| File name: | XMoon.exe |
| Full analysis: | https://app.any.run/tasks/10457f5f-7eb7-4ab6-9354-52495a1b2dd5 |
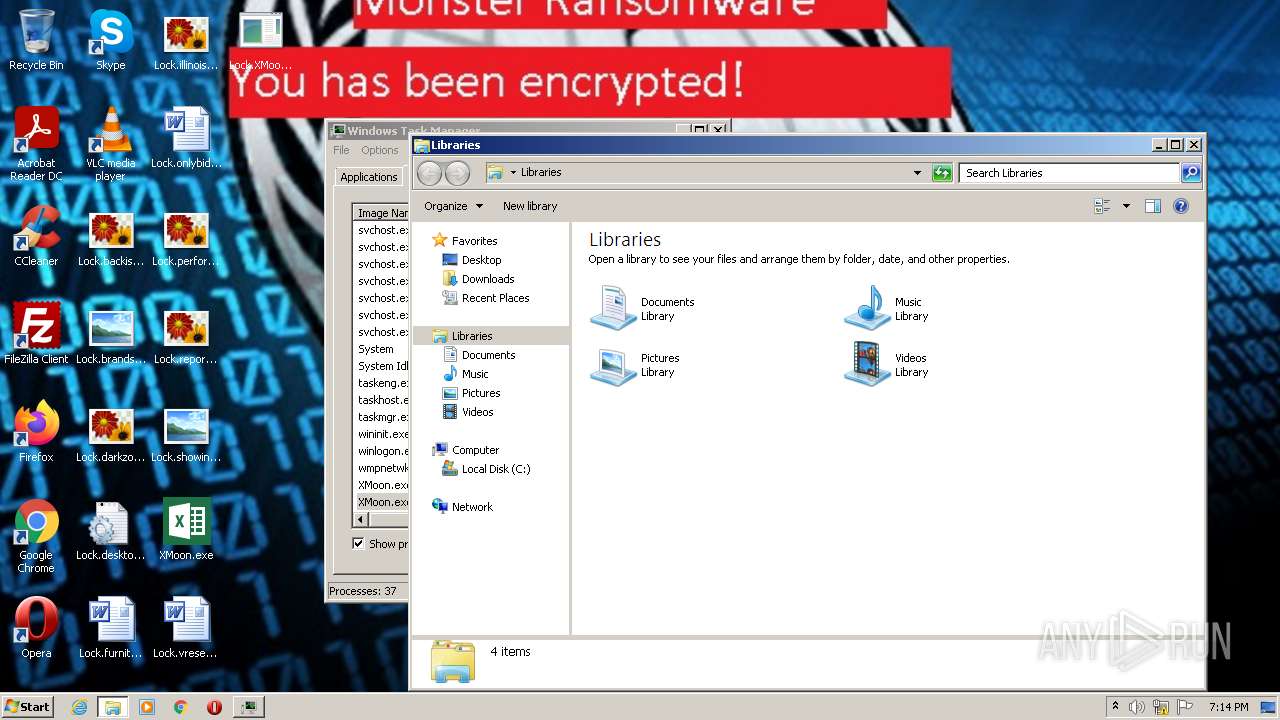
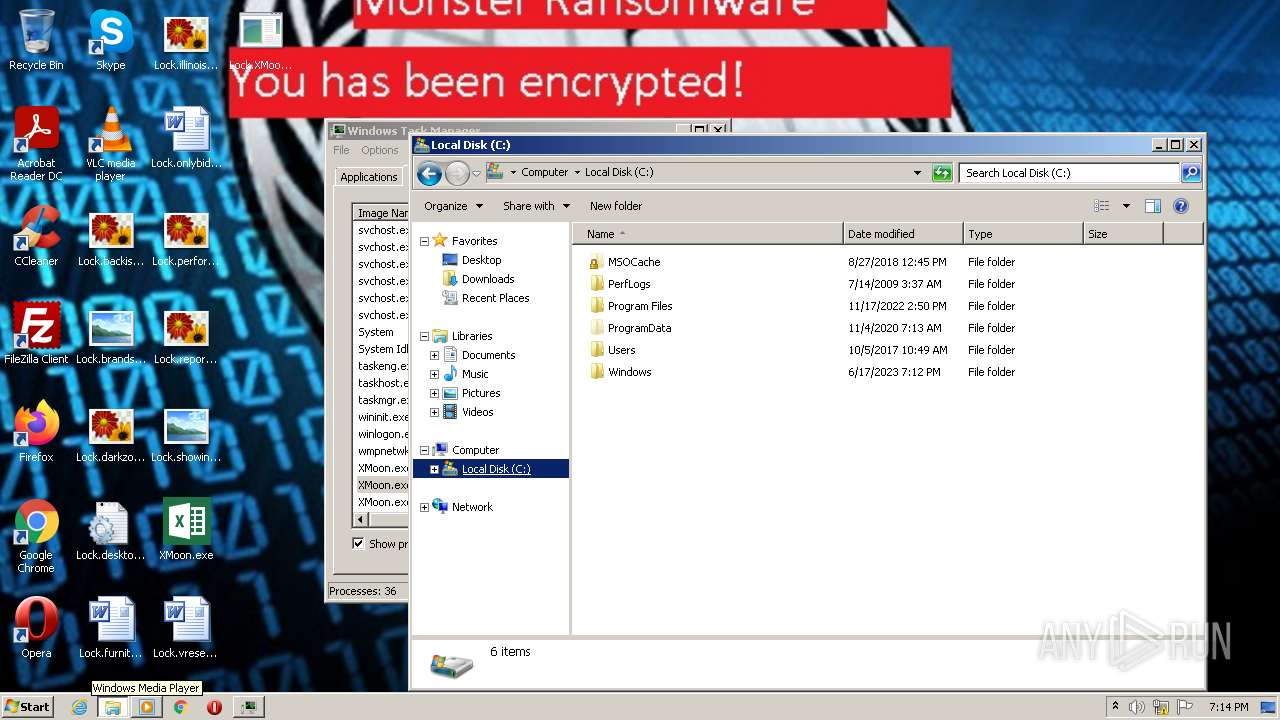
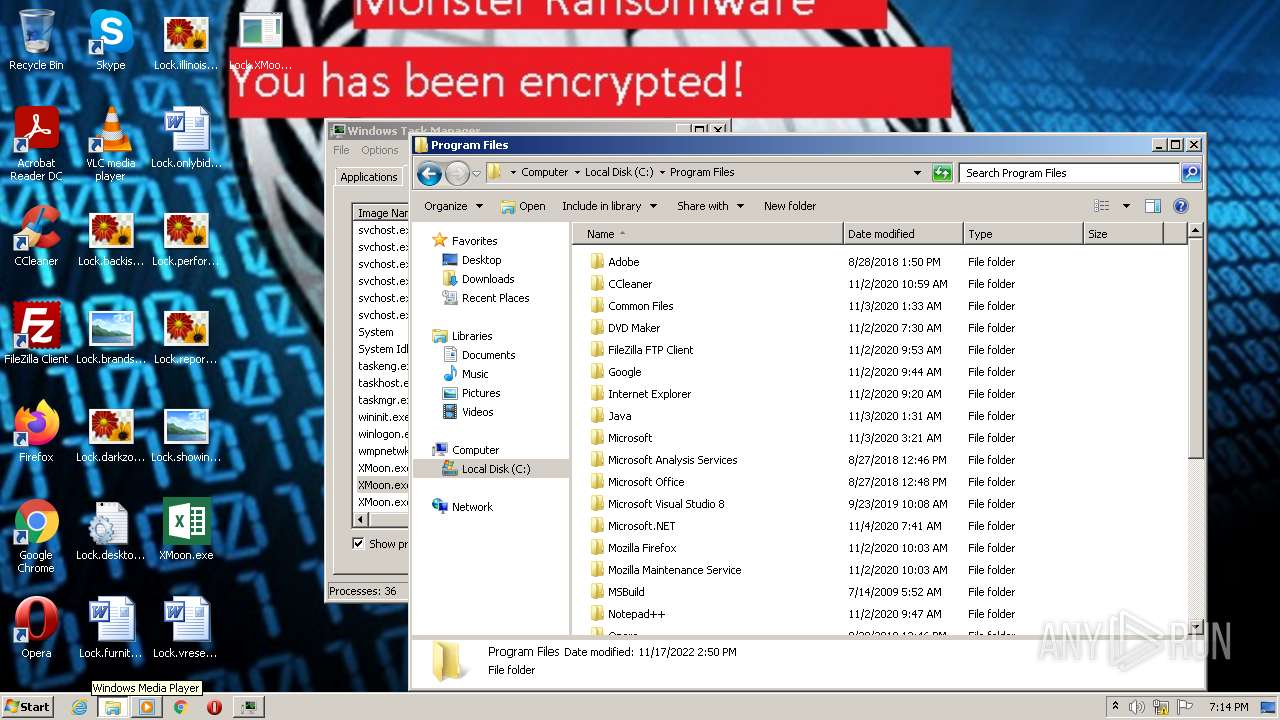
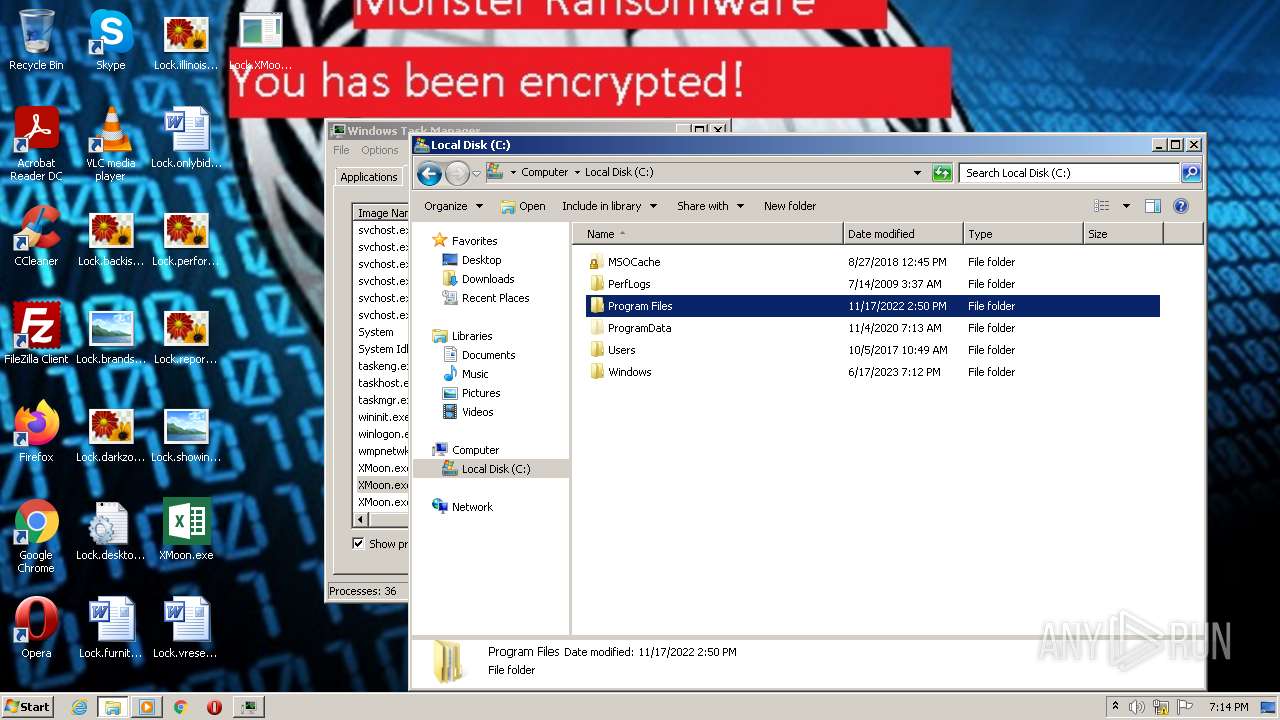
| Verdict: | Malicious activity |
| Analysis date: | June 17, 2023, 18:12:20 |
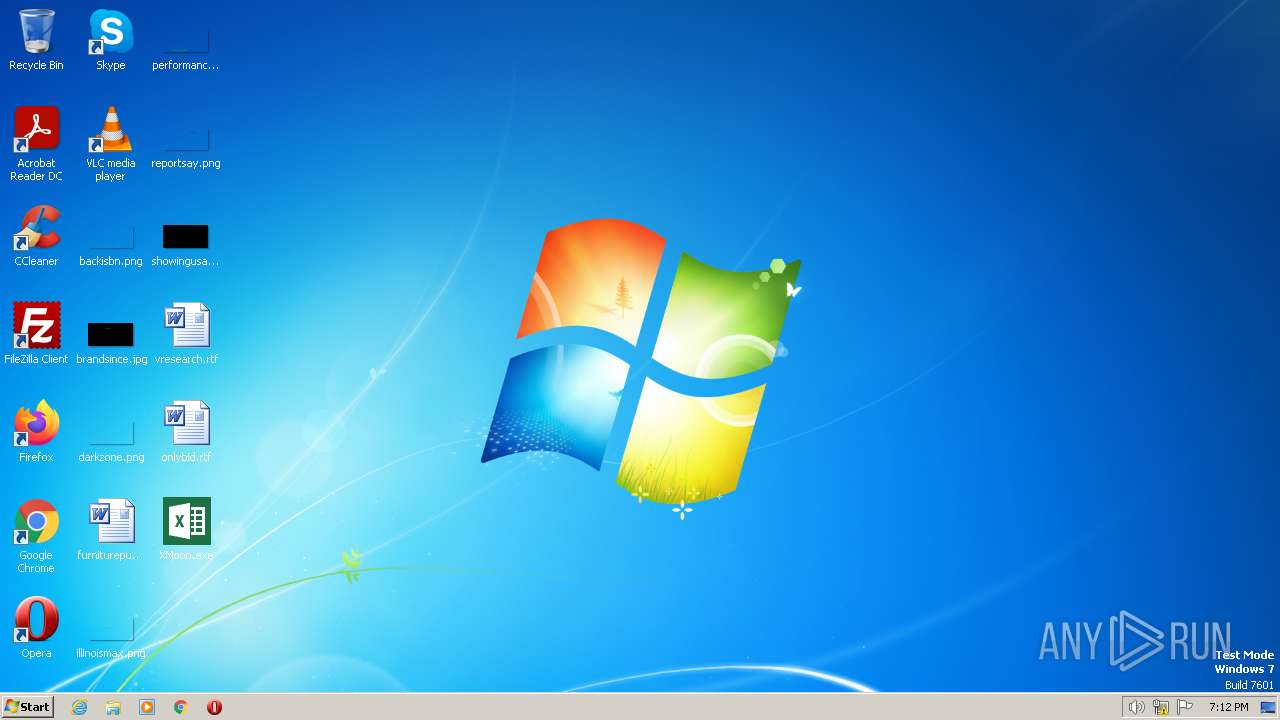
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | A690CCE59E21F5198CA304243B084F9E |
| SHA1: | 8AEB0B106DD21E2AFB50C3F7AE78CA4F8F4B29C5 |
| SHA256: | EA0A5854AA6E91EBE816D256F34F820697A92D86B4F81E8855C84DAEED40B9D4 |
| SSDEEP: | 12288:X6Wq4aaE6KwyF5L0Y2D1PqL6eqhBkEFY9ddNdzYaTW3aSDcyImRlL7zo:1thEVaPqL6JkF9YaTLSigL7c |
MALICIOUS
Creates a writable file the system directory
- wusa.exe (PID: 784)
- wusa.exe (PID: 3700)
- wusa.exe (PID: 1648)
Loads dropped or rewritten executable
- migwiz.exe (PID: 1360)
- migwiz.exe (PID: 768)
- migwiz.exe (PID: 3072)
Create files in the Startup directory
- XMoon.exe (PID: 2732)
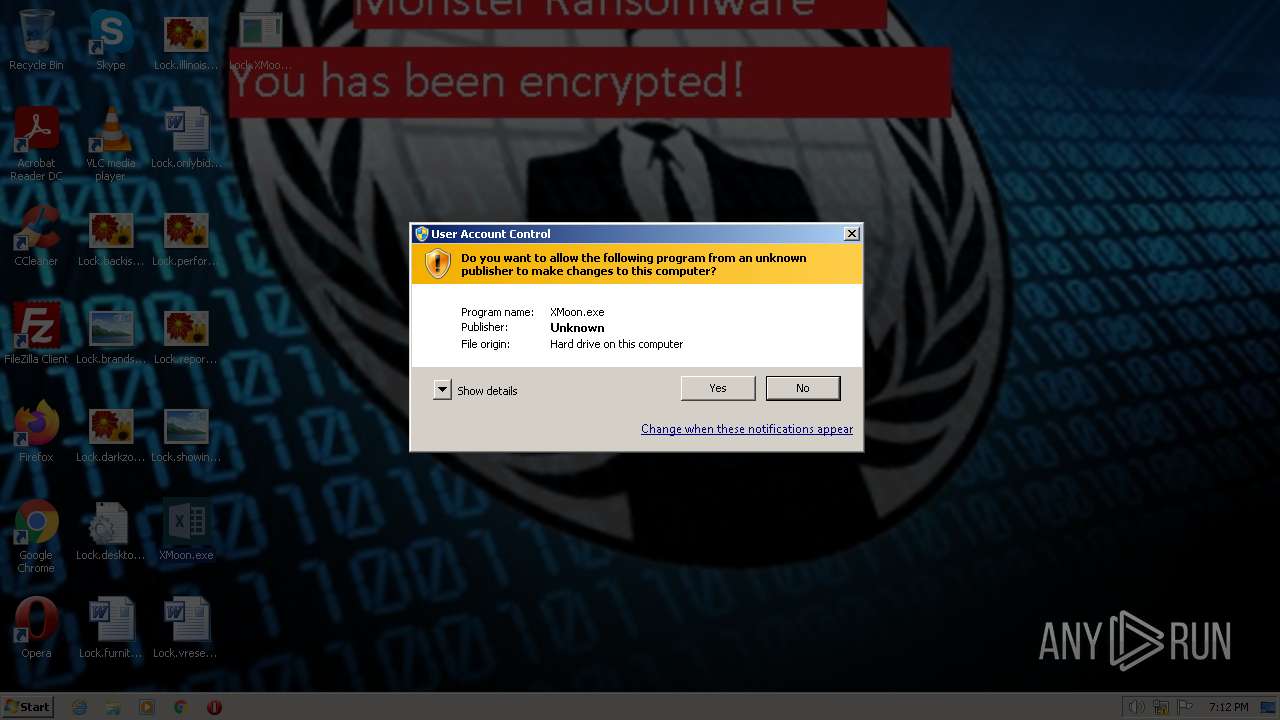
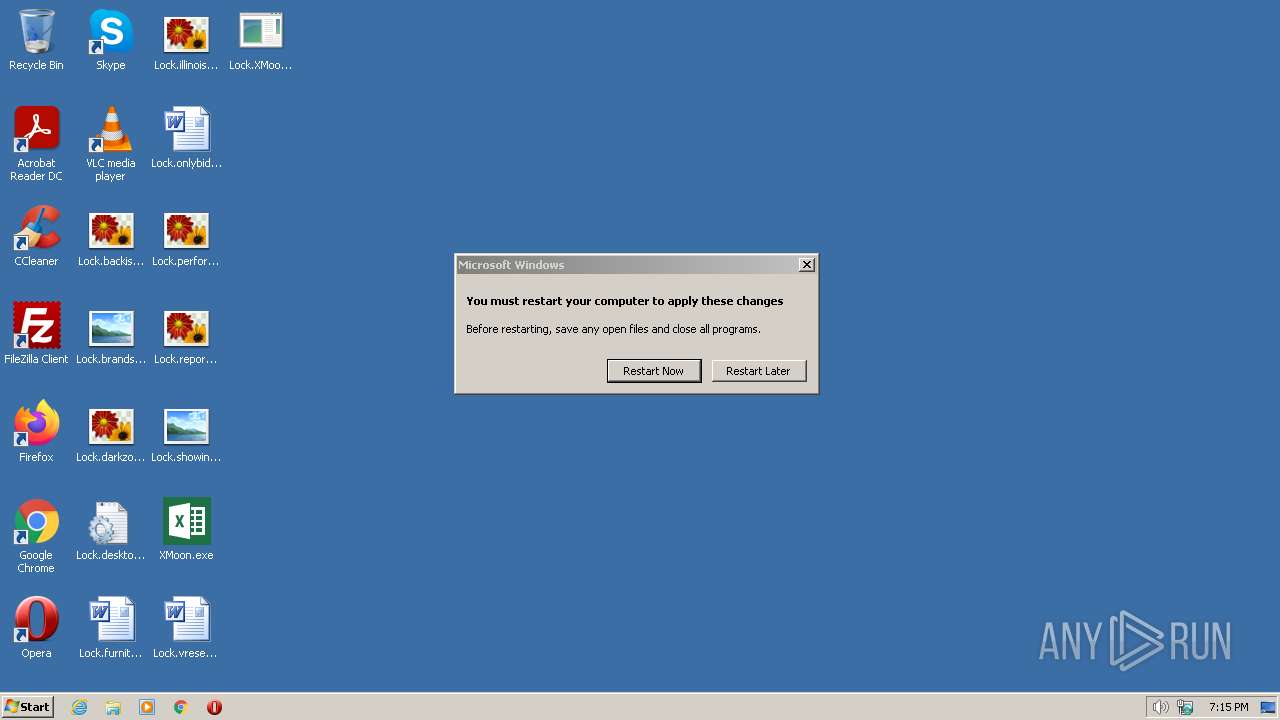
UAC/LUA settings modification
- reg.exe (PID: 1300)
- reg.exe (PID: 2268)
- reg.exe (PID: 3712)
Starts Visual C# compiler
- sdiagnhost.exe (PID: 2576)
- sdiagnhost.exe (PID: 1560)
SUSPICIOUS
Starts CMD.EXE for commands execution
- XMoon.exe (PID: 2732)
- migwiz.exe (PID: 1360)
- XMoon.exe (PID: 1596)
- XMoon.exe (PID: 3976)
- migwiz.exe (PID: 3072)
- migwiz.exe (PID: 768)
Reads the Internet Settings
- cmd.exe (PID: 624)
- XMoon.exe (PID: 2732)
- wscript.exe (PID: 1976)
- cmd.exe (PID: 2148)
- XMoon.exe (PID: 1596)
- wscript.exe (PID: 3972)
- wscript.exe (PID: 2800)
- XMoon.exe (PID: 3976)
- sdiagnhost.exe (PID: 2576)
- taskmgr.exe (PID: 1060)
