| File name: | nsepa_setup.exe |
| Full analysis: | https://app.any.run/tasks/4e099680-5119-4283-8ab9-2df9ccdb89ad |
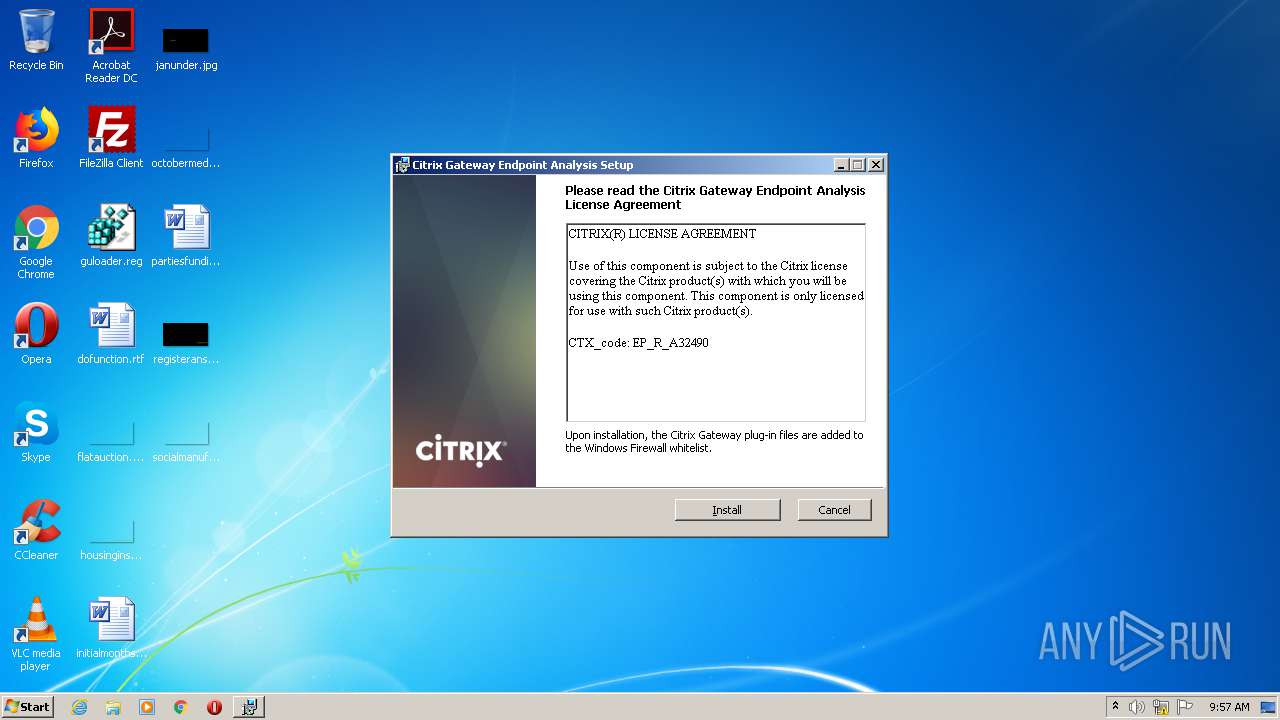
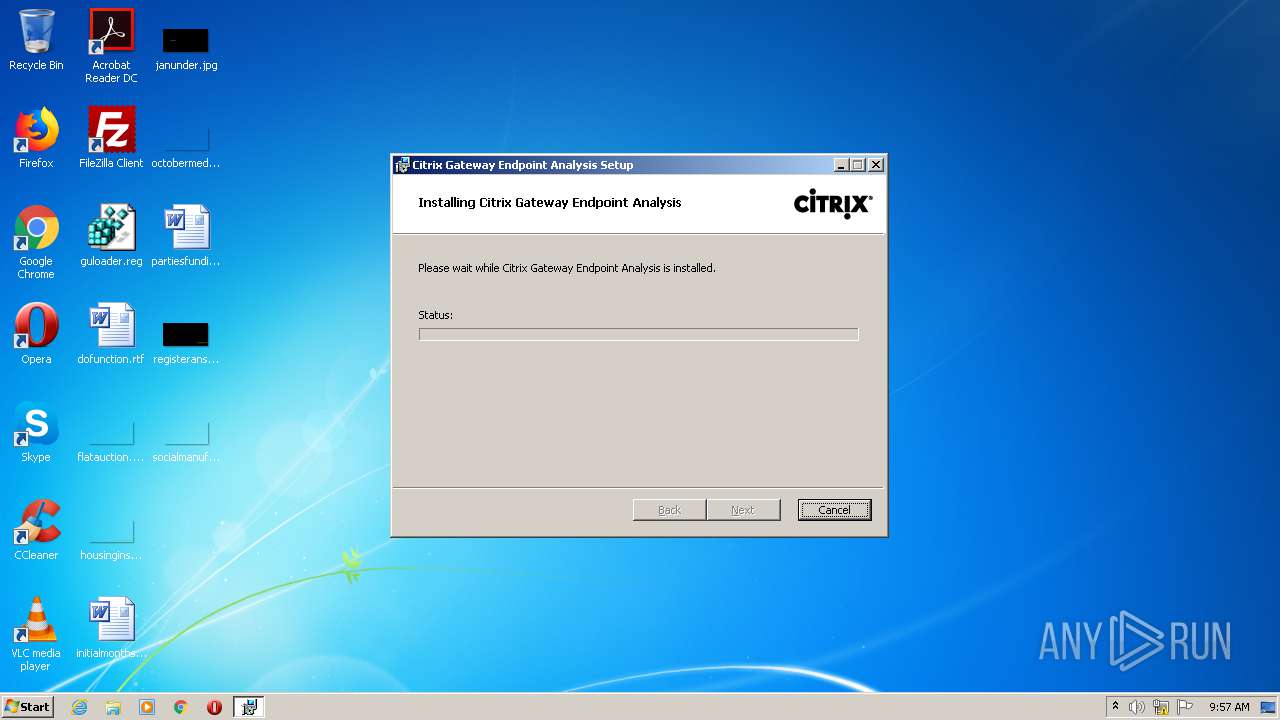
| Verdict: | Malicious activity |
| Analysis date: | November 22, 2020, 09:57:27 |
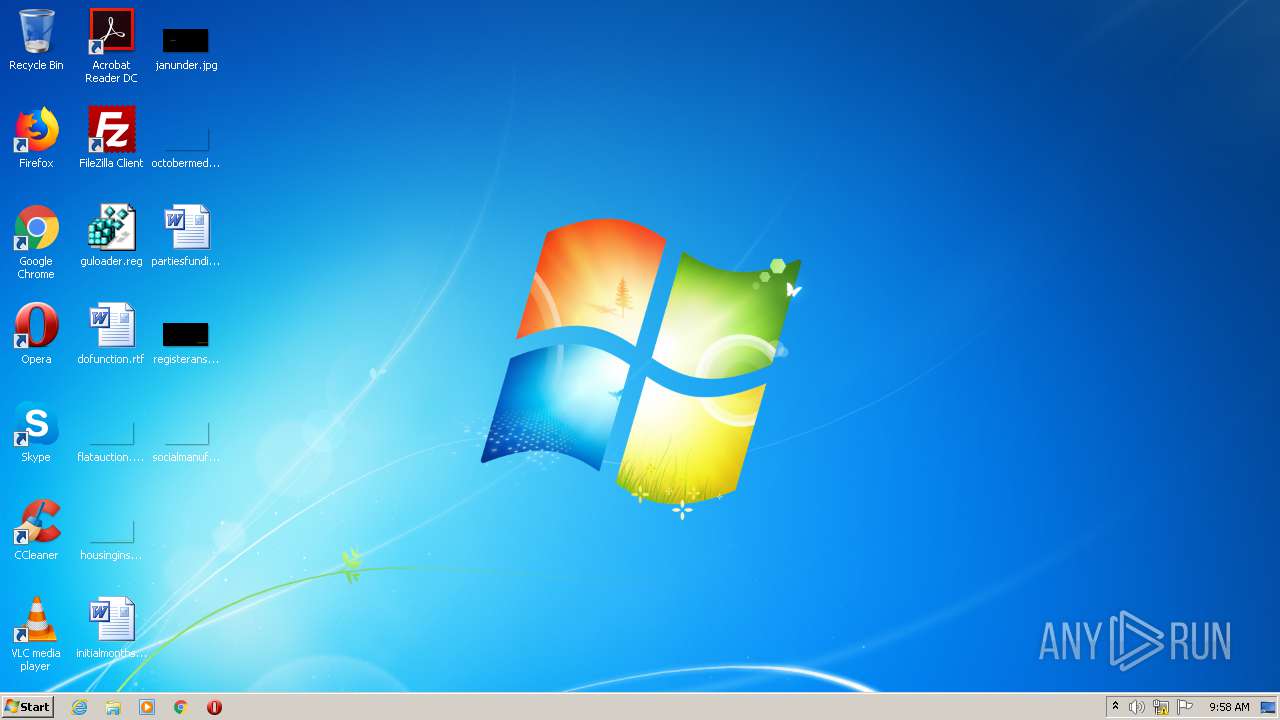
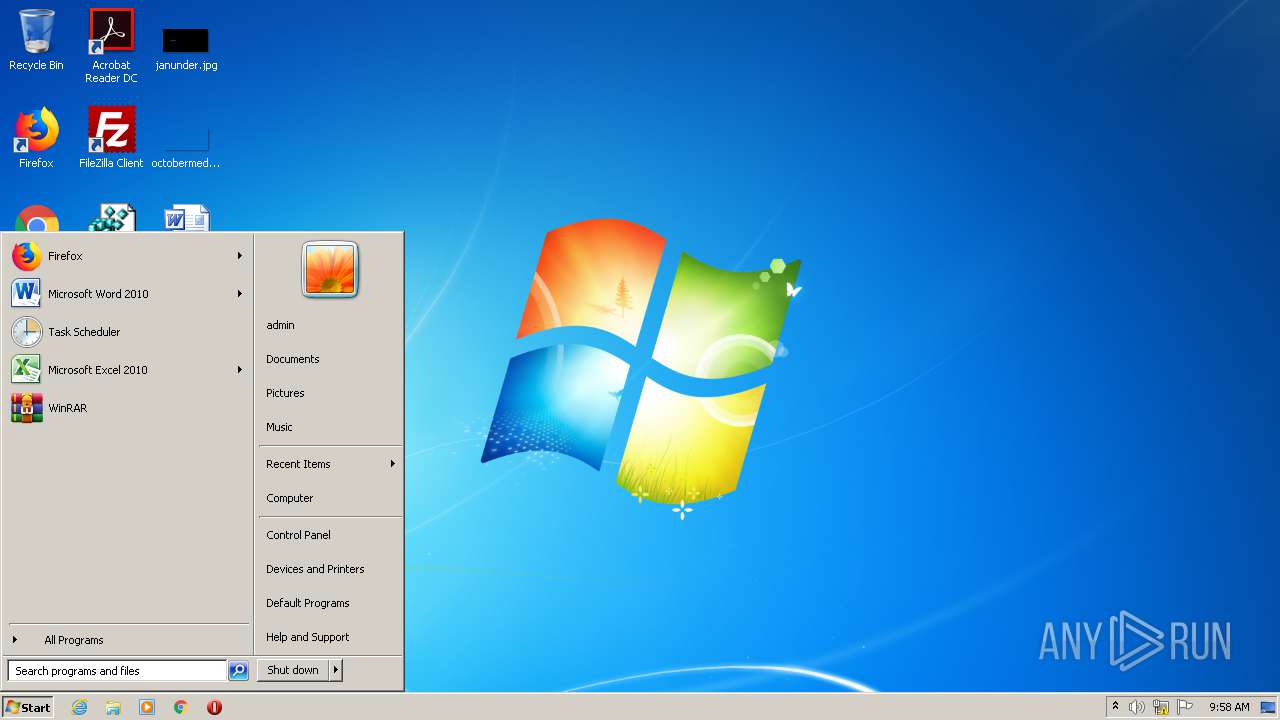
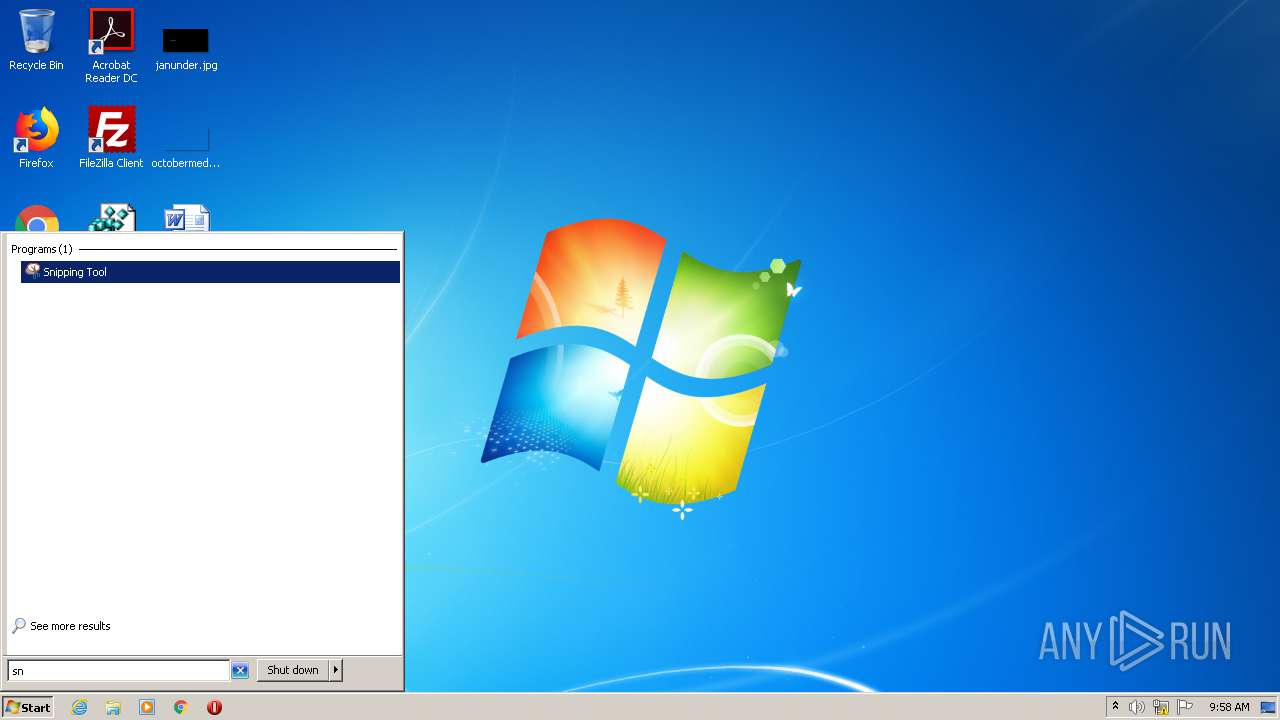
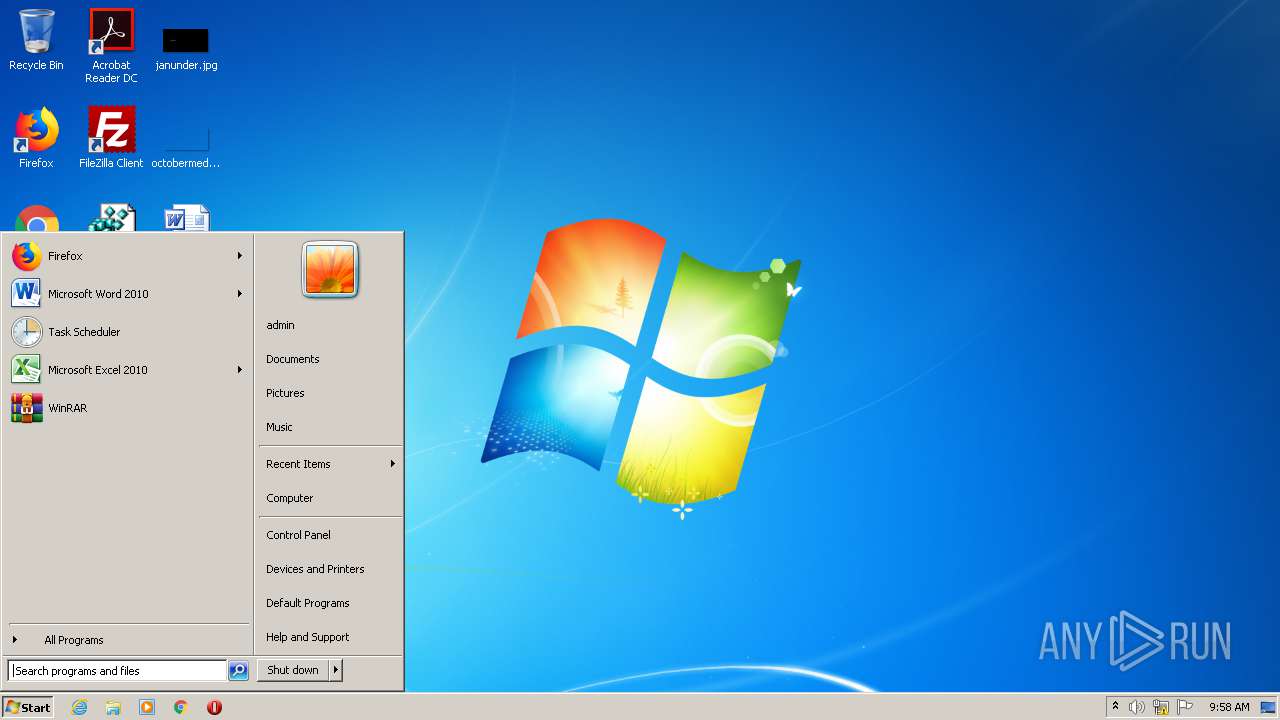
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 36141408F8B6CDBF2BA715B1E73EF7B4 |
| SHA1: | D447FDDDF11BAF0F5DBDC19A1DD9684B88DCC772 |
| SHA256: | E9D3E9A7B94A7EA11306CEEA973EFE77C4D37631C24082F9298EEA4A74417305 |
| SSDEEP: | 98304:qlKmp+7Exx+lJ1Ia/P28MbXyyV0W9+pIUypd3ub/lNo03hYeFYV6WK63M9xUYAjp:mp+oxUJ1IraWgKpd+bDo03hzFfo |
MALICIOUS
Drops executable file immediately after starts
- nsepa_setup.exe (PID: 3504)
Changes settings of System certificates
- combinedSetup.exe (PID: 2720)
Application was dropped or rewritten from another process
- combinedSetup.exe (PID: 2720)
- nglauncher.exe (PID: 3952)
Changes the autorun value in the registry
- nsepa_setup.exe (PID: 3504)
SUSPICIOUS
Drops a file that was compiled in debug mode
- nsepa_setup.exe (PID: 3504)
- msiexec.exe (PID: 1928)
Adds / modifies Windows certificates
- combinedSetup.exe (PID: 2720)
Executable content was dropped or overwritten
- nsepa_setup.exe (PID: 3504)
- msiexec.exe (PID: 1928)
Creates a directory in Program Files
- msiexec.exe (PID: 1928)
Executed as Windows Service
- vssvc.exe (PID: 3084)
Executed via COM
- DllHost.exe (PID: 2856)
Modifies the open verb of a shell class
- msiexec.exe (PID: 1928)
INFO
Reads settings of System Certificates
- combinedSetup.exe (PID: 2720)
Creates files in the program directory
- msiexec.exe (PID: 1928)
Searches for installed software
- msiexec.exe (PID: 1928)
Application launched itself
- msiexec.exe (PID: 1928)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3084)
Creates a software uninstall entry
- msiexec.exe (PID: 1928)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:07:16 03:42:10+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 26112 |
| InitializedDataSize: | 5805056 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6bd0 |
| OSVersion: | 10 |
| ImageVersion: | 10 |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 11.0.14393.0 |
| ProductVersionNumber: | 11.0.14393.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 11.00.14393.0 (rs1_release.160715-1616) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | WEXTRACT.EXE .MUI |
| ProductName: | Internet Explorer |
| ProductVersion: | 11.00.14393.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Jul-2016 01:42:10 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 11.00.14393.0 (rs1_release.160715-1616) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | WEXTRACT.EXE .MUI |
| ProductName: | Internet Explorer |
| ProductVersion: | 11.00.14393.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 16-Jul-2016 01:42:10 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000651C | 0x00006600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.30785 |
.data | 0x00008000 | 0x00001A48 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.97064 |
.idata | 0x0000A000 | 0x0000106E | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.05715 |
.rsrc | 0x0000C000 | 0x005874AC | 0x00587600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99723 |
.reloc | 0x00594000 | 0x00000890 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.27466 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.35134 | 1100 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.15864 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.07737 | 488 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.50949 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.56662 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.94251 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.99361 | 1736 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 3.37828 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 7.98515 | 55762 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 5.33023 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
Cabinet.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
VERSION.dll |
msvcrt.dll |
Total processes
44
Monitored processes
8
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1928 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2056 | C:\Windows\system32\MsiExec.exe -Embedding C176D4861712CF8CA75C81BAA5A0C1F3 M Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2720 | combinedSetup de es fr ja zh - /qf | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\combinedSetup.exe | — | nsepa_setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2720 | "C:\Users\admin\AppData\Local\Temp\nsepa_setup.exe" | C:\Users\admin\AppData\Local\Temp\nsepa_setup.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 3221226540 Version: 11.00.14393.0 (rs1_release.160715-1616) Modules
| |||||||||||||||
| 2856 | C:\Windows\system32\DllHost.exe /Processid:{E2B3C97F-6AE1-41AC-817A-F6F92166D7DD} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3084 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3504 | "C:\Users\admin\AppData\Local\Temp\nsepa_setup.exe" | C:\Users\admin\AppData\Local\Temp\nsepa_setup.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 11.00.14393.0 (rs1_release.160715-1616) Modules
| |||||||||||||||
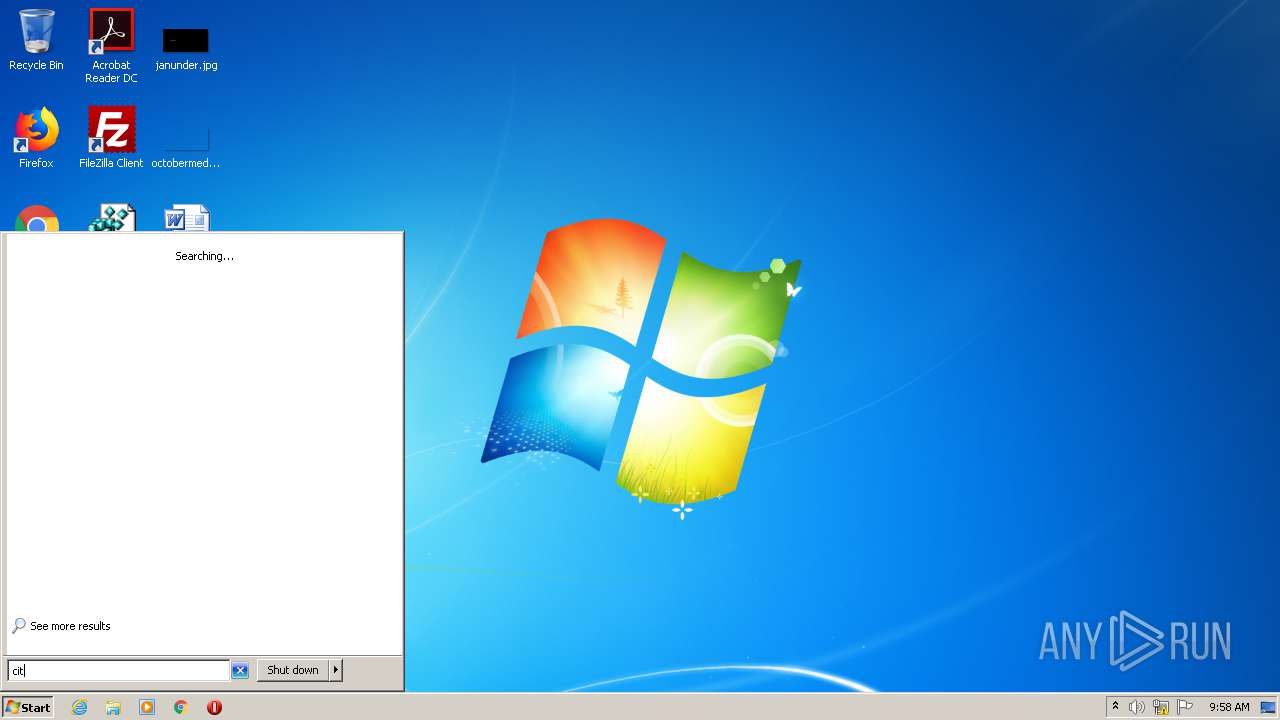
| 3952 | "C:\Program Files\Citrix\Secure Access Client\nglauncher.exe" autoLaunch | C:\Program Files\Citrix\Secure Access Client\nglauncher.exe | msiexec.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
835
Read events
520
Write events
302
Delete events
13
Modification events
| (PID) Process: | (2720) combinedSetup.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2720) combinedSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\0563B8630D62D75ABBC8AB1E4BDFB5A899B24D43 |
| Operation: | write | Name: | Blob |
Value: 04000000010000001000000087CE0B7B2A0E4900E158719B37A893720F00000001000000140000006DCA5BD00DCF1C0F327059D374B29CA6E3C50AA60300000001000000140000000563B8630D62D75ABBC8AB1E4BDFB5A899B24D431D00000001000000100000004F5F106930398D09107B40C3C7CA8F1C0B000000010000001200000044006900670069004300650072007400000014000000010000001400000045EBA2AFF492CB82312D518BA7A7219DF36DC80F6200000001000000200000003E9099B5015E8F486C00BCEA9D111EE721FABA355A89BCF1DF69561E3DC6325C5300000001000000230000003021301F06096086480186FD6C020130123010060A2B0601040182373C0101030200C0090000000100000034000000303206082B0601050507030106082B0601050507030206082B0601050507030406082B0601050507030306082B06010505070308190000000100000010000000749966CECC95C1874194CA7203F9B6202000000001000000BB030000308203B73082029FA00302010202100CE7E0E517D846FE8FE560FC1BF03039300D06092A864886F70D01010505003065310B300906035504061302555331153013060355040A130C446967694365727420496E6331193017060355040B13107777772E64696769636572742E636F6D312430220603550403131B4469676943657274204173737572656420494420526F6F74204341301E170D3036313131303030303030305A170D3331313131303030303030305A3065310B300906035504061302555331153013060355040A130C446967694365727420496E6331193017060355040B13107777772E64696769636572742E636F6D312430220603550403131B4469676943657274204173737572656420494420526F6F7420434130820122300D06092A864886F70D01010105000382010F003082010A0282010100AD0E15CEE443805CB187F3B760F97112A5AEDC269488AAF4CEF520392858600CF880DAA9159532613CB5B128848A8ADC9F0A0C83177A8F90AC8AE779535C31842AF60F98323676CCDEDD3CA8A2EF6AFB21F25261DF9F20D71FE2B1D9FE1864D2125B5FF9581835BC47CDA136F96B7FD4B0383EC11BC38C33D9D82F18FE280FB3A783D6C36E44C061359616FE599C8B766DD7F1A24B0D2BFF0B72DA9E60D08E9035C678558720A1CFE56D0AC8497C3198336C22E987D0325AA2BA138211ED39179D993A72A1E6FAA4D9D5173175AE857D22AE3F014686F62879C8B1DAE45717C47E1C0EB0B492A656B3BDB297EDAAA7F0B7C5A83F9516D0FFA196EB085F18774F0203010001A3633061300E0603551D0F0101FF040403020186300F0603551D130101FF040530030101FF301D0603551D0E0416041445EBA2AFF492CB82312D518BA7A7219DF36DC80F301F0603551D2304183016801445EBA2AFF492CB82312D518BA7A7219DF36DC80F300D06092A864886F70D01010505000382010100A20EBCDFE2EDF0E372737A6494BFF77266D832E4427562AE87EBF2D5D9DE56B39FCCCE1428B90D97605C124C58E4D33D834945589735691AA847EA56C679AB12D8678184DF7F093C94E6B8262C20BD3DB32889F75FFF22E297841FE965EF87E0DFC16749B35DEBB2092AEB26ED78BE7D3F2BF3B726356D5F8901B6495B9F01059BAB3D25C1CCB67FC2F16F86C6FA6468EB812D94EB42B7FA8C1EDD62F1BE5067B76CBDF3F11F6B0C3607167F377CA95B6D7AF112466083D72704BE4BCE97BEC3672A6811DF80E70C3366BF130D146EF37F1F63101EFA8D1B256D6C8FA5B76101B1D2A326A110719DADE2C3F9C39951B72B0708CE2EE650B2A7FA0A452FA2F0F2 | |||
| (PID) Process: | (3504) nsepa_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | wextract_cleanup0 |
Value: rundll32.exe C:\Windows\system32\advpack.dll,DelNodeRunDLL32 "C:\Users\admin\AppData\Local\Temp\IXP000.TMP\" | |||
| (PID) Process: | (1928) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 400000000000000048C780F3B5C0D60188070000840B0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1928) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 400000000000000048C780F3B5C0D60188070000840B0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1928) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 43 | |||
| (PID) Process: | (1928) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000007AEBC5F3B5C0D60188070000840B0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1928) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000007AEBC5F3B5C0D601880700001C0B0000E80300000100000000000000000000005472CA024A4B664F9B1652C51EFF972D0000000000000000 | |||
| (PID) Process: | (3084) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000E274CFF3B5C0D6010C0C0000E40A0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3084) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000E274CFF3B5C0D6010C0C0000A80D0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
4
Suspicious files
14
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3504 | nsepa_setup.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\nsepa.msi | — | |
MD5:— | SHA256:— | |||
| 3504 | nsepa_setup.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\nsepa64.msi | — | |
MD5:— | SHA256:— | |||
| 1928 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 1928 | msiexec.exe | C:\Windows\Installer\145458.msi | — | |
MD5:— | SHA256:— | |||
| 1928 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFB7D1EA7C703CE08A.TMP | — | |
MD5:— | SHA256:— | |||
| 3084 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 1928 | msiexec.exe | C:\Windows\Installer\14545b.msi | — | |
MD5:— | SHA256:— | |||
| 1928 | msiexec.exe | C:\Config.Msi\14545a.rbs | — | |
MD5:— | SHA256:— | |||
| 1928 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF6556A60C5A838AE1.TMP | — | |
MD5:— | SHA256:— | |||
| 1928 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report