| File name: | Slay & ELB Launcher.exe |
| Full analysis: | https://app.any.run/tasks/8098f9a1-dc1c-40f1-b26f-dbcd6fea83bc |
| Verdict: | Malicious activity |
| Analysis date: | March 08, 2021, 19:47:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2D0D0A7FE994F2C0F6782E76BD2E4B79 |
| SHA1: | AC70669D2CEB4BA9D8FAFFF948FE1131860495F4 |
| SHA256: | E9C2AF21B8D5ACAE1A21D0F3A7643AF227044D402E6E5BFD0C3127A29BBD7B16 |
| SSDEEP: | 393216:3gMkI86LQZy56tGA6kiFohhXgQ2ze0gL9V/iLuMI/:QMkI8by56YA6k4OR2gU5I/ |
MALICIOUS
Application was dropped or rewritten from another process
- ELB_X_SLAY.exe (PID: 2572)
- ELB_X_SLAY.exe (PID: 2620)
Changes settings of System certificates
- ELB_X_SLAY.exe (PID: 2620)
SUSPICIOUS
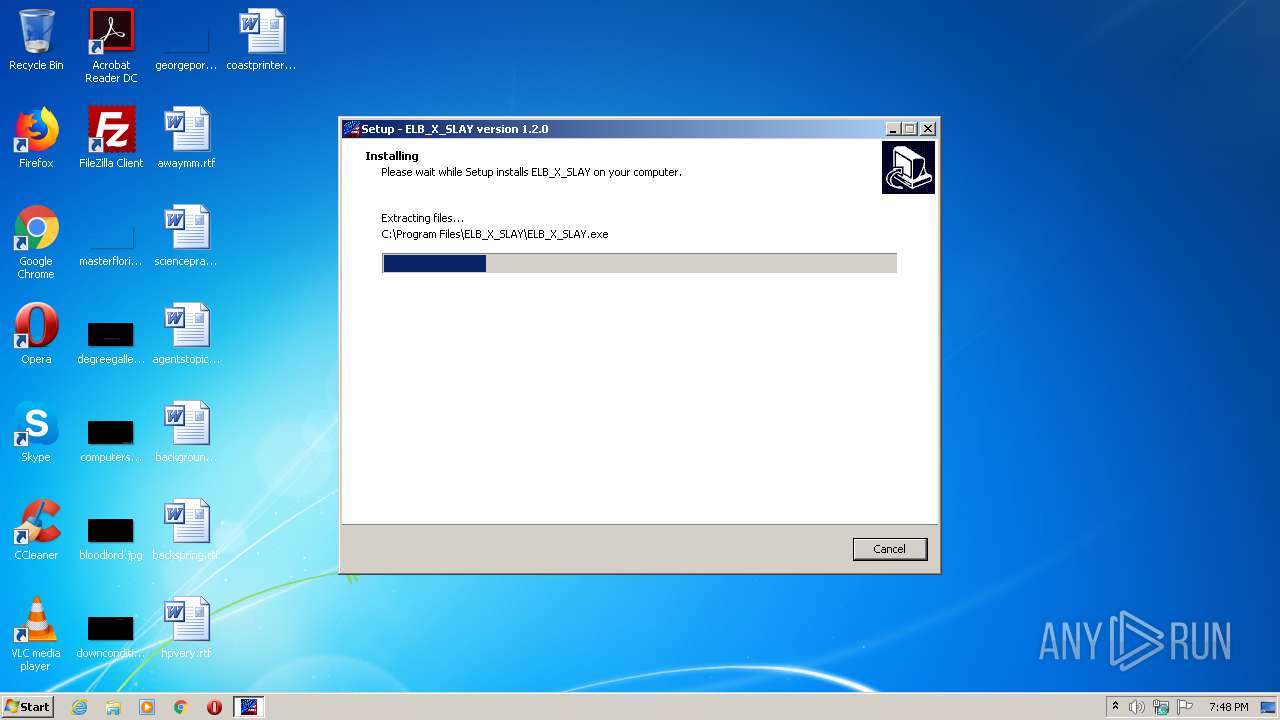
Executable content was dropped or overwritten
- Slay & ELB Launcher.exe (PID: 3284)
- Slay & ELB Launcher.exe (PID: 3616)
- Slay & ELB Launcher.tmp (PID: 2288)
- ELB_X_SLAY.exe (PID: 2620)
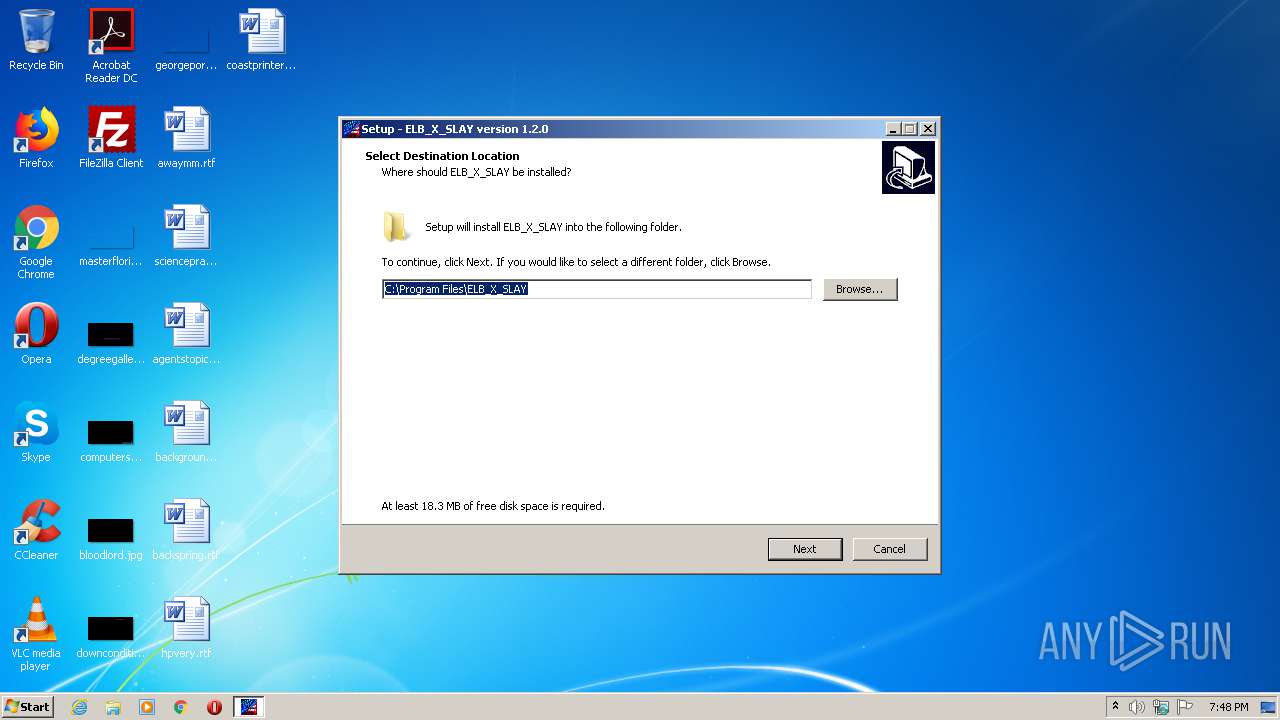
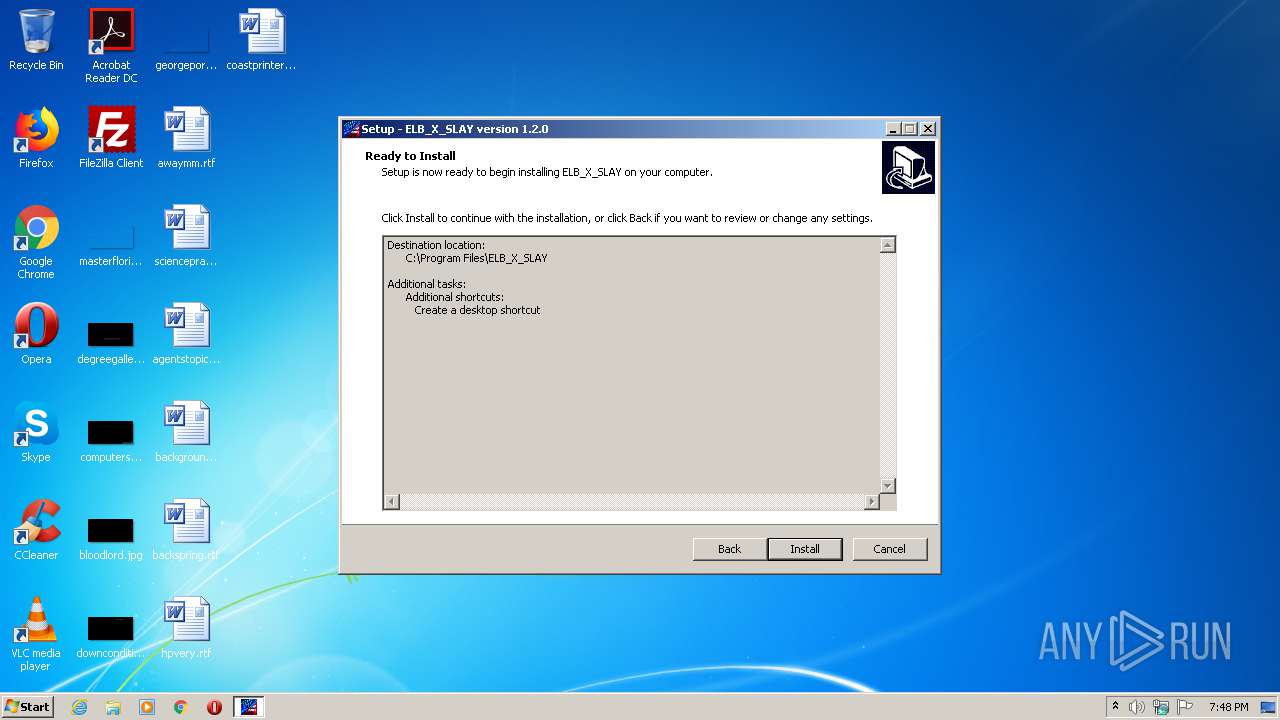
Creates a directory in Program Files
- Slay & ELB Launcher.tmp (PID: 2288)
Reads Windows owner or organization settings
- Slay & ELB Launcher.tmp (PID: 2288)
Drops a file with a compile date too recent
- Slay & ELB Launcher.tmp (PID: 2288)
Reads the Windows organization settings
- Slay & ELB Launcher.tmp (PID: 2288)
Drops a file that was compiled in debug mode
- Slay & ELB Launcher.tmp (PID: 2288)
- ELB_X_SLAY.exe (PID: 2620)
Drops a file with too old compile date
- Slay & ELB Launcher.tmp (PID: 2288)
- ELB_X_SLAY.exe (PID: 2620)
Changes default file association
- Slay & ELB Launcher.tmp (PID: 2288)
Creates files in the program directory
- ELB_X_SLAY.exe (PID: 2620)
Adds / modifies Windows certificates
- ELB_X_SLAY.exe (PID: 2620)
INFO
Application was dropped or rewritten from another process
- Slay & ELB Launcher.tmp (PID: 2592)
- Slay & ELB Launcher.tmp (PID: 2288)
Creates files in the program directory
- Slay & ELB Launcher.tmp (PID: 2288)
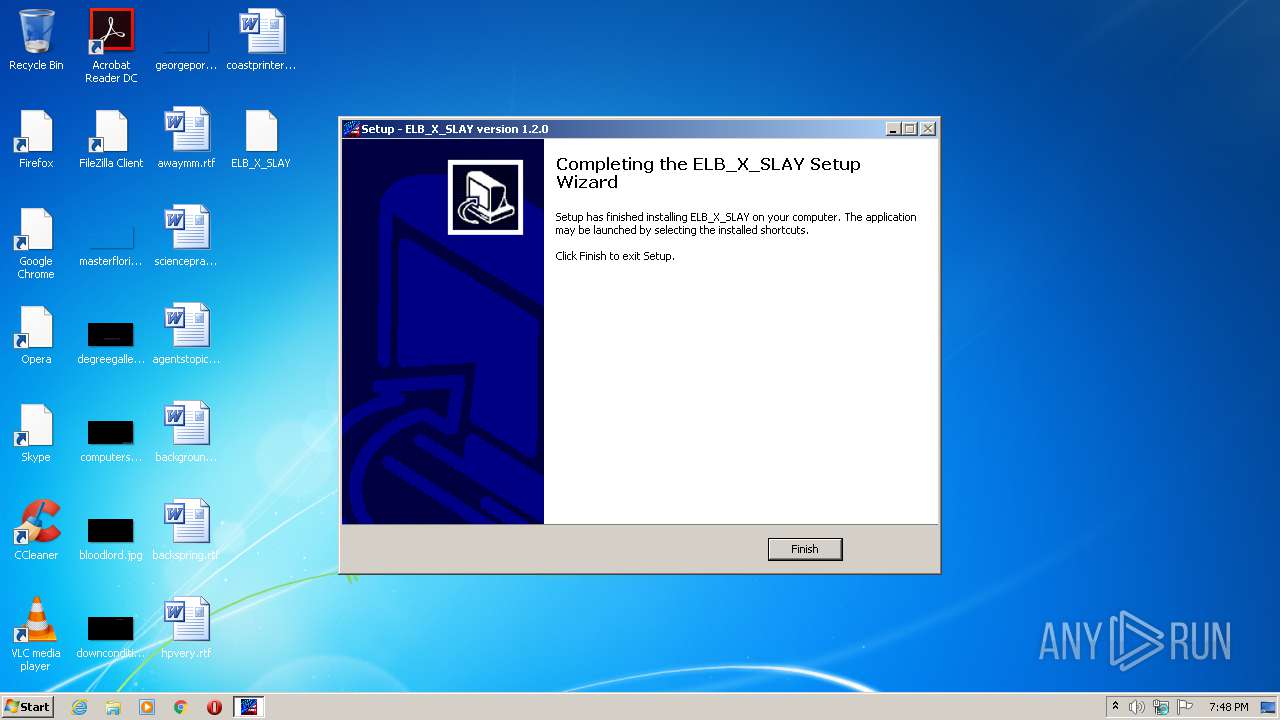
Creates a software uninstall entry
- Slay & ELB Launcher.tmp (PID: 2288)
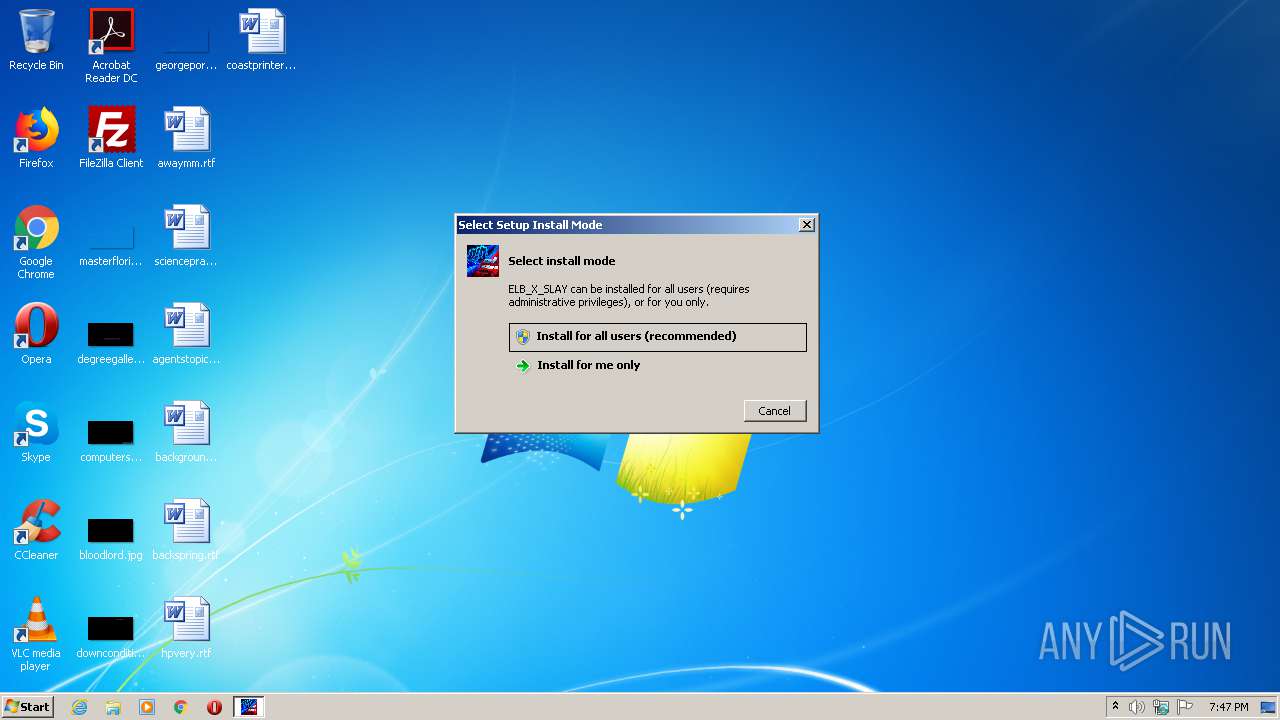
Manual execution by user
- ELB_X_SLAY.exe (PID: 2572)
- ELB_X_SLAY.exe (PID: 2620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (67.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (25.6) |
| .exe | | | Win32 Executable (generic) (2.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:11:15 10:48:30+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 741376 |
| InitializedDataSize: | 174592 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb5eec |
| OSVersion: | 6.1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
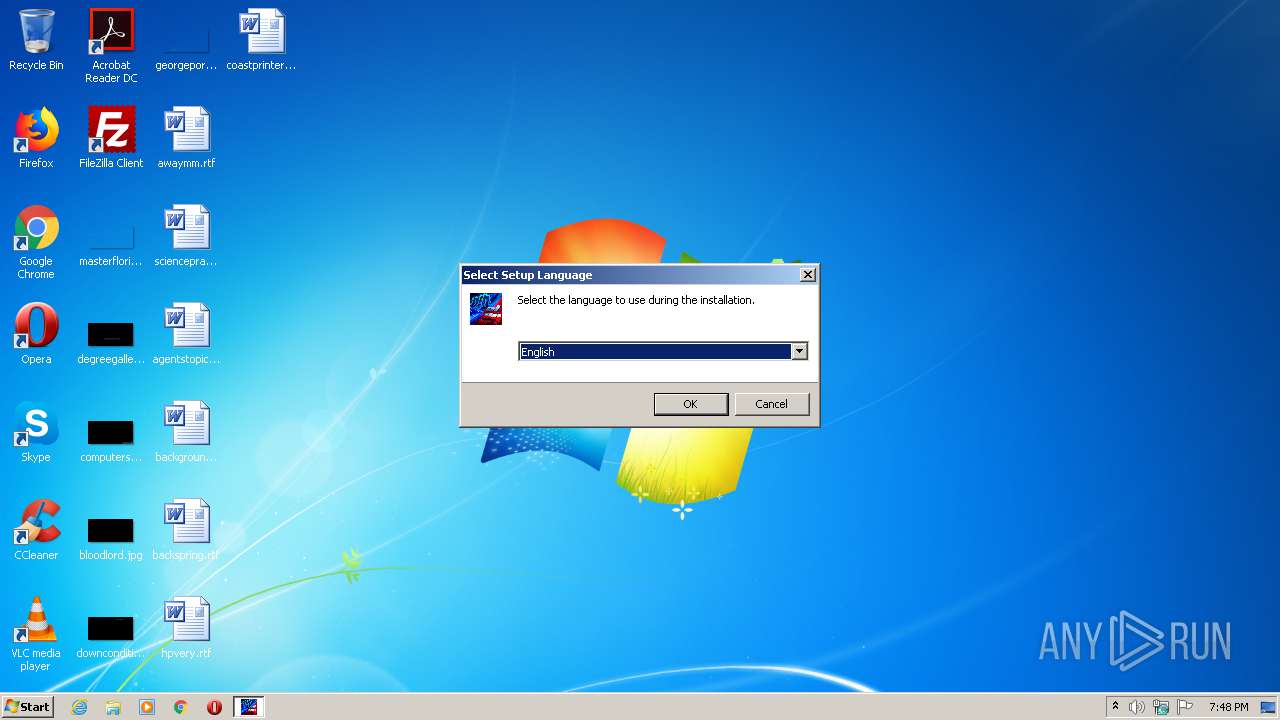
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | ELB Company, Inc. |
| FileDescription: | ELB_X_SLAY Setup |
| FileVersion: | |
| LegalCopyright: | |
| OriginalFileName: | |
| ProductName: | ELB_X_SLAY |
| ProductVersion: | 1.2.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Nov-2020 09:48:30 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | ELB Company, Inc. |
| FileDescription: | ELB_X_SLAY Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| OriginalFileName: | - |
| ProductName: | ELB_X_SLAY |
| ProductVersion: | 1.2.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 15-Nov-2020 09:48:30 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000B361C | 0x000B3800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.35606 |
.itext | 0x000B5000 | 0x00001688 | 0x00001800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.97275 |
.data | 0x000B7000 | 0x000037A4 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.0444 |
.bss | 0x000BB000 | 0x00006DE8 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x000C2000 | 0x00000F36 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.8987 |
.didata | 0x000C3000 | 0x000001A4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.75636 |
.edata | 0x000C4000 | 0x0000009A | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.87222 |
.tls | 0x000C5000 | 0x00000018 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x000C6000 | 0x0000005D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.38389 |
.rsrc | 0x000C7000 | 0x00025BF4 | 0x00025C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.89678 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.18295 | 1830 | Latin 1 / Western European | English - United States | RT_MANIFEST |
4086 | 3.16547 | 864 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4087 | 3.40938 | 608 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4088 | 3.31153 | 1116 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4089 | 3.33977 | 1036 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 3.36723 | 724 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4091 | 3.33978 | 184 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 3.15425 | 156 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 3.31895 | 884 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.28786 | 920 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
netapi32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x000BE63C |
__dbk_fcall_wrapper | 2 | 0x0000D0A0 |
TMethodImplementationIntercept | 3 | 0x00054060 |
Total processes
49
Monitored processes
6
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2288 | "C:\Users\admin\AppData\Local\Temp\is-FQ843.tmp\Slay & ELB Launcher.tmp" /SL5="$4014E,14204313,916992,C:\Users\admin\AppData\Local\Temp\Slay & ELB Launcher.exe" /SPAWNWND=$50134 /NOTIFYWND=$30154 /ALLUSERS | C:\Users\admin\AppData\Local\Temp\is-FQ843.tmp\Slay & ELB Launcher.tmp | Slay & ELB Launcher.exe | ||||||||||||
User: admin Company: ELB Company, Inc. Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2572 | "C:\Program Files\ELB_X_SLAY\ELB_X_SLAY.exe" | C:\Program Files\ELB_X_SLAY\ELB_X_SLAY.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: ELB X SLAY Exit code: 3221226540 Version: 1.2.0.0 Modules
| |||||||||||||||
| 2592 | "C:\Users\admin\AppData\Local\Temp\is-3P76N.tmp\Slay & ELB Launcher.tmp" /SL5="$30154,14204313,916992,C:\Users\admin\AppData\Local\Temp\Slay & ELB Launcher.exe" | C:\Users\admin\AppData\Local\Temp\is-3P76N.tmp\Slay & ELB Launcher.tmp | — | Slay & ELB Launcher.exe | |||||||||||
User: admin Company: ELB Company, Inc. Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2620 | "C:\Program Files\ELB_X_SLAY\ELB_X_SLAY.exe" | C:\Program Files\ELB_X_SLAY\ELB_X_SLAY.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: ELB X SLAY Exit code: 0 Version: 1.2.0.0 Modules
| |||||||||||||||
| 3284 | "C:\Users\admin\AppData\Local\Temp\Slay & ELB Launcher.exe" | C:\Users\admin\AppData\Local\Temp\Slay & ELB Launcher.exe | explorer.exe | ||||||||||||
User: admin Company: ELB Company, Inc. Integrity Level: MEDIUM Description: ELB_X_SLAY Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 3616 | "C:\Users\admin\AppData\Local\Temp\Slay & ELB Launcher.exe" /SPAWNWND=$50134 /NOTIFYWND=$30154 /ALLUSERS | C:\Users\admin\AppData\Local\Temp\Slay & ELB Launcher.exe | Slay & ELB Launcher.tmp | ||||||||||||
User: admin Company: ELB Company, Inc. Integrity Level: HIGH Description: ELB_X_SLAY Setup Exit code: 0 Version: Modules
| |||||||||||||||
Total events
630
Read events
566
Write events
58
Delete events
6
Modification events
| (PID) Process: | (2288) Slay & ELB Launcher.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: F0080000CA5BD4F15314D701 | |||
| (PID) Process: | (2288) Slay & ELB Launcher.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 15B7B1E86EF8A28786EA9CB157477CE71F50AB5C857B9BA147D62D47037EBF79 | |||
| (PID) Process: | (2288) Slay & ELB Launcher.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2288) Slay & ELB Launcher.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\ELB_X_SLAY\ELB_X_SLAY.exe | |||
| (PID) Process: | (2288) Slay & ELB Launcher.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 2165FA64004381BF7C8D6192125D0C42844A215C8C71CA872CF4E3F550C92385 | |||
| (PID) Process: | (2288) Slay & ELB Launcher.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.myp\OpenWithProgids |
| Operation: | write | Name: | ELB_X_SLAYFile.myp |
Value: | |||
| (PID) Process: | (2288) Slay & ELB Launcher.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\ELB_X_SLAYFile.myp |
| Operation: | write | Name: | (default) |
Value: ELB_X_SLAY File | |||
| (PID) Process: | (2288) Slay & ELB Launcher.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\ELB_X_SLAYFile.myp\DefaultIcon |
| Operation: | write | Name: | (default) |
Value: C:\Program Files\ELB_X_SLAY\ELB_X_SLAY.exe,0 | |||
| (PID) Process: | (2288) Slay & ELB Launcher.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\ELB_X_SLAYFile.myp\shell\open\command |
| Operation: | write | Name: | (default) |
Value: "C:\Program Files\ELB_X_SLAY\ELB_X_SLAY.exe" "%1" | |||
| (PID) Process: | (2288) Slay & ELB Launcher.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Applications\ELB_X_SLAY.exe\SupportedTypes |
| Operation: | write | Name: | .myp |
Value: | |||
Executable files
14
Suspicious files
0
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2288 | Slay & ELB Launcher.tmp | C:\Program Files\ELB_X_SLAY\is-C0VLI.tmp | — | |
MD5:— | SHA256:— | |||
| 2288 | Slay & ELB Launcher.tmp | C:\Program Files\ELB_X_SLAY\is-3UU27.tmp | — | |
MD5:— | SHA256:— | |||
| 2288 | Slay & ELB Launcher.tmp | C:\Program Files\ELB_X_SLAY\is-Q393N.tmp | — | |
MD5:— | SHA256:— | |||
| 2288 | Slay & ELB Launcher.tmp | C:\Program Files\ELB_X_SLAY\is-QC7MF.tmp | — | |
MD5:— | SHA256:— | |||
| 2288 | Slay & ELB Launcher.tmp | C:\Program Files\ELB_X_SLAY\is-QCDCI.tmp | — | |
MD5:— | SHA256:— | |||
| 2288 | Slay & ELB Launcher.tmp | C:\Program Files\ELB_X_SLAY\is-SEHK6.tmp | — | |
MD5:— | SHA256:— | |||
| 2288 | Slay & ELB Launcher.tmp | C:\Program Files\ELB_X_SLAY\is-60LOM.tmp | — | |
MD5:— | SHA256:— | |||
| 2288 | Slay & ELB Launcher.tmp | C:\Program Files\ELB_X_SLAY\is-36T6B.tmp | — | |
MD5:— | SHA256:— | |||
| 2288 | Slay & ELB Launcher.tmp | C:\Program Files\ELB_X_SLAY\is-LV7UU.tmp | — | |
MD5:— | SHA256:— | |||
| 2288 | Slay & ELB Launcher.tmp | C:\Program Files\ELB_X_SLAY\is-LJ1V5.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2620 | ELB_X_SLAY.exe | GET | 200 | 172.67.150.196:80 | http://elbmodzz.com/exe/launcher/maj/stats.php | US | text | 73 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 172.67.150.196:80 | elbmodzz.com | — | US | suspicious |
2620 | ELB_X_SLAY.exe | 172.67.150.196:443 | elbmodzz.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
elbmodzz.com |
| suspicious |