| File name: | 2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom |
| Full analysis: | https://app.any.run/tasks/8cb9f6d3-483a-4223-9b3f-f065c53c176c |
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2025, 02:17:08 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | E062403CC2BB29C1B528311DC7CFFD0E |
| SHA1: | 9EB70C1E13F1F612466FF8EF20E3BAE9E1932383 |
| SHA256: | E9C0ADB7671A01D5C0D5DF559526C9930CAF2AB8BBF4D1926DE738E53DA90982 |
| SSDEEP: | 98304:TjsBHzPnvEAEZGPBzJx7WQizOMAu8PHieEM1SBkyZiJYfpx7AHHWWmOOei8yRS48:kOjhHbxrWvzPuUq6ERaqT2yaRukG |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops legitimate windows executable
- 2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe (PID: 2108)
The process drops C-runtime libraries
- 2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe (PID: 2108)
Executable content was dropped or overwritten
- 2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe (PID: 2108)
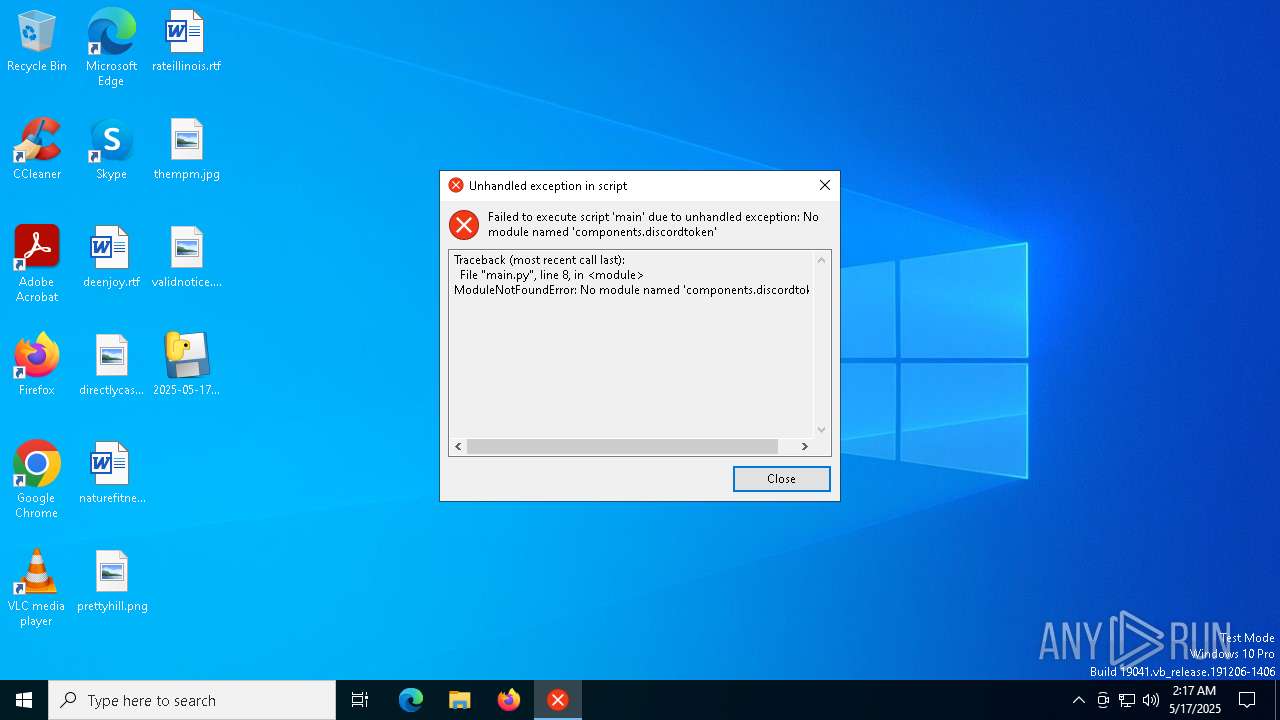
Process drops python dynamic module
- 2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe (PID: 2108)
Application launched itself
- 2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe (PID: 2108)
Loads Python modules
- 2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe (PID: 5416)
Starts CMD.EXE for commands execution
- 2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe (PID: 5416)
INFO
Checks supported languages
- 2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe (PID: 2108)
- 2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe (PID: 5416)
Create files in a temporary directory
- 2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe (PID: 2108)
- 2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe (PID: 5416)
Reads the computer name
- 2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe (PID: 2108)
- 2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe (PID: 5416)
The sample compiled with english language support
- 2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe (PID: 2108)
Reads the machine GUID from the registry
- 2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe (PID: 5416)
Checks operating system version
- 2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe (PID: 5416)
Checks proxy server information
- slui.exe (PID: 3132)
Reads the software policy settings
- slui.exe (PID: 3132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:05:08 22:25:16+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.32 |
| CodeSize: | 165888 |
| InitializedDataSize: | 154112 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xafa0 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
Total processes
128
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2108 | "C:\Users\admin\Desktop\2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe" | C:\Users\admin\Desktop\2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 3132 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3240 | C:\WINDOWS\system32\cmd.exe /c "ver" | C:\Windows\System32\cmd.exe | — | 2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5204 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5416 | "C:\Users\admin\Desktop\2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe" | C:\Users\admin\Desktop\2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe | — | 2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
Total events
6 474
Read events
6 474
Write events
0
Delete events
0
Modification events
Executable files
94
Suspicious files
3
Text files
40
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2108 | 2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe | C:\Users\admin\AppData\Local\Temp\_MEI21082\Crypto\Cipher\_Salsa20.pyd | executable | |
MD5:E3AE69E44C4C82D83082BBB8C25AA8DD | SHA256:4229235814BBEE62311E3623C07898B03D3B22281CD4E5F1A87B86450B1B740F | |||
| 2108 | 2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe | C:\Users\admin\AppData\Local\Temp\_MEI21082\Crypto\Cipher\_raw_des3.pyd | executable | |
MD5:D892F9D789C22787D846E405D0240987 | SHA256:100CD322EA2F8E3997432D6E292373F3A07F75818C7802D7386E9810BEE619B0 | |||
| 2108 | 2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe | C:\Users\admin\AppData\Local\Temp\_MEI21082\Crypto\Cipher\_raw_cbc.pyd | executable | |
MD5:FE44F698198190DE574DC193A0E1B967 | SHA256:32FA416A29802EB0017A2C7360BF942EDB132D4671168DE26BD4C3E94D8DE919 | |||
| 2108 | 2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe | C:\Users\admin\AppData\Local\Temp\_MEI21082\Crypto\Cipher\_raw_des.pyd | executable | |
MD5:B0EEF5CEAE8BA5E2A04C17B2B6AE87B5 | SHA256:C9BBA124BE36ADA4549276D984BB3812EE2207C7DBF646EC6DF9A968E83205FB | |||
| 2108 | 2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe | C:\Users\admin\AppData\Local\Temp\_MEI21082\Crypto\Cipher\_raw_ecb.pyd | executable | |
MD5:F94726F6B584647142EA6D5818B0349D | SHA256:B98297FD093E8AF7FCA2628C23A9916E767540C3C6FA8894394B5B97FFEC3174 | |||
| 2108 | 2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe | C:\Users\admin\AppData\Local\Temp\_MEI21082\Crypto\Cipher\_raw_cast.pyd | executable | |
MD5:243E336DEC71A28E7F61548A2425A2E1 | SHA256:BF53063304119CF151F22809356B5B4E44799131BBAB5319736D0321F3012238 | |||
| 2108 | 2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe | C:\Users\admin\AppData\Local\Temp\_MEI21082\Crypto\Cipher\_raw_ocb.pyd | executable | |
MD5:A76AEB47A31FD7F652C067AC1EA6D227 | SHA256:C816F4A89CE6126DA70CB44062294A6A4AC0F73EC3A73EAD9269425B7B82288A | |||
| 2108 | 2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe | C:\Users\admin\AppData\Local\Temp\_MEI21082\Crypto\Cipher\_raw_ctr.pyd | executable | |
MD5:D67F83D1482D9600AC012868FB49D16E | SHA256:AA463CD4D0B4BBD4159650D66C11A699B23775BF92455FB58A2206B932A65FEC | |||
| 2108 | 2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe | C:\Users\admin\AppData\Local\Temp\_MEI21082\Crypto\Hash\_BLAKE2b.pyd | executable | |
MD5:1BF5CD751AED60DD92D0AB3CE6D773FA | SHA256:CDA73AF34E4F542646952BBCB71559CCBDF3695AA74ED41D37A4A7D1F932A42D | |||
| 2108 | 2025-05-17_e062403cc2bb29c1b528311dc7cffd0e_black-basta_cobalt-strike_satacom.exe | C:\Users\admin\AppData\Local\Temp\_MEI21082\Crypto\Cipher\_raw_eksblowfish.pyd | executable | |
MD5:E5021B9925A53B20946C93B5BF686647 | SHA256:87922D0EE99AF46080AFD4BAA2F96219FA195731C0745FCB9C7789338ECC778F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
20
DNS requests
5
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5576 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3132 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |