| File name: | Downloader.apk |
| Full analysis: | https://app.any.run/tasks/d23dc7ce-4d37-49ae-bcad-56439f909871 |
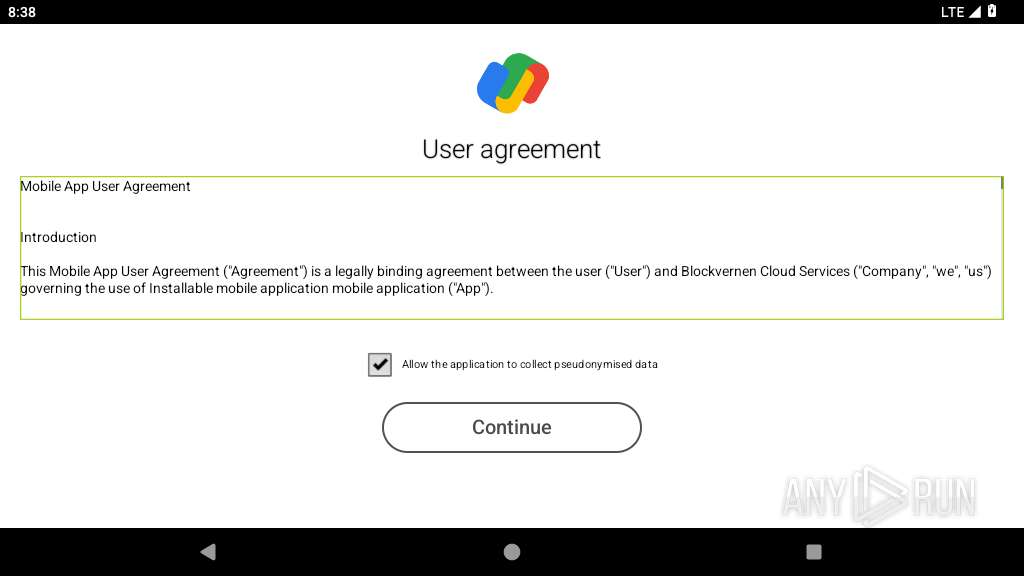
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2025, 08:38:10 |
| OS: | Android 14 |
| MIME: | application/vnd.android.package-archive |
| File info: | Android package (APK), with gradle app-metadata.properties, with APK Signing Block |
| MD5: | C6571506C0CDDA31B12540708102D88C |
| SHA1: | A3549B9201627582C098F8326B6714676E215D2A |
| SHA256: | E9E05F26262B565684D521FCC726C3B4C0907B33BA34DBD5C9A4212832019010 |
| SSDEEP: | 98304:SZsHXLGWNJOTBRog0FPP7zZKOkvN5jBIdHvS8/COyqc1iurm4EKd0RJ94Xj08Iis:yCnf |
MALICIOUS
No malicious indicators.SUSPICIOUS
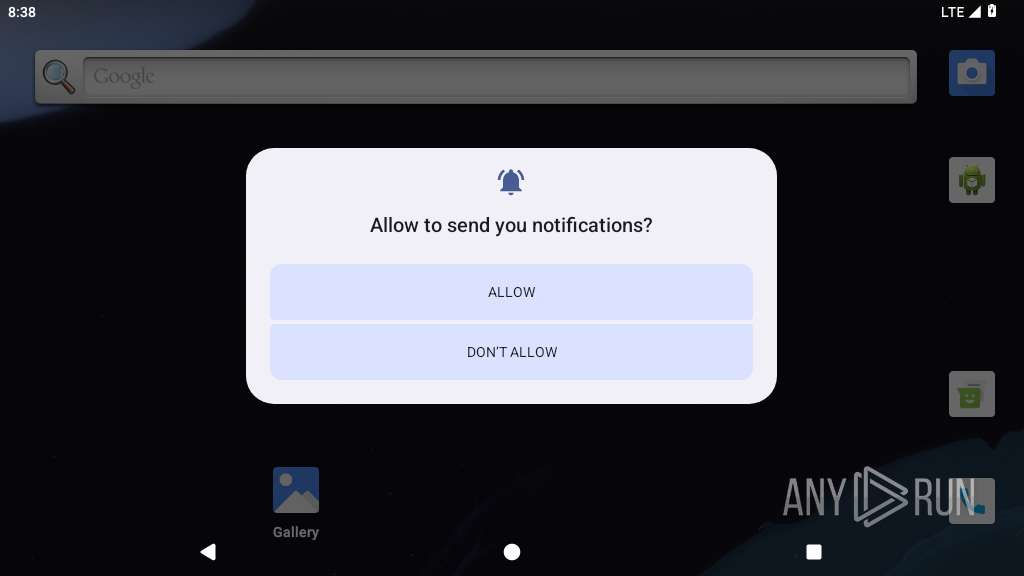
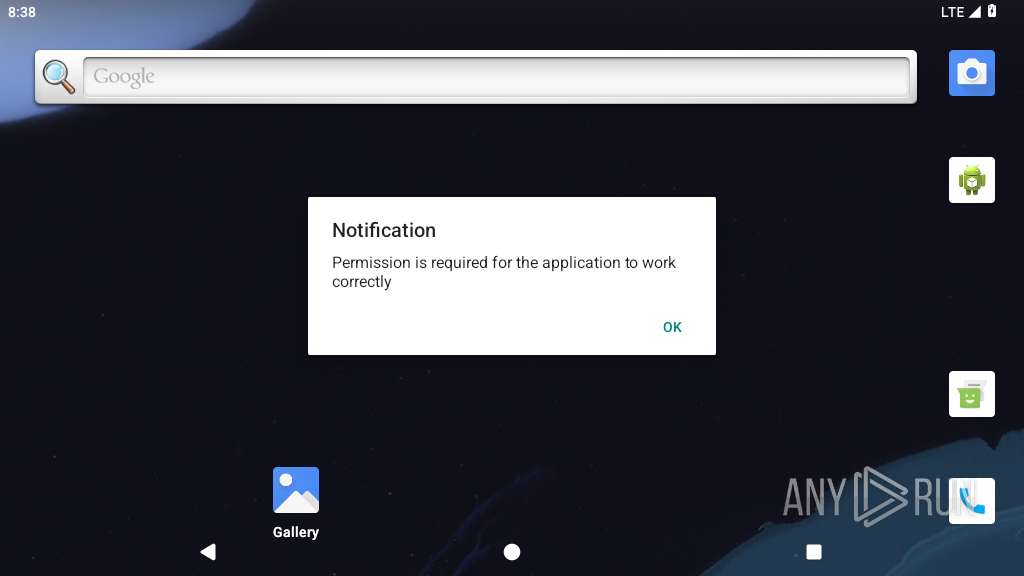
Abuses foreground service for persistence
- app_process64 (PID: 2231)
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 2231)
Establishing a connection
- app_process64 (PID: 2231)
Activates a regular task at set intervals
- app_process64 (PID: 2231)
Retrieves the ISO country code of the current SIM card
- app_process64 (PID: 2231)
Retrieves the ISO country code of the current network
- app_process64 (PID: 2231)
Retrieves the MCC and MNC of the SIM card operator
- app_process64 (PID: 2231)
Returns the name of the current network operator
- app_process64 (PID: 2231)
INFO
Dynamically inspects or modifies classes, methods, and fields at runtime
- app_process64 (PID: 2231)
Retrieves the value of a secure system setting
- app_process64 (PID: 2231)
Handles throwable exceptions in the app
- app_process64 (PID: 2231)
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 2231)
Returns elapsed time since boot
- app_process64 (PID: 2231)
Verifies whether the device is connected to the internet
- app_process64 (PID: 2231)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .jar | | | Java Archive (78.3) |
|---|---|---|
| .zip | | | ZIP compressed archive (21.6) |
EXIF
ZIP
| ZipRequiredVersion: | - |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1981:01:01 01:01:02 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 2 |
| ZipUncompressedSize: | - |
| ZipFileName: | META-INF/com/android/build/gradle/app-metadata.properties |
Total processes
130
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
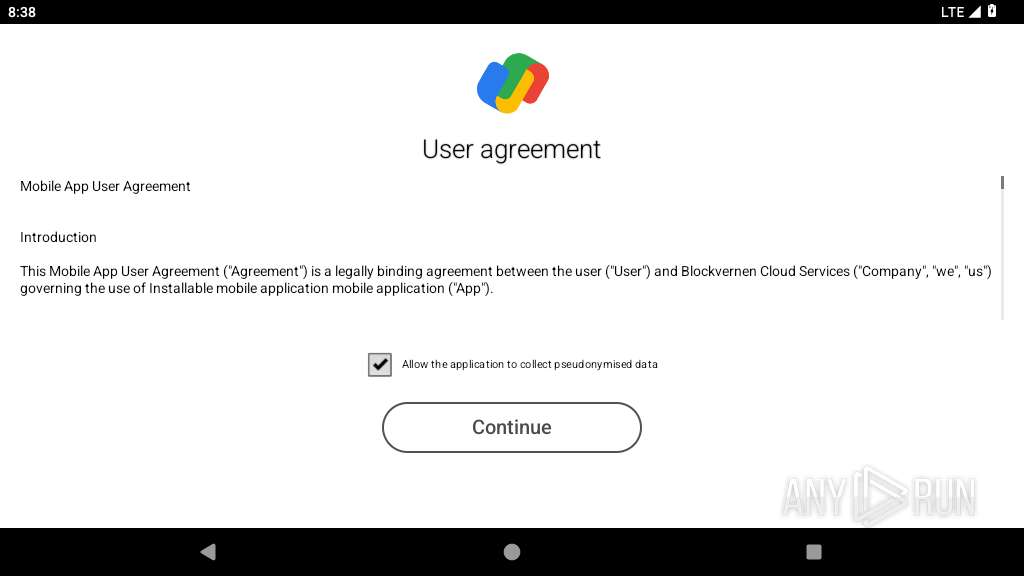
| 2231 | com.tuneonn.bhoot | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2264 | zygote | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2278 | webview_zygote | /system/bin/app_process32 | — | app_process32 |
User: webview_zygote Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2315 | zygote | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2383 | /apex/com.android.art/bin/artd | /apex/com.android.art/bin/artd | — | init |
User: artd Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
25
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2231 | app_process64 | /data/data/com.tuneonn.bhoot/files/df736951.dex | compressed | |
MD5:— | SHA256:— | |||
| 2231 | app_process64 | /data/data/com.tuneonn.bhoot/shared_prefs/FirebaseHeartBeatW0RFRkFVTFRd+MTozODA5MjQyMjU5NDQ6YW5kcm9pZDphYmE1NDM4ODI4ZjUzZjg4YWVhM2Vk.xml | xml | |
MD5:— | SHA256:— | |||
| 2231 | app_process64 | /data/data/com.tuneonn.bhoot/shared_prefs/com.google.firebase.messaging.xml | xml | |
MD5:— | SHA256:— | |||
| 2231 | app_process64 | /data/data/com.tuneonn.bhoot/shared_prefs/WebViewChromiumPrefs.xml | xml | |
MD5:— | SHA256:— | |||
| 2231 | app_process64 | /data/data/com.tuneonn.bhoot/cache/oat_primary/arm64/base.2231.tmp | binary | |
MD5:— | SHA256:— | |||
| 2231 | app_process64 | /data/data/com.tuneonn.bhoot/app_webview/Default/Local Storage/leveldb/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
| 2231 | app_process64 | /data/data/com.tuneonn.bhoot/app_webview/Default/Local Storage/leveldb/000001.dbtmp | text | |
MD5:— | SHA256:— | |||
| 2231 | app_process64 | /data/data/com.tuneonn.bhoot/app_webview/Default/Local Storage/leveldb/CURRENT | text | |
MD5:— | SHA256:— | |||
| 2231 | app_process64 | /data/data/com.tuneonn.bhoot/cache/WebView/Default/HTTP Cache/Code Cache/webui_js/index | binary | |
MD5:— | SHA256:— | |||
| 2231 | app_process64 | /data/data/com.tuneonn.bhoot/cache/WebView/Default/HTTP Cache/Code Cache/js/index | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
33
DNS requests
5
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 216.58.214.3:80 | http://connectivitycheck.gstatic.com/generate_204 | unknown | — | — | whitelisted |
2231 | app_process64 | GET | 200 | 49.13.235.100:80 | http://g3.shannksara.com//client.config/?app=pndr2&format=json&advert_key=ZWMwMDBhMDgxZjAwM2FlOTAwMDAzYWY4MDAzYWY4MDAzYWY4YmM2ZGE1MDY0ZA==&uid=ACD047AD546EEB0CAE5B55450ACCD802-227E6507B973595C146C379EFE78A7920634FB57&version=53.1&pckg=com.tuneonn.bhoot&ia=14&im=asus&id=ROG_Phone&did=2aff6733-4418-11ef-b781-d05099ffbb50&p1=_&ddate=1721163600&rlid=12676&refLink=&gateId=2a94a2c6-4418-11ef-99eb-a2337ba73149&net_type=914&net_id=cqbo6pck1vbs73ef9e7g&sp_time=10&ne=1&network_operator=Verizon&phone_type=gsm&sim_operator=Verizon&network_vpn=&sim_iso=us&networks=dummy0;lo;buried_eth0&network_type=MOBILE&network_iso=us&pndr_install=1 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
447 | mdnsd | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 8.8.8.8:443 | — | — | — | malicious |
— | — | 216.239.35.0:123 | time.android.com | — | — | whitelisted |
— | — | 142.251.36.4:443 | www.google.com | GOOGLE | US | whitelisted |
— | — | 216.58.214.3:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
— | — | 8.8.8.8:853 | — | GOOGLE | US | malicious |
— | — | 142.250.102.81:443 | staging-remoteprovisioning.sandbox.googleapis.com | GOOGLE | US | whitelisted |
575 | app_process64 | 216.239.35.12:123 | time.android.com | — | — | whitelisted |
575 | app_process64 | 216.239.35.4:123 | time.android.com | — | — | whitelisted |
2264 | app_process32 | 172.217.23.195:443 | — | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| whitelisted |
connectivitycheck.gstatic.com |
| whitelisted |
time.android.com |
| whitelisted |
staging-remoteprovisioning.sandbox.googleapis.com |
| whitelisted |
vtRo3E-dnsotls-ds.metric.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Android Device Connectivity Check |