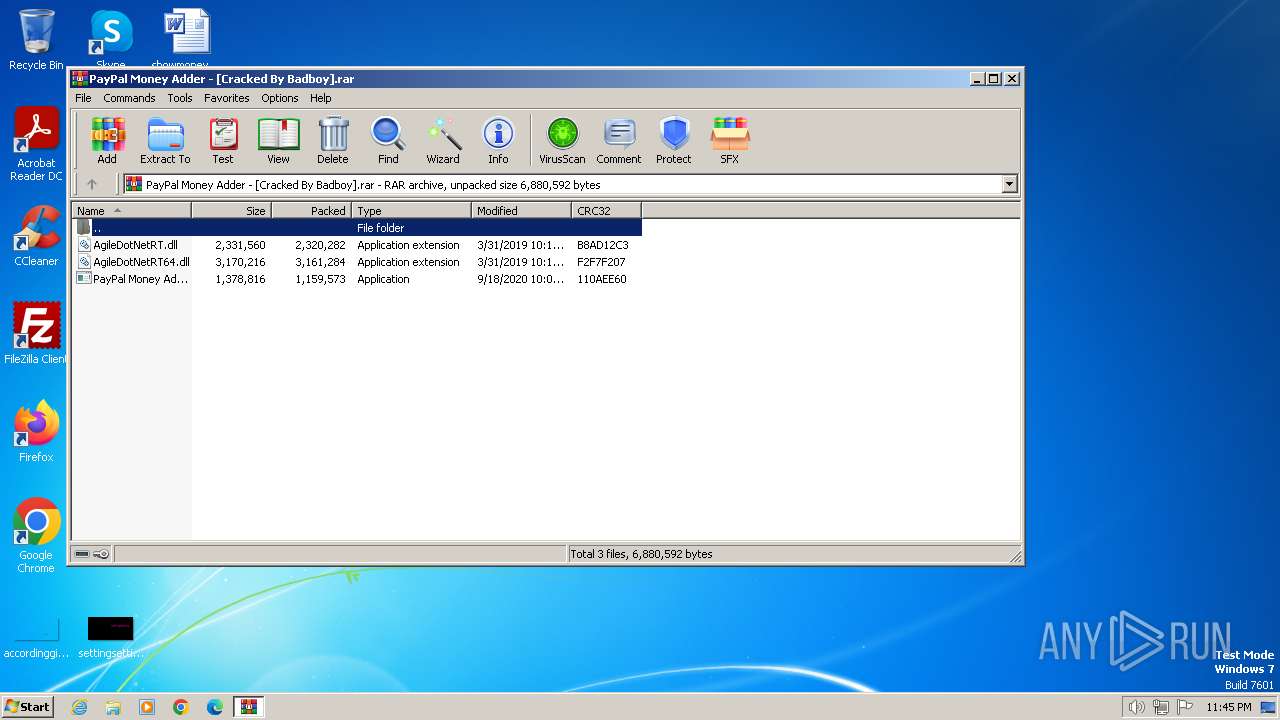
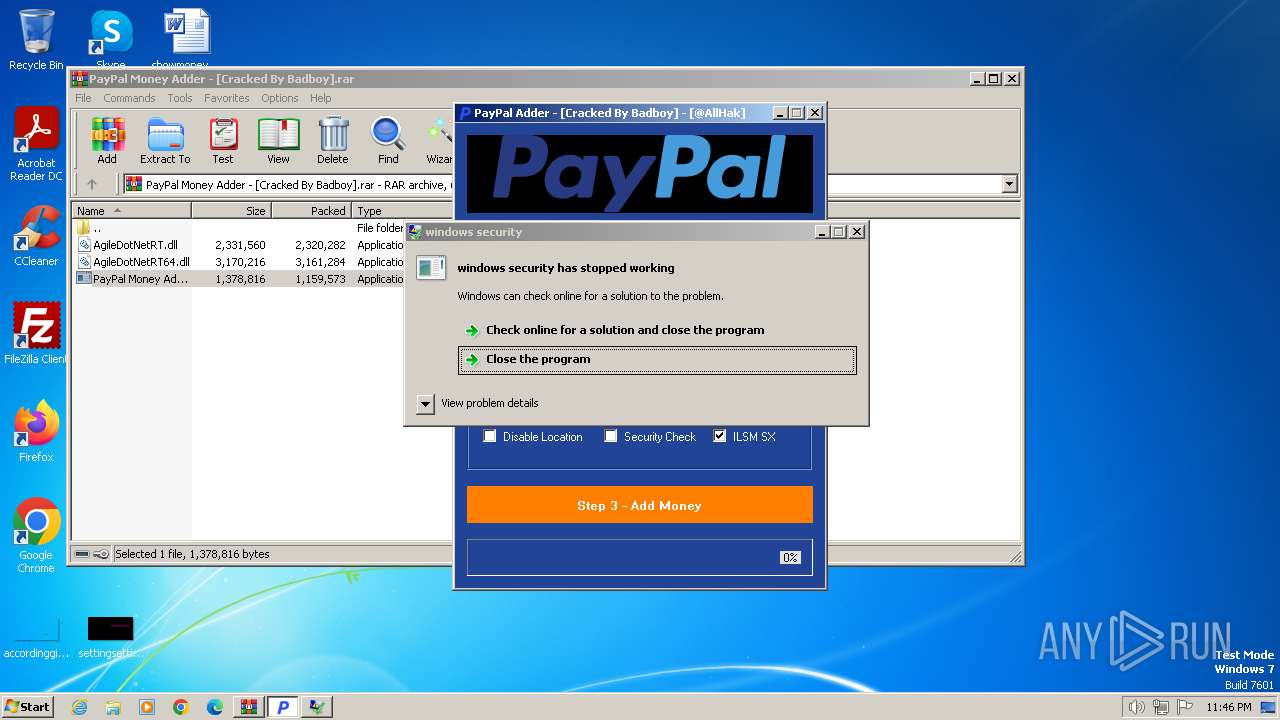
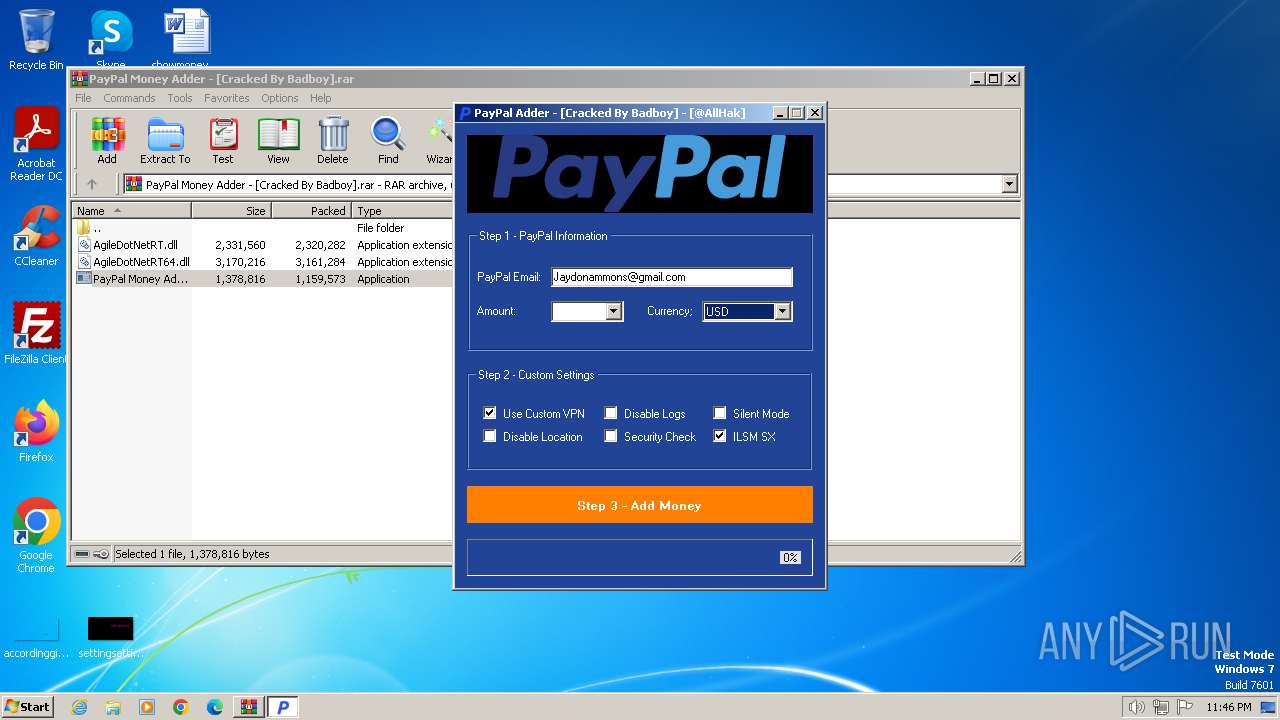
| File name: | PayPal Money Adder - [Cracked By Badboy].rar |
| Full analysis: | https://app.any.run/tasks/aabe8459-2d6b-4cf1-bf3c-34d194ba1228 |
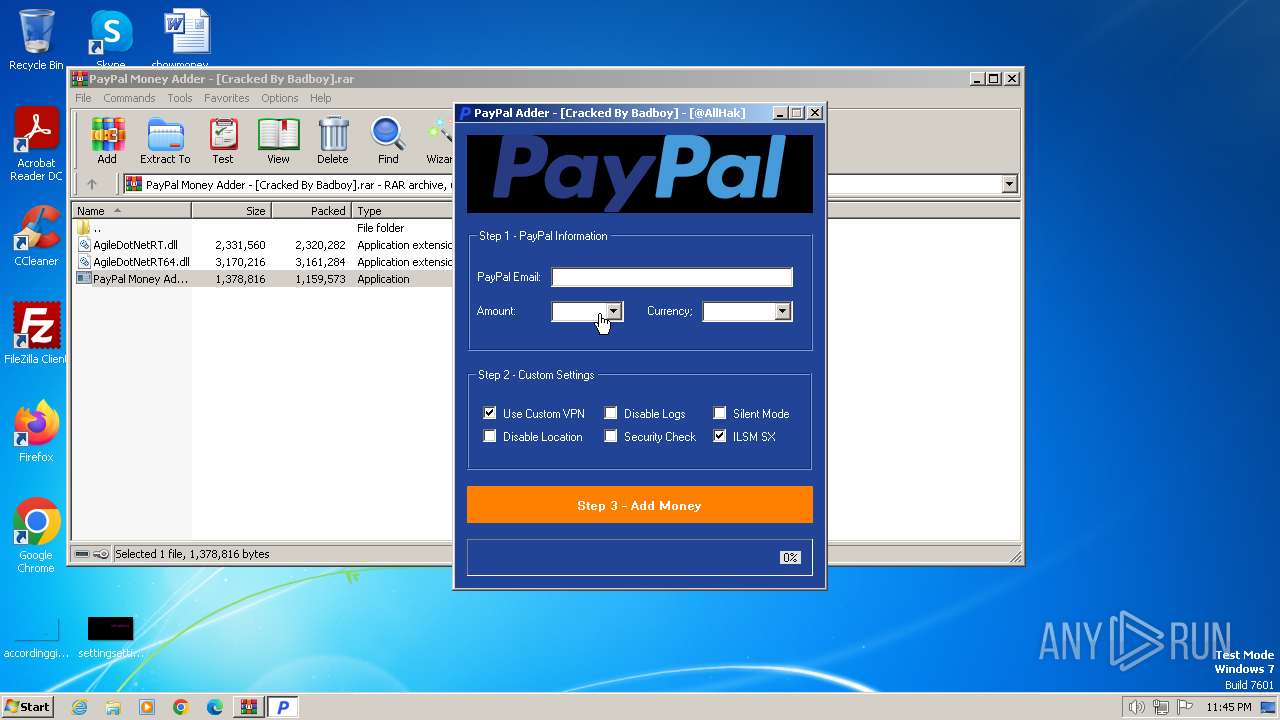
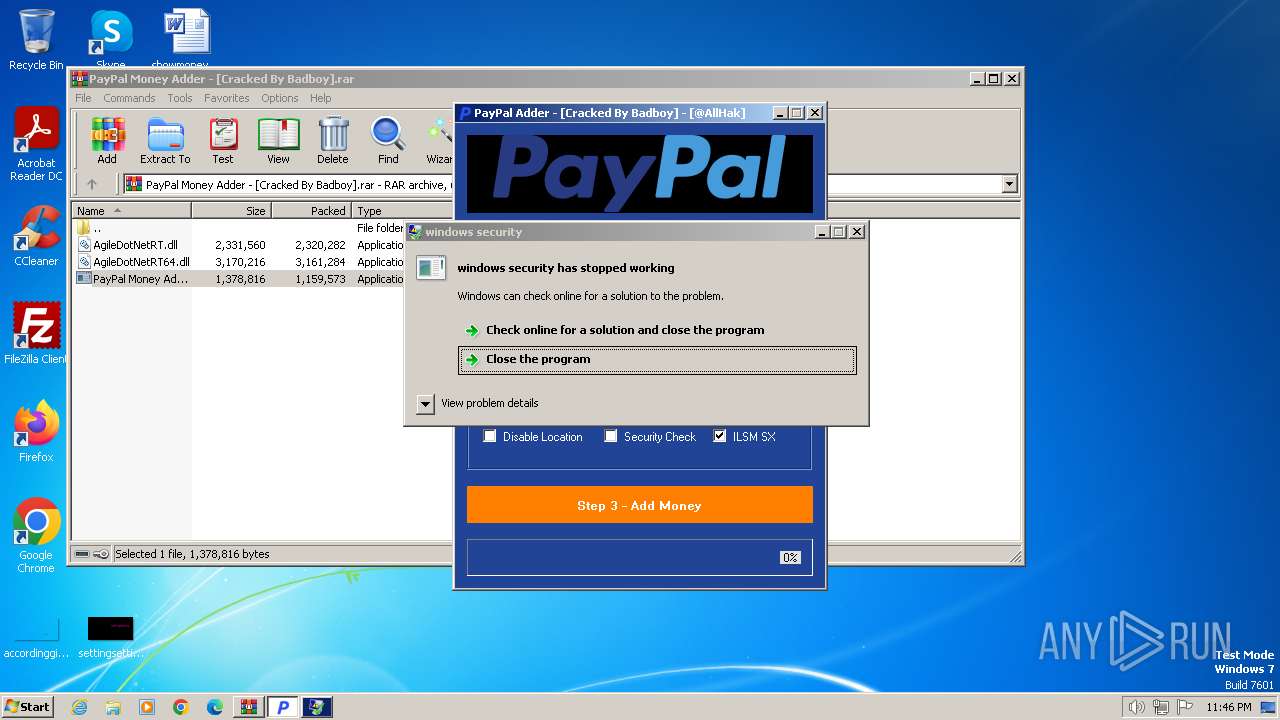
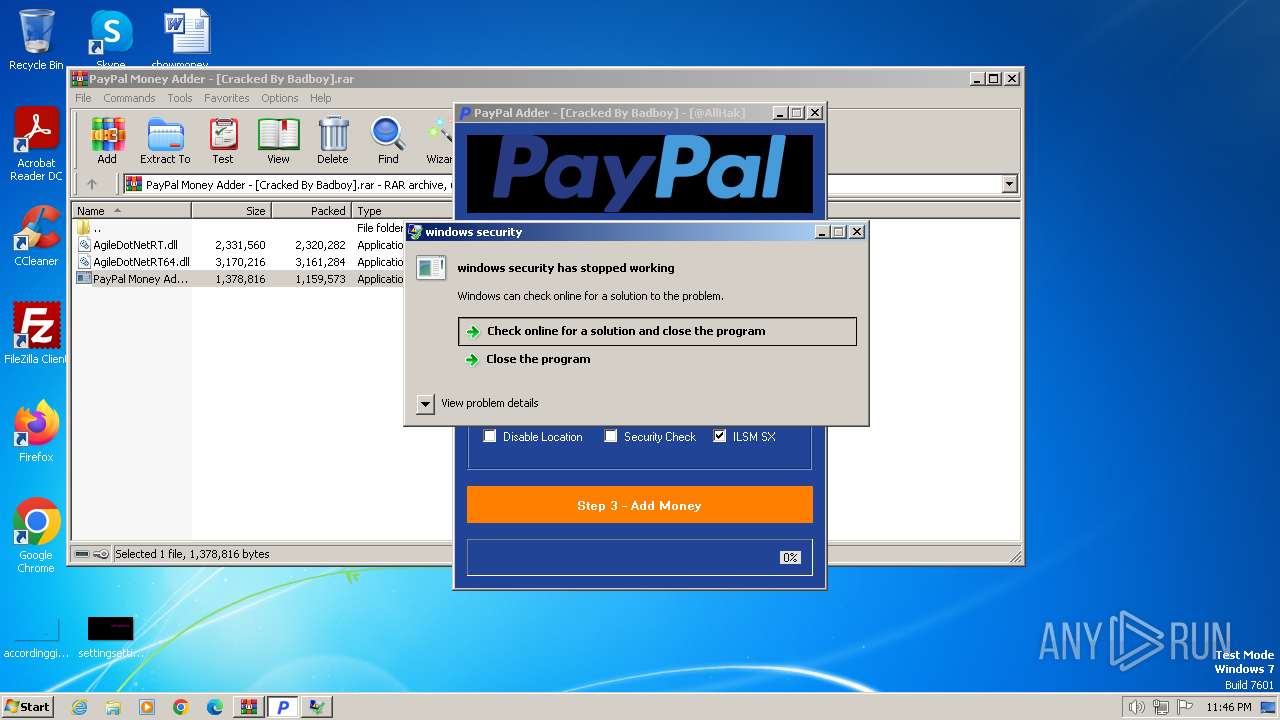
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2024, 22:45:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | F44F6DB85D74305636EA3A0B95728029 |
| SHA1: | 7AA91CF26E5361D3CFC3E933B0DF36873F4D30B8 |
| SHA256: | E9F6BDD75A5F26F44C5DDF97D396AF22617488D0298842F22505C71613CDE0B4 |
| SSDEEP: | 98304:J3nMoJz3xR3xg2uVCntep4lcmWOgUKFyP65UIqUdXkUBsj5B/gA3HWWCptKW79Lq:hFLZDTaWtxeeuAH |
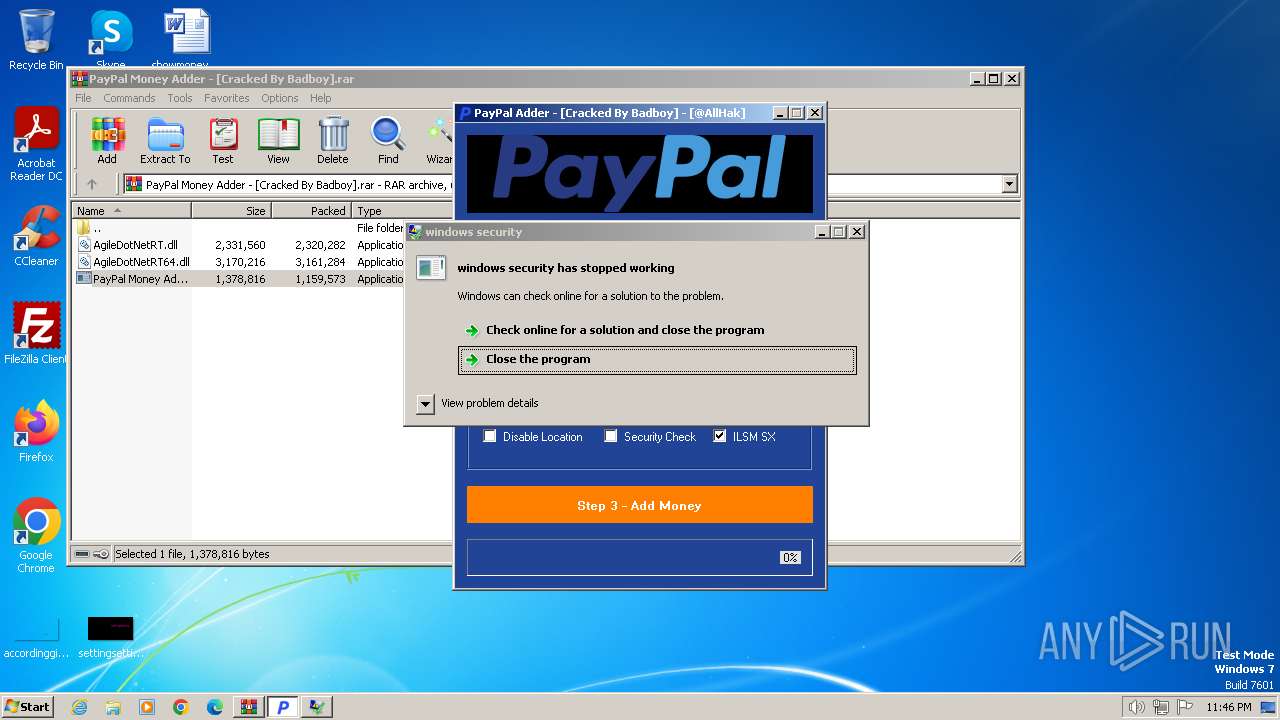
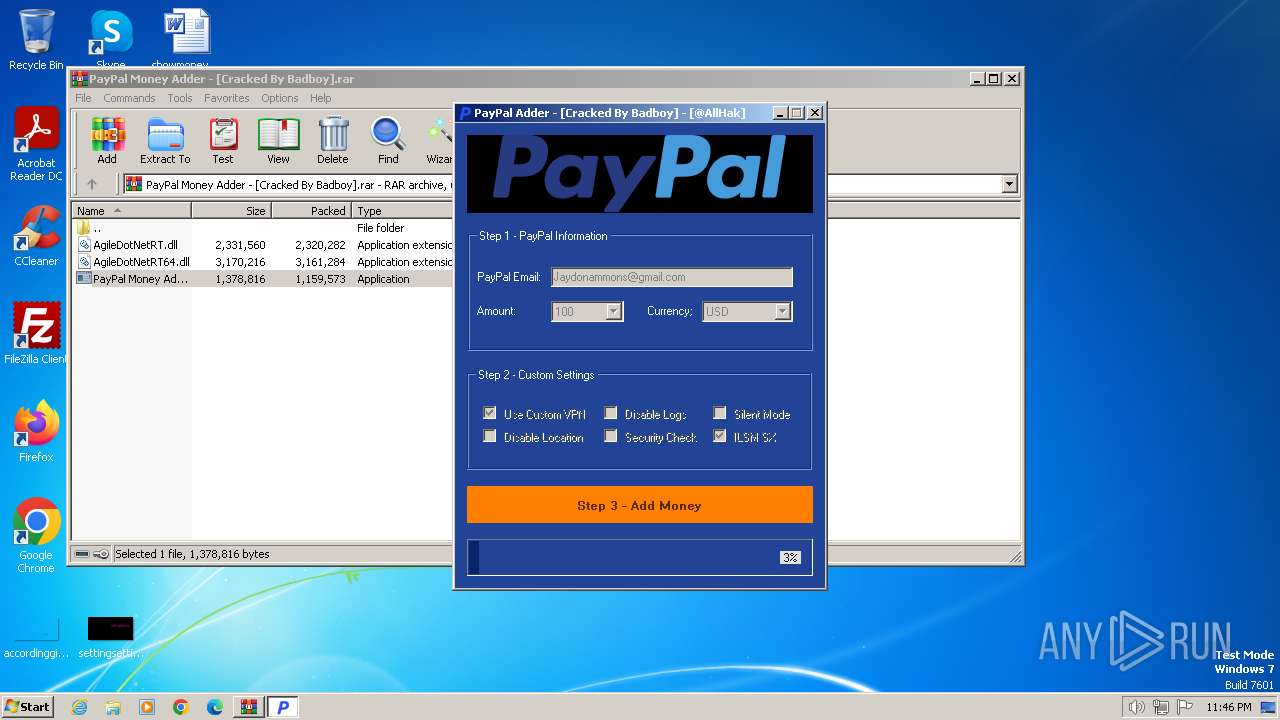
MALICIOUS
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3416)
- PayPal Money Adder - [Cracked By Badboy] .exe (PID: 3428)
- WINDOWS SECURITY.EXE (PID: 3224)
- WINDOWS SECURITY.EXE (PID: 3372)
- WINDOWS SECURITY.EXE (PID: 2936)
- WINDOWS SECURITY.EXE (PID: 4004)
- WINDOWS SECURITY.EXE (PID: 1992)
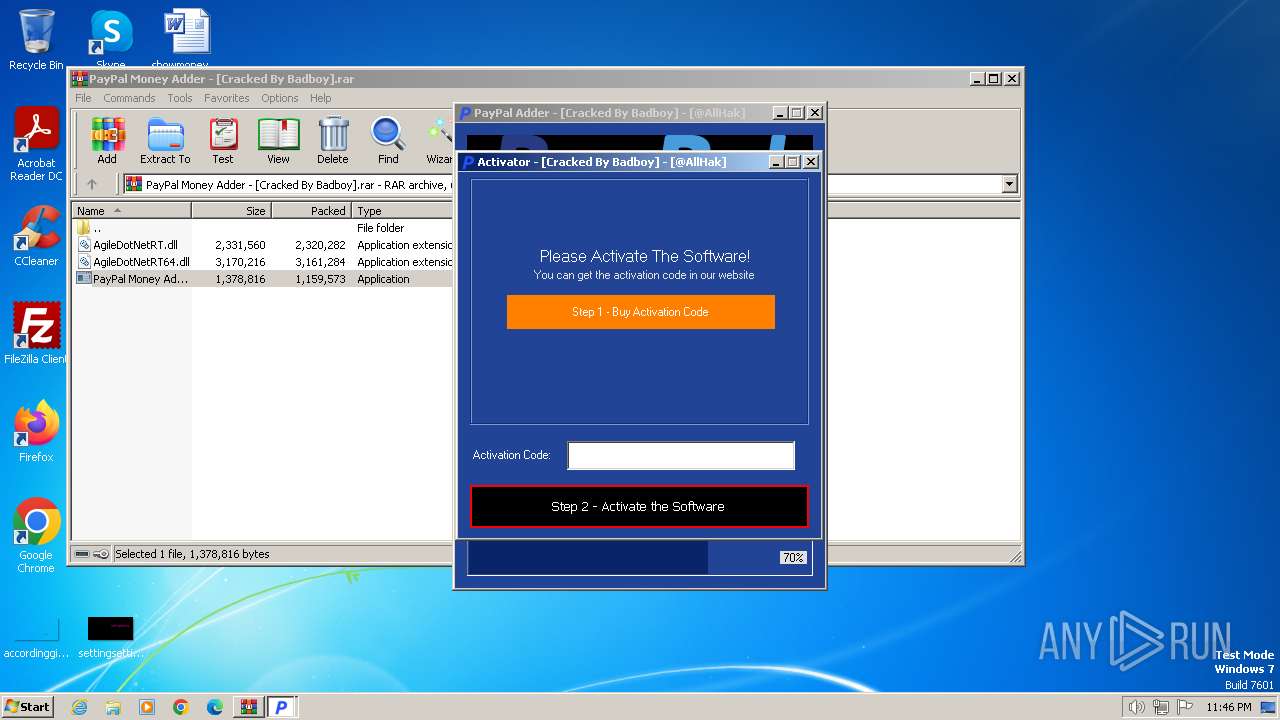
Changes the autorun value in the registry
- WINDOWS SECURITY.EXE (PID: 2936)
- WINDOWS SECURITY.EXE (PID: 3372)
- windows security.exe (PID: 996)
- windows security.exe (PID: 4016)
- WINDOWS SECURITY.EXE (PID: 4004)
- windows security.exe (PID: 3836)
- WINDOWS SECURITY.EXE (PID: 1992)
- windows security.exe (PID: 3772)
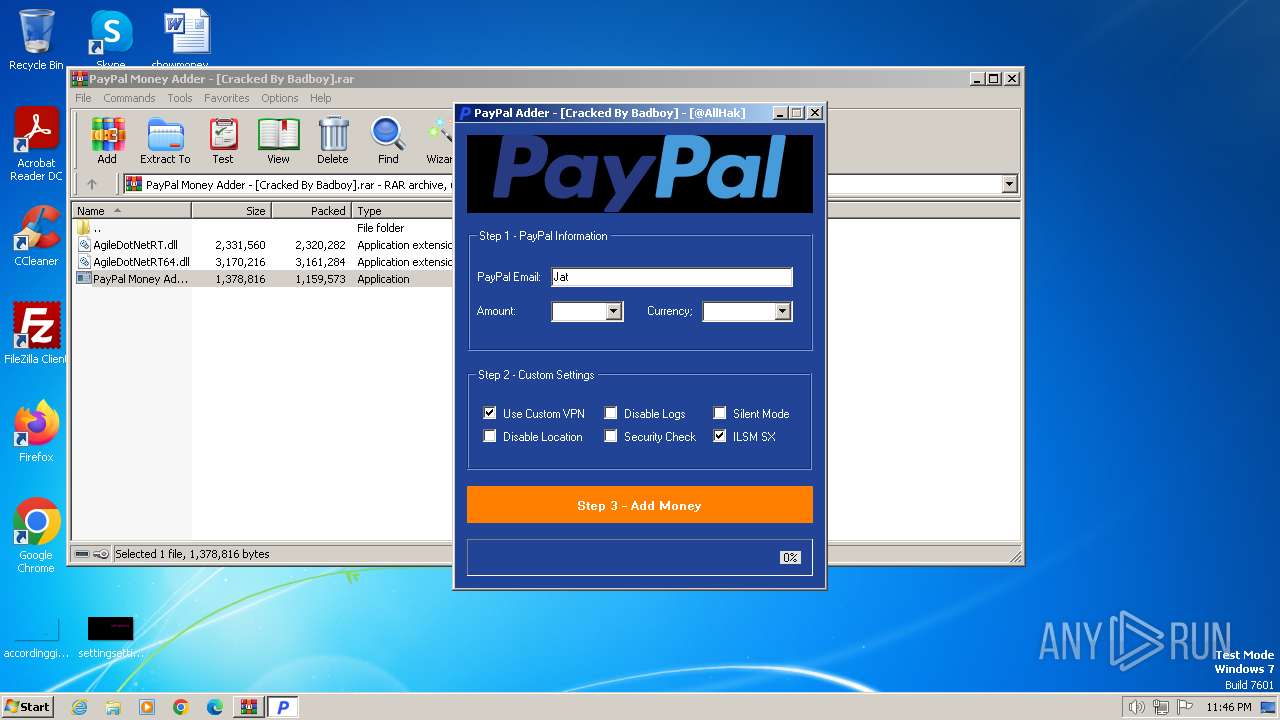
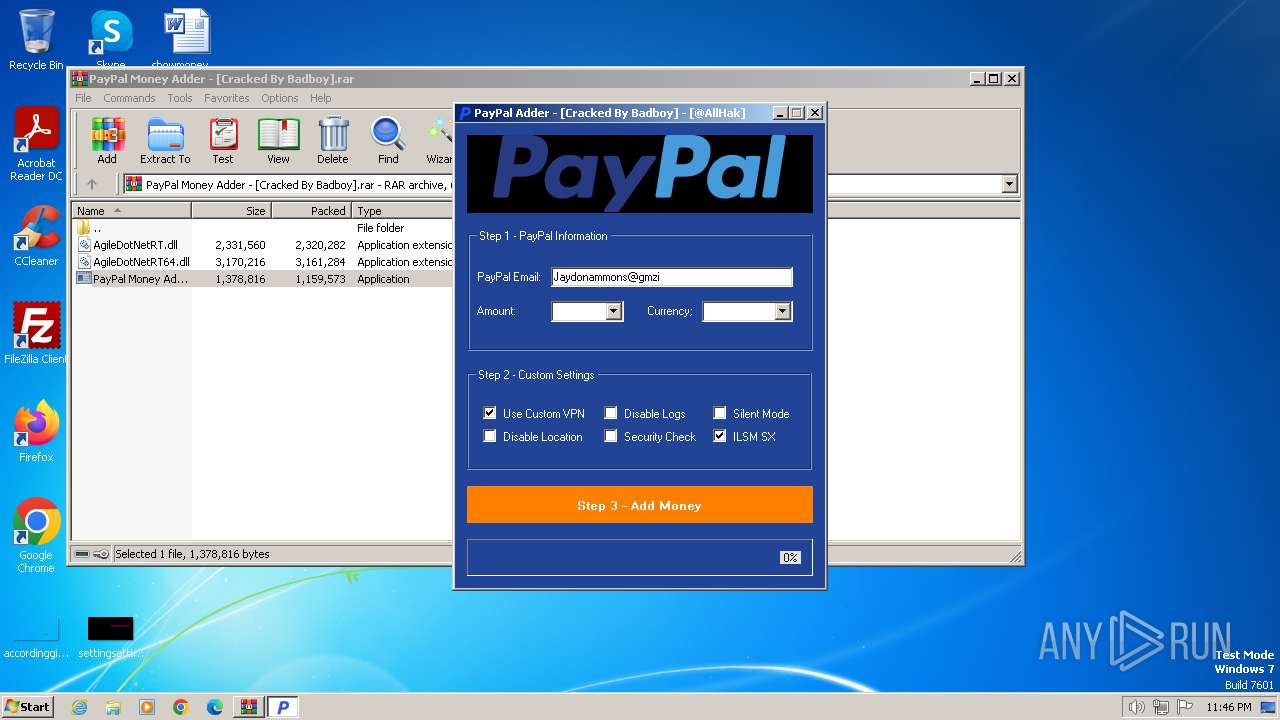
Actions looks like stealing of personal data
- WINDOWS SECURITY.EXE (PID: 3224)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3416)
- PayPal Money Adder - [Cracked By Badboy] .exe (PID: 3428)
- WINDOWS SECURITY.EXE (PID: 3224)
- windows security.exe (PID: 996)
- WINDOWS SECURITY.EXE (PID: 2936)
- windows security.exe (PID: 4016)
- WINDOWS SECURITY.EXE (PID: 4004)
- windows security.exe (PID: 3836)
- WINDOWS SECURITY.EXE (PID: 1992)
- windows security.exe (PID: 3772)
- windows security.exe (PID: 3868)
- WINDOWS SECURITY.EXE (PID: 2640)
Executable content was dropped or overwritten
- PayPal Money Adder - [Cracked By Badboy] .exe (PID: 3428)
- WINDOWS SECURITY.EXE (PID: 3224)
- WINDOWS SECURITY.EXE (PID: 3372)
