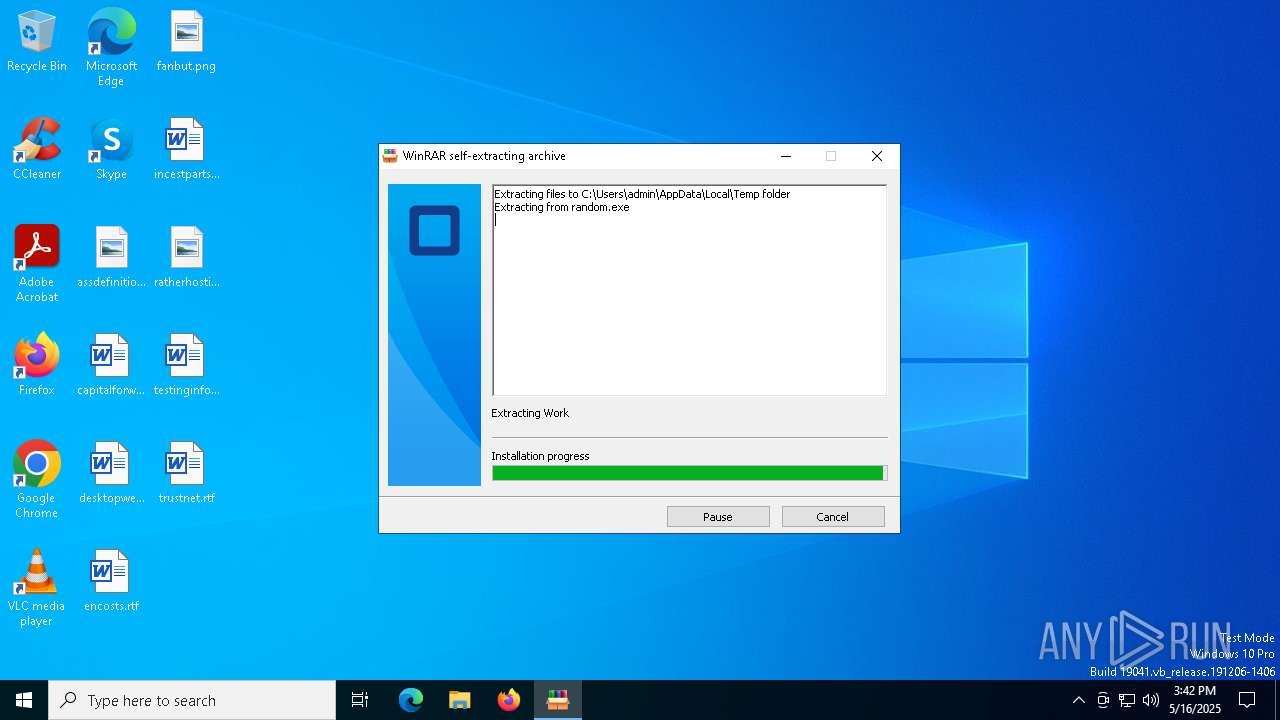
| File name: | random.exe |
| Full analysis: | https://app.any.run/tasks/93aedb64-cc6e-4bb1-8d5d-40d6cbcafaab |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 15:42:01 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 5ADE7DB3148345AE21825DC6430DC087 |
| SHA1: | 6DEBAB245E89951EDD0806842F4514FA8EEBD8B6 |
| SHA256: | E9DD7565EBD5C2CC874083A1C59D7710EB66557CB1B1DCCAC13F7415361848D9 |
| SSDEEP: | 98304:Oyi35vcoKogj0YjbdDXayrZryYCUVUZ/f9Mj2tikcazgDoY0291uQ4+zqkUxSd2W:4gBkza9 |
MALICIOUS
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 7148)
- NSudoLG.exe (PID: 5548)
Changes Windows Defender settings
- NSudoLG.exe (PID: 5548)
Starts SC.EXE for service management
- cmd.exe (PID: 7148)
SUSPICIOUS
Starts application with an unusual extension
- cmd.exe (PID: 672)
- cmd.exe (PID: 1760)
- cmd.exe (PID: 7148)
Drops 7-zip archiver for unpacking
- random.exe (PID: 1276)
The process creates files with name similar to system file names
- random.exe (PID: 1276)
Executable content was dropped or overwritten
- random.exe (PID: 1276)
- 7z.exe (PID: 1188)
- Unlocker.exe (PID: 5868)
- cmd.exe (PID: 7148)
Reads security settings of Internet Explorer
- random.exe (PID: 1276)
- nircmd.exe (PID: 4400)
- Unlocker.exe (PID: 5384)
- Unlocker.exe (PID: 5868)
- Unlocker.exe (PID: 7780)
Starts CMD.EXE for commands execution
- random.exe (PID: 1276)
- nircmd.exe (PID: 4400)
- cmd.exe (PID: 1188)
- NSudoLG.exe (PID: 6436)
- cmd.exe (PID: 6808)
- cmd.exe (PID: 7148)
- Unlocker.exe (PID: 5384)
- cmd.exe (PID: 6964)
- Unlocker.exe (PID: 5868)
- Unlocker.exe (PID: 7780)
The executable file from the user directory is run by the CMD process
- nircmd.exe (PID: 4400)
- NSudoLG.exe (PID: 6436)
- NSudoLG.exe (PID: 5548)
- 7z.exe (PID: 1188)
- Unlocker.exe (PID: 5384)
- Unlocker.exe (PID: 7780)
- Unlocker.exe (PID: 5868)
Executing commands from a ".bat" file
- nircmd.exe (PID: 4400)
- cmd.exe (PID: 1188)
- NSudoLG.exe (PID: 6436)
- cmd.exe (PID: 6808)
- random.exe (PID: 1276)
- cmd.exe (PID: 6964)
Reads the date of Windows installation
- nircmd.exe (PID: 4400)
- Unlocker.exe (PID: 5384)
- Unlocker.exe (PID: 5868)
- Unlocker.exe (PID: 7780)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 1760)
- cmd.exe (PID: 7148)
Application launched itself
- cmd.exe (PID: 1188)
- cmd.exe (PID: 6808)
- cmd.exe (PID: 7148)
- cmd.exe (PID: 6964)
Get information on the list of running processes
- cmd.exe (PID: 7148)
- cmd.exe (PID: 2320)
Script adds exclusion path to Windows Defender
- NSudoLG.exe (PID: 5548)
PowerShell delay command usage (probably sleep evasion)
- powershell.exe (PID: 2564)
Starts POWERSHELL.EXE for commands execution
- NSudoLG.exe (PID: 5548)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7148)
Windows service management via SC.EXE
- sc.exe (PID: 6576)
- sc.exe (PID: 5936)
- sc.exe (PID: 4208)
- sc.exe (PID: 7020)
- sc.exe (PID: 920)
- sc.exe (PID: 5936)
- sc.exe (PID: 6044)
- sc.exe (PID: 4432)
- sc.exe (PID: 6148)
- sc.exe (PID: 4180)
- sc.exe (PID: 1512)
- sc.exe (PID: 6824)
- sc.exe (PID: 4448)
- sc.exe (PID: 664)
- sc.exe (PID: 6080)
- sc.exe (PID: 904)
- sc.exe (PID: 3272)
- sc.exe (PID: 2692)
- sc.exe (PID: 6248)
- sc.exe (PID: 5512)
- sc.exe (PID: 2616)
- sc.exe (PID: 4868)
- sc.exe (PID: 6272)
- sc.exe (PID: 6040)
- sc.exe (PID: 4652)
- sc.exe (PID: 3156)
- sc.exe (PID: 5260)
- sc.exe (PID: 4172)
- sc.exe (PID: 6592)
- sc.exe (PID: 856)
- sc.exe (PID: 4932)
- sc.exe (PID: 5400)
- sc.exe (PID: 2404)
- sc.exe (PID: 2284)
- sc.exe (PID: 1668)
- sc.exe (PID: 7180)
- sc.exe (PID: 7220)
- sc.exe (PID: 5728)
- sc.exe (PID: 7904)
- sc.exe (PID: 8036)
- sc.exe (PID: 8056)
Starts SC.EXE for service management
- cmd.exe (PID: 5964)
- cmd.exe (PID: 7148)
- cmd.exe (PID: 680)
- cmd.exe (PID: 6132)
- cmd.exe (PID: 7848)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 856)
- cmd.exe (PID: 6708)
- cmd.exe (PID: 7932)
Stops a currently running service
- sc.exe (PID: 5960)
- sc.exe (PID: 3132)
- sc.exe (PID: 2096)
- sc.exe (PID: 2560)
- sc.exe (PID: 5776)
- sc.exe (PID: 736)
- sc.exe (PID: 3676)
- sc.exe (PID: 5680)
- sc.exe (PID: 1096)
- sc.exe (PID: 5352)
- sc.exe (PID: 5244)
- sc.exe (PID: 6944)
- sc.exe (PID: 1324)
- sc.exe (PID: 2564)
- sc.exe (PID: 7200)
- sc.exe (PID: 2316)
- sc.exe (PID: 3240)
Creates or modifies Windows services
- Unlocker.exe (PID: 5868)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 7260)
- schtasks.exe (PID: 7332)
- schtasks.exe (PID: 7284)
- schtasks.exe (PID: 7308)
- schtasks.exe (PID: 7356)
Process drops legitimate windows executable
- cmd.exe (PID: 7148)
Drops a system driver (possible attempt to evade defenses)
- Unlocker.exe (PID: 5868)
INFO
Reads the computer name
- random.exe (PID: 1276)
- nircmd.exe (PID: 4400)
- NSudoLG.exe (PID: 6436)
- NSudoLG.exe (PID: 5548)
- 7z.exe (PID: 1188)
- Unlocker.exe (PID: 5384)
- Unlocker.exe (PID: 5868)
- IObitUnlocker.exe (PID: 1388)
- IObitUnlocker.exe (PID: 4920)
- Unlocker.exe (PID: 7780)
Checks supported languages
- chcp.com (PID: 6436)
- nircmd.exe (PID: 4400)
- random.exe (PID: 1276)
- chcp.com (PID: 5332)
- NSudoLG.exe (PID: 6436)
- chcp.com (PID: 6268)
- mode.com (PID: 5332)
- NSudoLG.exe (PID: 5548)
- 7z.exe (PID: 1188)
- Unlocker.exe (PID: 5384)
- Unlocker.exe (PID: 5868)
- IObitUnlocker.exe (PID: 1388)
- IObitUnlocker.exe (PID: 4920)
- Unlocker.exe (PID: 7780)
The sample compiled with english language support
- random.exe (PID: 1276)
- Unlocker.exe (PID: 5868)
- cmd.exe (PID: 7148)
Create files in a temporary directory
- random.exe (PID: 1276)
- 7z.exe (PID: 1188)
Process checks computer location settings
- random.exe (PID: 1276)
- nircmd.exe (PID: 4400)
Changes the display of characters in the console
- cmd.exe (PID: 1760)
- cmd.exe (PID: 7148)
- cmd.exe (PID: 672)
Starts MODE.COM to configure console settings
- mode.com (PID: 5332)
Checks operating system version
- cmd.exe (PID: 7148)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 2564)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2564)
Reads the machine GUID from the registry
- Unlocker.exe (PID: 5384)
- Unlocker.exe (PID: 5868)
- Unlocker.exe (PID: 7780)
NirSoft software is detected
- nircmd.exe (PID: 4400)
Reads the software policy settings
- slui.exe (PID: 536)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:03:03 13:15:57+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.3 |
| CodeSize: | 203776 |
| InitializedDataSize: | 261632 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1f530 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
317
Monitored processes
183
Malicious processes
8
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | reg delete "HKLM\System\CurrentControlset\Services\SecurityHealthService" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Registry Console Tool Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | reg query "HKLM\System\CurrentControlSet\Services\WdNisSvc" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | sc config "webthreatdefsvc" start= disabled | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | "C:\WINDOWS\system32\cmd.exe" /c "C:\Users\admin\AppData\Local\Temp\gxm0PqP.bat" any_word | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | reg query "HKLM\System\CurrentControlSet\Services\MsSecFlt" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | "C:\Windows\System32\cmd.exe" /c sc query IObitUnlocker | C:\Windows\System32\cmd.exe | — | Unlocker.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 720 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 720 | reg delete "HKLM\System\CurrentControlset\Services\WdBoot" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Registry Console Tool Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | sc stop "SecurityHealthService" | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 232
Read events
11 091
Write events
9
Delete events
132
Modification events
| (PID) Process: | (4400) nircmd.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.FriendlyAppName |
Value: Windows Command Processor | |||
| (PID) Process: | (4400) nircmd.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.ApplicationCompany |
Value: Microsoft Corporation | |||
| (PID) Process: | (2504) reg.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Themes\Personalize |
| Operation: | write | Name: | AppsUseLightTheme |
Value: 0 | |||
| (PID) Process: | (5736) reg.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Themes\Personalize |
| Operation: | write | Name: | AppsUseLightTheme |
Value: 0 | |||
| (PID) Process: | (5384) Unlocker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\DK |
| Operation: | write | Name: | CurrentDiskSize |
Value: 228900667392 | |||
| (PID) Process: | (5868) Unlocker.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\IObitUnlocker |
| Operation: | write | Name: | Type |
Value: 1 | |||
| (PID) Process: | (5868) Unlocker.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\IObitUnlocker |
| Operation: | write | Name: | Start |
Value: 3 | |||
| (PID) Process: | (5868) Unlocker.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\IObitUnlocker |
| Operation: | write | Name: | ErrorControl |
Value: 1 | |||
| (PID) Process: | (5868) Unlocker.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\IObitUnlocker |
| Operation: | write | Name: | ImagePath |
Value: C:\WINDOWS\TEMP\IObitUnlocker\IObitUnlocker.sys | |||
| (PID) Process: | (1756) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\WinDefend\Security |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
10
Suspicious files
3
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2564 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_14fwgmpg.0d1.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1388 | IObitUnlocker.exe | C:\Windows\Temp\IObitUnlocker\IObitUnlocker.log | text | |
MD5:16E2D4A523EF292BC03F50292DFD4071 | SHA256:F3ECEA573634A45E0967BA2F524809A83E9A383B179A5AC21028AA6E6E01B68C | |||
| 1276 | random.exe | C:\Users\admin\AppData\Local\Temp\Work\NSudoLG.exe | executable | |
MD5:423129DDB24FB923F35B2DD5787B13DD | SHA256:5094AD359D8CF6DC5324598605C35F68519CC5AF9C7ED5427E02A6B28121E4C7 | |||
| 2564 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_txoyyvfg.glh.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1188 | 7z.exe | C:\Users\admin\AppData\Local\Temp\Work\Unlocker.exe | executable | |
MD5:49C7A62751050E4B46822CE25AF57E6F | SHA256:2EA997FB5896EBD2CBBCDEA7995DBB871F2358BF0BFF9470801845879506CE44 | |||
| 5868 | Unlocker.exe | C:\Windows\Temp\IObitUnlocker\IObitUnlocker.dll | executable | |
MD5:2C6233C8DBC560027EE1427F5413E4B1 | SHA256:37D2A1626DC205D60F0BEC8746AB256569267E4EF2F8F84DFF4D9D792AA3AF30 | |||
| 1276 | random.exe | C:\Users\admin\AppData\Local\Temp\Work\DKTolz.zip | compressed | |
MD5:6B617C0196FE449E27C84532EC2C38E7 | SHA256:E3528C57765074D5D73021F747B26EDEFA15227D0F1A3B80A6CDEF21322C99CA | |||
| 1276 | random.exe | C:\Users\admin\AppData\Local\Temp\gxm0PqP.bat | text | |
MD5:350D172630B12F10564C78EEF37E3F95 | SHA256:73BC1BD40DCB68AC6DBF25FFB5E0B708F43FD4CA8A17D08647EEB89641B37062 | |||
| 1276 | random.exe | C:\Users\admin\AppData\Local\Temp\Work\7z.exe | executable | |
MD5:426CCB645E50A3143811CFA0E42E2BA6 | SHA256:CF878BFBD9ED93DC551AC038AFF8A8BBA4C935DDF8D48E62122BDDFDB3E08567 | |||
| 5868 | Unlocker.exe | C:\Windows\Temp\IObitUnlocker\IObitUnlocker.sys | executable | |
MD5:AC055B6C011B2E015DE44154E2D46ADB | SHA256:1845FE8545B6708E64250B8807F26D095F1875CC1F6159B24C2D0589FEB74F0C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
18
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8180 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8180 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
2104 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6108 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |