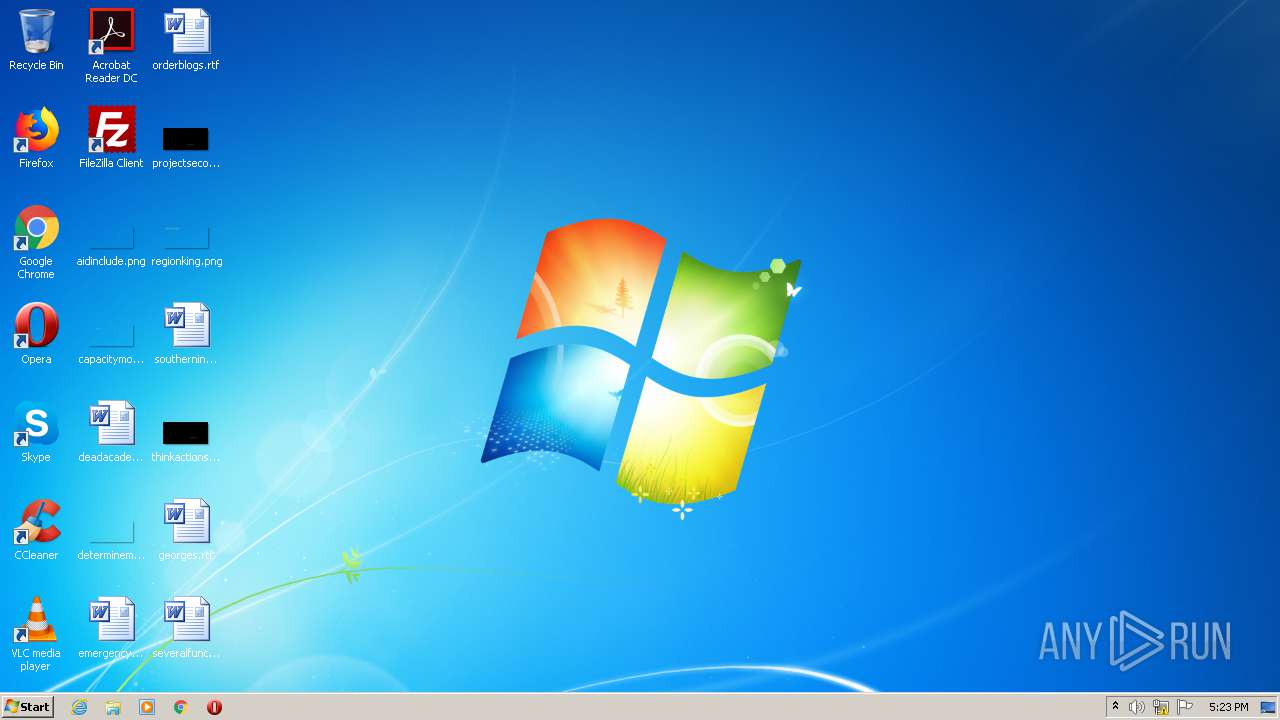
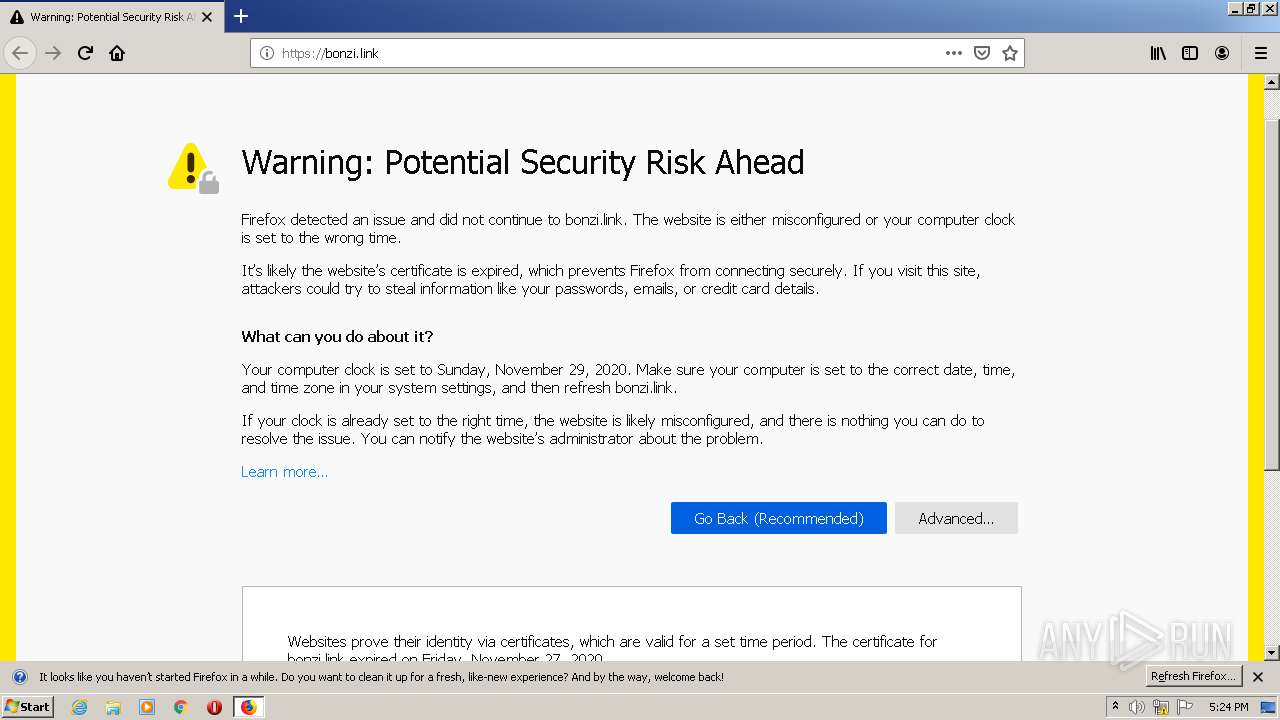
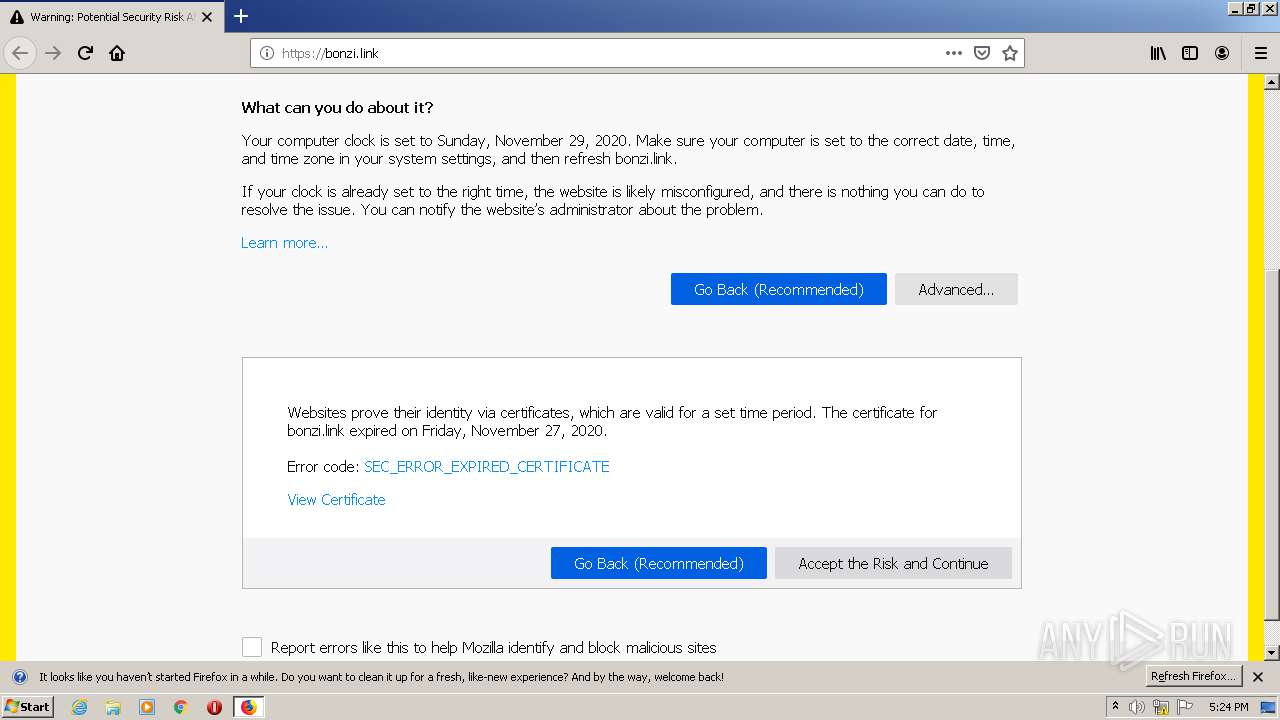
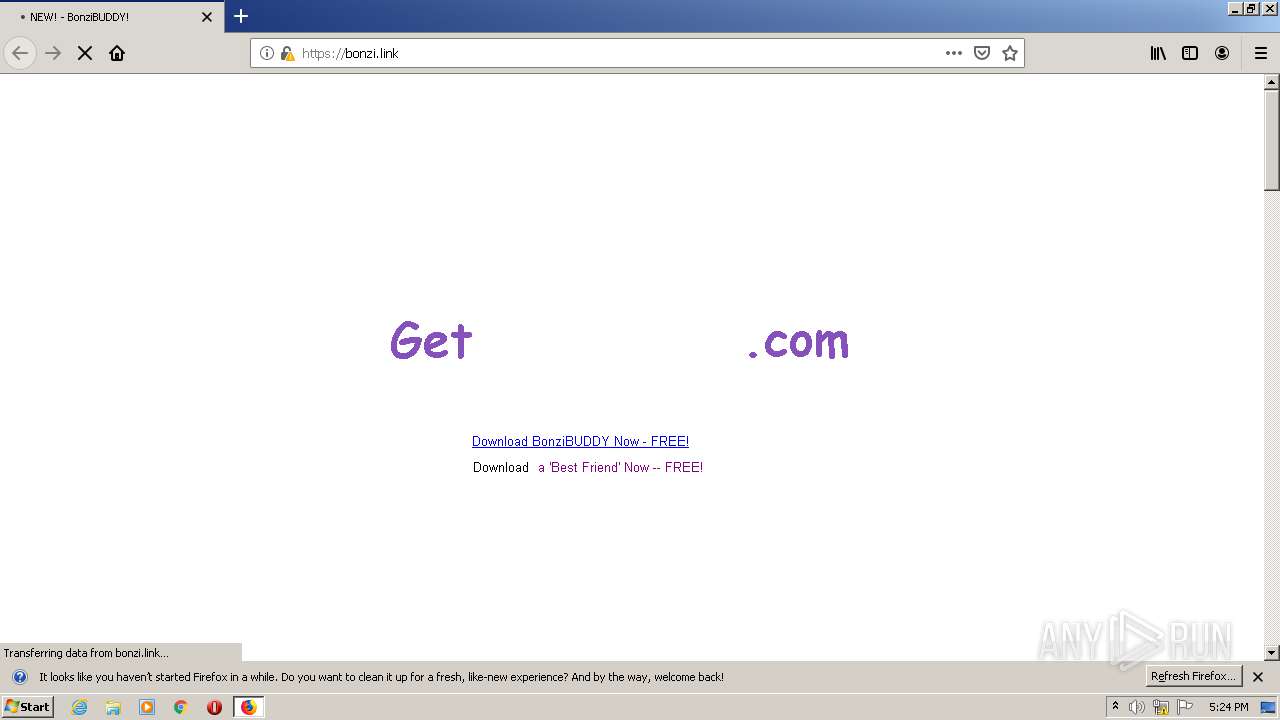
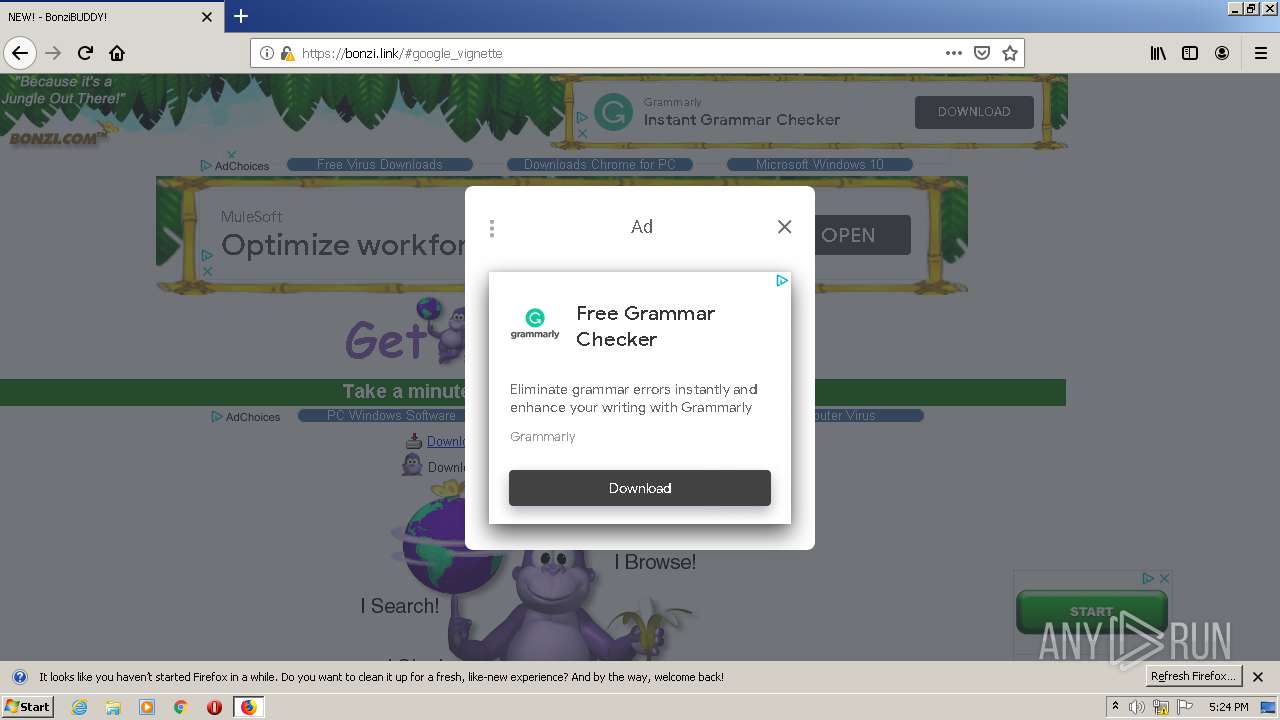
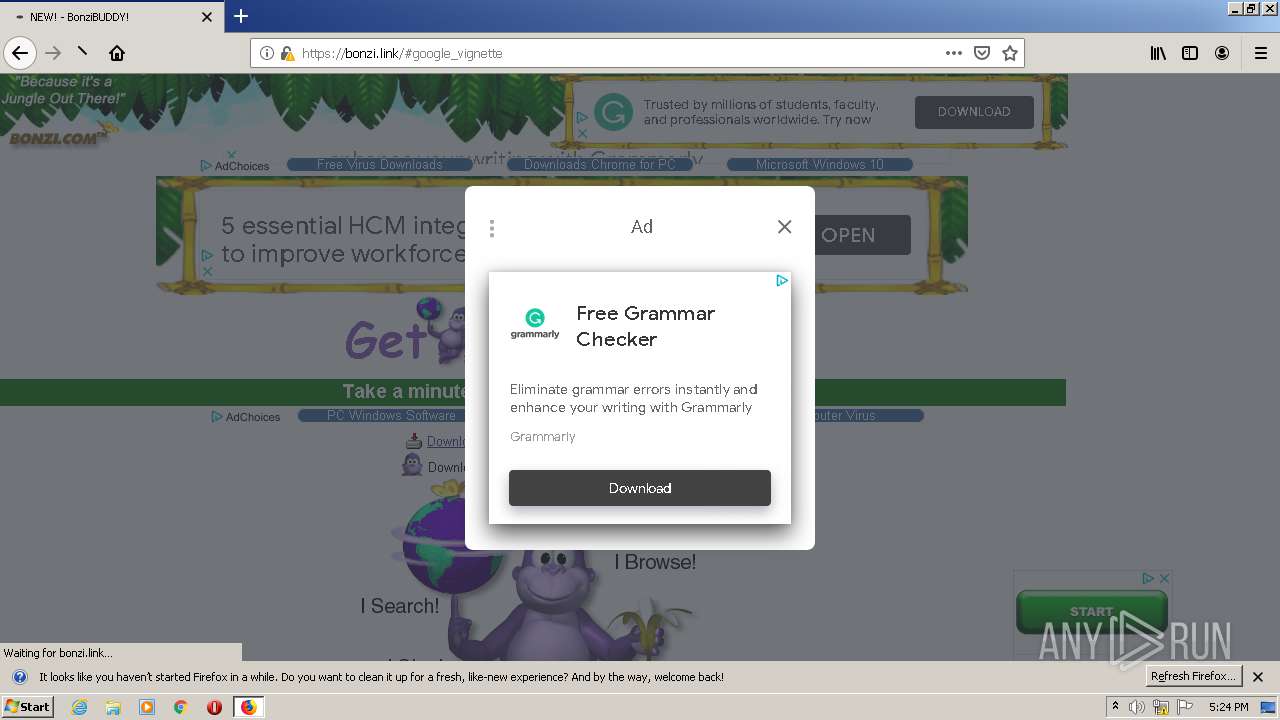
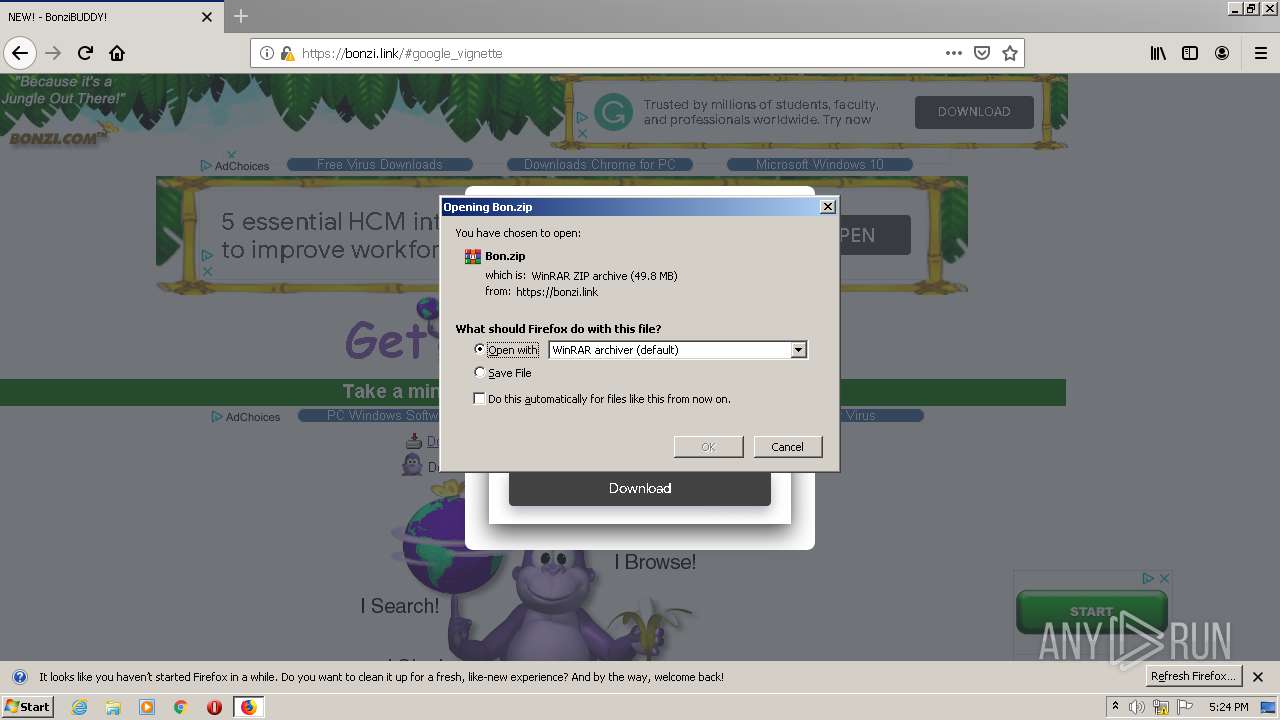
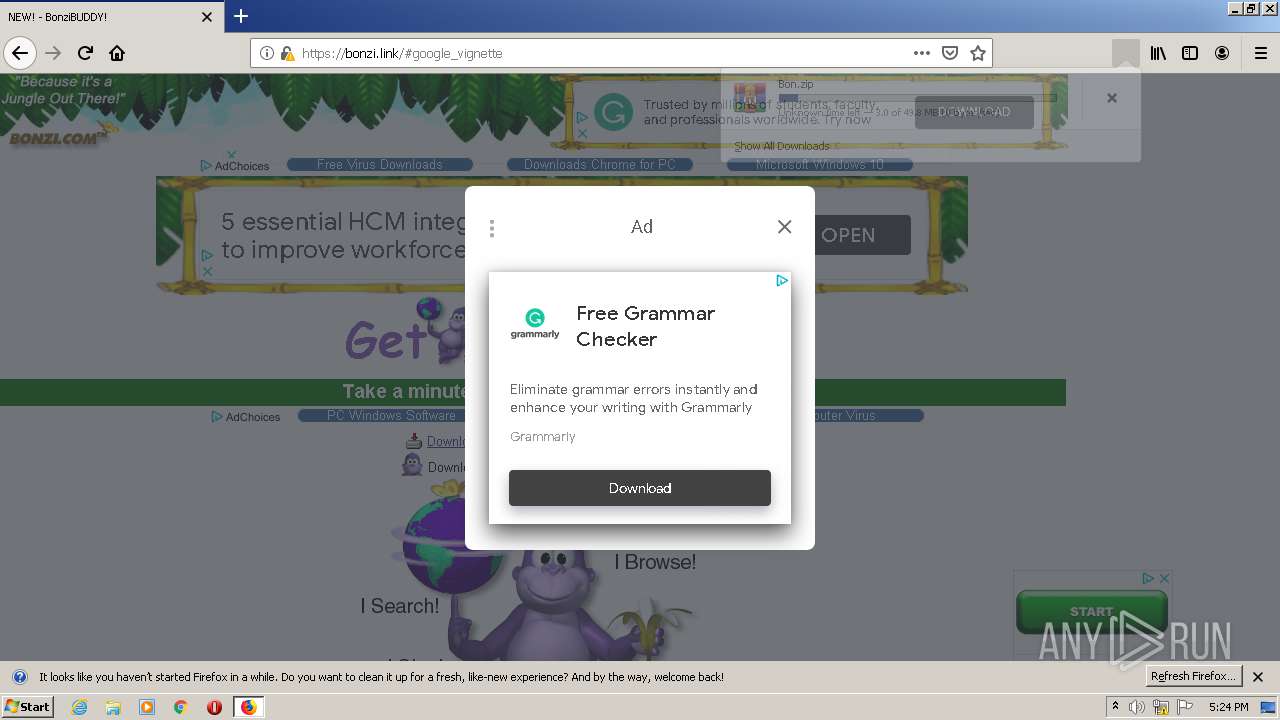
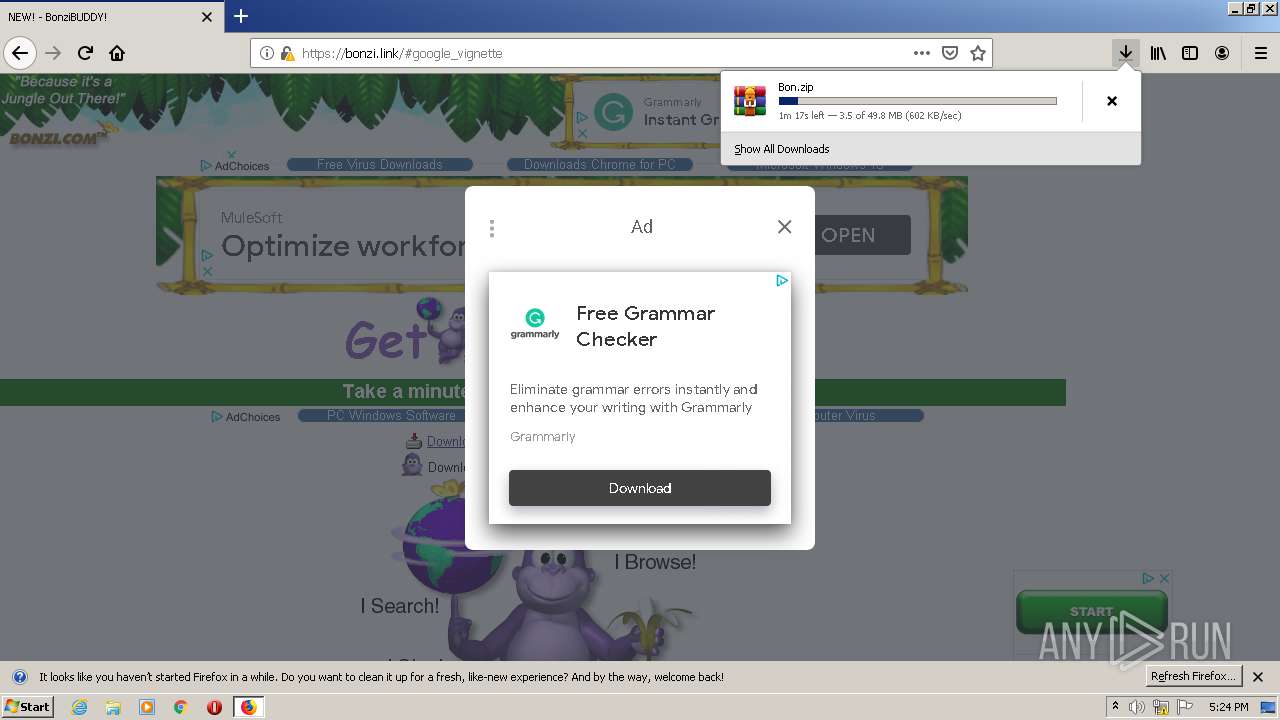
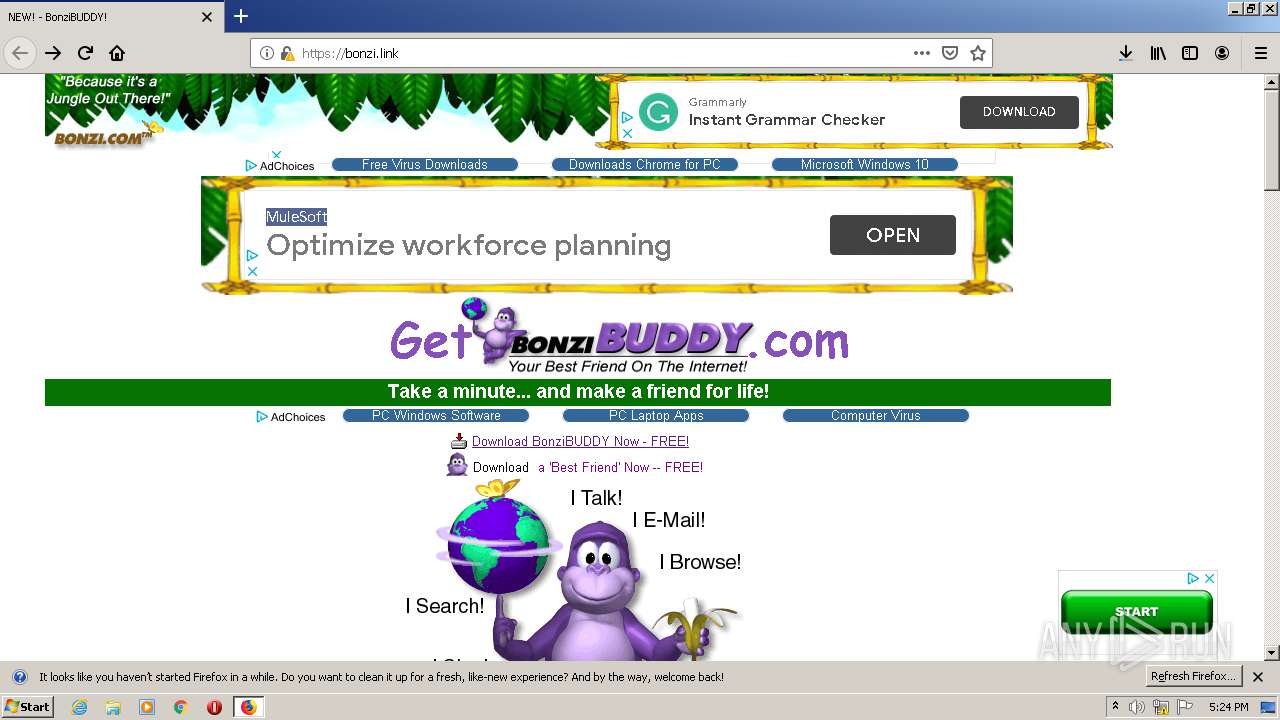
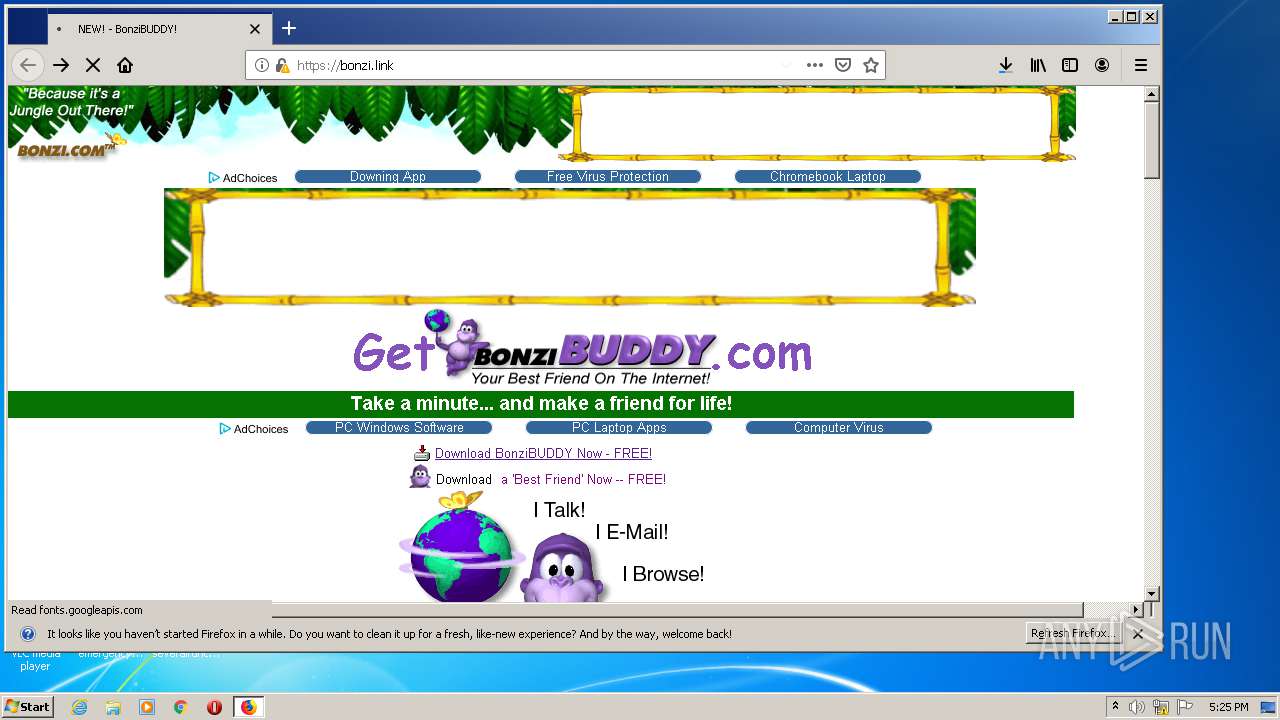
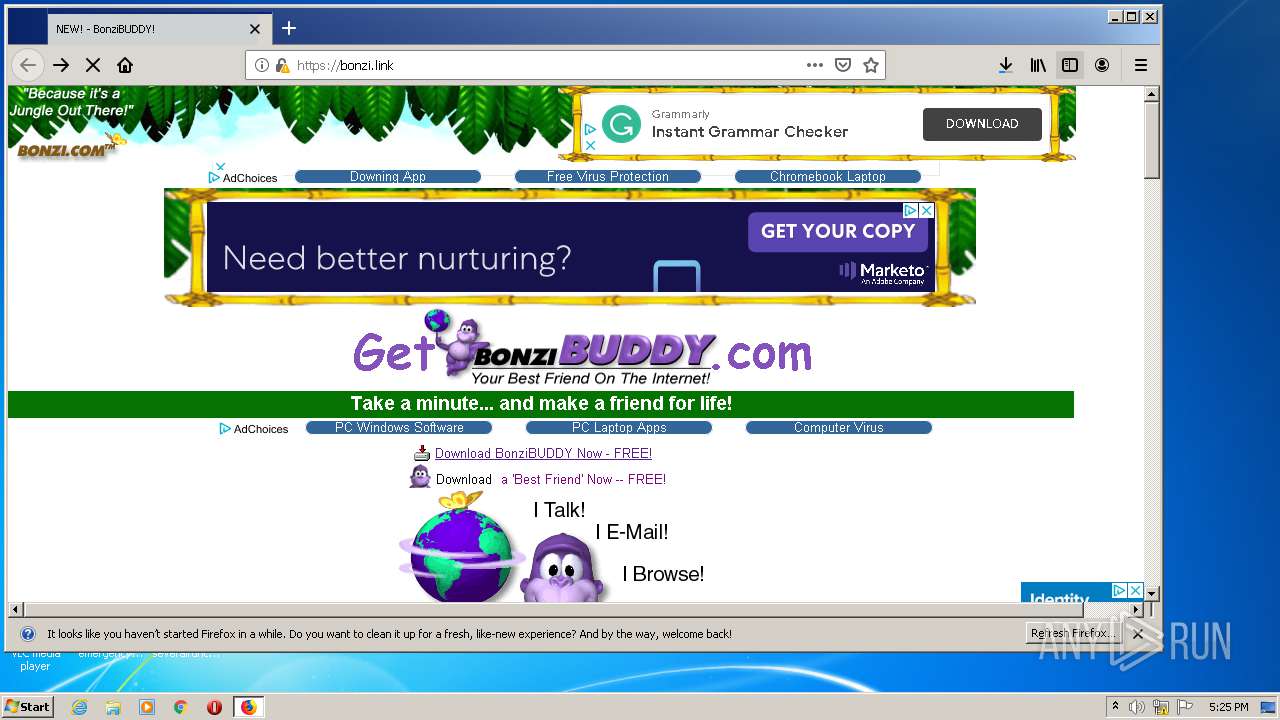
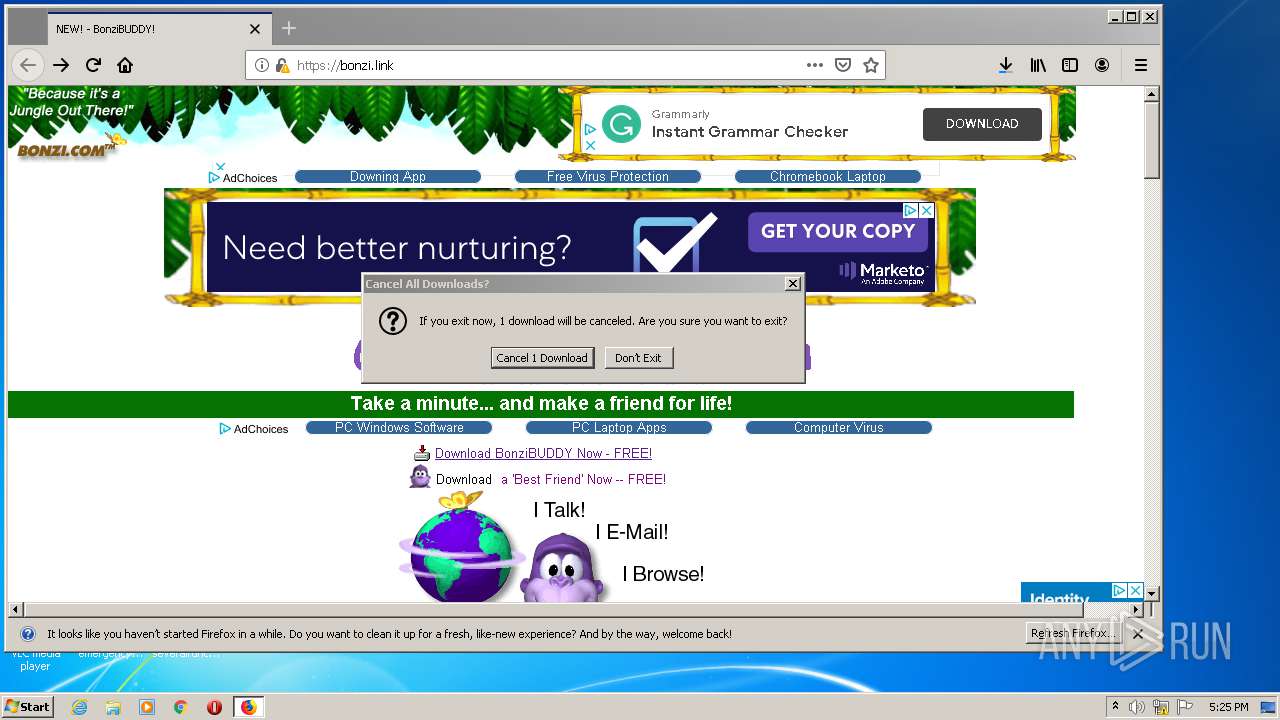
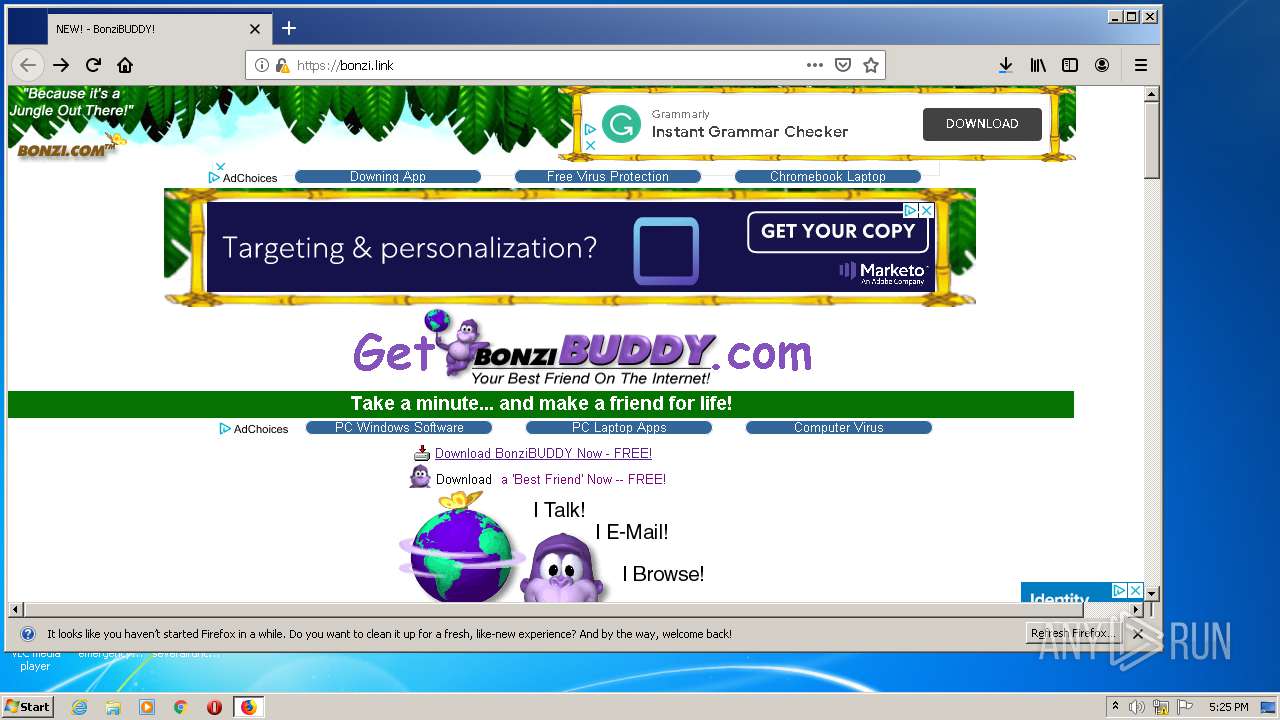
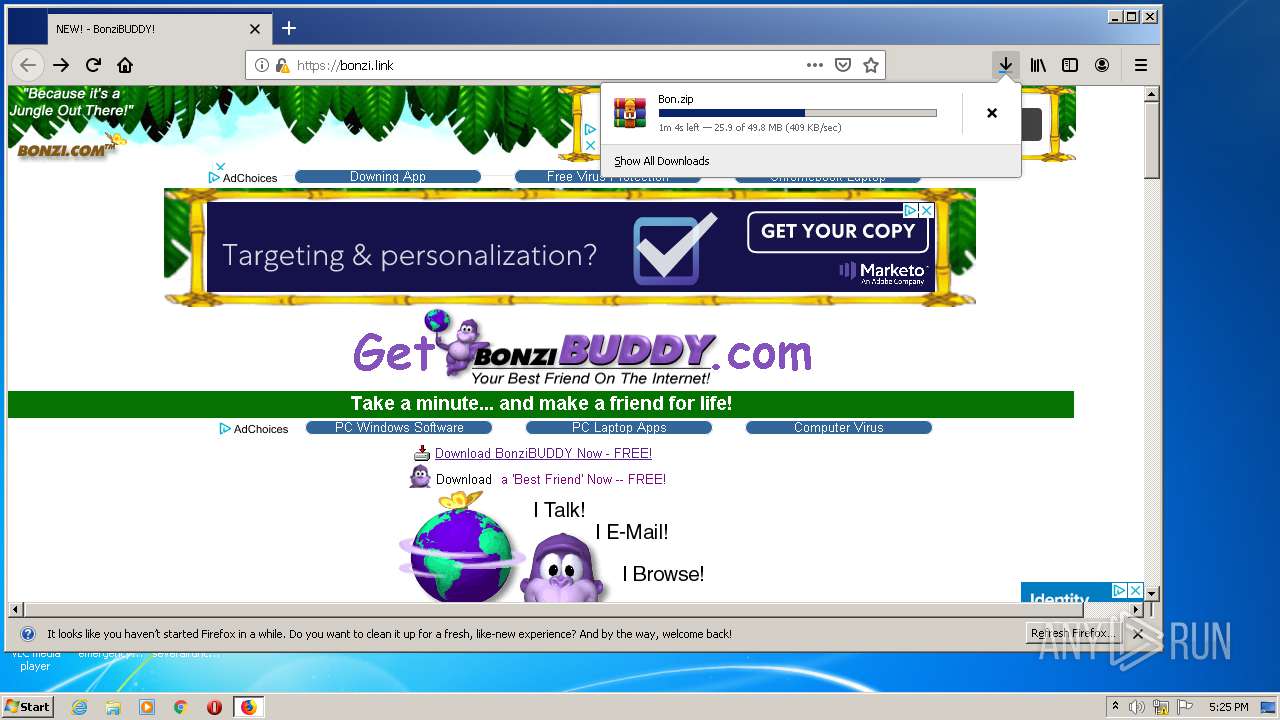
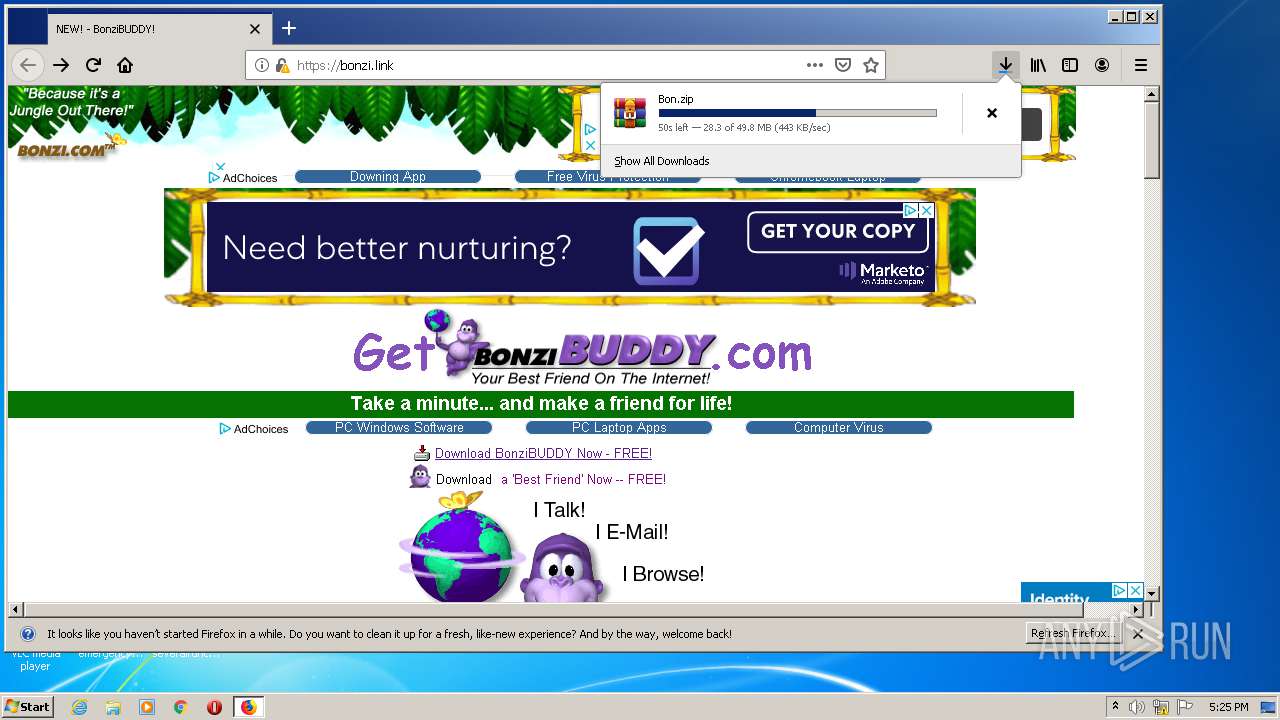
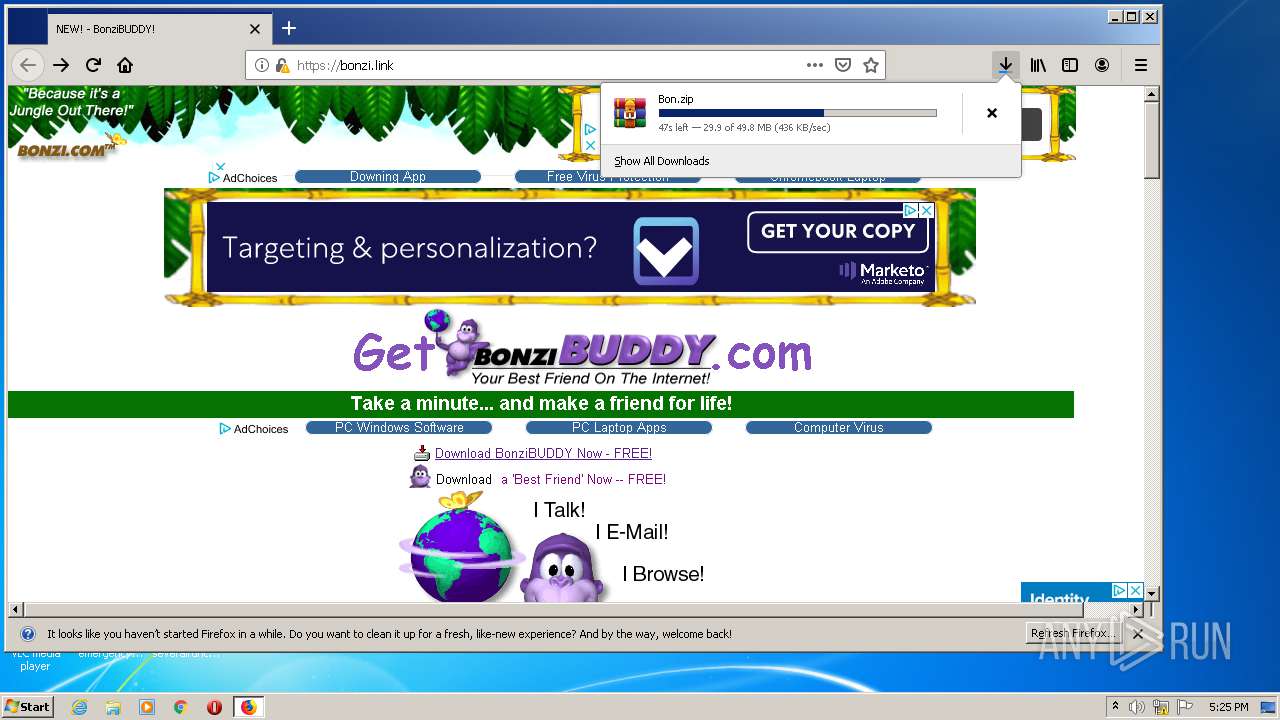
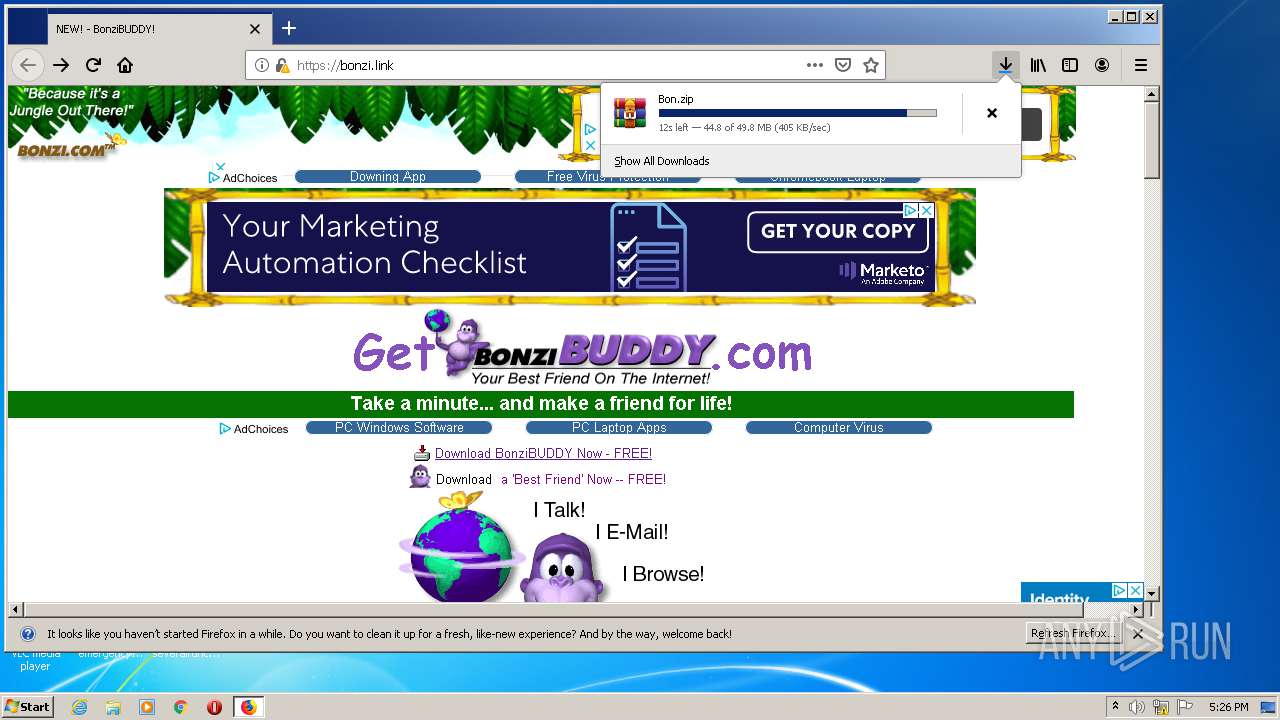
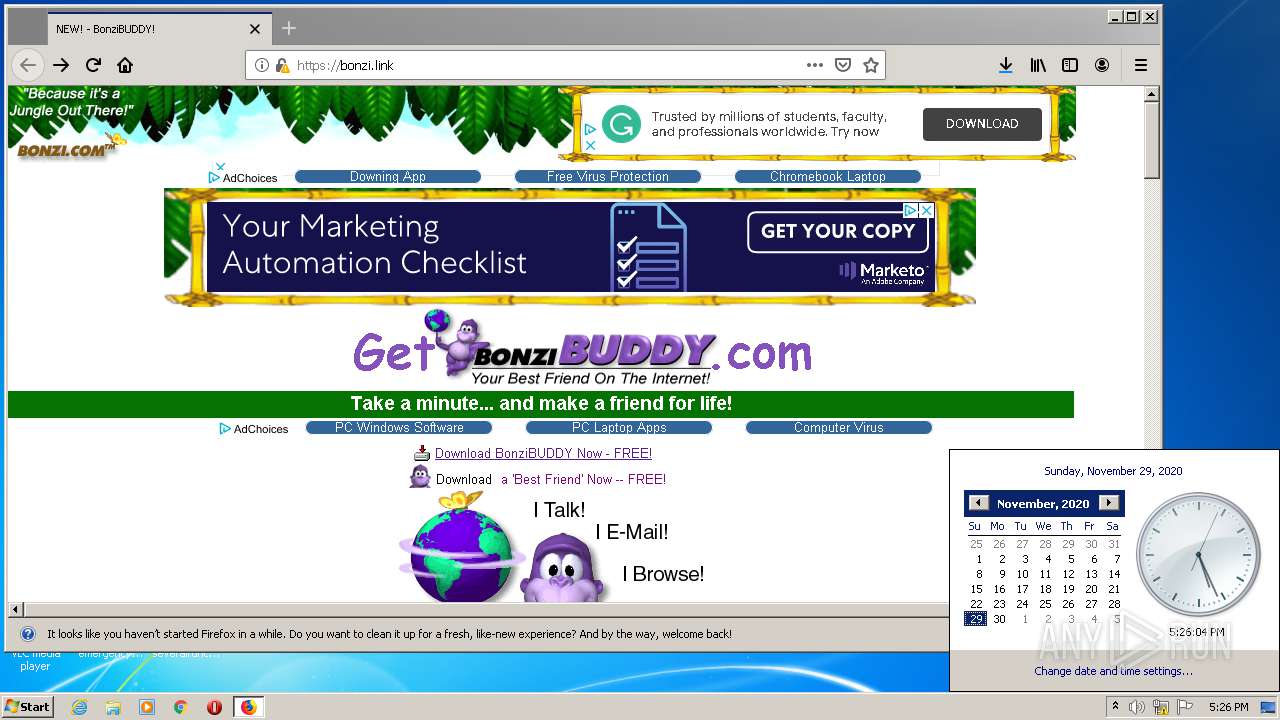
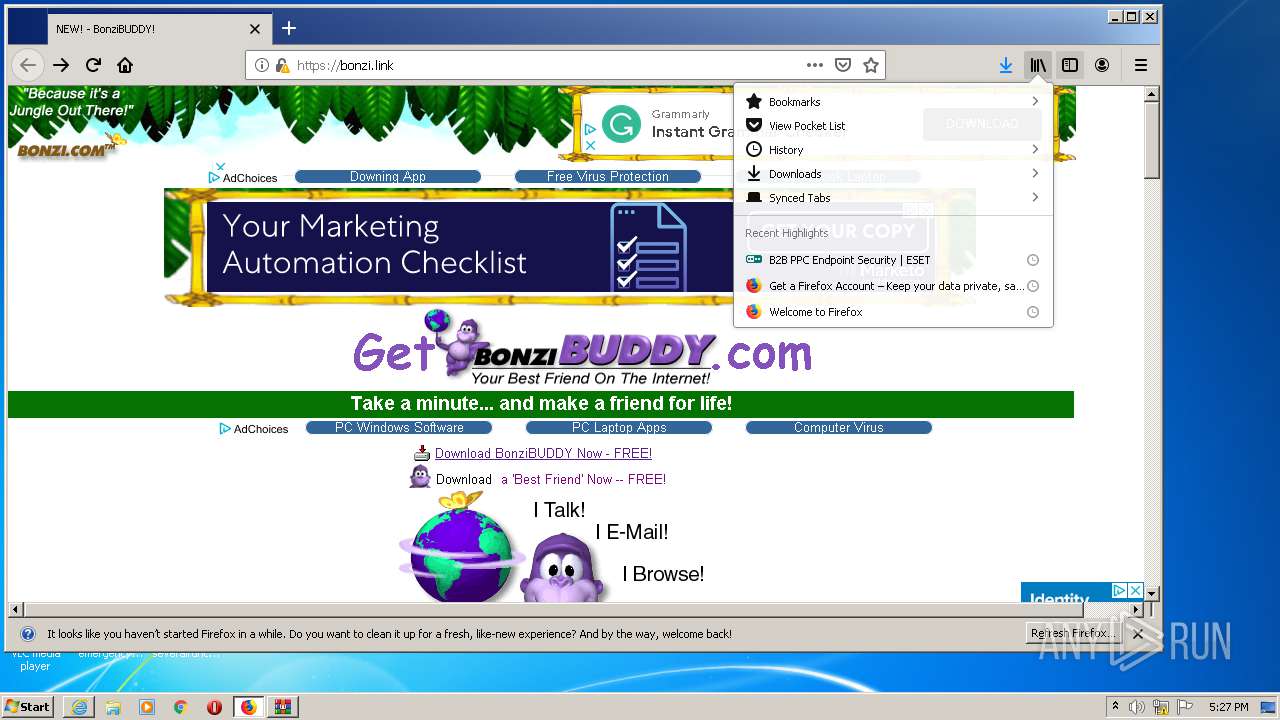
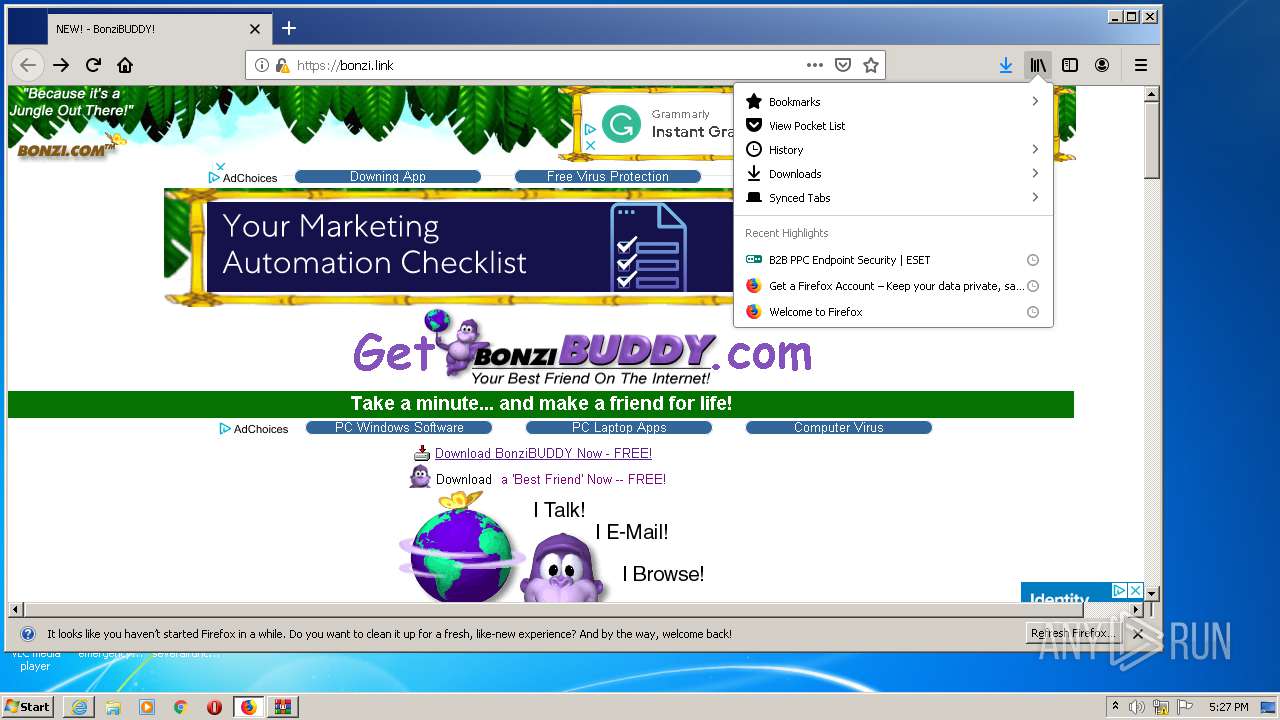
| URL: | https://bonzi.link/ |
| Full analysis: | https://app.any.run/tasks/3b49d928-35f4-414a-90b0-e500fb50aa42 |
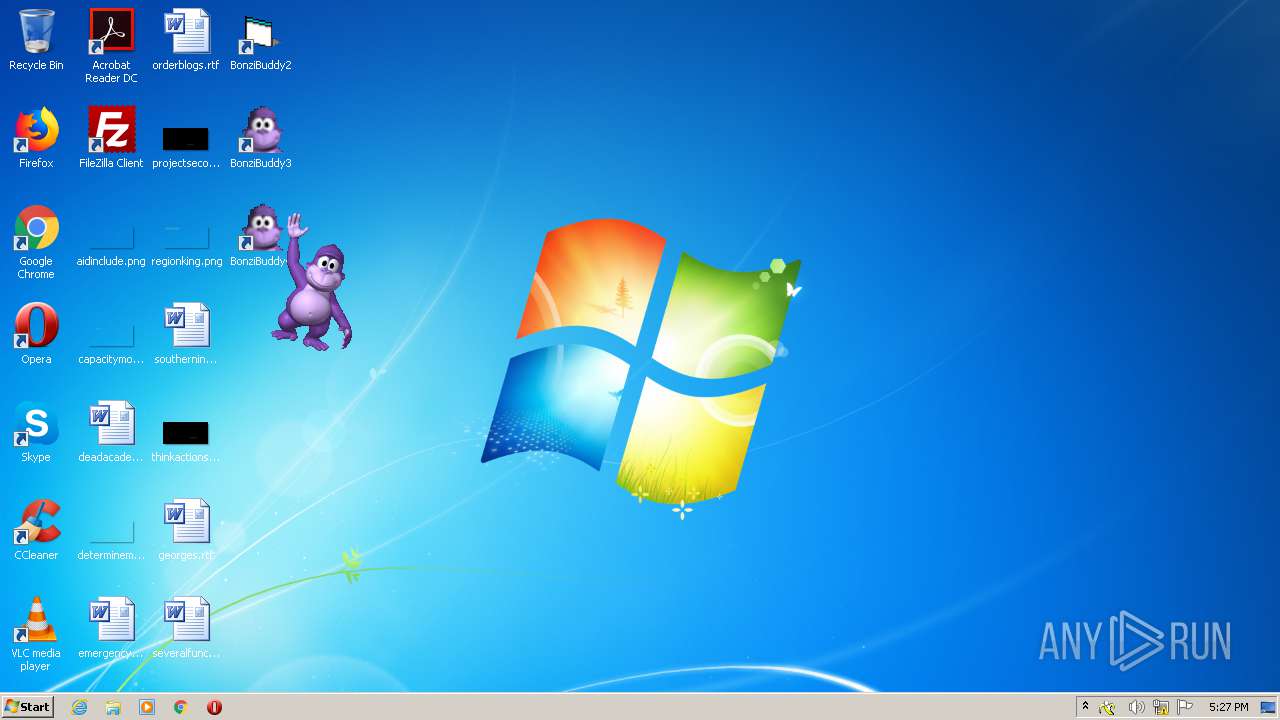
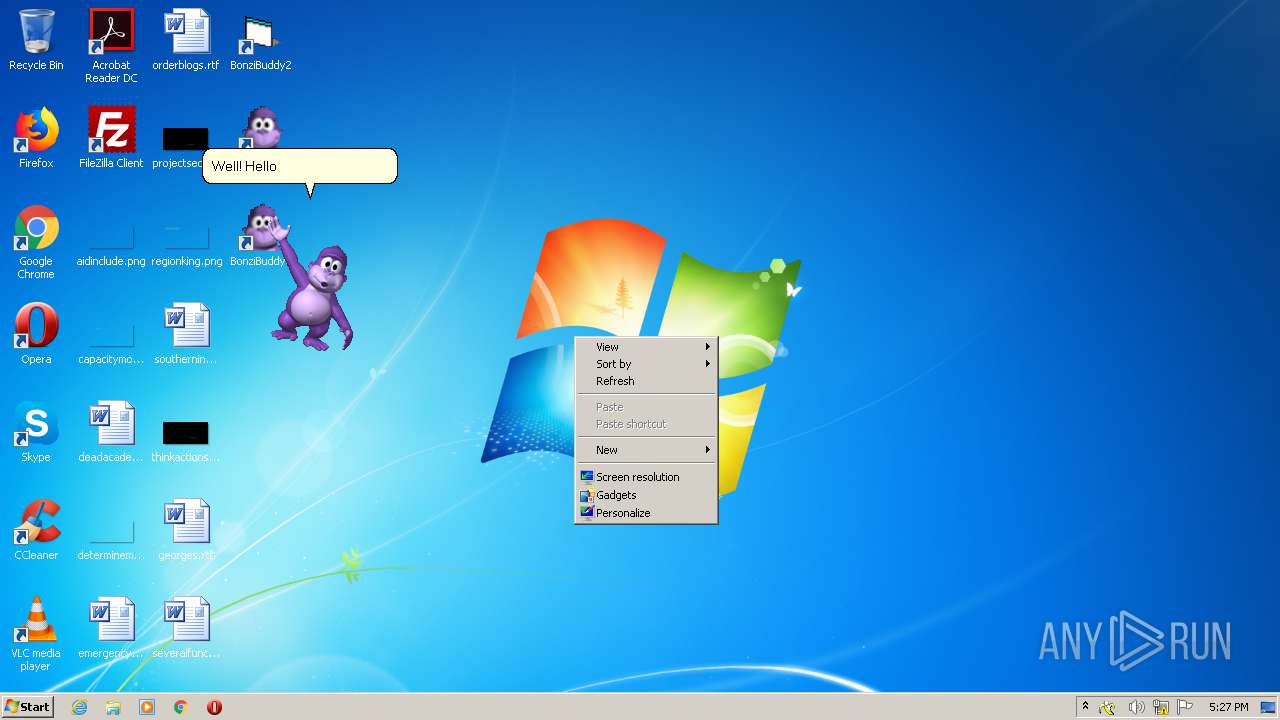
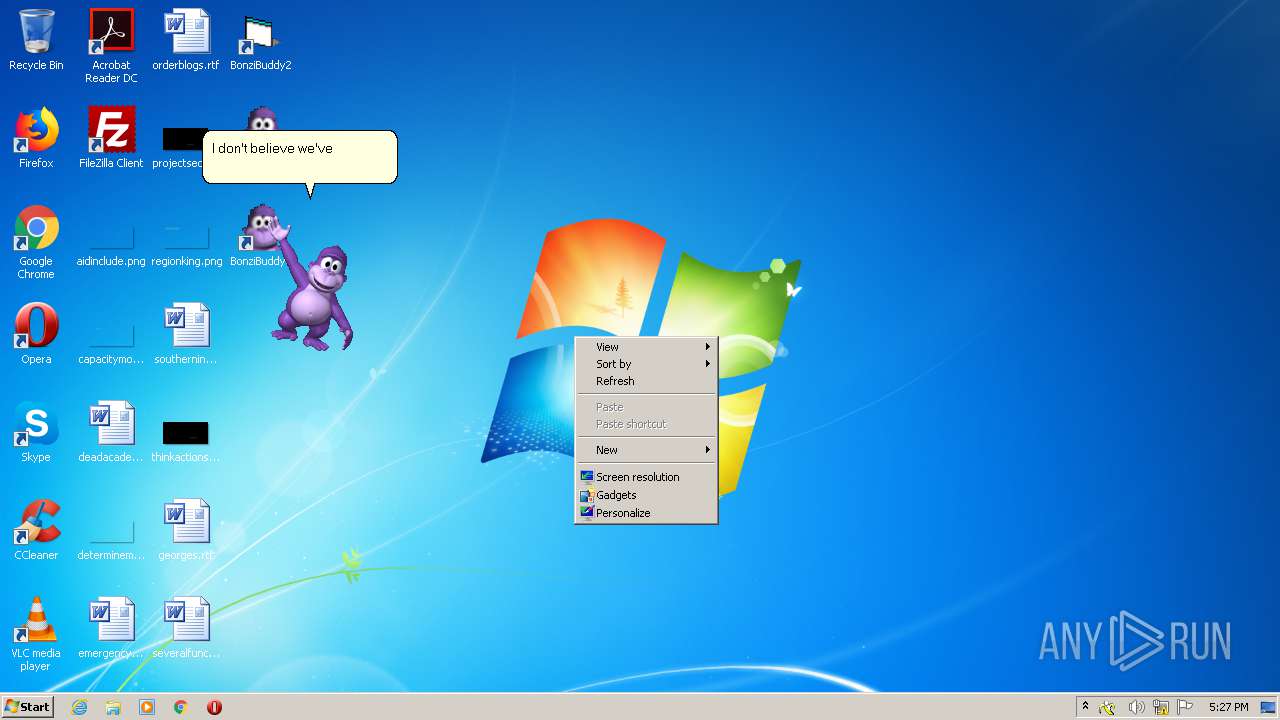
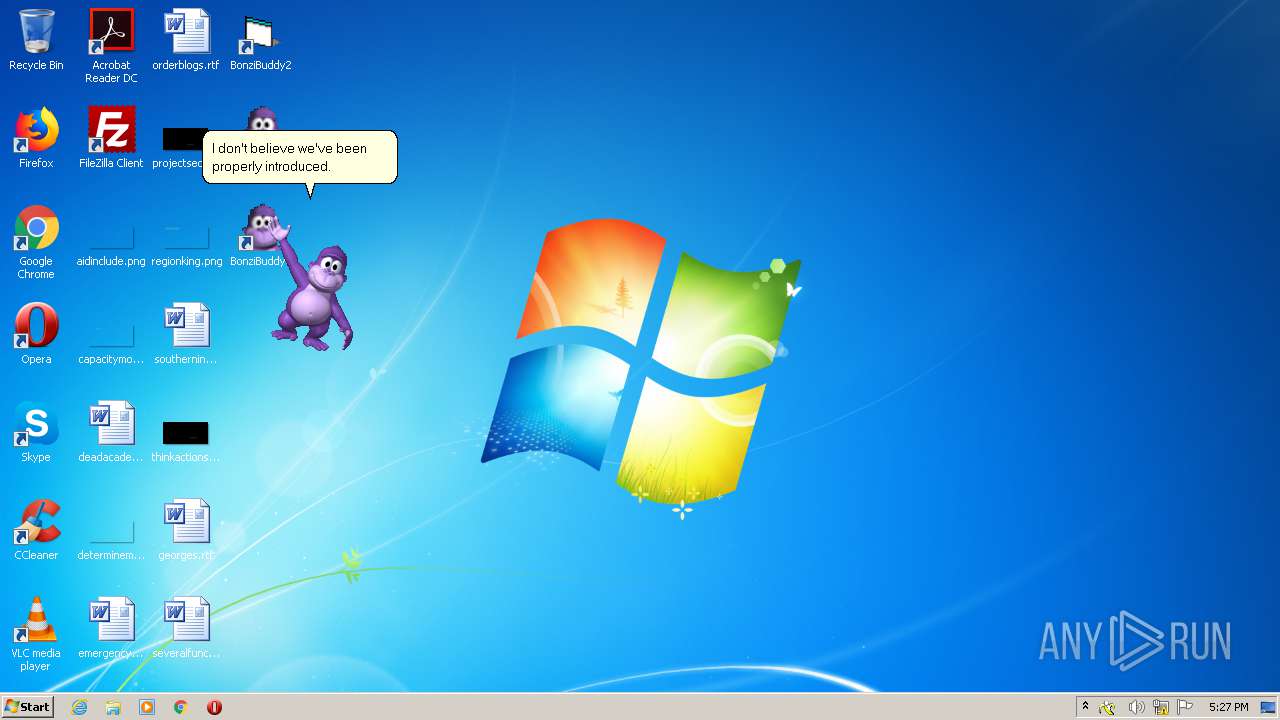
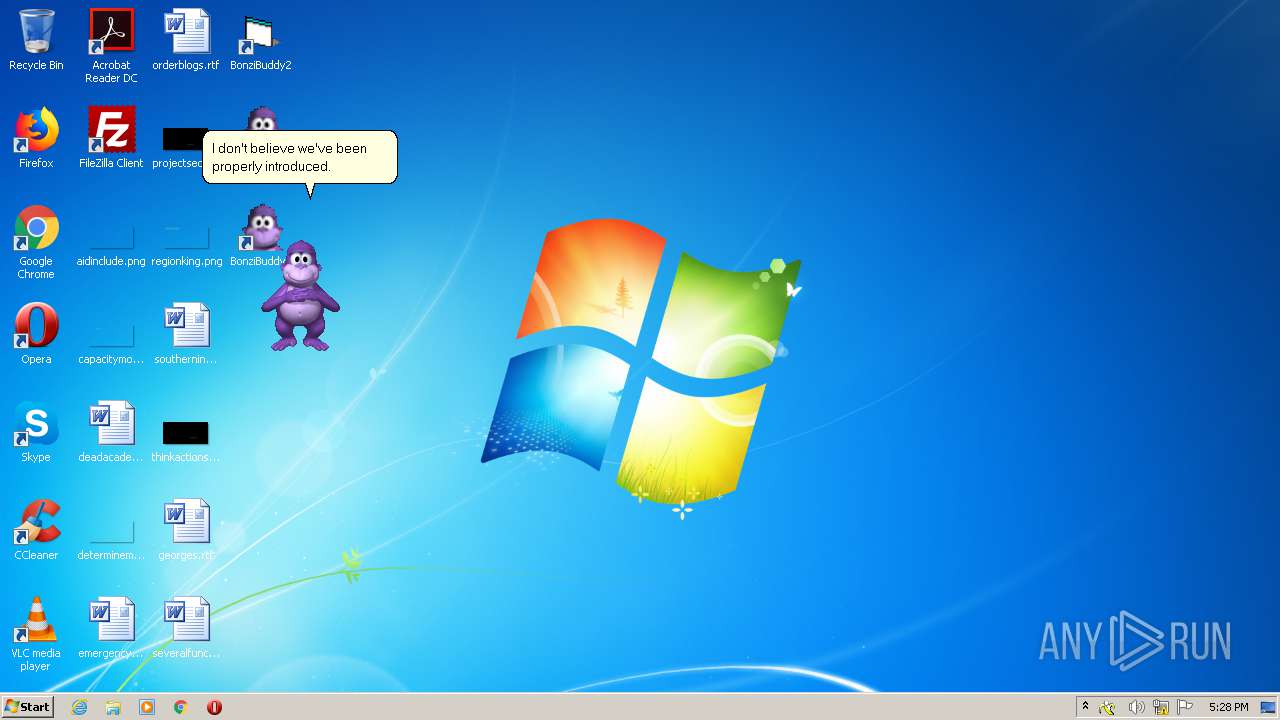
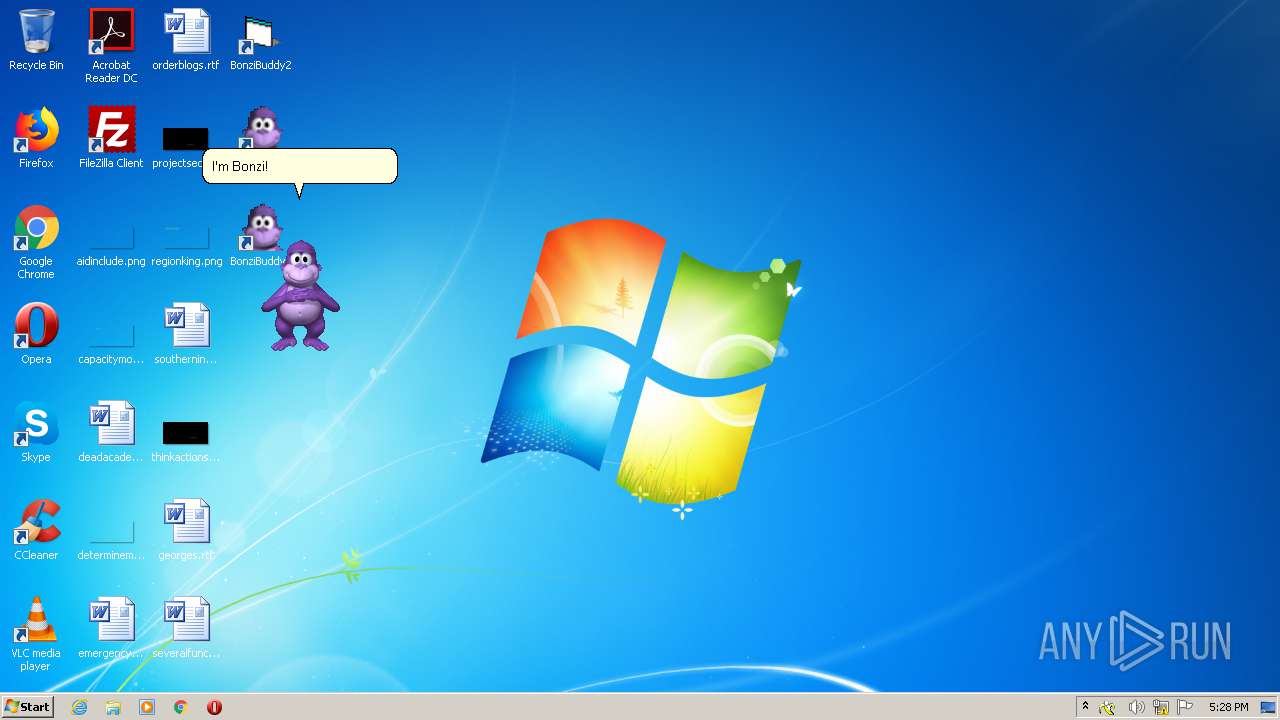
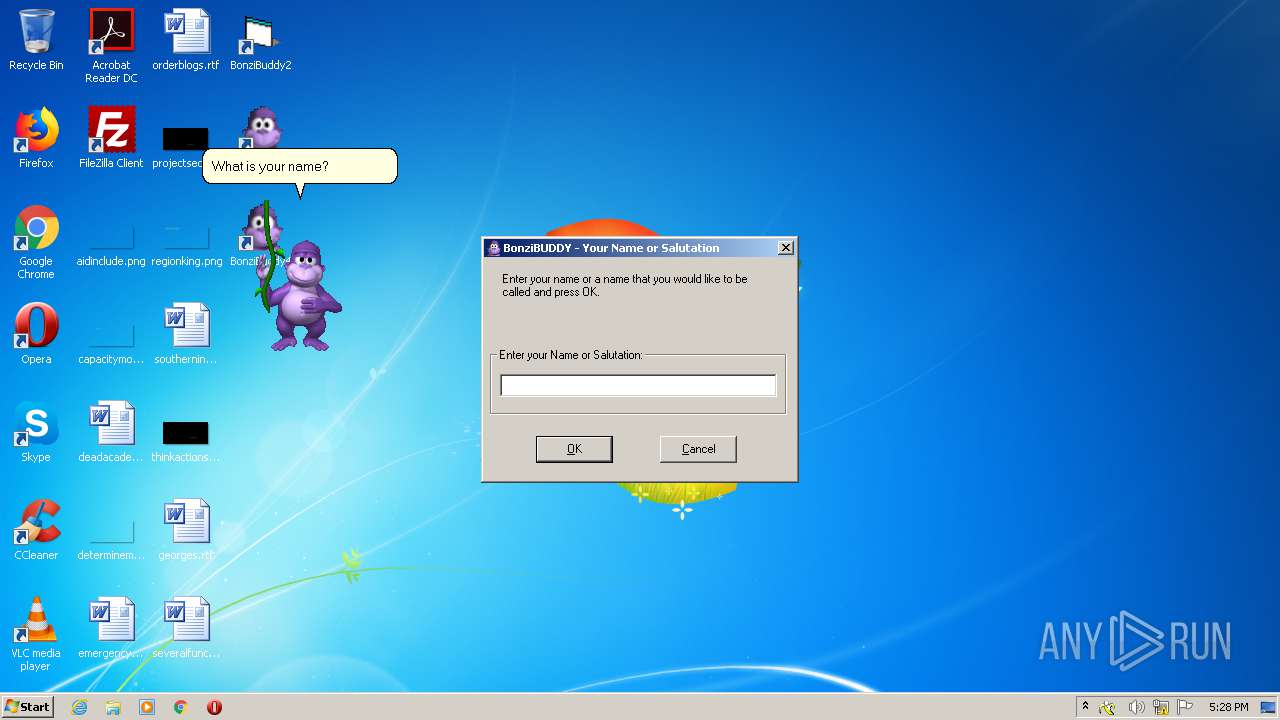
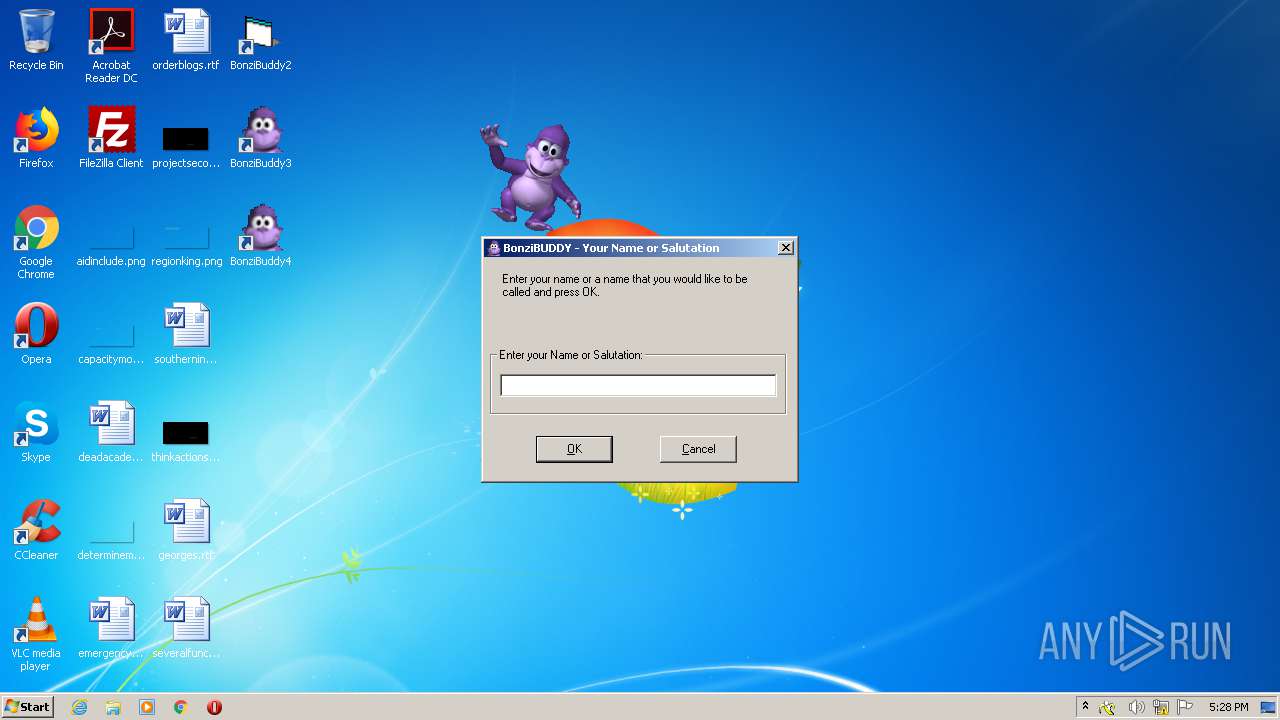
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 17:23:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1140171B39D570CE50B3779922DF0894 |
| SHA1: | BCF0DB75B50DFC7EB2906063628C9B14D4FA7B58 |
| SHA256: | E9F27F4B83B04B449BC7D4C120CB245ED43E338CBB94D341F735FE0889D60BFD |
| SSDEEP: | 3:N89K:29K |
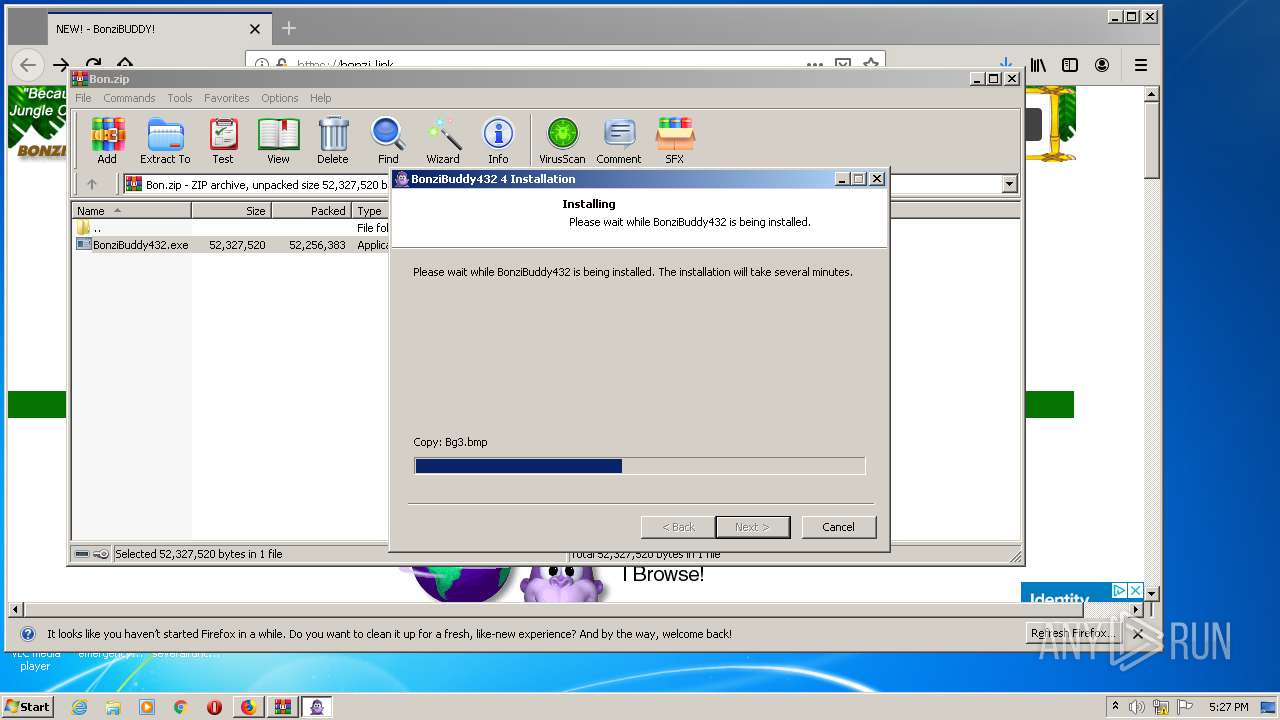
