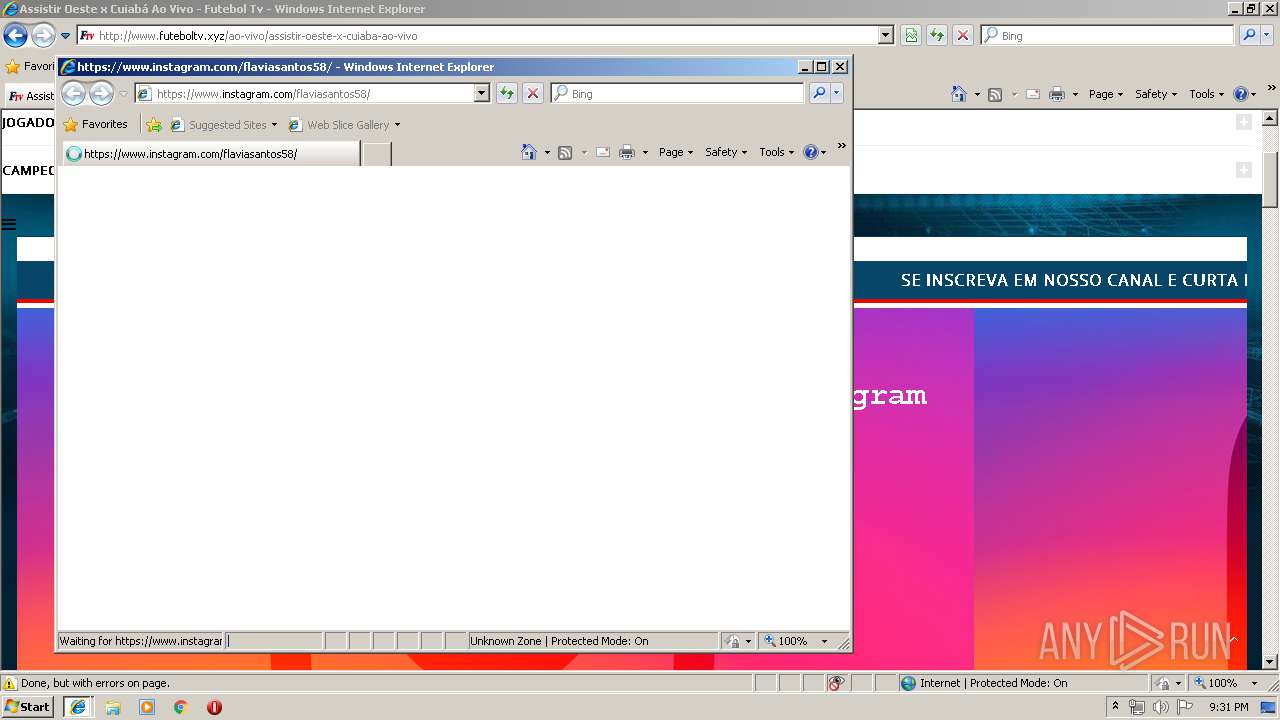
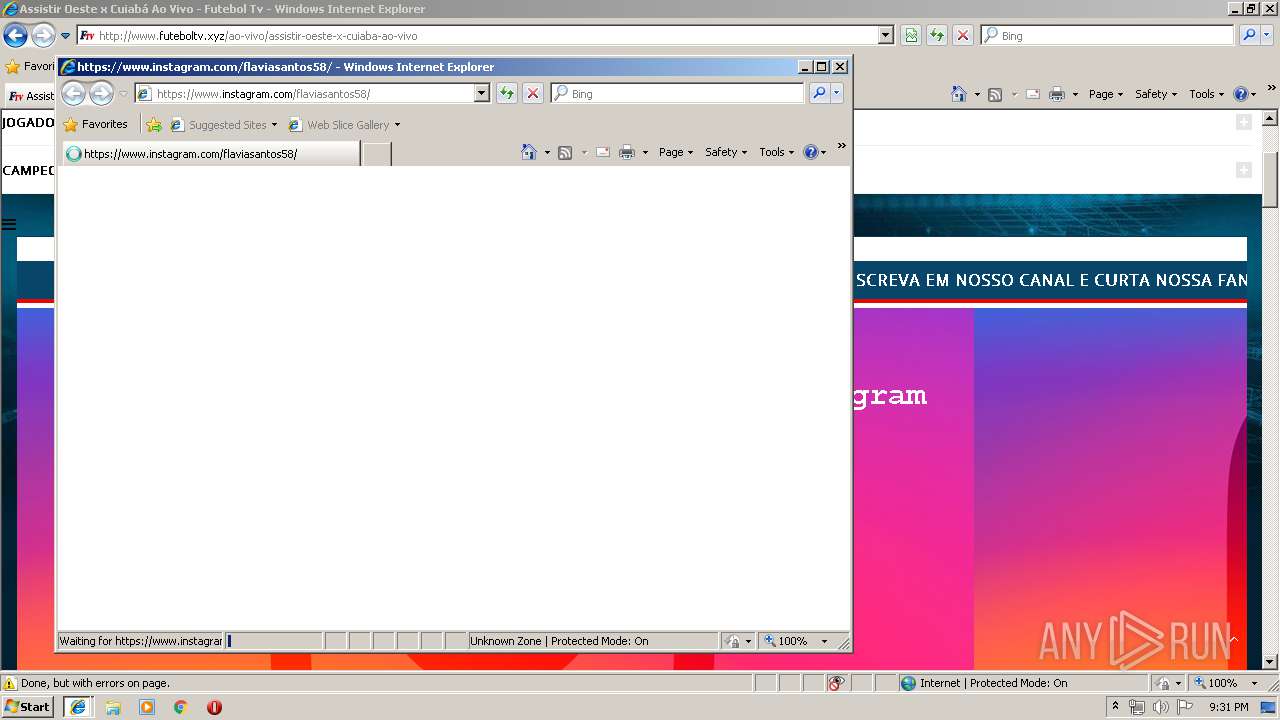
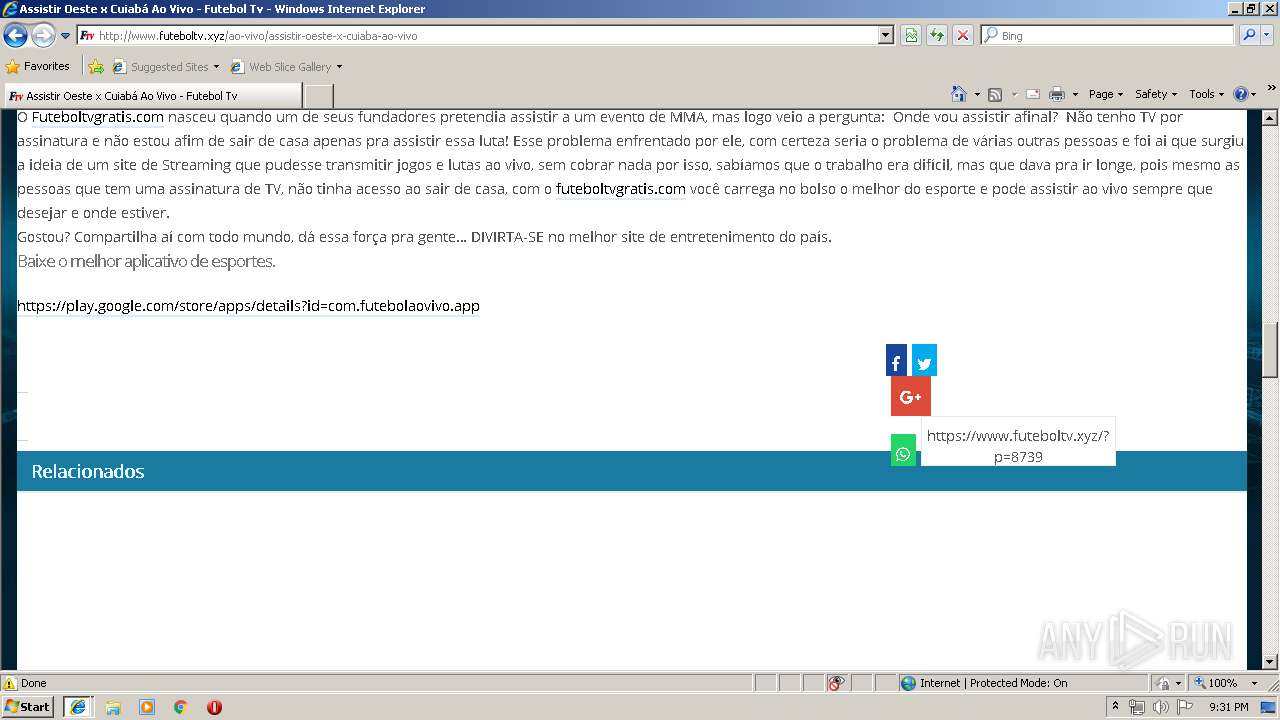
| URL: | https://www.futeboltv.xyz |
| Full analysis: | https://app.any.run/tasks/bfbe1055-ee77-4f23-aeef-bd18186f71d7 |
| Verdict: | No threats detected |
| Analysis date: | May 14, 2019, 20:30:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 02AE6D29463077A67226EF7EC3676690 |
| SHA1: | 12FFD1845B8313D0C3DB3C583858E81D1ED5F657 |
| SHA256: | EA08AA776CCA1FC2342E04FFE5B96BCED4C0468FEAF48BF28D8041A5047CB8AA |
| SSDEEP: | 3:N8DSLM/f+f:2OLM/Gf |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Creates files in the user directory
- iexplore.exe (PID: 608)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 1520)
- iexplore.exe (PID: 880)
Reads internet explorer settings
- iexplore.exe (PID: 608)
- iexplore.exe (PID: 3424)
Changes settings of System certificates
- iexplore.exe (PID: 880)
Reads Internet Cache Settings
- iexplore.exe (PID: 3424)
- iexplore.exe (PID: 608)
Reads settings of System Certificates
- iexplore.exe (PID: 880)
Adds / modifies Windows certificates
- iexplore.exe (PID: 880)
Application launched itself
- iexplore.exe (PID: 880)
Changes internet zones settings
- iexplore.exe (PID: 880)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 608 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:880 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 880 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1520 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 3424 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:880 CREDAT:203009 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
996
Read events
755
Write events
233
Delete events
8
Modification events
| (PID) Process: | (880) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (880) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (880) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (880) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (880) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (880) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (880) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {20701191-7687-11E9-B63D-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (880) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (880) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (880) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307050002000E0014001E0024009101 | |||
Executable files
0
Suspicious files
1
Text files
91
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 608 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\EBVSSIQL\futeboltv_xyz[1].txt | — | |
MD5:— | SHA256:— | |||
| 608 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\index.dat | dat | |
MD5:— | SHA256:— | |||
| 608 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 608 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 608 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@futeboltv[1].txt | text | |
MD5:— | SHA256:— | |||
| 608 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\ESUW8GNC\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 608 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 608 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\ESUW8GNC\jquery.smartbanner-04[1].css | text | |
MD5:— | SHA256:— | |||
| 608 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\JUPC24KL\jquery.smartbanner.min[1].css | text | |
MD5:— | SHA256:— | |||
| 608 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\EBVSSIQL\futeboltv_xyz[1].htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
65
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
608 | iexplore.exe | GET | 200 | 104.18.45.64:80 | http://www.futeboltv.xyz/wp-content/themes/goodlife-wp/assets/css/app.css | US | text | 39.5 Kb | suspicious |
608 | iexplore.exe | GET | 200 | 104.18.45.64:80 | http://www.futeboltv.xyz/wp-content/themes/goodlife-wp-child/style.css | US | text | 6.50 Kb | suspicious |
608 | iexplore.exe | GET | 200 | 104.18.45.64:80 | http://www.futeboltv.xyz/wp-content/plugins/appbanners/lib/smartbanner/jquery.smartbanner.min.css | US | text | 1.23 Kb | suspicious |
608 | iexplore.exe | GET | 200 | 143.204.98.84:80 | http://d63a3au5lqmtu.cloudfront.net/?luaad=723738 | US | text | 32.1 Kb | whitelisted |
608 | iexplore.exe | GET | 200 | 104.18.45.64:80 | http://www.futeboltv.xyz/i9.html?jogo=http://www.estouapaixonado.com/p/pdesk.php?live=http://apkftv.cinemafacil.com:8081/live/5/playlist.m3u8&capa=https://www.futeboltv.xyz/wp-content/uploads/2019/05/oeste-x-cuiaba.jpg&ad=1&ig=flaviasantos58 | US | html | 805 b | suspicious |
608 | iexplore.exe | GET | 200 | 104.18.45.64:80 | http://www.futeboltv.xyz/wp-content/plugins/appbanners/js/config.min.js | US | text | 133 b | suspicious |
608 | iexplore.exe | GET | 200 | 104.18.45.64:80 | http://www.futeboltv.xyz/wp-content/themes/goodlife-wp/assets/js/vendor.min.js | US | text | 88.6 Kb | suspicious |
608 | iexplore.exe | GET | 200 | 172.217.16.206:80 | http://www.google-analytics.com/collect?v=1&_v=j73&a=1225041824&t=pageview&_s=1&dl=http%3A%2F%2Fwww.futeboltv.xyz%2Fao-vivo%2Fassistir-oeste-x-cuiaba-ao-vivo&ul=en-us&de=utf-8&dt=Assistir%20Oeste%20x%20Cuiab%C3%A1%20Ao%20Vivo%20-%20Futebol%20Tv&sd=32-bit&sr=1280x720&vp=1260x560&je=0&fl=26.0%20r0&_u=AACAAE~&jid=&gjid=&cid=1223364184.1557865844&tid=UA-102310521-1&_gid=1612408173.1557865844&z=497036500 | US | image | 35 b | whitelisted |
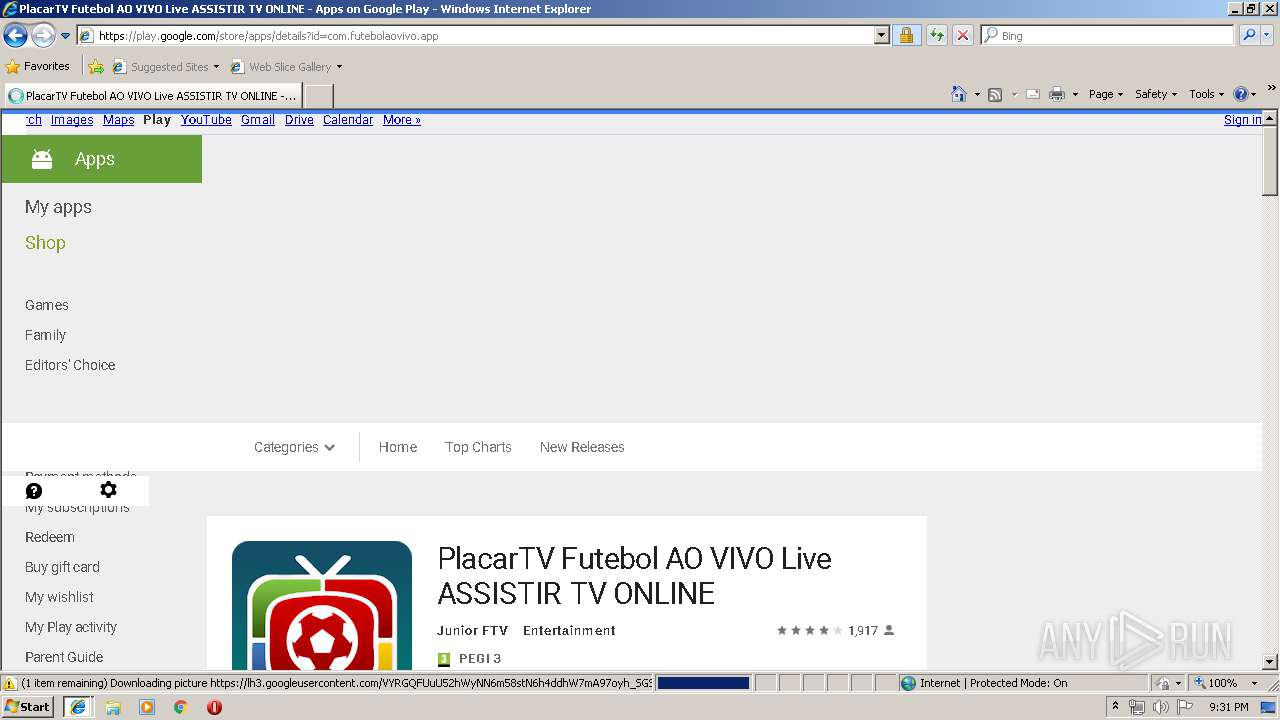
608 | iexplore.exe | GET | 200 | 104.18.45.64:80 | http://www.futeboltv.xyz/wp-content/plugins/appbanners/lib/smartbanner/jquery.smartbanner.min.js | US | html | 2.79 Kb | suspicious |
608 | iexplore.exe | GET | 200 | 104.18.45.64:80 | http://www.futeboltv.xyz/ao-vivo/assistir-oeste-x-cuiaba-ao-vivo | US | html | 14.0 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
608 | iexplore.exe | 104.20.21.239:443 | rum-static.pingdom.net | Cloudflare Inc | US | shared |
880 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
608 | iexplore.exe | 104.18.45.64:80 | www.futeboltv.xyz | Cloudflare Inc | US | shared |
880 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
608 | iexplore.exe | 104.18.45.64:443 | www.futeboltv.xyz | Cloudflare Inc | US | shared |
608 | iexplore.exe | 172.217.18.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
608 | iexplore.exe | 172.217.21.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
608 | iexplore.exe | 104.19.198.151:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | shared |
608 | iexplore.exe | 143.204.98.84:80 | d63a3au5lqmtu.cloudfront.net | — | US | suspicious |
608 | iexplore.exe | 172.217.16.206:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.futeboltv.xyz |
| suspicious |
www.bing.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
d63a3au5lqmtu.cloudfront.net |
| whitelisted |
embed.tawk.to |
| whitelisted |
rum-static.pingdom.net |
| whitelisted |
www.futeboltvgratis.com |
| unknown |