- sdiagnhost.exe (PID: 1560)
Executable content was dropped or overwritten
- wusa.exe (PID: 784)
- wusa.exe (PID: 3700)
- XMoon.exe (PID: 2732)
- wusa.exe (PID: 1648)
- msdt.exe (PID: 3884)
- csc.exe (PID: 3056)
- csc.exe (PID: 3408)
- csc.exe (PID: 3724)
- csc.exe (PID: 3672)
- csc.exe (PID: 2424)
The process executes VB scripts
- XMoon.exe (PID: 2732)
- XMoon.exe (PID: 1596)
- XMoon.exe (PID: 3976)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3580)
- cmd.exe (PID: 2756)
- cmd.exe (PID: 3388)
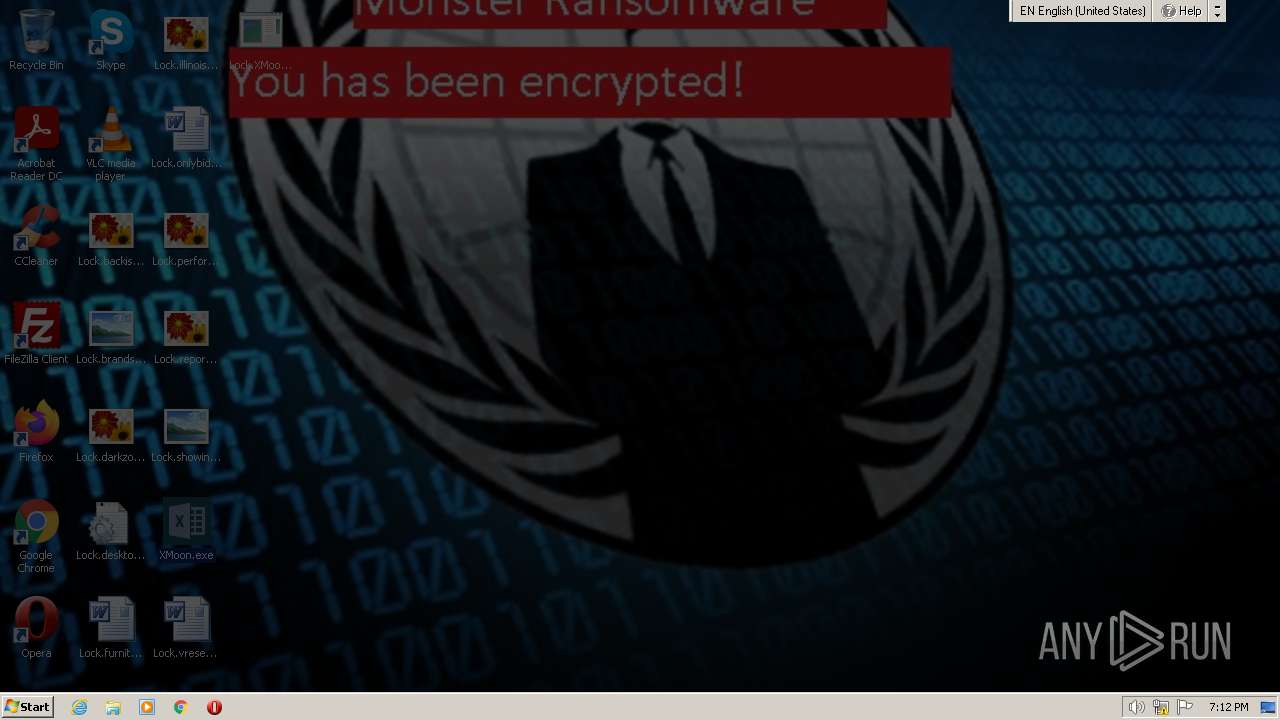
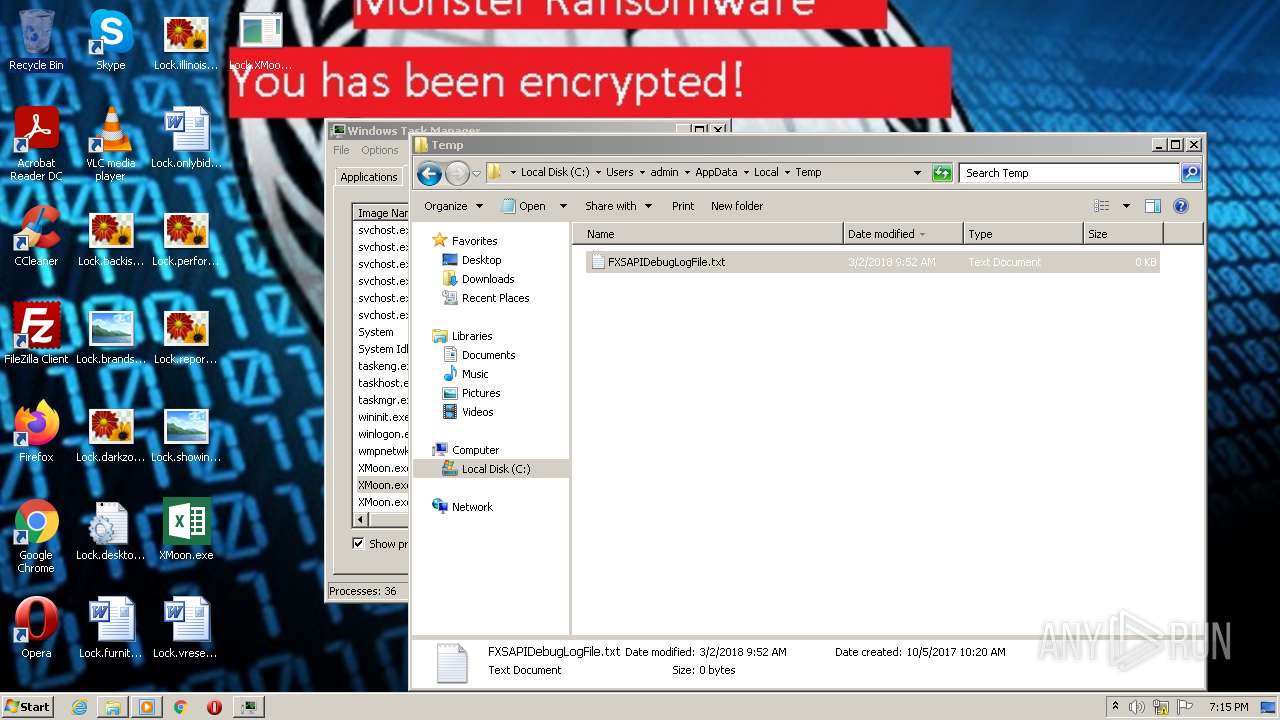
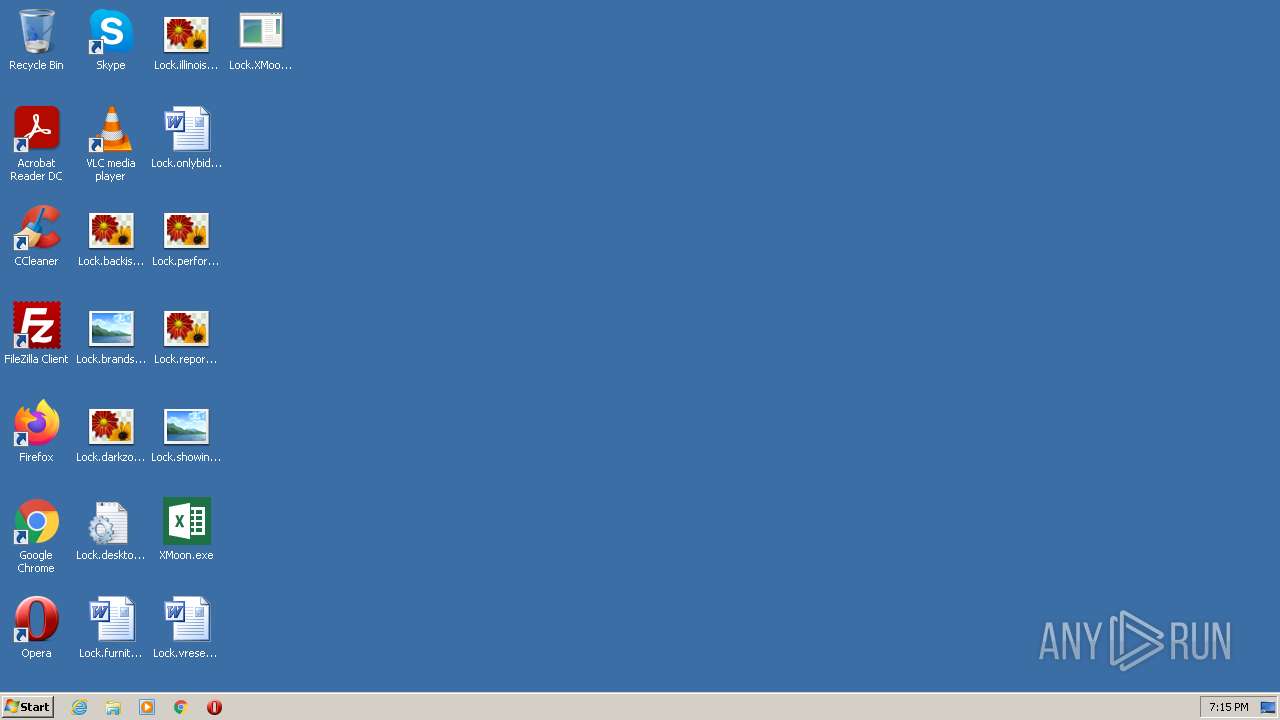
Changes the desktop background image
- XMoon.exe (PID: 2732)
- XMoon.exe (PID: 1596)
- XMoon.exe (PID: 3976)
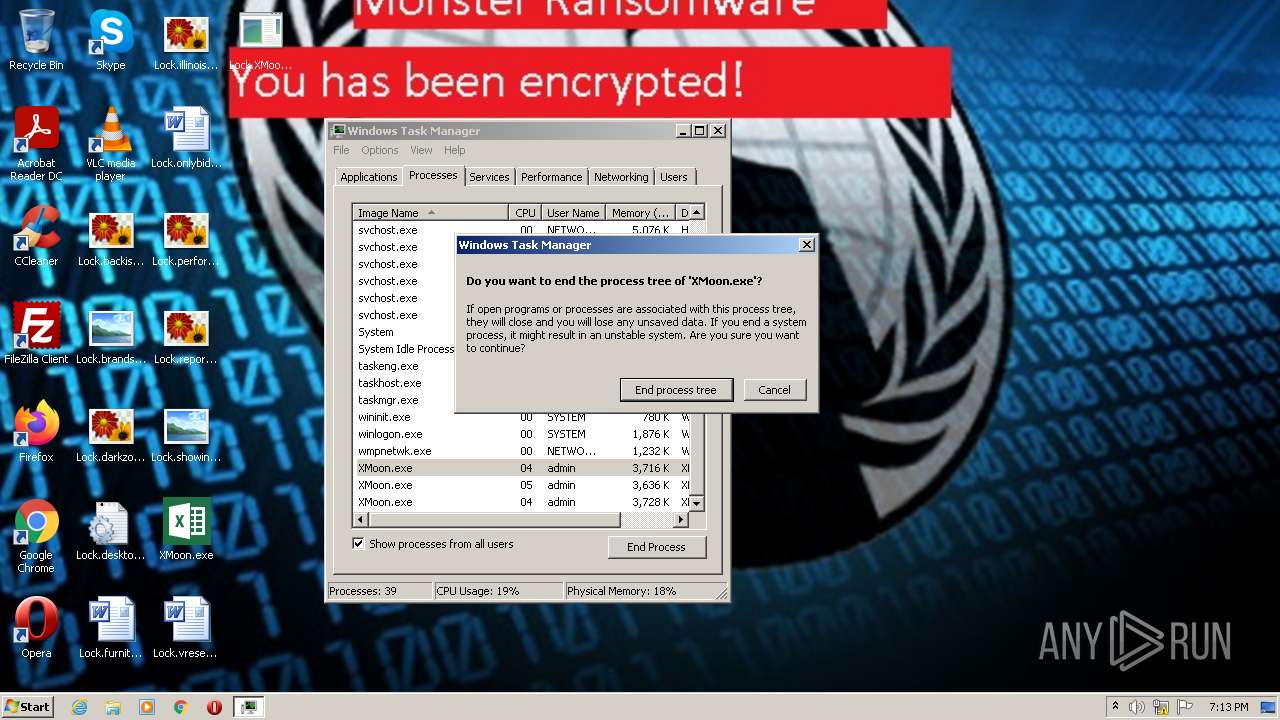
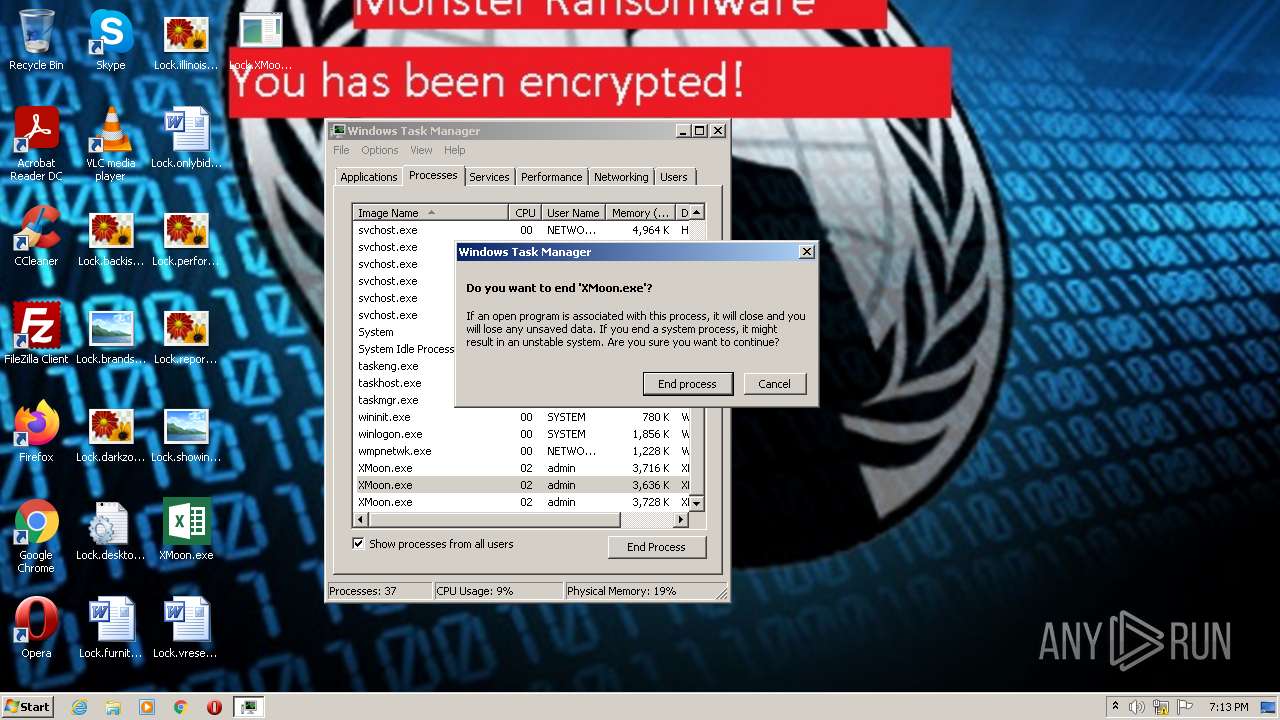
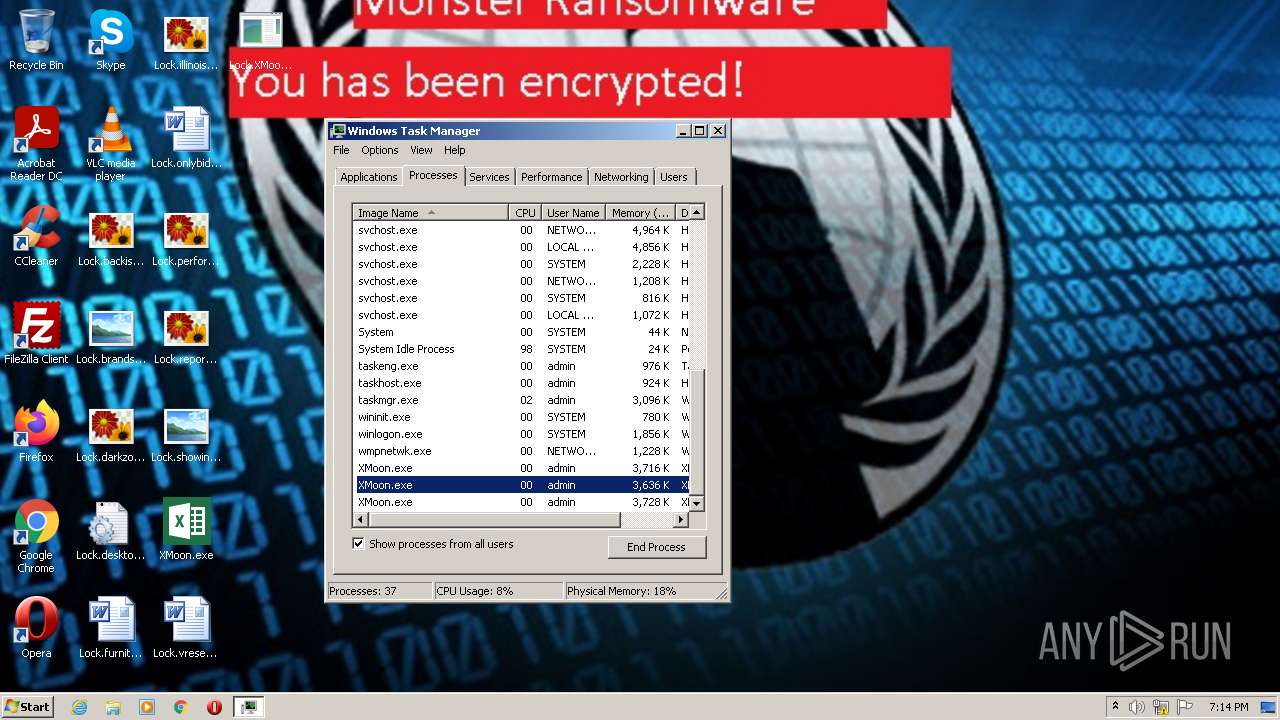
Application launched itself
- taskmgr.exe (PID: 1060)
Probably uses Microsoft diagnostics tool to execute malicious payload
- pcwrun.exe (PID: 3232)
Reads settings of System Certificates
- msdt.exe (PID: 3884)
Uses .NET C# to load dll
- sdiagnhost.exe (PID: 2576)
- sdiagnhost.exe (PID: 1560)
Write to the desktop.ini file (may be used to cloak folders)
- XMoon.exe (PID: 2732)
INFO
Reads mouse settings
- XMoon.exe (PID: 2732)
- XMoon.exe (PID: 1596)
- XMoon.exe (PID: 3976)
Checks supported languages
- XMoon.exe (PID: 2732)
- XMoon.exe (PID: 1596)
- XMoon.exe (PID: 3976)
- csc.exe (PID: 3056)
- cvtres.exe (PID: 1364)
- csc.exe (PID: 3408)
- cvtres.exe (PID: 3536)
- csc.exe (PID: 3724)
- cvtres.exe (PID: 3816)
- csc.exe (PID: 3672)
- cvtres.exe (PID: 2924)
- csc.exe (PID: 2424)
- cvtres.exe (PID: 3024)
Reads the computer name
- XMoon.exe (PID: 2732)
- XMoon.exe (PID: 1596)
- XMoon.exe (PID: 3976)
The process checks LSA protection
- wusa.exe (PID: 784)
- XMoon.exe (PID: 2732)
- wusa.exe (PID: 3700)
- XMoon.exe (PID: 1596)
- XMoon.exe (PID: 3976)
- wusa.exe (PID: 1648)
- msdt.exe (PID: 3884)
- sdiagnhost.exe (PID: 2576)
- csc.exe (PID: 3056)
- cvtres.exe (PID: 1364)
- csc.exe (PID: 3408)
- cvtres.exe (PID: 3536)
- cvtres.exe (PID: 3816)
- sdiagnhost.exe (PID: 1560)
- csc.exe (PID: 2424)
- csc.exe (PID: 3672)
- explorer.exe (PID: 3268)
- cvtres.exe (PID: 3024)
- csc.exe (PID: 3724)
- cvtres.exe (PID: 2924)
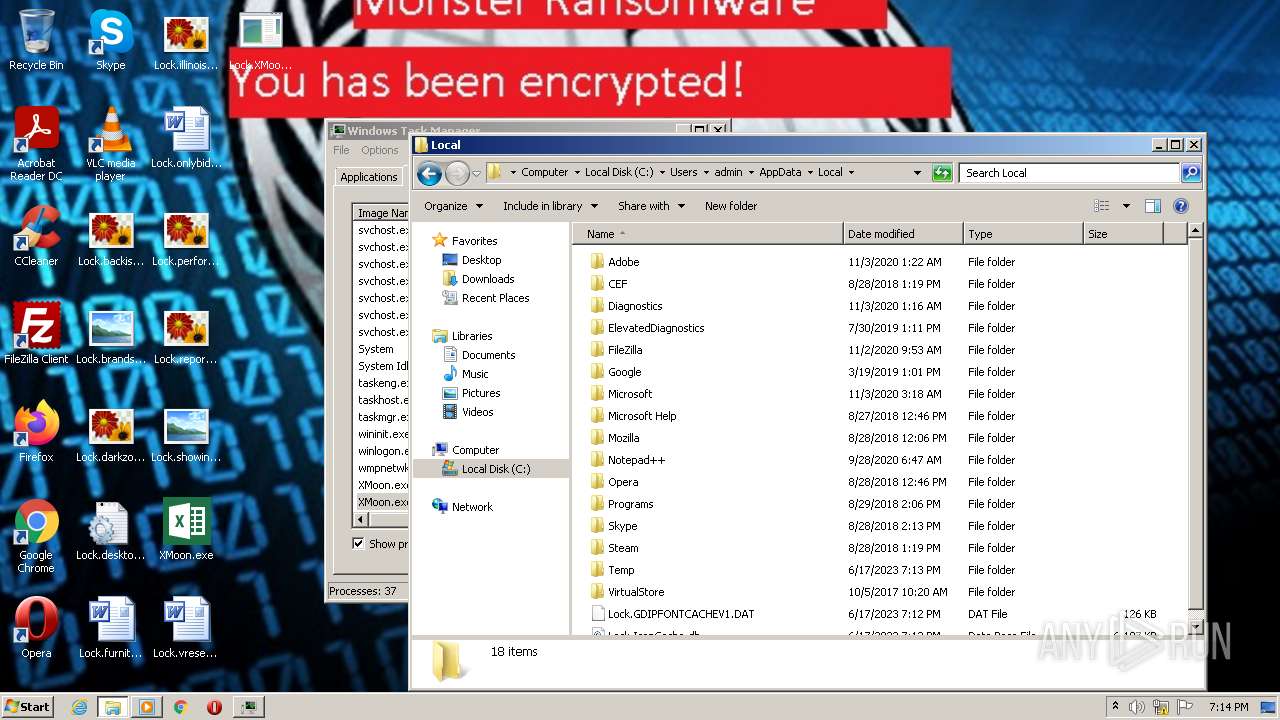
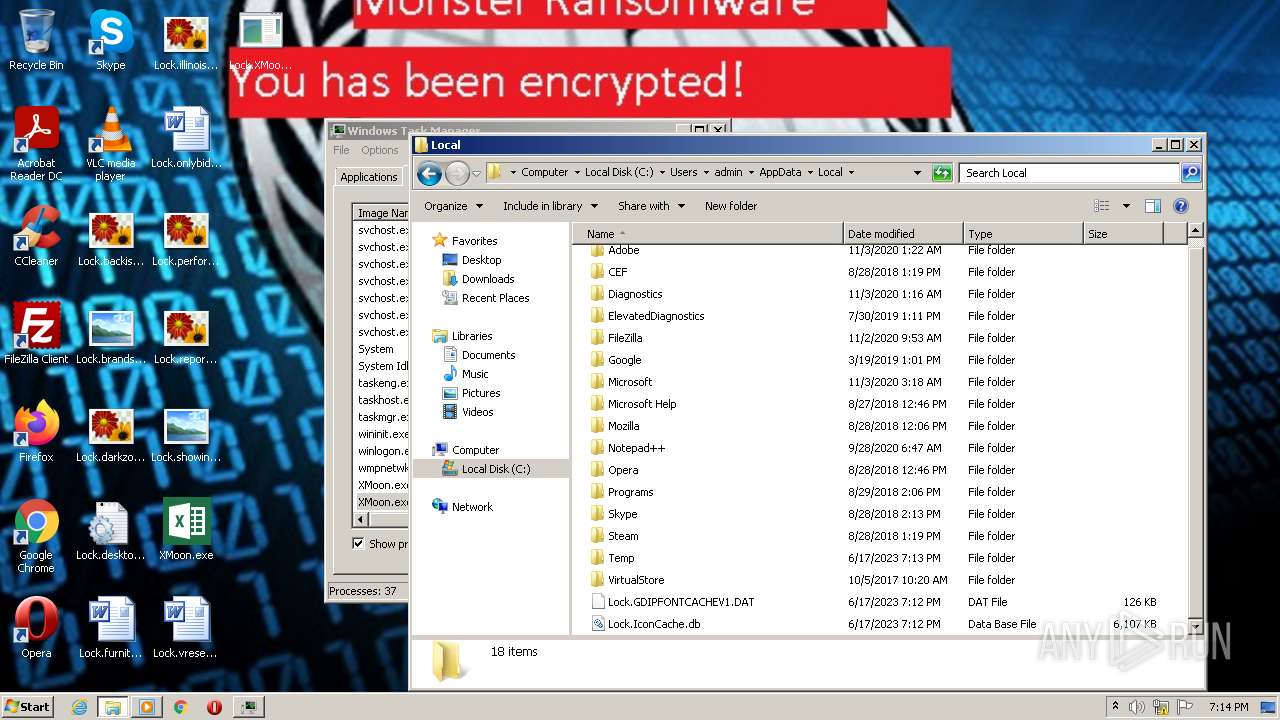
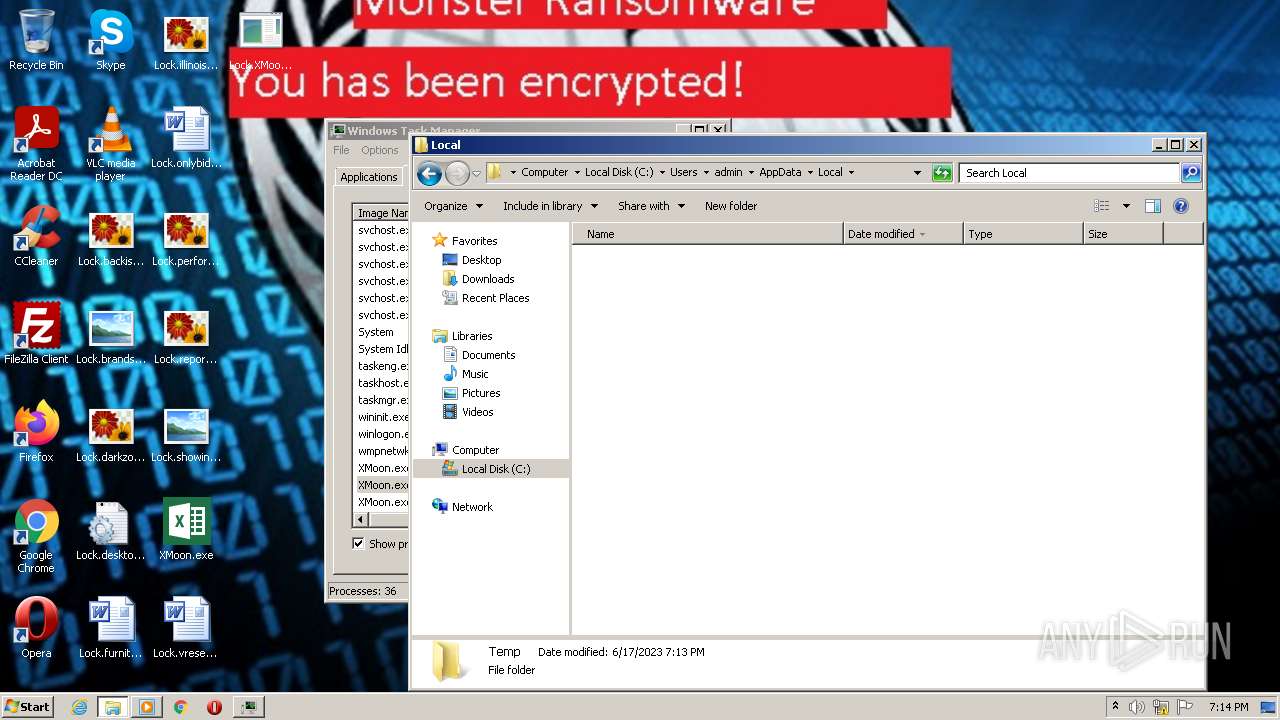
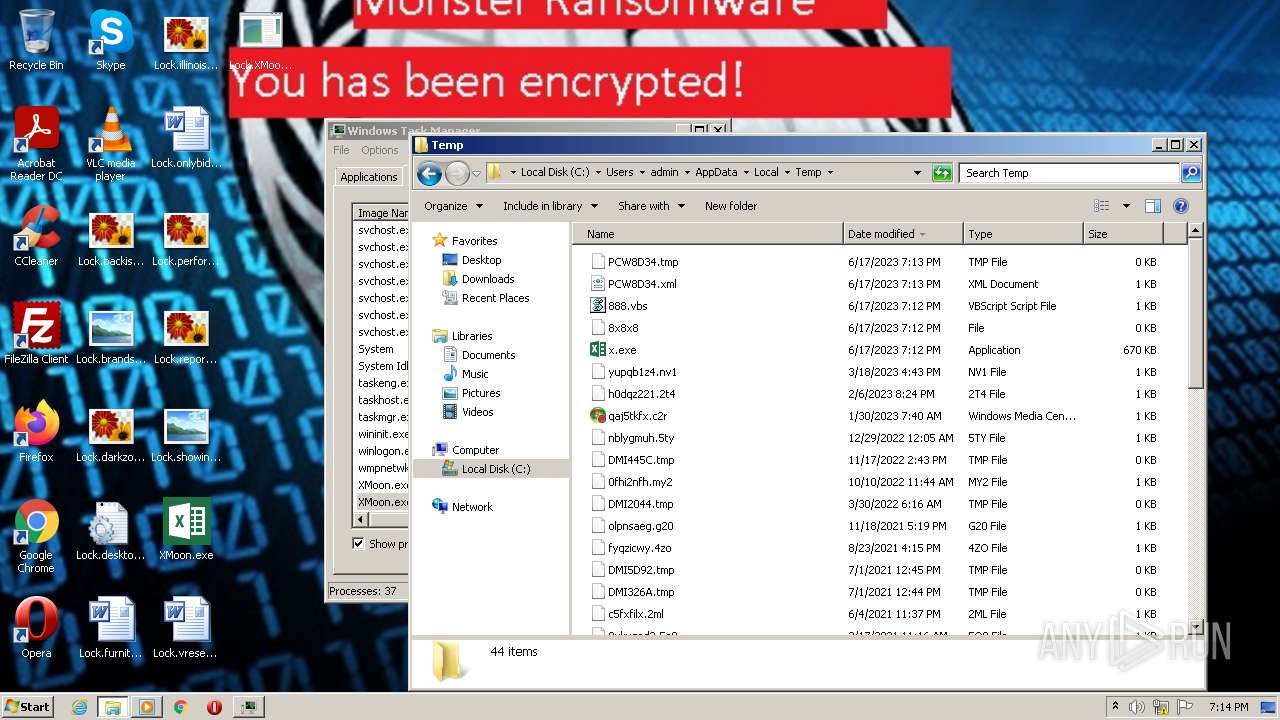
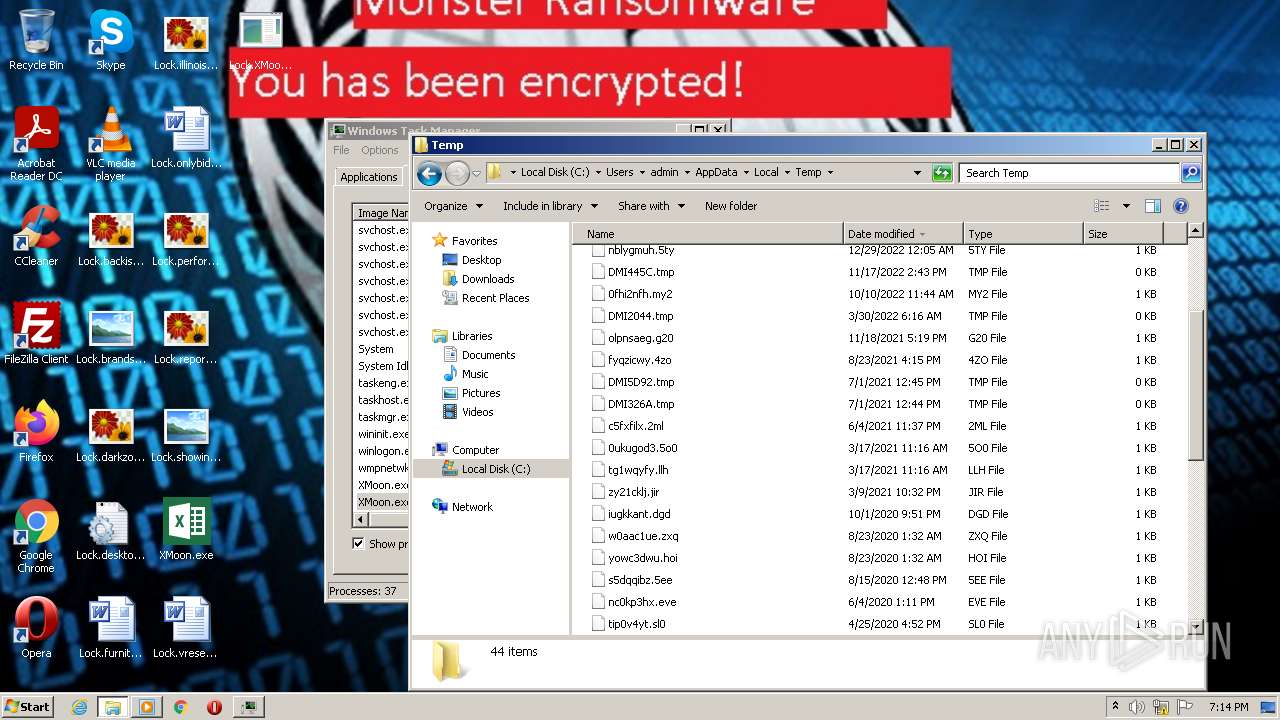
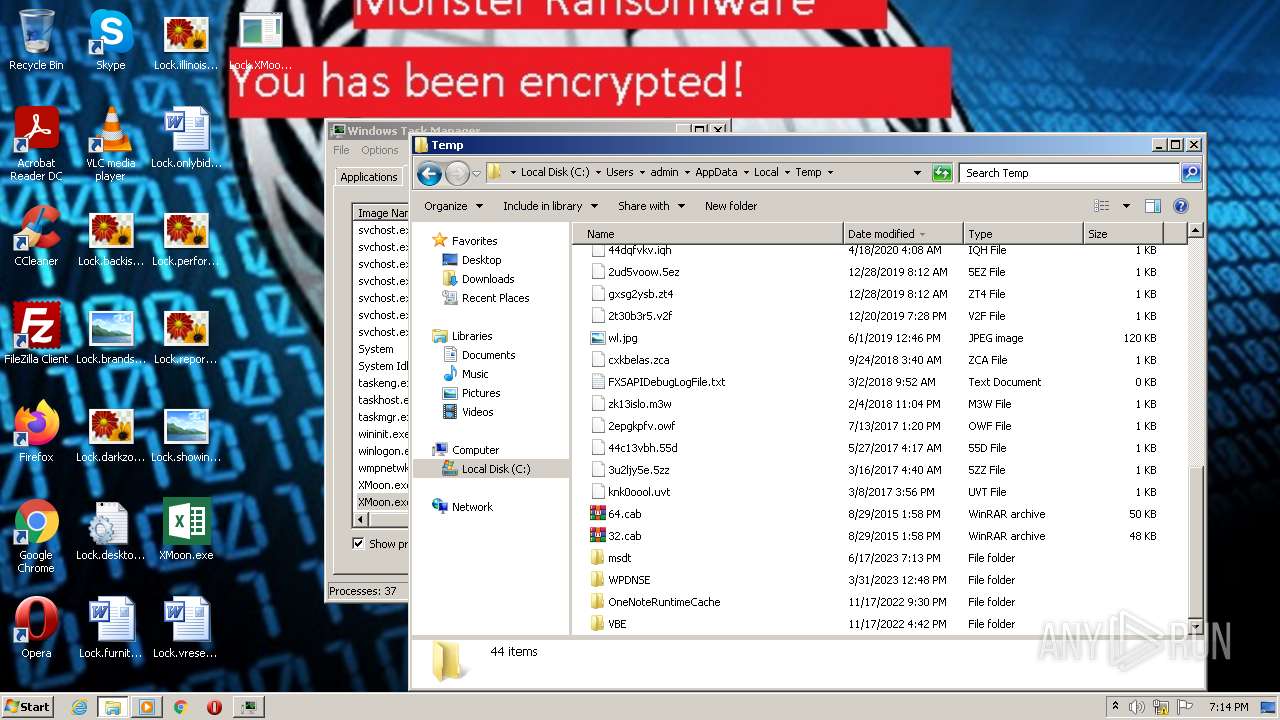
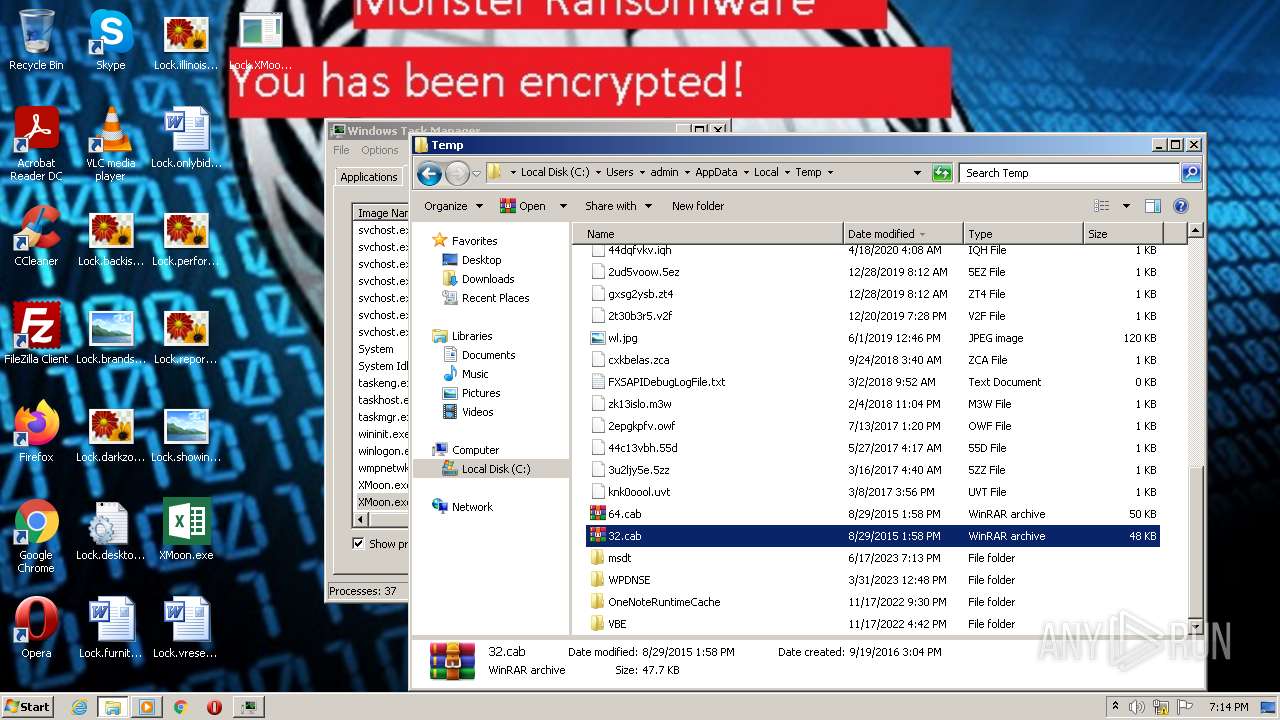
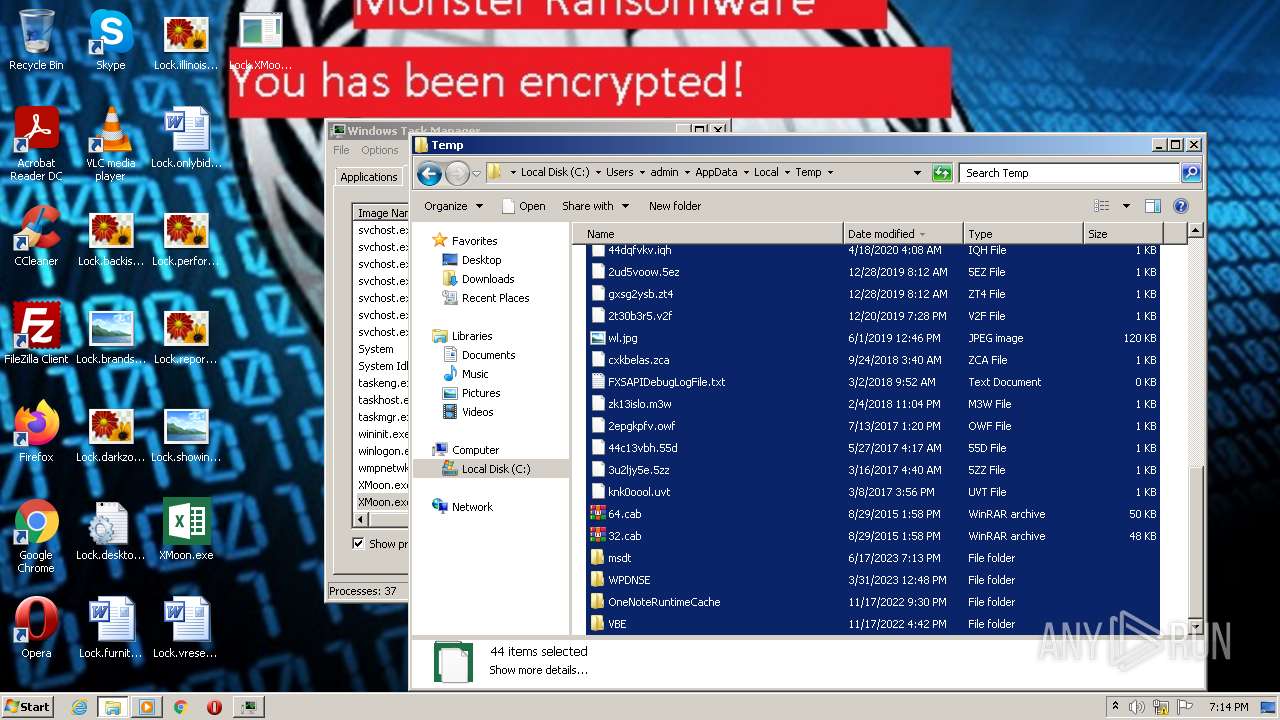
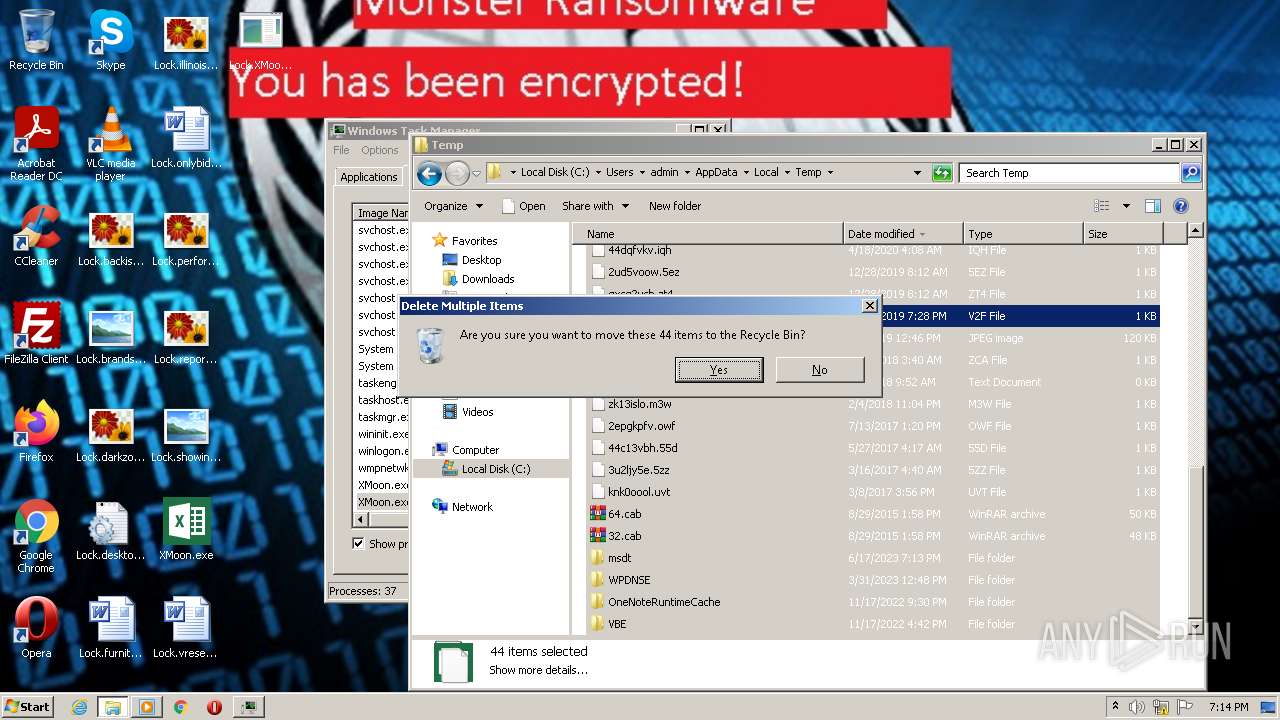
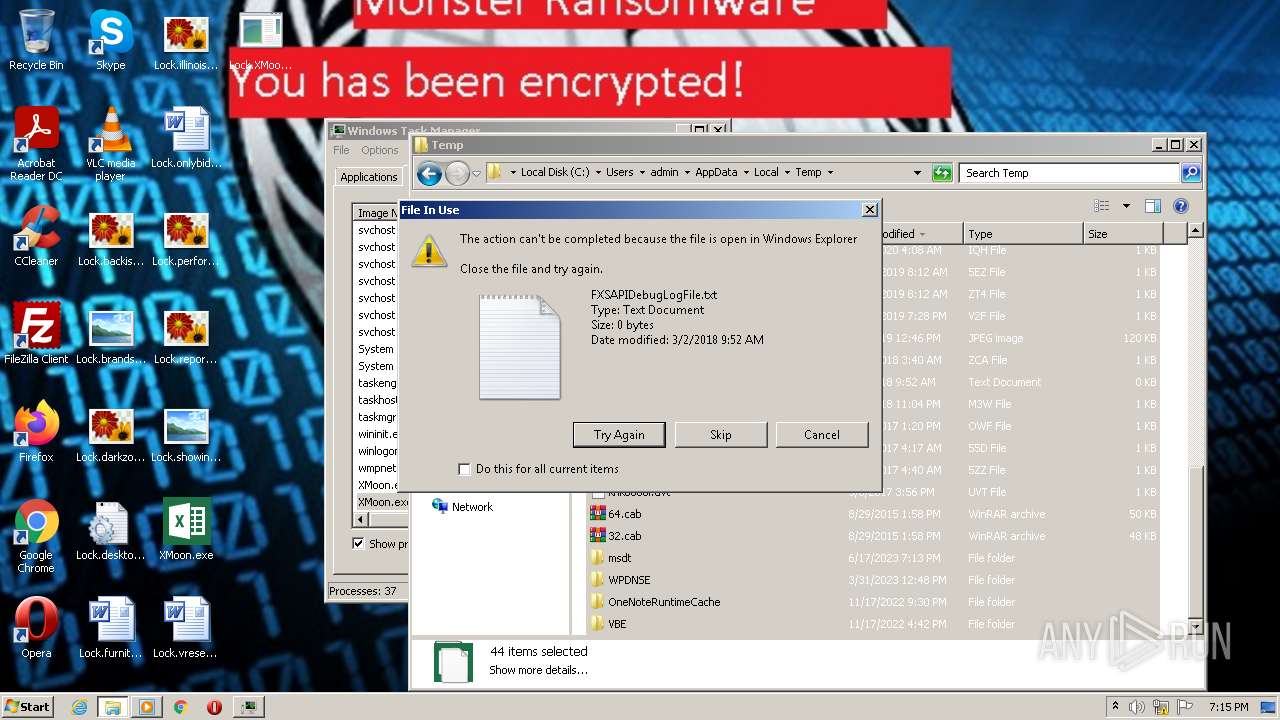
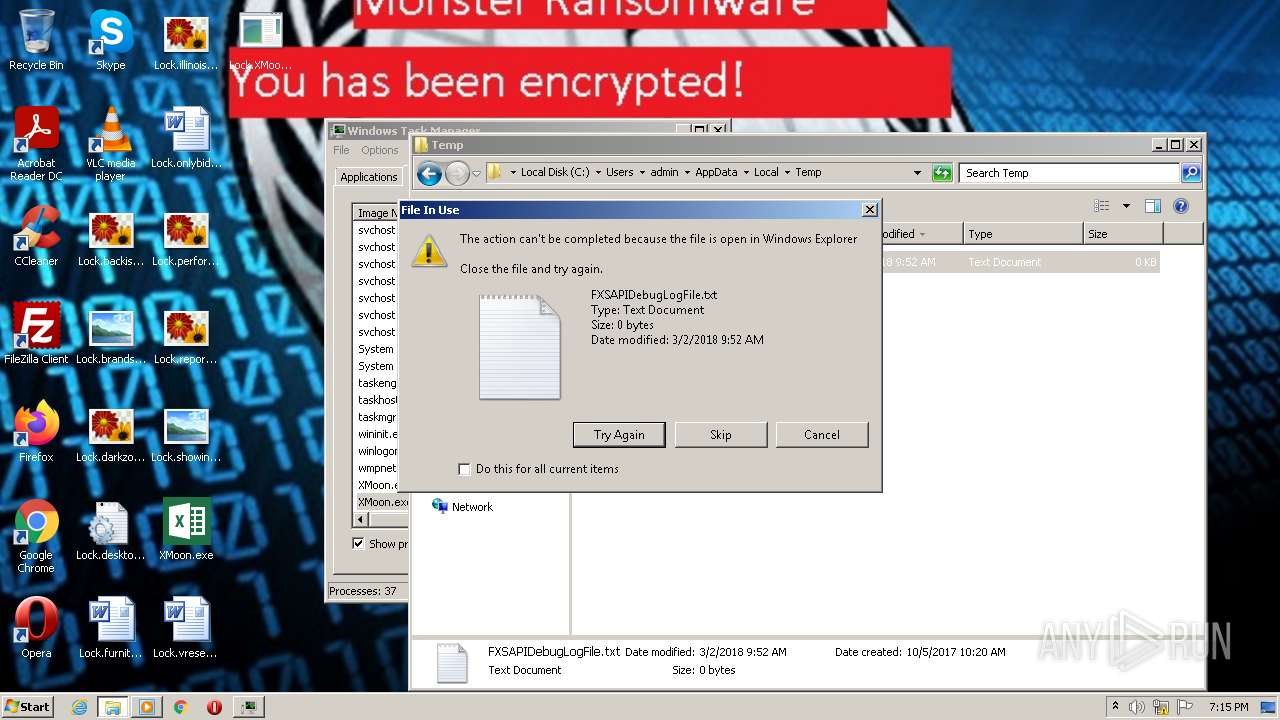
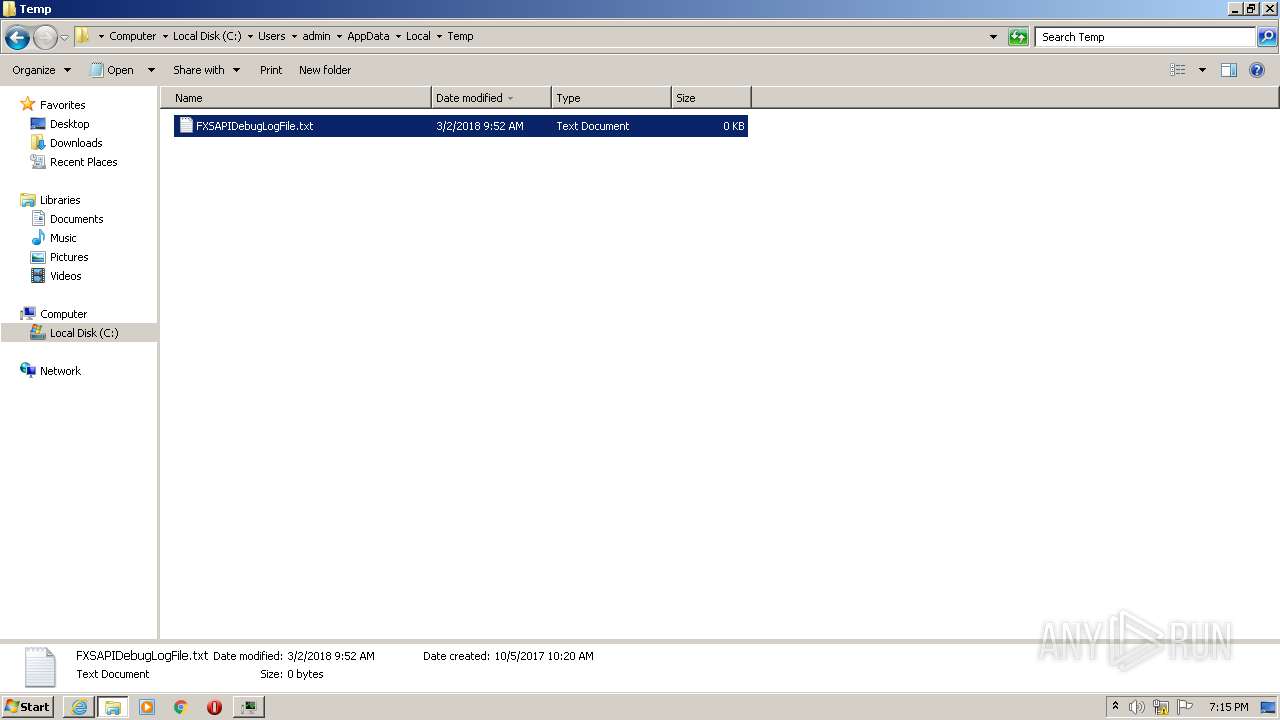
Create files in a temporary directory
- XMoon.exe (PID: 2732)
- XMoon.exe (PID: 1596)
- XMoon.exe (PID: 3976)
- pcwrun.exe (PID: 3232)
- msdt.exe (PID: 3884)
- sdiagnhost.exe (PID: 2576)
- csc.exe (PID: 3056)
- cvtres.exe (PID: 1364)
- csc.exe (PID: 3408)
- cvtres.exe (PID: 3536)
- csc.exe (PID: 3724)
- cvtres.exe (PID: 3816)
- sdiagnhost.exe (PID: 1560)
- csc.exe (PID: 3672)
- cvtres.exe (PID: 2924)
- cvtres.exe (PID: 3024)
- csc.exe (PID: 2424)
Reads the machine GUID from the registry
- XMoon.exe (PID: 2732)
- XMoon.exe (PID: 1596)
- XMoon.exe (PID: 3976)
- cvtres.exe (PID: 1364)
- csc.exe (PID: 3056)
- cvtres.exe (PID: 3536)
- csc.exe (PID: 3724)
- cvtres.exe (PID: 3816)
- csc.exe (PID: 3672)
- cvtres.exe (PID: 2924)
- csc.exe (PID: 2424)
- cvtres.exe (PID: 3024)
- csc.exe (PID: 3408)
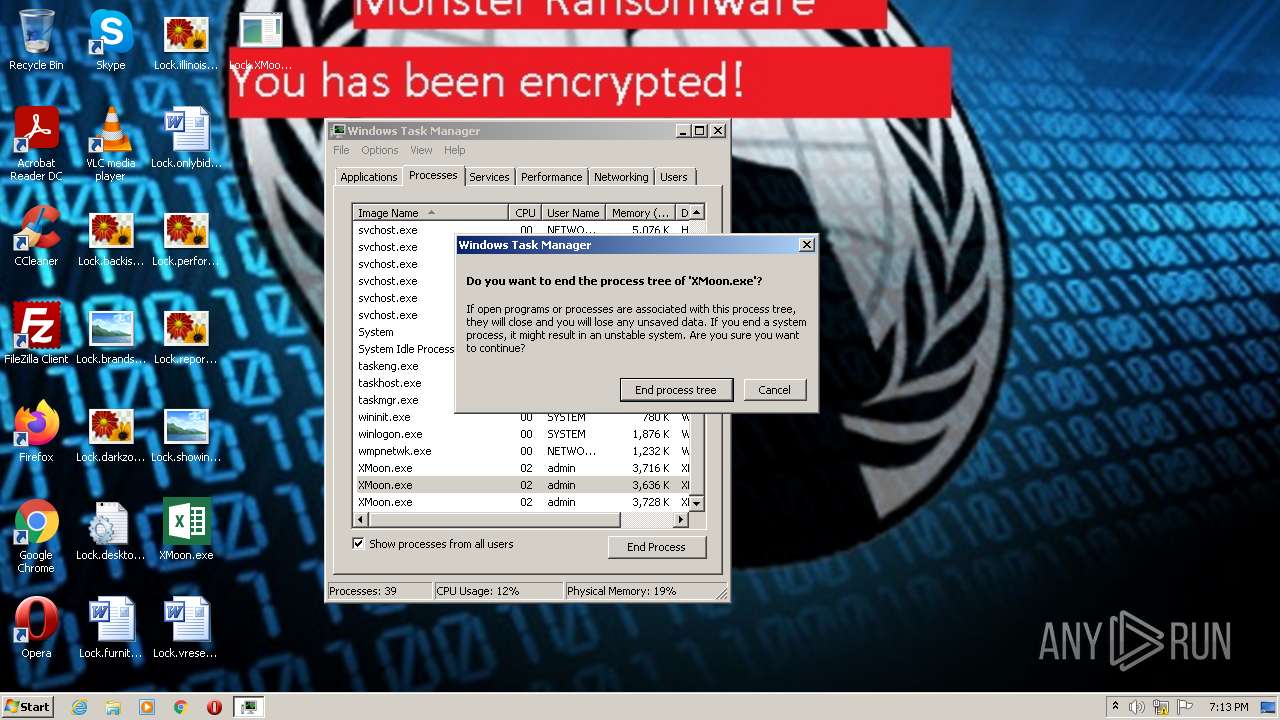
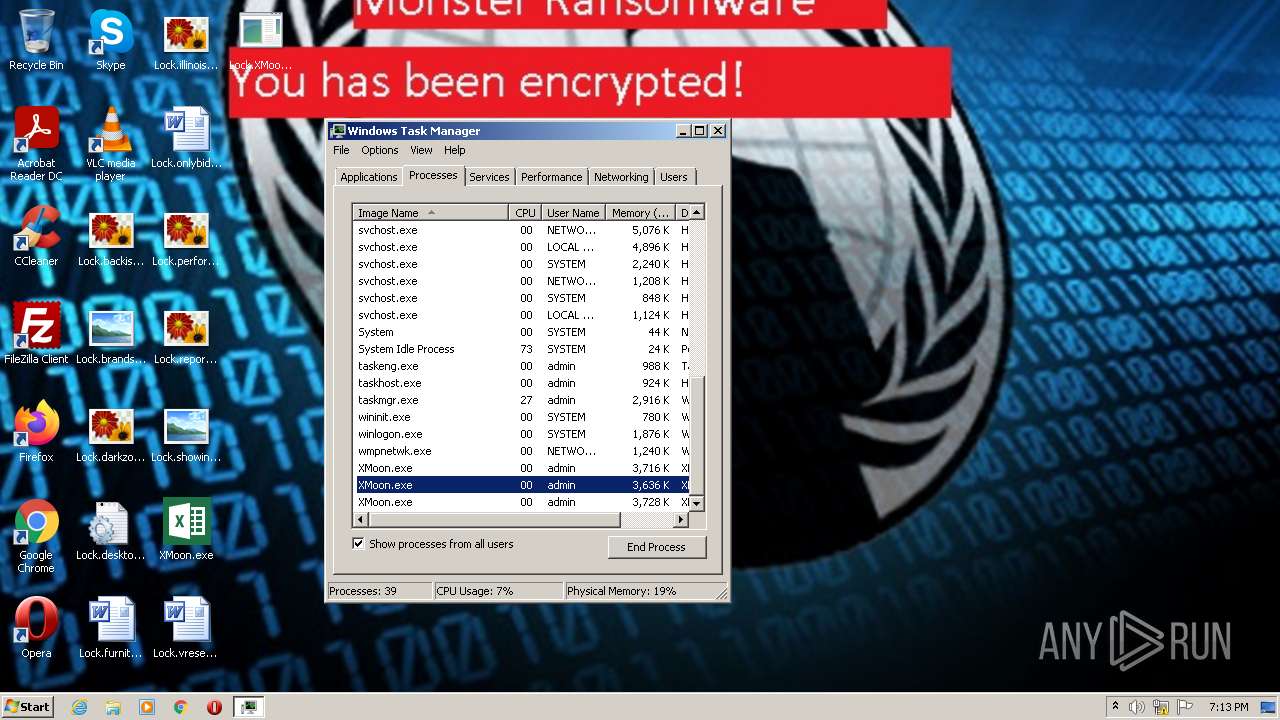
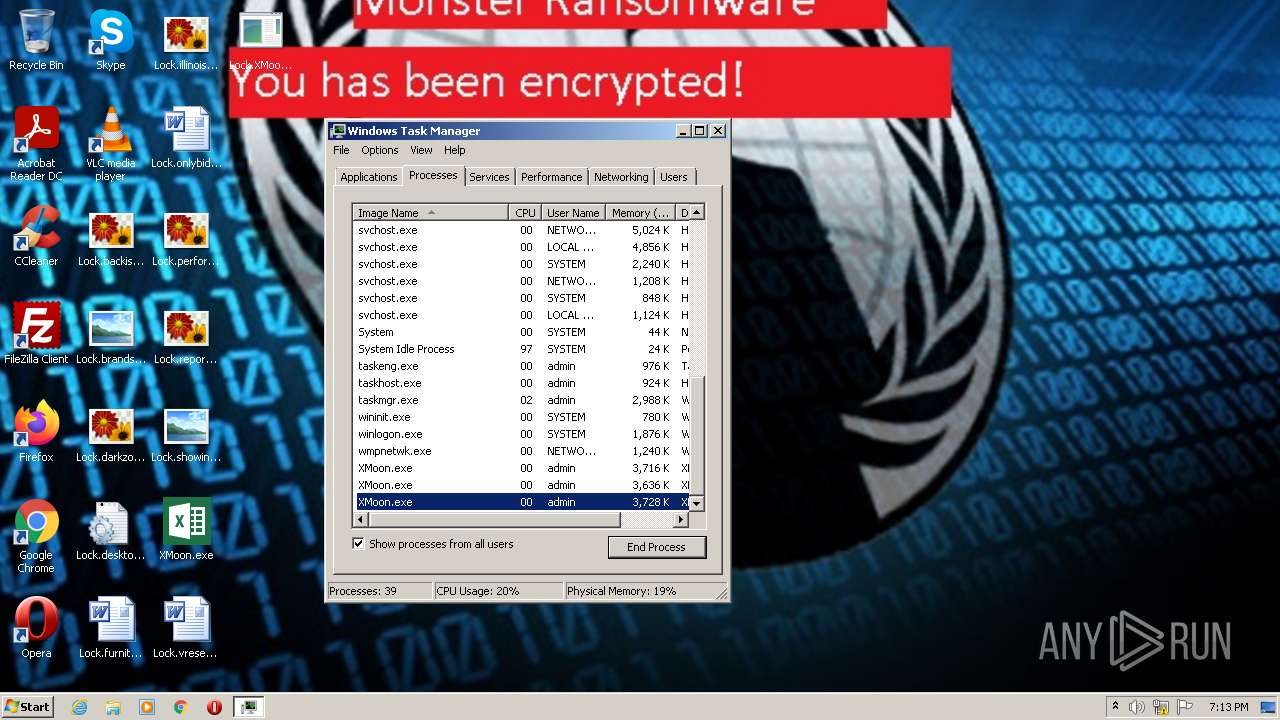
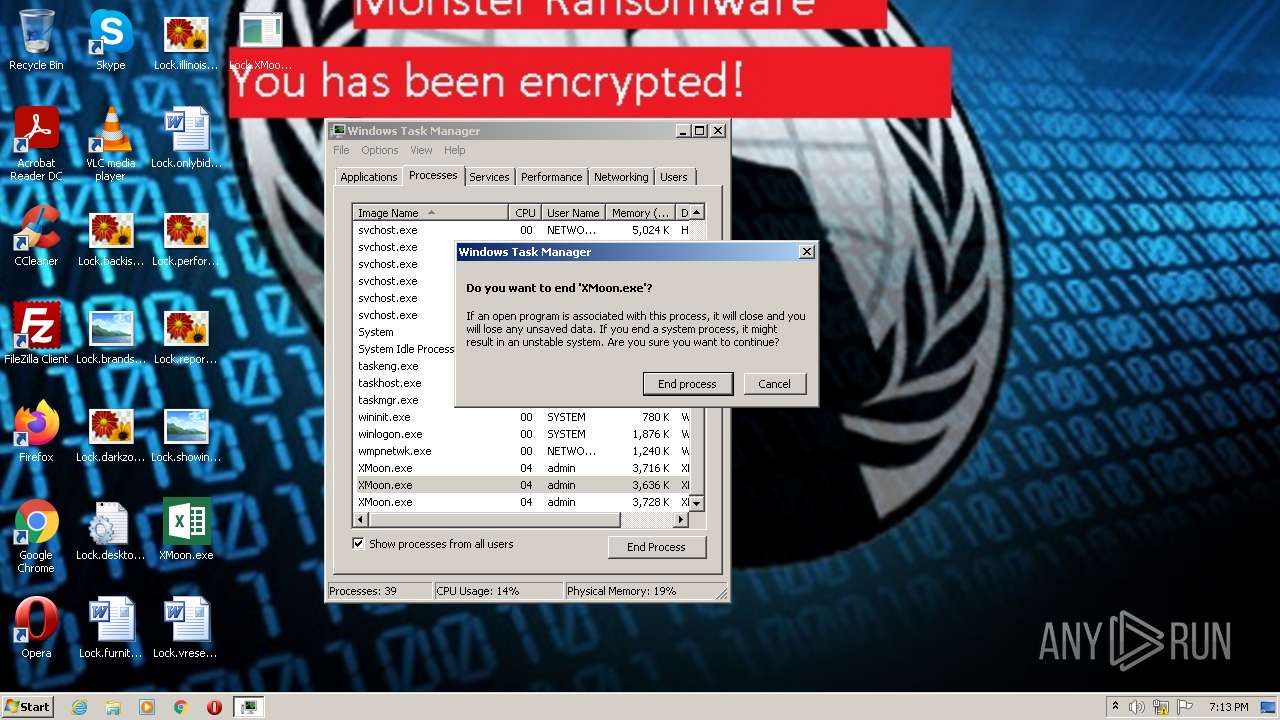
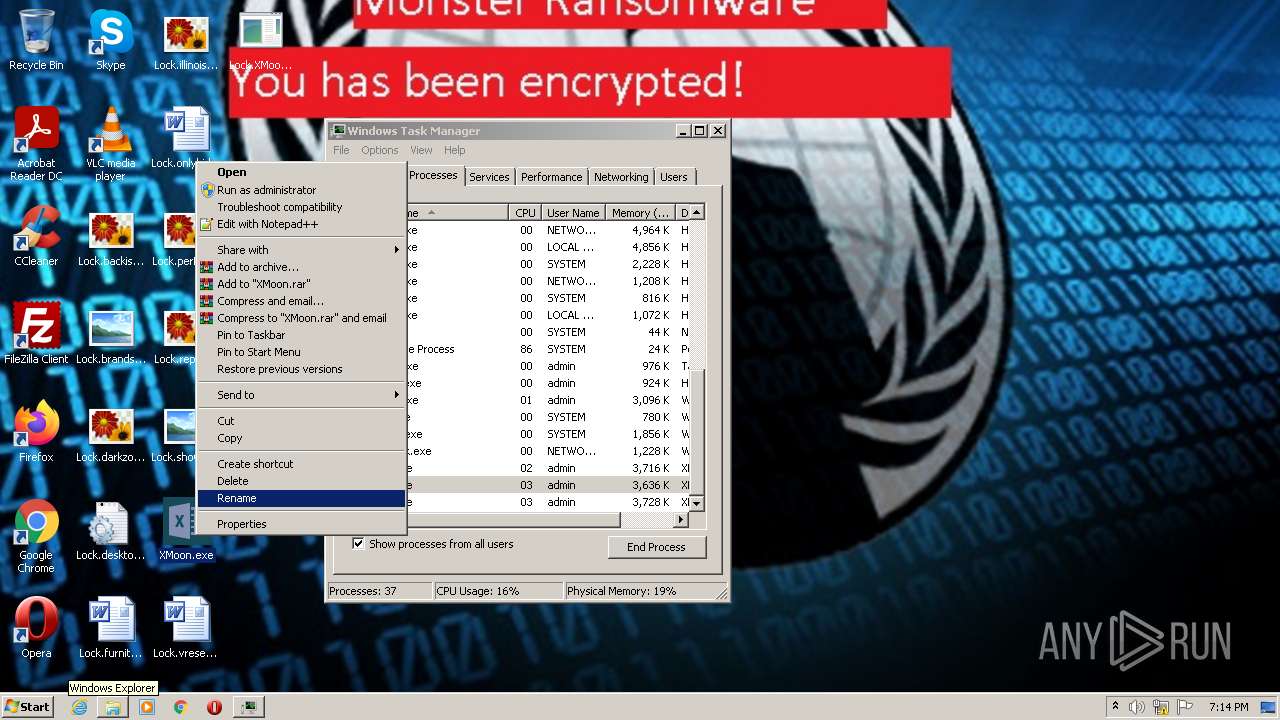
Manual execution by a user
- XMoon.exe (PID: 1596)
- XMoon.exe (PID: 3976)
- taskmgr.exe (PID: 1060)
- pcwrun.exe (PID: 3232)
- explorer.exe (PID: 3268)
- WinRAR.exe (PID: 2244)
- WinRAR.exe (PID: 3536)
Reads security settings of Internet Explorer
- msdt.exe (PID: 3884)
- sdiagnhost.exe (PID: 2576)
- sdiagnhost.exe (PID: 1560)
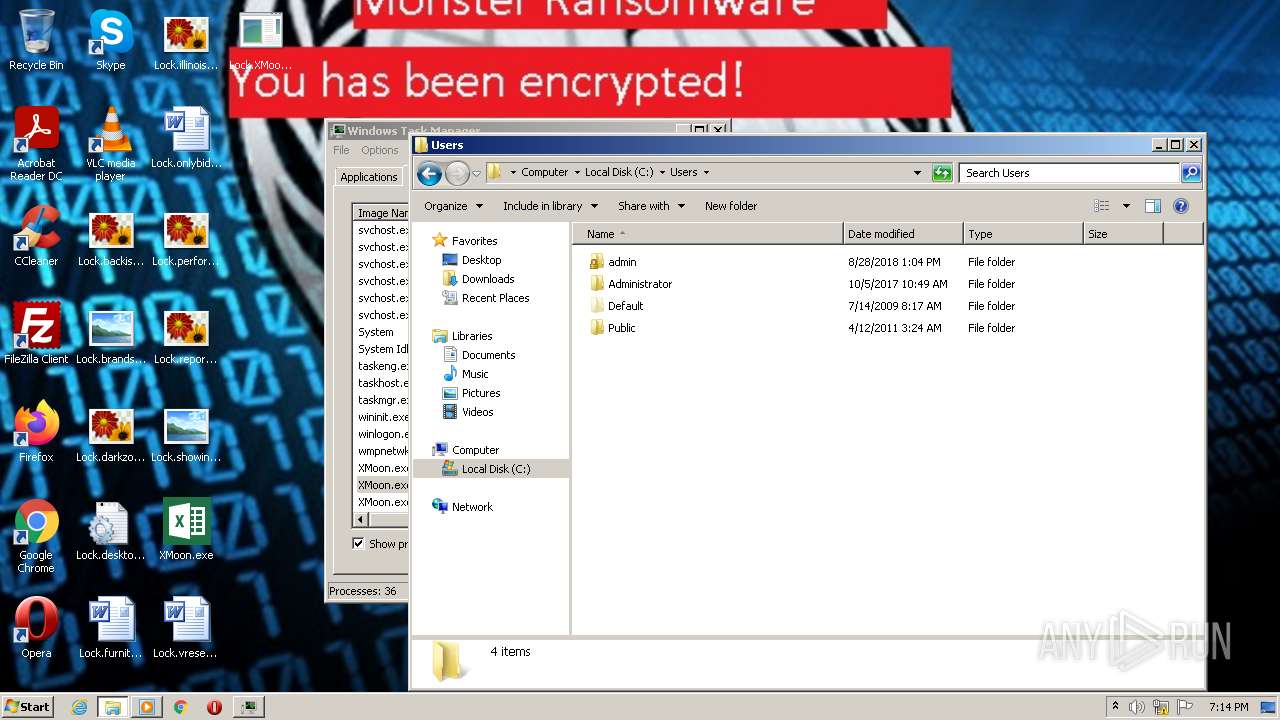
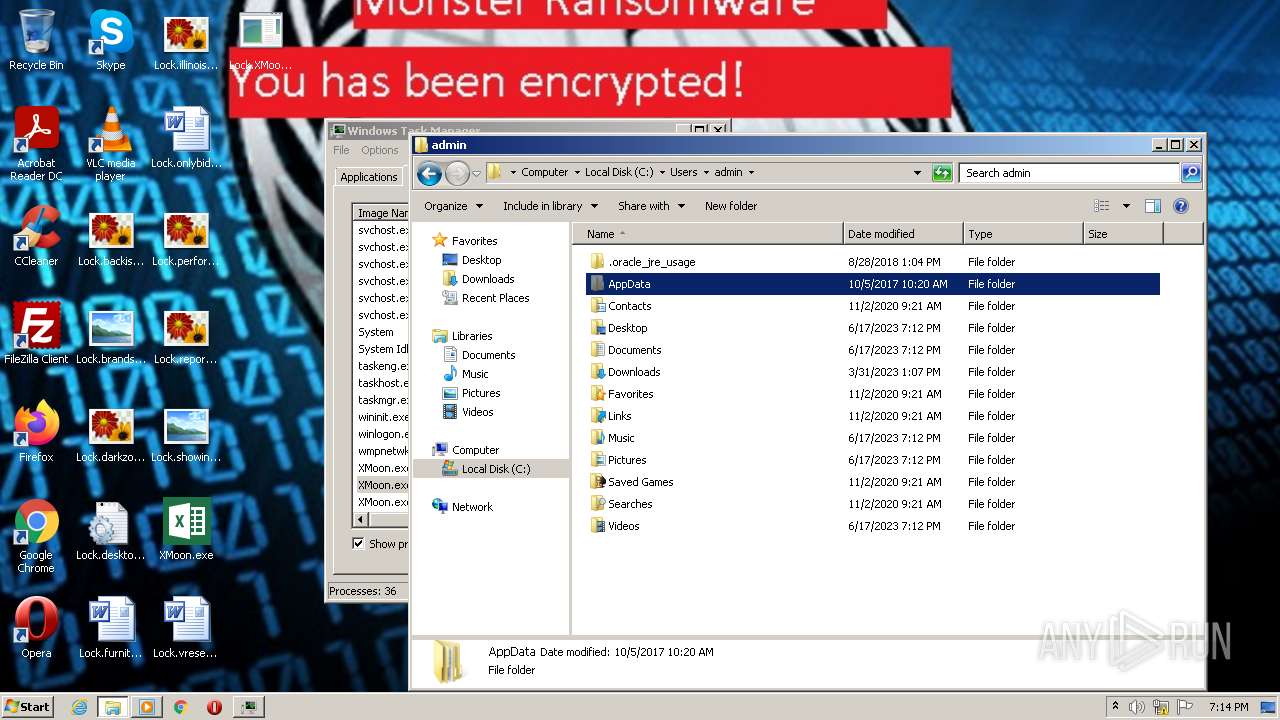
Creates files or folders in the user directory
- XMoon.exe (PID: 2732)
- sdiagnhost.exe (PID: 2576)
- msdt.exe (PID: 3884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | AutoIt3 compiled script executable (88.1) |
|---|---|---|
| .exe | | | UPX compressed Win32 Executable (4.6) |
| .exe | | | Win32 EXE Yoda's Crypter (4.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.1) |
| .exe | | | Win32 Executable (generic) (0.7) |
EXIF
EXE
| CompiledScript: | AutoIt v3 Script: 3, 3, 8, 1 |
|---|---|
| FileVersion: | 3, 3, 8, 1 |
| FileDescription: | - |
| CharacterSet: | Unicode |
| LanguageCode: | English (British) |
| FileSubtype: | - |
| ObjectFileType: | Unknown |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0017 |
| ProductVersionNumber: | 3.3.8.1 |
| FileVersionNumber: | 3.3.8.1 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0xdaea0 |
| UninitializedDataSize: | 622592 |
| InitializedDataSize: | 172032 |
| CodeSize: | 274432 |
| LinkerVersion: | 10 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, Large address aware, 32-bit |
| TimeStamp: | 2012:01:29 21:32:28+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-Jan-2012 21:32:28 |
| Detected languages: |
|
| FileDescription: | - |
| FileVersion: | 3, 3, 8, 1 |
| CompiledScript: | AutoIt v3 Script: 3, 3, 8, 1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 29-Jan-2012 21:32:28 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00098000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00099000 | 0x00043000 | 0x00042200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.92944 |
.rsrc | 0x000DC000 | 0x0002A000 | 0x00029600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.04776 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.01246 | 620 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.66371 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
3 | 2.25499 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
4 | 7.57713 | 3125 | UNKNOWN | English - United Kingdom | RT_ICON |
5 | 2.28267 | 67624 | UNKNOWN | English - United Kingdom | RT_ICON |
6 | 2.12925 | 38056 | UNKNOWN | English - United Kingdom | RT_ICON |
7 | 7.77597 | 1328 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
8 | 7.80166 | 1680 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
9 | 7.71722 | 1232 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
10 | 7.7285 | 1532 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.DLL |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
USER32.dll |
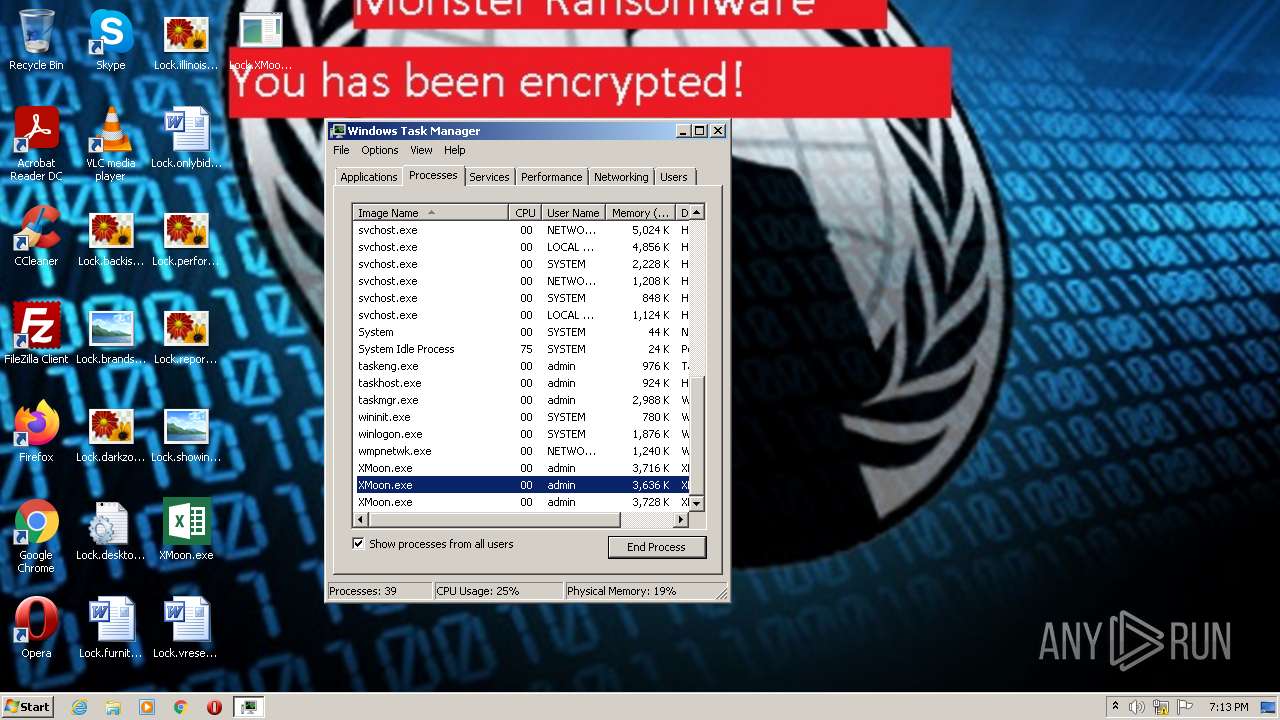
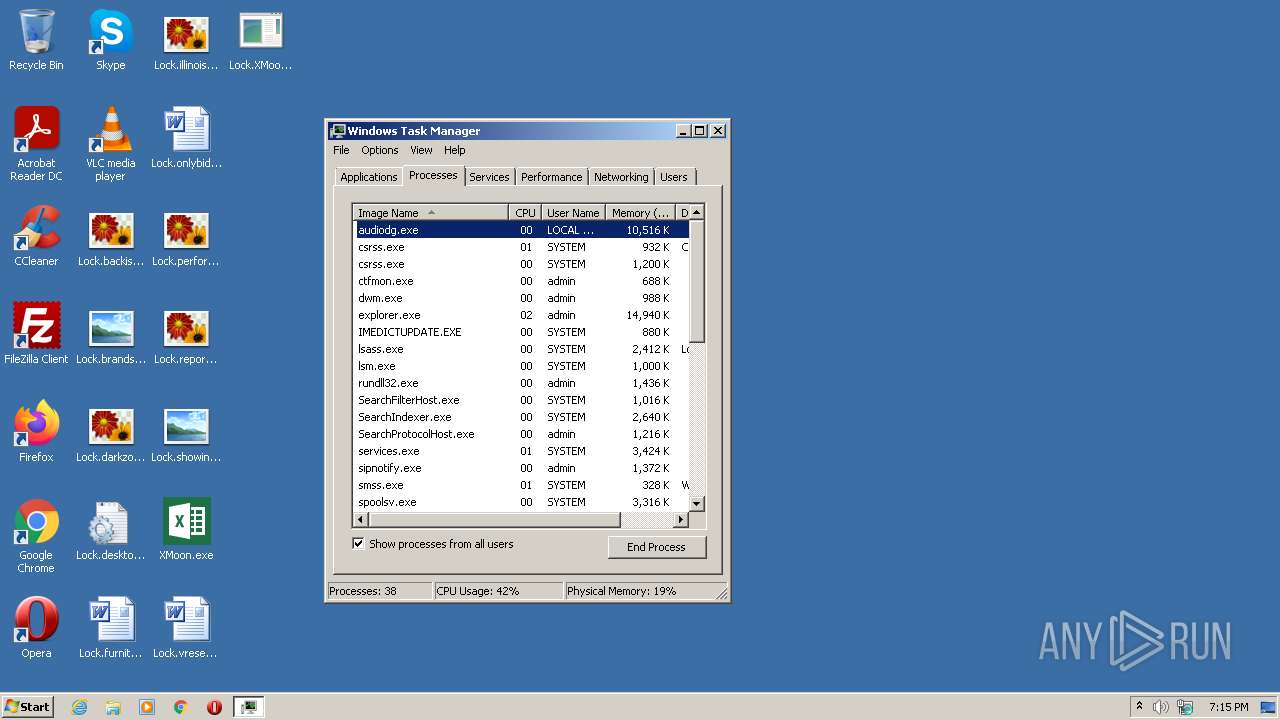
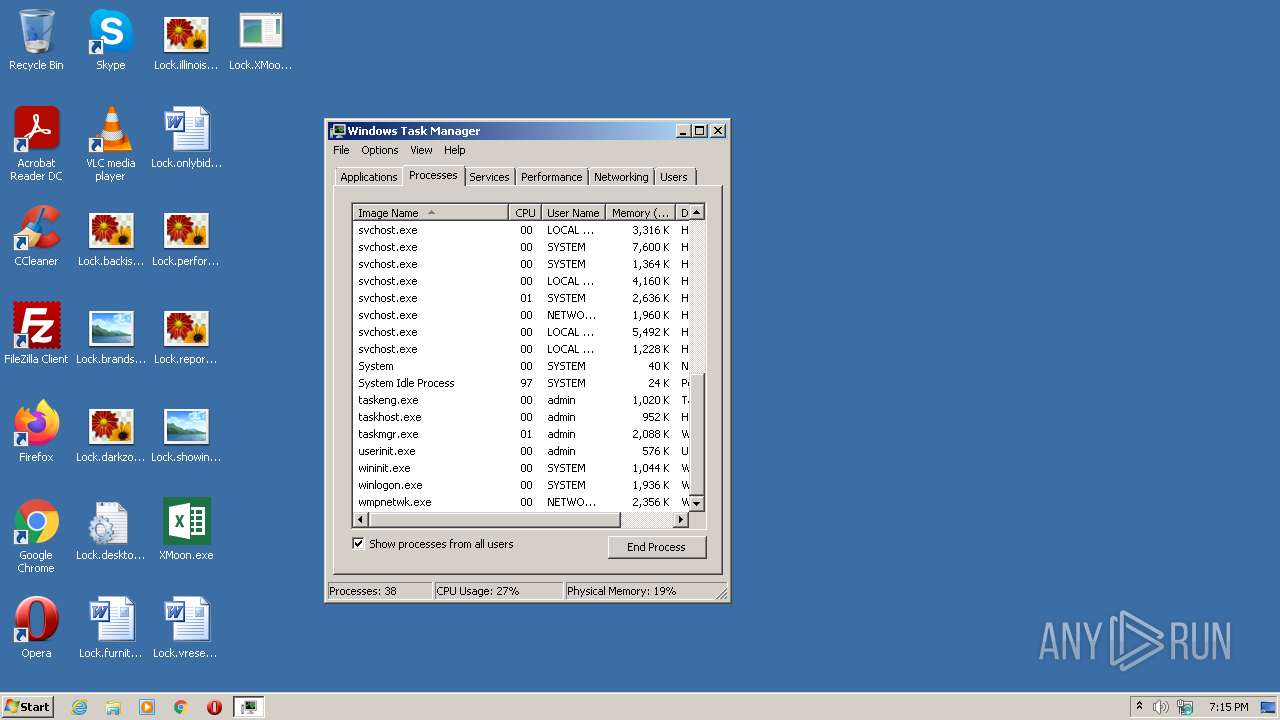
Total processes
114
Monitored processes
46
Malicious processes
13
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
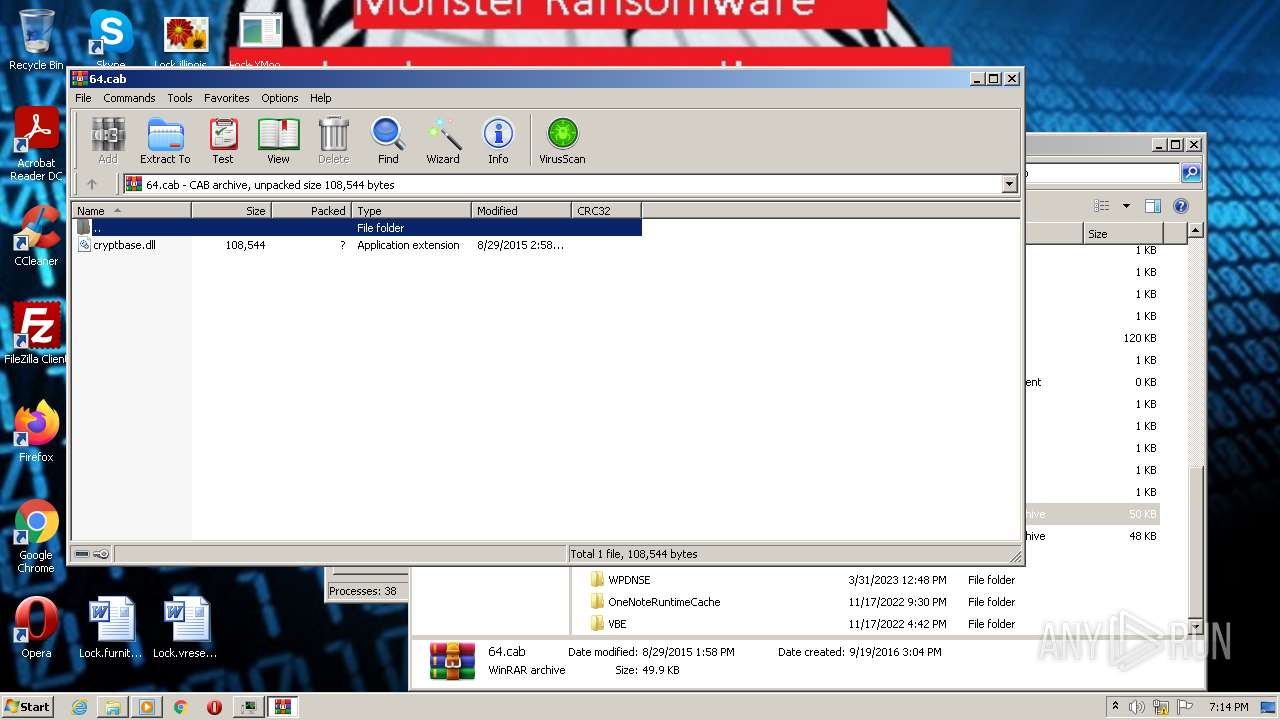
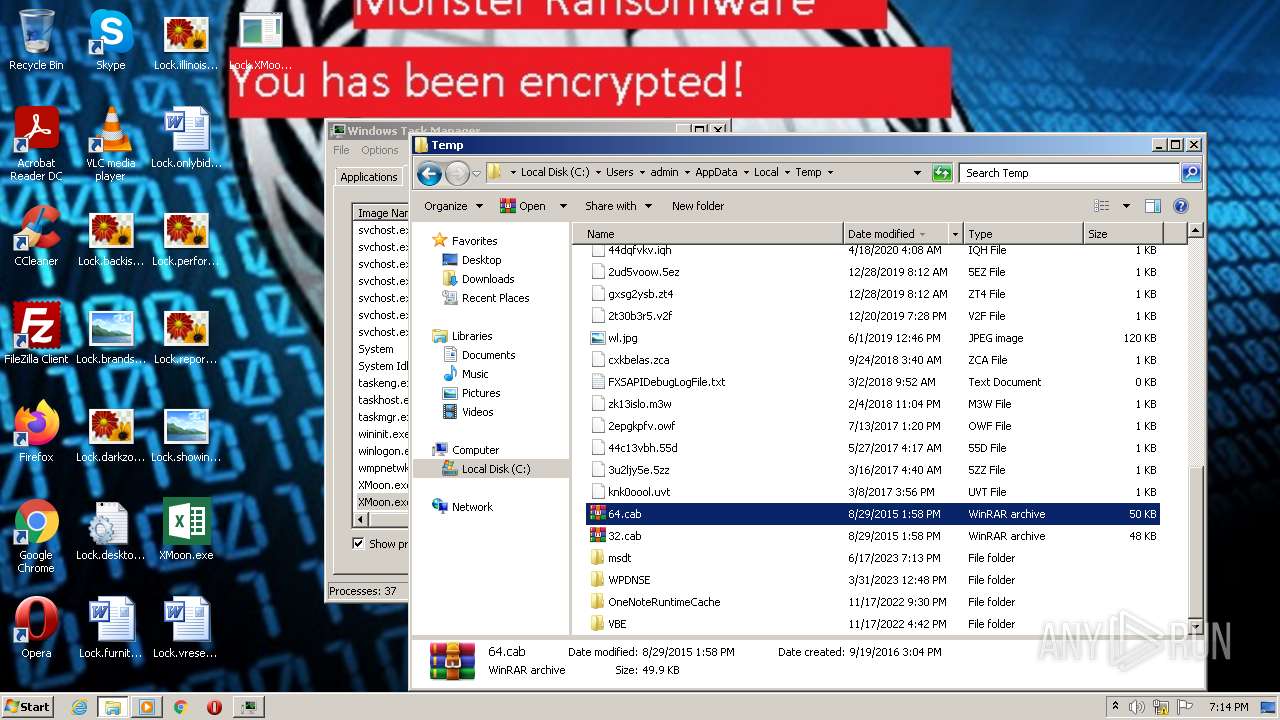
| 624 | C:\Windows\system32\cmd.exe /c wusa C:\Users\admin\AppData\Local\Temp\32.cab /quiet /extract:C:\Windows\system32\migwiz\ & exit | C:\Windows\System32\cmd.exe | — | XMoon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 768 | "C:\Windows\System32\migwiz\migwiz.exe" C:\Windows\System32\cmd.exe /c C:\Windows\System32\reg.exe ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System /v EnableLUA /t REG_DWORD /d 0 /f | C:\Windows\System32\migwiz\migwiz.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Easy Transfer Application Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 784 | "C:\Windows\system32\wusa.exe" C:\Users\admin\AppData\Local\Temp\32.cab /quiet /extract:C:\Windows\system32\migwiz\ | C:\Windows\System32\wusa.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Update Standalone Installer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1060 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\System32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1300 | C:\Windows\System32\reg.exe ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System /v EnableLUA /t REG_DWORD /d 0 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1328 | "C:\Windows\System32\migwiz\migwiz.exe" C:\Windows\System32\cmd.exe /c C:\Windows\System32\reg.exe ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System /v EnableLUA /t REG_DWORD /d 0 /f | C:\Windows\System32\migwiz\migwiz.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Easy Transfer Application Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1360 | "C:\Windows\System32\migwiz\migwiz.exe" C:\Windows\System32\cmd.exe /c C:\Windows\System32\reg.exe ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System /v EnableLUA /t REG_DWORD /d 0 /f | C:\Windows\System32\migwiz\migwiz.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Easy Transfer Application Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1364 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES9266.tmp" "c:\Users\admin\AppData\Local\Temp\CSC9265.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.5003 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 1560 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1584 | C:\Windows\system32\cmd.exe /c wusa C:\Users\admin\AppData\Local\Temp\32.cab /quiet /extract:C:\Windows\system32\migwiz\ & exit | C:\Windows\System32\cmd.exe | — | XMoon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
14 013
Read events
13 501
Write events
512
Delete events
0
Modification events
| (PID) Process: | (624) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (624) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (624) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (624) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2732) XMoon.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2732) XMoon.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2732) XMoon.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2732) XMoon.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1976) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1976) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
16
Suspicious files
64
Text files
56
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
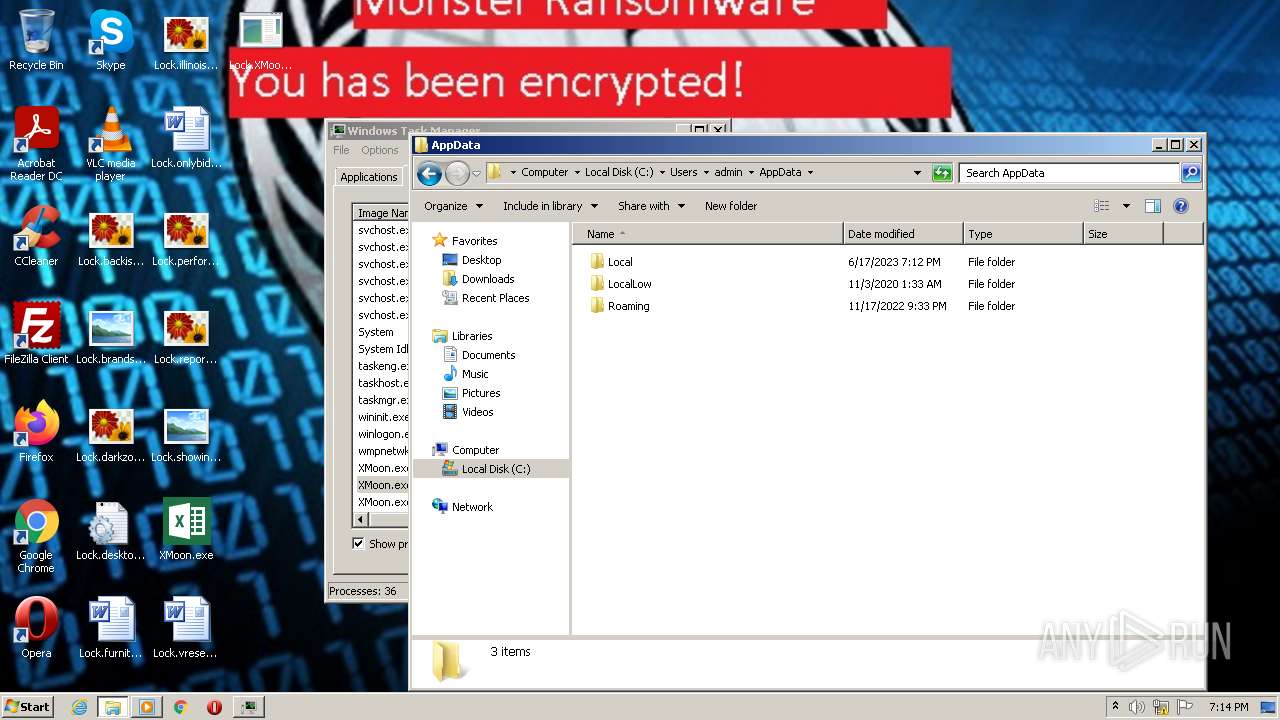
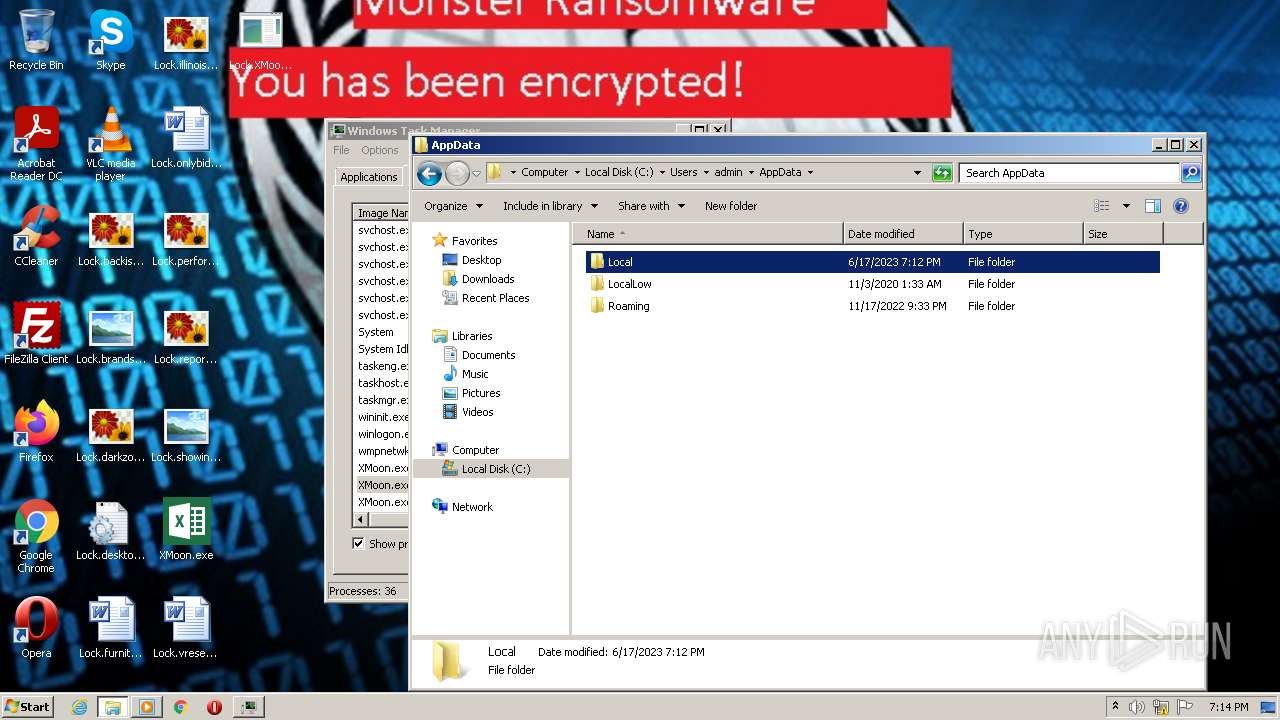
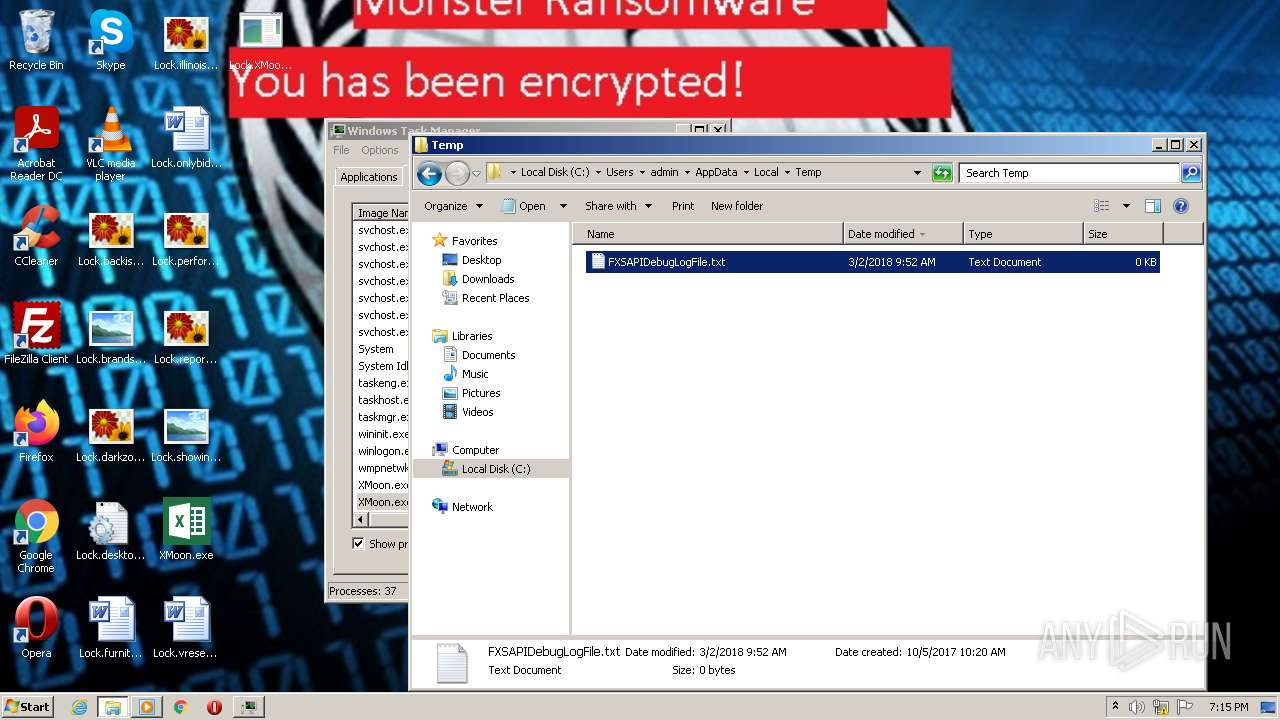
| 2732 | XMoon.exe | C:\Users\admin\AppData\Local\Temp\vudusbq | text | |
MD5:1D7B0CD12A825917A17C121A0A187CF9 | SHA256:74CB8D2B443334996287C79EE7EFC5905E25319101734B29B82164D3AC680B32 | |||
| 2732 | XMoon.exe | C:\Users\admin\AppData\Local\Temp\aut64E3.tmp | compressed | |
MD5:8CFA6B4ACD035A2651291A2A4623B1C7 | SHA256:6E438201A14A70980048D2377C2195608D5DC2CF915F489C0A59AC0627C98FA9 | |||
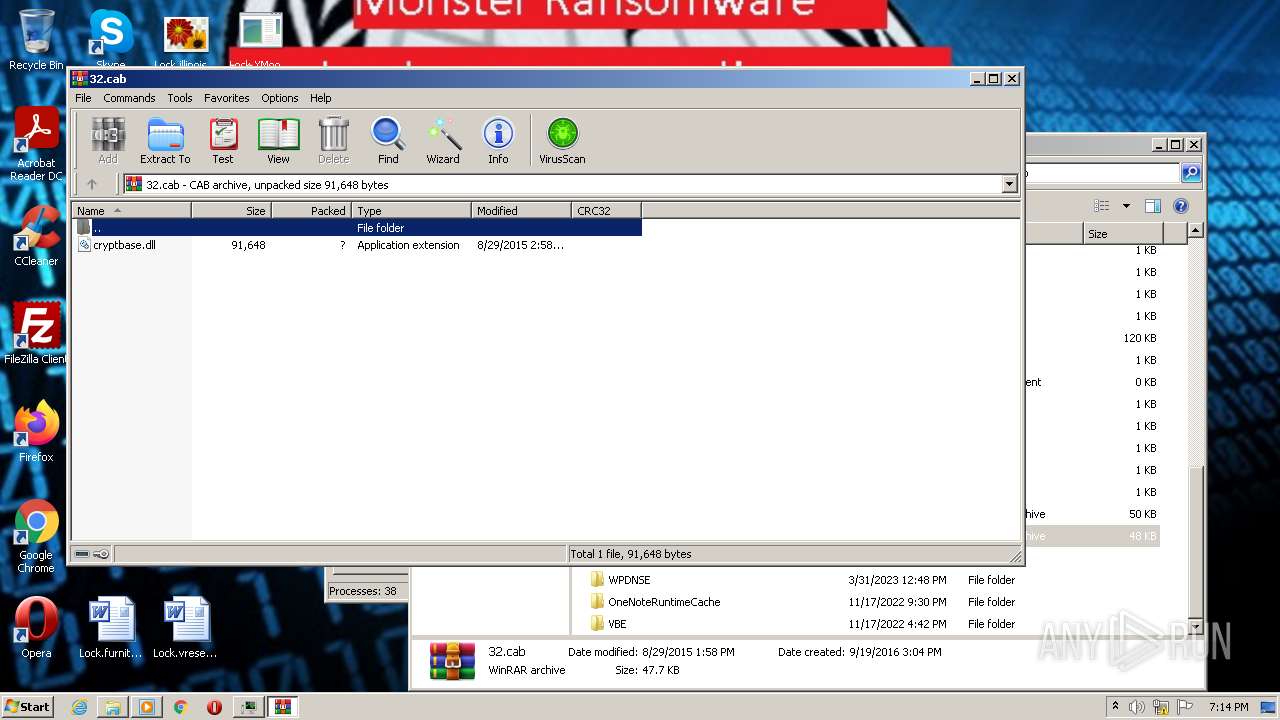
| 2732 | XMoon.exe | C:\Users\admin\AppData\Local\Temp\32.cab | compressed | |
MD5:9DDA4DB9E90FF039AD5A58785B9D626D | SHA256:FC31B205D5E4F32FA0C71C8F72EE06B92A28BD8690F71AB8F94FF401AF2228FE | |||
| 2732 | XMoon.exe | C:\Users\admin\AppData\Local\Lock.IconCache.db | — | |
MD5:— | SHA256:— | |||
| 2732 | XMoon.exe | C:\Users\admin\AppData\Local\Temp\aut64E2.tmp | compressed | |
MD5:9DDA4DB9E90FF039AD5A58785B9D626D | SHA256:FC31B205D5E4F32FA0C71C8F72EE06B92A28BD8690F71AB8F94FF401AF2228FE | |||
| 2732 | XMoon.exe | C:\Users\admin\AppData\Local\Temp\aut64C2.tmp | binary | |
MD5:1D6CDF0C07339EA9CBE8B8CA91F8AA99 | SHA256:37BDA065F92164E6AAA39224B70B09703B1435077AB502195AFFC43281B3CED8 | |||
| 2732 | XMoon.exe | C:\Users\admin\AppData\Local\Temp\64.cab | compressed | |
MD5:8CFA6B4ACD035A2651291A2A4623B1C7 | SHA256:6E438201A14A70980048D2377C2195608D5DC2CF915F489C0A59AC0627C98FA9 | |||
| 2732 | XMoon.exe | C:\Users\admin\AppData\Local\Temp\888.vbs | text | |
MD5:8BE57121A3ECAE9C90CCE4ADF00F2454 | SHA256:35D7204F9582B63B47942A4DF9A55B8825B6D0AF295B641F6257C39F7DDA5F5E | |||
| 784 | wusa.exe | C:\Windows\System32\migwiz\cryptbase.dll | executable | |
MD5:D98DE49616F8218D1978DC701A72AE3A | SHA256:856623BC2E40D43960E2309F317F7D2C841650D91F2CD847003E0396299C3F98 | |||
| 2732 | XMoon.exe | C:\Users\admin\Desktop\Lock.furniturepublications.rtf | binary | |
MD5:895221BE2CAE7DA5C55B288C9F5125D3 | SHA256:73D2221CF41BB364196ED54BF055C722E2B92B2EDDBB122F228CBB6C9B9256A6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|