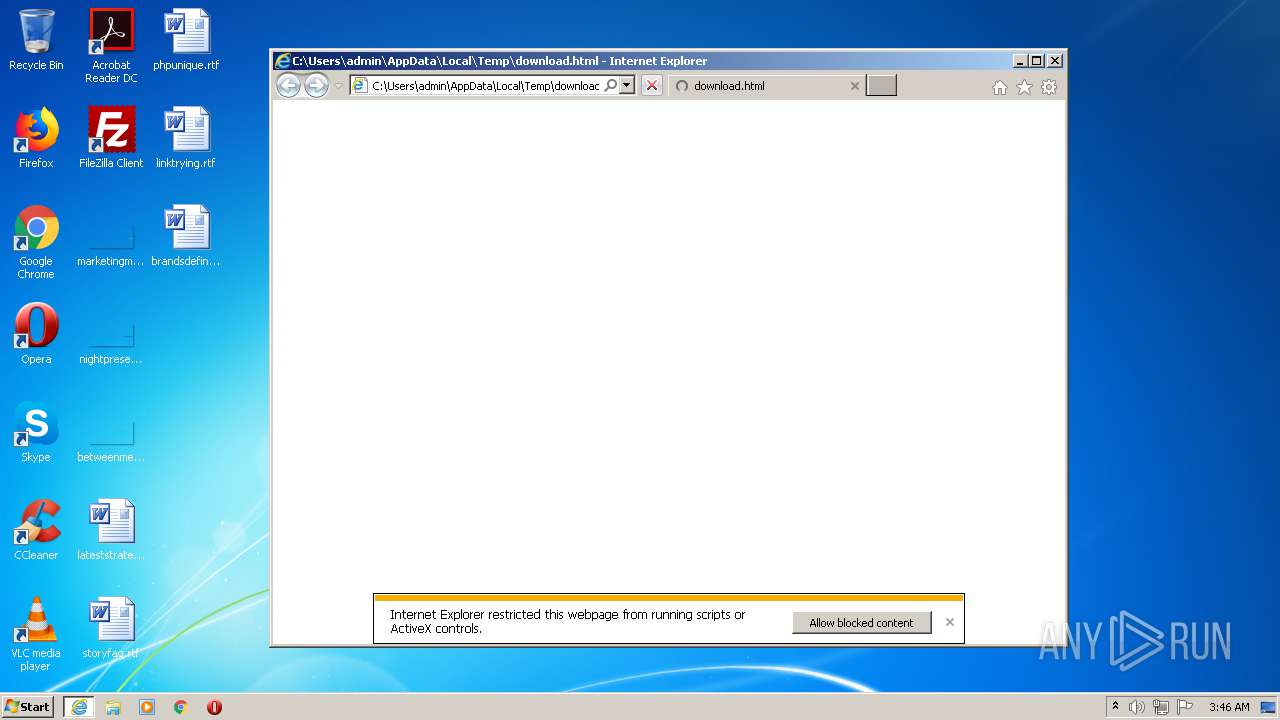
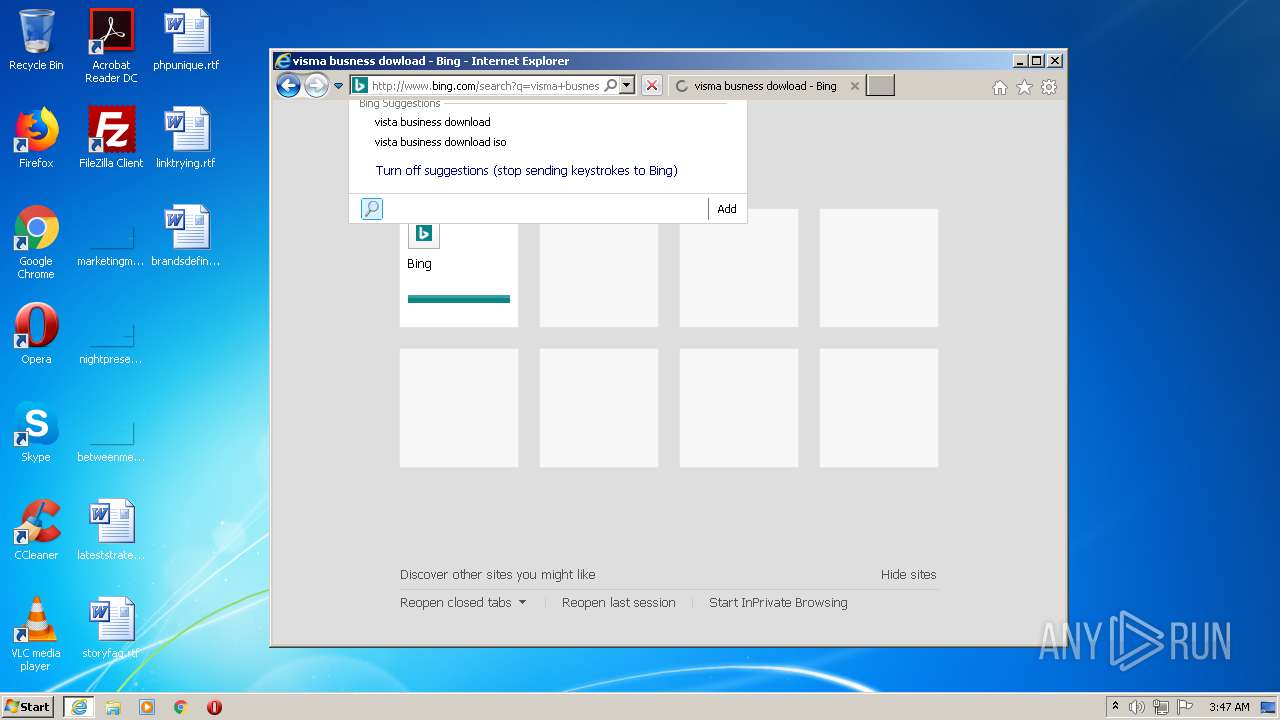
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | 4EEC1BEBE94BBF9D1C9E3F630672F925 |
| SHA1: | D0076F70EA4AAE319E2B5541A09E6CD566690221 |
| SHA256: | EA190D3851BA898134404C27C712F11CA0E3A62611175D948011D403166229FE |
| SSDEEP: | 1536:+hcahyKPqVWPgPJ9spXsUx4JbCYppE7UaOKrvwOS37YZPdHr8ntyBZb37vQVATuK:q/dP/oGcpI7UaOKrvwOS370uVATu1LQ |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads settings of System Certificates
- iexplore.exe (PID: 2720)
- iexplore.exe (PID: 1824)
Reads internet explorer settings
- iexplore.exe (PID: 2720)
- iexplore.exe (PID: 312)
Reads Internet Cache Settings
- iexplore.exe (PID: 1824)
- iexplore.exe (PID: 312)
Changes internet zones settings
- iexplore.exe (PID: 1824)
Application launched itself
- iexplore.exe (PID: 1824)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 312)
Creates files in the user directory
- iexplore.exe (PID: 312)
Changes settings of System certificates
- iexplore.exe (PID: 2720)
- iexplore.exe (PID: 1824)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2720)
- iexplore.exe (PID: 1824)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
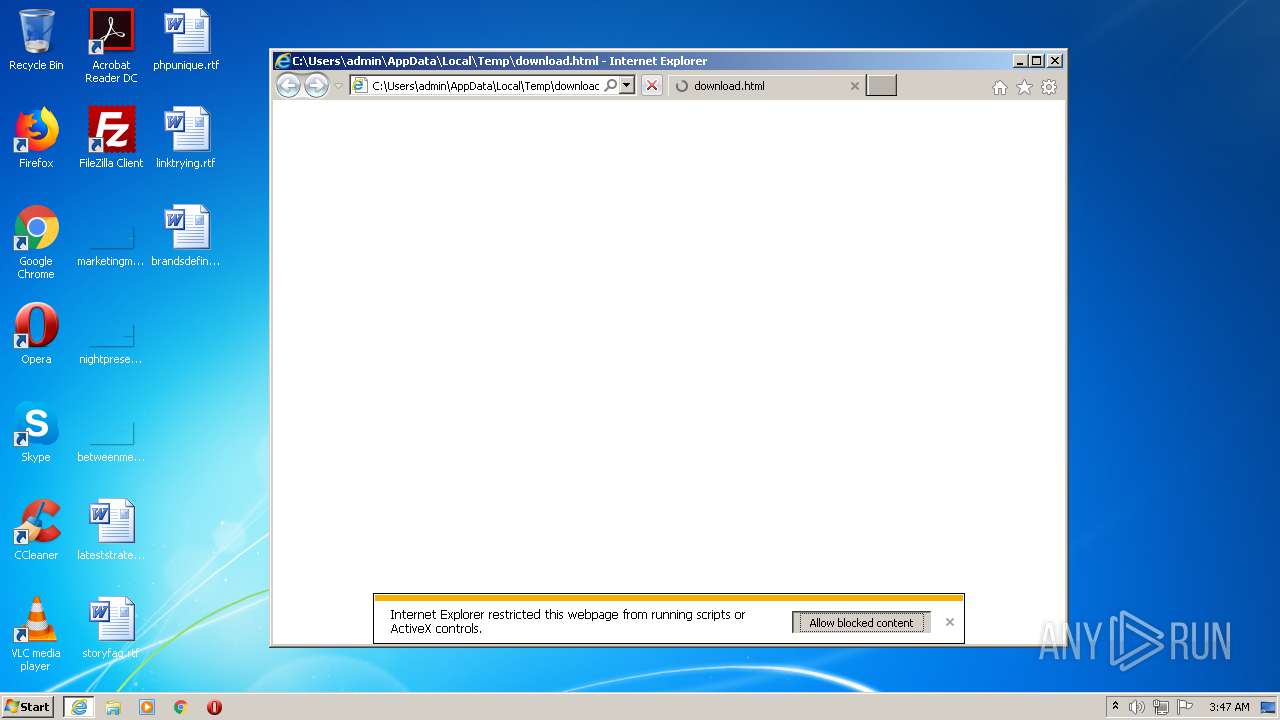
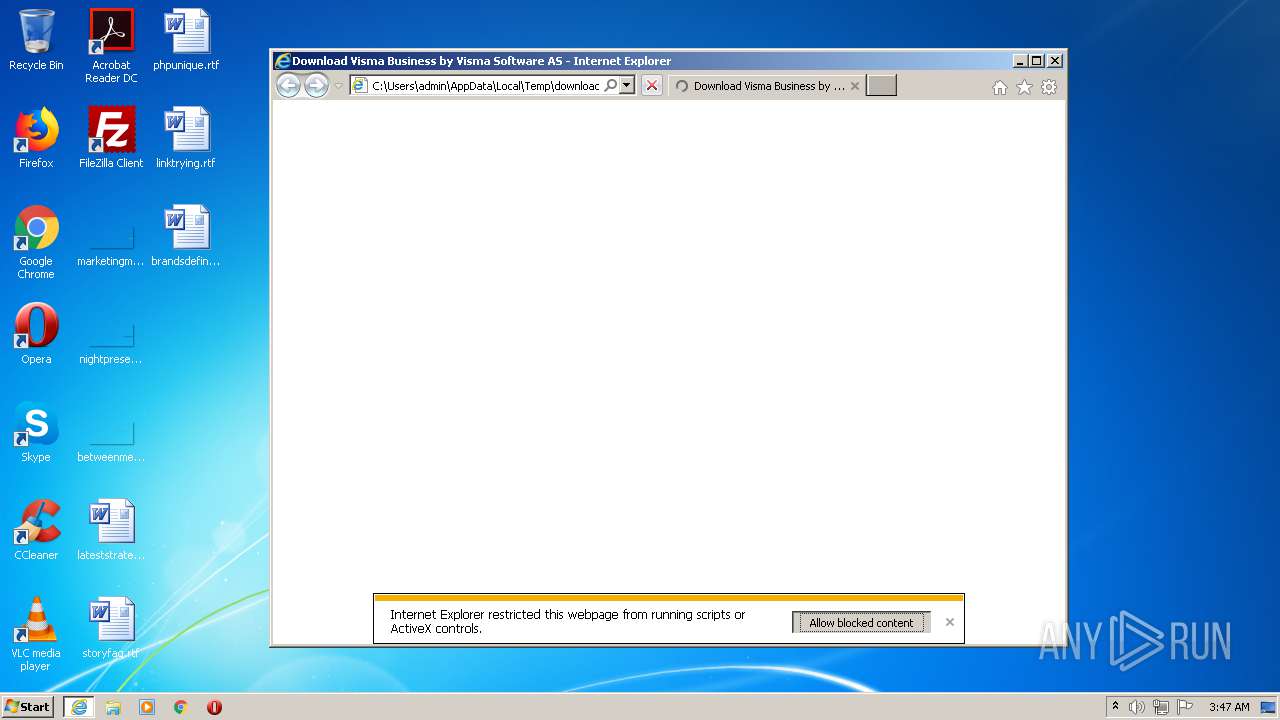
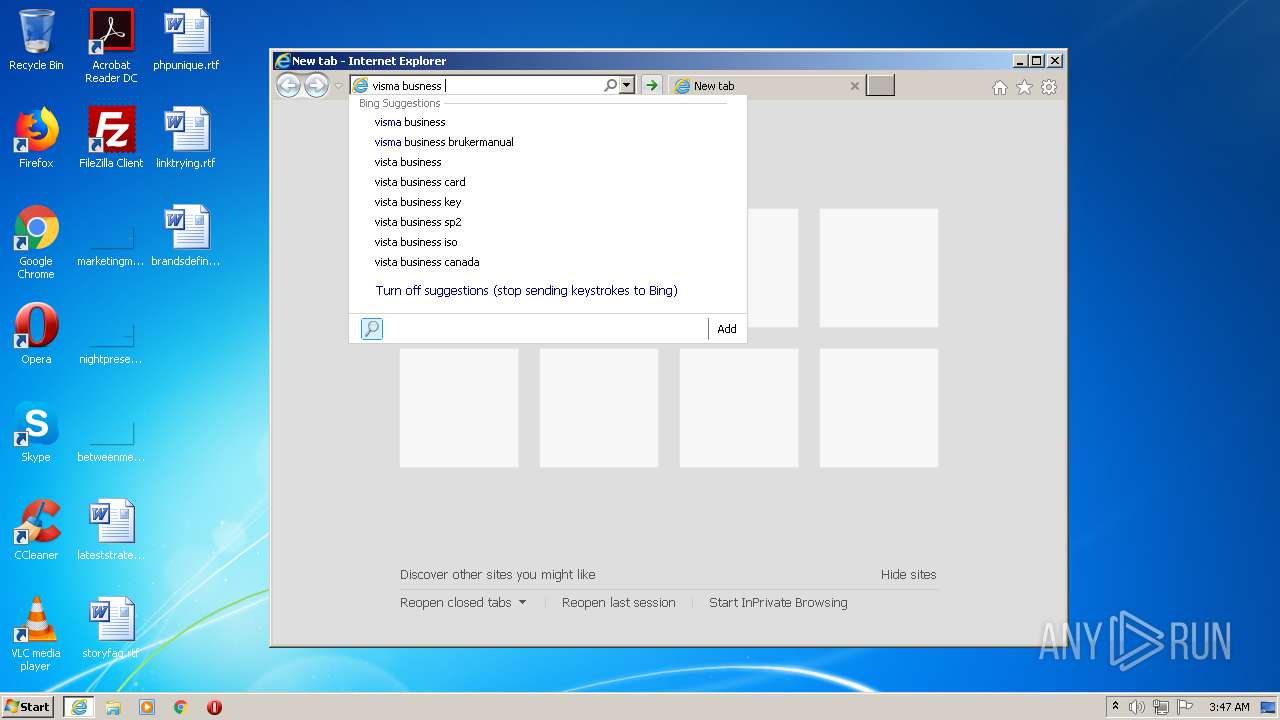
| Title: | Download Visma Business by Visma Software AS |
|---|---|
| Description: | Visma Business, Free Download by Visma Software AS |
| viewport: | width=device-width, initial-scale=1 |
| Robots: | noindex,follow |
Total processes
39
Monitored processes
3
Malicious processes
0
Suspicious processes
0
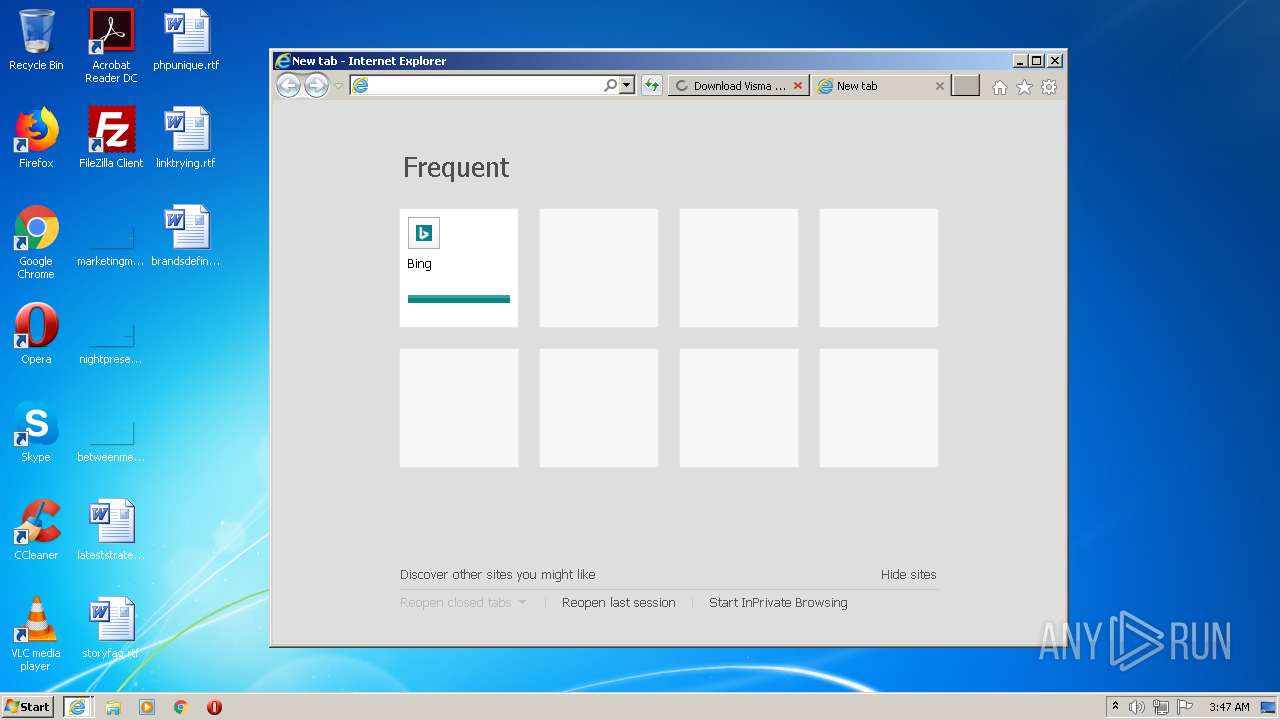
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 1824 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\download.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) | ||||
| 2720 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1824 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) | ||||
| 312 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1824 CREDAT:398593 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) | ||||
Total events
1 864
Read events
1 696
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
32
Text files
34
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1824 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2720 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab5148.tmp | — | |
MD5:— | SHA256:— | |||
| 2720 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar5149.tmp | — | |
MD5:— | SHA256:— | |||
| 2720 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | der | |
MD5:2F2F3B99CAC7A176C812443D5A01835A | SHA256:082786FADFB2F7BBA05DBF4ADA4A9B665ABC1081967948899B2DDB214B0CBFA3 | |||
| 2720 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\verABCE.tmp | — | |
MD5:— | SHA256:— | |||
| 2720 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:8024540B570CEF0636B705131A50655C | SHA256:CA57F58BEBB1839F6FA06262651309D6728C546D06977275CD70997913AC735C | |||
| 2720 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:0A7E0606EBE9447CBEB5DD64256F36FC | SHA256:987ABA07A44C2C1710D4DC03F7BA0CA7AF990B8F444F2243061659CCF37C43B8 | |||
| 2720 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\5A2FD97C5759F987A072FE888B288C9C | der | |
MD5:593A250FF70FBDE9EC4CA8F9E63CDA3A | SHA256:E7CA66511E46E5D8C5AD6DA9B90099842B858FC66B2E8E93EABD47A240A2990F | |||
| 1824 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF9A5D102880DC3C50.TMP | — | |
MD5:— | SHA256:— | |||
