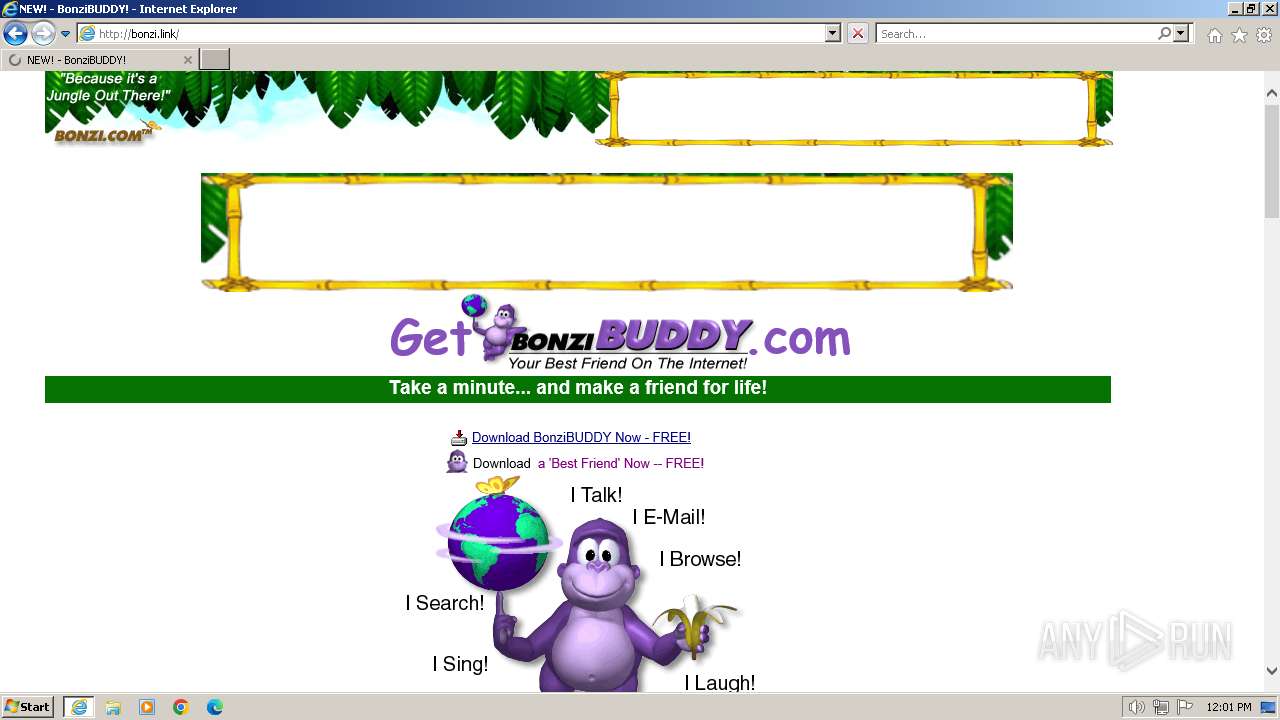
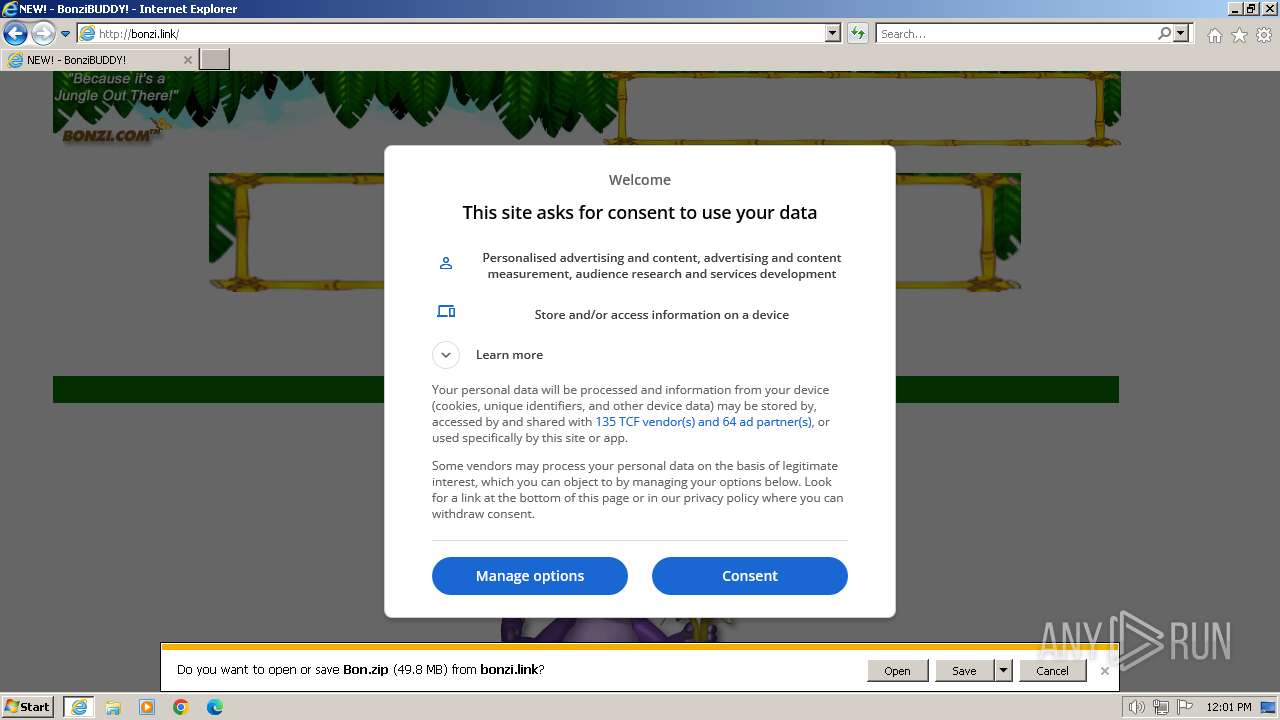
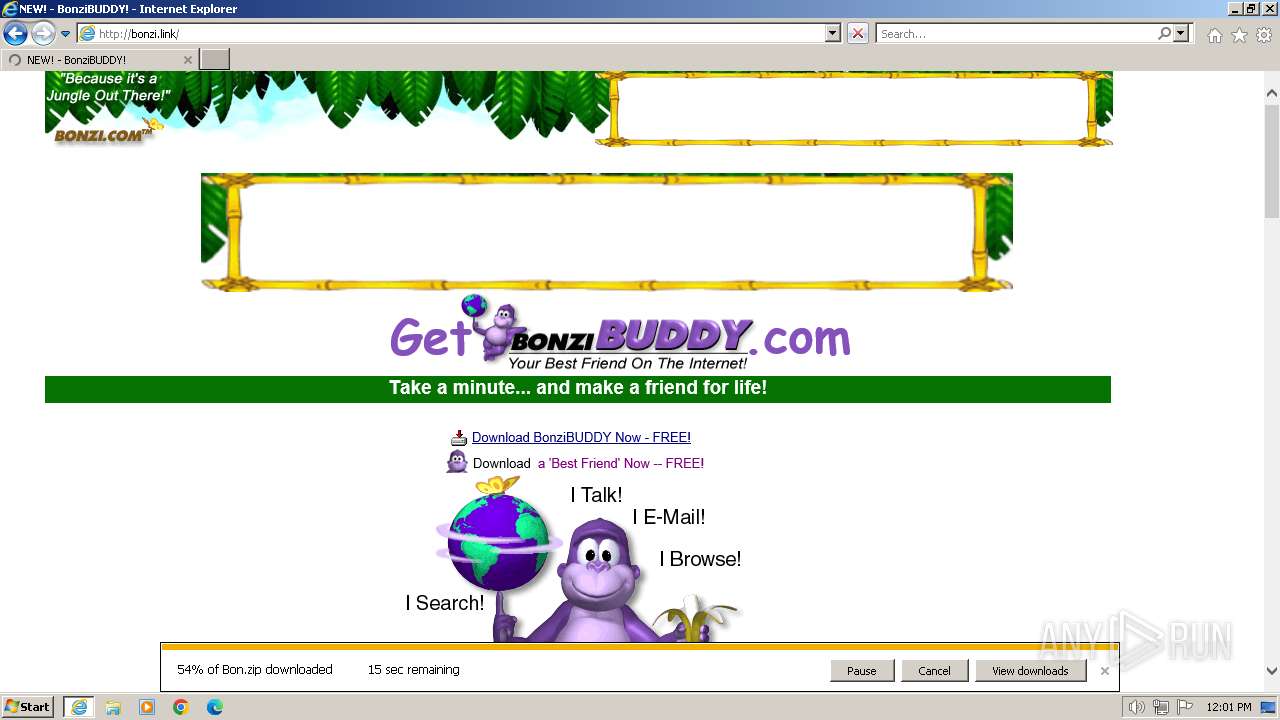
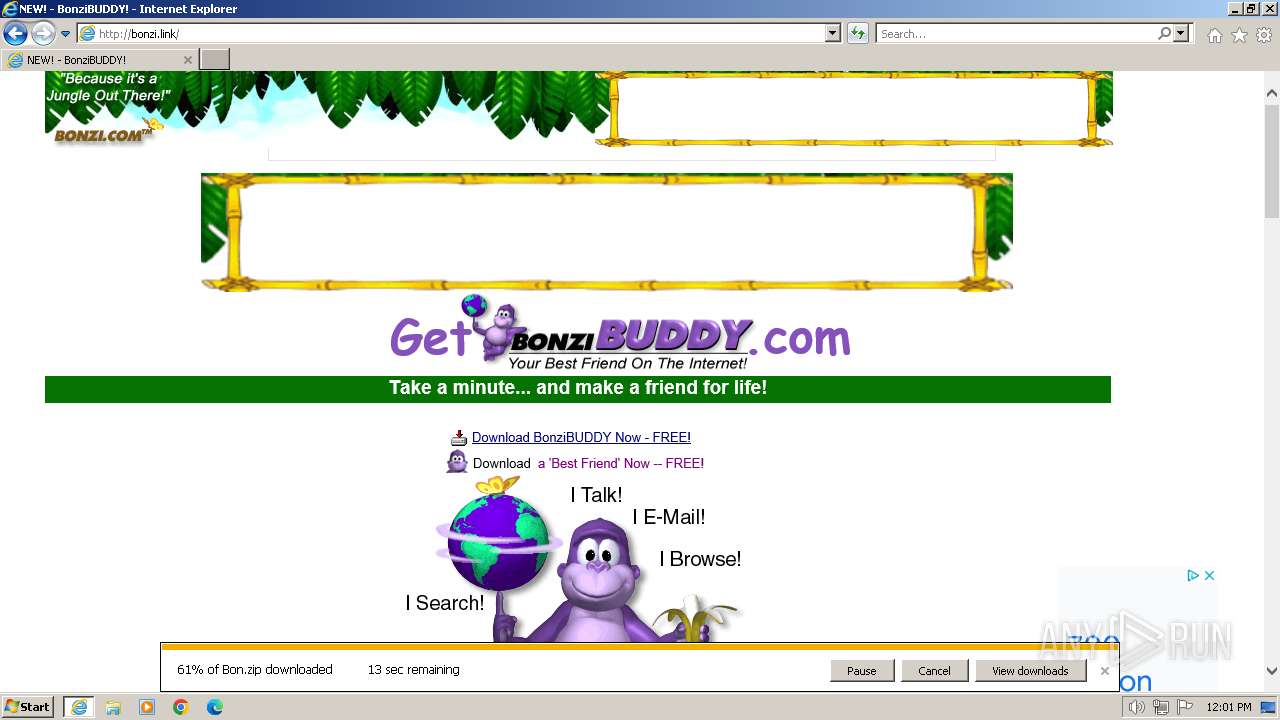
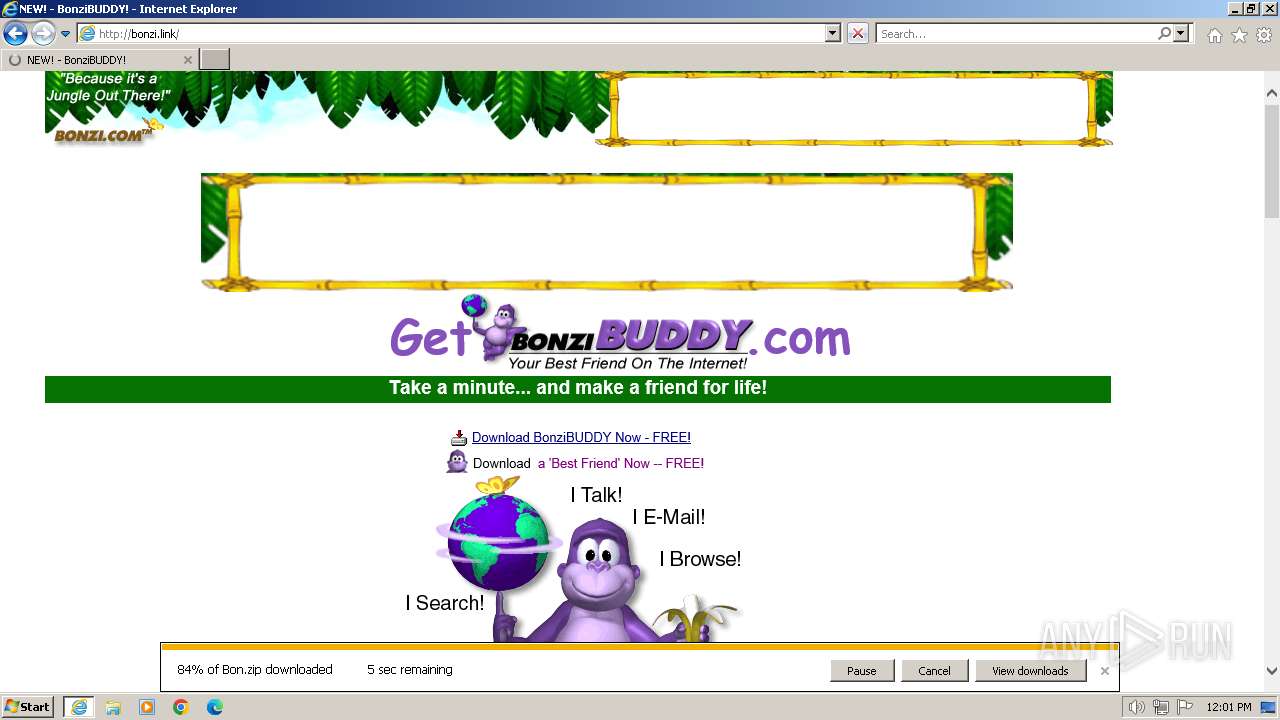
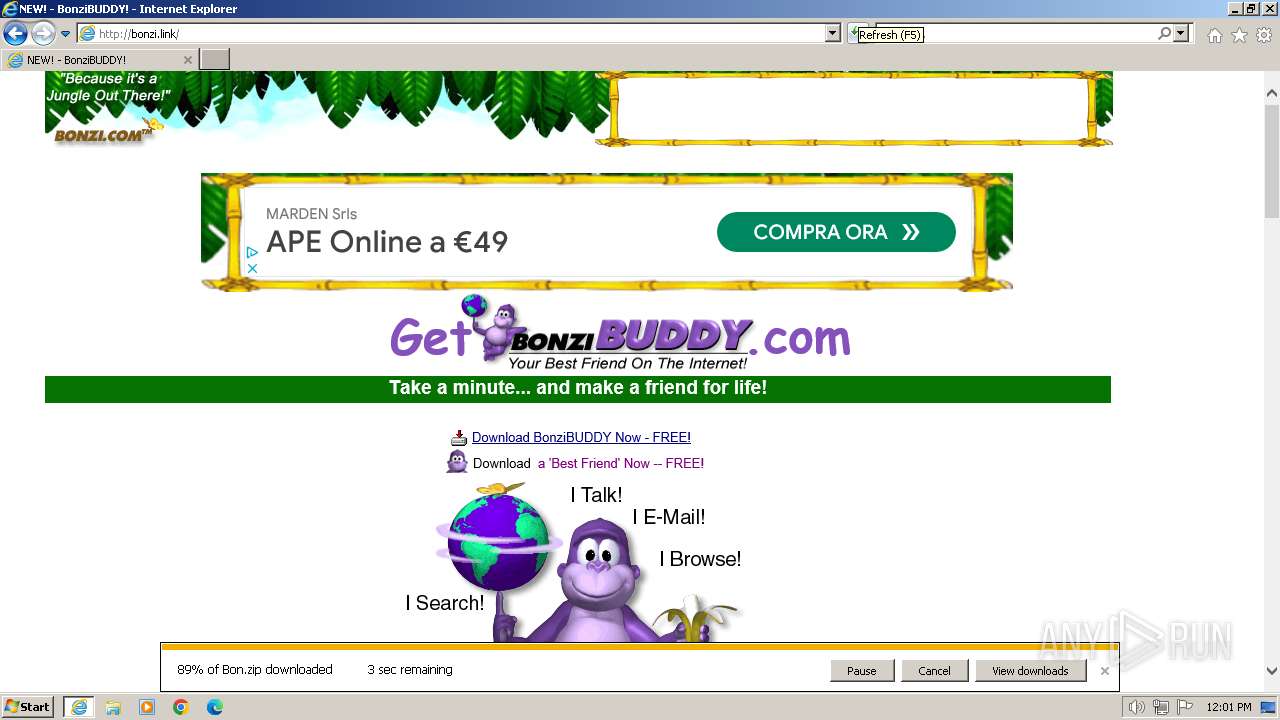
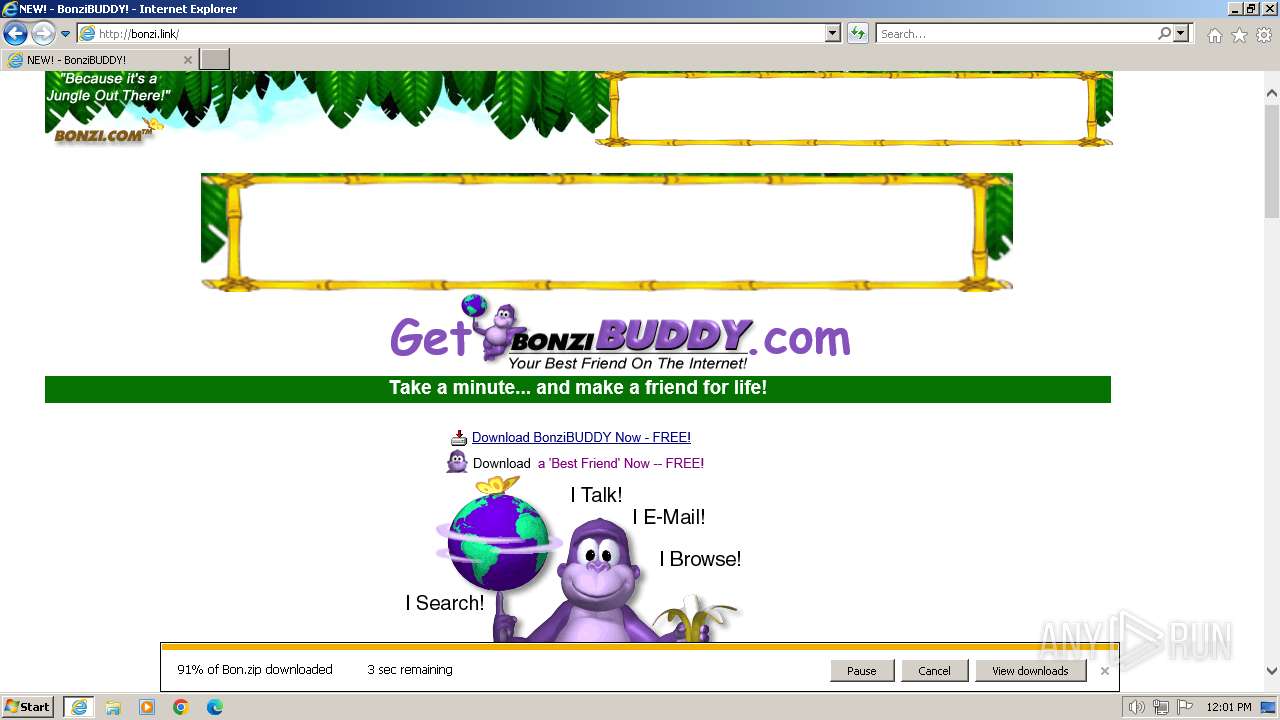
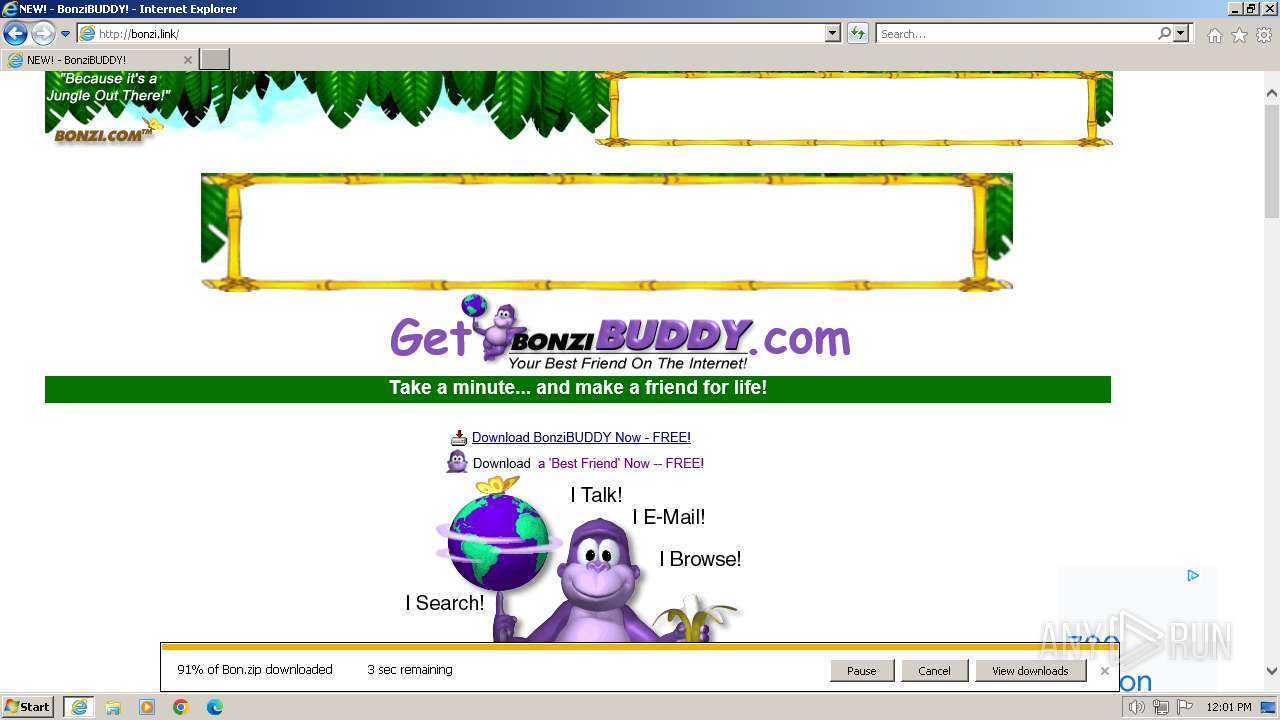
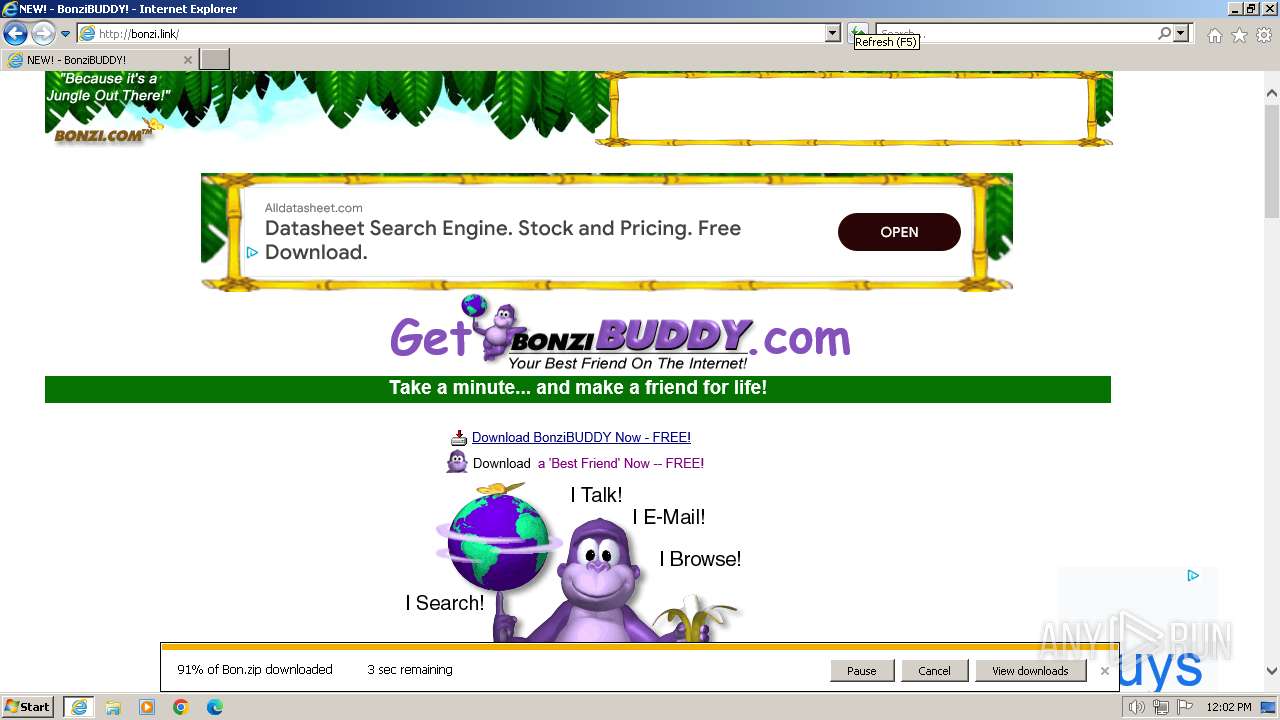
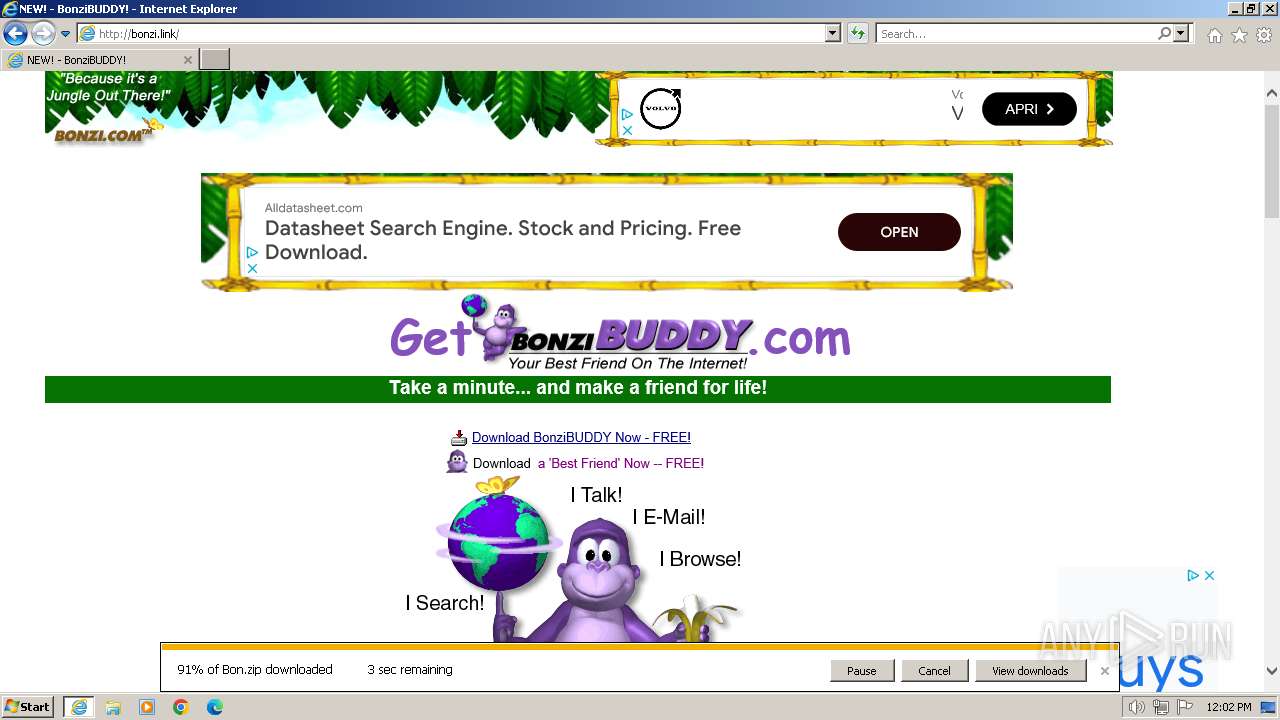
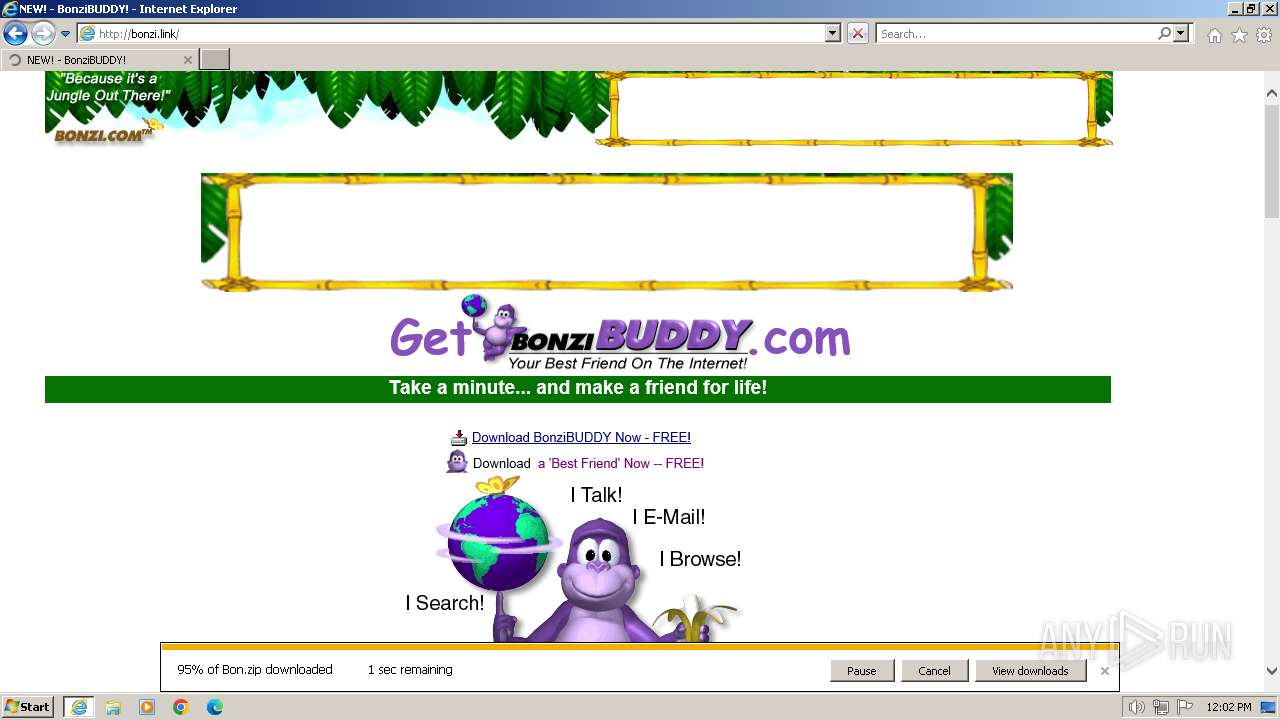
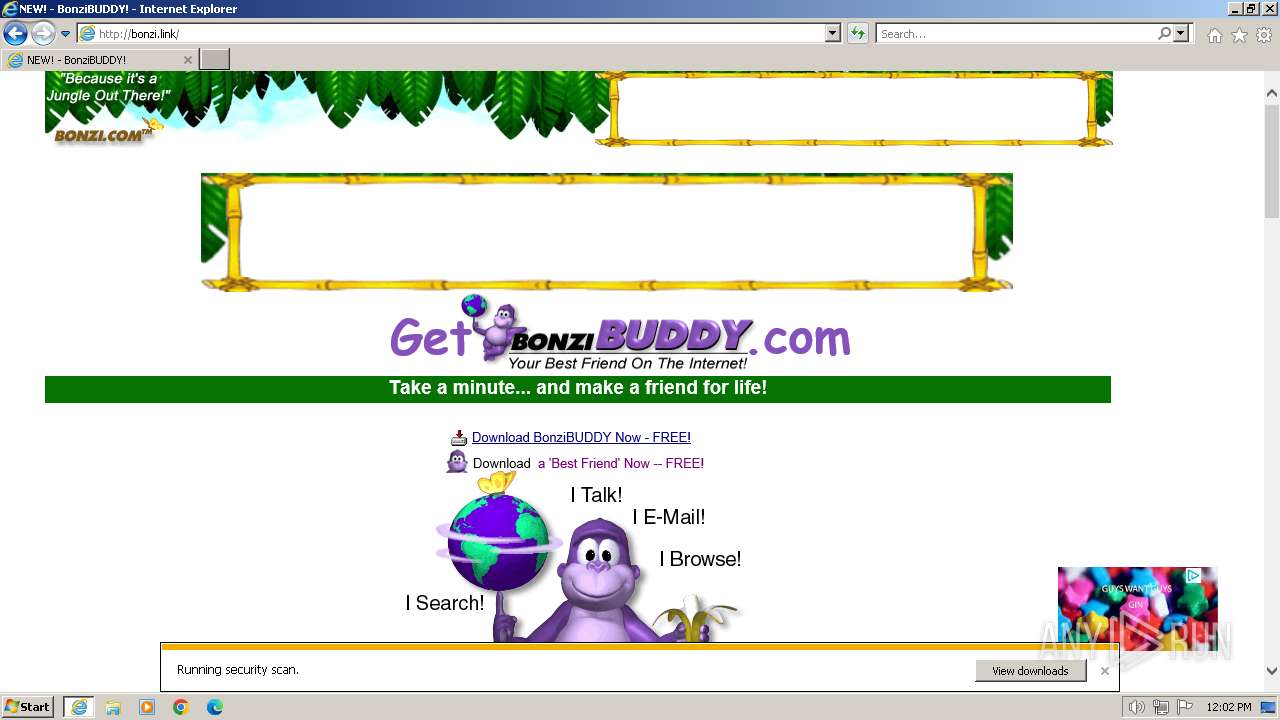
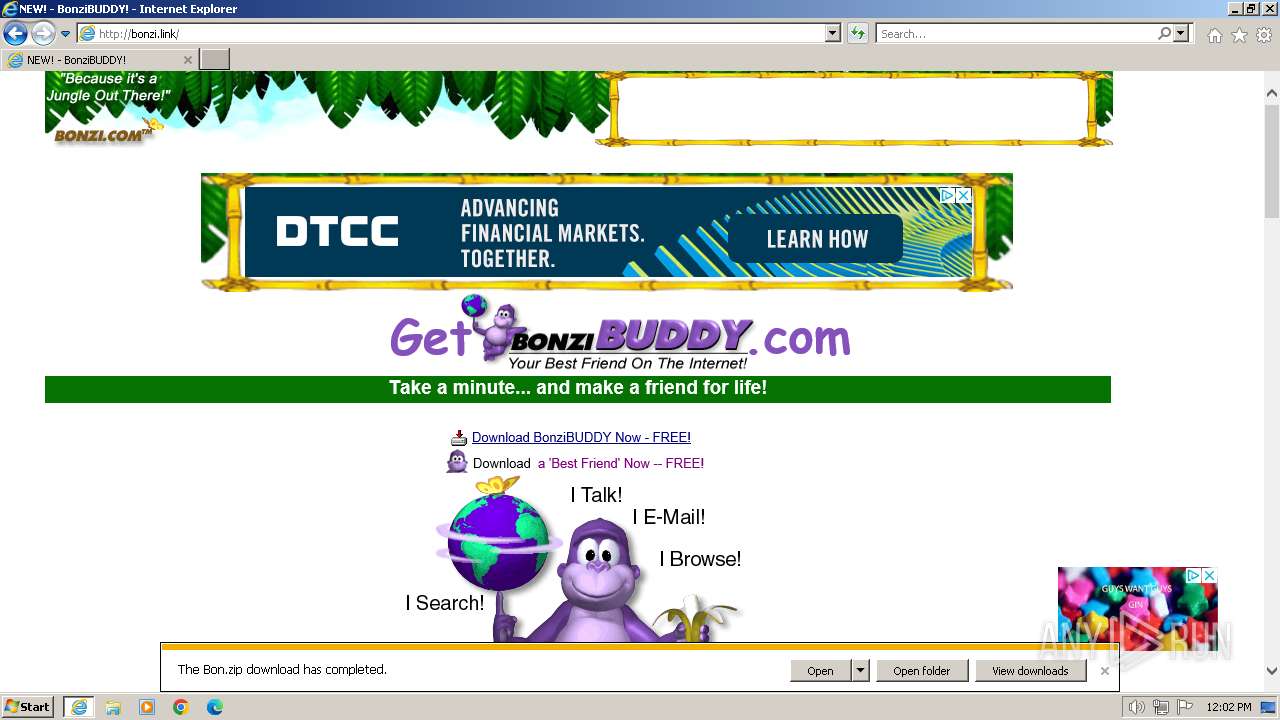
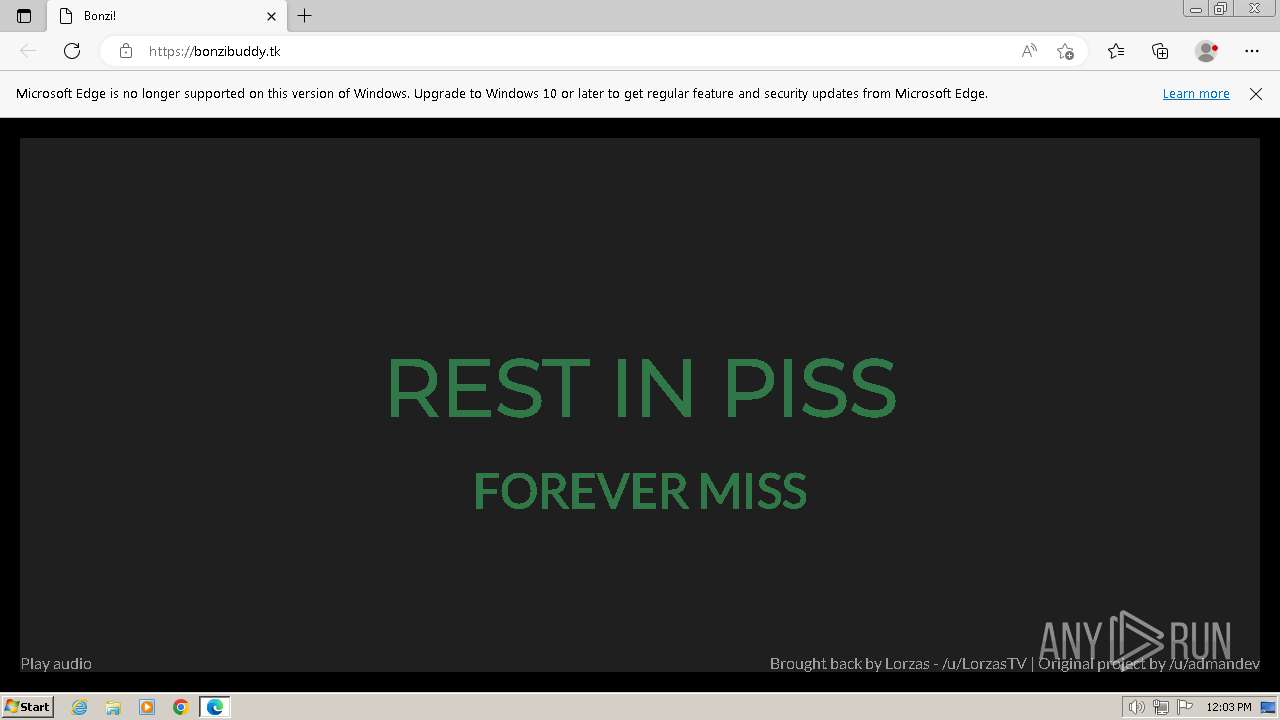
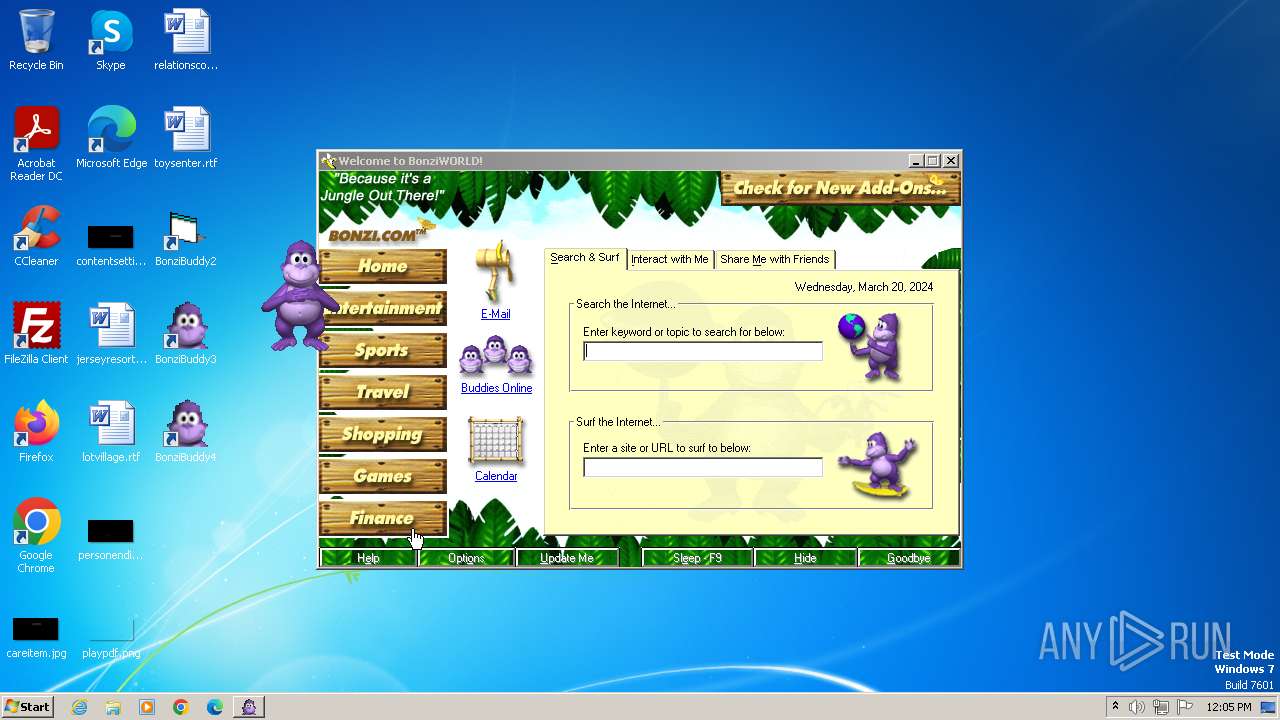
| URL: | https://bonzi.link/ |
| Full analysis: | https://app.any.run/tasks/49053099-57fe-4428-a166-0dab98eba912 |
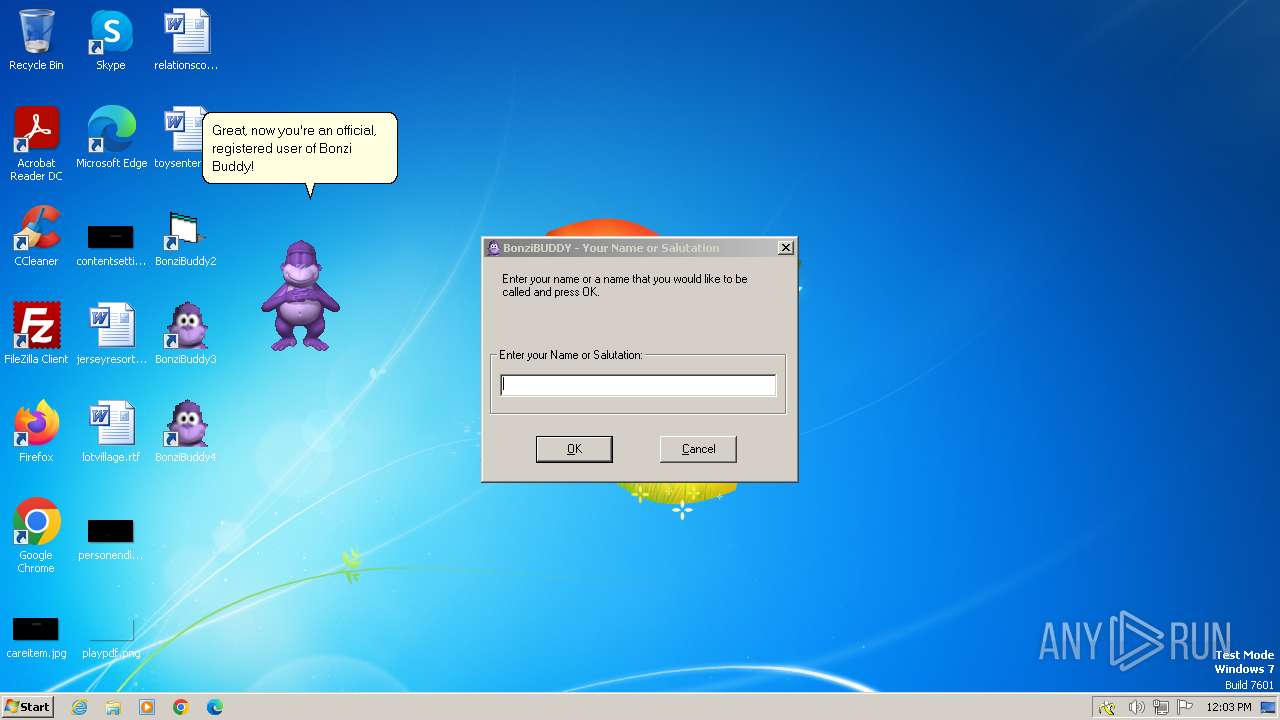
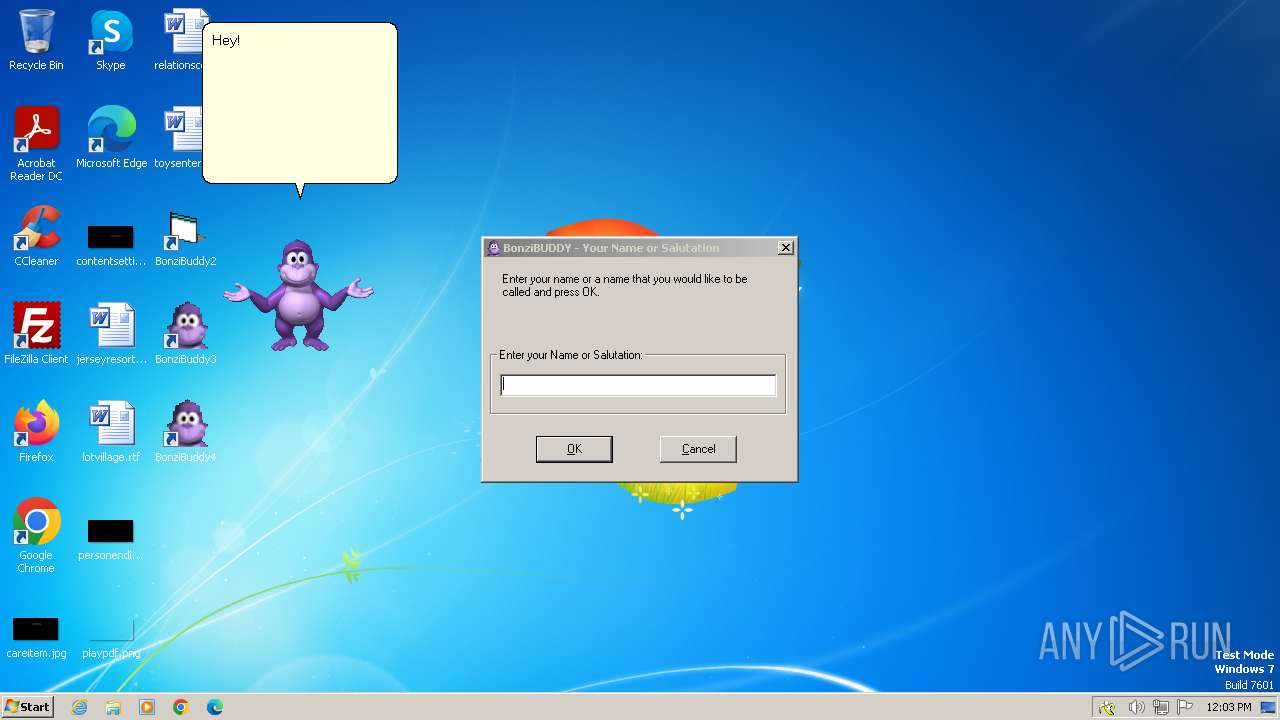
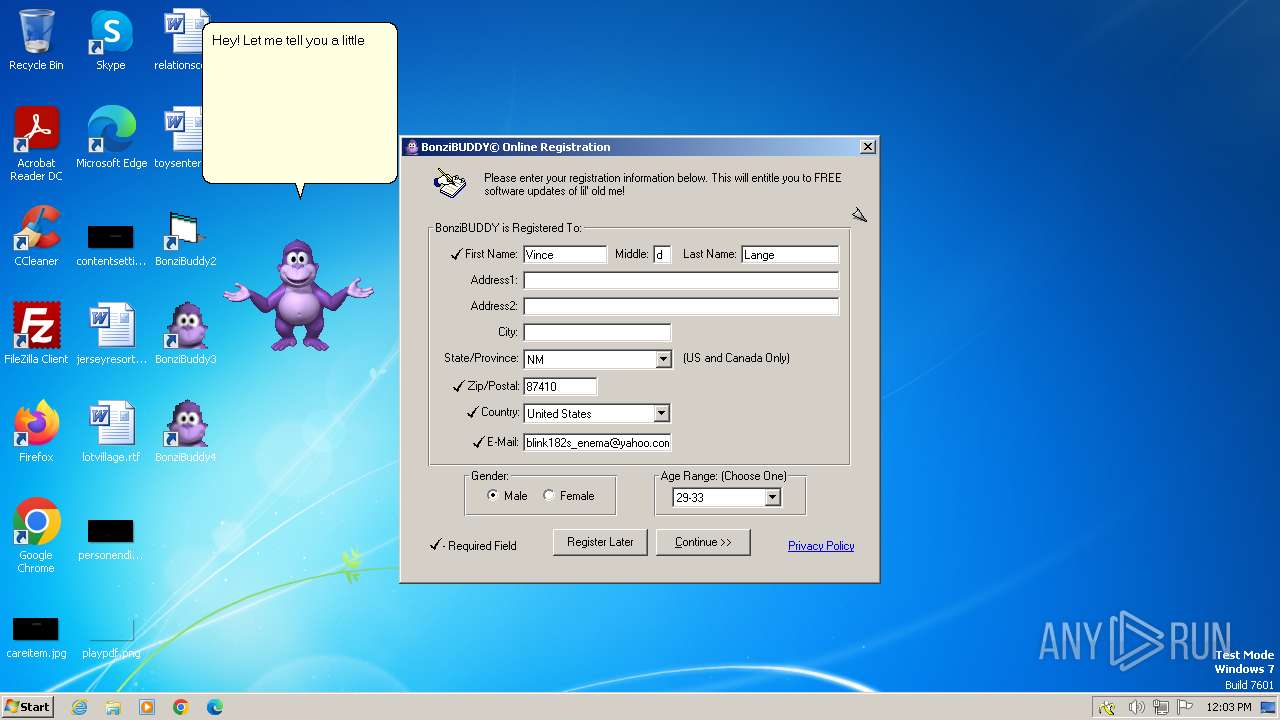
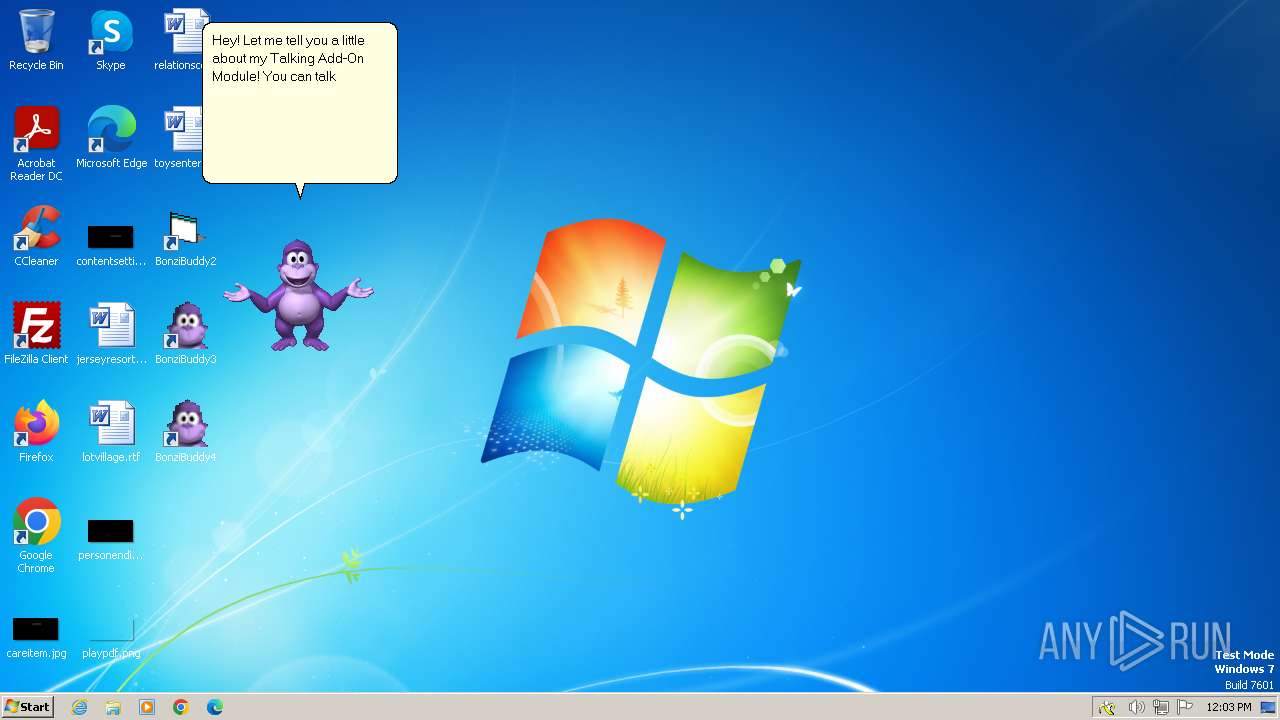
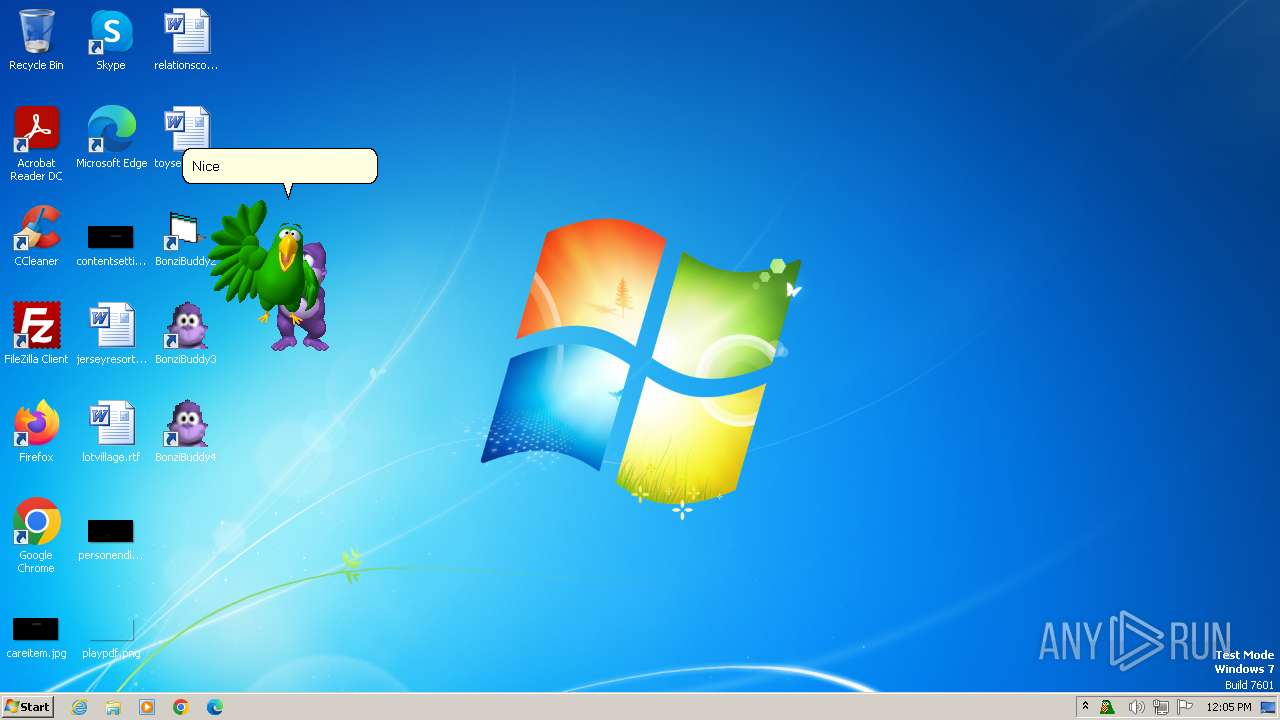
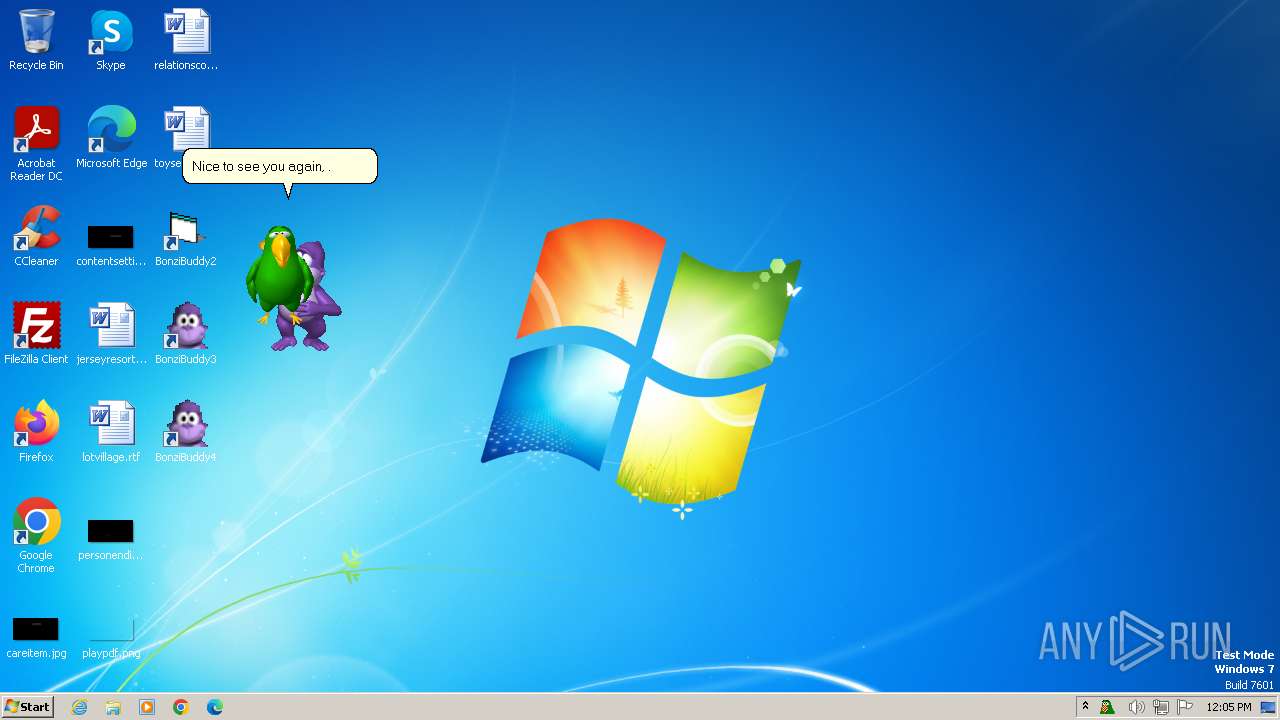
| Verdict: | Malicious activity |
| Analysis date: | March 20, 2024, 12:00:36 |
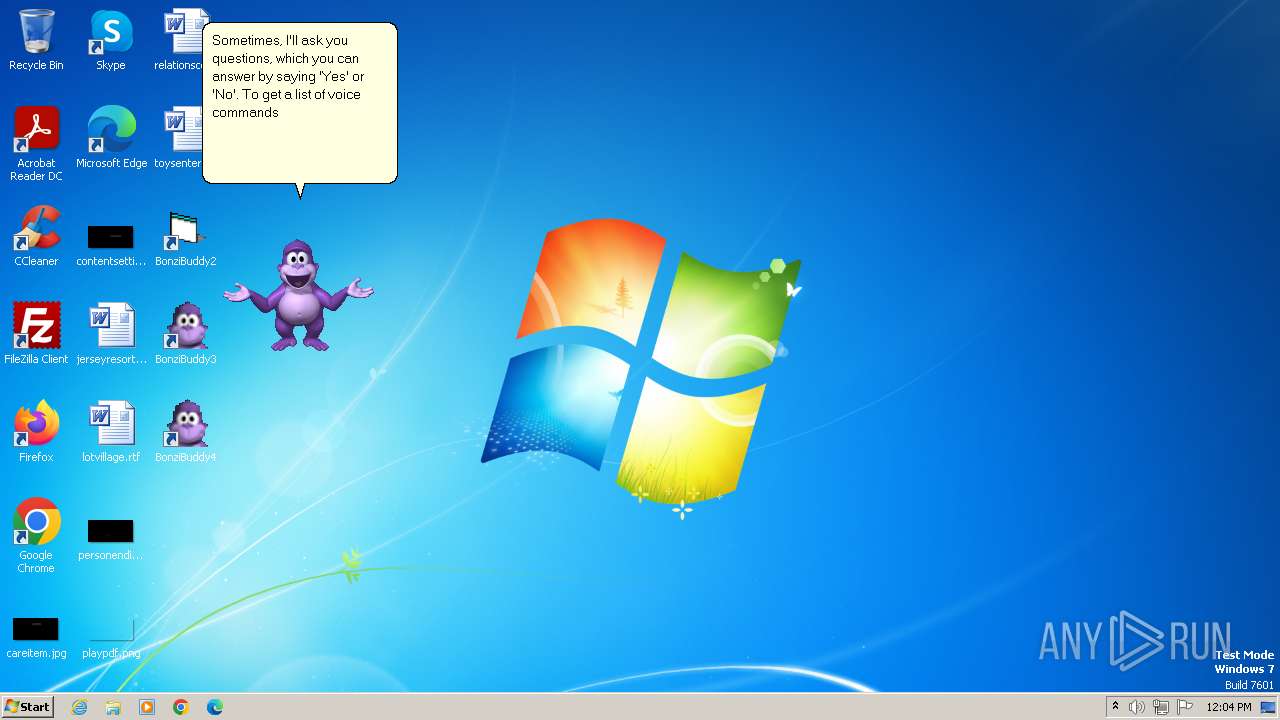
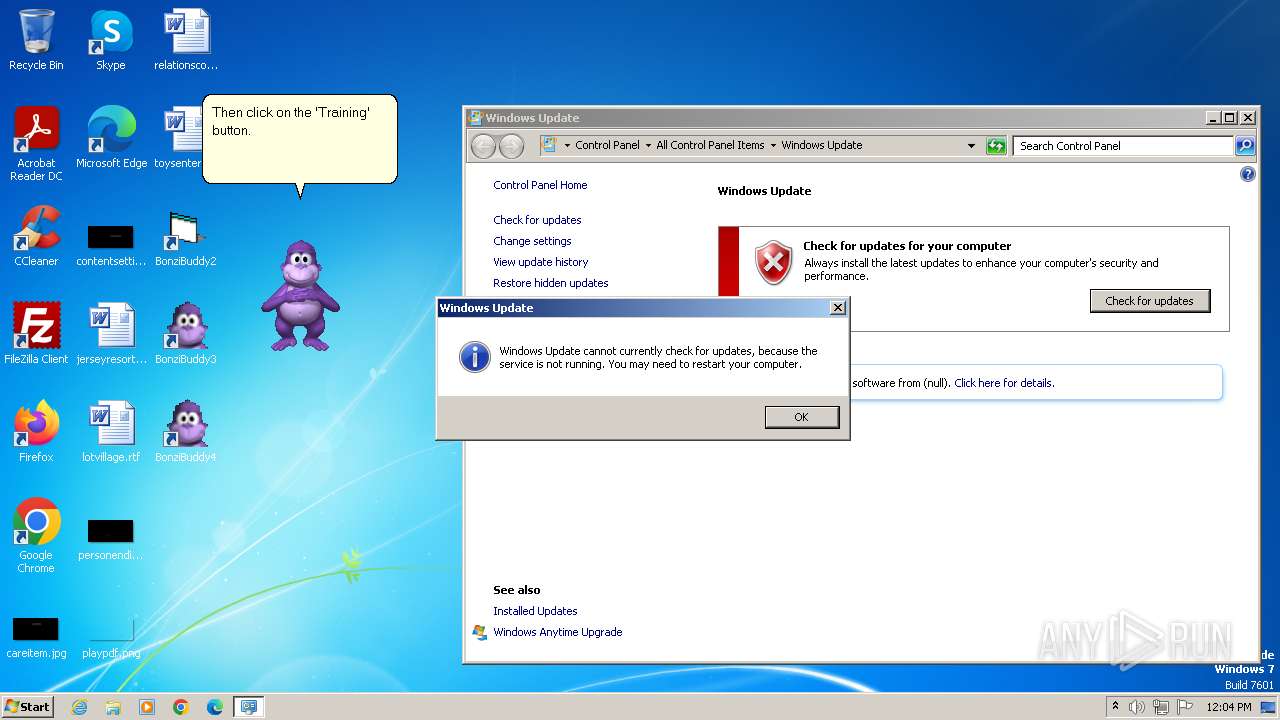
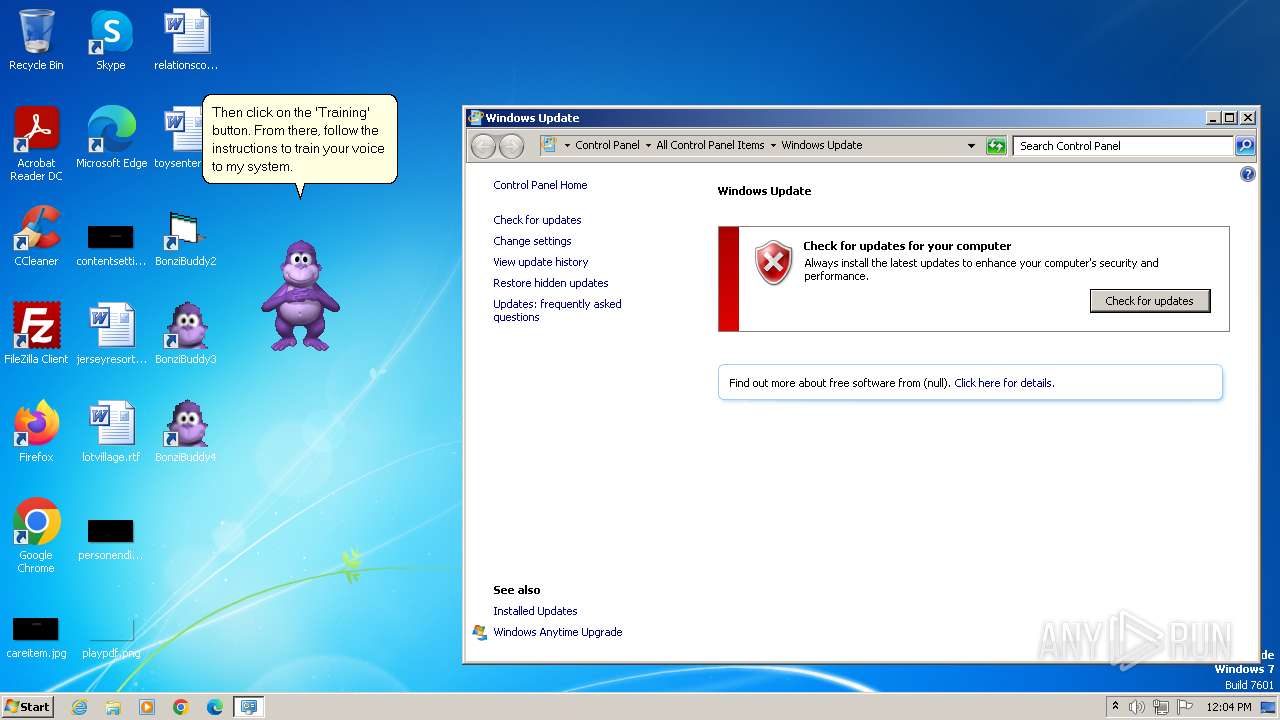
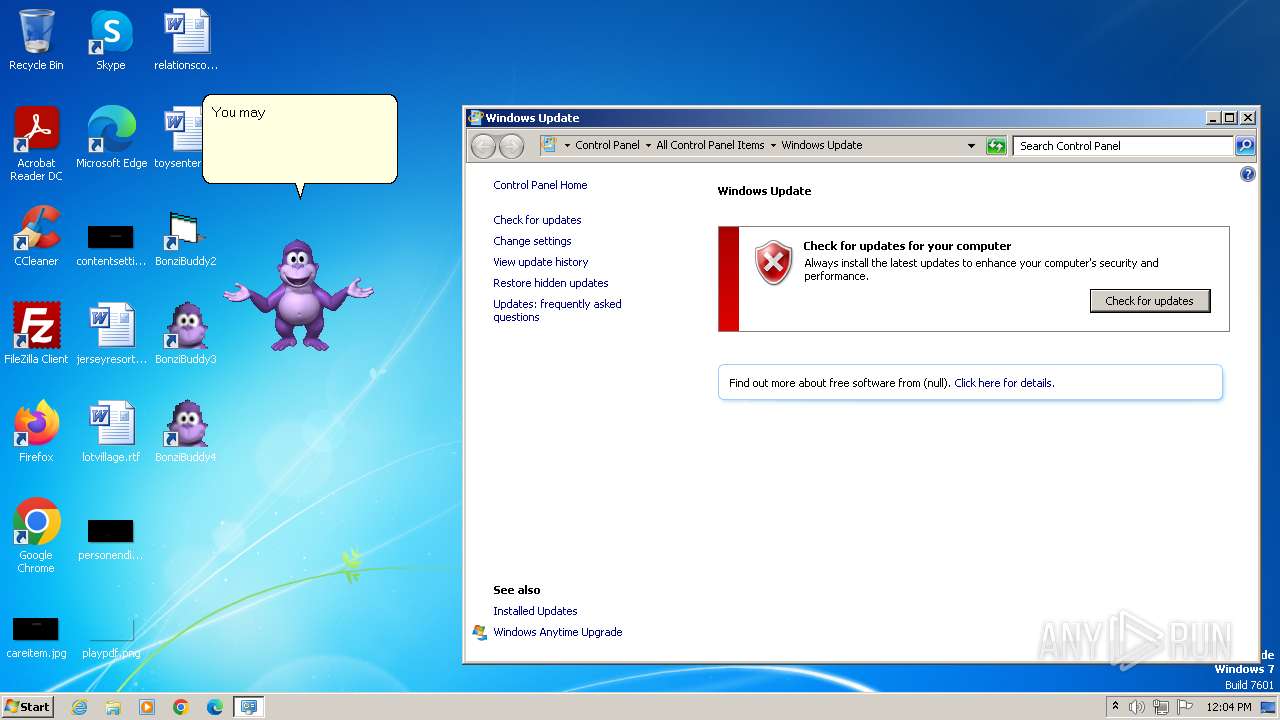
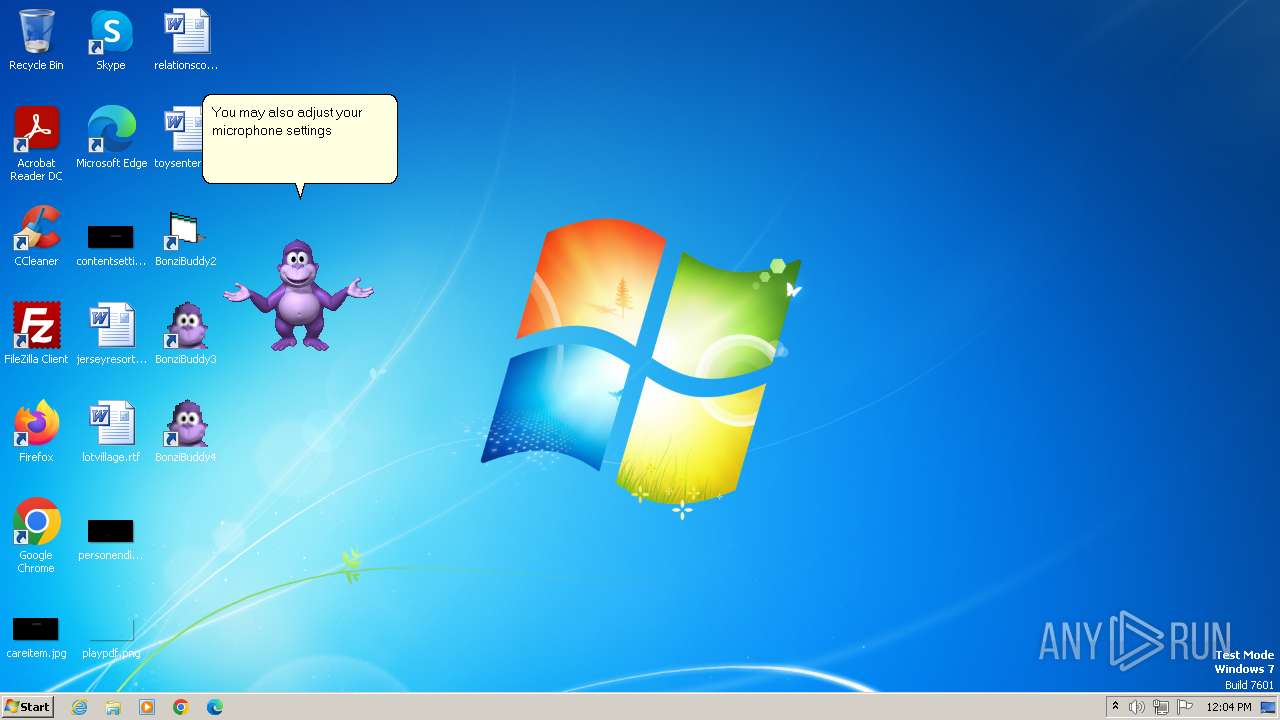
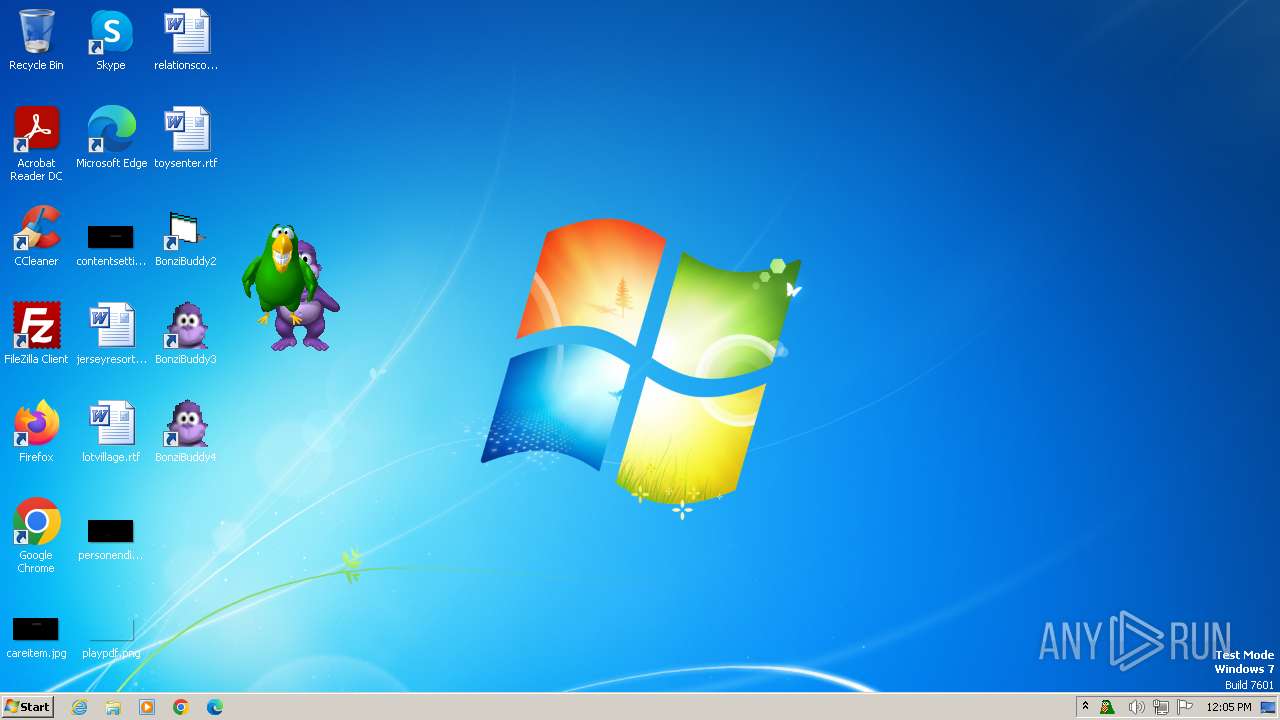
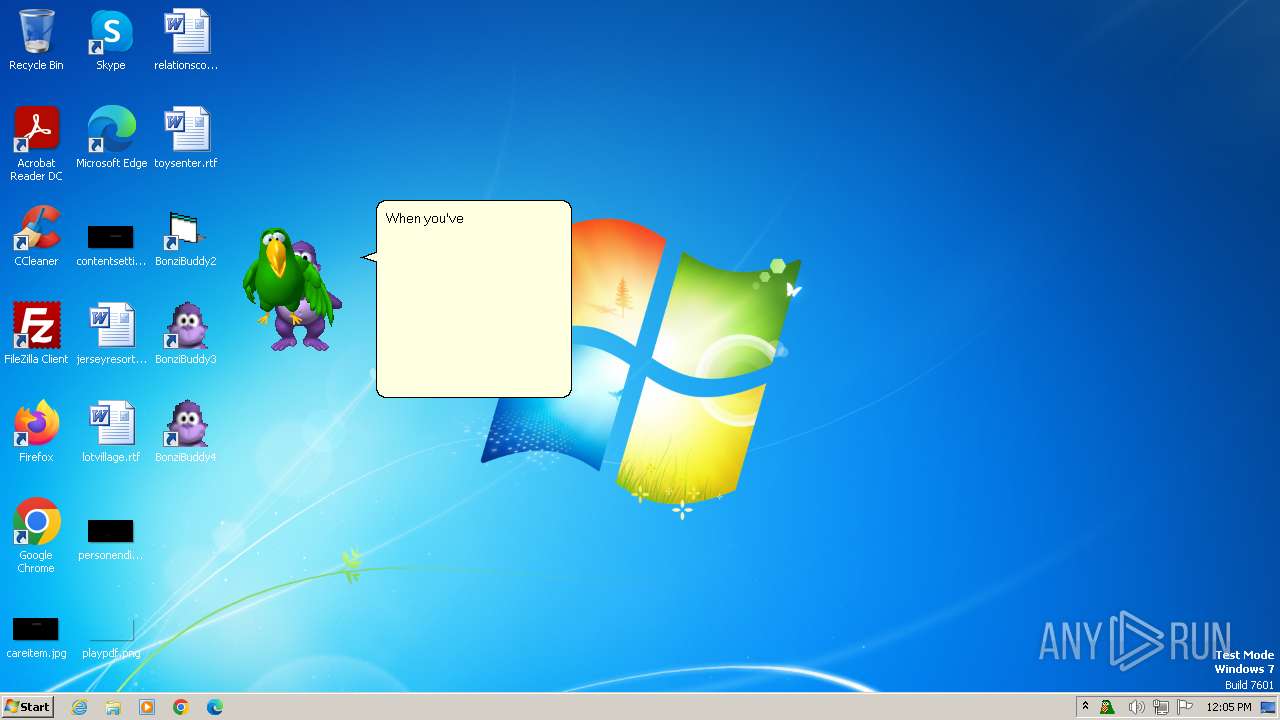
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1140171B39D570CE50B3779922DF0894 |
| SHA1: | BCF0DB75B50DFC7EB2906063628C9B14D4FA7B58 |
| SHA256: | E9F27F4B83B04B449BC7D4C120CB245ED43E338CBB94D341F735FE0889D60BFD |
| SSDEEP: | 3:N89K:29K |
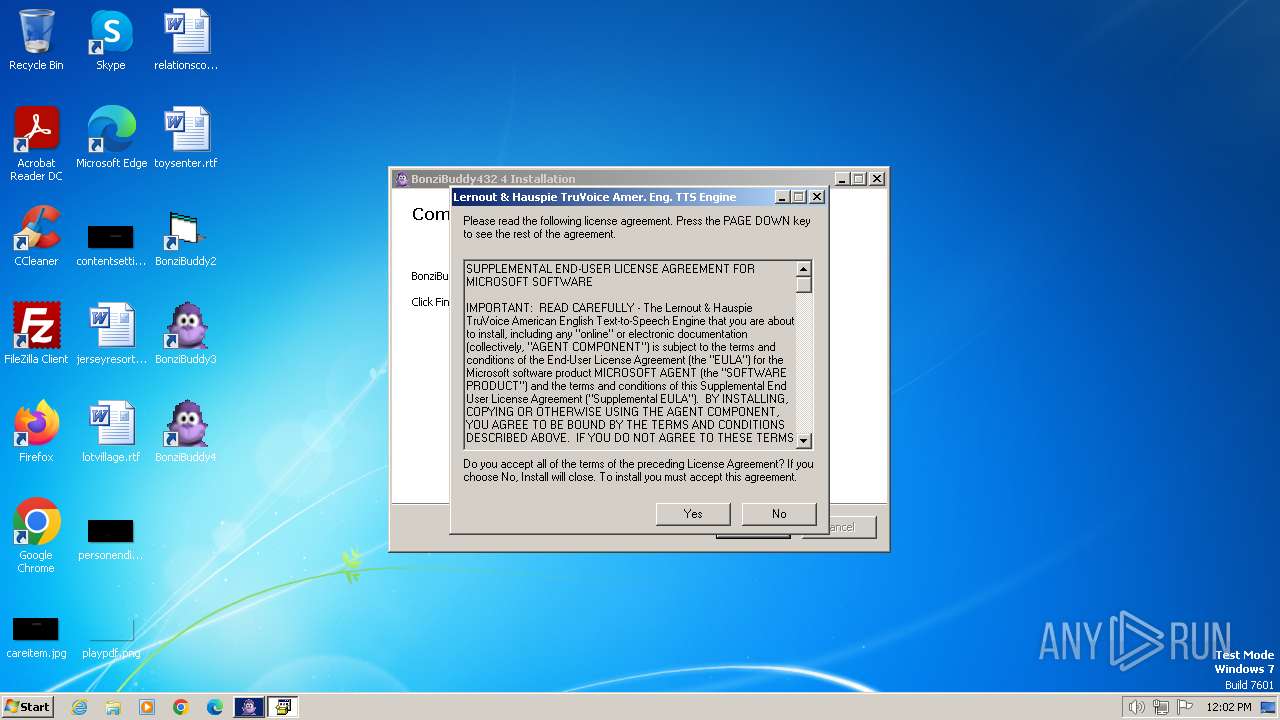
MALICIOUS
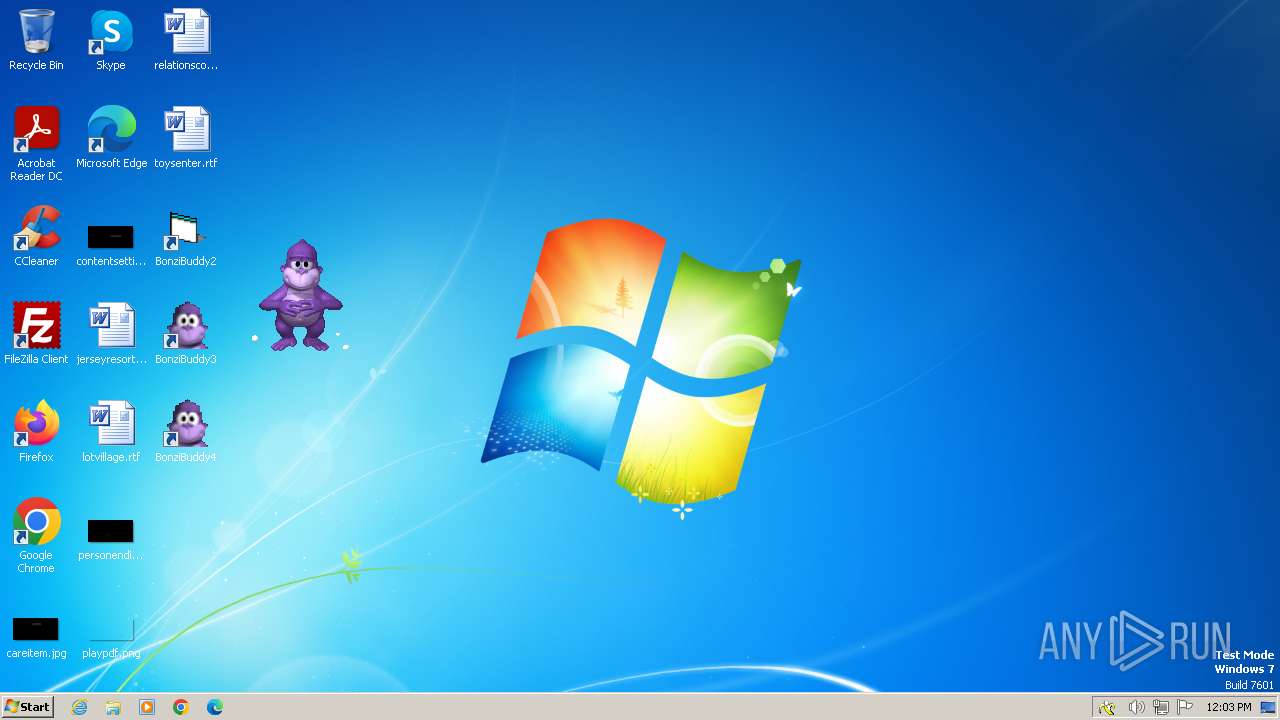
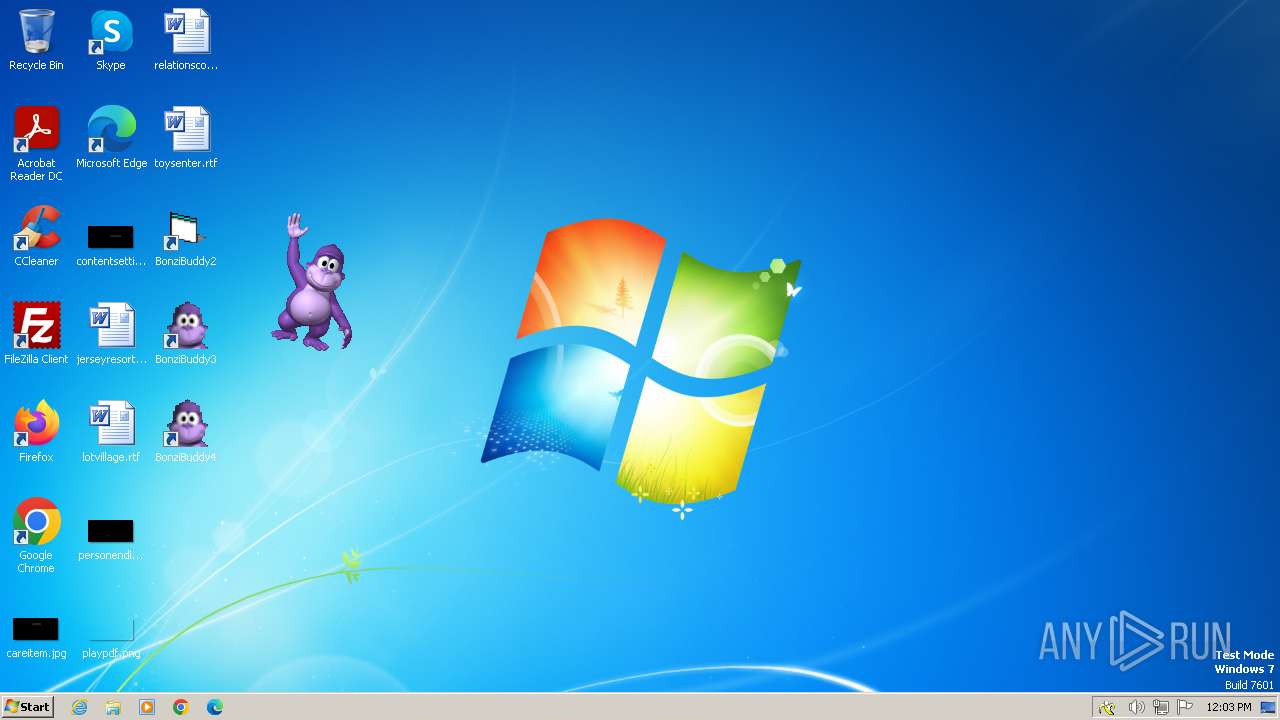
Drops the executable file immediately after the start
- BonziBuddy432.exe (PID: 1028)
- MSAGENT.EXE (PID: 1288)
- tv_enua.exe (PID: 1072)
Registers / Runs the DLL via REGSVR32.EXE
- MSAGENT.EXE (PID: 1288)
- tv_enua.exe (PID: 1072)
Changes the autorun value in the registry
- tv_enua.exe (PID: 1072)
Creates a writable file in the system directory
- tv_enua.exe (PID: 1072)
SUSPICIOUS
Process drops legitimate windows executable
- BonziBuddy432.exe (PID: 1028)
- MSAGENT.EXE (PID: 1288)
- tv_enua.exe (PID: 1072)
Executable content was dropped or overwritten
- BonziBuddy432.exe (PID: 1028)
- MSAGENT.EXE (PID: 1288)
- tv_enua.exe (PID: 1072)
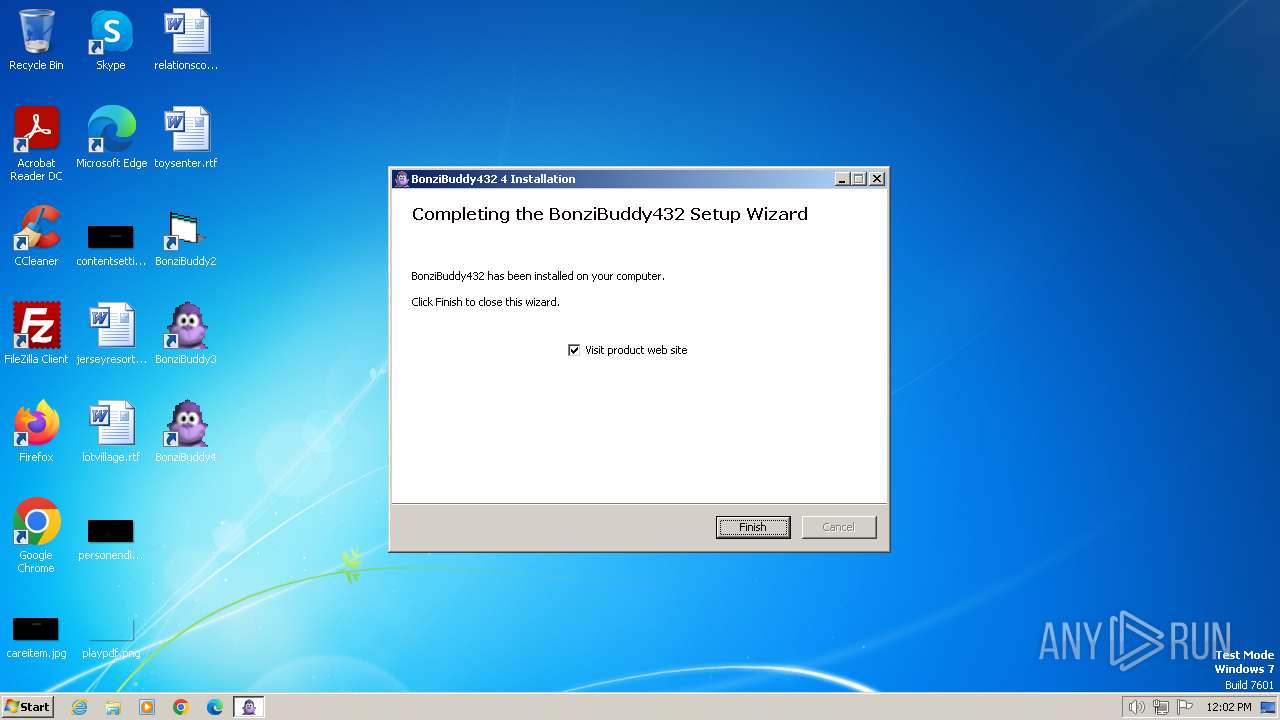
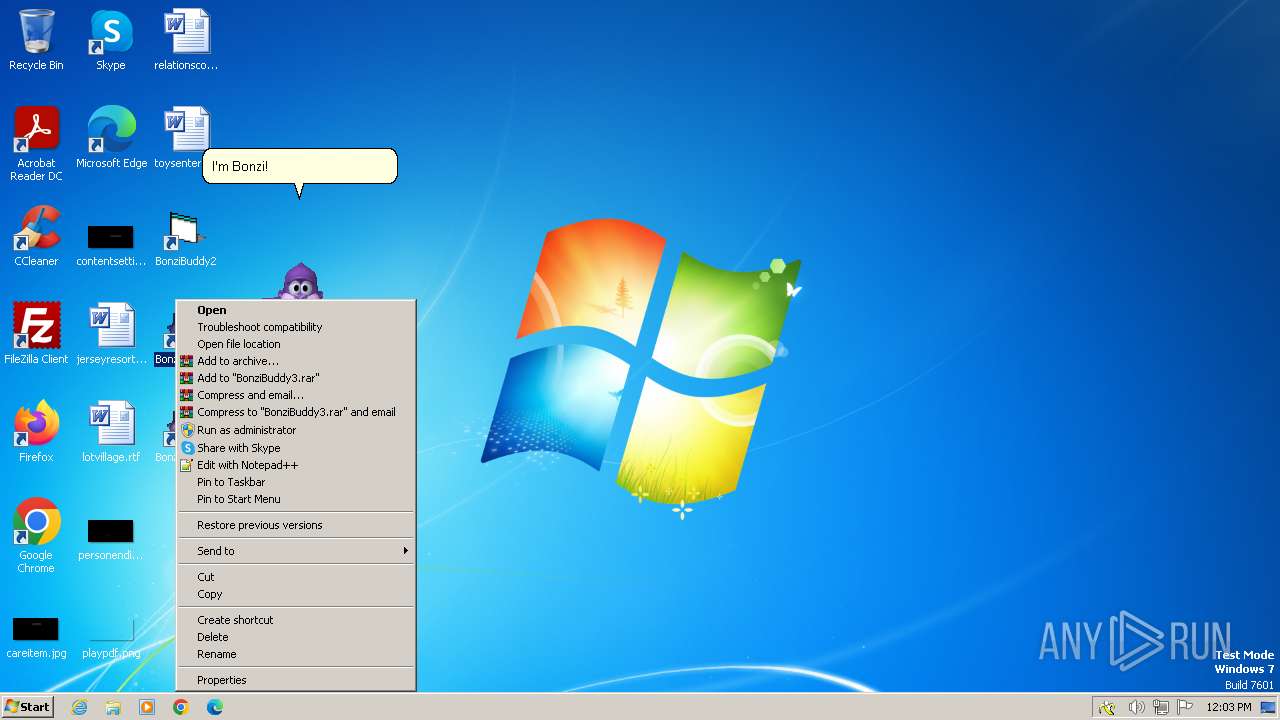
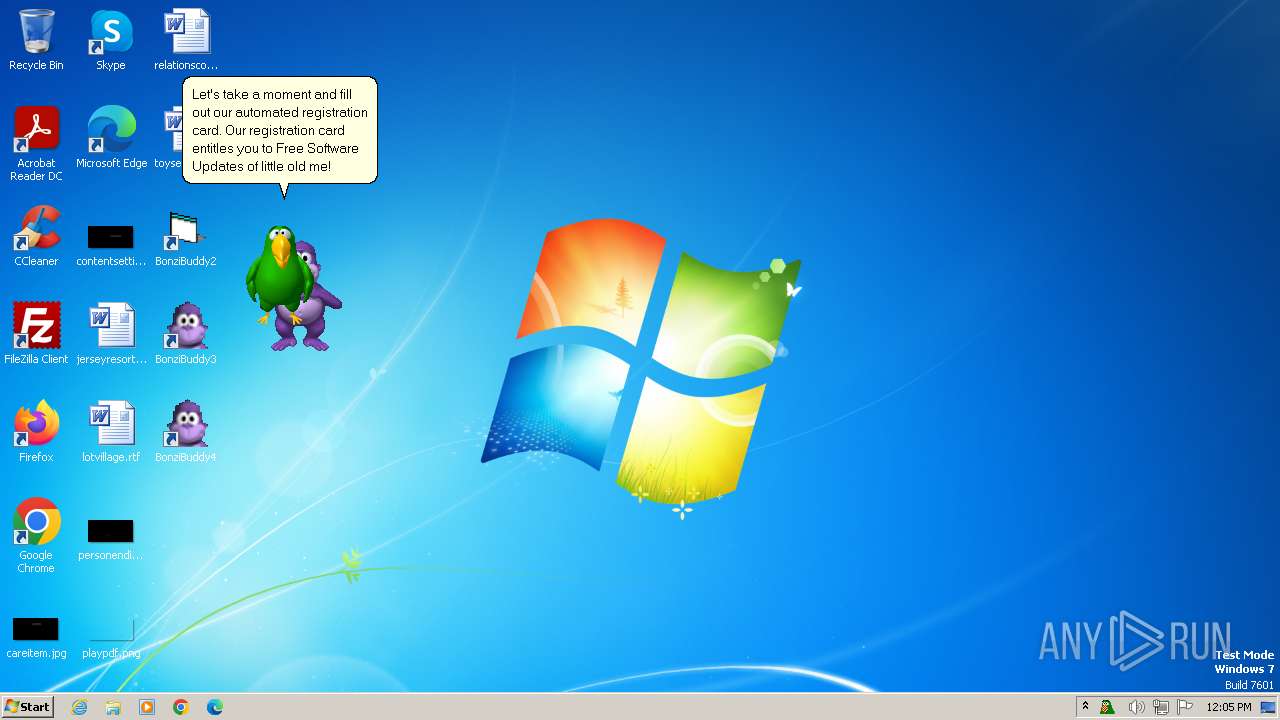
Creates a software uninstall entry
- BonziBuddy432.exe (PID: 1028)
- tv_enua.exe (PID: 1072)
Reads security settings of Internet Explorer
- BonziBuddy432.exe (PID: 1028)
- BonziBDY_35.EXE (PID: 1604)
- BonziBDY_4.EXE (PID: 2760)
Reads the Internet Settings
- BonziBuddy432.exe (PID: 1028)
- BonziBDY_35.EXE (PID: 1604)
- BonziBDY_4.EXE (PID: 2760)
Executing commands from a ".bat" file
- BonziBuddy432.exe (PID: 1028)
Starts CMD.EXE for commands execution
- BonziBuddy432.exe (PID: 1028)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 3060)
- regsvr32.exe (PID: 2612)
- regsvr32.exe (PID: 2436)
- regsvr32.exe (PID: 4016)
- regsvr32.exe (PID: 2228)
- BonziBuddy432.exe (PID: 1028)
- regsvr32.exe (PID: 3688)
- regsvr32.exe (PID: 3368)
- regsvr32.exe (PID: 3056)
- regsvr32.exe (PID: 3560)
Reads settings of System Certificates
- BonziBDY_35.EXE (PID: 1604)
Checks Windows Trust Settings
- BonziBDY_35.EXE (PID: 1604)
Adds/modifies Windows certificates
- BonziBDY_35.EXE (PID: 1604)
Uses RUNDLL32.EXE to load library
- BonziBDY_35.EXE (PID: 1604)
INFO
Application launched itself
- iexplore.exe (PID: 3500)