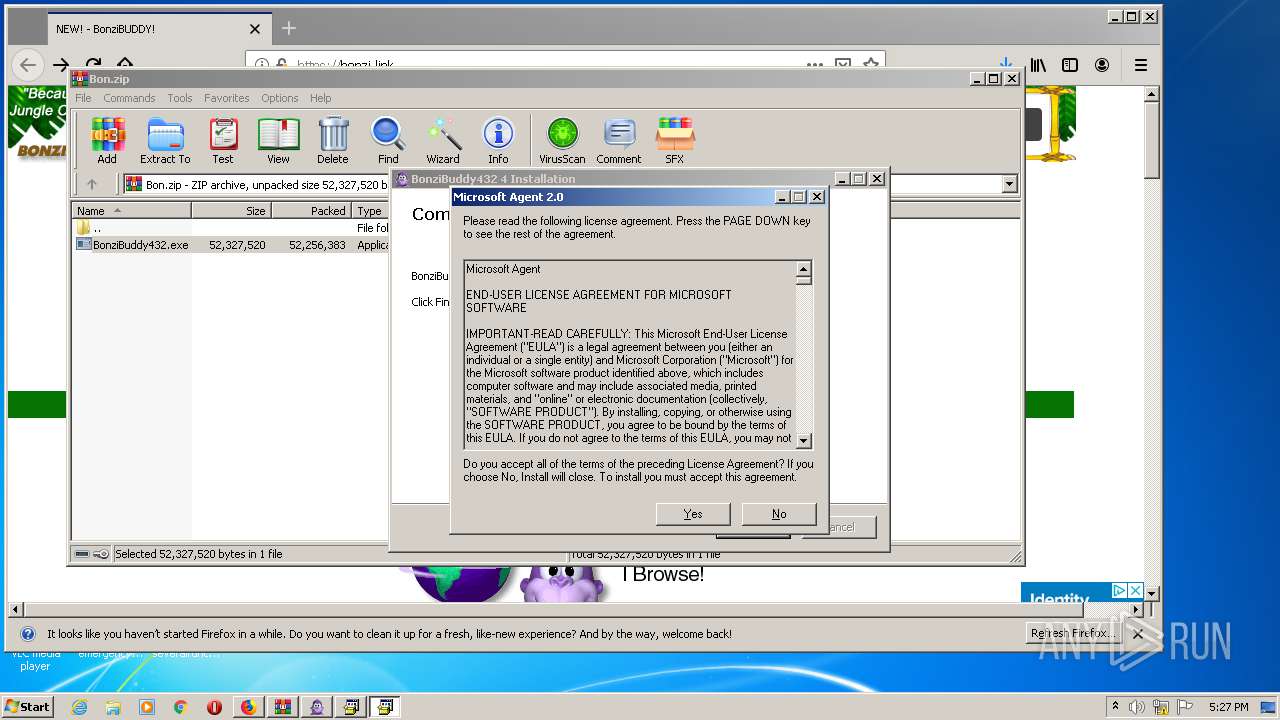
MALICIOUS
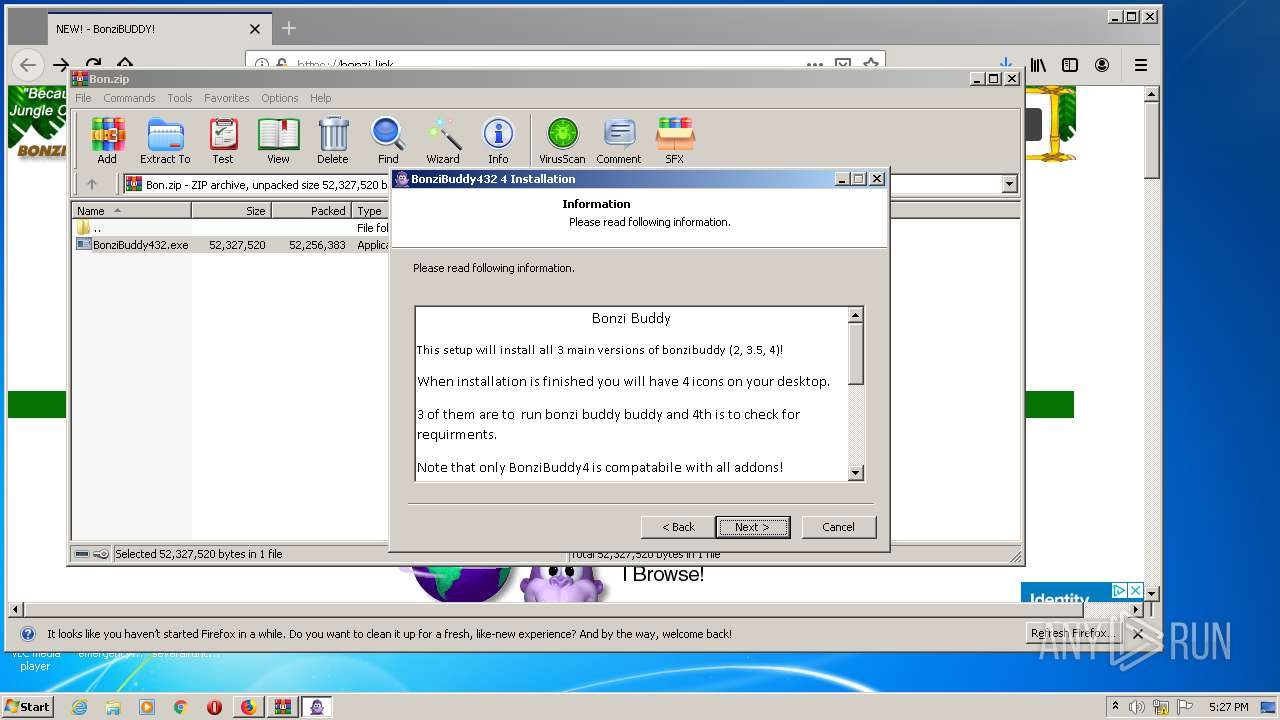
Loads dropped or rewritten executable
- BonziBuddy432.exe (PID: 4052)
- regsvr32.exe (PID: 3244)
- regsvr32.exe (PID: 2724)
- regsvr32.exe (PID: 2608)
- regsvr32.exe (PID: 3852)
- MSAGENT.EXE (PID: 3428)
- regsvr32.exe (PID: 3024)
- regsvr32.exe (PID: 2972)
- regsvr32.exe (PID: 2180)
- tv_enua.exe (PID: 4020)
- regsvr32.exe (PID: 2376)
- regsvr32.exe (PID: 2436)
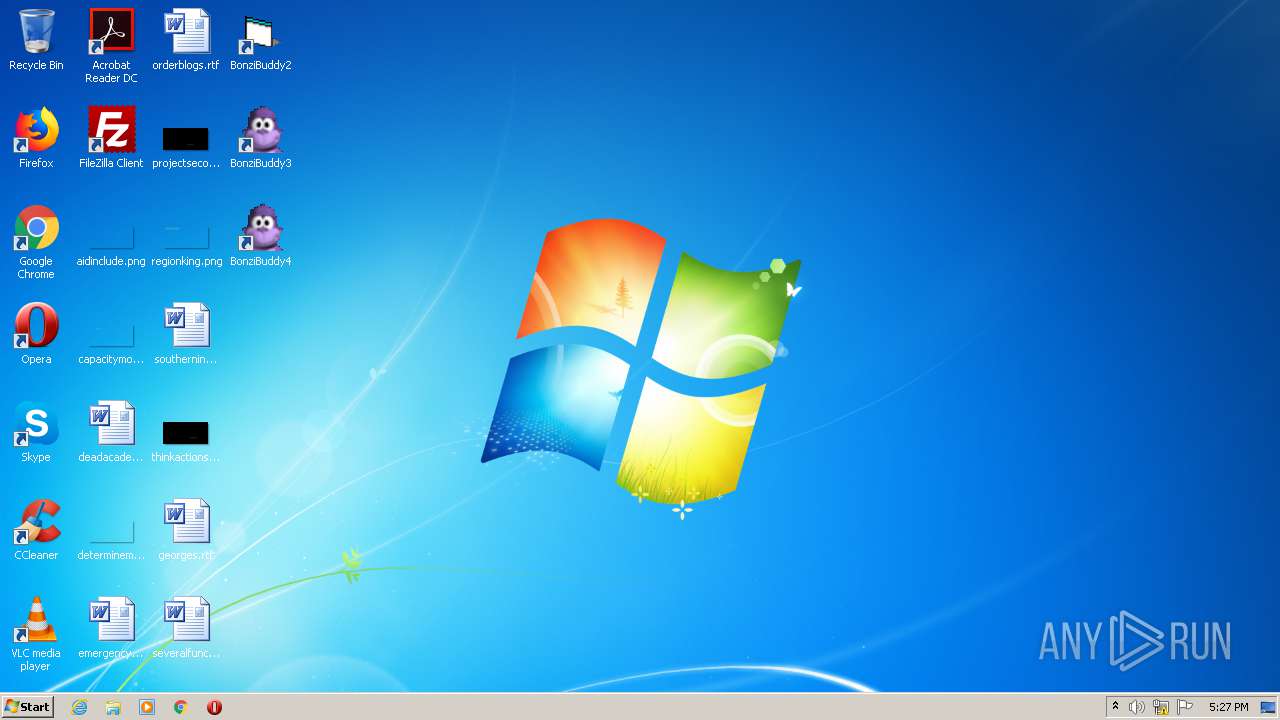
- BonziBDY_4.EXE (PID: 3804)
- AgentSvr.exe (PID: 848)
- BonziBDY_2.EXE (PID: 3972)
- BonziBDY_35.EXE (PID: 2404)
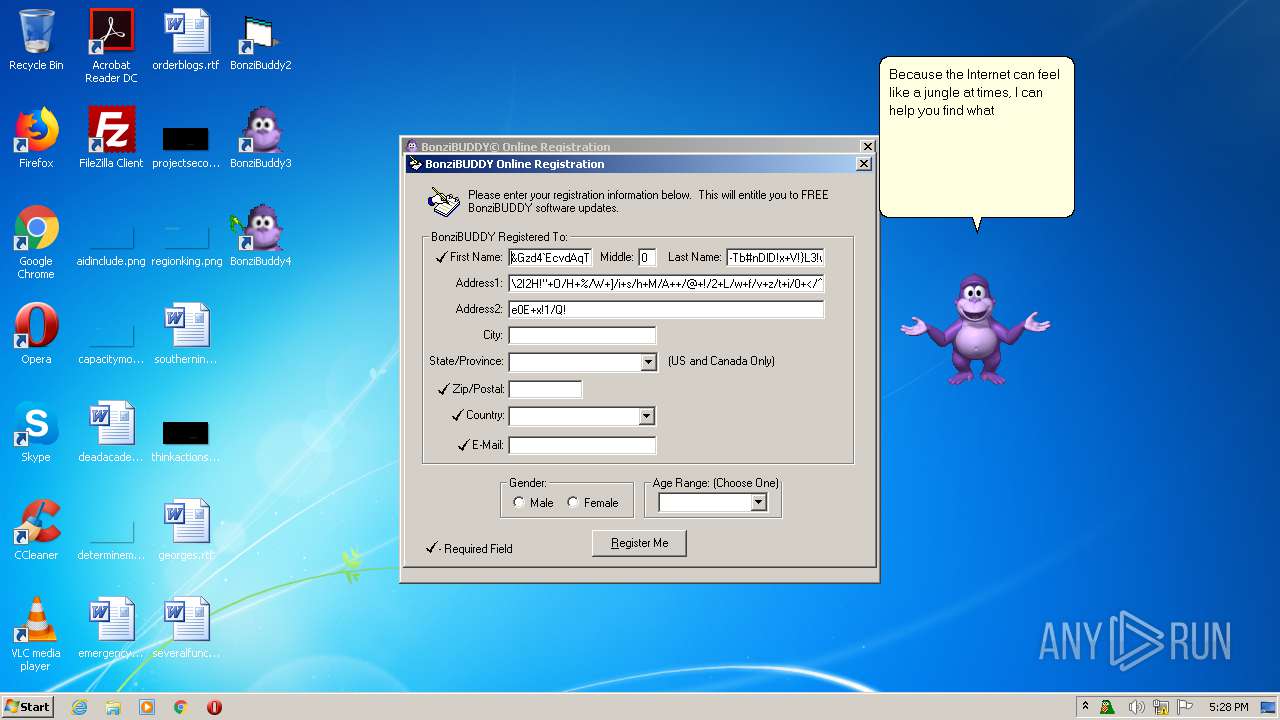
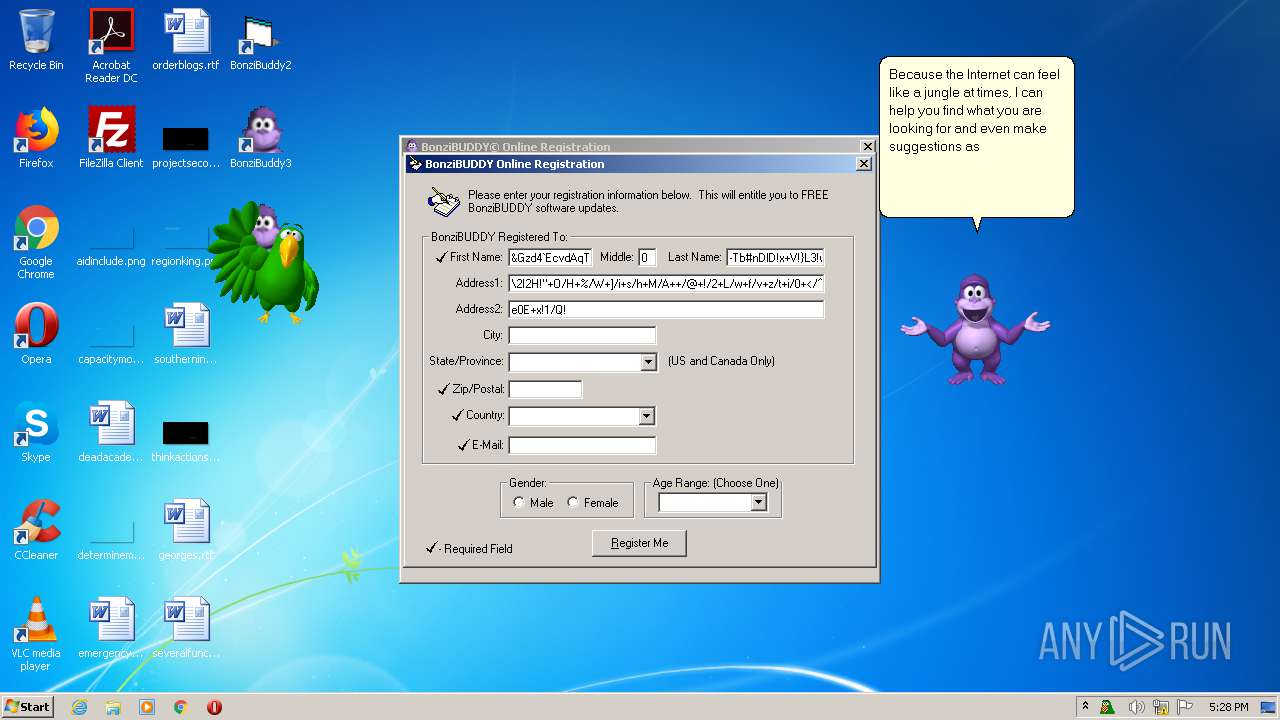
Application was dropped or rewritten from another process
- MSAGENT.EXE (PID: 3428)
- tv_enua.exe (PID: 4020)
- AgentSvr.exe (PID: 556)
- BonziBDY_4.EXE (PID: 3804)
- AgentSvr.exe (PID: 848)
- BonziBDY_2.EXE (PID: 3972)
- BonziBDY_35.EXE (PID: 2404)
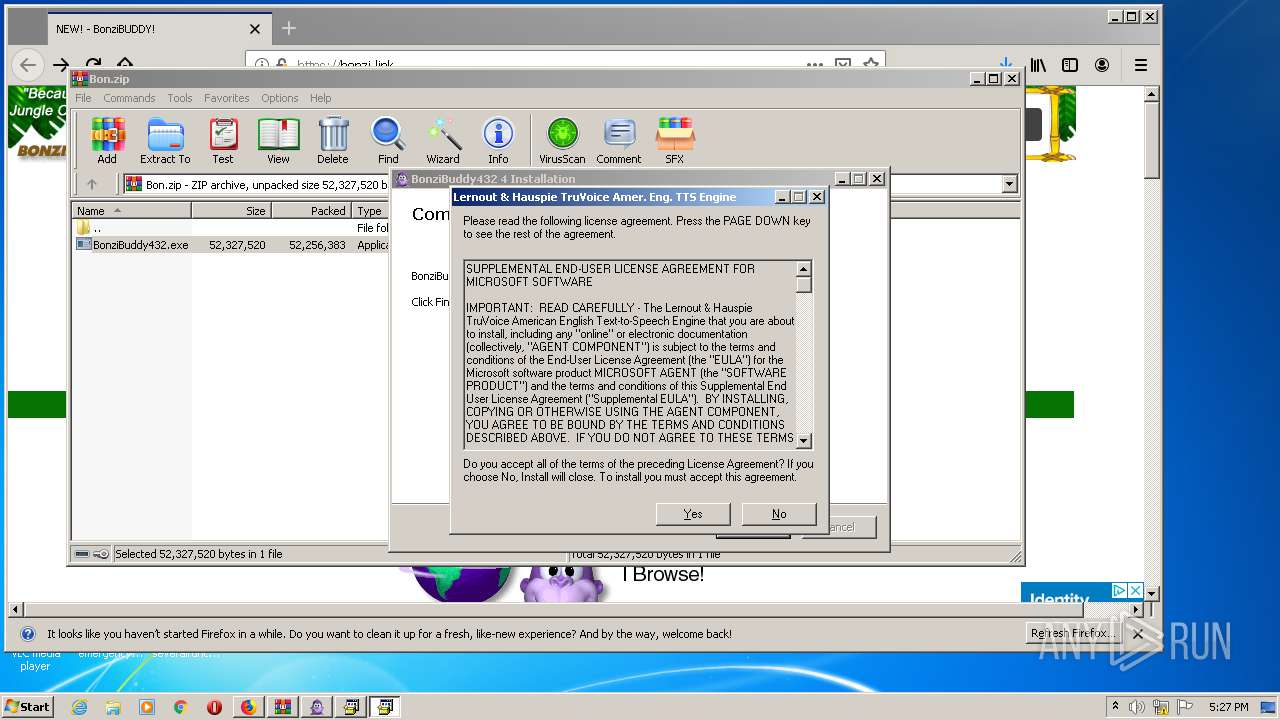
Registers / Runs the DLL via REGSVR32.EXE
- MSAGENT.EXE (PID: 3428)
- tv_enua.exe (PID: 4020)
Changes the autorun value in the registry
- tv_enua.exe (PID: 4020)
SUSPICIOUS
Executed via COM
- DllHost.exe (PID: 2104)
- AgentSvr.exe (PID: 848)
Executable content was dropped or overwritten
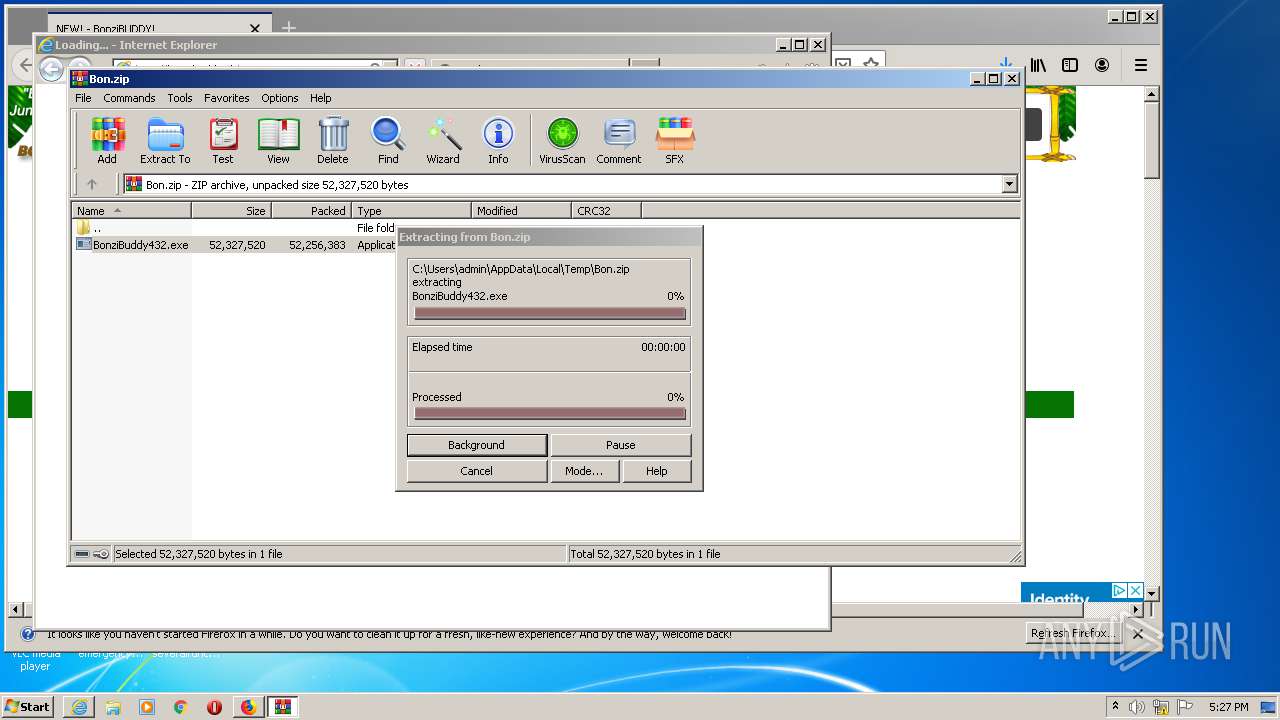
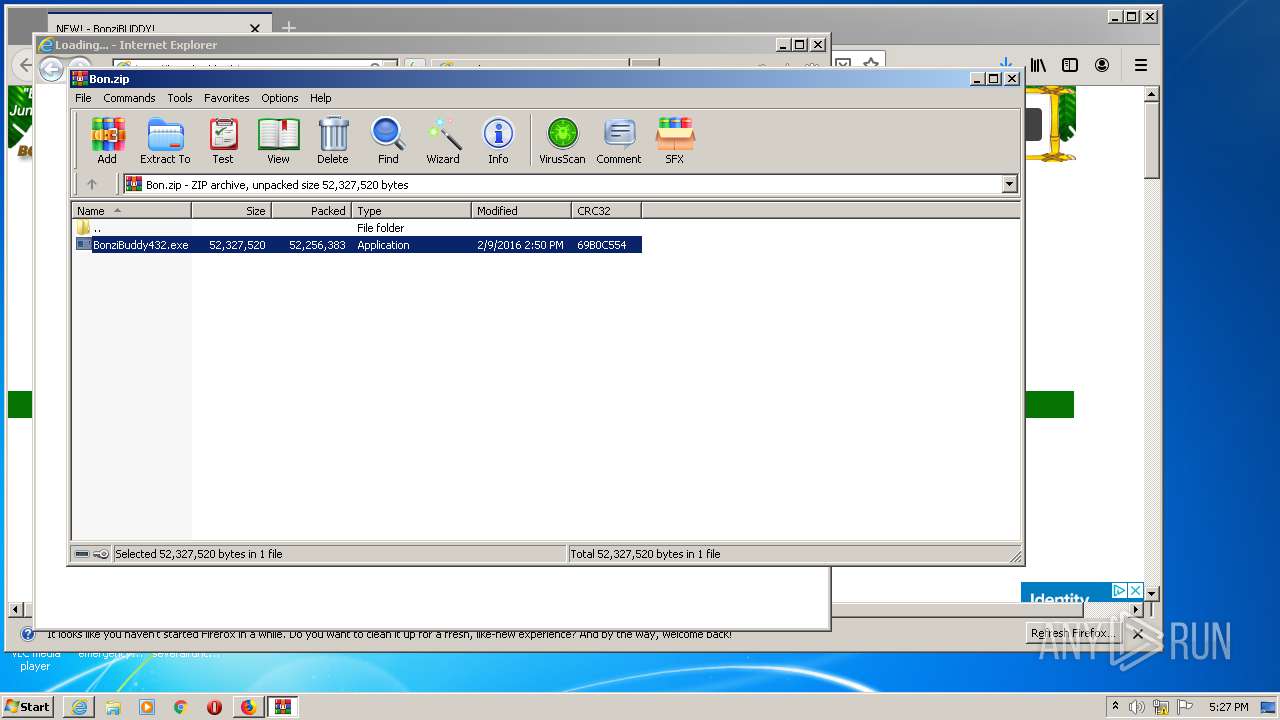
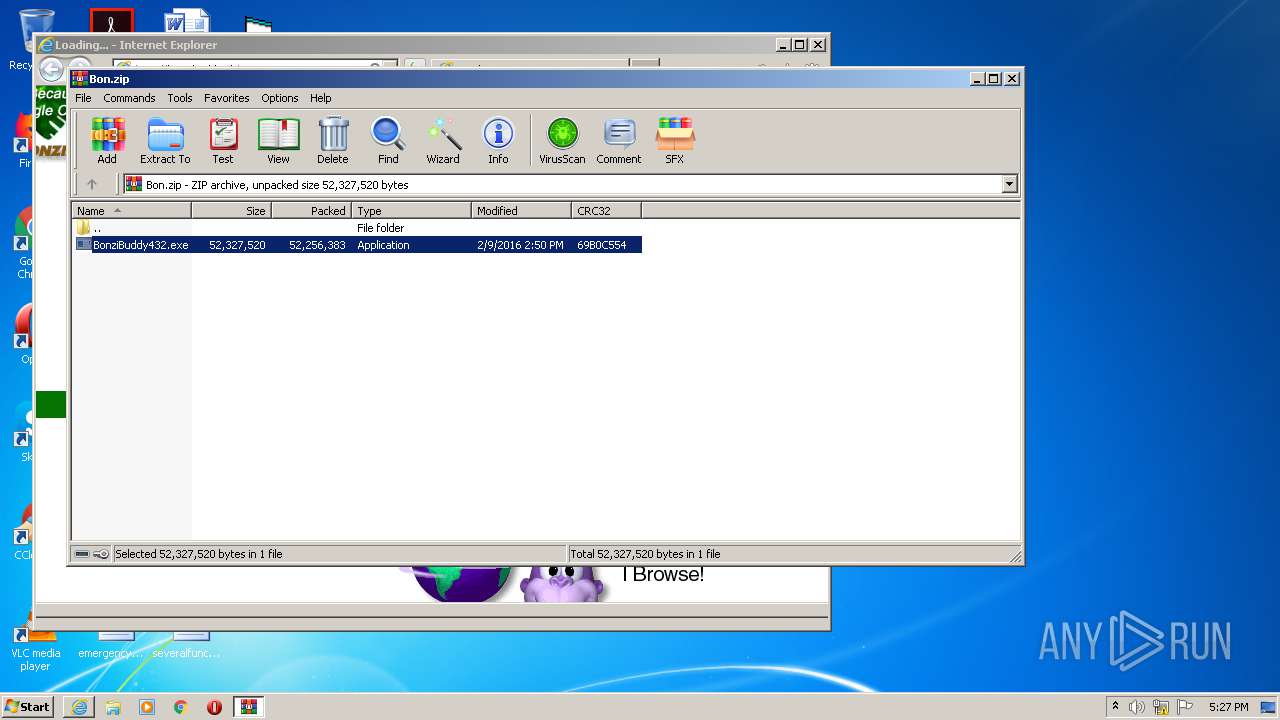
- BonziBuddy432.exe (PID: 4052)
- MSAGENT.EXE (PID: 3428)
- tv_enua.exe (PID: 4020)
Uses RUNDLL32.EXE to load library
- control.exe (PID: 2964)
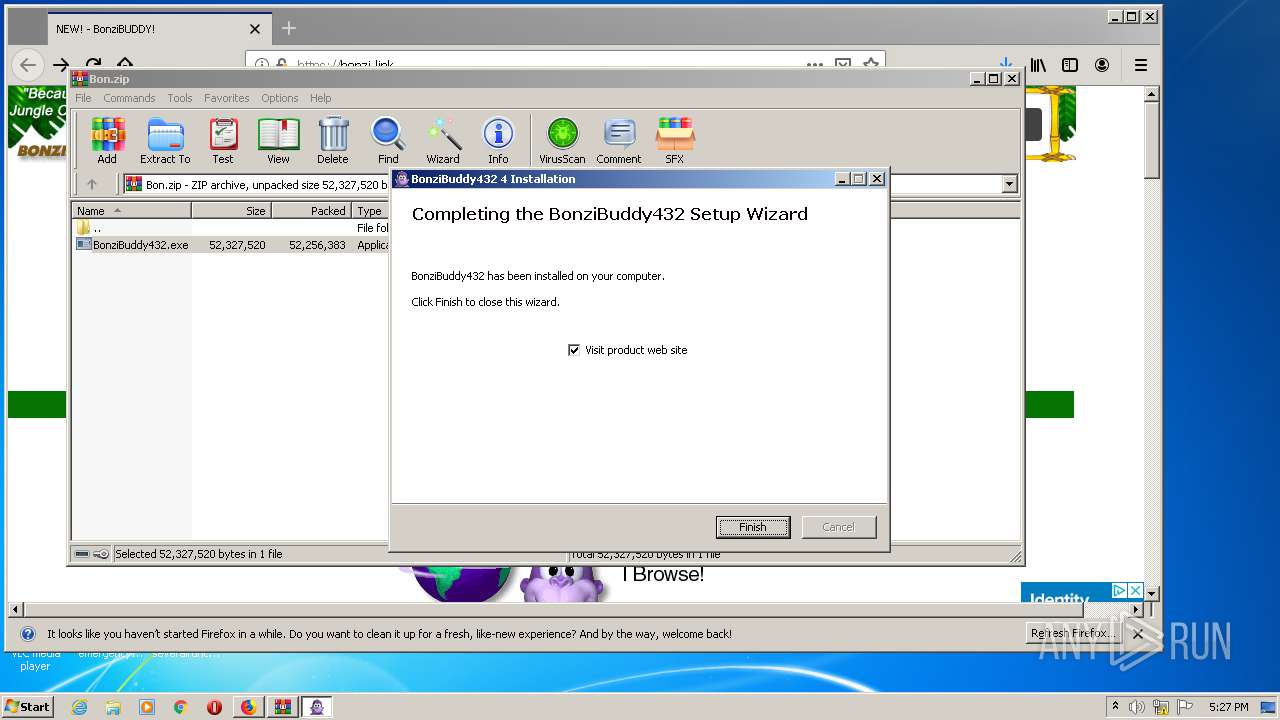
Creates a directory in Program Files
- BonziBuddy432.exe (PID: 4052)
Drops a file that was compiled in debug mode
