| File name: | Temp.exe |
| Full analysis: | https://app.any.run/tasks/7feb344e-46fb-427b-aadb-632fe62406c7 |
| Verdict: | Malicious activity |
| Analysis date: | November 15, 2019, 17:06:32 |
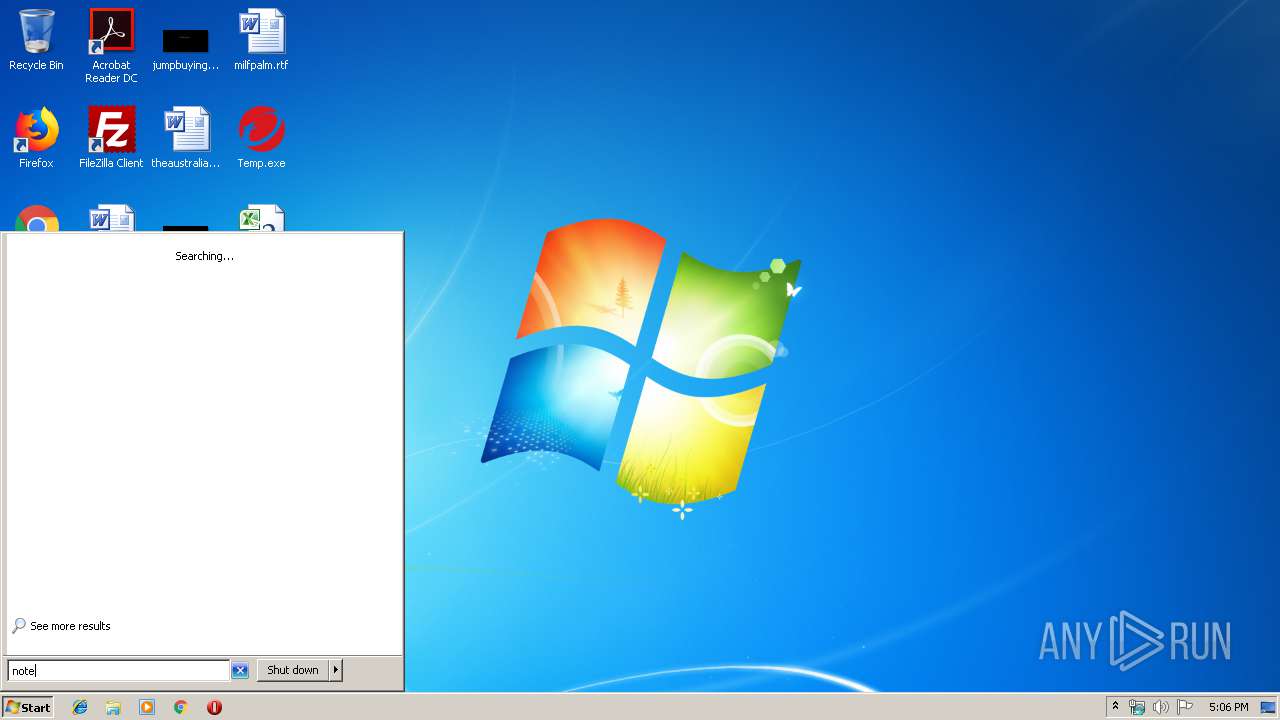
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | AC99C69E914DDCDDFBD15279CD2343C4 |
| SHA1: | 08436C3ECAA97CCE433168F026D5F839A06B15B9 |
| SHA256: | E9CA59D2548EE794DF91EDF197D1DB6978D7A89B74E5E90EEC771F7E74190B12 |
| SSDEEP: | 3072:pbY3YmmjCu/ojEFuy0+bnSF4saLqVS+0DJYCzb/+/D0GO:pbY3pmQEF2+bnSVz2rvU0r |
MALICIOUS
Application was dropped or rewritten from another process
- tmp2770.exe (PID: 3392)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2872)
- Temp.exe (PID: 1600)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 4016)
Executable content was dropped or overwritten
- Temp.exe (PID: 1600)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 2256)
- cmd.exe (PID: 3324)
- cmd.exe (PID: 272)
- cmd.exe (PID: 3048)
- cmd.exe (PID: 3860)
- cmd.exe (PID: 1956)
Application launched itself
- cmd.exe (PID: 2872)
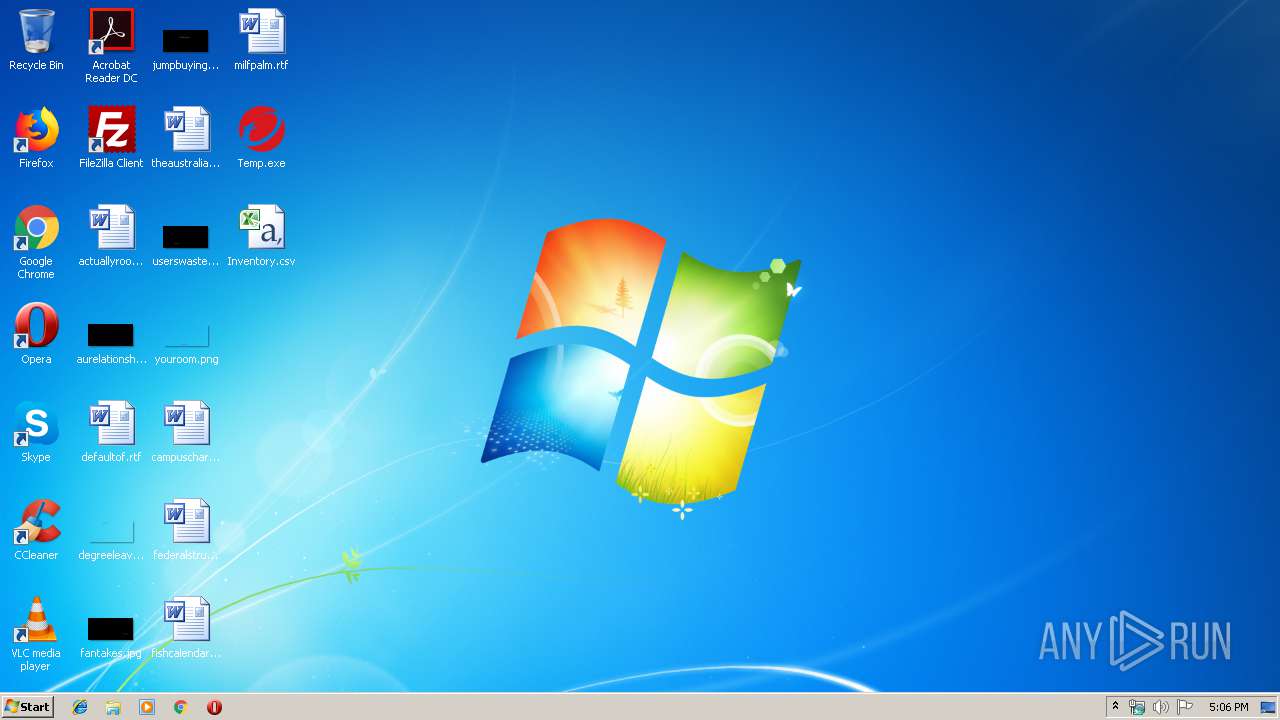
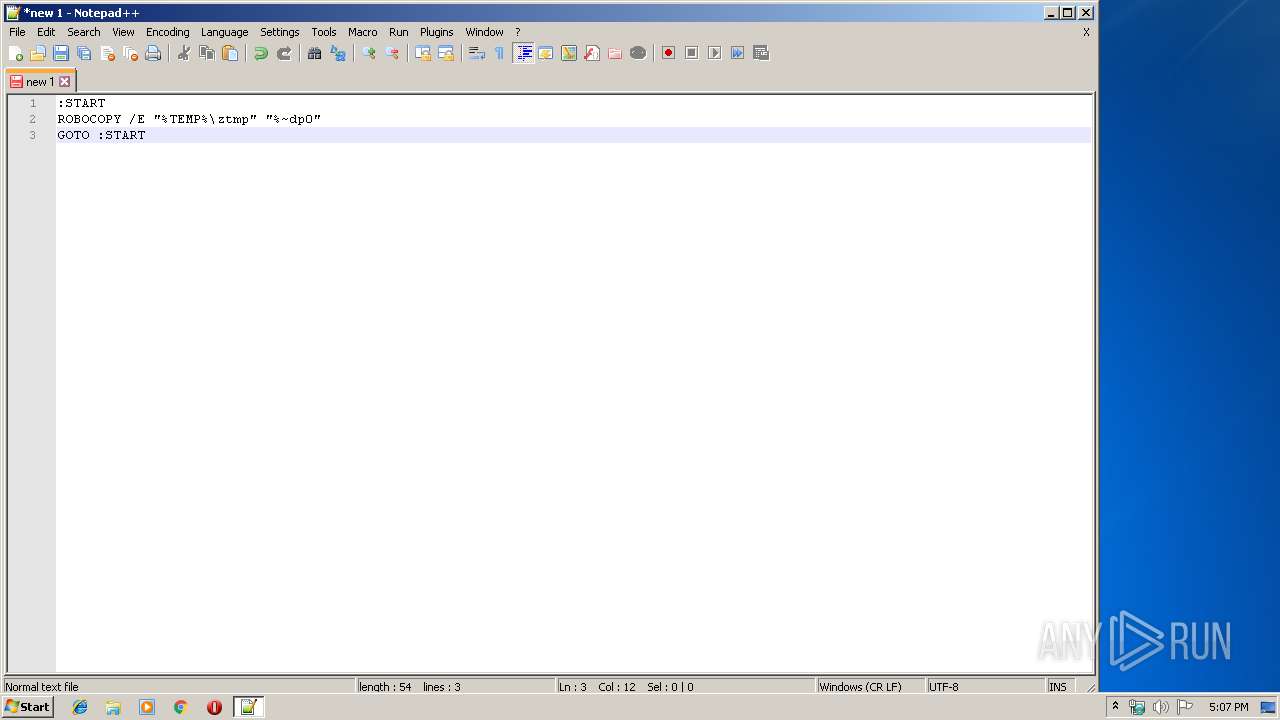
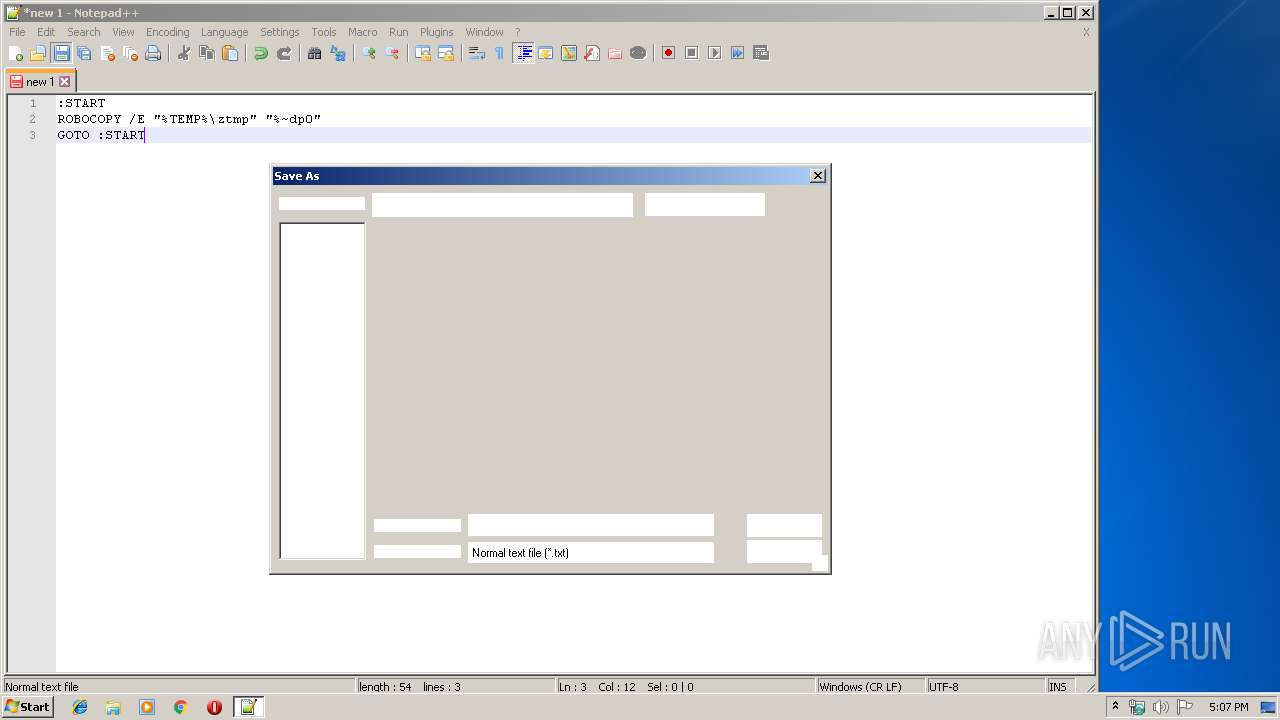
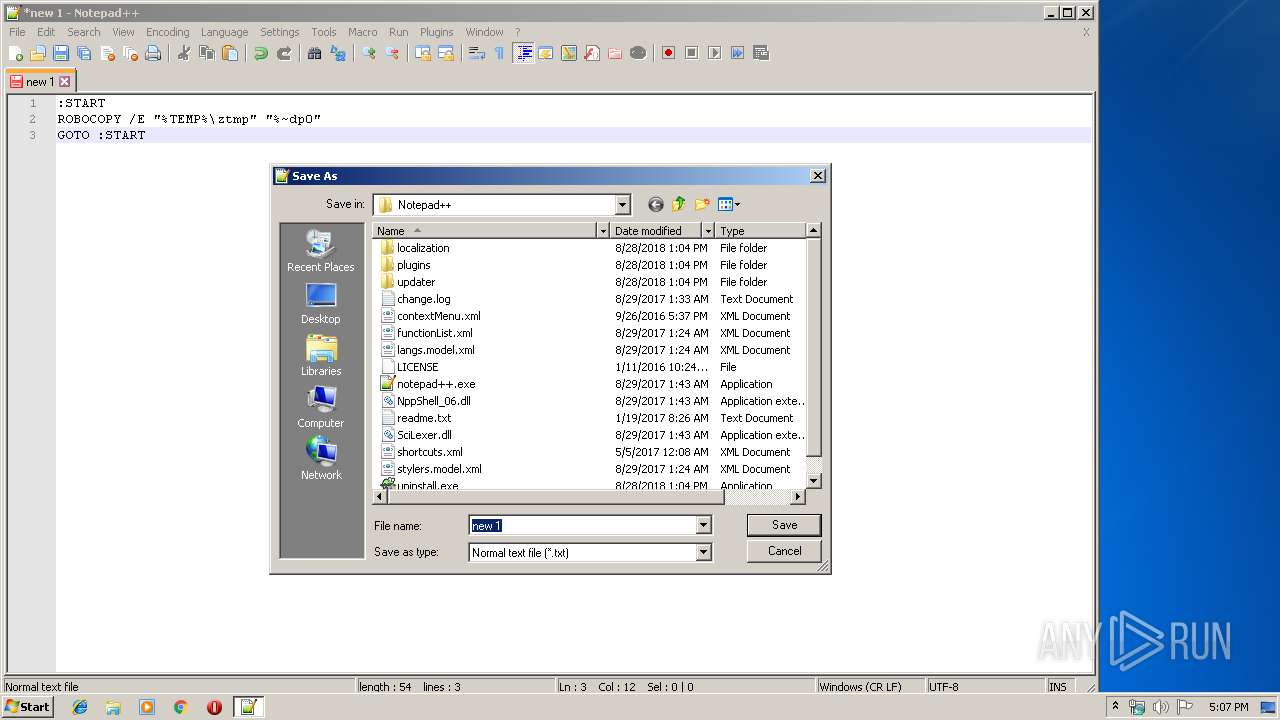
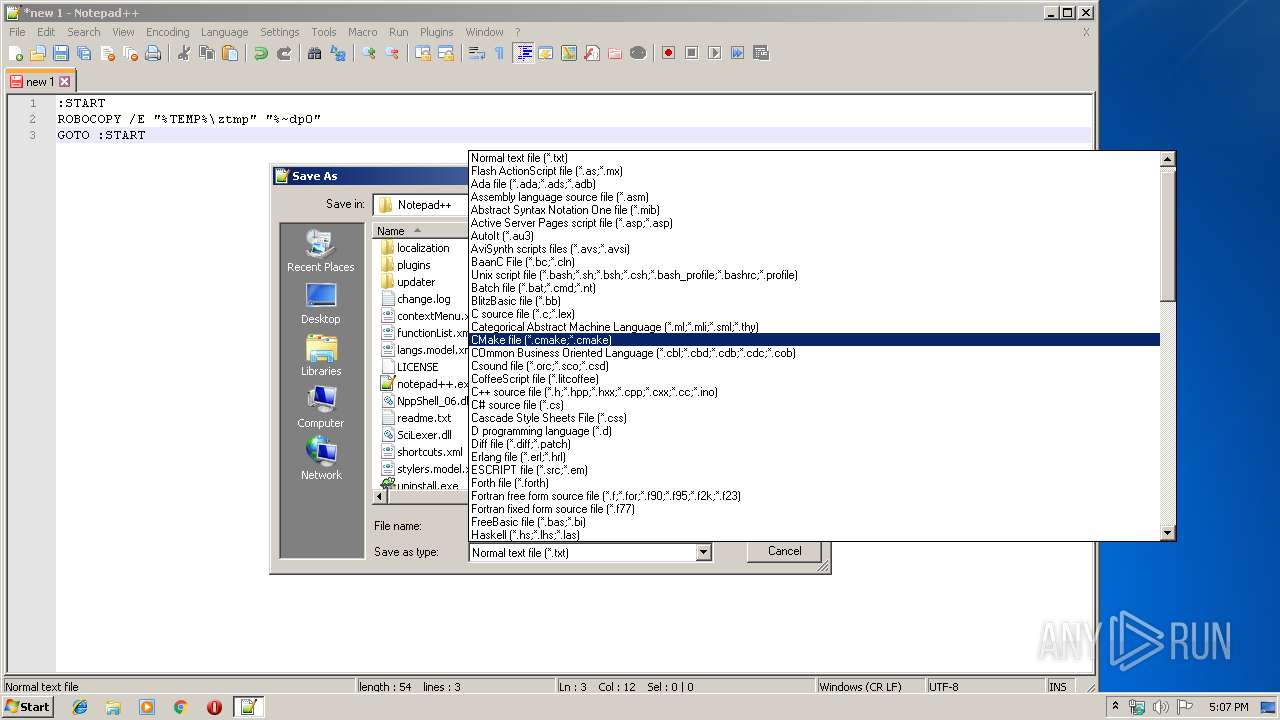
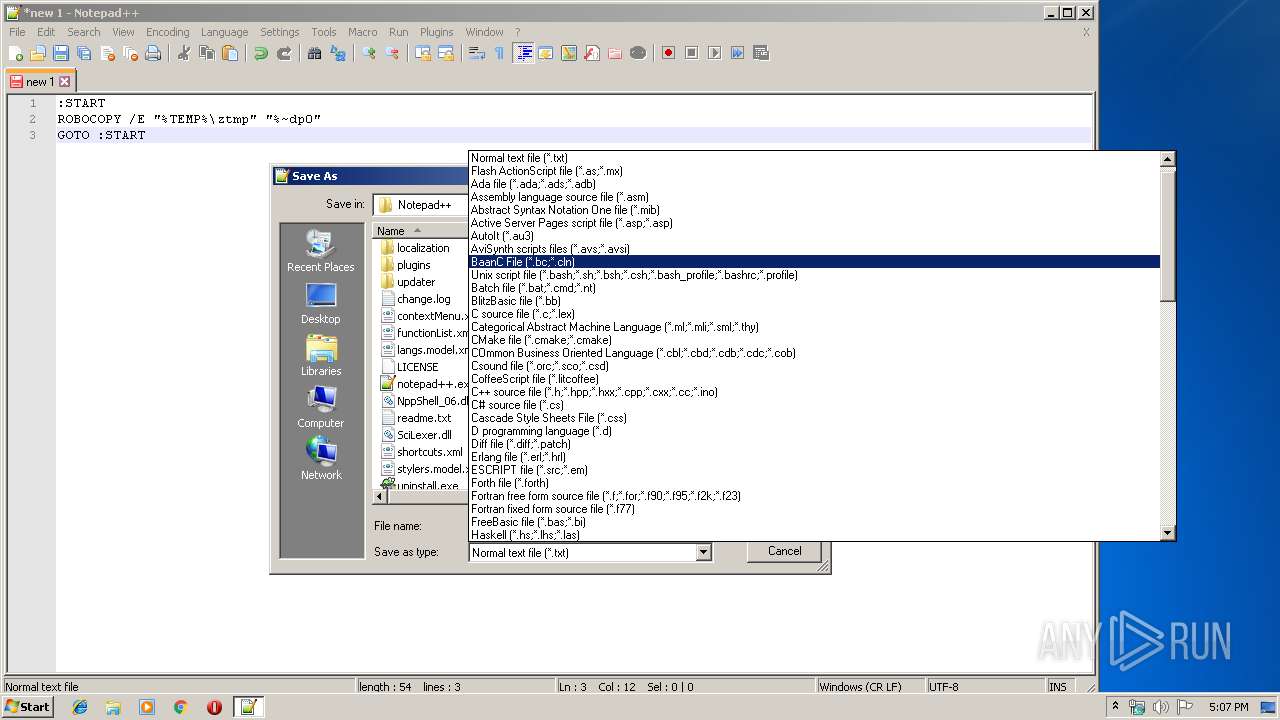
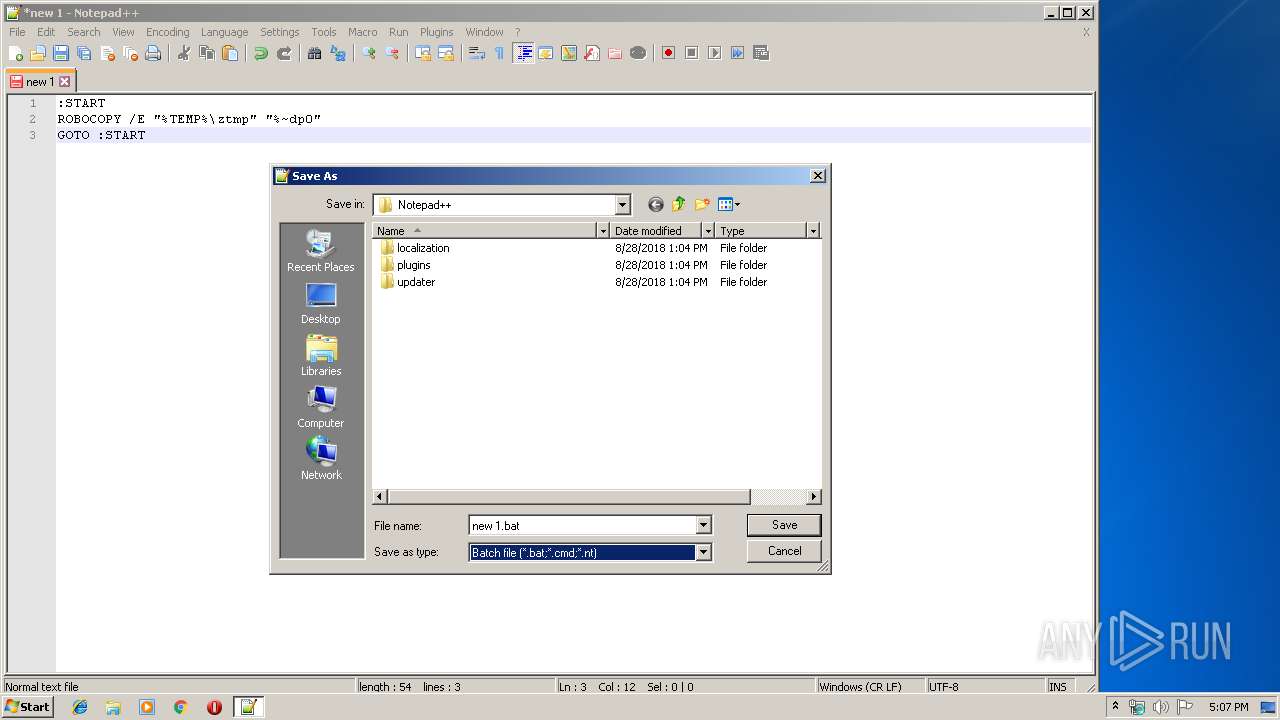
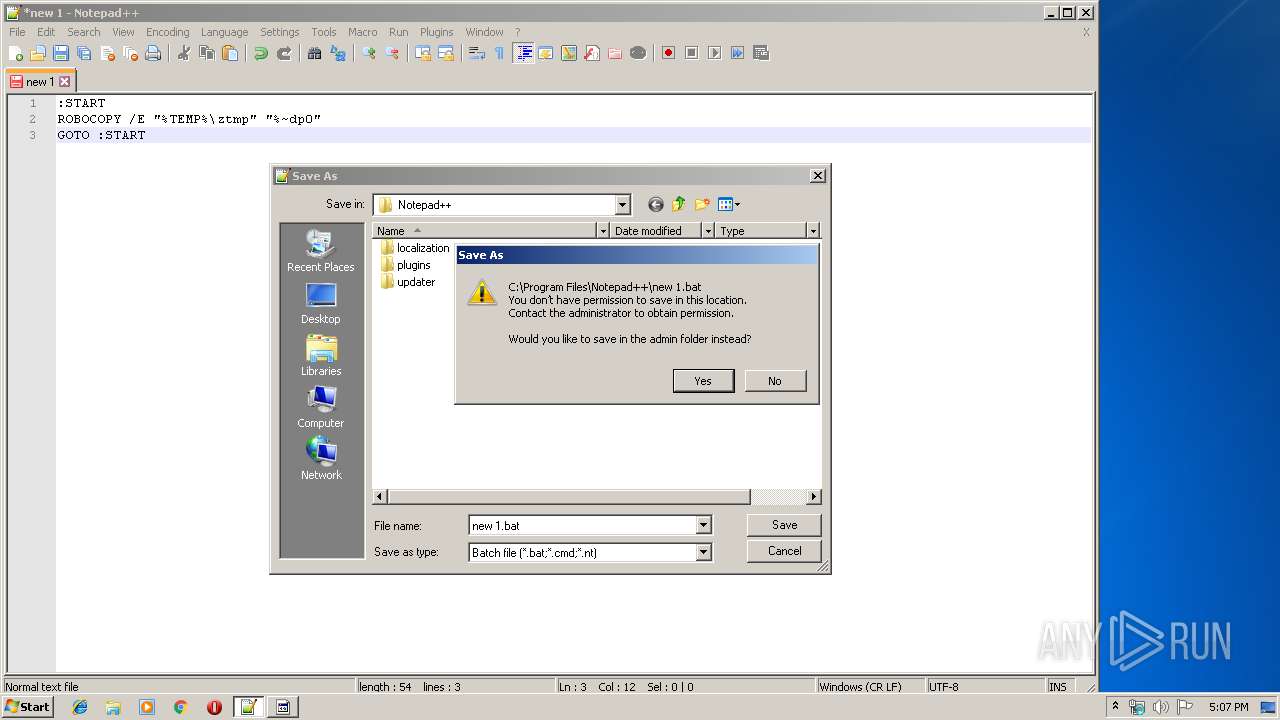
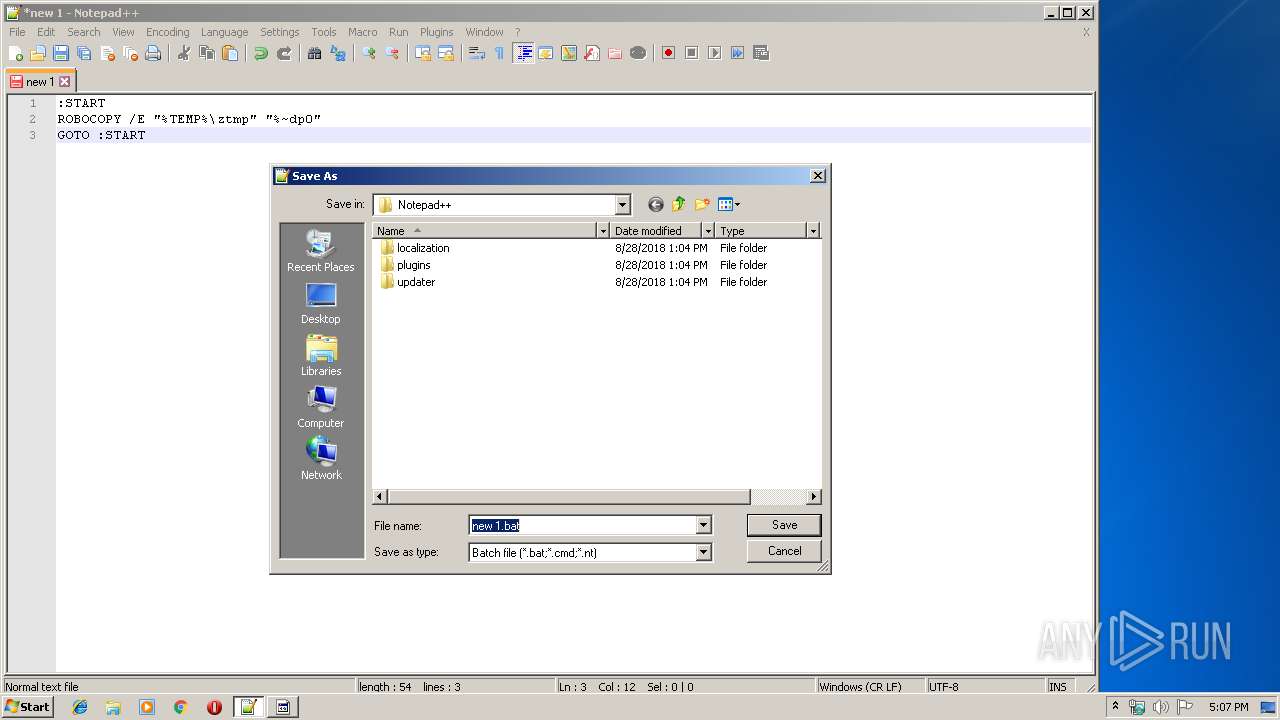
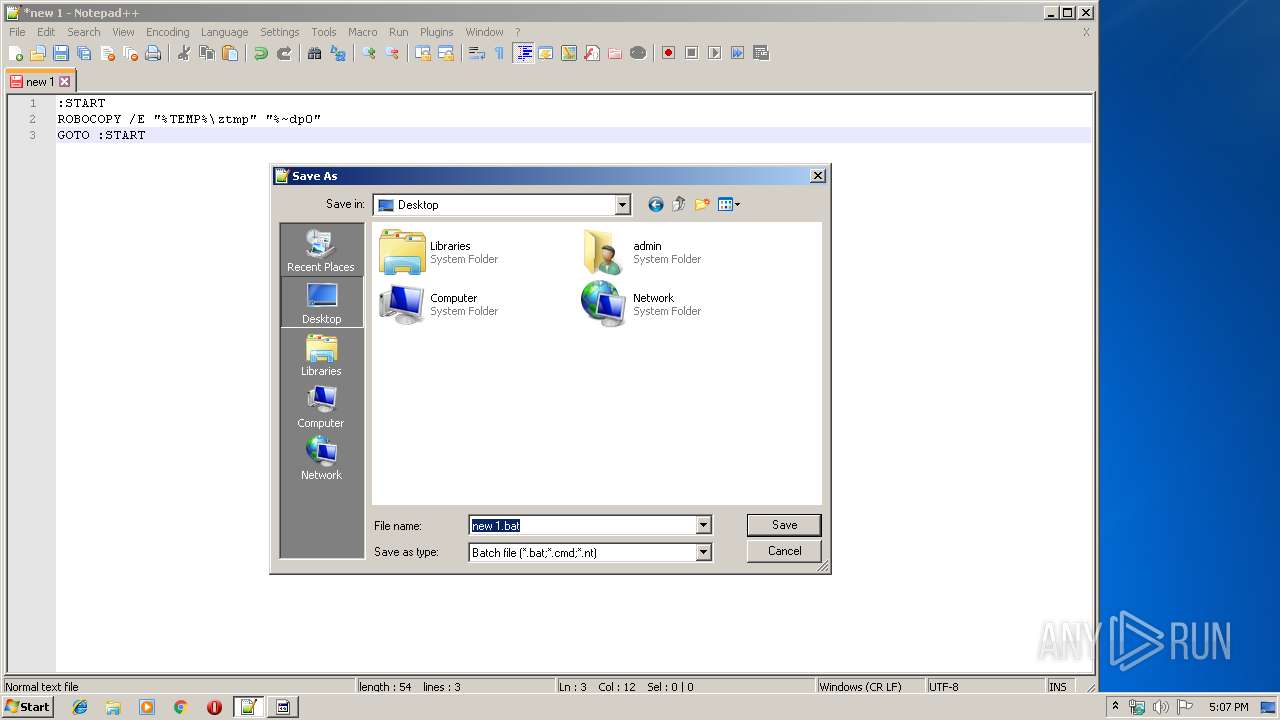
Creates files in the user directory
- notepad++.exe (PID: 1852)
INFO
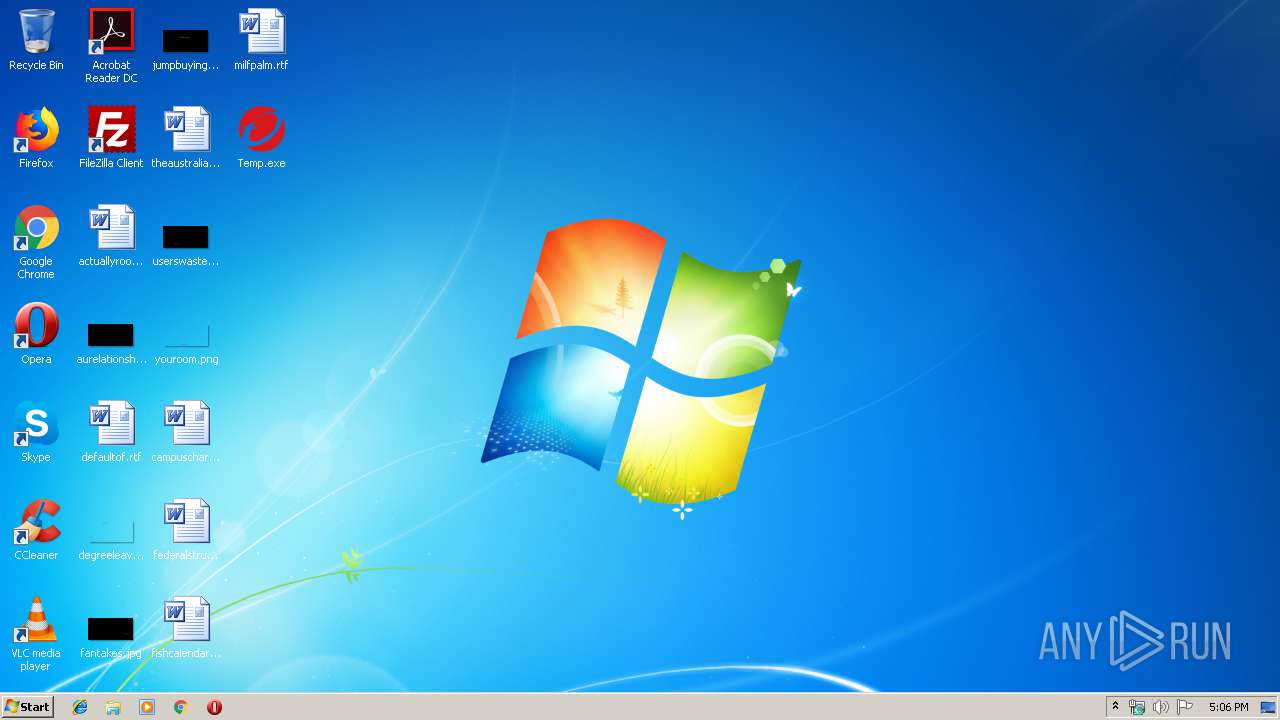
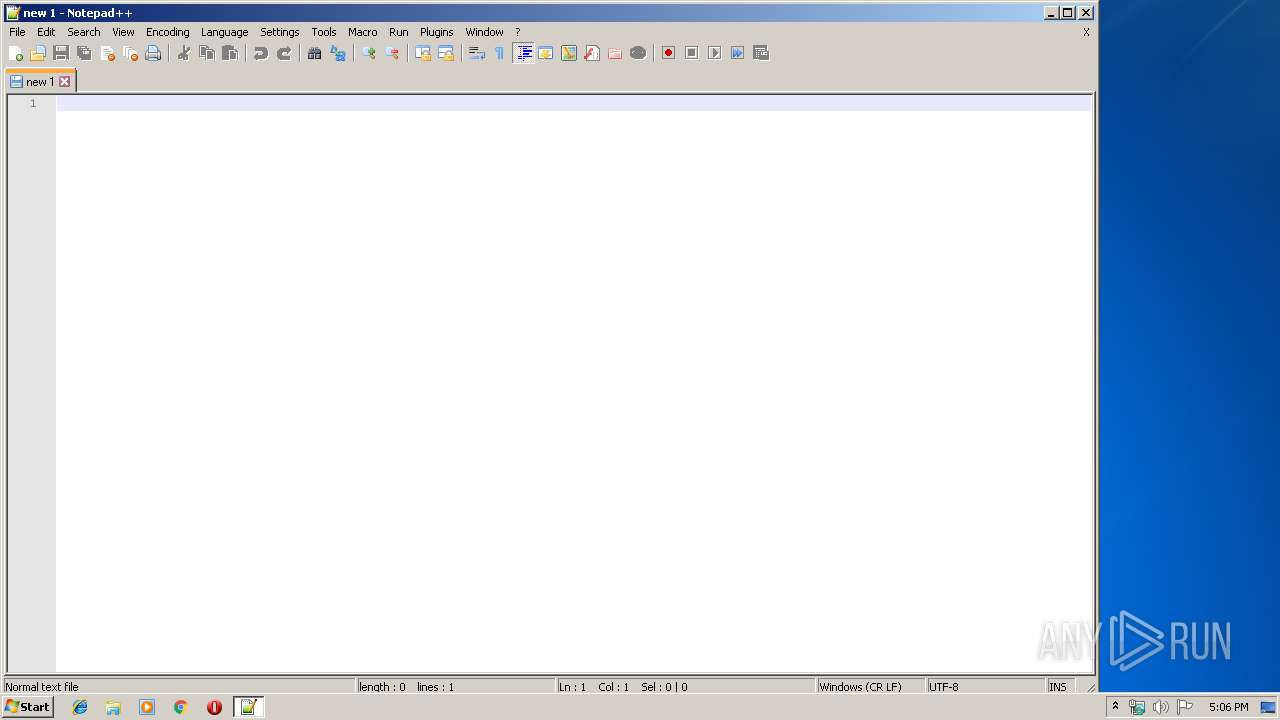
Manual execution by user
- notepad++.exe (PID: 1852)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:02:26 20:34:11+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 49152 |
| InitializedDataSize: | 139264 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6444 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileVersion: | 1.0.0.0 |
| ProductVersion: | 1.0.0.0 |
| FileDescription: | Trend Micro TMSCCM |
| CompanyName: | Trend Micro Service Provider Partner |
| LegalCopyright: | 2018 TrendMicro Service Provider Partner |
| ProductName: | TMSCCM - Inventory Manager Part |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 26-Feb-2013 19:34:11 |
| FileVersion: | 1.0.0.0 |
| ProductVersion: | 1.0.0.0 |
| FileDescription: | Trend Micro TMSCCM |
| CompanyName: | Trend Micro Service Provider Partner |
| LegalCopyright: | 2018 TrendMicro Service Provider Partner |
| ProductName: | TMSCCM - Inventory Manager Part |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 26-Feb-2013 19:34:11 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000BFF6 | 0x0000C000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.5407 |
.rdata | 0x0000D000 | 0x00000B60 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.29476 |
.data | 0x0000E000 | 0x00B00E98 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.71126 |
.rsrc | 0x00B0F000 | 0x0001EACC | 0x0001F000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.69688 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.28229 | 724 | Latin 1 / Western European | UNKNOWN | RT_VERSION |
2 | 3.08362 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 3.42858 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 3.66883 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 3.92402 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 4.29691 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
KERNEL32.dll |
WINMM.dll |
Total processes
62
Monitored processes
25
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | C:\Windows\system32\cmd.exe /c wmic cpu get /value /format:csv | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 436 | wmic os get Caption, BuildNumber, OSArchitecture, MUILanguages, TotalVisibleMemorySize /format:csv | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1532 | wmic cpu get /value /format:csv | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1600 | "C:\Users\admin\Desktop\Temp.exe" | C:\Users\admin\Desktop\Temp.exe | explorer.exe | ||||||||||||
User: admin Company: Trend Micro Service Provider Partner Integrity Level: MEDIUM Description: Trend Micro TMSCCM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1852 | "C:\Program Files\Notepad++\notepad++.exe" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
| 1956 | C:\Windows\system32\cmd.exe /c wmic printer get drivername /value | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2196 | C:\Windows\system32\cmd.exe /c if exist "C:\Users\admin\AppData\Local\Temp\ztmp\tmp5384.bat" del "C:\Users\admin\AppData\Local\Temp\ztmp\tmp5384.bat" | C:\Windows\system32\cmd.exe | — | Temp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2256 | C:\Windows\system32\cmd.exe /c wmic os get Caption, BuildNumber, OSArchitecture, MUILanguages, TotalVisibleMemorySize /format:csv | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2400 | C:\Windows\system32\cmd.exe /c if exist "C:\Users\admin\AppData\Local\Temp\ztmp\tmp2770.exe" del "C:\Users\admin\AppData\Local\Temp\ztmp\tmp2770.exe" | C:\Windows\system32\cmd.exe | — | Temp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2724 | C:\Windows\system32\cmd.exe /c if exist "C:\Users\admin\AppData\Local\Temp\ztmp\tmp2770.exe" del "C:\Users\admin\AppData\Local\Temp\ztmp\tmp2770.exe" | C:\Windows\system32\cmd.exe | — | Temp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
781
Read events
736
Write events
45
Delete events
0
Modification events
| (PID) Process: | (1852) notepad++.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1852) notepad++.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\p2pcollab.dll,-8042 |
Value: Peer to Peer Trust | |||
| (PID) Process: | (1852) notepad++.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\qagentrt.dll,-10 |
Value: System Health Authentication | |||
| (PID) Process: | (1852) notepad++.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dnsapi.dll,-103 |
Value: Domain Name System (DNS) Server Trust | |||
| (PID) Process: | (1852) notepad++.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-843 |
Value: BitLocker Drive Encryption | |||
| (PID) Process: | (1852) notepad++.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-844 |
Value: BitLocker Data Recovery Agent | |||
| (PID) Process: | (1852) notepad++.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1852) notepad++.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1852) notepad++.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | 0 |
Value: 43003A005C00500072006F006700720061006D002000460069006C00650073005C004E006F00740065007000610064002B002B005C006E006F00740065007000610064002B002B002E00650078006500000043003A005C00500072006F006700720061006D002000460069006C00650073005C004E006F00740065007000610064002B002B000000 | |||
| (PID) Process: | (1852) notepad++.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
Executable files
1
Suspicious files
0
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1600 | Temp.exe | C:\Users\admin\AppData\Local\Temp\ztmp\tmp5384.bat | text | |
MD5:— | SHA256:— | |||
| 1852 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\session.xml | text | |
MD5:— | SHA256:— | |||
| 1852 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\backup\new 1@2019-11-15_170718 | text | |
MD5:— | SHA256:— | |||
| 2872 | cmd.exe | C:\Users\admin\Desktop\Inventory.csv | text | |
MD5:— | SHA256:— | |||
| 1852 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\langs.xml | xml | |
MD5:E792264BEC29005B9044A435FBA185AB | SHA256:5298FD2F119C43D04F6CF831F379EC25B4156192278E40E458EC356F9B49D624 | |||
| 1852 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\shortcuts.xml | text | |
MD5:AD21A64014891793DD9B21D835278F36 | SHA256:C24699C9D00ABDD510140FE1B2ACE97BFC70D8B21BF3462DED85AFC4F73FE52F | |||
| 1852 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\plugins\Config\converter.ini | text | |
MD5:F70F579156C93B097E656CABA577A5C9 | SHA256:B926498A19CA95DC28964B7336E5847107DD3C0F52C85195C135D9DD6CA402D4 | |||
| 1600 | Temp.exe | C:\Users\admin\AppData\Local\Temp\ztmp\tmp2770.exe | executable | |
MD5:FAA5D9E45A090C37461F7B8ADA0998B1 | SHA256:C549F6C47F057864CDF421C0F6D3C6F25AF1201368E7DA68AD6852A8551A102B | |||
| 1852 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\stylers.xml | xml | |
MD5:44982E1D48434C0AB3E8277E322DD1E4 | SHA256:3E661D3F1FF3977B022A0ACC26B840B5E57D600BC03DCFC6BEFDB408C665904C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3696 | gup.exe | 104.31.88.28:443 | notepad-plus-plus.org | Cloudflare Inc | US | shared |
3696 | gup.exe | 104.31.89.28:443 | notepad-plus-plus.org | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
notepad-plus-plus.org |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|