- msedge.exe (PID: 2836)
- msedge.exe (PID: 2860)
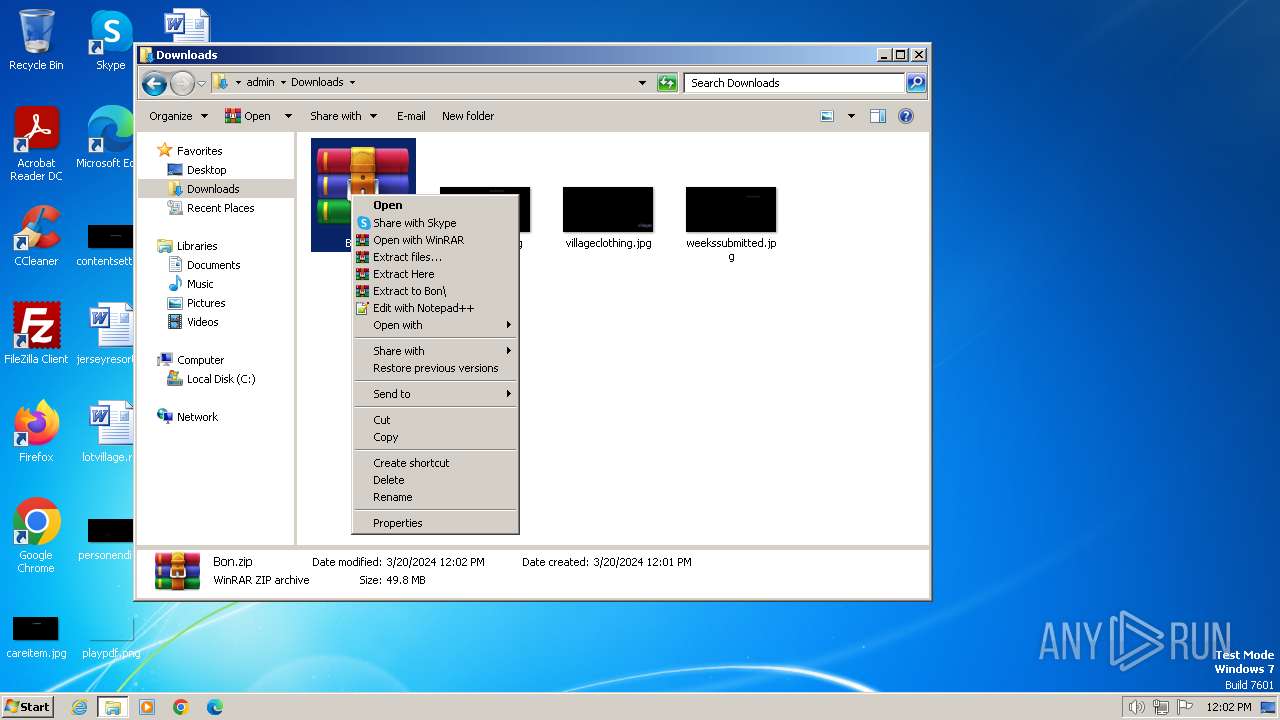
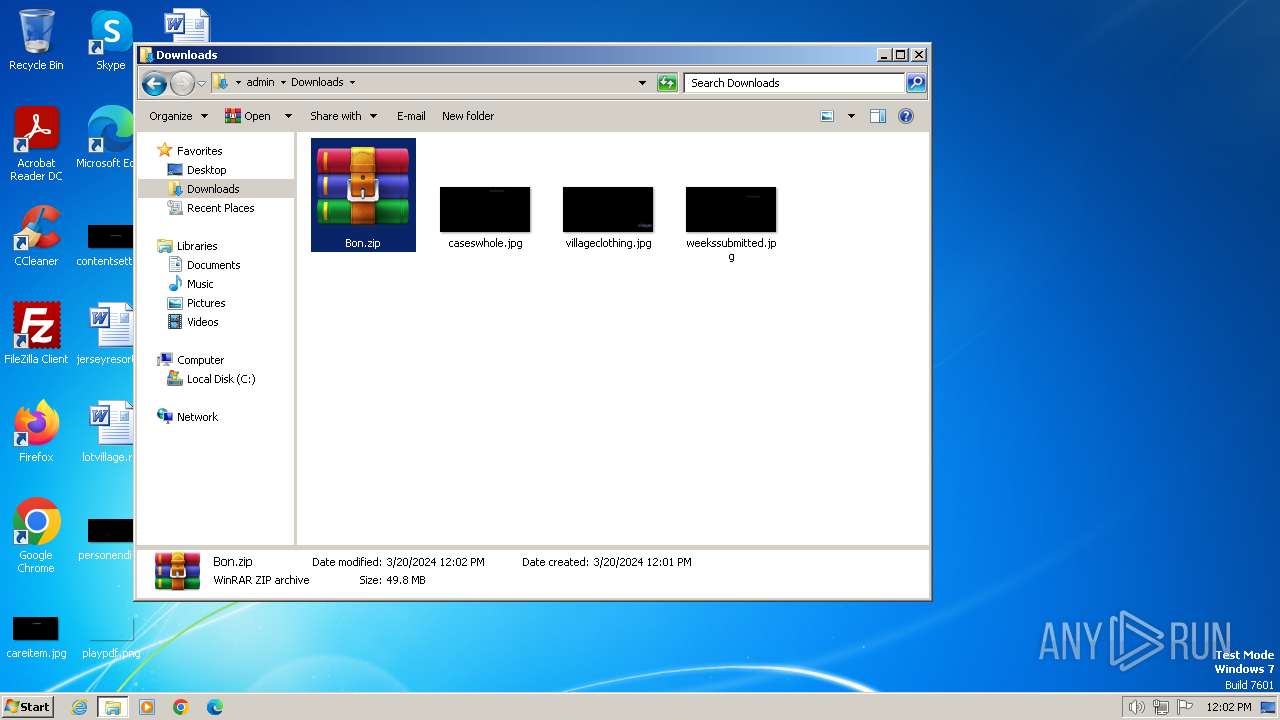
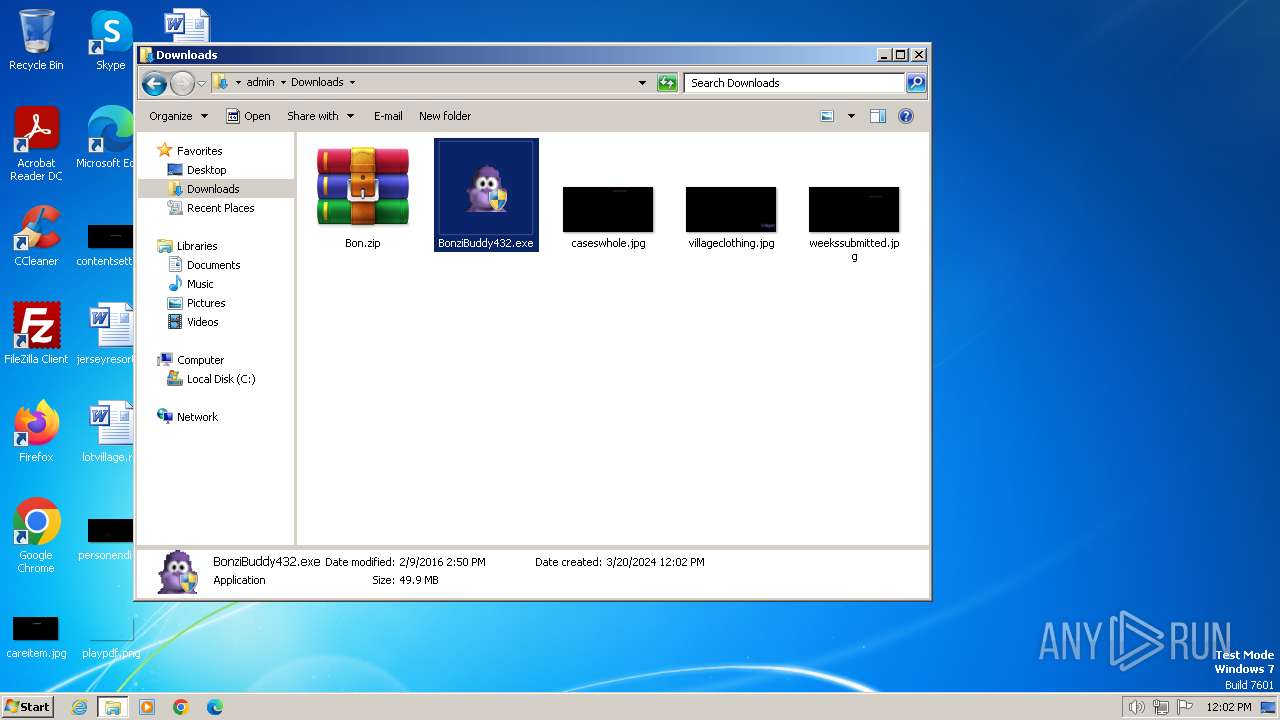
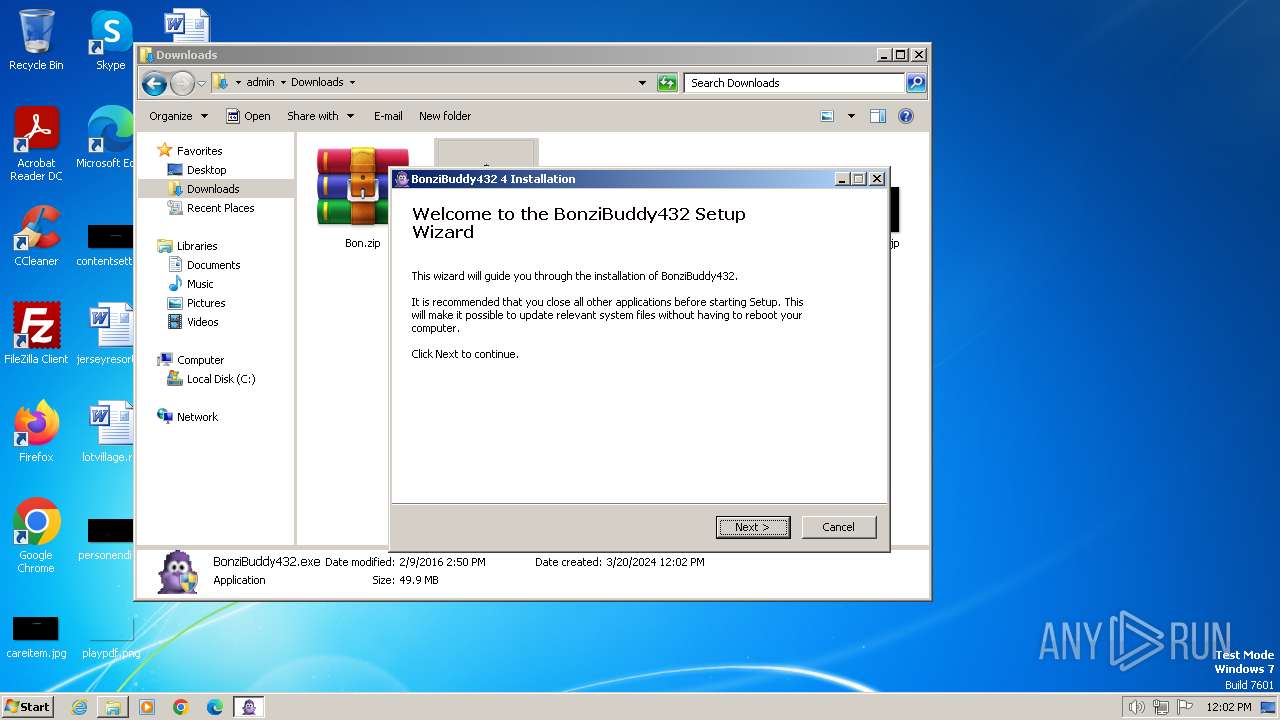
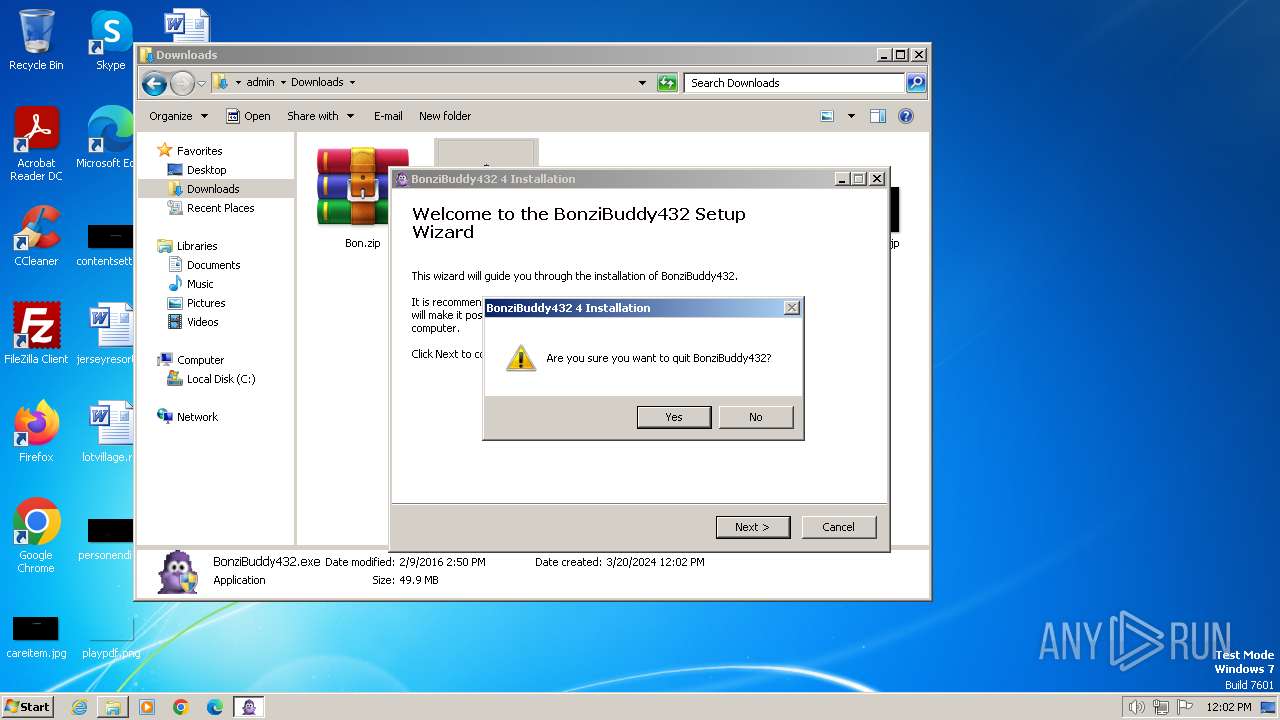
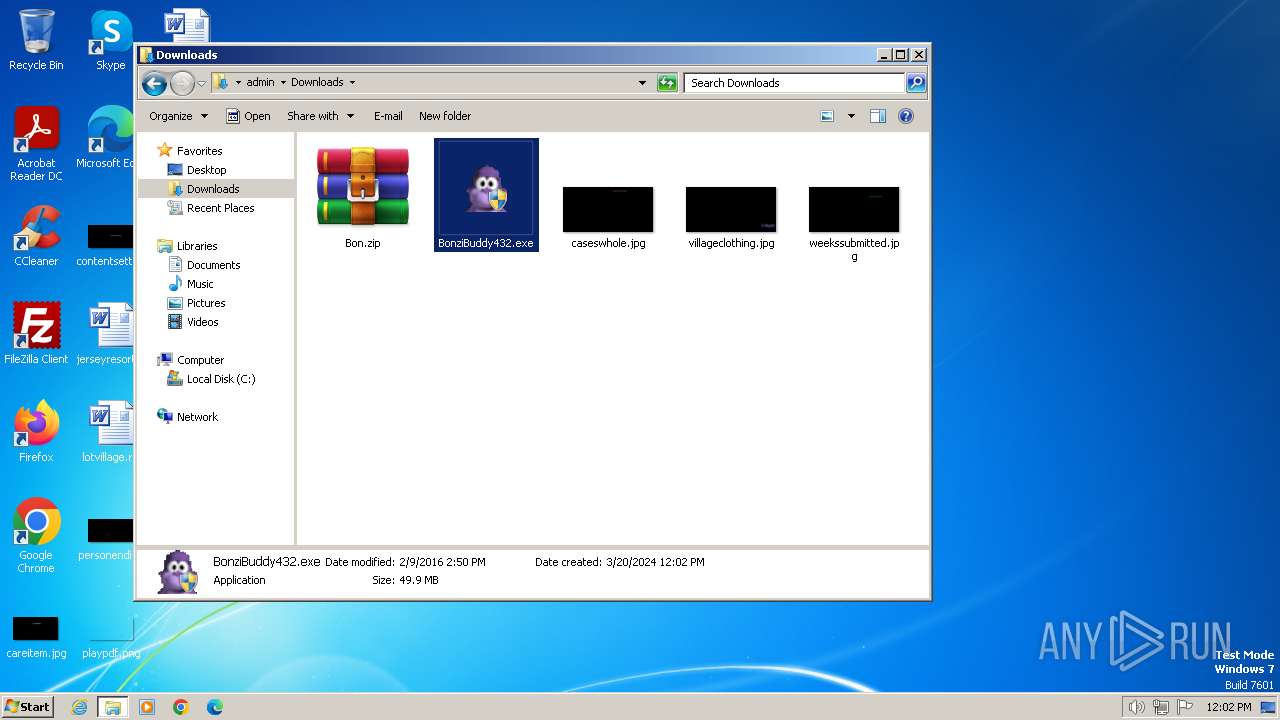
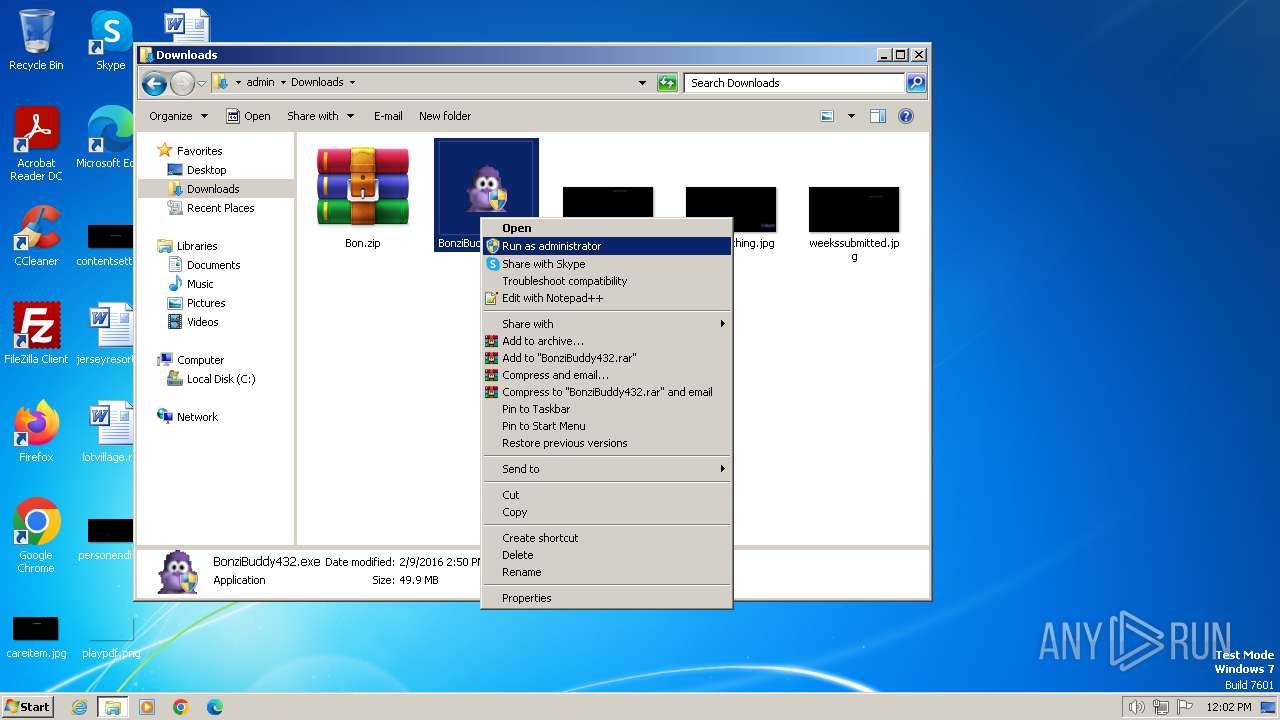
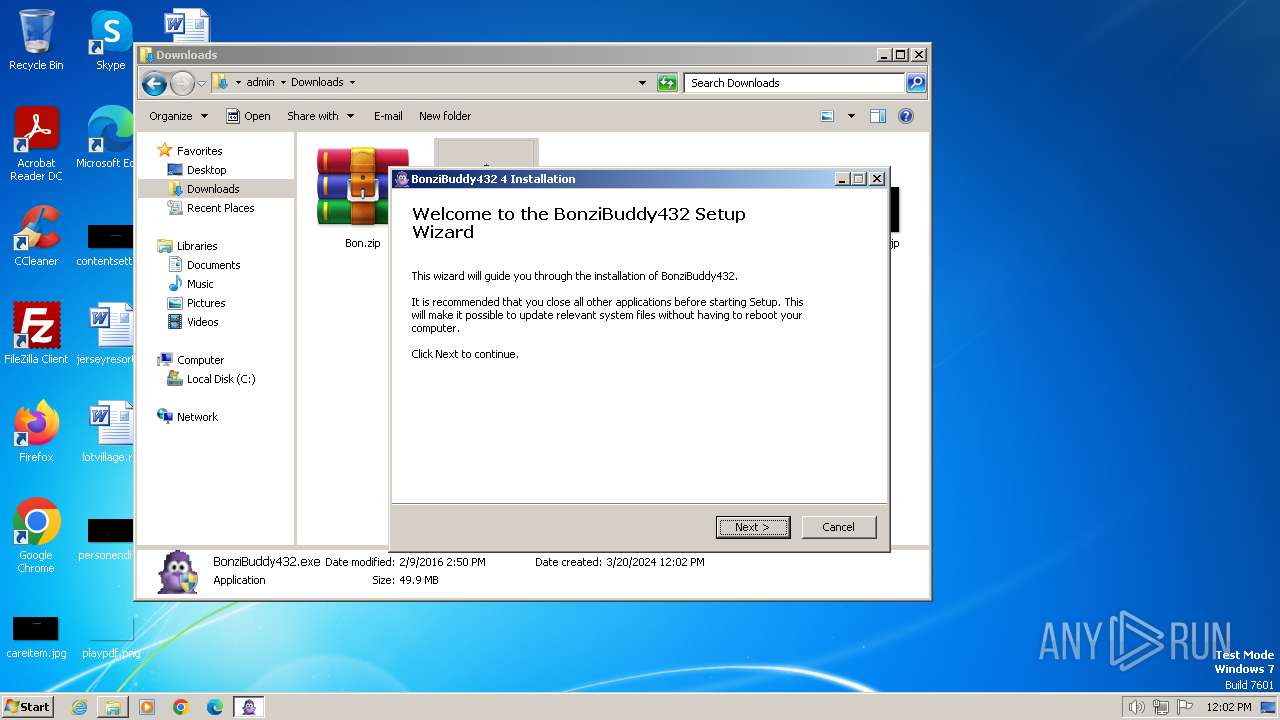
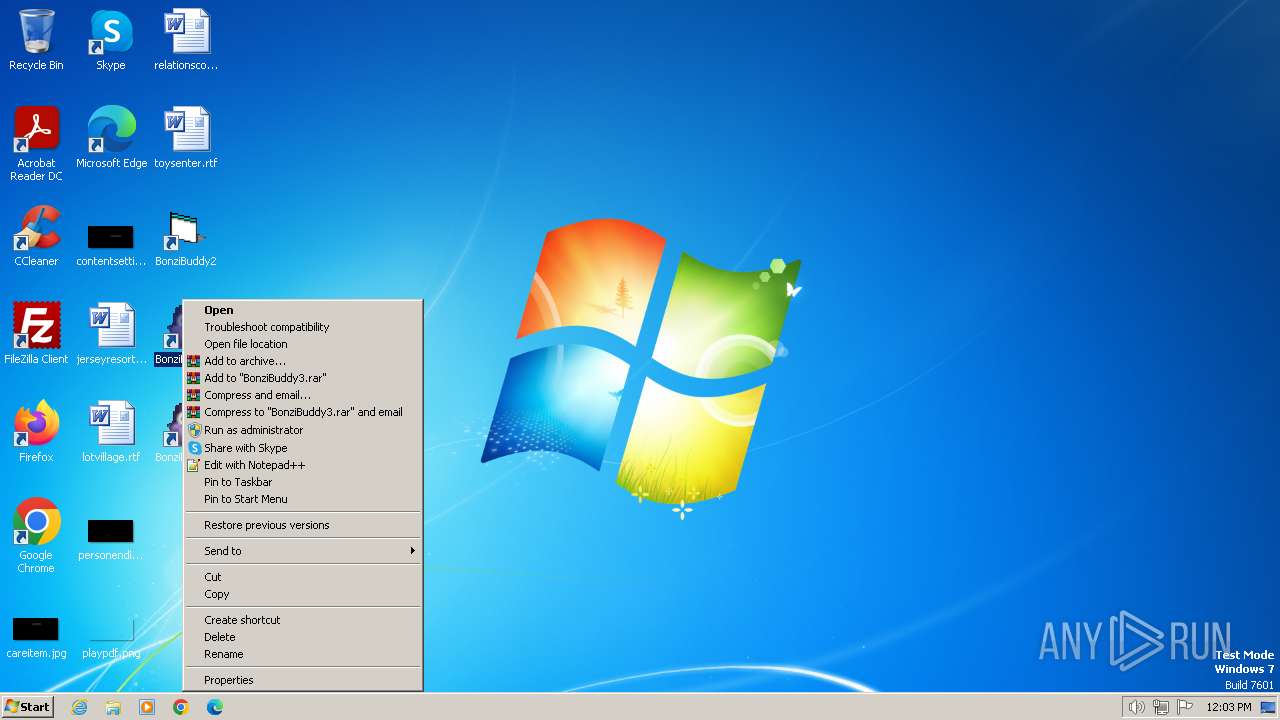
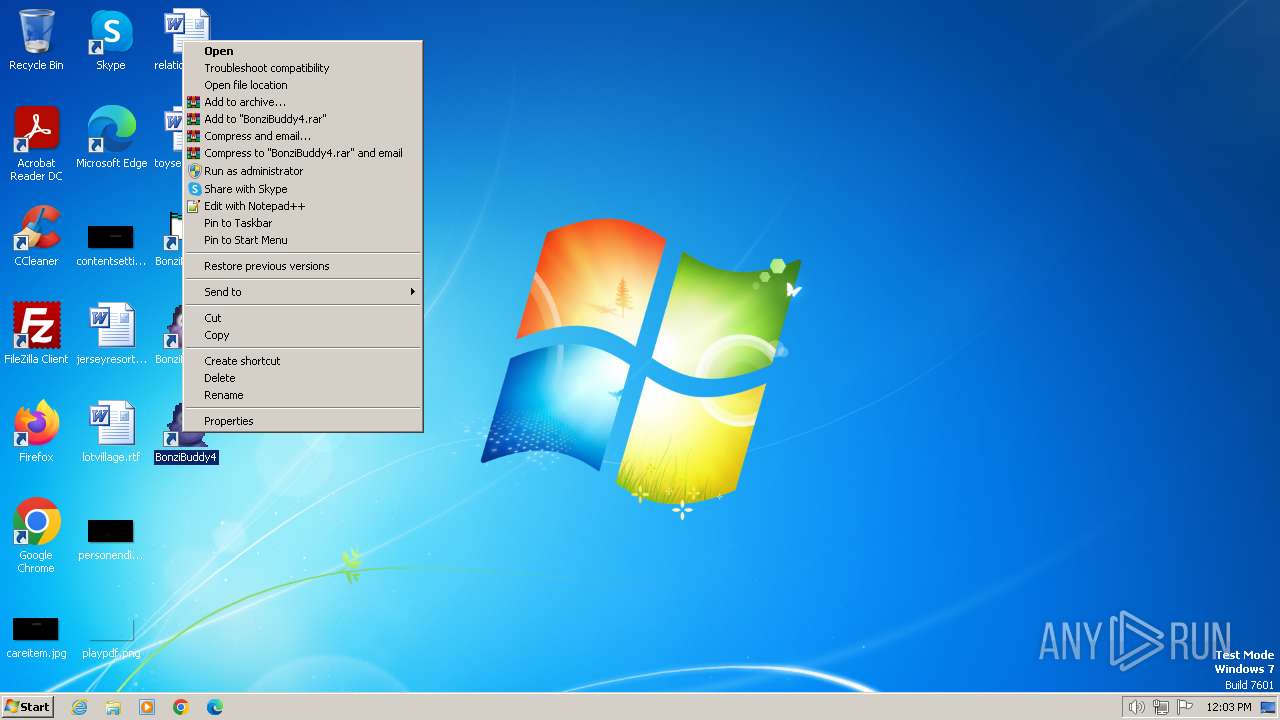
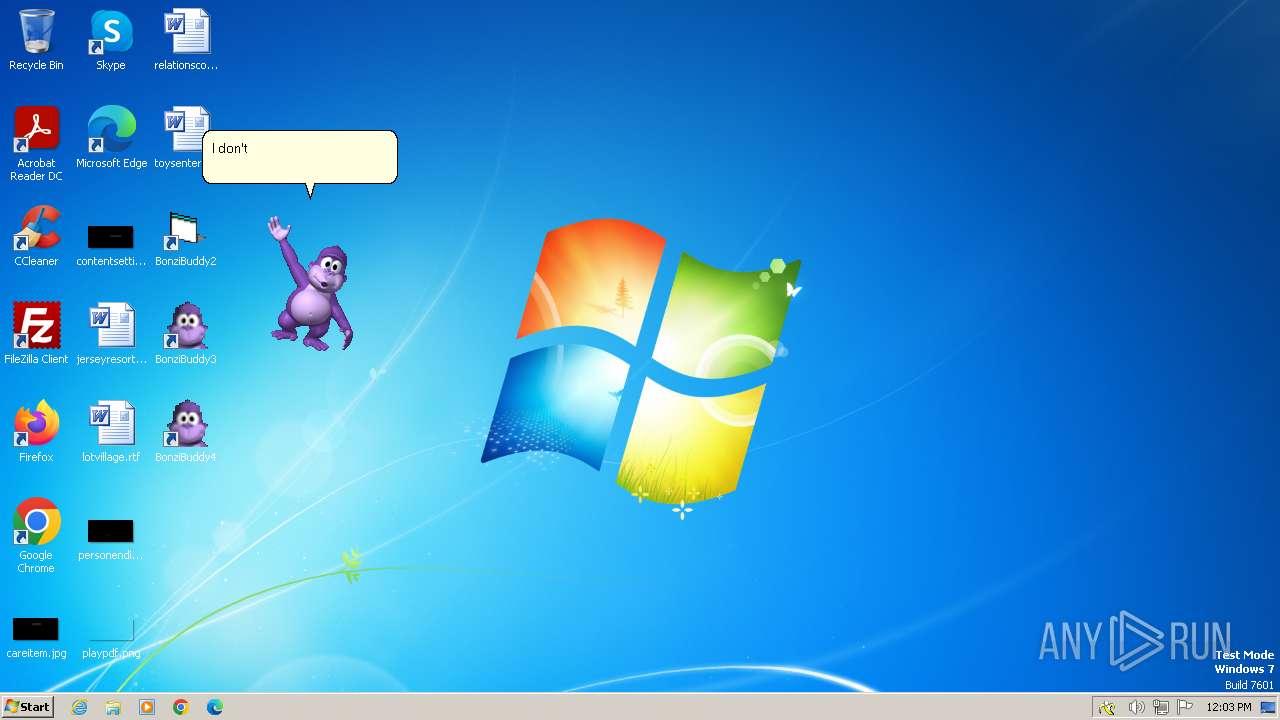
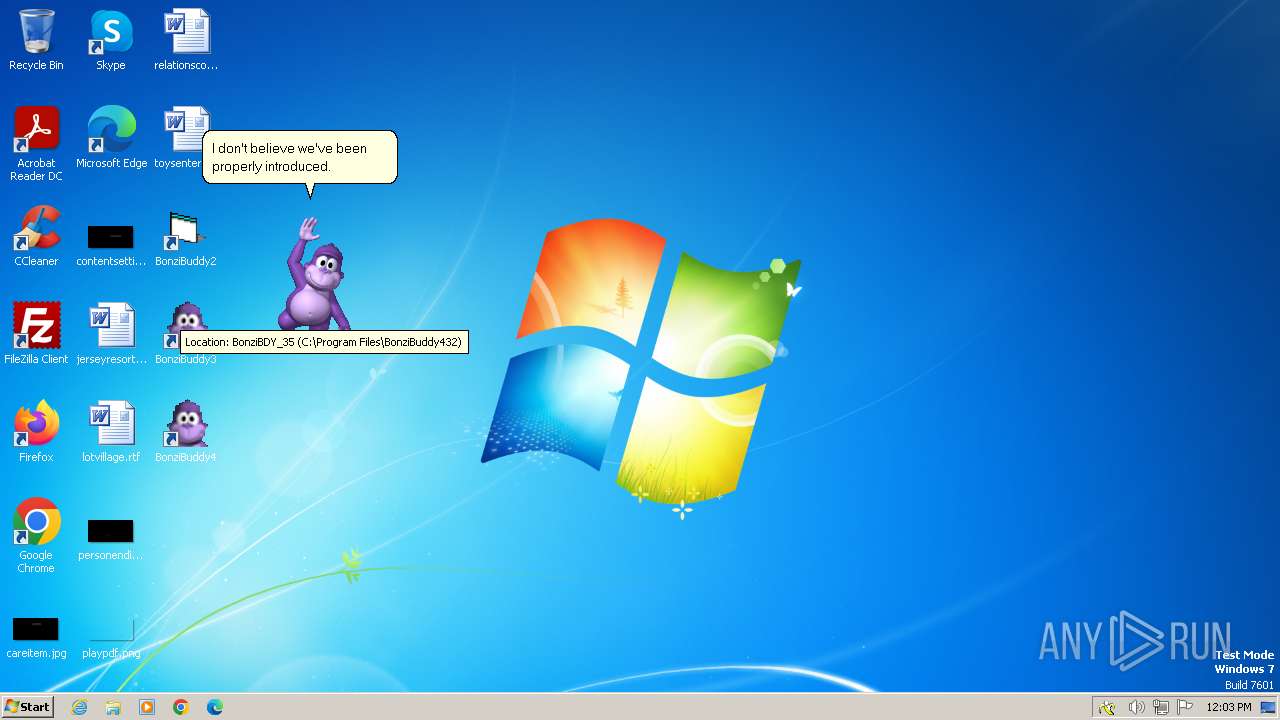
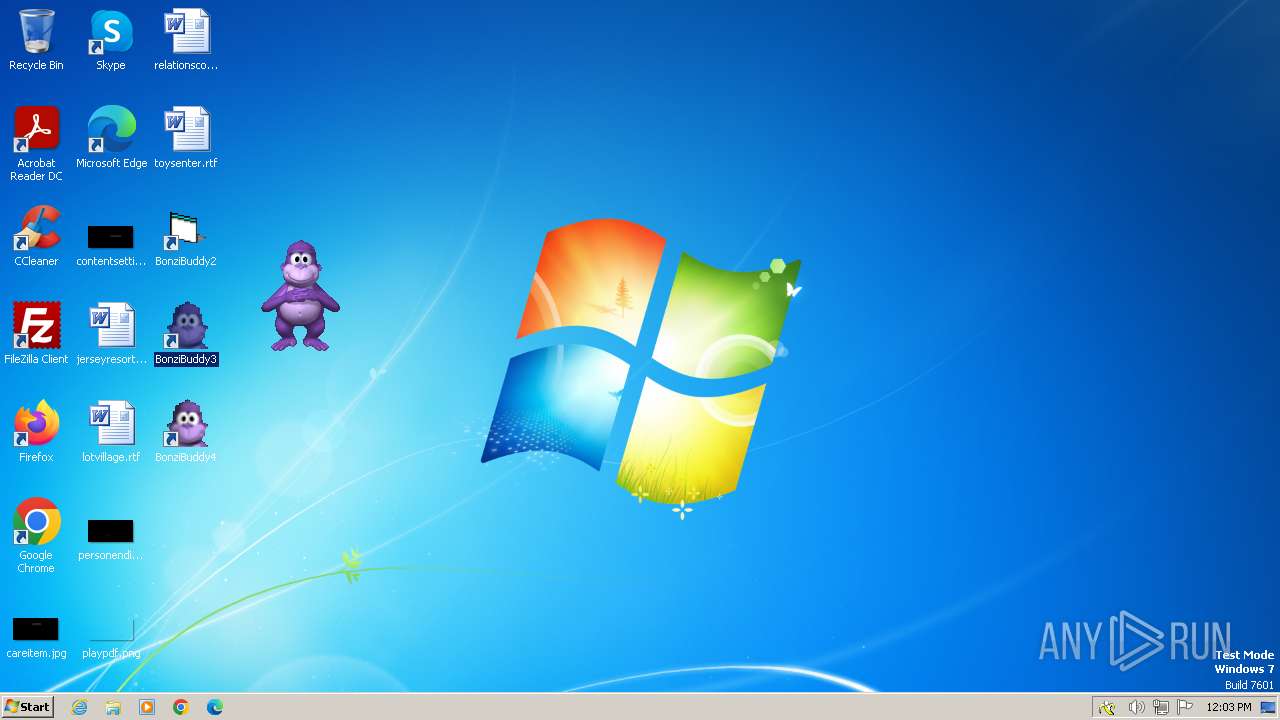
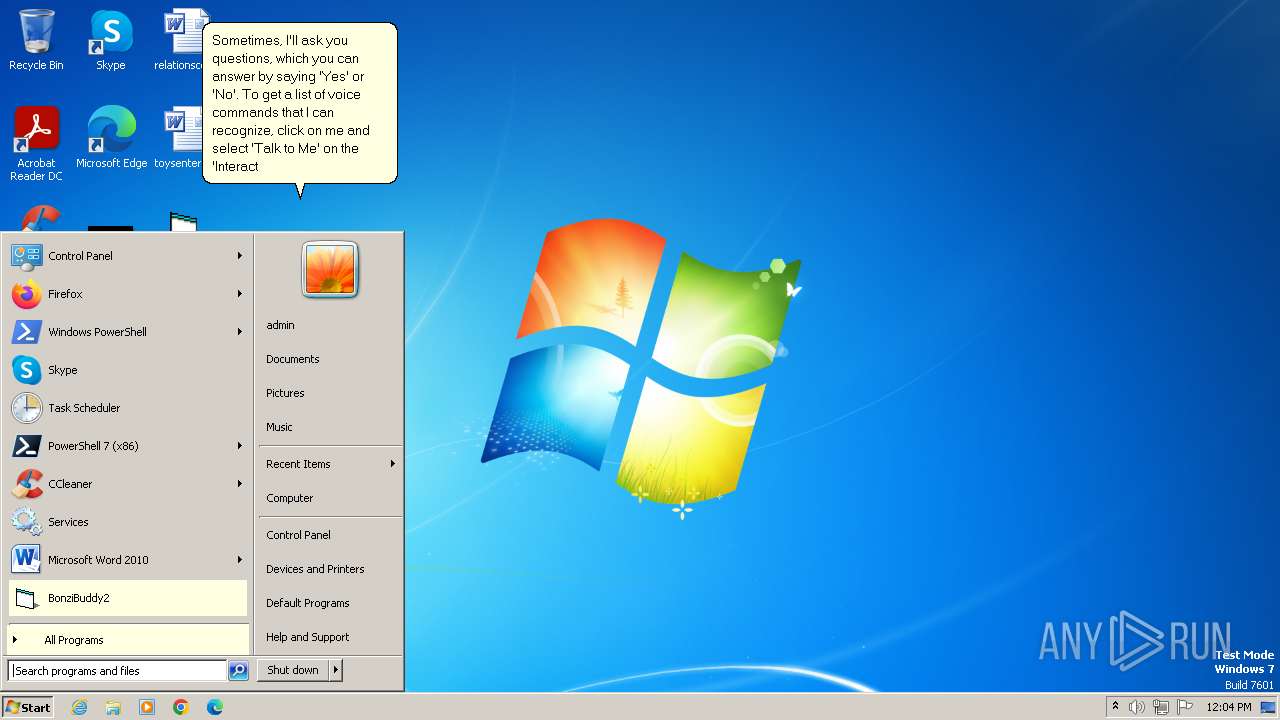
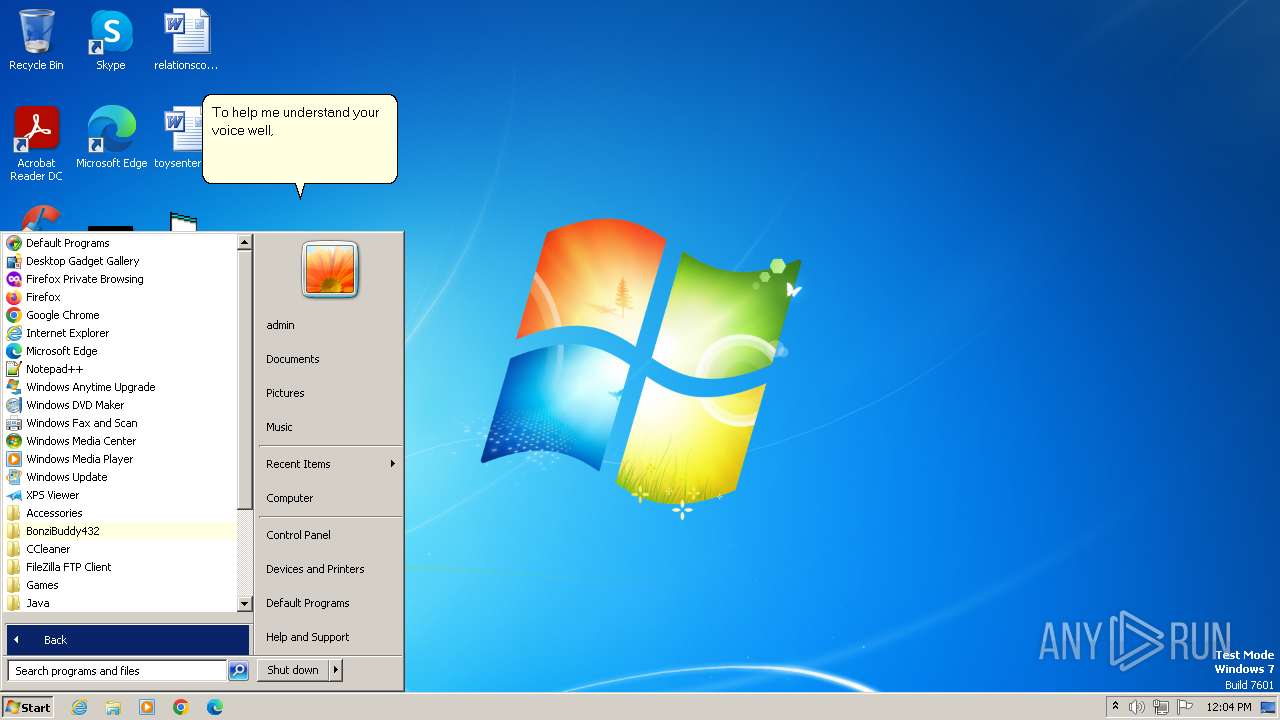
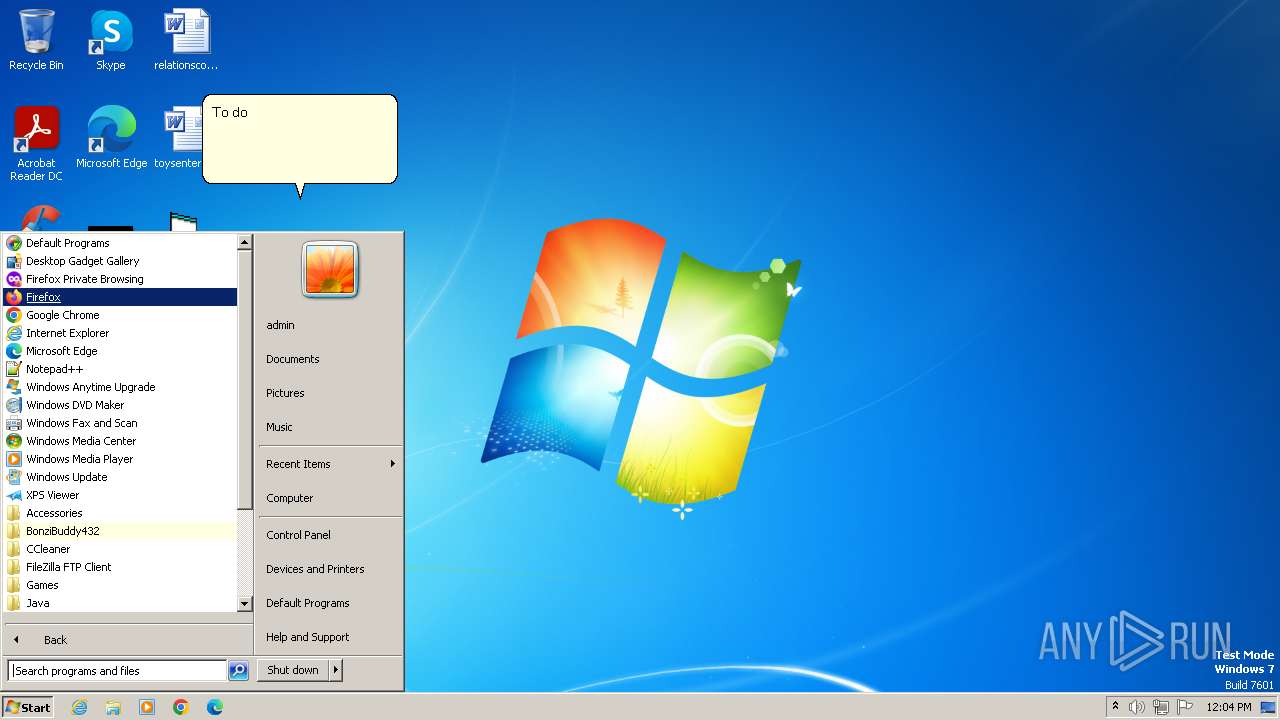
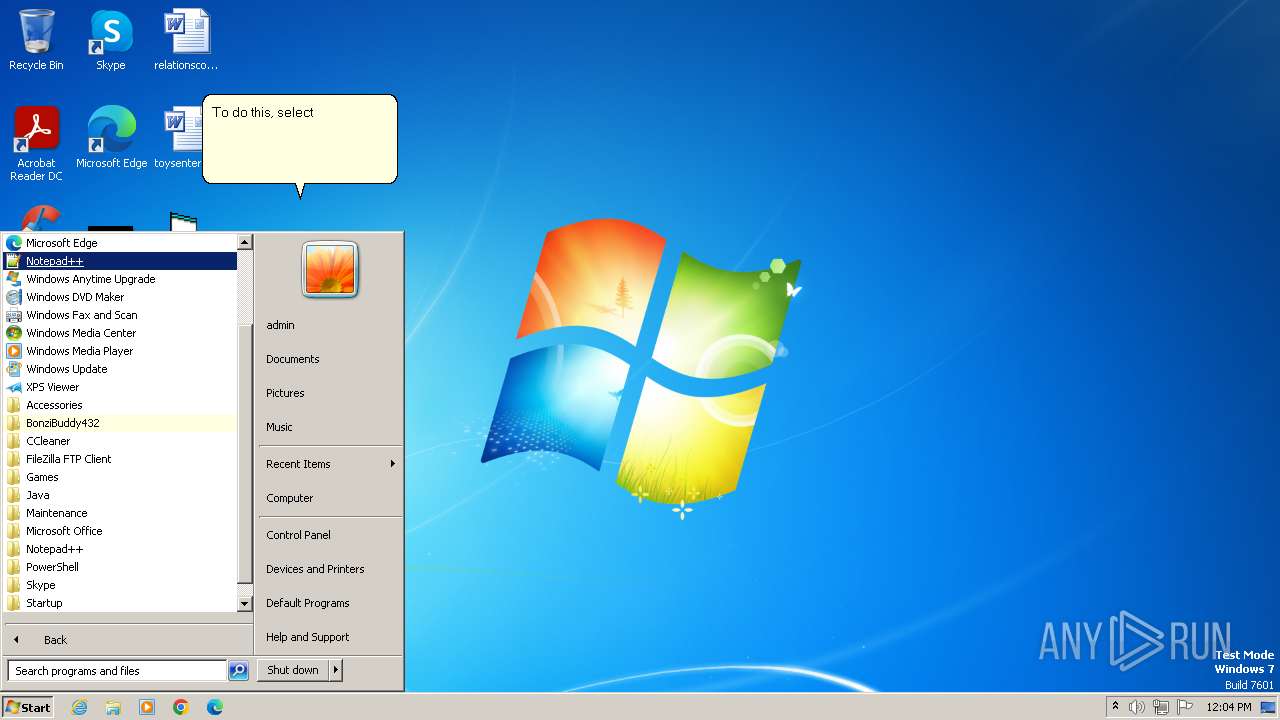
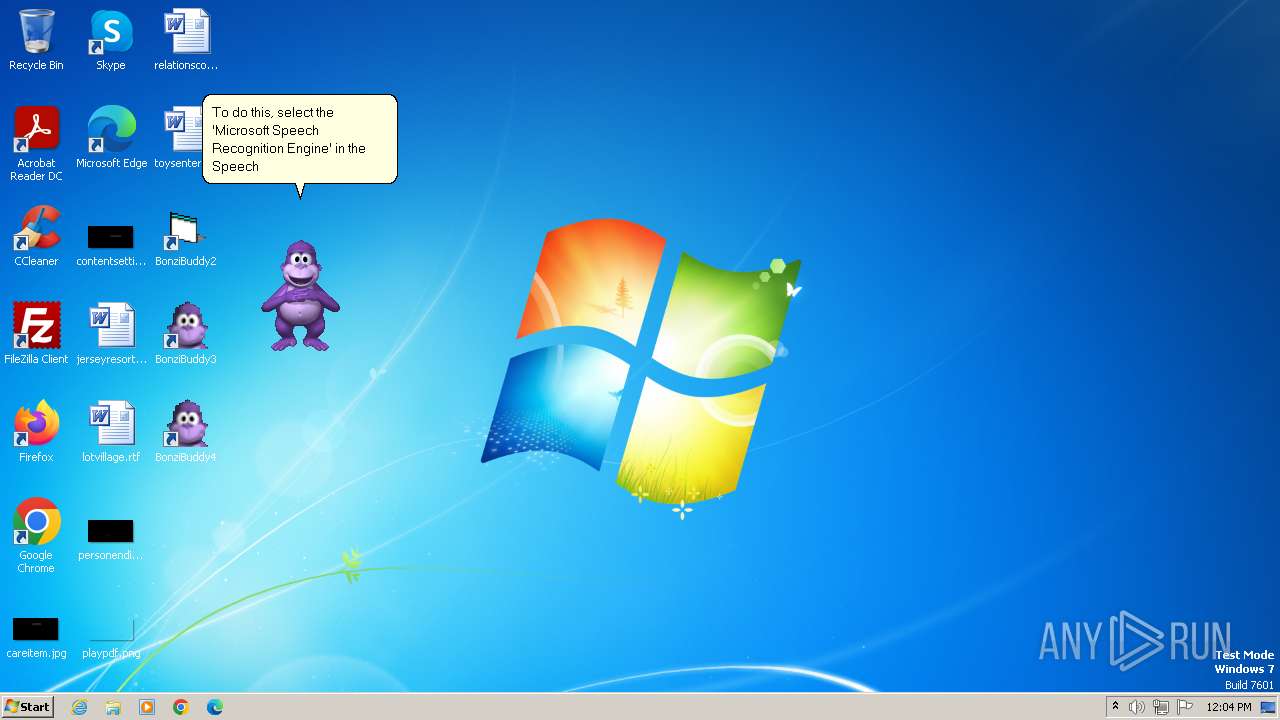
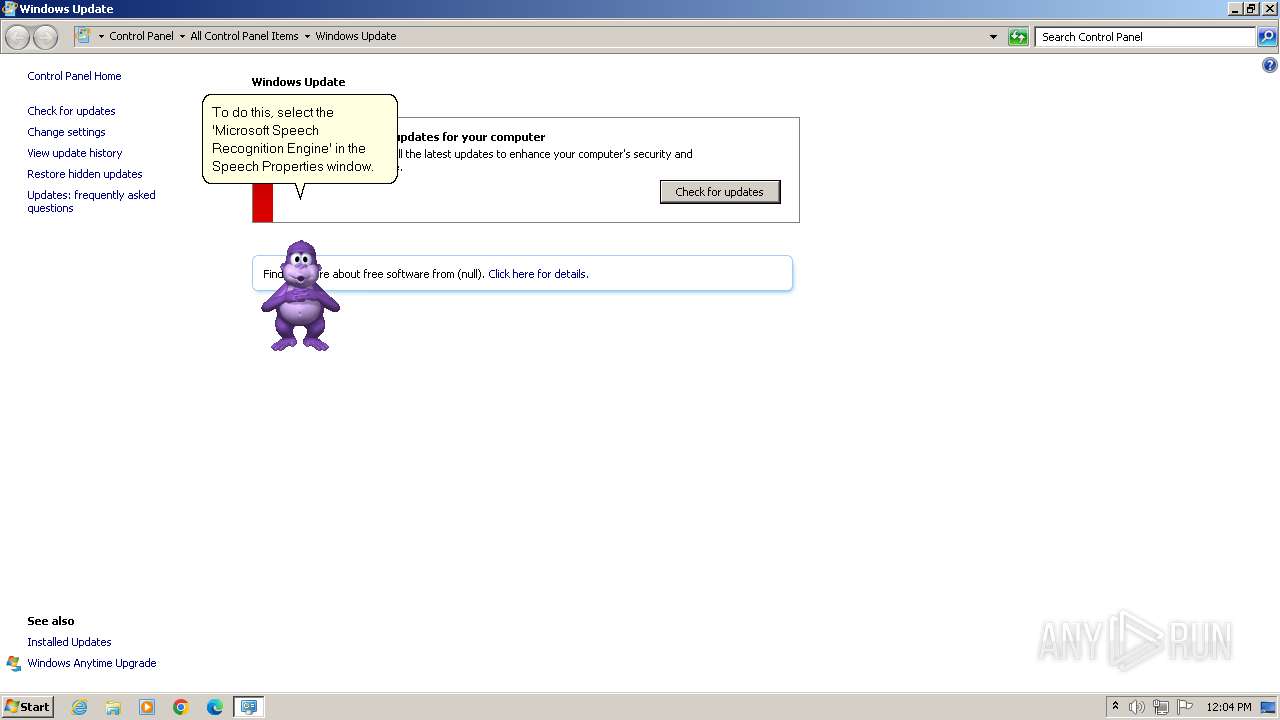
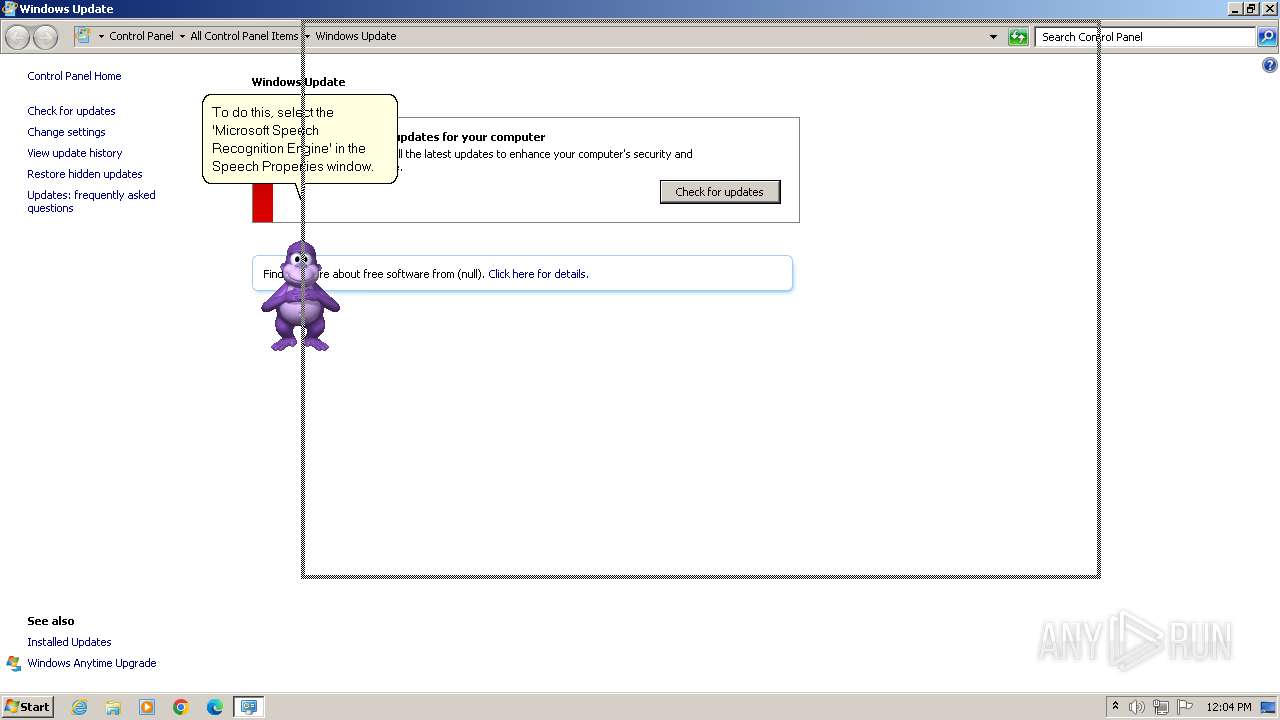
Manual execution by a user
- wmpnscfg.exe (PID: 1624)
- WinRAR.exe (PID: 1592)
- explorer.exe (PID: 1484)
- BonziBuddy432.exe (PID: 3292)
- BonziBuddy432.exe (PID: 1380)
- BonziBuddy432.exe (PID: 1028)
- msedge.exe (PID: 2860)
- BonziBDY_4.EXE (PID: 2760)
- BonziBDY_35.EXE (PID: 1604)
- wuapp.exe (PID: 2324)
- BonziBDY_2.EXE (PID: 2636)
Reads the computer name
- wmpnscfg.exe (PID: 1624)
- BonziBuddy432.exe (PID: 1380)
- BonziBuddy432.exe (PID: 1028)
- tv_enua.exe (PID: 1072)
- BonziBDY_4.EXE (PID: 2760)
- AgentSvr.exe (PID: 1596)
- BonziBDY_35.EXE (PID: 1604)
- BonziBDY_2.EXE (PID: 2636)
- MSAGENT.EXE (PID: 1288)
Checks supported languages
- wmpnscfg.exe (PID: 1624)
- BonziBuddy432.exe (PID: 1380)
- BonziBuddy432.exe (PID: 1028)
- MSAGENT.EXE (PID: 1288)
- tv_enua.exe (PID: 1072)
- AgentSvr.exe (PID: 3968)
- BonziBDY_4.EXE (PID: 2760)
- AgentSvr.exe (PID: 1596)
- BonziBDY_35.EXE (PID: 1604)
- BonziBDY_2.EXE (PID: 2636)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3500)
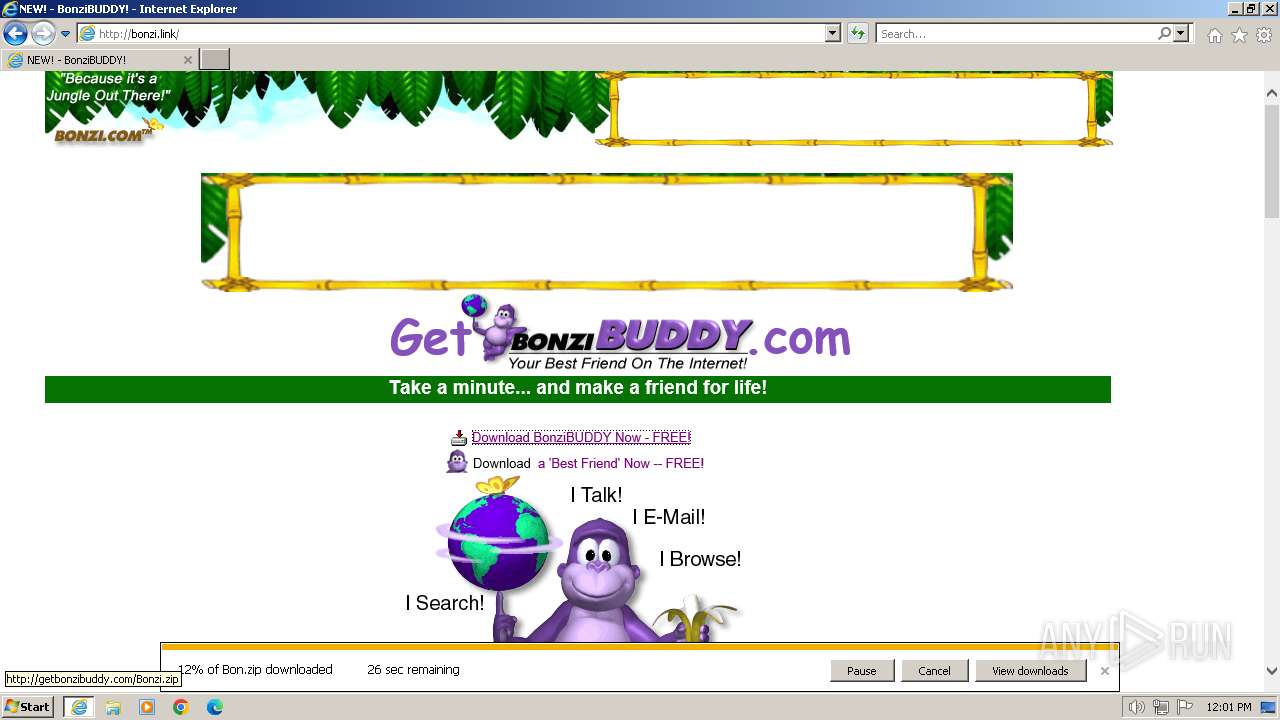
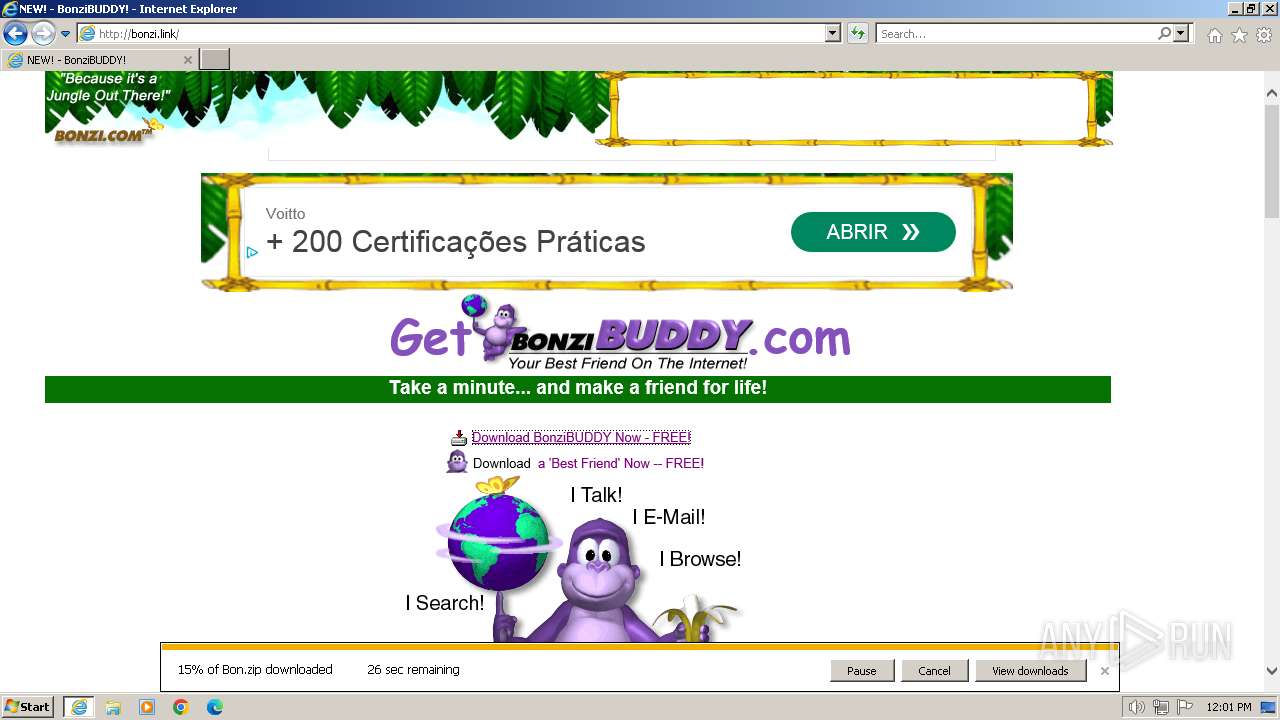
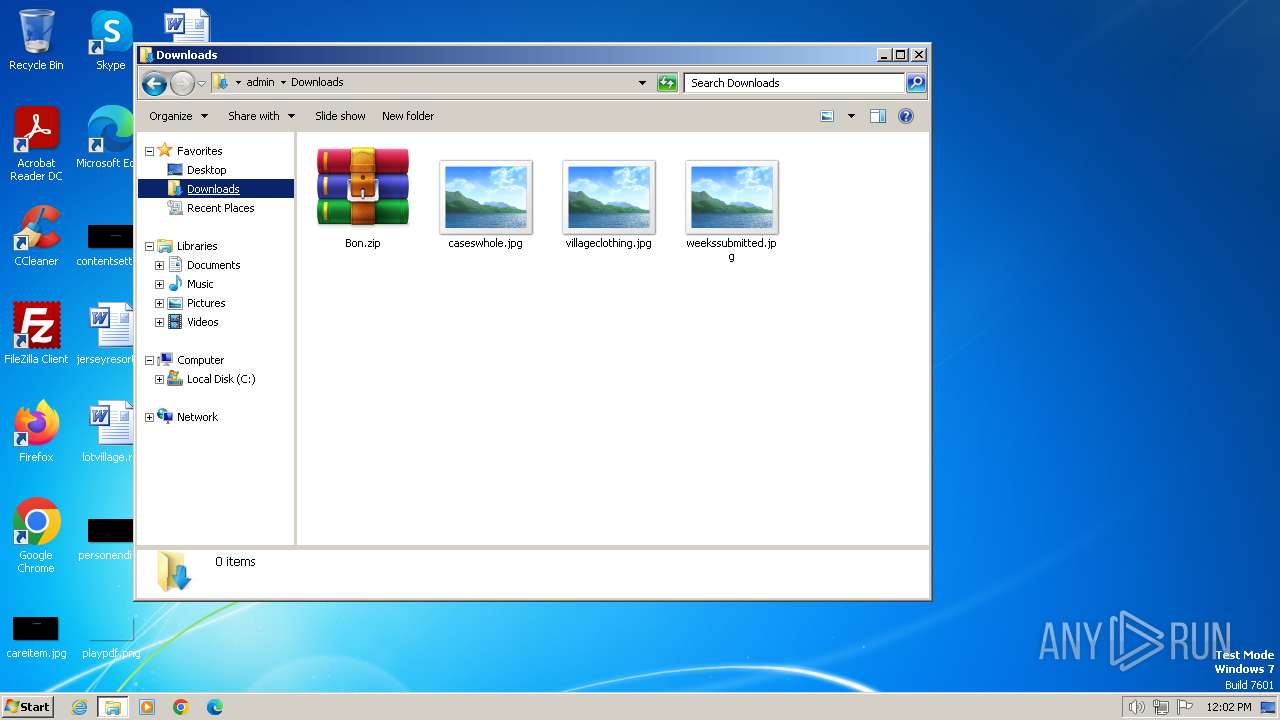
The process uses the downloaded file
- iexplore.exe (PID: 3500)
- WinRAR.exe (PID: 1592)
Create files in a temporary directory
- BonziBuddy432.exe (PID: 1380)
- BonziBuddy432.exe (PID: 1028)
- MSAGENT.EXE (PID: 1288)
- tv_enua.exe (PID: 1072)
- BonziBDY_4.EXE (PID: 2760)
- BonziBDY_35.EXE (PID: 1604)
- BonziBDY_2.EXE (PID: 2636)
Creates files in the program directory
- BonziBuddy432.exe (PID: 1028)
- BonziBDY_35.EXE (PID: 1604)
- BonziBDY_4.EXE (PID: 2760)
Reads mouse settings
- BonziBuddy432.exe (PID: 1028)
- BonziBDY_35.EXE (PID: 1604)
Creates files or folders in the user directory
- BonziBuddy432.exe (PID: 1028)
- BonziBDY_35.EXE (PID: 1604)
Reads the machine GUID from the registry
- BonziBDY_4.EXE (PID: 2760)
- AgentSvr.exe (PID: 1596)
- BonziBDY_35.EXE (PID: 1604)
- BonziBDY_2.EXE (PID: 2636)
Reads Microsoft Office registry keys
- BonziBDY_35.EXE (PID: 1604)
Reads the software policy settings
- BonziBDY_35.EXE (PID: 1604)
Checks proxy server information
- BonziBDY_35.EXE (PID: 1604)
- BonziBDY_4.EXE (PID: 2760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
102
Monitored processes
43
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
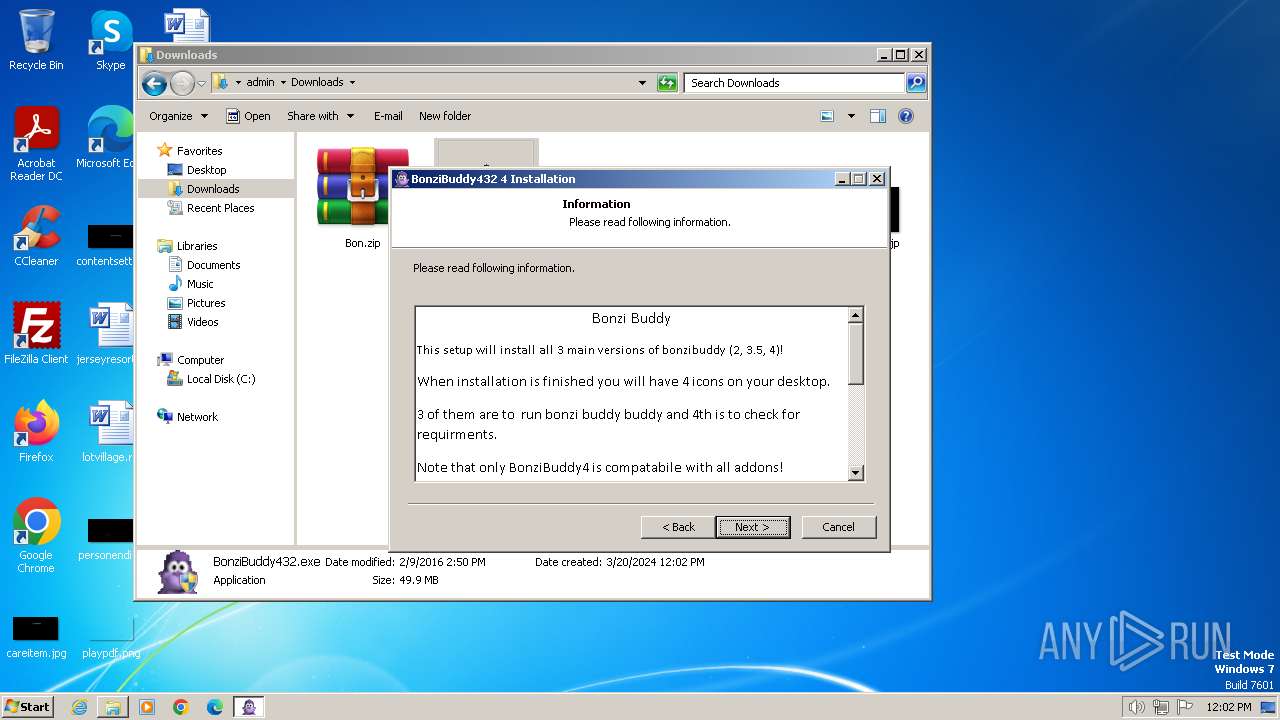
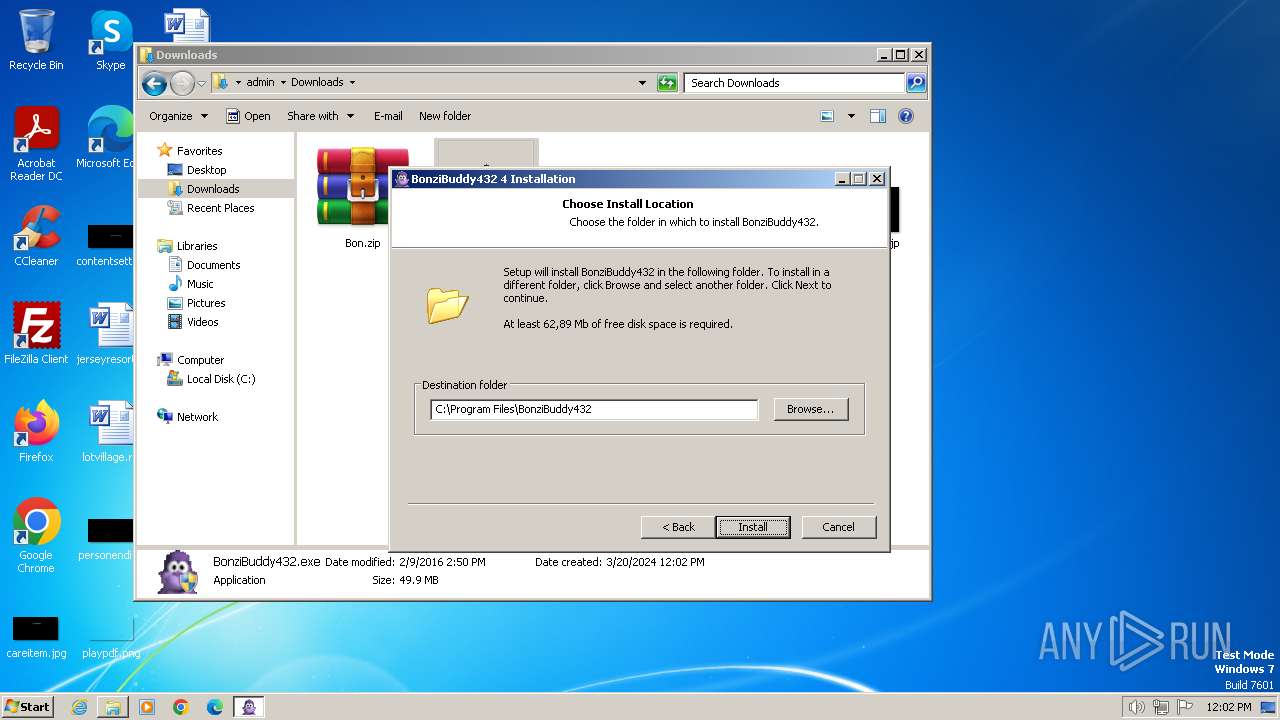
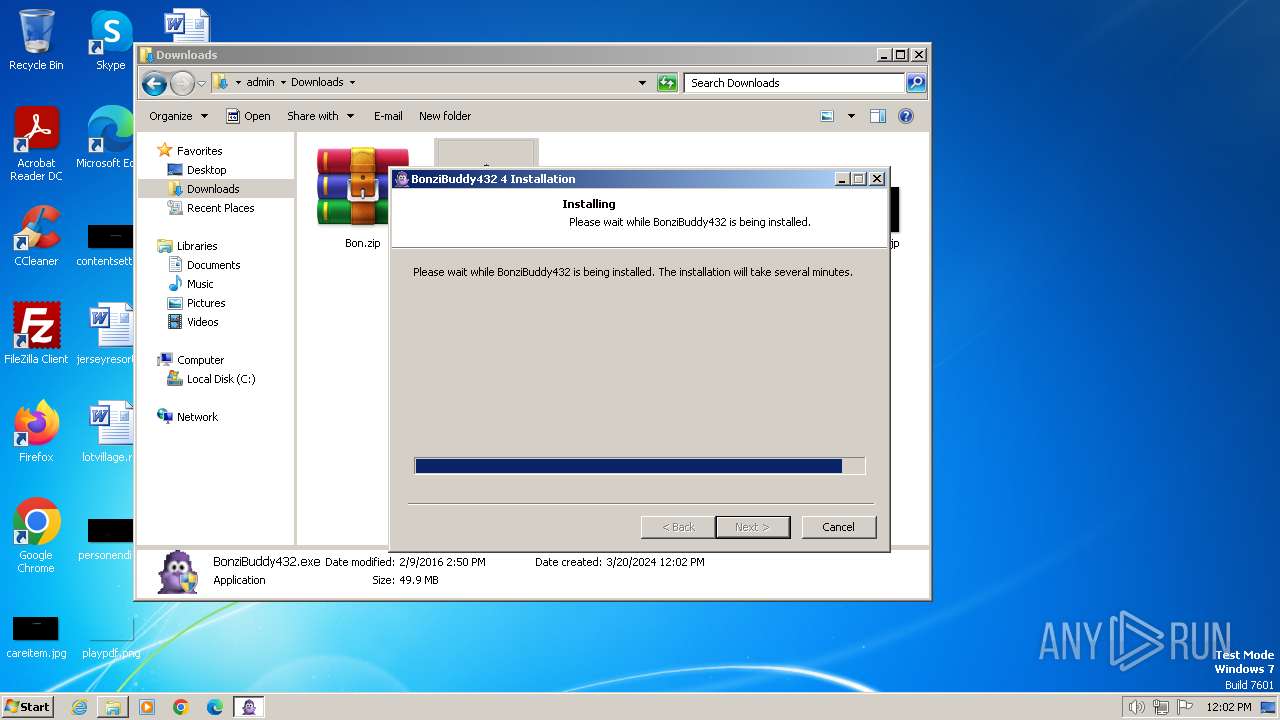
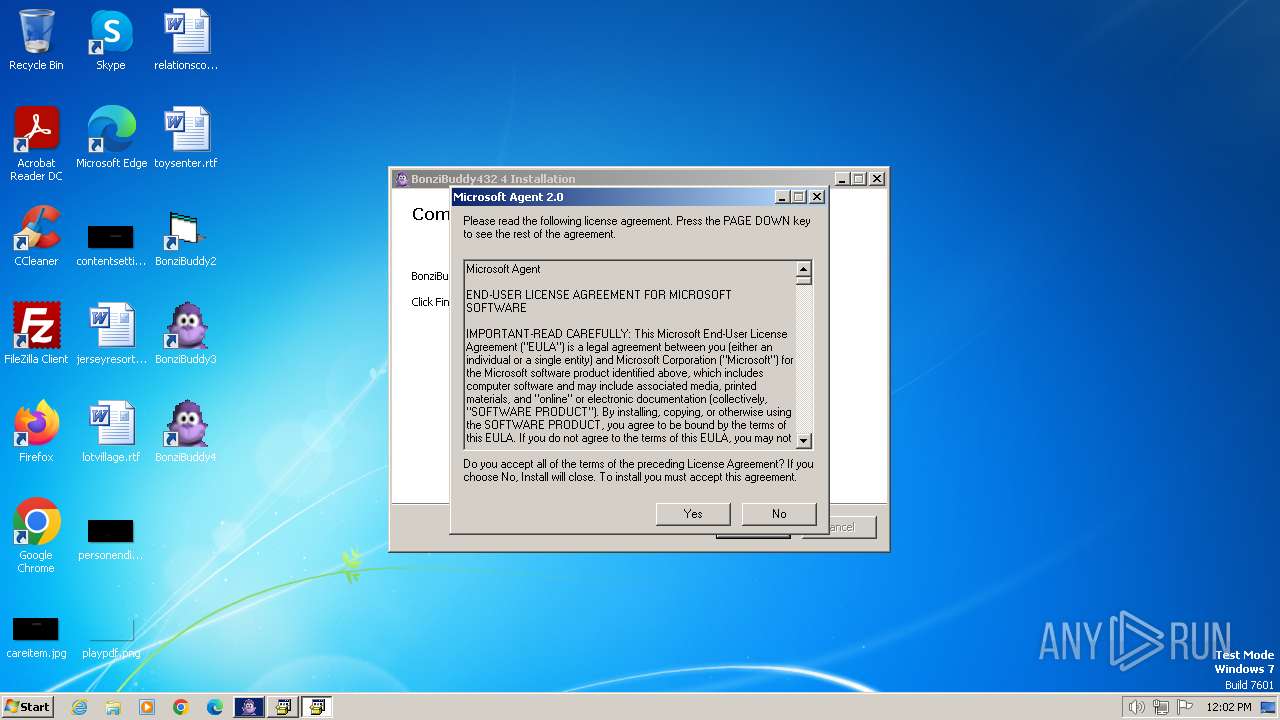
| 1028 | "C:\Users\admin\Downloads\BonziBuddy432.exe" | C:\Users\admin\Downloads\BonziBuddy432.exe | explorer.exe | ||||||||||||
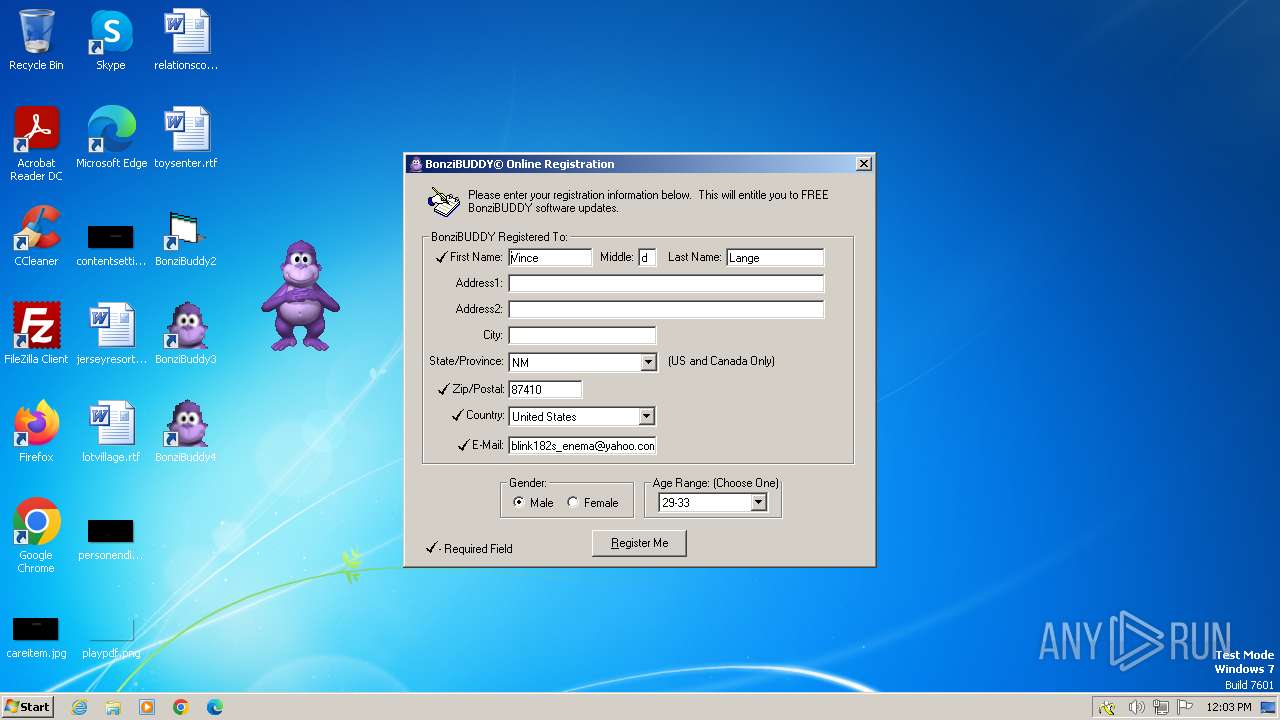
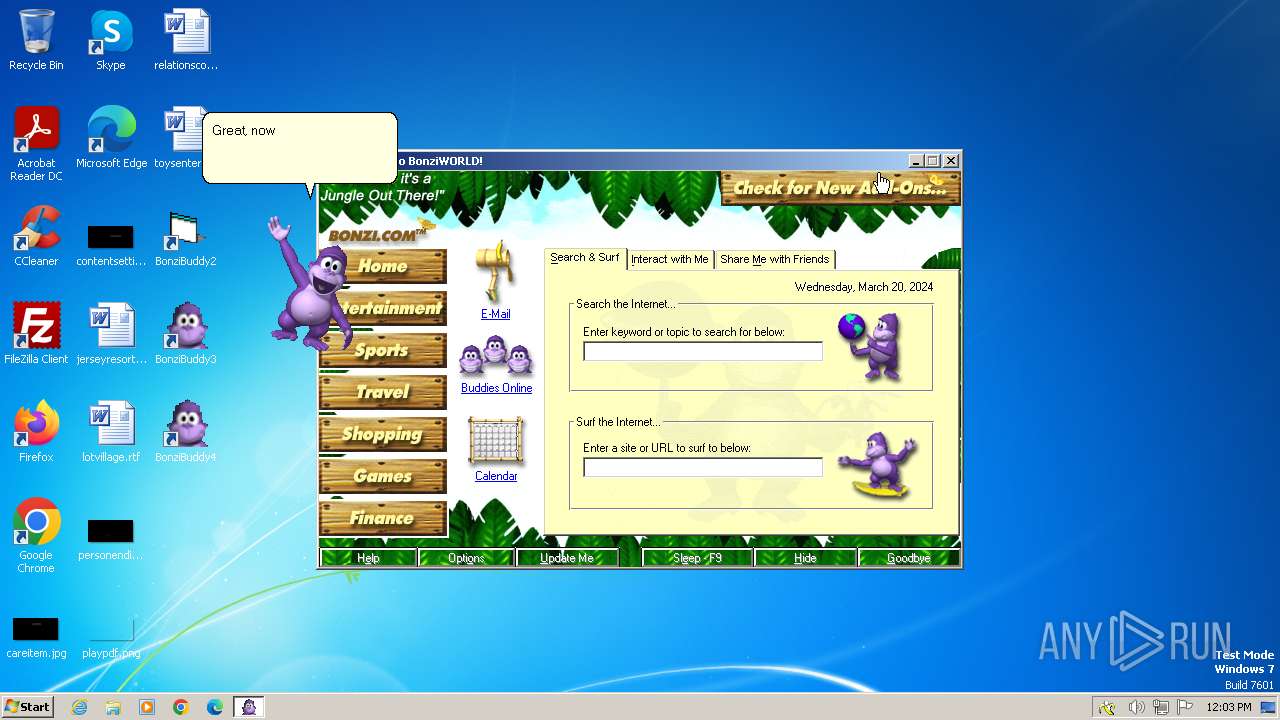
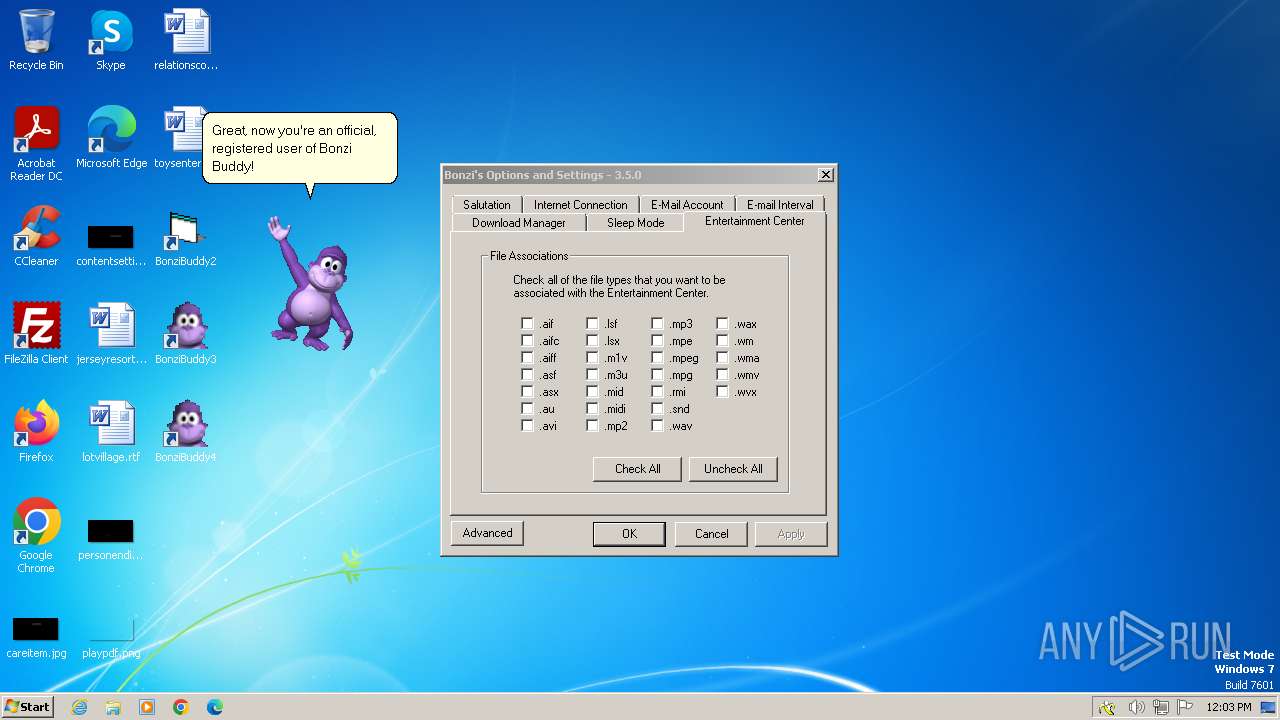
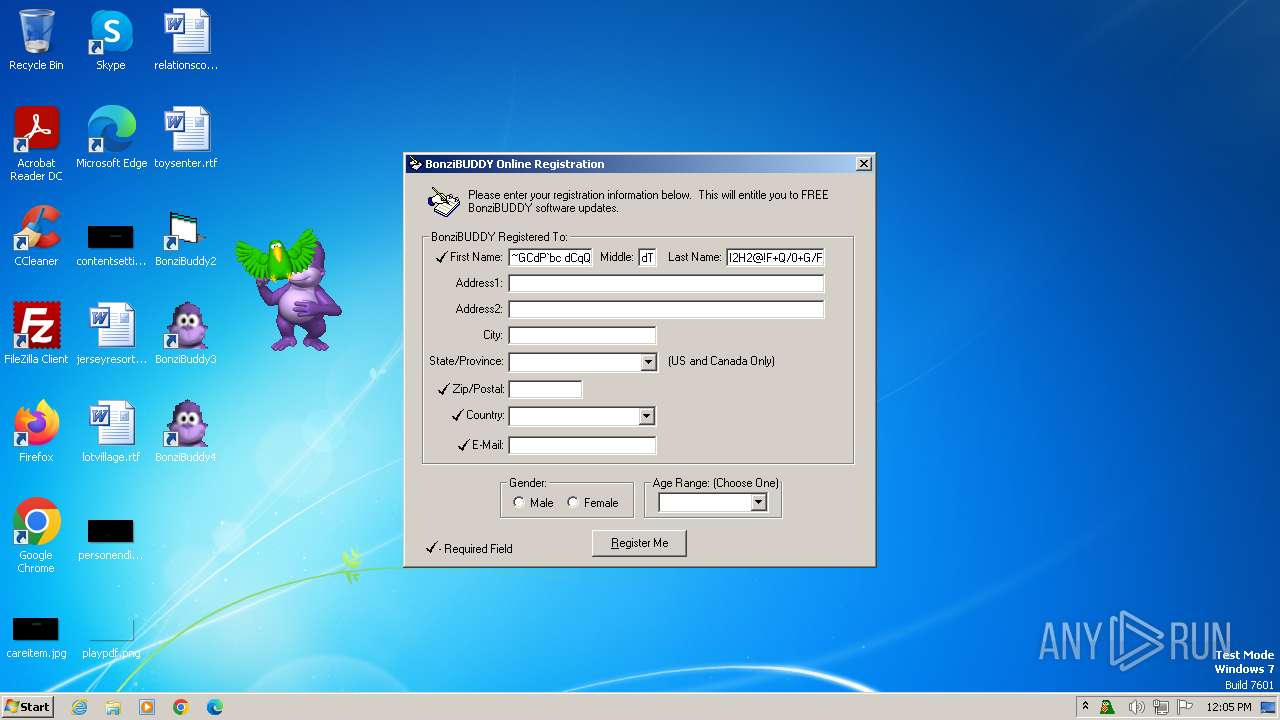
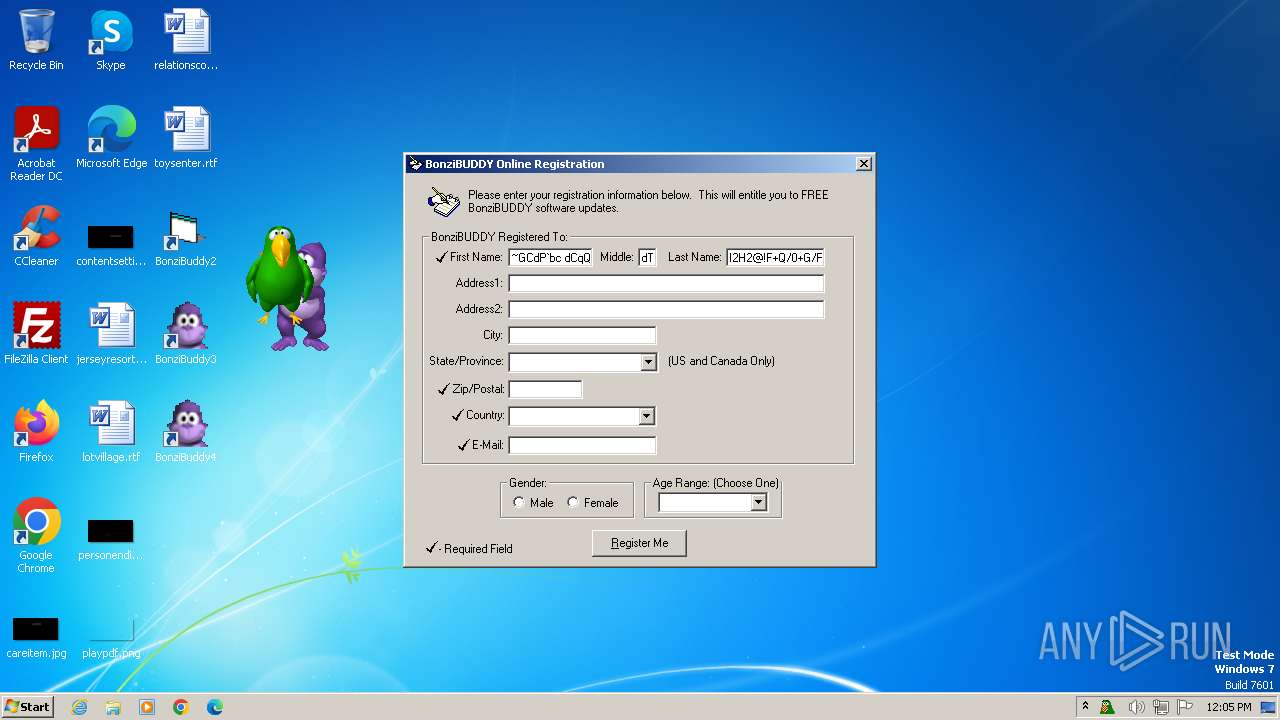
User: admin Company: Bonzi Software Integrity Level: HIGH Description: BonziBuddy432 4 Installation Exit code: 0 Version: 4 Modules
| |||||||||||||||
| 1072 | tv_enua.exe | C:\Program Files\BonziBuddy432\Runtimes\tv_enua.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 4.71.1015.0 Modules
| |||||||||||||||
| 1168 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=3232 --field-trial-handle=1288,i,4511402256110208696,16170208328677655014,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1288 | MSAGENT.EXE | C:\Program Files\BonziBuddy432\Runtimes\MSAGENT.EXE | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 4.71.1015.0 Modules
| |||||||||||||||
| 1380 | "C:\Users\admin\Downloads\BonziBuddy432.exe" | C:\Users\admin\Downloads\BonziBuddy432.exe | explorer.exe | ||||||||||||
User: admin Company: Bonzi Software Integrity Level: HIGH Description: BonziBuddy432 4 Installation Exit code: 0 Version: 4 Modules
| |||||||||||||||
| 1384 | grpconv.exe -o | C:\Windows\System32\grpconv.exe | — | tv_enua.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Progman Group Converter Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1484 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1572 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1572 --field-trial-handle=1288,i,4511402256110208696,16170208328677655014,131072 /prefetch:3 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1592 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\Bon.zip" C:\Users\admin\Downloads\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1596 | C:\Windows\msagent\AgentSvr.exe -Embedding | C:\Windows\msagent\AgentSvr.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Agent Server Exit code: 0 Version: 2.00.0.2202 Modules
| |||||||||||||||
Total events
52 426
Read events
51 387
Write events
786
Delete events
253
Modification events
| (PID) Process: | (3500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31095486 | |||
| (PID) Process: | (3500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31095486 | |||
| (PID) Process: | (3500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
84
Suspicious files
125
Text files
423
Unknown types
79
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3500 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:32418AAD6A59377813B0DCA5B0B79EDB | SHA256:D9E699252C740D93344BCC332D739B13FB6B5261F3430ACB75D5E19ED7638D06 | |||
| 3500 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | binary | |
MD5:1E1162F2EF525E8B39D679CA593AE98A | SHA256:55F86AF2E11CE31FEE5F700C0A1205E72E554D08E480C9B40BF49CF48F5F1479 | |||
| 3500 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:89D0A0B14D9B578C4AF0F6B364F7844A | SHA256:D2C595EC72E0173470B3E0D0335C4A165FD5C8253B365B71A3B11B924A3A9FD6 | |||
| 2232 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\80237EE4964FC9C409AAF55BF996A292_C0427F5F77D9B3A439FC620EDAAB6177 | binary | |
MD5:823CA70D3B2303DE0887061D6FADFC5A | SHA256:9D31CAEB6C493ED2459DE54554CDF3E871C61D5C9E698B6DFABD78BE8DA3F18D | |||
| 3500 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | binary | |
MD5:7D1B274938774F9A8E6B3191740FD1DB | SHA256:CA6F02E76DB21050C0FF5C41C07C7DA9CECE660259E907205E4F17A2BA7E9401 | |||
| 2232 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\80237EE4964FC9C409AAF55BF996A292_C0427F5F77D9B3A439FC620EDAAB6177 | binary | |
MD5:BD9C66DE2211B54E403119C37352906F | SHA256:7732683E15DF321528E9BD1A54A0C1A2D65A2EA350BADFD11BD2EFA0B6E5B690 | |||
| 2232 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\BHEU5Y8V.txt | text | |
MD5:F1242F5080428BCD24AEA50B272731EF | SHA256:A9BDD672DD0E708F6087FE435C4665F12060327BB7233B77AF41CB5137667CD7 | |||
| 2232 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\375RQGMT.txt | text | |
MD5:6A29617BAB20ABB8FB03A0315A6CD561 | SHA256:B7E17C8B71F20F1AF67DF8E348865633A57070ECE7DCD11CE95A02C2487C3BD6 | |||
| 2232 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\XTH45033.txt | text | |
MD5:7070BB35445534F625C15965E9C28DD2 | SHA256:C0EB4DE9571E1C43FD32148EA489B621671AB0DC85490123458C3578313D43BD | |||
| 2232 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\EVWBIM0L.txt | text | |
MD5:E55F323EED71AF3DBA995DDE3D191A42 | SHA256:466BCB49D2118081BF56CB5C4DBC533EC847B211A4811979551E6CB190ED21CF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
222
TCP/UDP connections
156
DNS requests
64
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3500 | iexplore.exe | GET | 304 | 62.115.252.232:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?76ad697231f9b13b | ES | — | — | unknown |
3500 | iexplore.exe | GET | 304 | 62.115.252.160:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?96c8eb5dfc595a04 | ES | — | — | unknown |
3500 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | US | binary | 314 b | unknown |
2232 | iexplore.exe | GET | 200 | 151.106.4.82:80 | http://bonzi.link/images/bbabilities2.gif | FR | image | 24.8 Kb | unknown |
2232 | iexplore.exe | GET | 200 | 151.106.4.82:80 | http://bonzi.link/images/download.gif | FR | image | 151 b | unknown |
2232 | iexplore.exe | GET | 200 | 151.106.4.82:80 | http://bonzi.link/images/bbvine.gif | FR | image | 4.59 Kb | unknown |
2232 | iexplore.exe | GET | 200 | 151.106.4.82:80 | http://bonzi.link/images/sepbar.jpg | FR | image | 1.05 Kb | unknown |
2232 | iexplore.exe | GET | 200 | 151.106.4.82:80 | http://bonzi.link/images/meetyou.jpg | FR | image | 39.2 Kb | unknown |
2232 | iexplore.exe | GET | 200 | 151.106.4.82:80 | http://bonzi.link/images/bbmail.gif | FR | image | 23.0 Kb | unknown |
2232 | iexplore.exe | GET | 200 | 151.106.4.82:80 | http://bonzi.link/images/bbsearch.gif | FR | image | 2.78 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2232 | iexplore.exe | 151.106.4.82:443 | bonzi.link | Host Europe GmbH | FR | unknown |
3500 | iexplore.exe | 62.115.252.67:443 | www.bing.com | Telia Company AB | ES | unknown |
3500 | iexplore.exe | 62.115.252.232:80 | ctldl.windowsupdate.com | Telia Company AB | ES | unknown |
3500 | iexplore.exe | 62.115.252.160:80 | ctldl.windowsupdate.com | Telia Company AB | ES | unknown |
3500 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2232 | iexplore.exe | 13.107.5.80:443 | api.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2232 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bonzi.link |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
d36ee2fcip1434.cloudfront.net |
| unknown |
ocsp.pki.goog |
| whitelisted |
fundingchoicesmessages.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
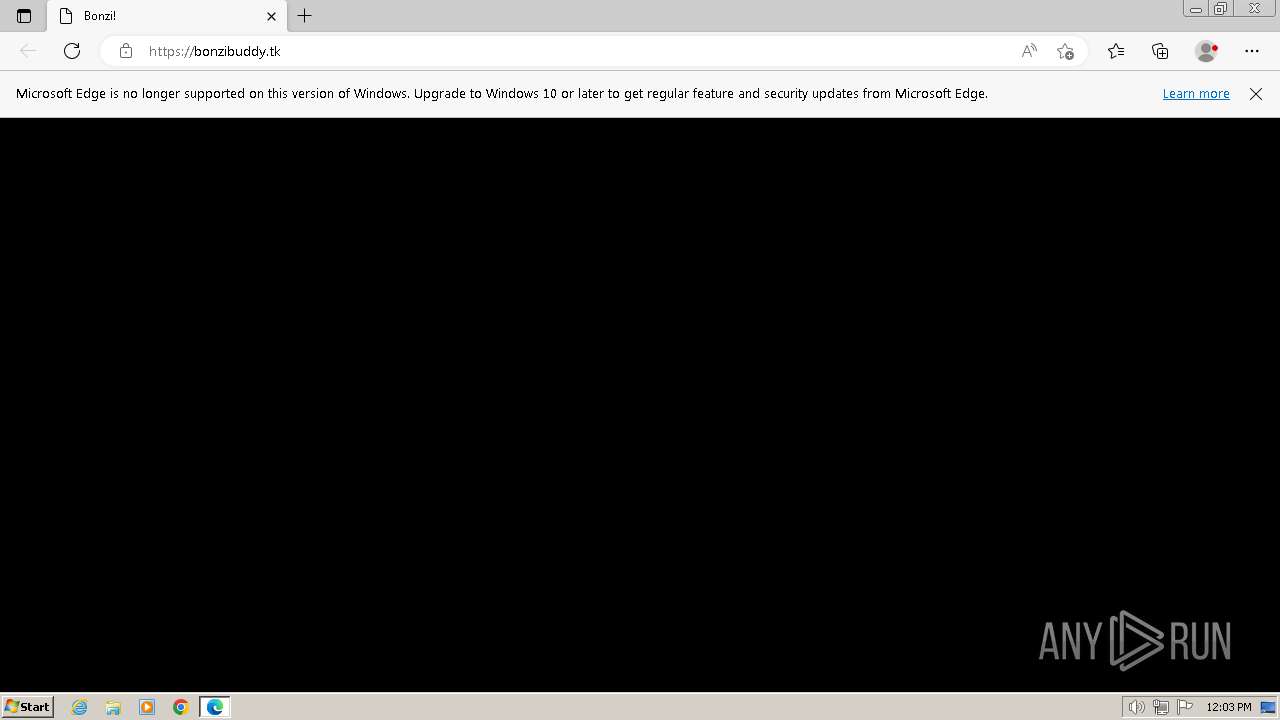
Threats
PID | Process | Class | Message |
|---|---|---|---|
1572 | msedge.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
1572 | msedge.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
1572 | msedge.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
1572 | msedge.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
1572 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code.jquery .com) |
1572 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
Process | Message |
|---|---|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|