- BonziBuddy432.exe (PID: 4052)
- MSAGENT.EXE (PID: 3428)
- tv_enua.exe (PID: 4020)
Drops a file with too old compile date
- BonziBuddy432.exe (PID: 4052)
- MSAGENT.EXE (PID: 3428)
- tv_enua.exe (PID: 4020)
Starts CMD.EXE for commands execution
- BonziBuddy432.exe (PID: 4052)
Creates files in the Windows directory
- BonziBuddy432.exe (PID: 4052)
- MSAGENT.EXE (PID: 3428)
- tv_enua.exe (PID: 4020)
Creates a software uninstall entry
- BonziBuddy432.exe (PID: 4052)
- tv_enua.exe (PID: 4020)
Creates files in the user directory
- BonziBuddy432.exe (PID: 4052)
Drops a file with a compile date too recent
- MSAGENT.EXE (PID: 3428)
- tv_enua.exe (PID: 4020)
Removes files from Windows directory
- MSAGENT.EXE (PID: 3428)
- tv_enua.exe (PID: 4020)
Creates COM task schedule object
- regsvr32.exe (PID: 2608)
- regsvr32.exe (PID: 2724)
- regsvr32.exe (PID: 3852)
- regsvr32.exe (PID: 3244)
- regsvr32.exe (PID: 3024)
- regsvr32.exe (PID: 2972)
- regsvr32.exe (PID: 2180)
- regsvr32.exe (PID: 2436)
- regsvr32.exe (PID: 2376)
Creates files in the program directory
- BonziBuddy432.exe (PID: 4052)
- BonziBDY_4.EXE (PID: 3804)
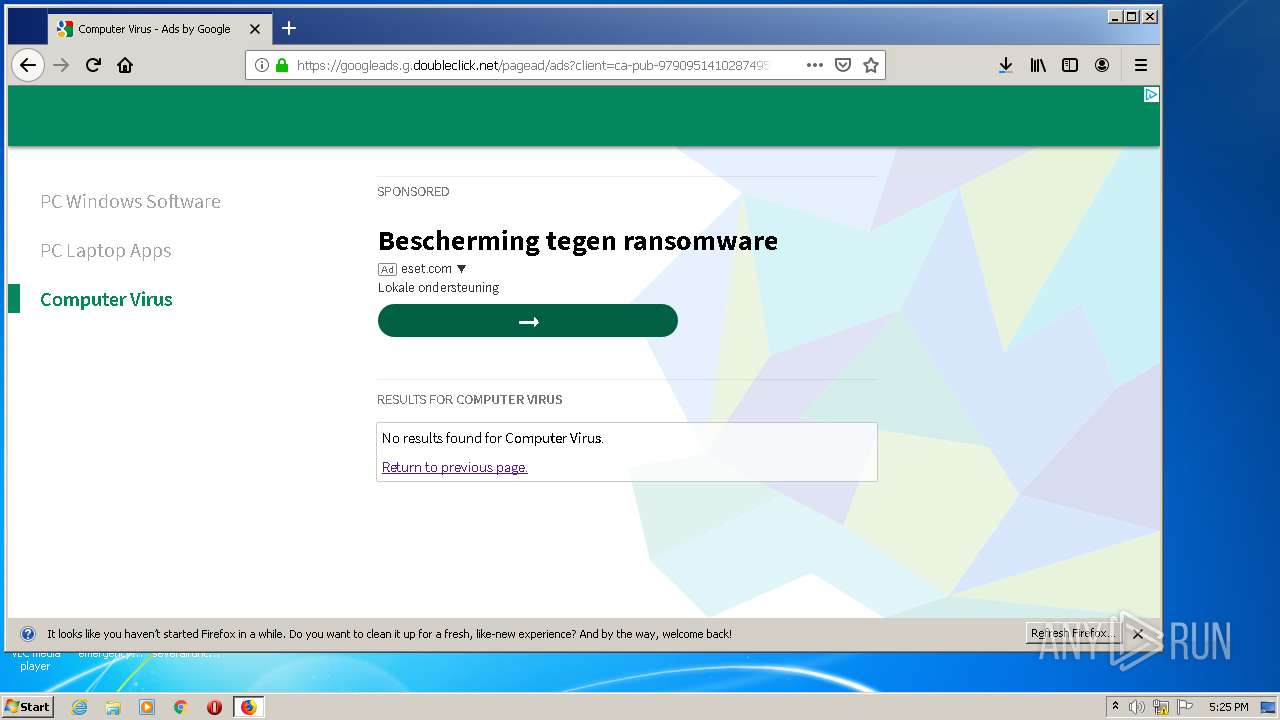
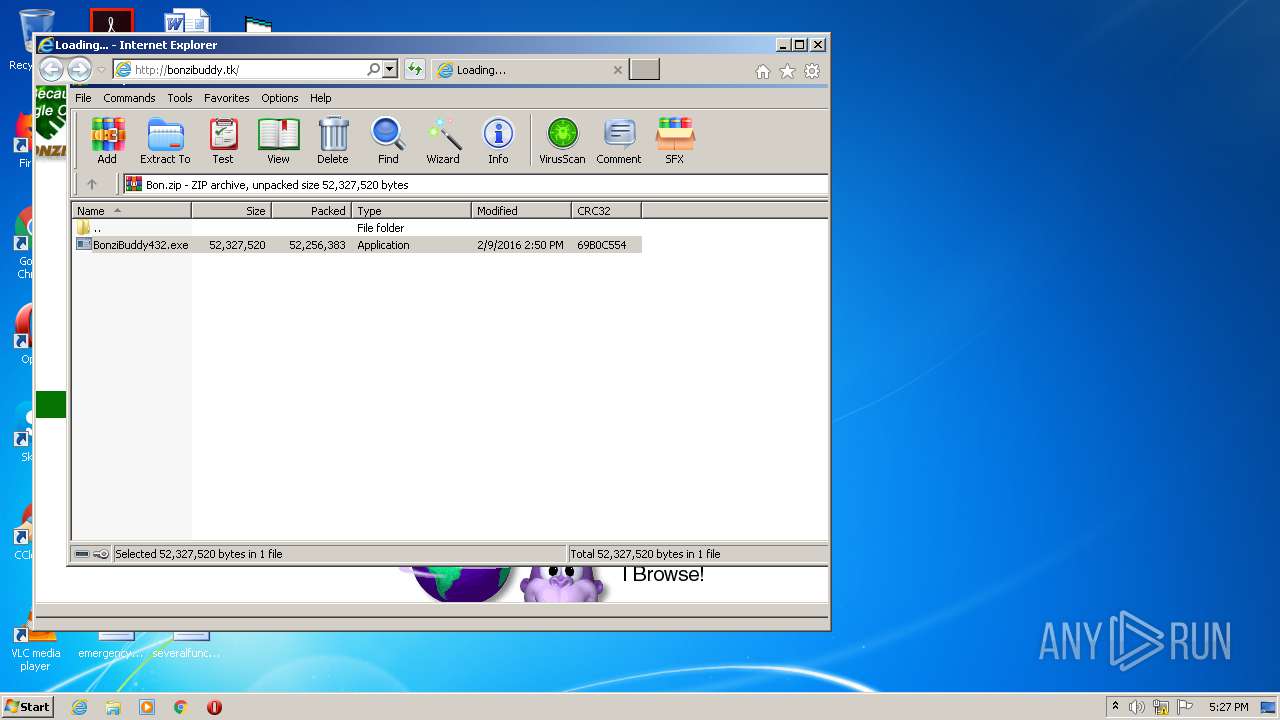
Starts Internet Explorer
- BonziBuddy432.exe (PID: 4052)
INFO
Application launched itself
- firefox.exe (PID: 840)
- firefox.exe (PID: 3748)
- iexplore.exe (PID: 3776)
Creates files in the program directory
- firefox.exe (PID: 3748)
Reads CPU info
- firefox.exe (PID: 3748)
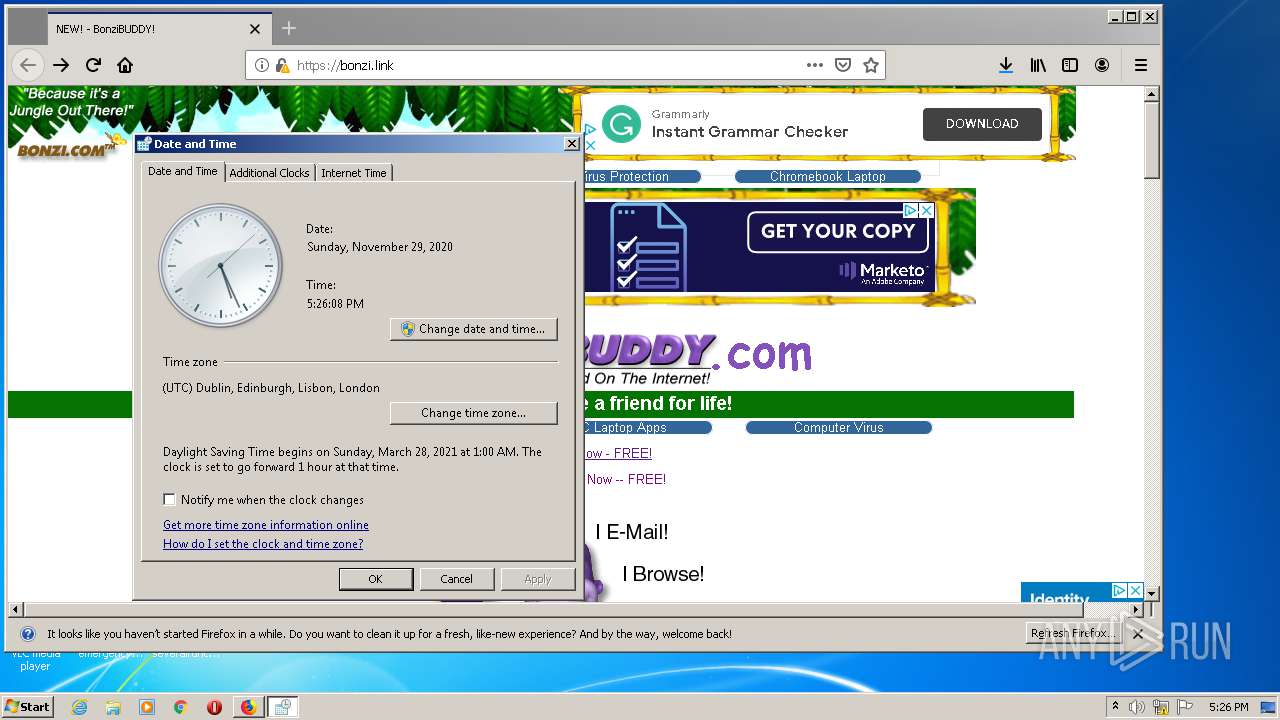
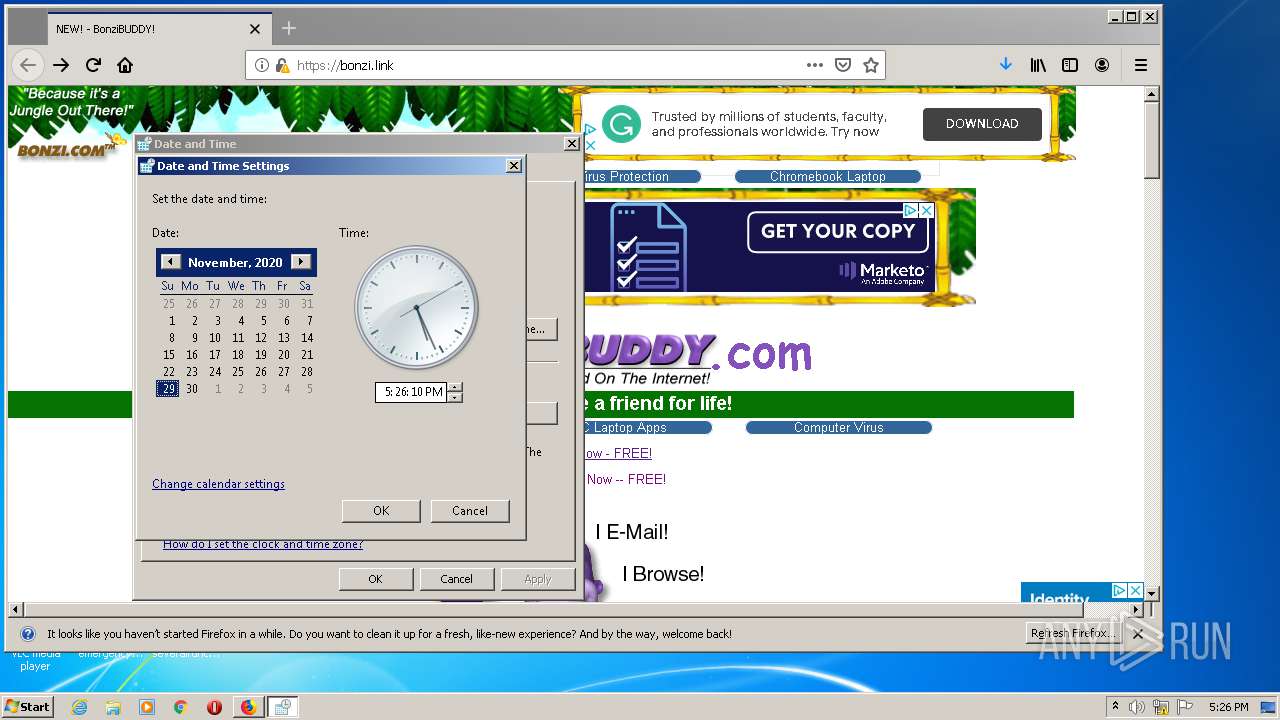
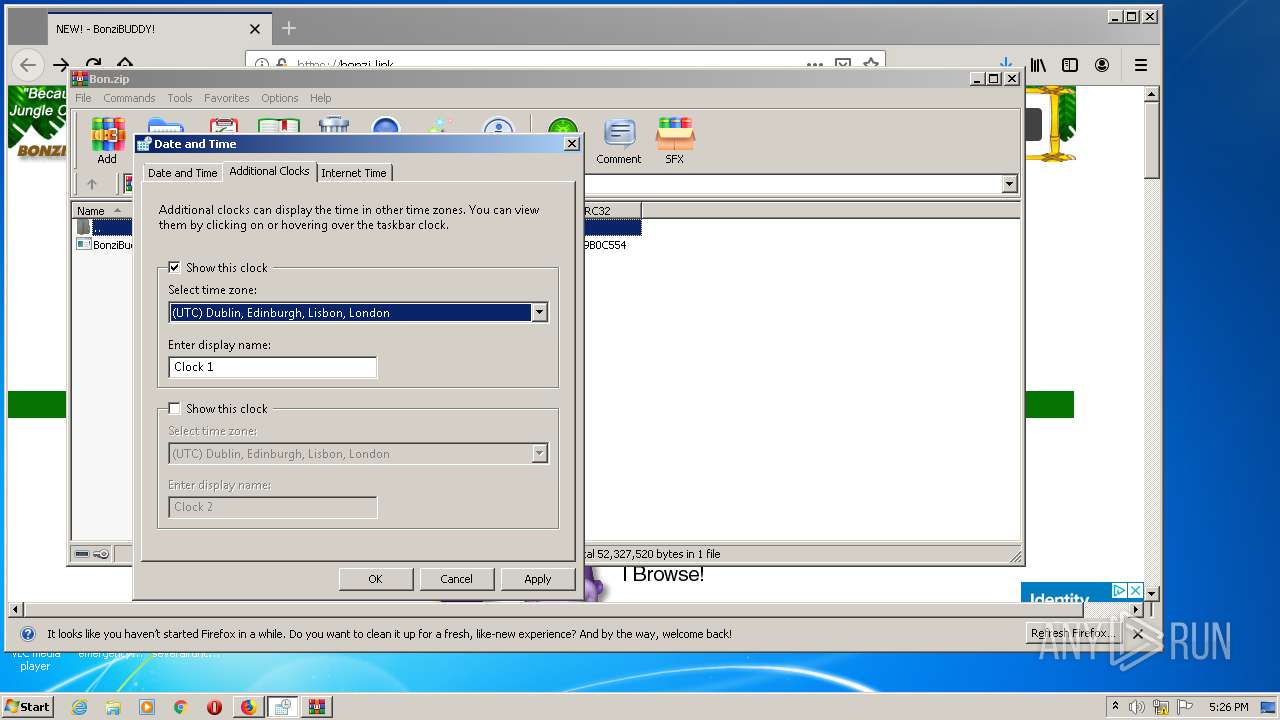
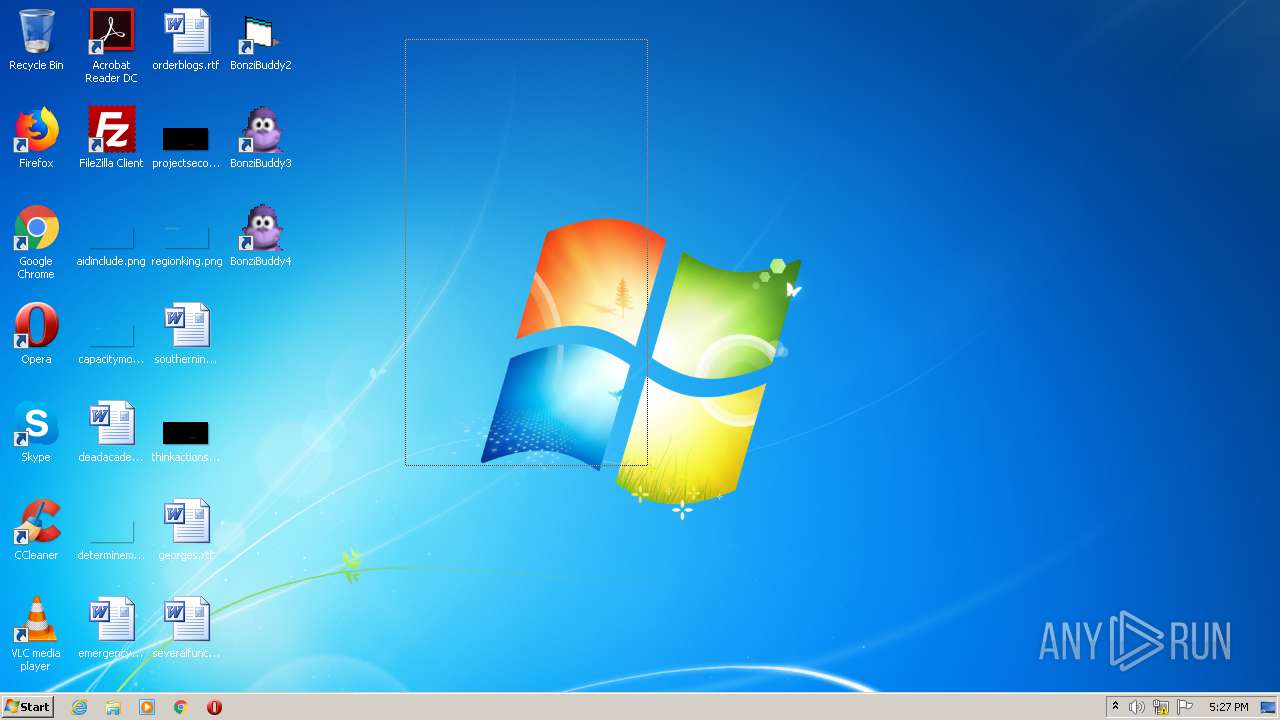
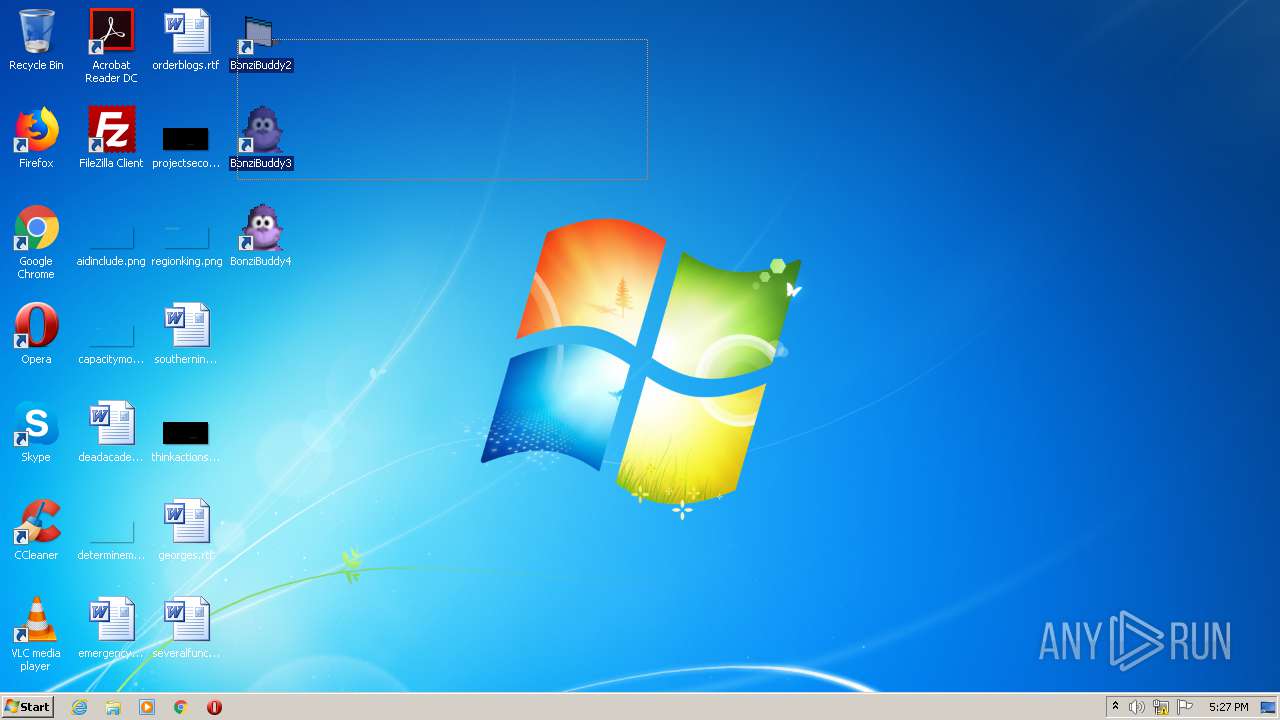
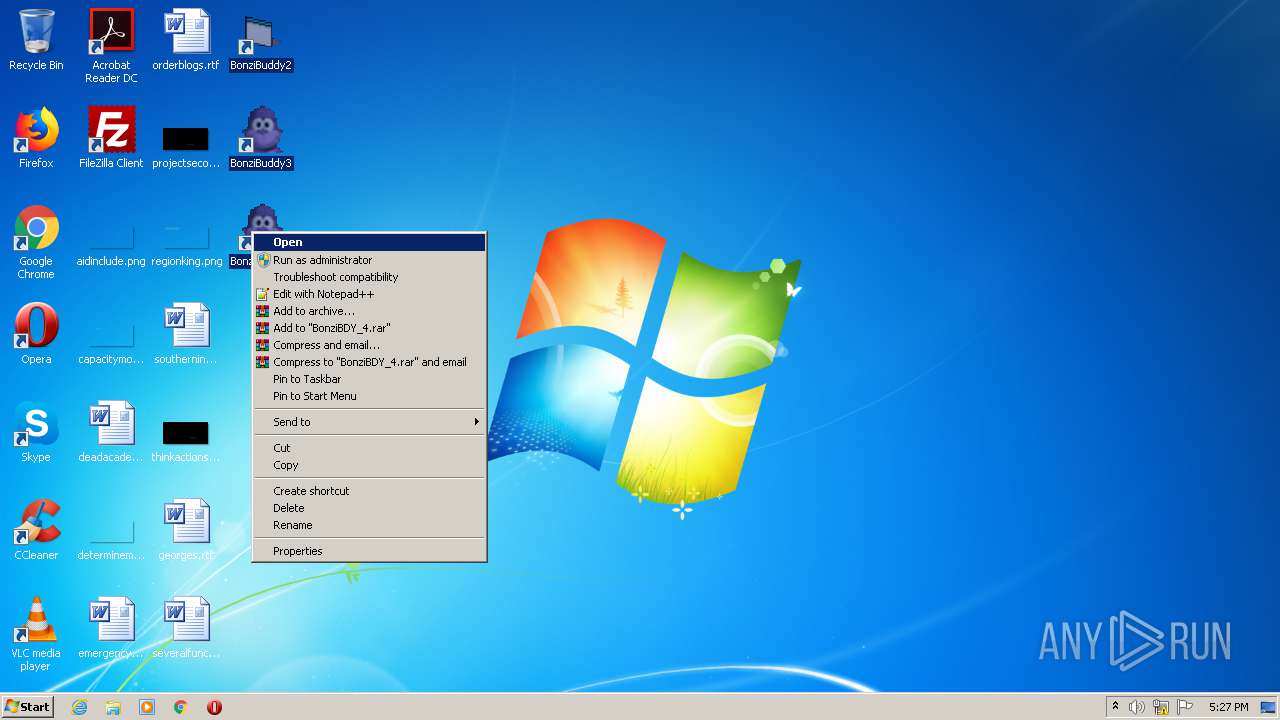
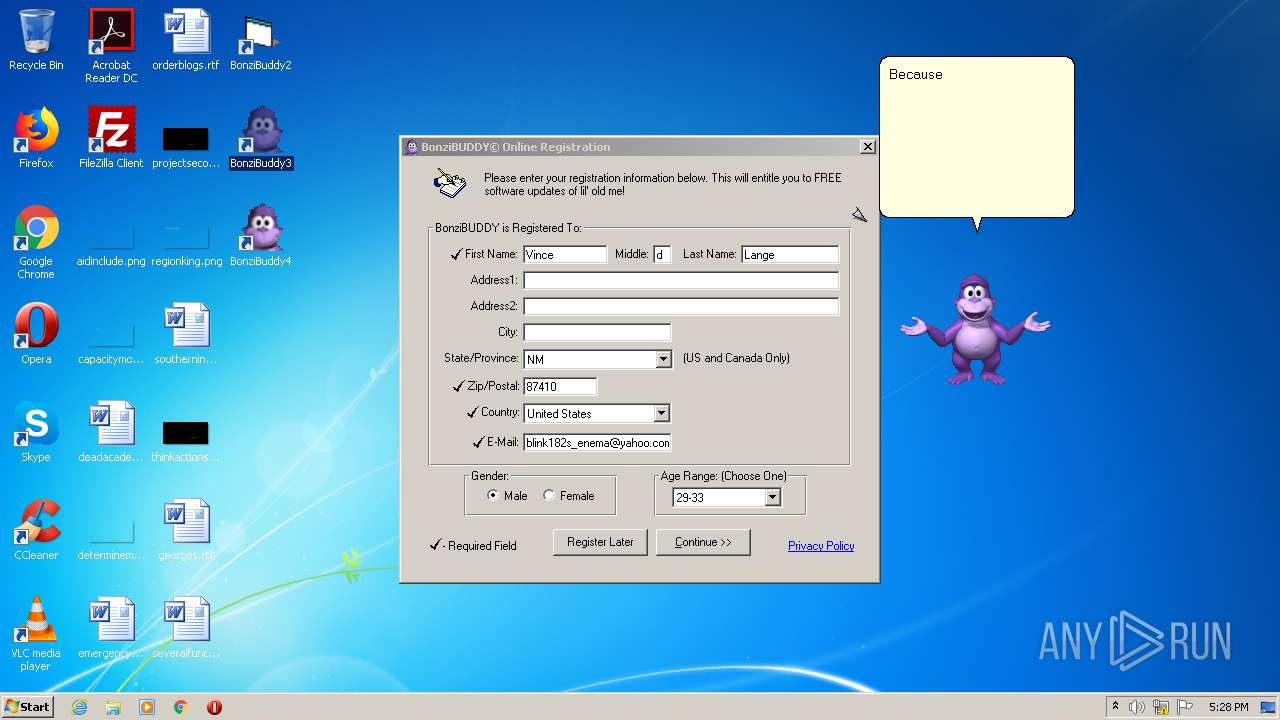
Manual execution by user
- control.exe (PID: 2964)
- BonziBDY_4.EXE (PID: 3804)
- BonziBDY_2.EXE (PID: 3972)
- BonziBDY_35.EXE (PID: 2404)
Creates files in the user directory
- firefox.exe (PID: 3748)
- iexplore.exe (PID: 3600)
Changes internet zones settings
- iexplore.exe (PID: 3776)
Reads settings of System Certificates
- iexplore.exe (PID: 3600)
- iexplore.exe (PID: 3776)
Changes settings of System certificates
- iexplore.exe (PID: 3600)
- pingsender.exe (PID: 1352)
- pingsender.exe (PID: 2420)
- iexplore.exe (PID: 3776)
Adds / modifies Windows certificates
- pingsender.exe (PID: 1352)
- iexplore.exe (PID: 3600)
- pingsender.exe (PID: 2420)
- iexplore.exe (PID: 3776)
Reads internet explorer settings
- iexplore.exe (PID: 3600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
96
Monitored processes
39
Malicious processes
11
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 556 | "C:\Windows\msagent\AgentSvr.exe" /regserver | C:\Windows\msagent\AgentSvr.exe | — | MSAGENT.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Agent Server Exit code: 0 Version: 2.00.0.2202 Modules
| |||||||||||||||
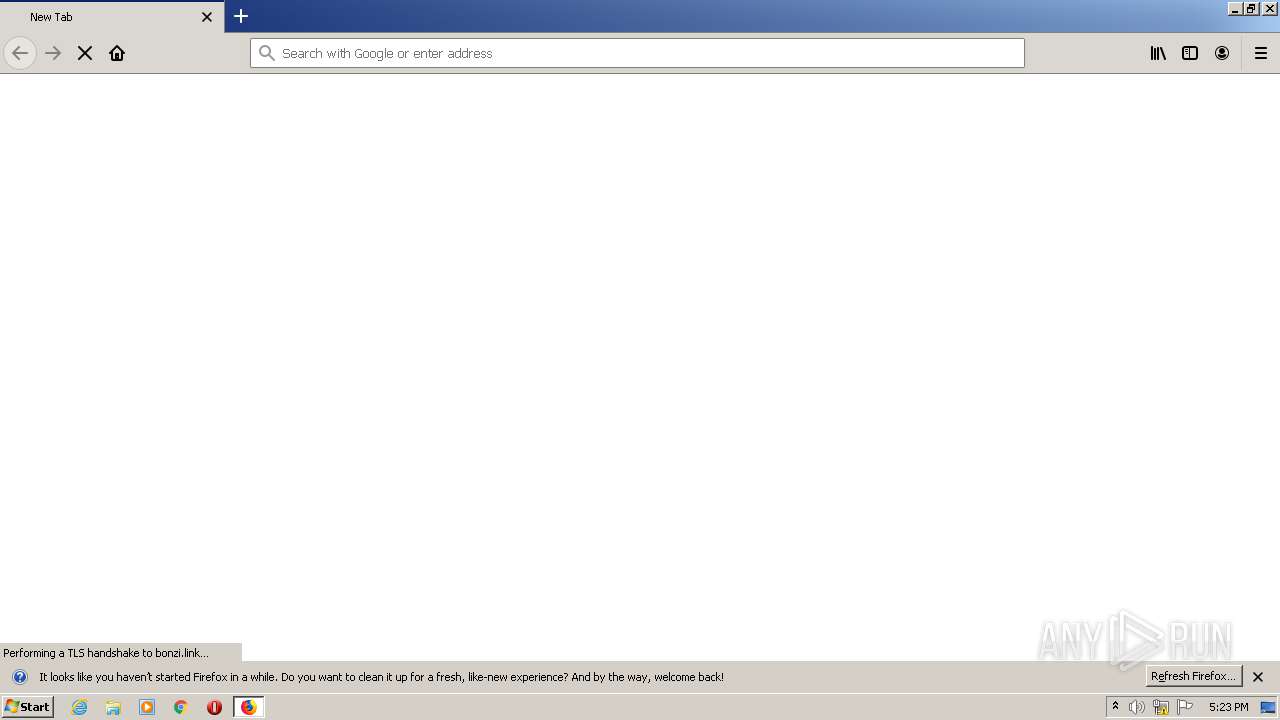
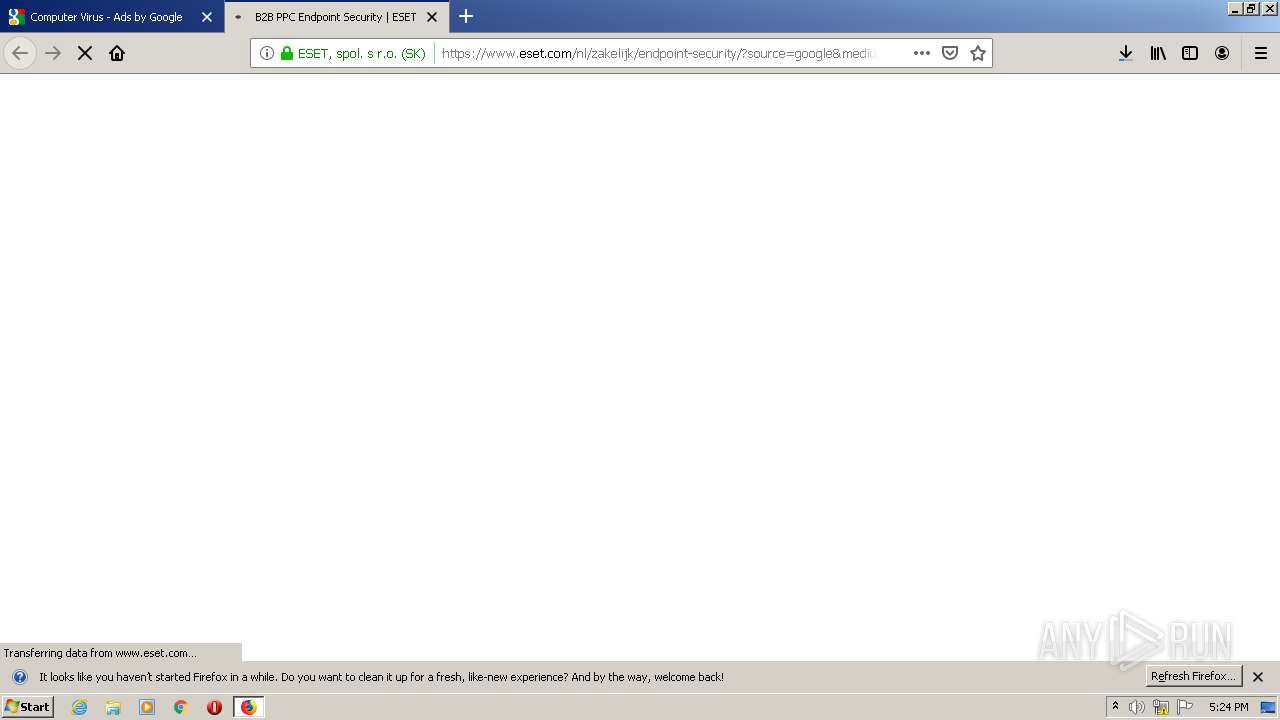
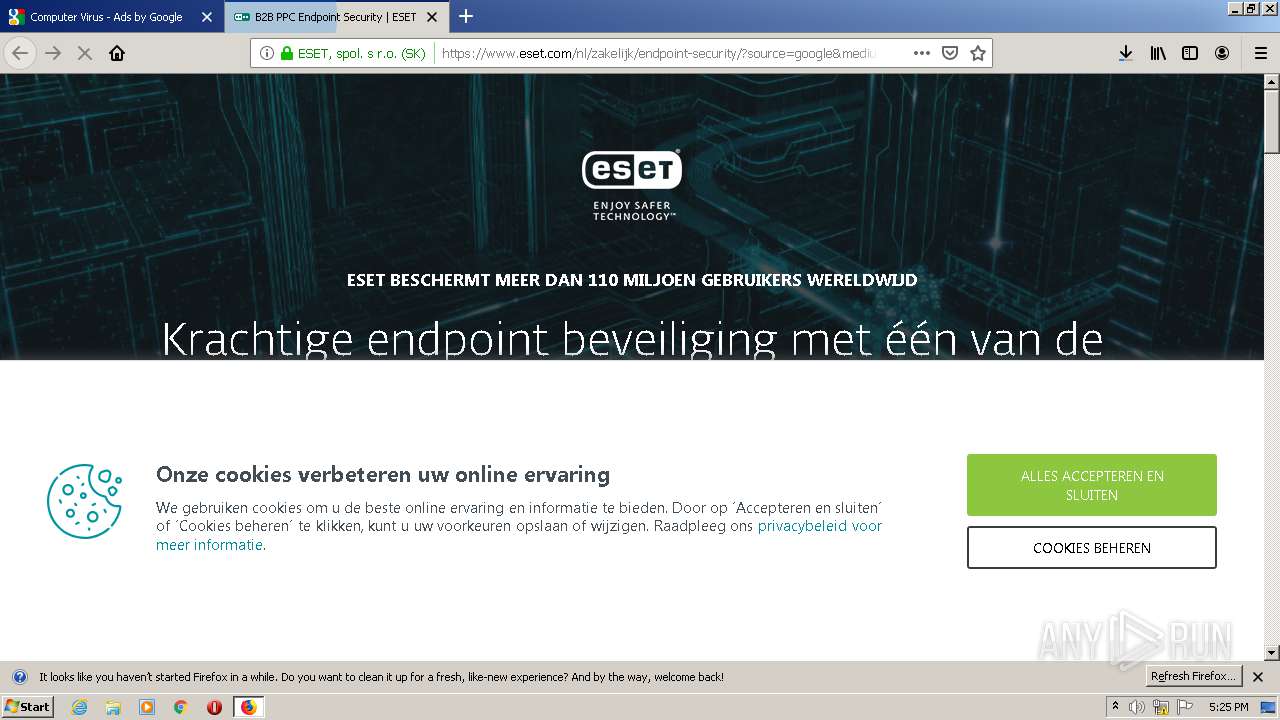
| 840 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://bonzi.link/" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 848 | C:\Windows\msagent\AgentSvr.exe -Embedding | C:\Windows\msagent\AgentSvr.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Agent Server Exit code: 0 Version: 2.00.0.2202 Modules
| |||||||||||||||
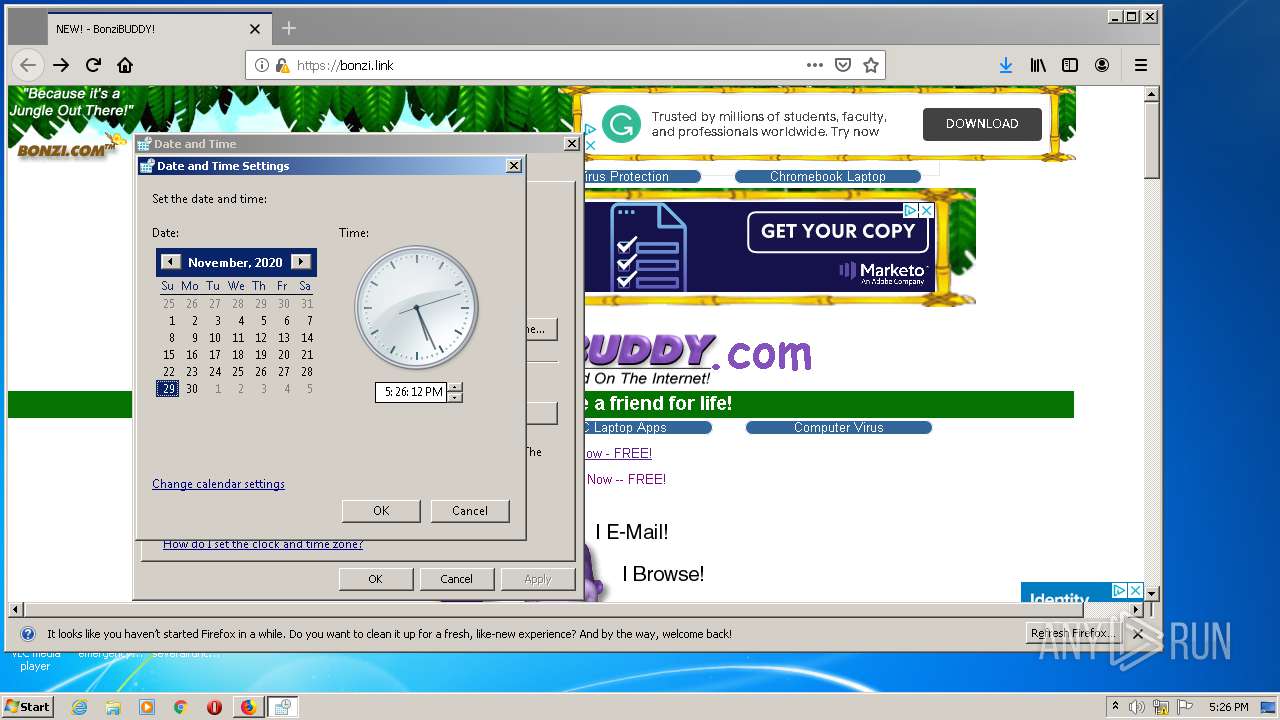
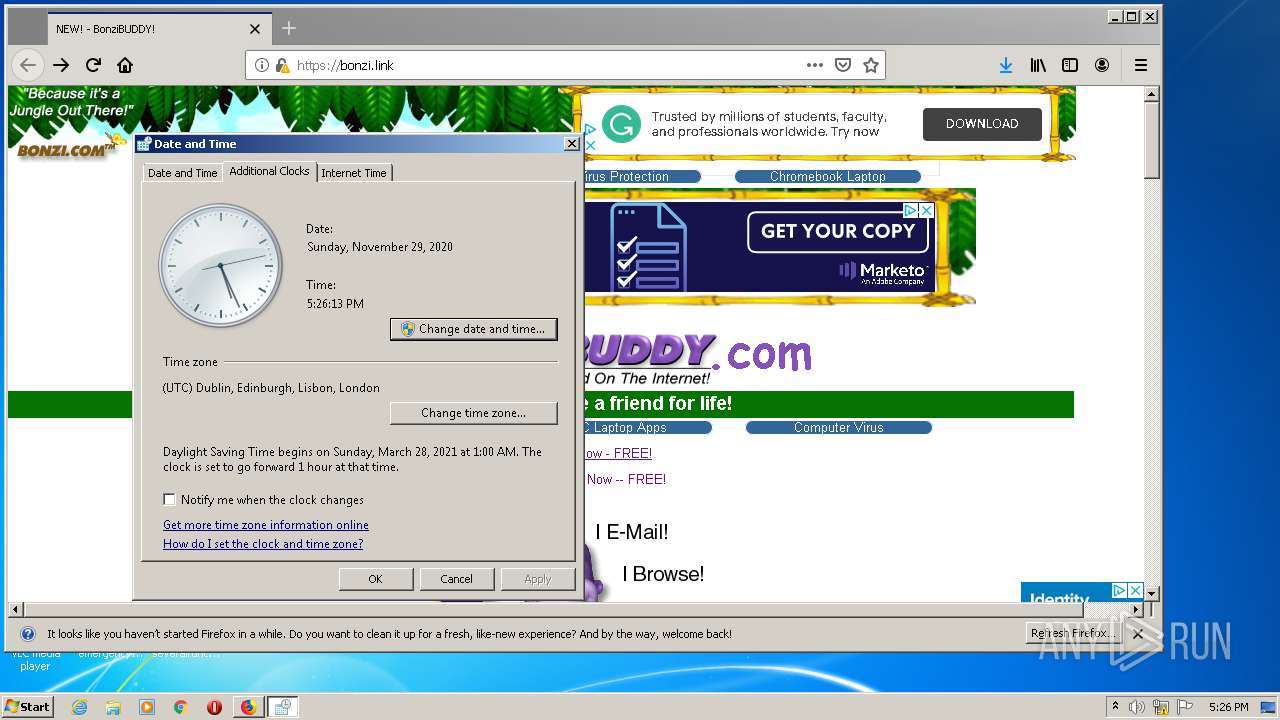
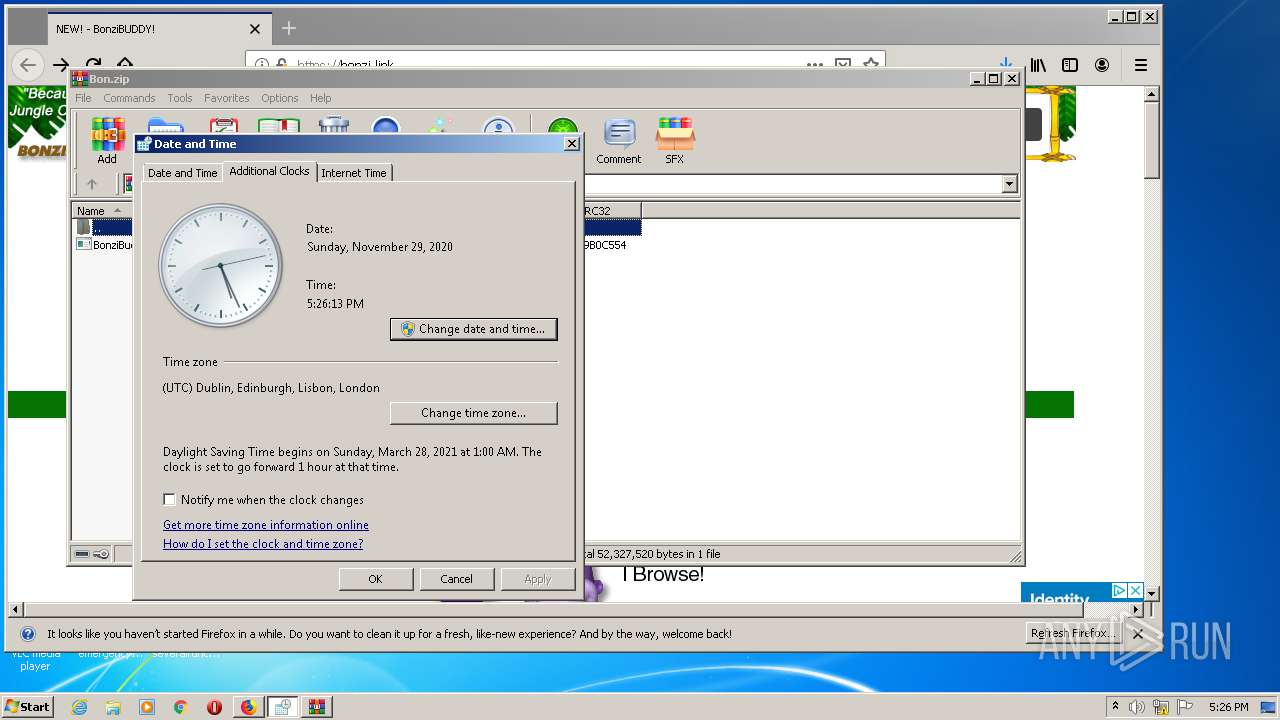
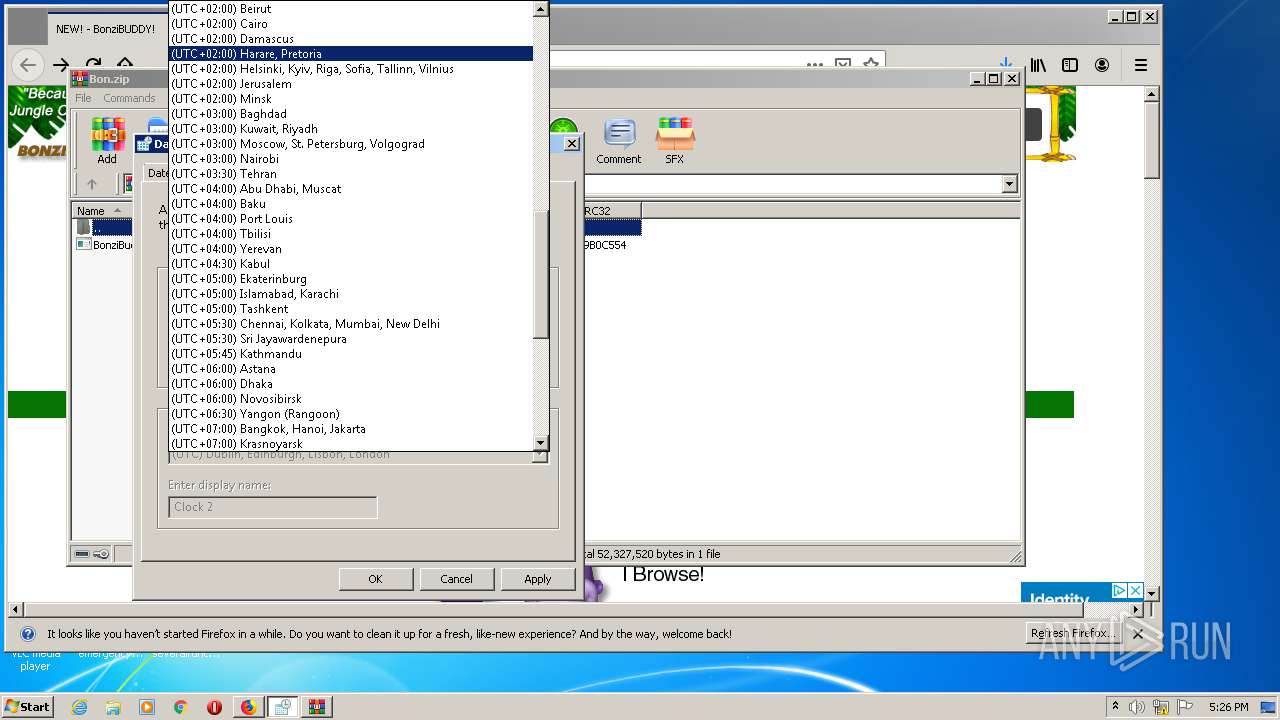
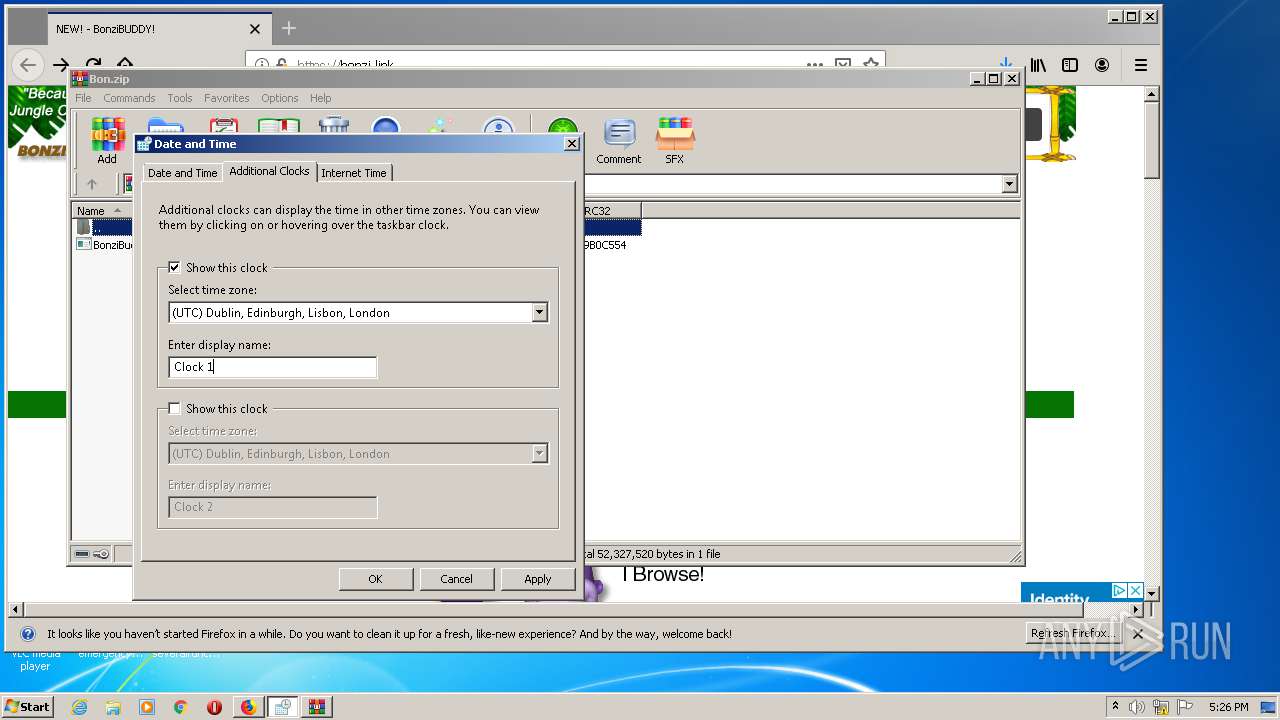
| 1084 | "C:\Windows\system32\rundll32.exe" Shell32.dll,Control_RunDLL "C:\Windows\system32\timedate.cpl", | C:\Windows\system32\rundll32.exe | — | control.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
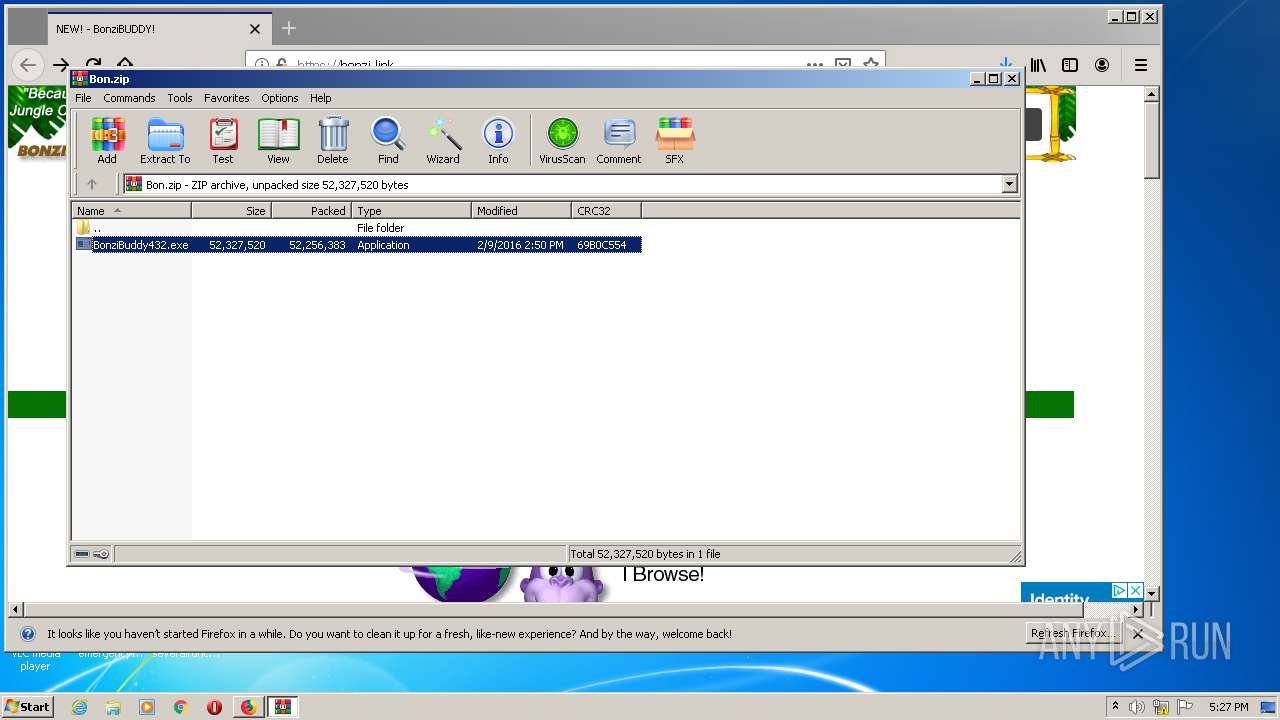
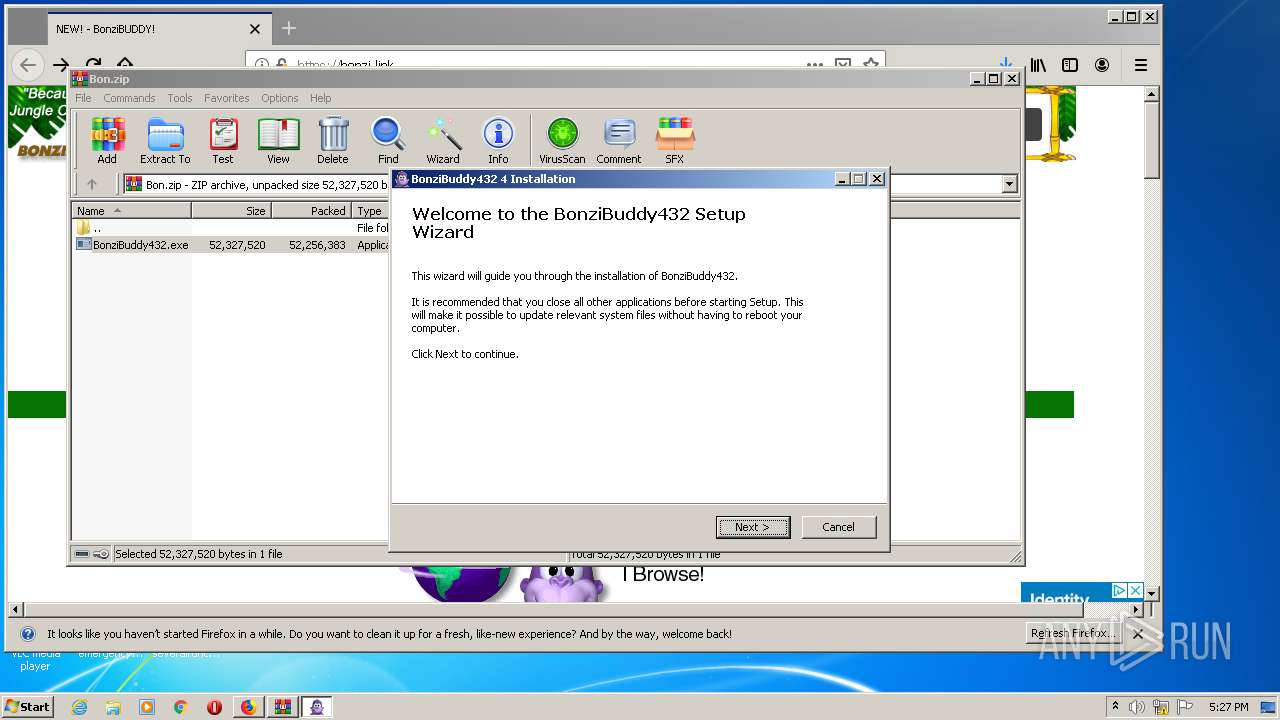
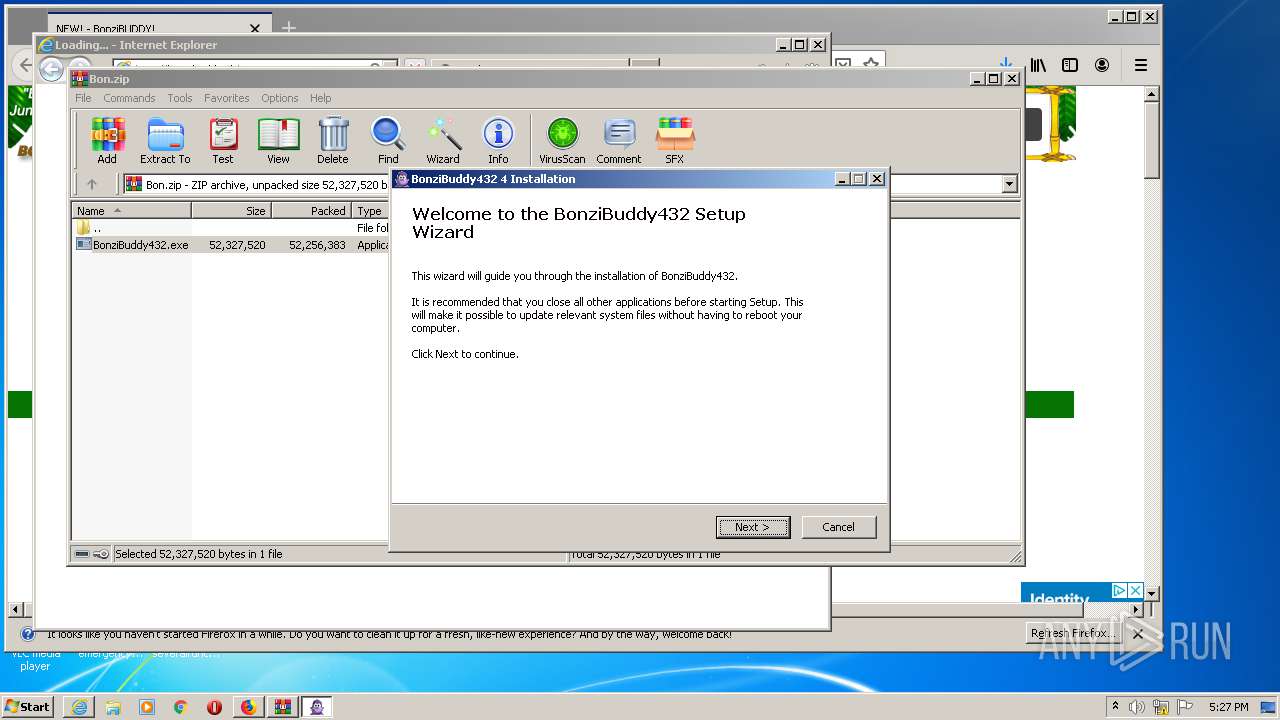
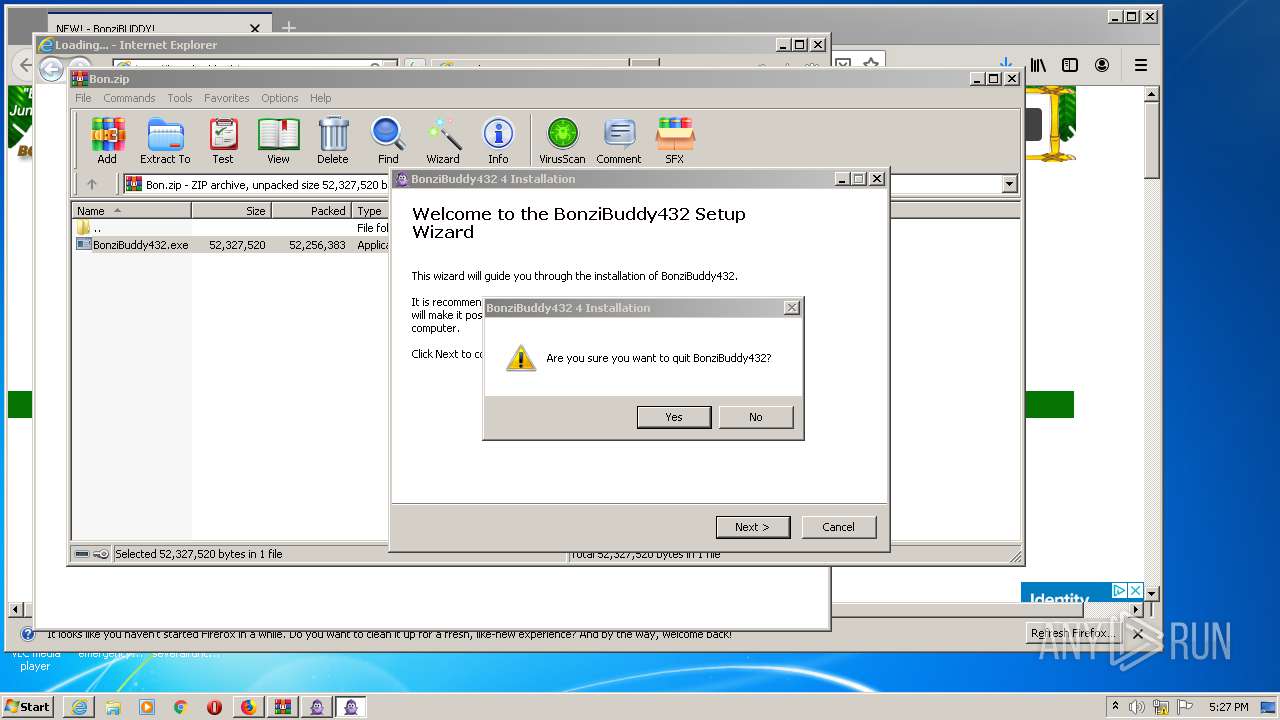
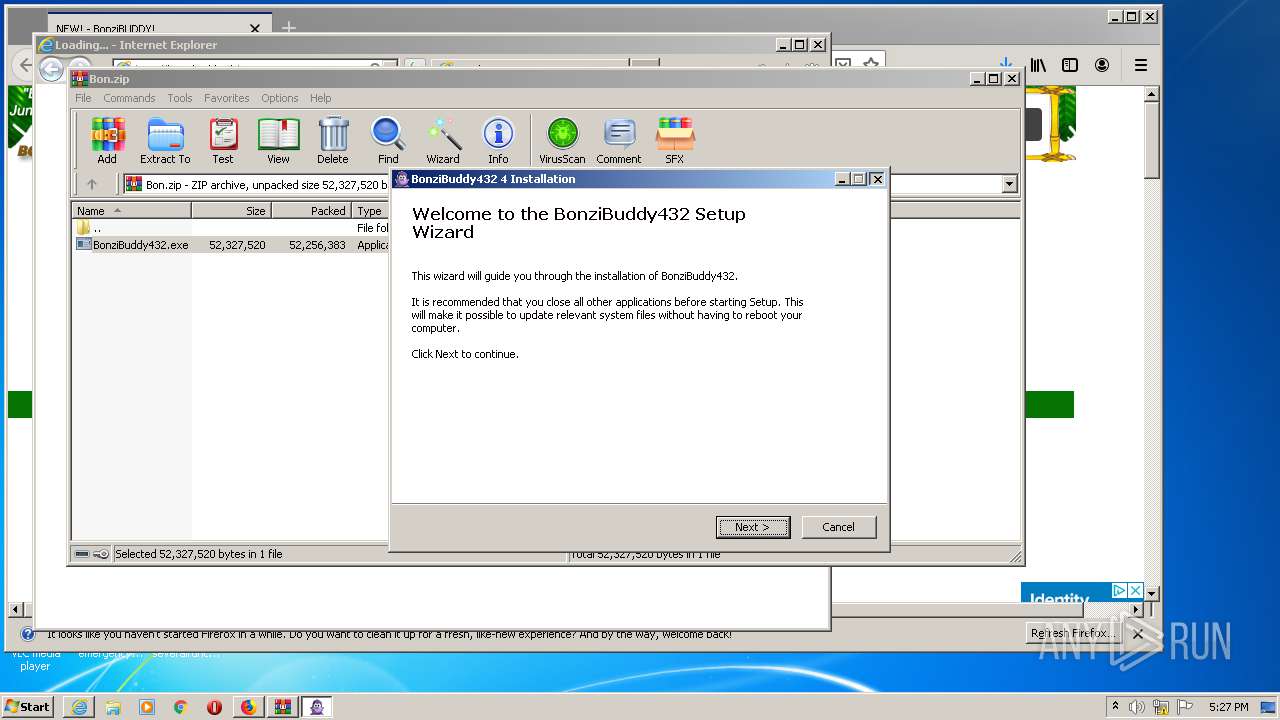
| 1124 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3664.17627\BonziBuddy432.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3664.17627\BonziBuddy432.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Bonzi Software Integrity Level: MEDIUM Description: BonziBuddy432 4 Installation Exit code: 3221226540 Version: 4 Modules
| |||||||||||||||
| 1352 | "C:\Program Files\Mozilla Firefox\pingsender.exe" https://incoming.telemetry.mozilla.org/submit/telemetry/b4ce1758-152c-4d02-bf98-71c07122648a/main/Firefox/68.0.1/release/20190717172542?v=4 C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\saved-telemetry-pings\b4ce1758-152c-4d02-bf98-71c07122648a | C:\Program Files\Mozilla Firefox\pingsender.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1932 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3664.17472\BonziBuddy432.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3664.17472\BonziBuddy432.exe | WinRAR.exe | ||||||||||||
User: admin Company: Bonzi Software Integrity Level: HIGH Description: BonziBuddy432 4 Installation Exit code: 0 Version: 4 Modules
| |||||||||||||||
| 2104 | C:\Windows\system32\DllHost.exe /Processid:{9DF523B0-A6C0-4EA9-B5F1-F4565C3AC8B8} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2180 | regsvr32 /s "C:\Windows\msagent\AgentPsh.dll" | C:\Windows\system32\regsvr32.exe | — | MSAGENT.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2376 | regsvr32 /s C:\Windows\lhsp\tv\tvenuax.dll | C:\Windows\system32\regsvr32.exe | — | tv_enua.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 270
Read events
3 199
Write events
1 999
Delete events
72
Modification events
| (PID) Process: | (840) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 8B6C7B0300000000 | |||
| (PID) Process: | (3748) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 8B6C7B0300000000 | |||
| (PID) Process: | (3748) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (3748) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3748) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2964) control.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2964) control.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3748) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3748) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3748) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithProgids |
| Operation: | write | Name: | WinRAR.ZIP |
Value: | |||
Executable files
68
Suspicious files
388
Text files
326
Unknown types
171
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3748 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3748 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3748 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 3748 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3748 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3748 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3748 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3748 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:— | SHA256:— | |||
| 3748 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.sbstore | binary | |
MD5:— | SHA256:— | |||
| 3748 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
58
TCP/UDP connections
108
DNS requests
195
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3748 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3748 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3748 | firefox.exe | POST | 200 | 143.204.214.142:80 | http://ocsp.sca1b.amazontrust.com/ | US | der | 471 b | whitelisted |
3748 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3748 | firefox.exe | POST | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/ | US | der | 471 b | whitelisted |
3748 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3748 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3748 | firefox.exe | POST | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1o1core | US | der | 472 b | whitelisted |
3748 | firefox.exe | POST | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1o1core | US | der | 472 b | whitelisted |
3748 | firefox.exe | POST | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1o1core | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3748 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | — | US | whitelisted |
3748 | firefox.exe | 34.218.9.172:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
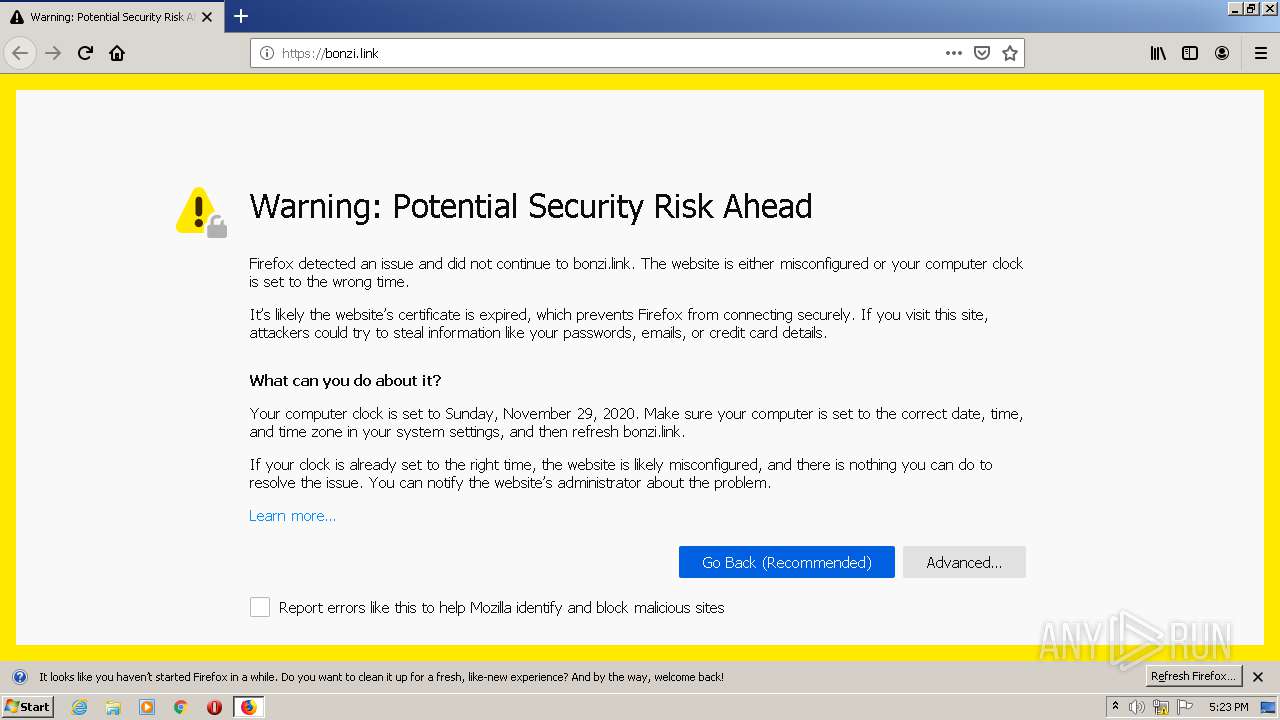
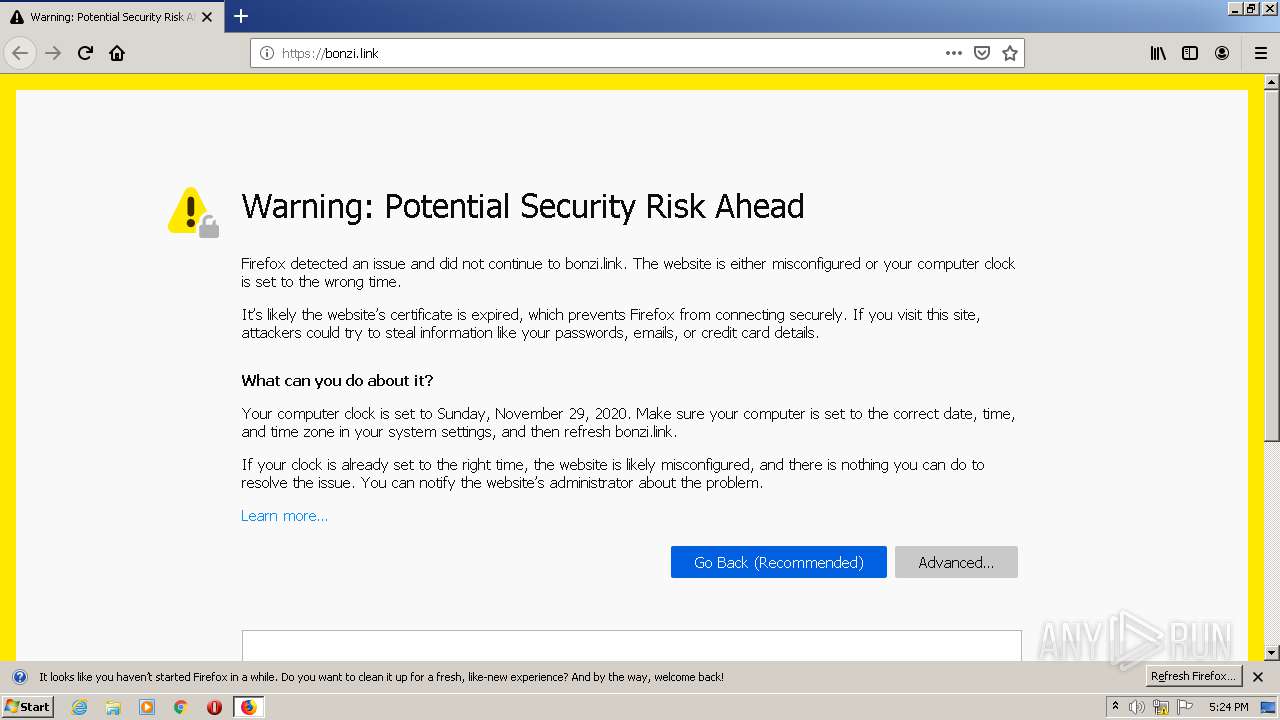
— | — | 45.58.34.146:443 | bonzi.link | Atlantic.net, Inc. | US | suspicious |
3748 | firefox.exe | 65.9.68.17:443 | snippets.cdn.mozilla.net | AT&T Services, Inc. | US | unknown |
3748 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3748 | firefox.exe | 172.217.16.202:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3748 | firefox.exe | 65.9.68.64:443 | firefox.settings.services.mozilla.com | AT&T Services, Inc. | US | suspicious |
3748 | firefox.exe | 216.58.212.163:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3748 | firefox.exe | 65.9.68.11:443 | content-signature-2.cdn.mozilla.net | AT&T Services, Inc. | US | suspicious |
3748 | firefox.exe | 54.186.24.65:443 | shavar.services.mozilla.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bonzi.link |
| suspicious |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
d228z91au11ukj.cloudfront.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
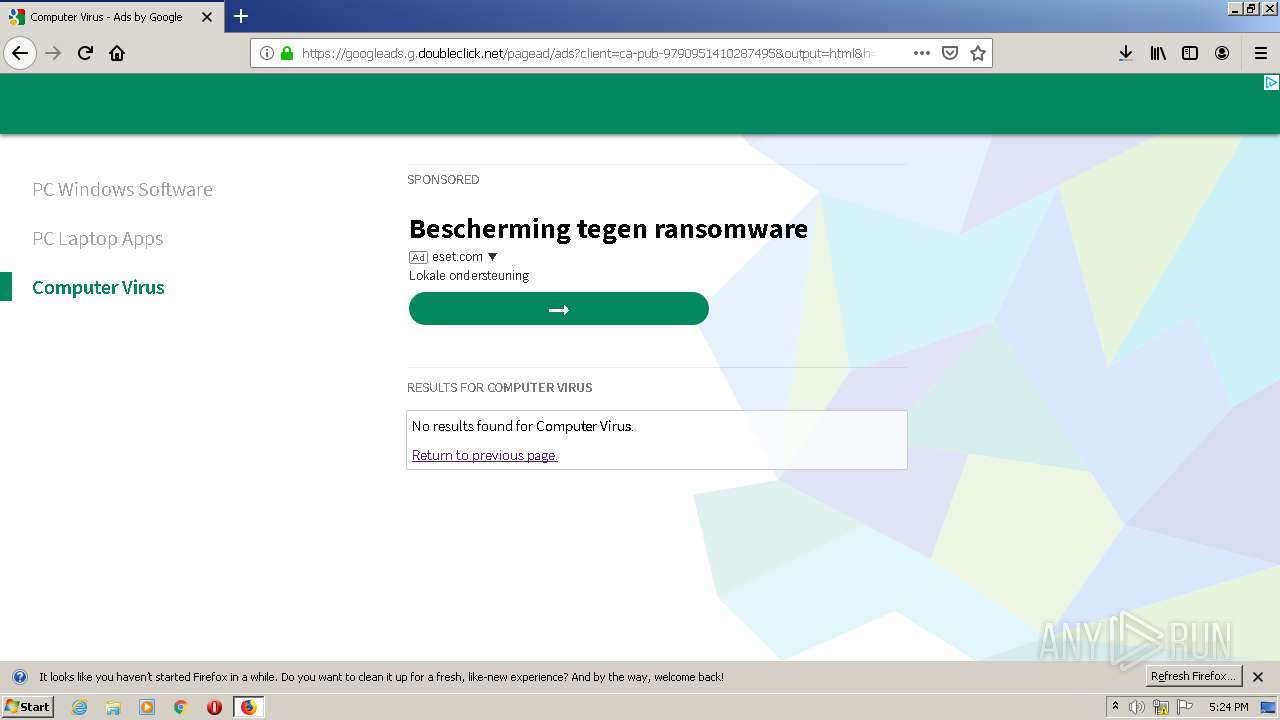
1056 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1056 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
3600 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
3600 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
3600 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
3600 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
3600 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
3600 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
Process | Message |
|---|---|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|