| 2720 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:DDDF4BB9D1093EE07BEAAE7DC913F9D4 | SHA256:46EF9E1F5A8128CB7E231A8CF93B7769B46F72264C79F4D679617A5E94440C45 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
46
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2720 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEQC98wdfa2xiQewEDHzwctEh | US | der | 472 b | whitelisted |
2720 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
2720 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
2720 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEQC98wdfa2xiQewEDHzwctEh | US | der | 472 b | whitelisted |
2720 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
2720 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
2720 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
2720 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
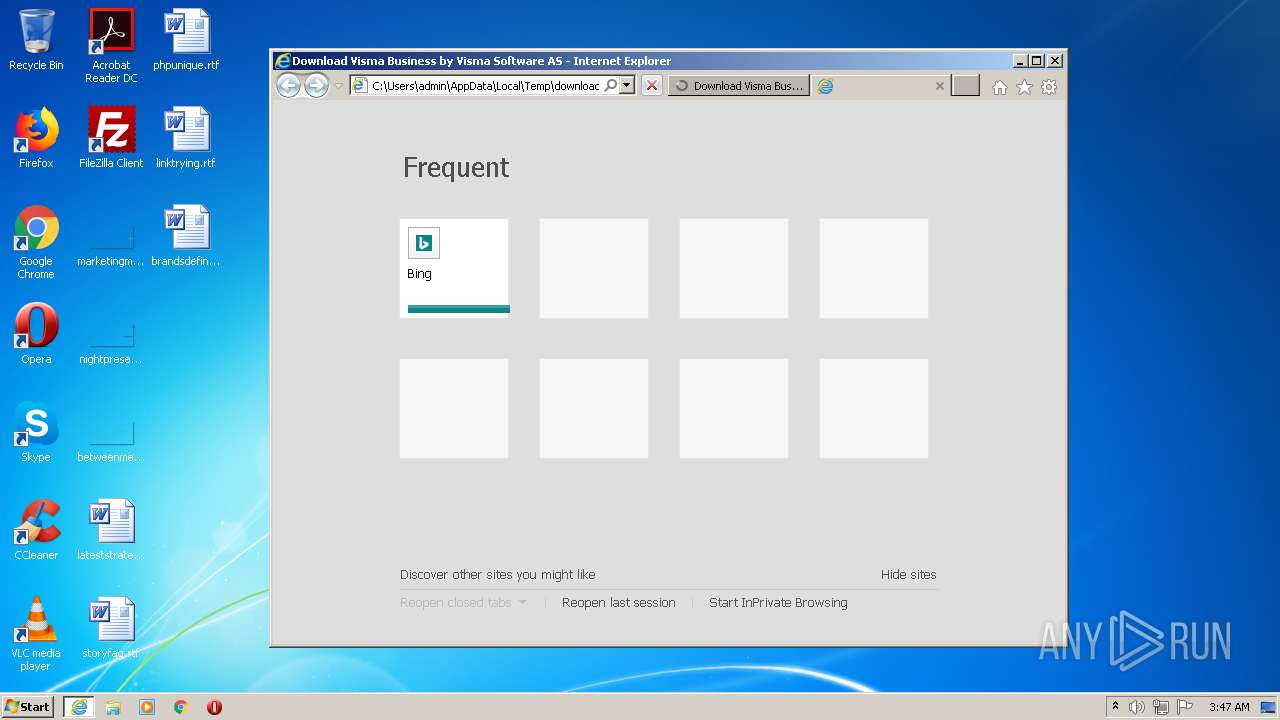
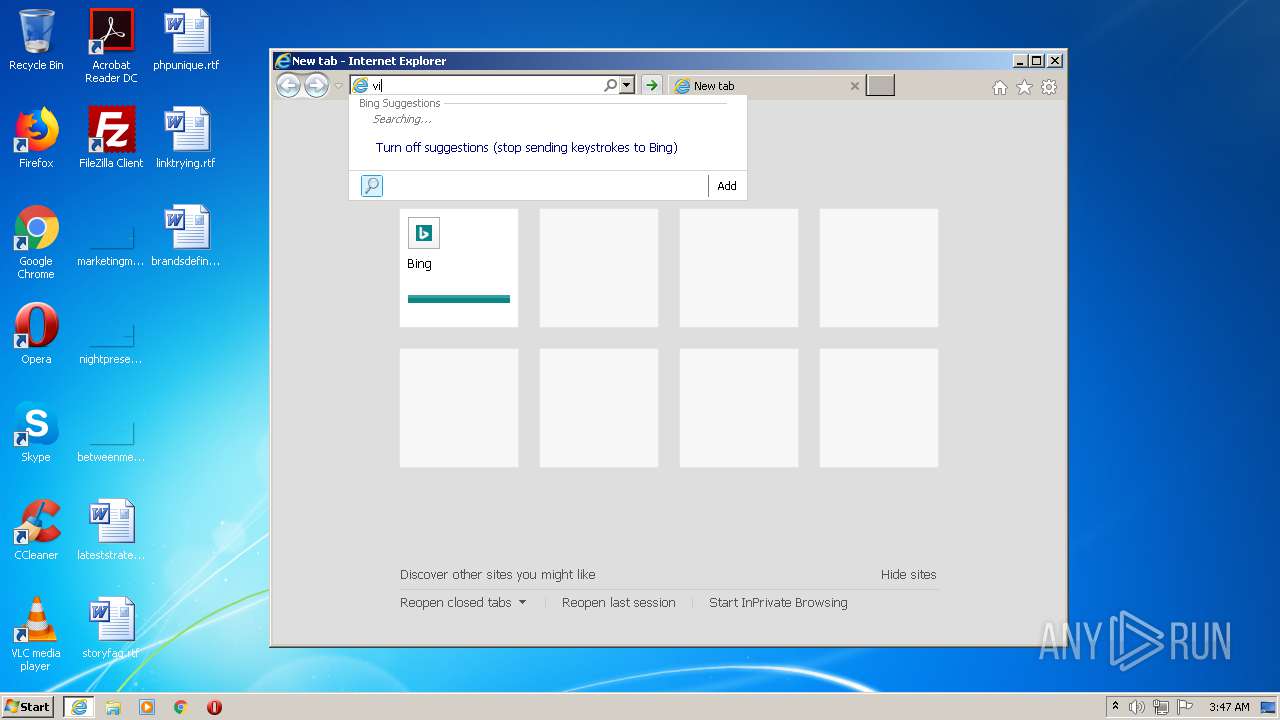
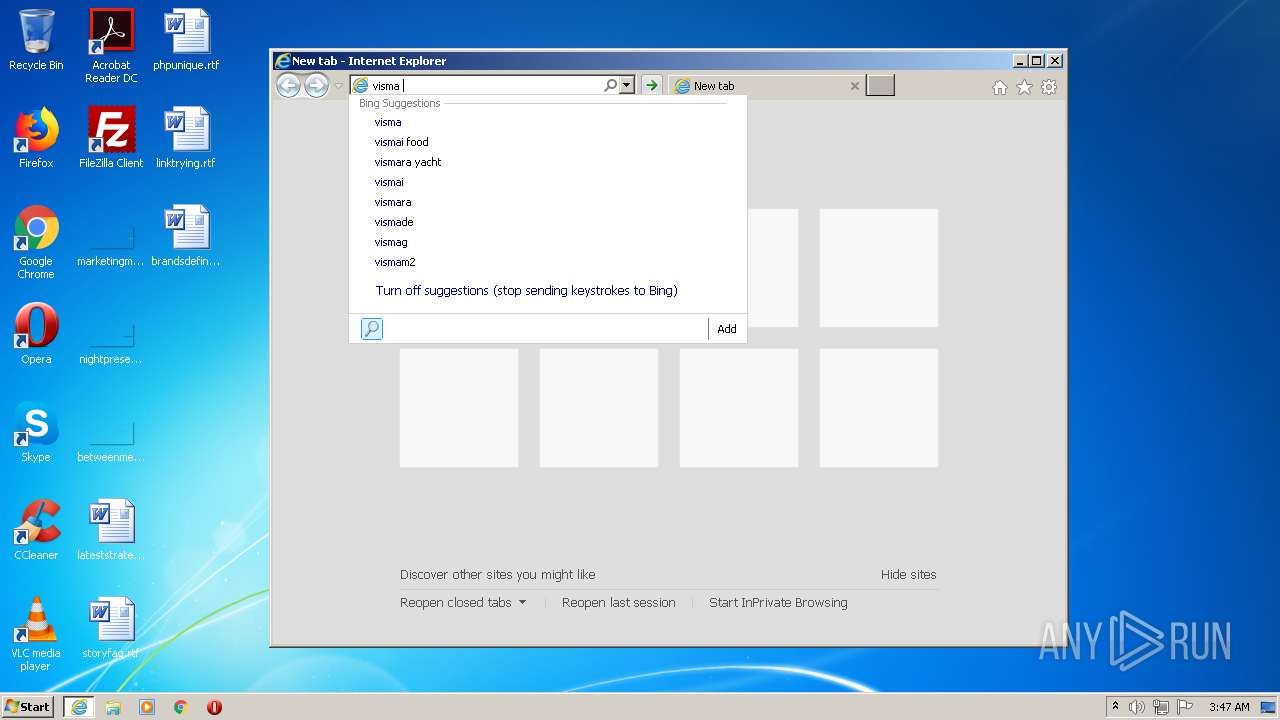
312 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=v&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
2720 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEQC98wdfa2xiQewEDHzwctEh | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2720 | iexplore.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4 | System | 172.217.16.130:139 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
4 | System | 172.217.16.130:445 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
1824 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2720 | iexplore.exe | 208.88.224.98:443 | i.informer.com | WZ Communications Inc. | US | unknown |
2720 | iexplore.exe | 74.117.179.70:443 | img.informer.com | WZ Communications Inc. | US | suspicious |
312 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2720 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2720 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
img.informer.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
i.informer.com |
| whitelisted |
software.informer.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |