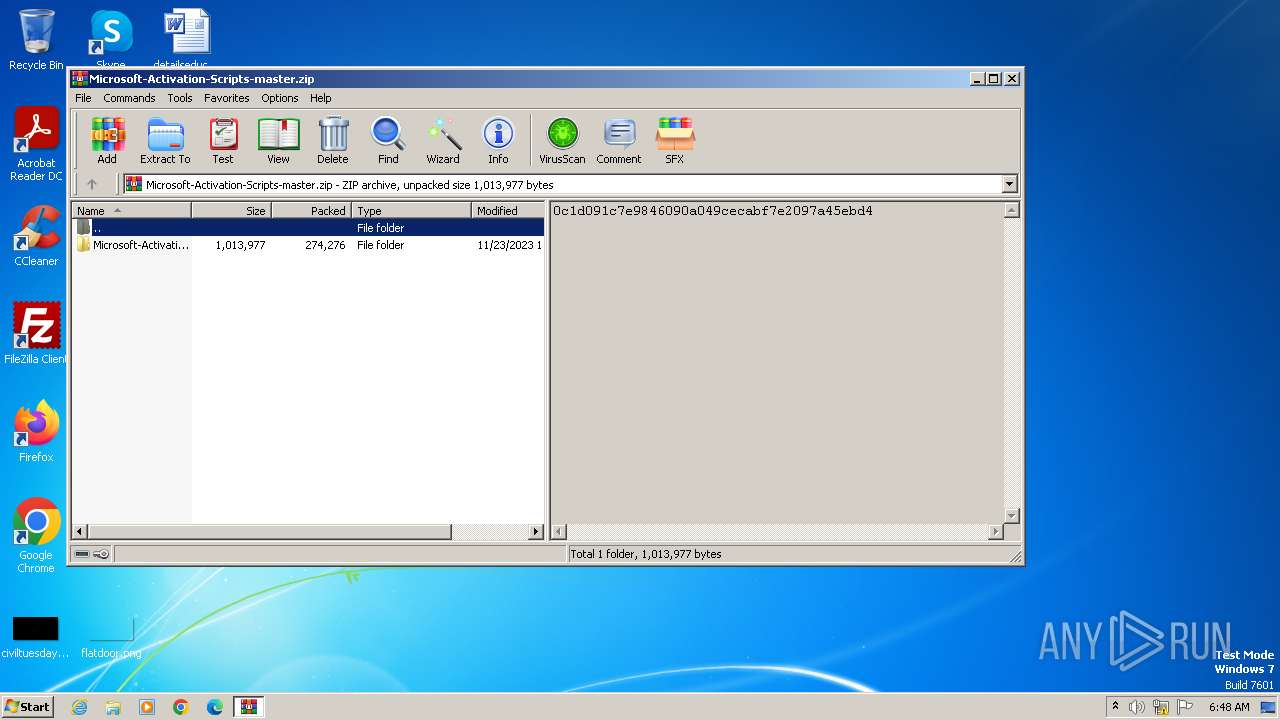
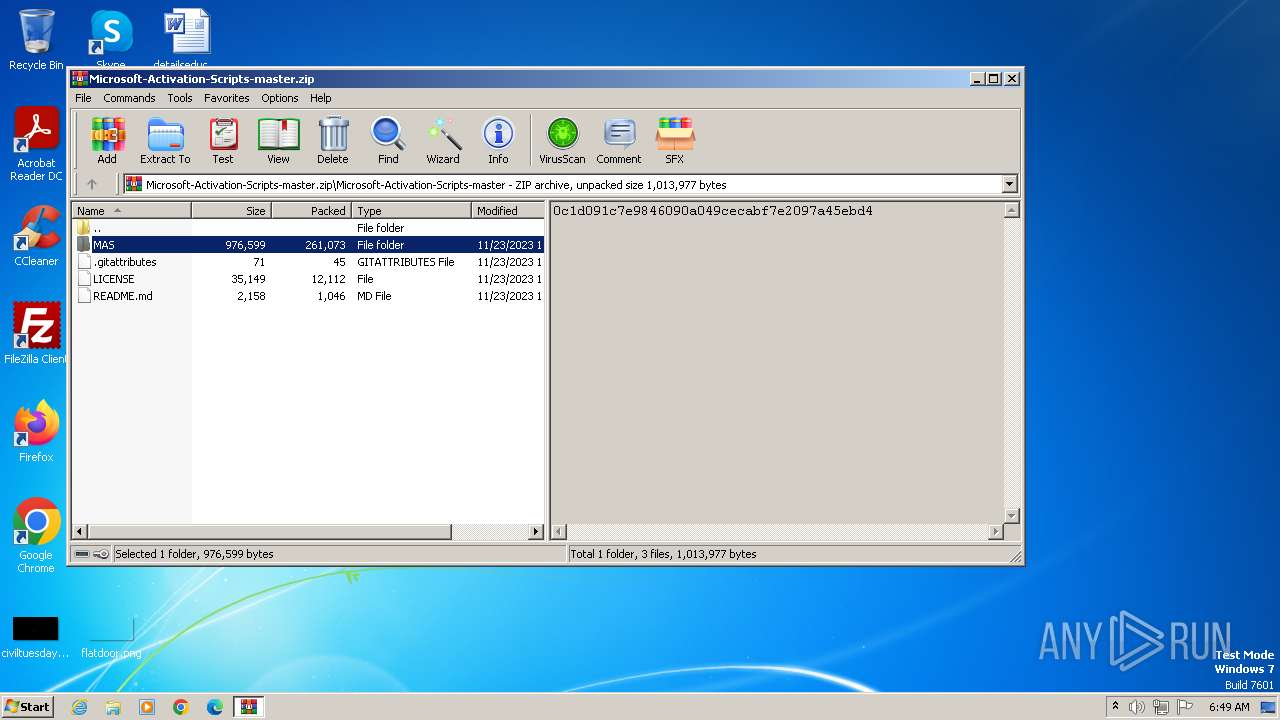
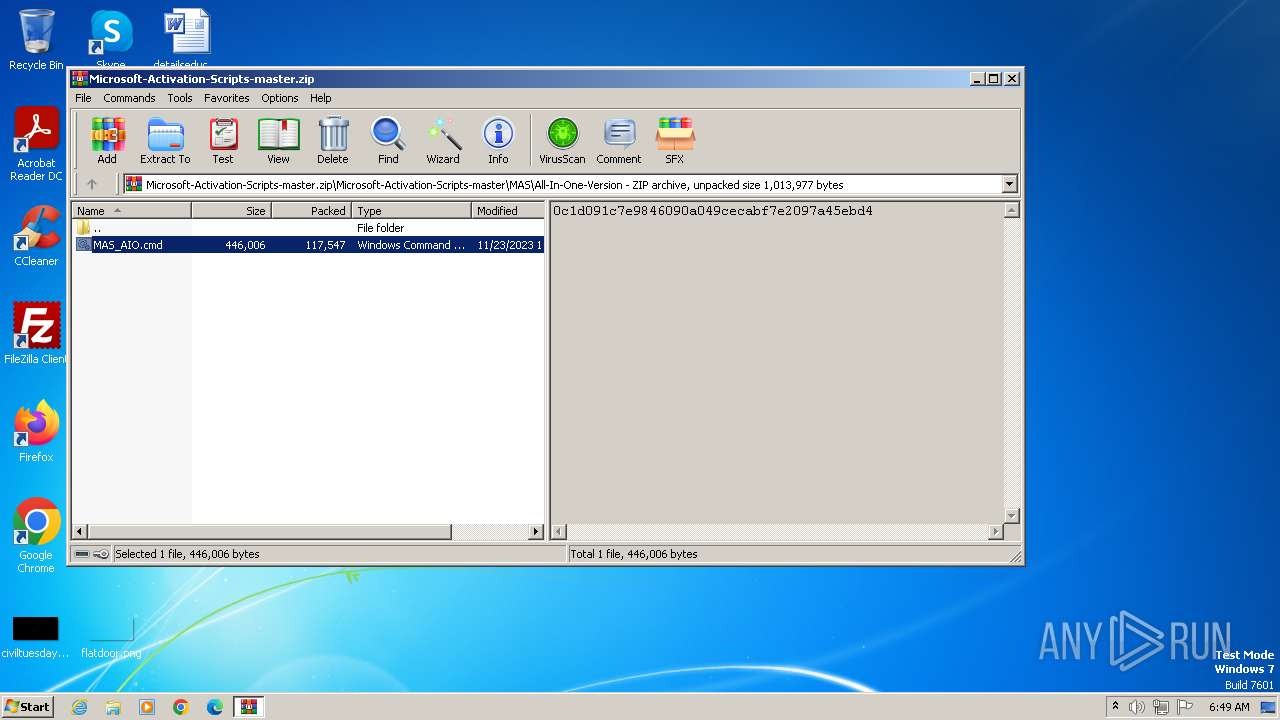
| File name: | Microsoft-Activation-Scripts-master.zip |
| Full analysis: | https://app.any.run/tasks/bc01e98f-18c6-4988-8071-37ec071f5ec0 |
| Verdict: | Malicious activity |
| Analysis date: | December 05, 2023, 06:48:37 |
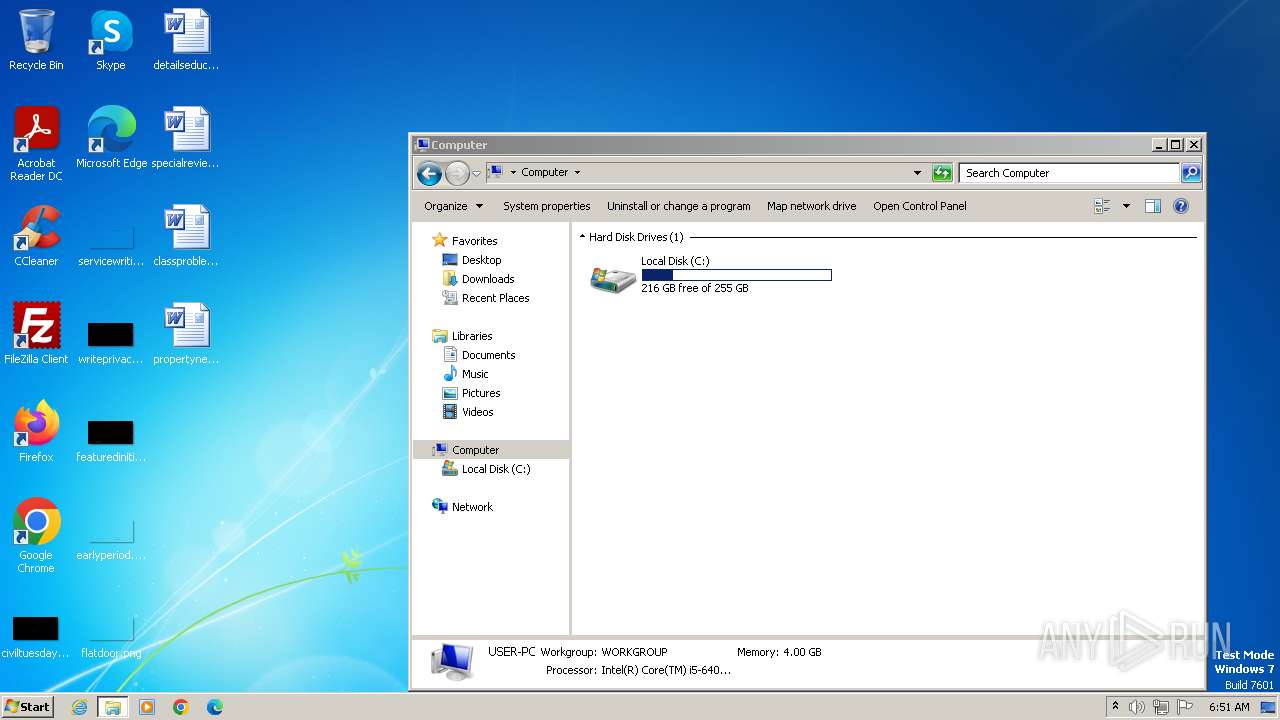
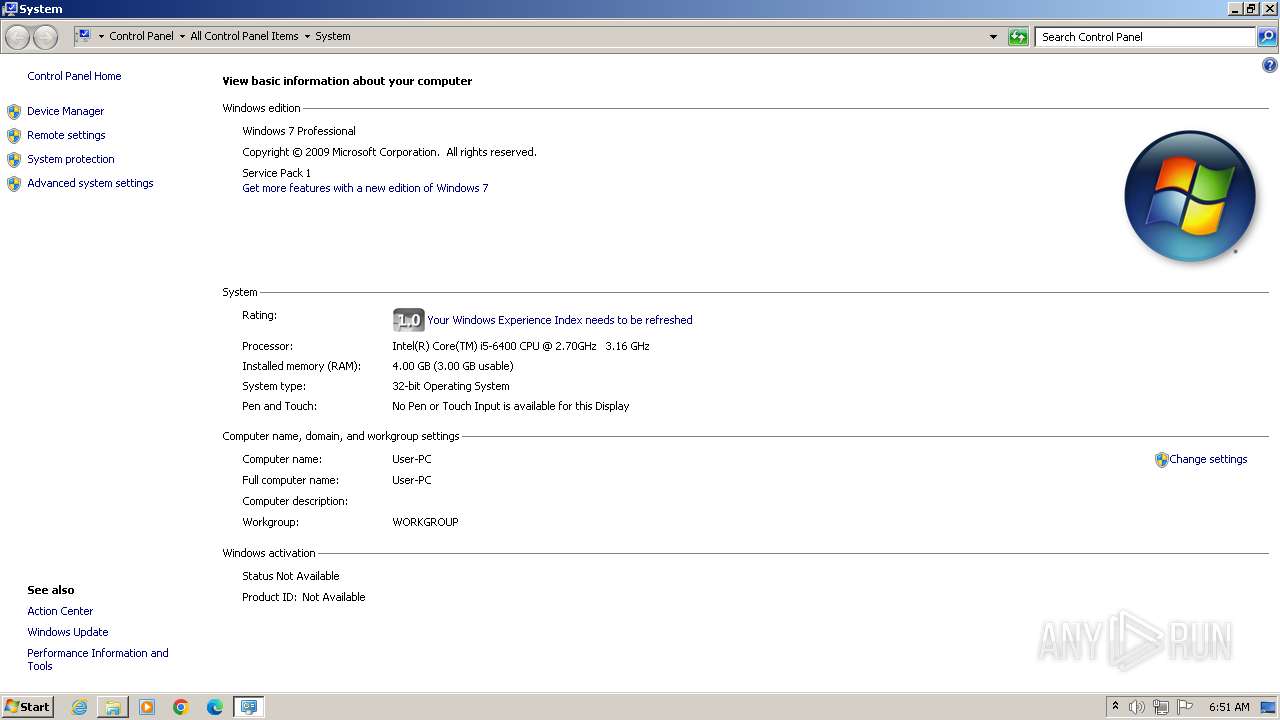
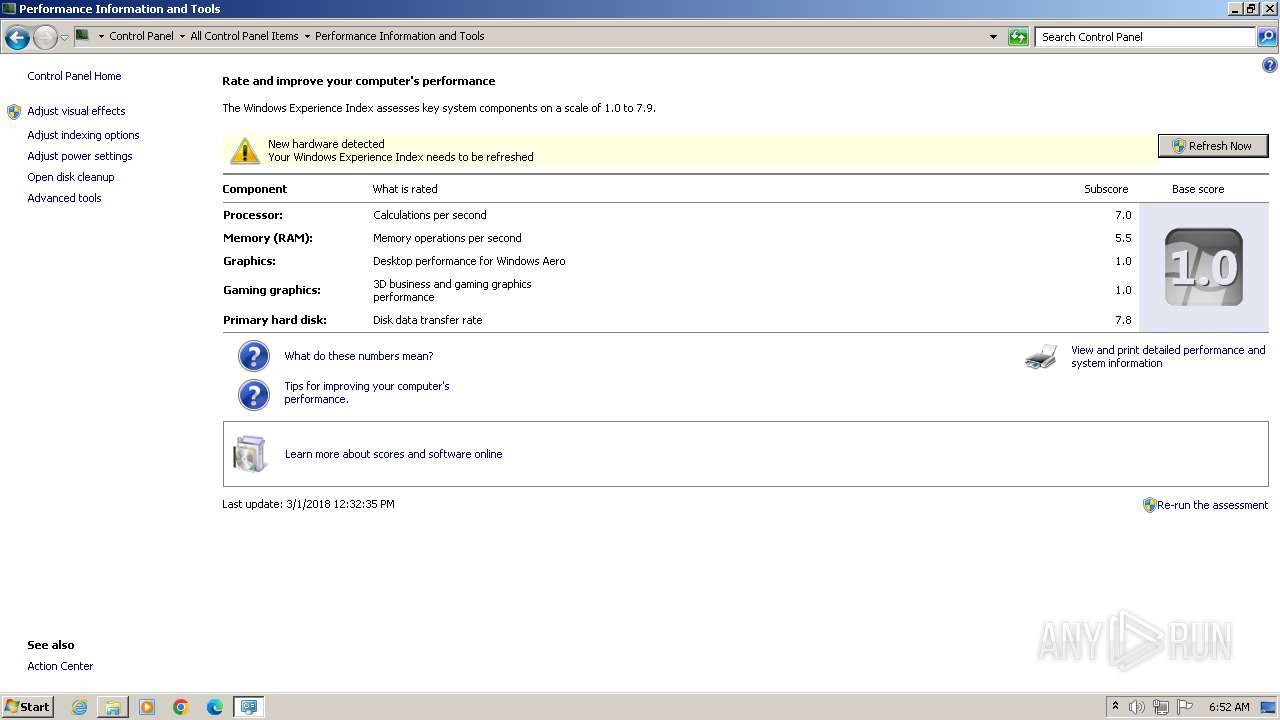
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | C97B1B8155967DECE293CEDA773C8119 |
| SHA1: | 32AB9A94C81BFAEA5158EEB80119EBB2ECD06749 |
| SHA256: | E9B8D0670D7AA43D634D84C933D363CE4DBC7E35A84BB02A58404E60399348E9 |
| SSDEEP: | 6144:BaTpyqaCx1X6rBDX84LwHOL6mdLDLGDYomUppd0J9TAGAbm3oQpen:BalTX6rBTEA6mpLgYmpH0J9MGAbm4Ien |
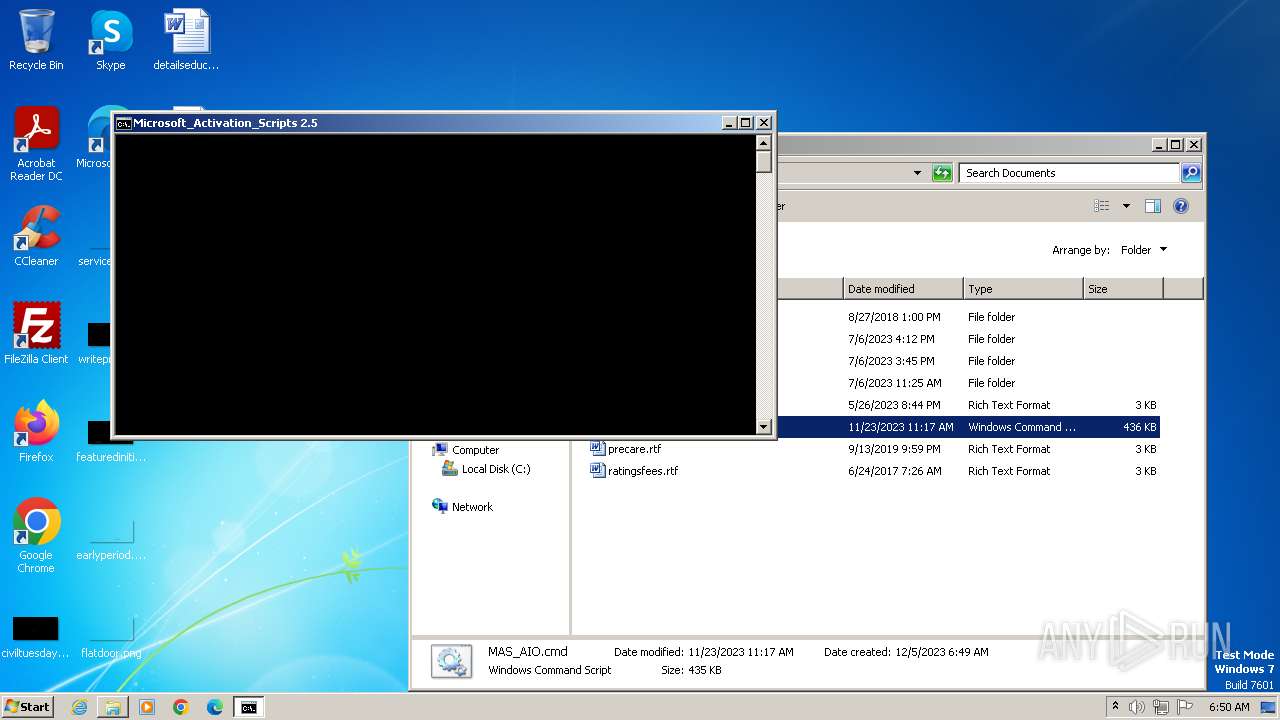
MALICIOUS
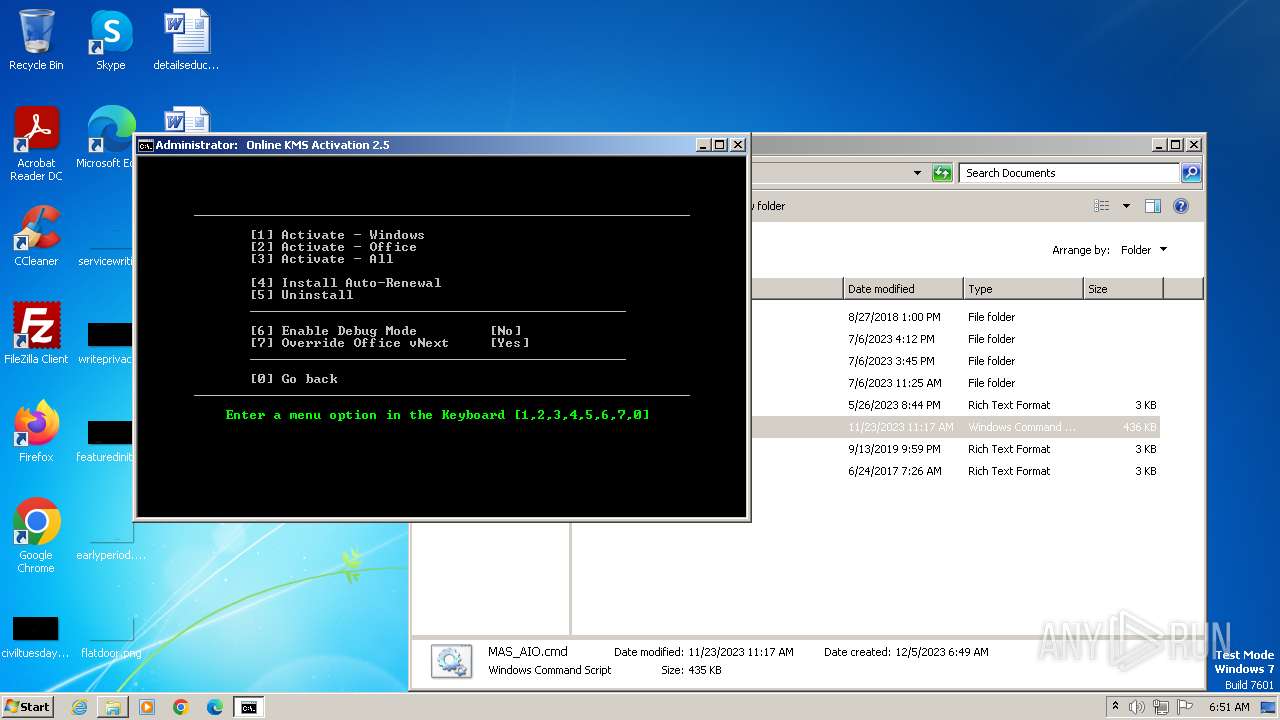
Starts NET.EXE for service management
- net.exe (PID: 3496)
- cmd.exe (PID: 2892)
SUSPICIOUS
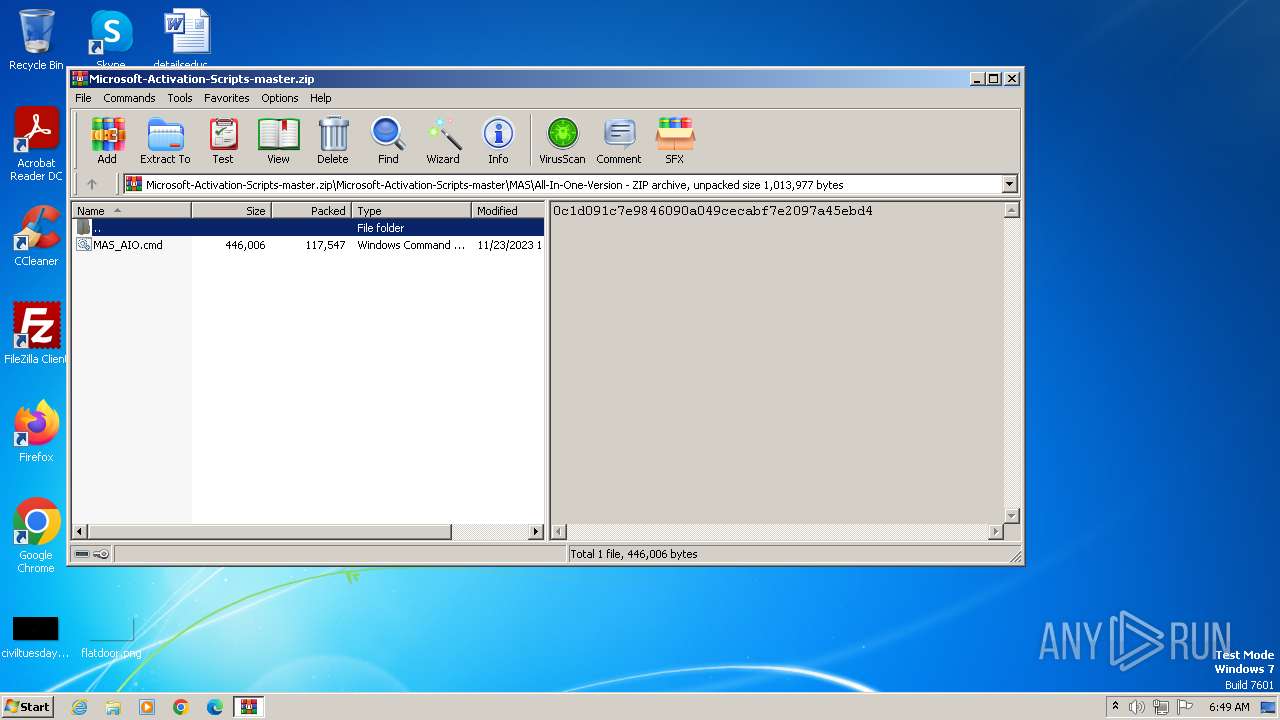
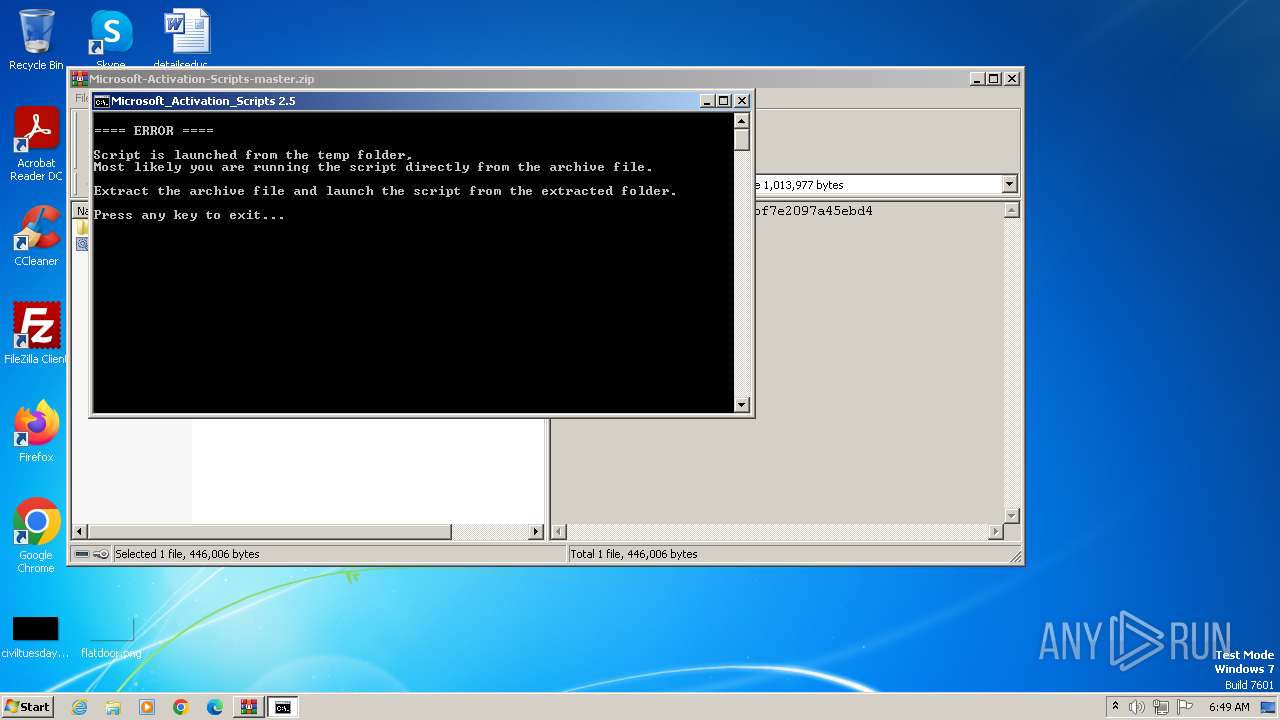
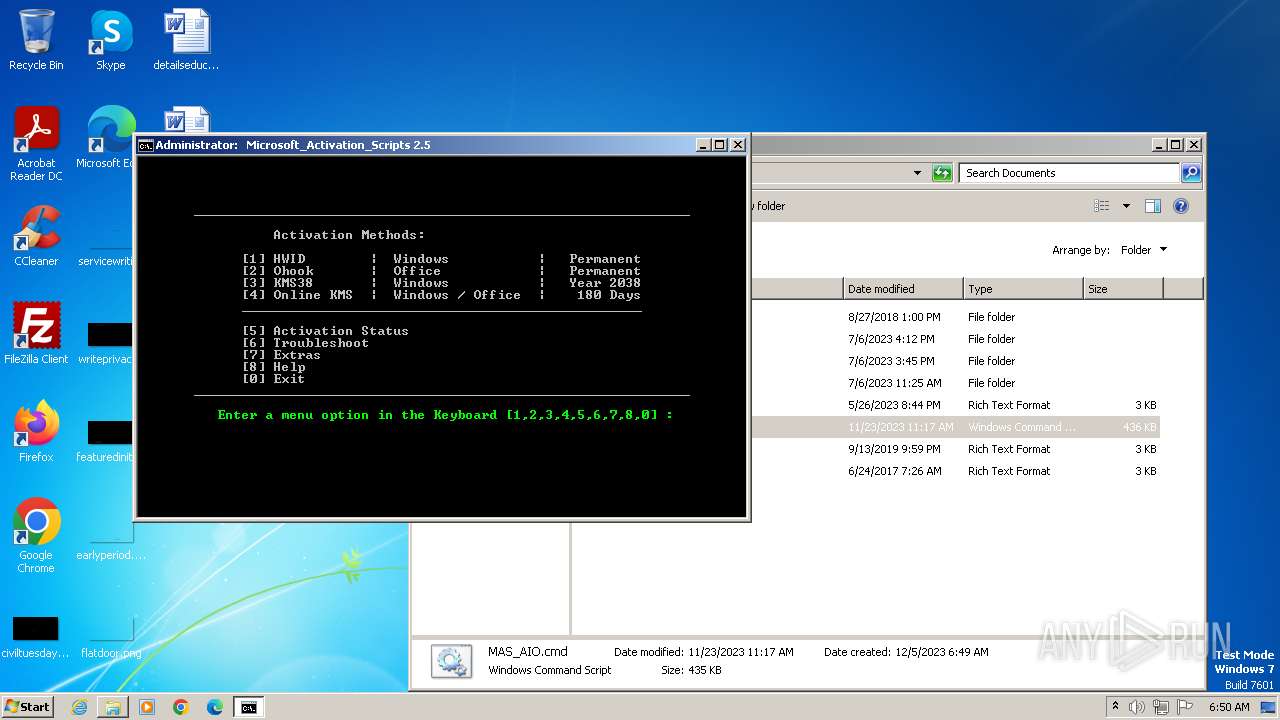
Executing commands from ".cmd" file
- WinRAR.exe (PID: 1864)
- cmd.exe (PID: 3784)
- powershell.exe (PID: 3928)
- cmd.exe (PID: 2892)
- cmd.exe (PID: 3944)
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 1864)
- cmd.exe (PID: 3784)
- cmd.exe (PID: 3944)
- powershell.exe (PID: 3928)
- cmd.exe (PID: 2892)
Starts SC.EXE for service management
- cmd.exe (PID: 3784)
- cmd.exe (PID: 3944)
- cmd.exe (PID: 2892)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 3784)
- cmd.exe (PID: 3944)
- cmd.exe (PID: 2892)
Application launched itself
- cmd.exe (PID: 3784)
- cmd.exe (PID: 2892)
- cmd.exe (PID: 3944)
Powershell version downgrade attack
- powershell.exe (PID: 3928)
- powershell.exe (PID: 3788)
- powershell.exe (PID: 1272)
- powershell.exe (PID: 1460)
Reads the Internet Settings
- powershell.exe (PID: 3928)
- WMIC.exe (PID: 948)
- WMIC.exe (PID: 2052)
- WMIC.exe (PID: 3460)
- WMIC.exe (PID: 984)
- WMIC.exe (PID: 1508)
- WMIC.exe (PID: 3220)
- WMIC.exe (PID: 3740)
- WMIC.exe (PID: 3524)
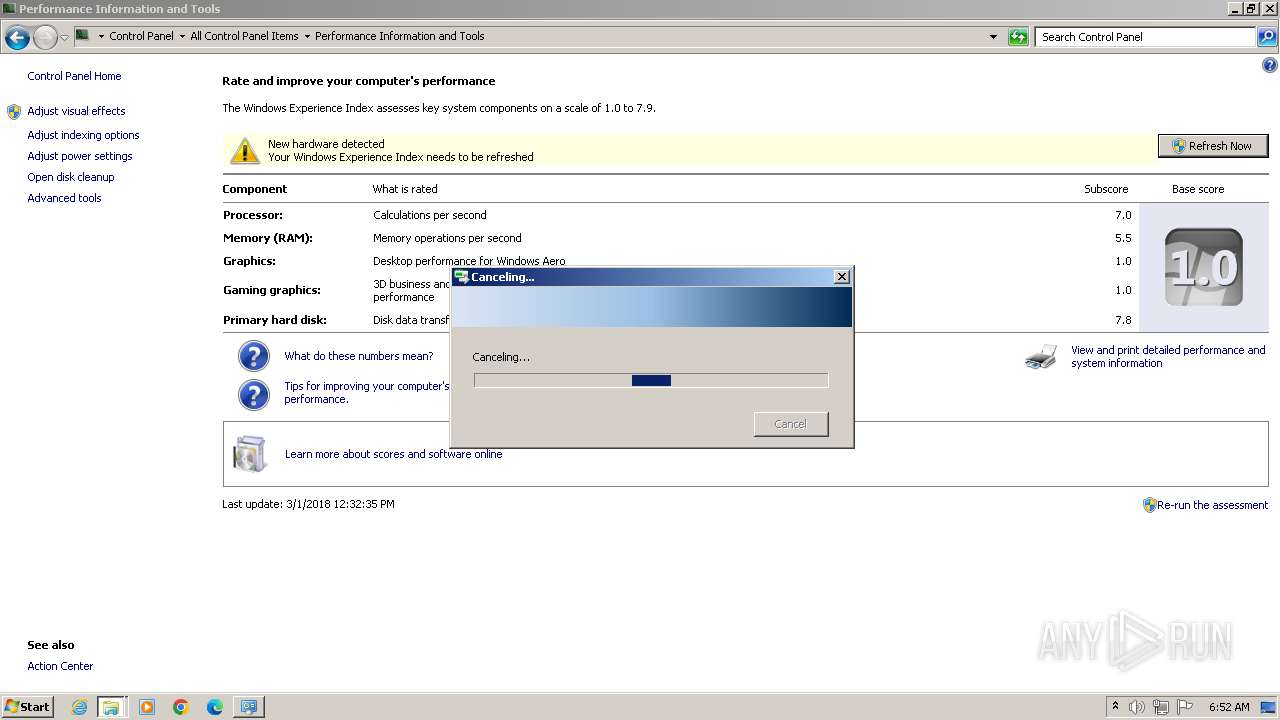
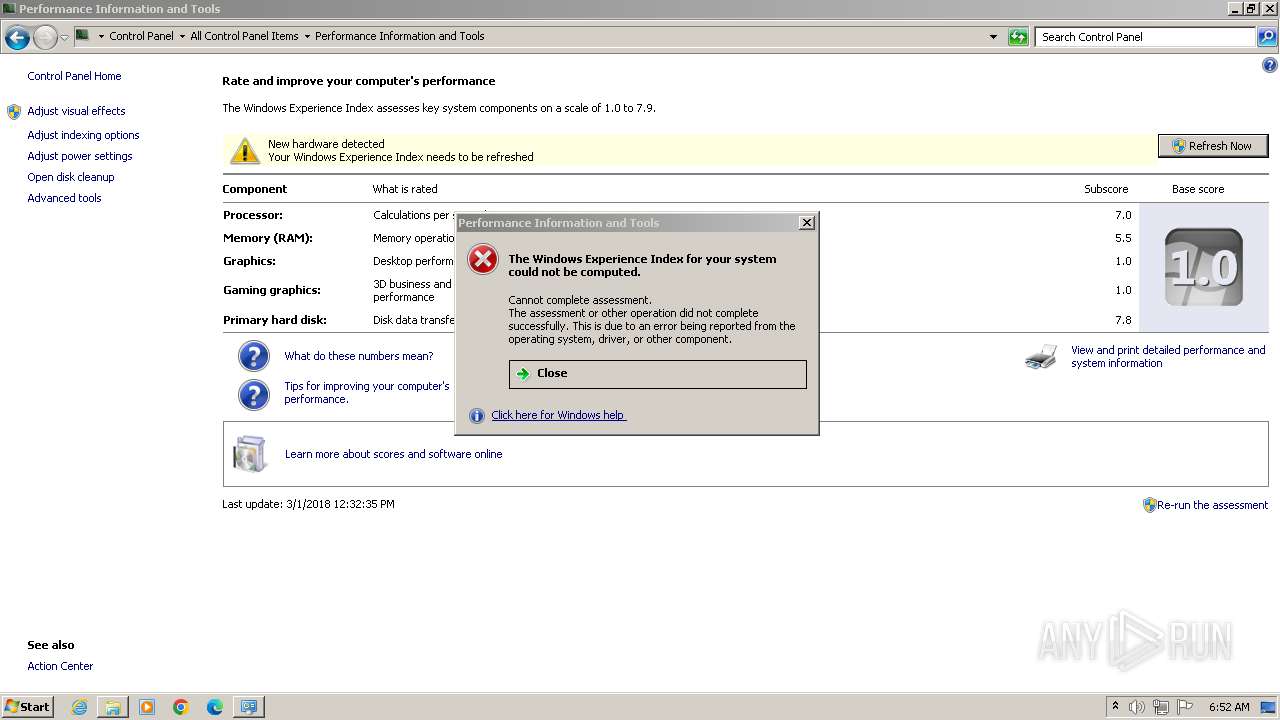
- WinSAT.exe (PID: 2464)
- WMIC.exe (PID: 3652)
- WMIC.exe (PID: 2116)
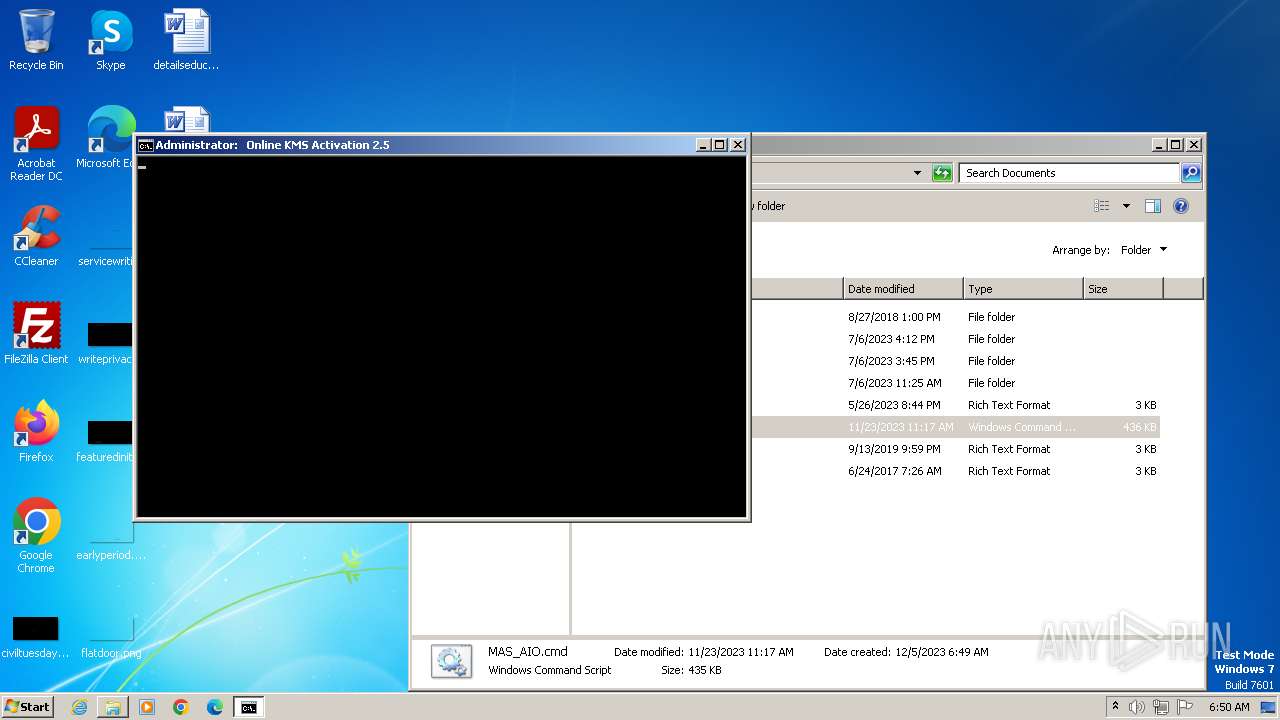
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2892)
- cmd.exe (PID: 3944)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2892)
Starts NET.EXE to map network drives
- cmd.exe (PID: 2892)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 2892)
- cmd.exe (PID: 3616)
- cmd.exe (PID: 3236)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 3752)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 2892)
INFO
Checks supported languages
- wmpnscfg.exe (PID: 2132)
- mode.com (PID: 120)
- mode.com (PID: 1760)
- mode.com (PID: 3924)
- mode.com (PID: 2612)
- mode.com (PID: 3320)
Reads the computer name
- wmpnscfg.exe (PID: 2132)
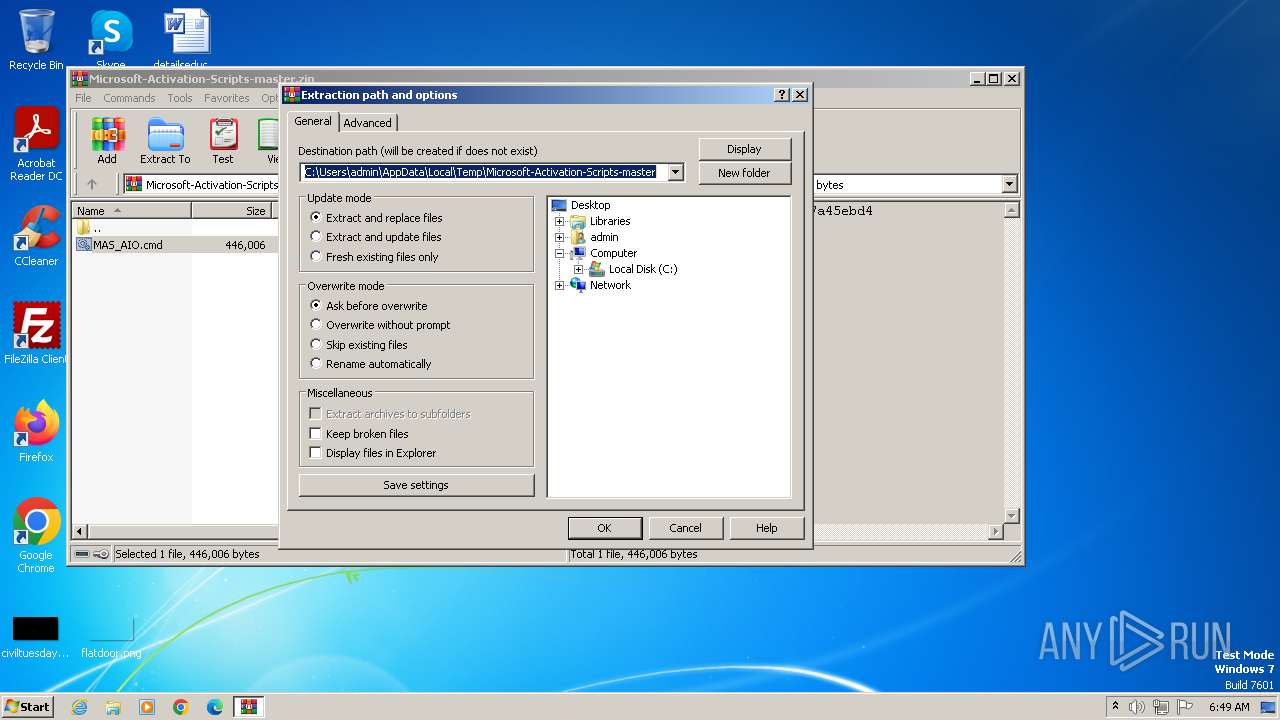
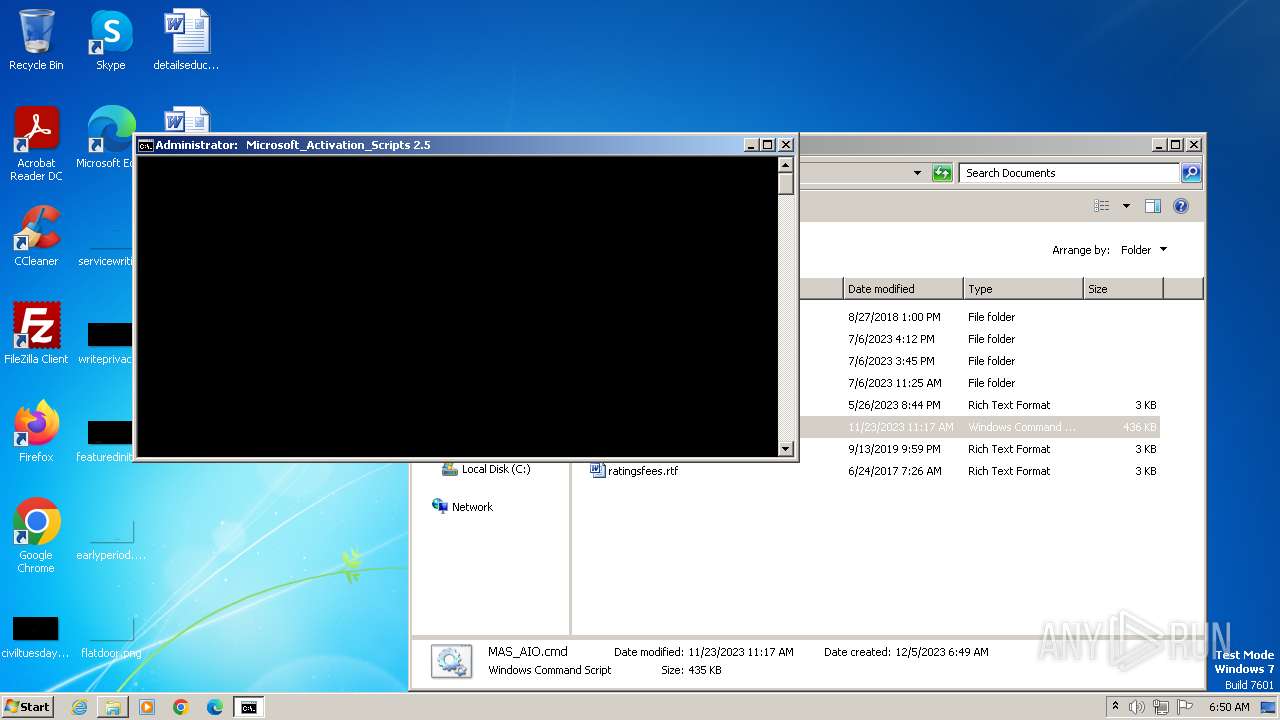
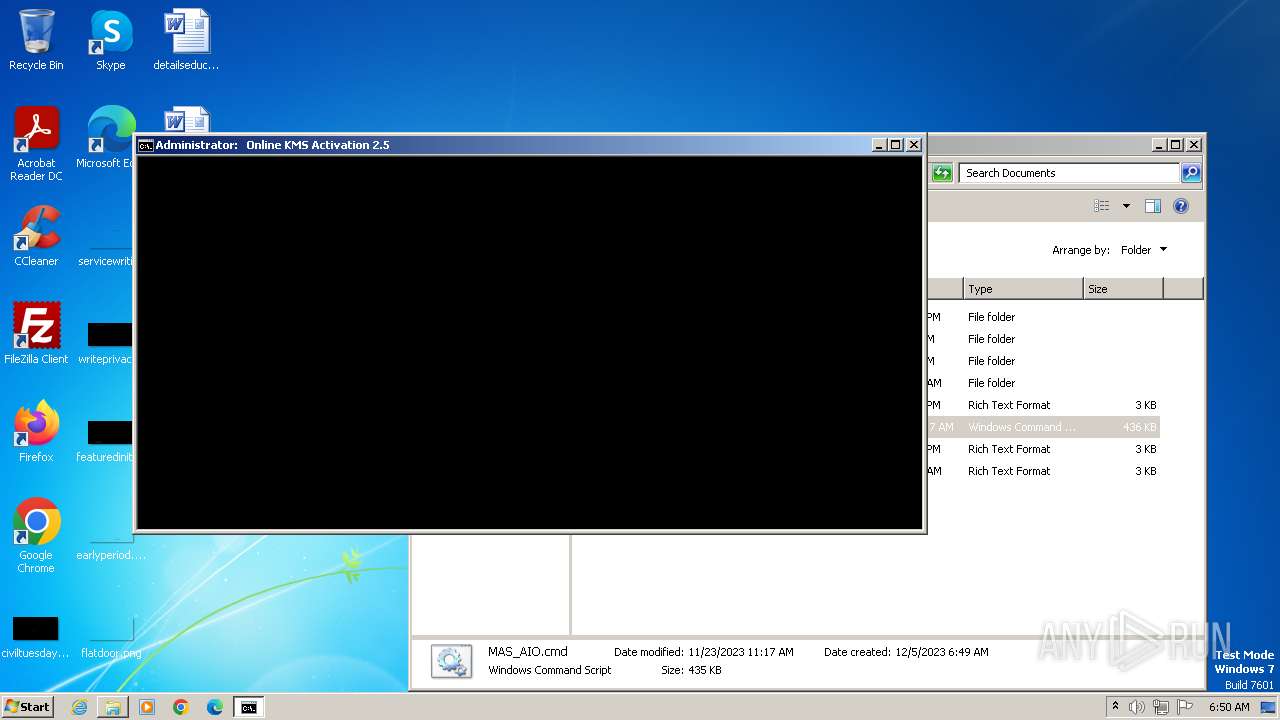
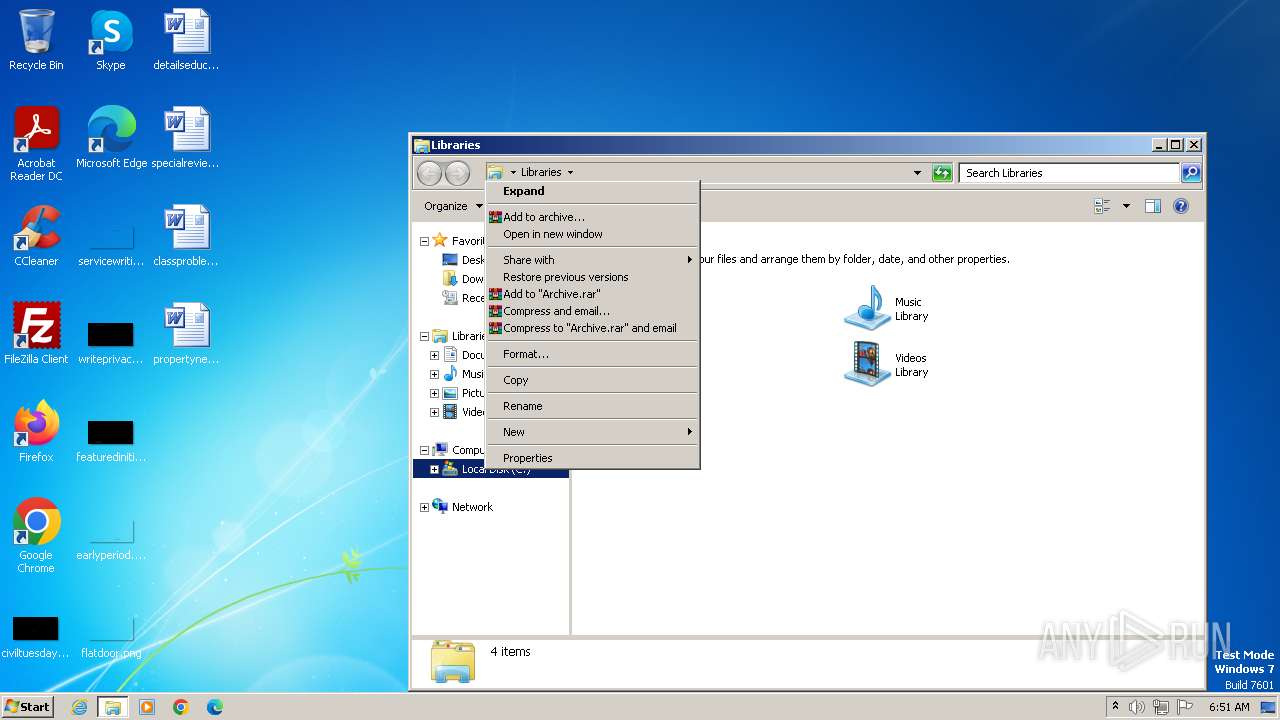
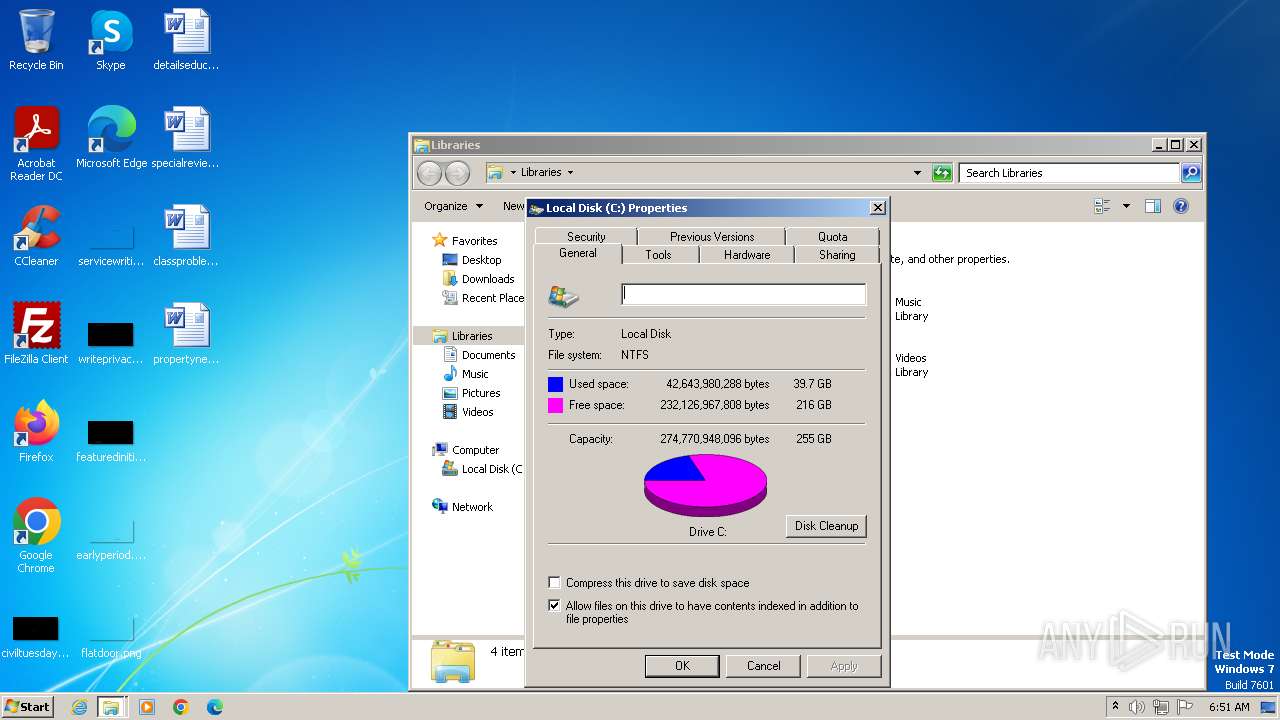
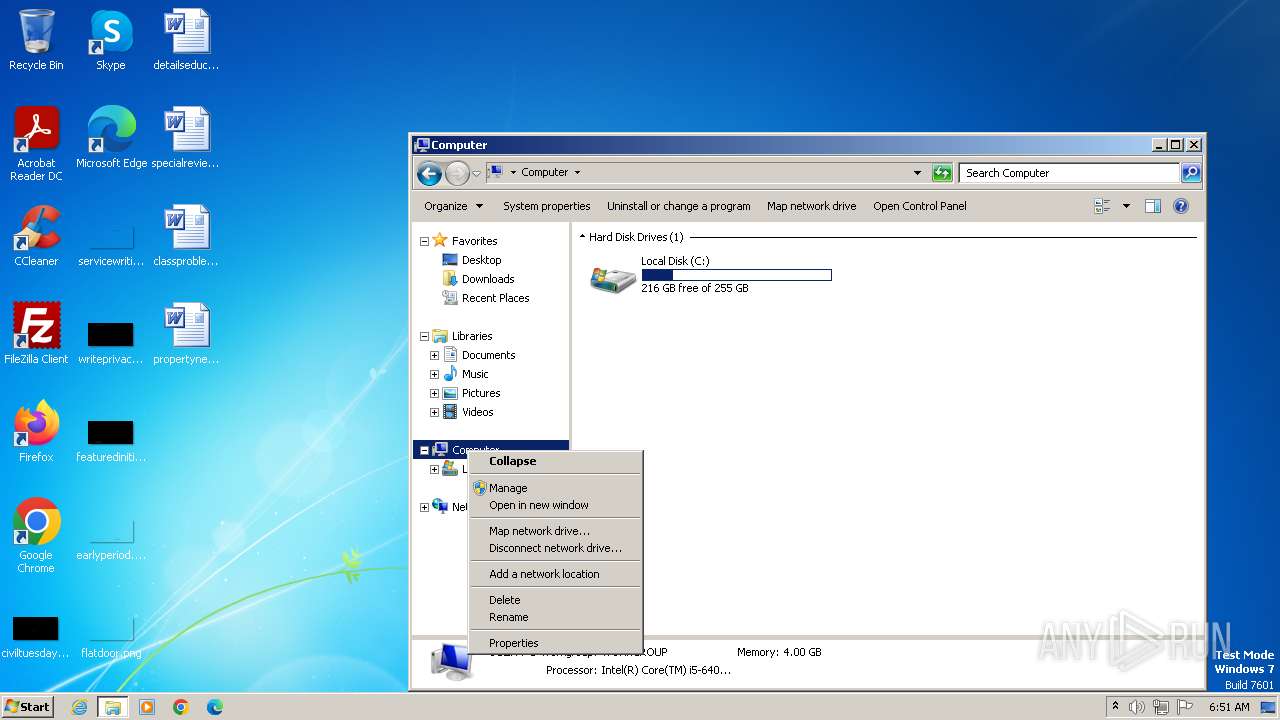
Manual execution by a user
- wmpnscfg.exe (PID: 2132)
- explorer.exe (PID: 4036)
- cmd.exe (PID: 3944)
- control.exe (PID: 2868)
- explorer.exe (PID: 2060)
- WinSAT.exe (PID: 2464)
- WinSAT.exe (PID: 1628)
Checks operating system version
- cmd.exe (PID: 3784)
- cmd.exe (PID: 2892)
- cmd.exe (PID: 3944)
Reads Microsoft Office registry keys
- reg.exe (PID: 3632)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2023:11:23 03:17:12 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Microsoft-Activation-Scripts-master/ |
Total processes
248
Monitored processes
195
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | mode 76, 30 | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 188 | sc query sppsvc | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 368 | ping -4 -n 1 kms.moeyuuko.com | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 372 | reg delete "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform" /f /v KeyManagementServicePort | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 476 | sc start sppsvc trigger=timer;sessionid=0 | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 528 | C:\Windows\system32\cmd.exe /S /D /c" echo "127.69.2.5" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 600 | reg delete "HKLM\SOFTWARE\Microsoft\OfficeSoftwareProtectionPlatform" /f /v DisableKeyManagementServiceHostCaching | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 604 | sc query Null | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 756 | reg add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform" /f /v KeyManagementServiceName /t REG_SZ /d "52.220.218.76" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 844 | findstr /a:07 /f:`.txt "." | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
10 057
Read events
9 778
Write events
274
Delete events
5
Modification events
| (PID) Process: | (1864) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (1864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (1864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
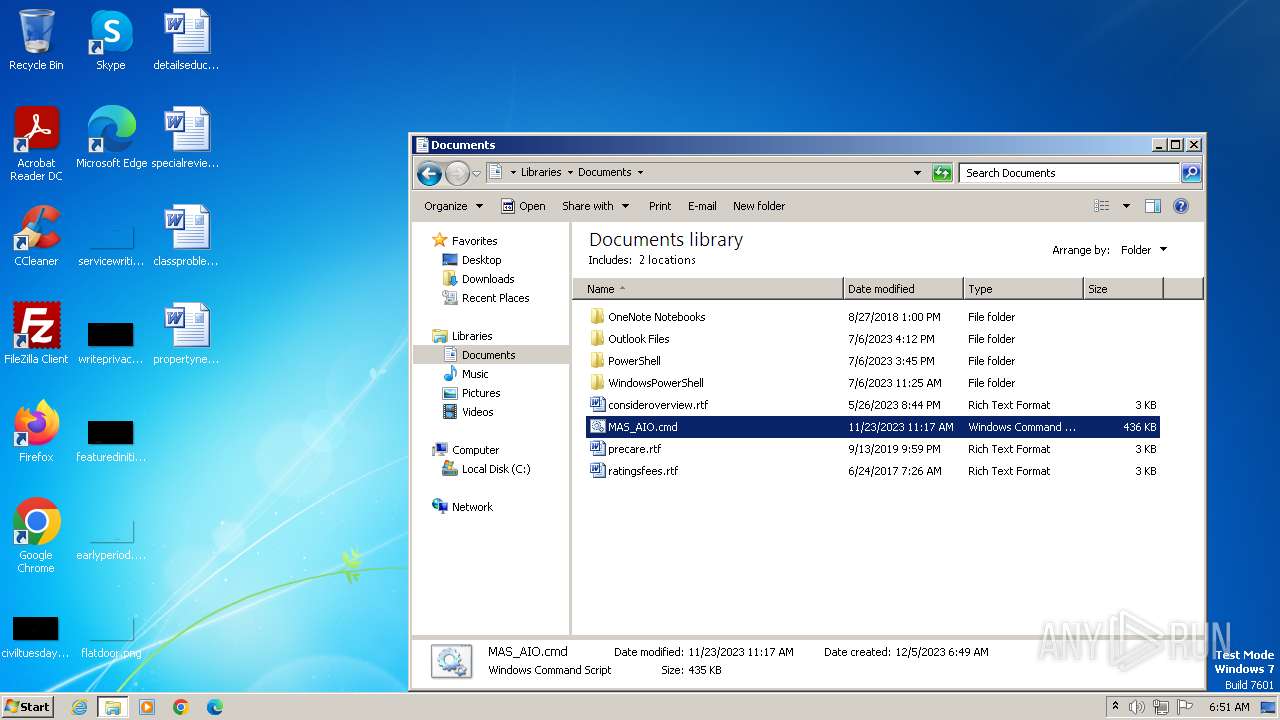
Executable files
1
Suspicious files
13
Text files
6
Unknown types
0
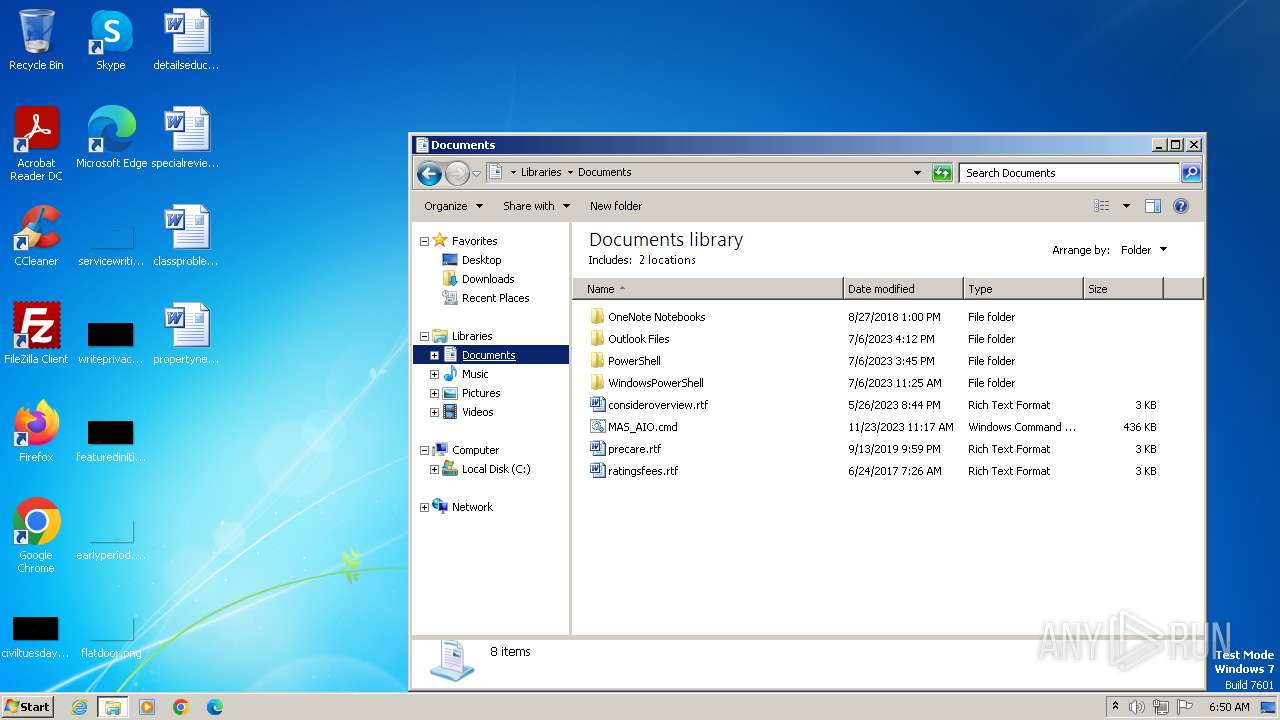
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3928 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\OWOFY50O87TQ13SQM7XS.temp | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 3928 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 1864 | WinRAR.exe | C:\Users\admin\Documents\MAS_AIO.cmd | text | |
MD5:E75E9DC1E59D194F3B626A0F75C88D46 | SHA256:A48F20CBF7155D6606E1C2ED6F31C5BF6713FA66BAF67157FAFF80CC57E10C2E | |||
| 3788 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\45B75WQMO915R6W40KF7.temp | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 2892 | cmd.exe | C:\Windows\Temp\' | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3788 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF2282b7.TMP | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 1272 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF227f5c.TMP | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 1272 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 3788 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 1272 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\F4FXD94SI5XLGD61PE08.temp | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
4
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
868 | svchost.exe | 23.35.228.137:80 | — | AKAMAI-AS | DE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
868 | svchost.exe | 95.101.148.135:80 | armmf.adobe.com | Akamai International B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
armmf.adobe.com |
| whitelisted |
updatecheck.massgrave.dev |
| unknown |
kms.zhuxiaole.org |
| unknown |
kms.moeyuuko.com |
| unknown |