- WINDOWS SECURITY.EXE (PID: 2936)
- WINDOWS SECURITY.EXE (PID: 4004)
- WINDOWS SECURITY.EXE (PID: 1992)
Reads the Internet Settings
- PayPal Money Adder - [Cracked By Badboy] .exe (PID: 3428)
- WINDOWS SECURITY.EXE (PID: 3224)
- WINDOWS SECURITY.EXE (PID: 2936)
- windows security.exe (PID: 996)
- windows security.exe (PID: 4016)
- WINDOWS SECURITY.EXE (PID: 4004)
- windows security.exe (PID: 3836)
- WINDOWS SECURITY.EXE (PID: 1992)
- windows security.exe (PID: 3772)
- windows security.exe (PID: 3868)
- WINDOWS SECURITY.EXE (PID: 2640)
Process drops legitimate windows executable
- WINDOWS SECURITY.EXE (PID: 3224)
- WINDOWS SECURITY.EXE (PID: 3372)
- WINDOWS SECURITY.EXE (PID: 2936)
- WINDOWS SECURITY.EXE (PID: 4004)
- WINDOWS SECURITY.EXE (PID: 1992)
Starts a Microsoft application from unusual location
- WINDOWS SECURITY.EXE (PID: 3372)
- WINDOWS SECURITY.EXE (PID: 2936)
- WINDOWS SECURITY.EXE (PID: 4008)
- WINDOWS SECURITY.EXE (PID: 4004)
- WINDOWS SECURITY.EXE (PID: 2780)
- WINDOWS SECURITY.EXE (PID: 1992)
- WINDOWS SECURITY.EXE (PID: 2640)
- WINDOWS SECURITY.EXE (PID: 3116)
Mutex name with non-standard characters
- WINDOWS SECURITY.EXE (PID: 3224)
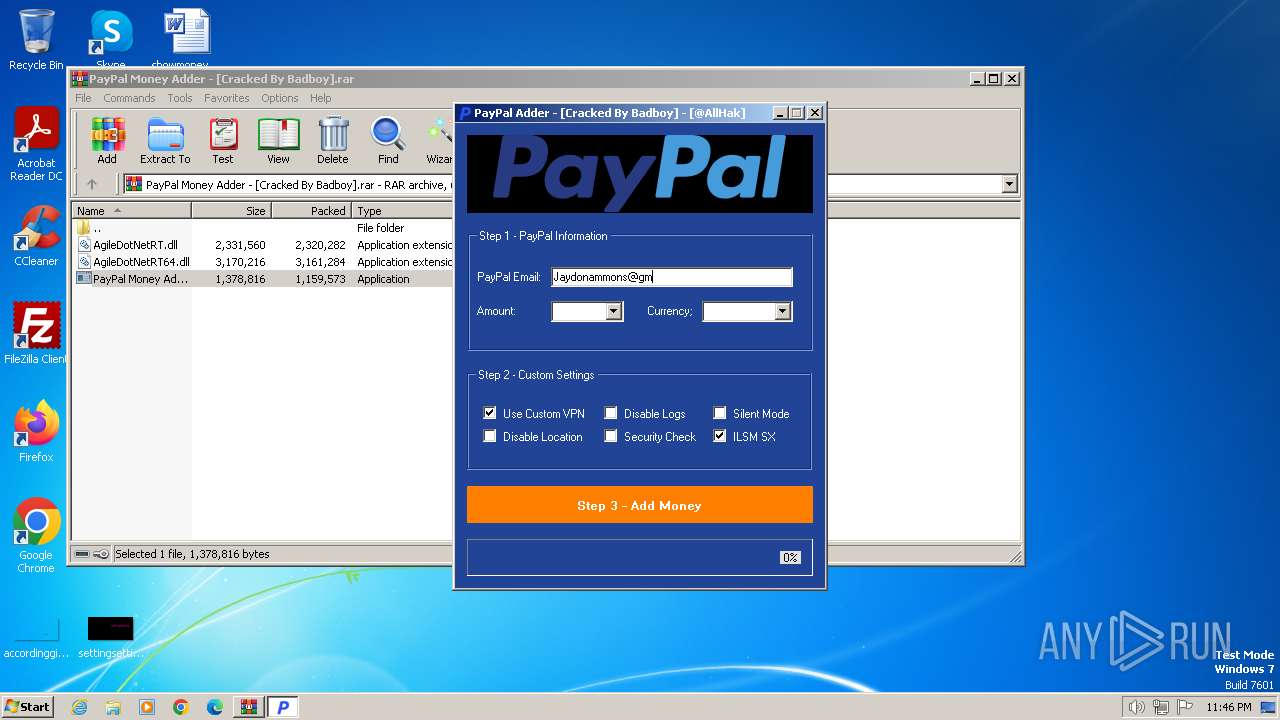
Reads the BIOS version
- PAYPAL MONEY ADDER - [CRACKED BY BADBOY] - [@ALLHAK].EXE (PID: 3172)
Starts itself from another location
- WINDOWS SECURITY.EXE (PID: 2936)
- WINDOWS SECURITY.EXE (PID: 4004)
- WINDOWS SECURITY.EXE (PID: 1992)
Application launched itself
- WINDOWS SECURITY.EXE (PID: 3372)
- windows security.exe (PID: 2840)
- windows security.exe (PID: 1808)
- WINDOWS SECURITY.EXE (PID: 4008)
- windows security.exe (PID: 748)
- windows security.exe (PID: 1580)
- WINDOWS SECURITY.EXE (PID: 2780)
- windows security.exe (PID: 3604)
- windows security.exe (PID: 1652)
- WINDOWS SECURITY.EXE (PID: 3116)
- windows security.exe (PID: 3612)
- windows security.exe (PID: 1476)
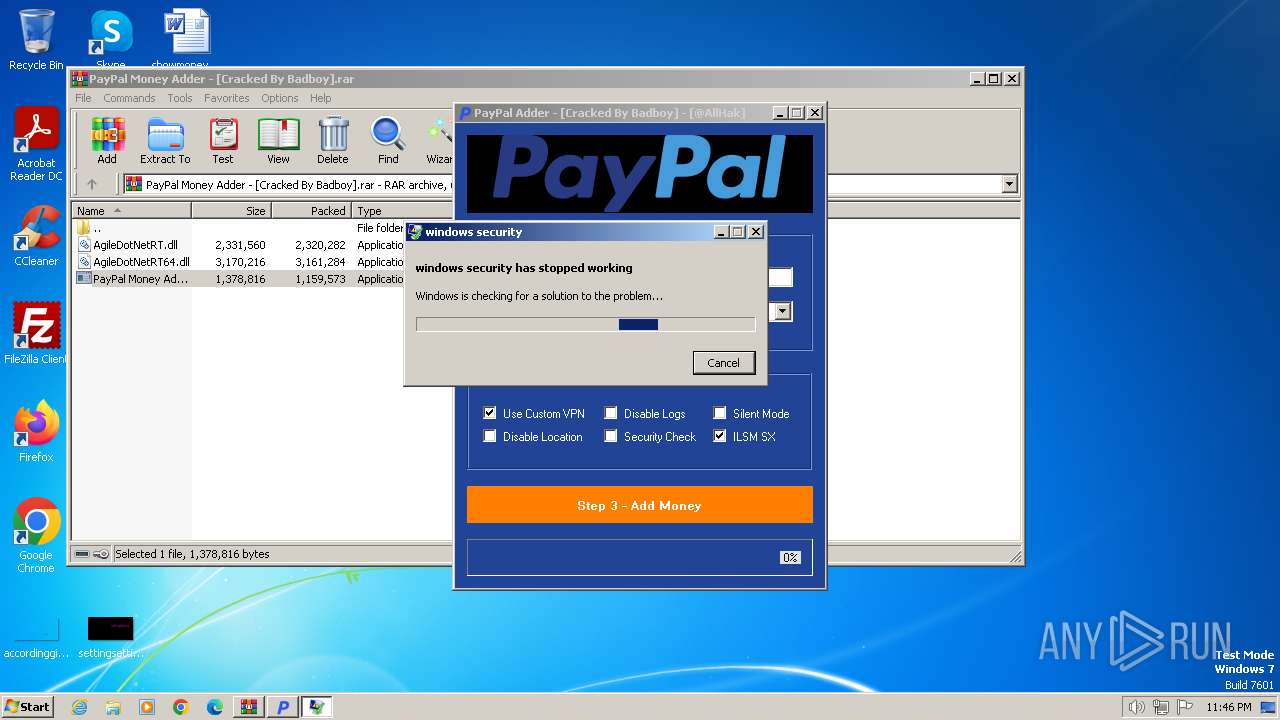
Checks for external IP
- WINDOWS SECURITY.EXE (PID: 2936)
- windows security.exe (PID: 996)
- windows security.exe (PID: 4016)
- WINDOWS SECURITY.EXE (PID: 4004)
- windows security.exe (PID: 3836)
- WINDOWS SECURITY.EXE (PID: 1992)
- windows security.exe (PID: 3772)
- WINDOWS SECURITY.EXE (PID: 2640)
Reads settings of System Certificates
- WINDOWS SECURITY.EXE (PID: 2936)
- WINDOWS SECURITY.EXE (PID: 4004)
- WINDOWS SECURITY.EXE (PID: 1992)
Executing commands from a ".bat" file
- windows security.exe (PID: 996)
- WINDOWS SECURITY.EXE (PID: 2936)
- windows security.exe (PID: 4016)
- WINDOWS SECURITY.EXE (PID: 4004)
- windows security.exe (PID: 3836)
- WINDOWS SECURITY.EXE (PID: 1992)
- windows security.exe (PID: 3868)
- windows security.exe (PID: 3772)
- WINDOWS SECURITY.EXE (PID: 2640)
Starts CMD.EXE for commands execution
- windows security.exe (PID: 996)
- WINDOWS SECURITY.EXE (PID: 2936)
- windows security.exe (PID: 4016)
- WINDOWS SECURITY.EXE (PID: 4004)
- windows security.exe (PID: 3836)
- WINDOWS SECURITY.EXE (PID: 1992)
- windows security.exe (PID: 3772)
- windows security.exe (PID: 3868)
- WINDOWS SECURITY.EXE (PID: 2640)
Starts application with an unusual extension
- cmd.exe (PID: 3572)
- cmd.exe (PID: 3112)
- cmd.exe (PID: 3316)
- cmd.exe (PID: 1384)
- cmd.exe (PID: 2912)
- cmd.exe (PID: 1920)
- cmd.exe (PID: 2960)
- cmd.exe (PID: 2652)
- cmd.exe (PID: 568)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 3112)
- cmd.exe (PID: 3572)
- cmd.exe (PID: 3316)
- cmd.exe (PID: 2912)
- cmd.exe (PID: 1384)
- cmd.exe (PID: 1920)
- cmd.exe (PID: 2960)
- cmd.exe (PID: 2652)
- cmd.exe (PID: 568)
The executable file from the user directory is run by the CMD process
- windows security.exe (PID: 1808)
- WINDOWS SECURITY.EXE (PID: 4008)
- windows security.exe (PID: 1580)
- WINDOWS SECURITY.EXE (PID: 2780)
- windows security.exe (PID: 1652)
- WINDOWS SECURITY.EXE (PID: 3116)
- windows security.exe (PID: 3612)
- windows security.exe (PID: 1476)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3416)
Checks supported languages
- PayPal Money Adder - [Cracked By Badboy] .exe (PID: 3428)
- PAYPAL MONEY ADDER - [CRACKED BY BADBOY] - [@ALLHAK].EXE (PID: 3172)
- WINDOWS SECURITY.EXE (PID: 3224)
- WINDOWS SECURITY.EXE (PID: 3372)
- WINDOWS SECURITY.EXE (PID: 2936)
- windows security.exe (PID: 2840)
- windows security.exe (PID: 996)
- chcp.com (PID: 2796)
- windows security.exe (PID: 1808)
- windows security.exe (PID: 4016)
- chcp.com (PID: 3852)
- chcp.com (PID: 3864)
- WINDOWS SECURITY.EXE (PID: 4008)
- WINDOWS SECURITY.EXE (PID: 4004)
- windows security.exe (PID: 748)
- windows security.exe (PID: 1580)
- windows security.exe (PID: 3836)
- chcp.com (PID: 900)
- chcp.com (PID: 1392)
- WINDOWS SECURITY.EXE (PID: 2780)
- WINDOWS SECURITY.EXE (PID: 1992)
- windows security.exe (PID: 3772)
- windows security.exe (PID: 3604)
- chcp.com (PID: 3260)
- windows security.exe (PID: 3868)
- windows security.exe (PID: 1652)
- chcp.com (PID: 3156)
- chcp.com (PID: 2852)
- WINDOWS SECURITY.EXE (PID: 3116)
- WINDOWS SECURITY.EXE (PID: 2640)
- windows security.exe (PID: 3612)
- windows security.exe (PID: 4068)
- chcp.com (PID: 1072)
- windows security.exe (PID: 1476)
Create files in a temporary directory
- PayPal Money Adder - [Cracked By Badboy] .exe (PID: 3428)
- WINDOWS SECURITY.EXE (PID: 3224)
- windows security.exe (PID: 996)
- WINDOWS SECURITY.EXE (PID: 2936)
- windows security.exe (PID: 4016)
- WINDOWS SECURITY.EXE (PID: 4004)
- windows security.exe (PID: 3836)
- WINDOWS SECURITY.EXE (PID: 1992)
- windows security.exe (PID: 3772)
- windows security.exe (PID: 3868)
- WINDOWS SECURITY.EXE (PID: 2640)
Reads the computer name
- PayPal Money Adder - [Cracked By Badboy] .exe (PID: 3428)
- PAYPAL MONEY ADDER - [CRACKED BY BADBOY] - [@ALLHAK].EXE (PID: 3172)
- WINDOWS SECURITY.EXE (PID: 3224)
- WINDOWS SECURITY.EXE (PID: 2936)
- windows security.exe (PID: 2840)
- WINDOWS SECURITY.EXE (PID: 3372)
- windows security.exe (PID: 996)
- windows security.exe (PID: 1808)
- windows security.exe (PID: 4016)
- WINDOWS SECURITY.EXE (PID: 4008)
- WINDOWS SECURITY.EXE (PID: 4004)
- windows security.exe (PID: 748)
- windows security.exe (PID: 1580)
- windows security.exe (PID: 3836)
- WINDOWS SECURITY.EXE (PID: 2780)
- WINDOWS SECURITY.EXE (PID: 1992)
- windows security.exe (PID: 3604)
- windows security.exe (PID: 3772)
- windows security.exe (PID: 1652)
- windows security.exe (PID: 3868)
- WINDOWS SECURITY.EXE (PID: 3116)
- windows security.exe (PID: 3612)
- WINDOWS SECURITY.EXE (PID: 2640)
- windows security.exe (PID: 1476)
- windows security.exe (PID: 4068)
Reads the machine GUID from the registry
- PAYPAL MONEY ADDER - [CRACKED BY BADBOY] - [@ALLHAK].EXE (PID: 3172)
- WINDOWS SECURITY.EXE (PID: 3372)
- WINDOWS SECURITY.EXE (PID: 2936)
- windows security.exe (PID: 2840)
- windows security.exe (PID: 996)
- windows security.exe (PID: 1808)
- windows security.exe (PID: 4016)
- WINDOWS SECURITY.EXE (PID: 4008)
- WINDOWS SECURITY.EXE (PID: 4004)
- windows security.exe (PID: 748)
- windows security.exe (PID: 1580)
- windows security.exe (PID: 3836)
- WINDOWS SECURITY.EXE (PID: 2780)
- WINDOWS SECURITY.EXE (PID: 1992)
- windows security.exe (PID: 3772)
- windows security.exe (PID: 3604)
- windows security.exe (PID: 1652)
- windows security.exe (PID: 3868)
- WINDOWS SECURITY.EXE (PID: 3116)
- WINDOWS SECURITY.EXE (PID: 2640)
- windows security.exe (PID: 3612)
- windows security.exe (PID: 4068)
- windows security.exe (PID: 1476)
Creates files or folders in the user directory
- WINDOWS SECURITY.EXE (PID: 3372)
- WINDOWS SECURITY.EXE (PID: 2936)
- windows security.exe (PID: 996)
- WINDOWS SECURITY.EXE (PID: 4004)
- WINDOWS SECURITY.EXE (PID: 1992)
Reads Environment values
- WINDOWS SECURITY.EXE (PID: 2936)
- windows security.exe (PID: 996)
- windows security.exe (PID: 4016)
- WINDOWS SECURITY.EXE (PID: 4004)
- windows security.exe (PID: 3836)
- WINDOWS SECURITY.EXE (PID: 1992)
- windows security.exe (PID: 3772)
- WINDOWS SECURITY.EXE (PID: 2640)
Disables trace logs
- WINDOWS SECURITY.EXE (PID: 2936)
- windows security.exe (PID: 996)
- windows security.exe (PID: 4016)
- WINDOWS SECURITY.EXE (PID: 4004)
- windows security.exe (PID: 3836)
- WINDOWS SECURITY.EXE (PID: 1992)
- windows security.exe (PID: 3772)
- WINDOWS SECURITY.EXE (PID: 2640)
Reads the software policy settings
- WINDOWS SECURITY.EXE (PID: 2936)
- WINDOWS SECURITY.EXE (PID: 4004)
- WINDOWS SECURITY.EXE (PID: 1992)
Themida protector has been detected
- PAYPAL MONEY ADDER - [CRACKED BY BADBOY] - [@ALLHAK].EXE (PID: 3172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
109
Monitored processes
59
Malicious processes
18
Suspicious processes
13
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 328 | ping -n 10 localhost | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 568 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\ZmA3DnVKDhzL.bat" " | C:\Windows\System32\cmd.exe | — | WINDOWS SECURITY.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 596 | ping -n 10 localhost | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 744 | "C:\Users\admin\AppData\Roaming\SubDir\windows security.exe" | C:\Users\admin\AppData\Roaming\SubDir\windows security.exe | — | windows security.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: windows security Exit code: 4294967295 Version: 10.0.17763.0 Modules
| |||||||||||||||
| 748 | "C:\Users\admin\AppData\Roaming\SubDir\windows security.exe" | C:\Users\admin\AppData\Roaming\SubDir\windows security.exe | — | WINDOWS SECURITY.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: windows security Exit code: 0 Version: 10.0.17763.0 Modules
| |||||||||||||||
| 900 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 952 | "C:\Users\admin\AppData\Roaming\SubDir\windows security.exe" | C:\Users\admin\AppData\Roaming\SubDir\windows security.exe | — | windows security.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: windows security Exit code: 4294967295 Version: 10.0.17763.0 Modules
| |||||||||||||||
| 996 | "C:\Users\admin\AppData\Roaming\SubDir\windows security.exe" | C:\Users\admin\AppData\Roaming\SubDir\windows security.exe | windows security.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: windows security Exit code: 3762504530 Version: 10.0.17763.0 Modules
| |||||||||||||||
| 1072 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1384 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\pjlvcDx4fGT5.bat" " | C:\Windows\System32\cmd.exe | — | windows security.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
54 867
Read events
54 690
Write events
177
Delete events
0
Modification events
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\PayPal Money Adder - [Cracked By Badboy].rar | |||
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
52
Suspicious files
2
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3224 | WINDOWS SECURITY.EXE | C:\Users\admin\AppData\Local\Temp\3582-490\WINDOWS SECURITY.EXE | executable | |
MD5:D5A55513FE1D64452763CB6240DBFEB5 | SHA256:AD2C69A35946B417527918A8986499D752EF18EC618E97C7567EF0737FF90BC0 | |||
| 3416 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3416.16318\AgileDotNetRT64.dll | executable | |
MD5:E3BD88B3C3E9B33DFA72C814F8826CFF | SHA256:28E9458A43E5D86A341590EAA83D0DA18C29FCE81F2383D84BDA484E049A1796 | |||
| 3428 | PayPal Money Adder - [Cracked By Badboy] .exe | C:\Users\admin\AppData\Local\Temp\WINDOWS SECURITY.EXE | executable | |
MD5:DCA31EE64CF3A05FE2606A9C1A25FACE | SHA256:D7FB15D7D1D564E56FEECFB1129C8BF2E2129043CD35C9926F0A90EFC221294D | |||
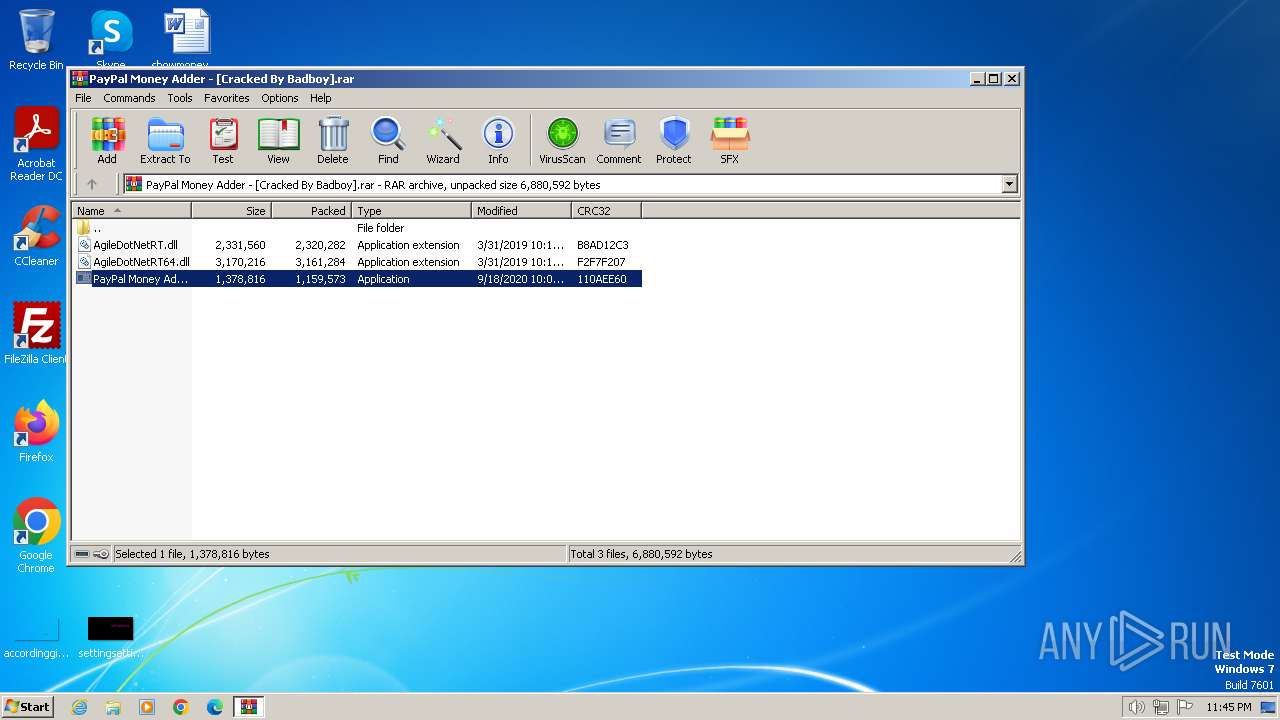
| 3416 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3416.16318\PayPal Money Adder - [Cracked By Badboy] .exe | executable | |
MD5:8EC353D918813738DDE7A6CE66B0CE32 | SHA256:69A44A5806A07E43820366150381BAB82A15271D5B3D0AEE7C0B35E24A51A01D | |||
| 3224 | WINDOWS SECURITY.EXE | C:\MSOCache\All Users\{90140000-006E-0407-0000-0000000FF1CE}-C\DW20.EXE | executable | |
MD5:02EE6A3424782531461FB2F10713D3C1 | SHA256:EAD58C483CB20BCD57464F8A4929079539D634F469B213054BF737D227C026DC | |||
| 3224 | WINDOWS SECURITY.EXE | C:\MSOCache\All Users\{90140000-006E-0410-0000-0000000FF1CE}-C\DW20.EXE | executable | |
MD5:02EE6A3424782531461FB2F10713D3C1 | SHA256:EAD58C483CB20BCD57464F8A4929079539D634F469B213054BF737D227C026DC | |||
| 3224 | WINDOWS SECURITY.EXE | C:\MSOCache\All Users\{90140000-006E-0410-0000-0000000FF1CE}-C\dwtrig20.exe | executable | |
MD5:CF6C595D3E5E9667667AF096762FD9C4 | SHA256:593E60CC30AE0789448547195AF77F550387F6648D45847EA244DD0DD7ABF03D | |||
| 3224 | WINDOWS SECURITY.EXE | C:\MSOCache\All Users\{90140000-006E-0412-0000-0000000FF1CE}-C\dwtrig20.exe | executable | |
MD5:CF6C595D3E5E9667667AF096762FD9C4 | SHA256:593E60CC30AE0789448547195AF77F550387F6648D45847EA244DD0DD7ABF03D | |||
| 3372 | WINDOWS SECURITY.EXE | C:\Users\admin\AppData\Roaming\xEPYeKsYHB\mFBANbCzNg.exe | executable | |
MD5:D5A55513FE1D64452763CB6240DBFEB5 | SHA256:AD2C69A35946B417527918A8986499D752EF18EC618E97C7567EF0737FF90BC0 | |||
| 3224 | WINDOWS SECURITY.EXE | C:\MSOCache\All Users\{90140000-006E-0411-0000-0000000FF1CE}-C\dwtrig20.exe | executable | |
MD5:CF6C595D3E5E9667667AF096762FD9C4 | SHA256:593E60CC30AE0789448547195AF77F550387F6648D45847EA244DD0DD7ABF03D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
25
DNS requests
10
Threats
25
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2936 | WINDOWS SECURITY.EXE | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | US | binary | 289 b | shared |
3836 | windows security.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | US | binary | 289 b | shared |
3772 | windows security.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | US | binary | 289 b | shared |
2640 | WINDOWS SECURITY.EXE | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | US | binary | 289 b | shared |
1060 | svchost.exe | GET | 304 | 87.248.205.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?67a3611ec3c0260d | US | — | — | whitelisted |
996 | windows security.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | US | binary | 289 b | shared |
1372 | svchost.exe | GET | 304 | 87.248.205.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | US | — | — | whitelisted |
1372 | svchost.exe | GET | 200 | 184.25.50.10:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
1992 | WINDOWS SECURITY.EXE | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | US | binary | 289 b | shared |
4016 | windows security.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | US | binary | 289 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
— | — | 239.255.255.250:3702 | — | — | — | whitelisted |
1372 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
2936 | WINDOWS SECURITY.EXE | 208.95.112.1:80 | ip-api.com | TUT-AS | US | unknown |
2936 | WINDOWS SECURITY.EXE | 145.14.145.17:443 | payloads-poison.000webhostapp.com | Hostinger International Limited | NL | shared |
996 | windows security.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | unknown |
1372 | svchost.exe | 87.248.205.0:80 | ctldl.windowsupdate.com | LLNW | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
ip-api.com |
| shared |
payloads-poison.000webhostapp.com |
| shared |
quasarrat220-24487.portmap.io |
| malicious |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
watson.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
1060 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
2936 | WINDOWS SECURITY.EXE | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
1060 | svchost.exe | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |
2936 | WINDOWS SECURITY.EXE | A Network Trojan was detected | ET MALWARE Common RAT Connectivity Check Observed |
1060 | svchost.exe | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |
2936 | WINDOWS SECURITY.EXE | Not Suspicious Traffic | ET INFO Observed SSL Cert for Free Hosting Domain (*.000webhostapp .com) |
1060 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query to a Reverse Proxy Service Observed |
996 | windows security.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
1060 | svchost.exe | Misc activity | ET INFO DNS Query for Port Mapping/Tunneling Service Domain (.portmap .io) |
Process | Message |
|---|---|
PayPal Money Adder - [Cracked By Badboy] .exe | C:\Users\admin\AppData\Local\Temp\PAYPAL MONEY ADDER - [CRACKED BY BADBOY] - [@ALLHAK].EXE |
PayPal Money Adder - [Cracked By Badboy] .exe | C:\Users\admin\AppData\Local\Temp\WINDOWS SECURITY.EXE |