| File name: | sup32.zip |
| Full analysis: | https://app.any.run/tasks/3c544787-1882-4a12-aa19-1504c5d0d055 |
| Verdict: | Malicious activity |
| Analysis date: | October 09, 2019, 14:19:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 392F1BC268E4184E54AE5E04615A9B53 |
| SHA1: | 3FE76F251375E4440F337D300BF9EA838F8AF396 |
| SHA256: | E9B5DEB4CCF8630FA7B0D188BDEDC10CB25C015B7175790D26BE5BBB11F66997 |
| SSDEEP: | 12288:l1n/fIYVoeYSgZ723CQq2fSE9jwyMc+hJlVPwWeDyb4:lt/AYA7IC/23BMh7VE2b4 |
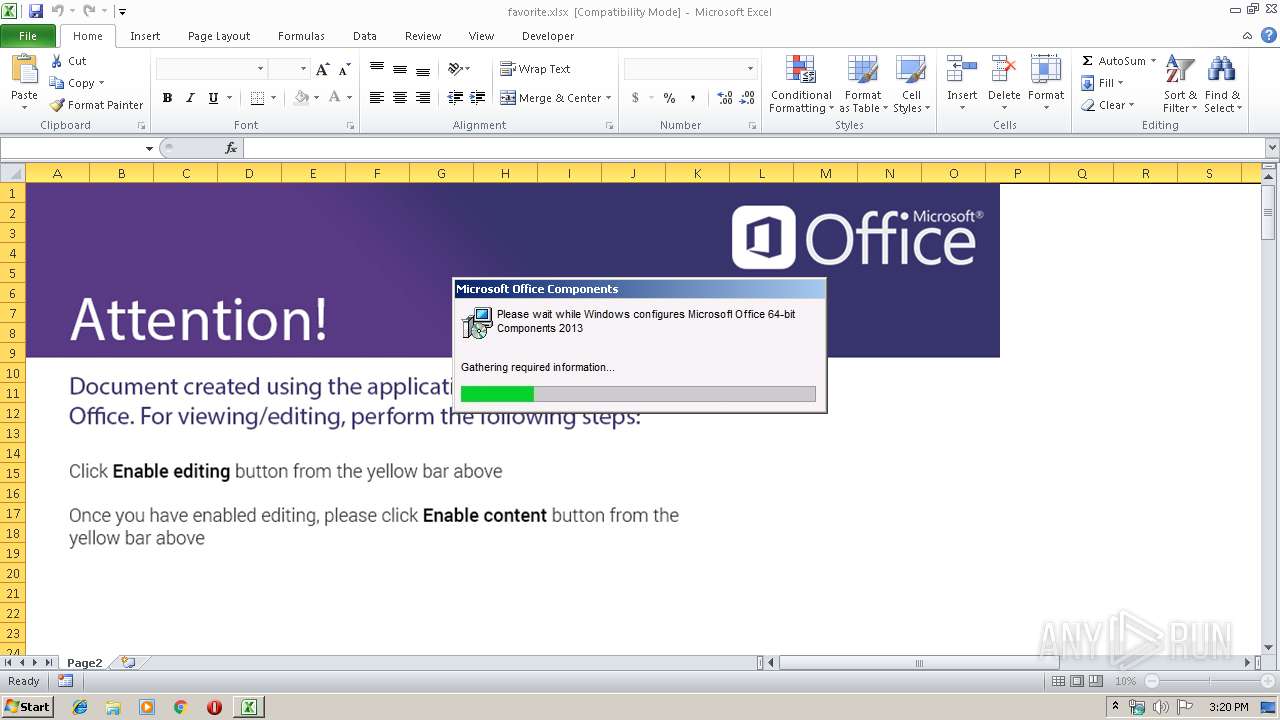
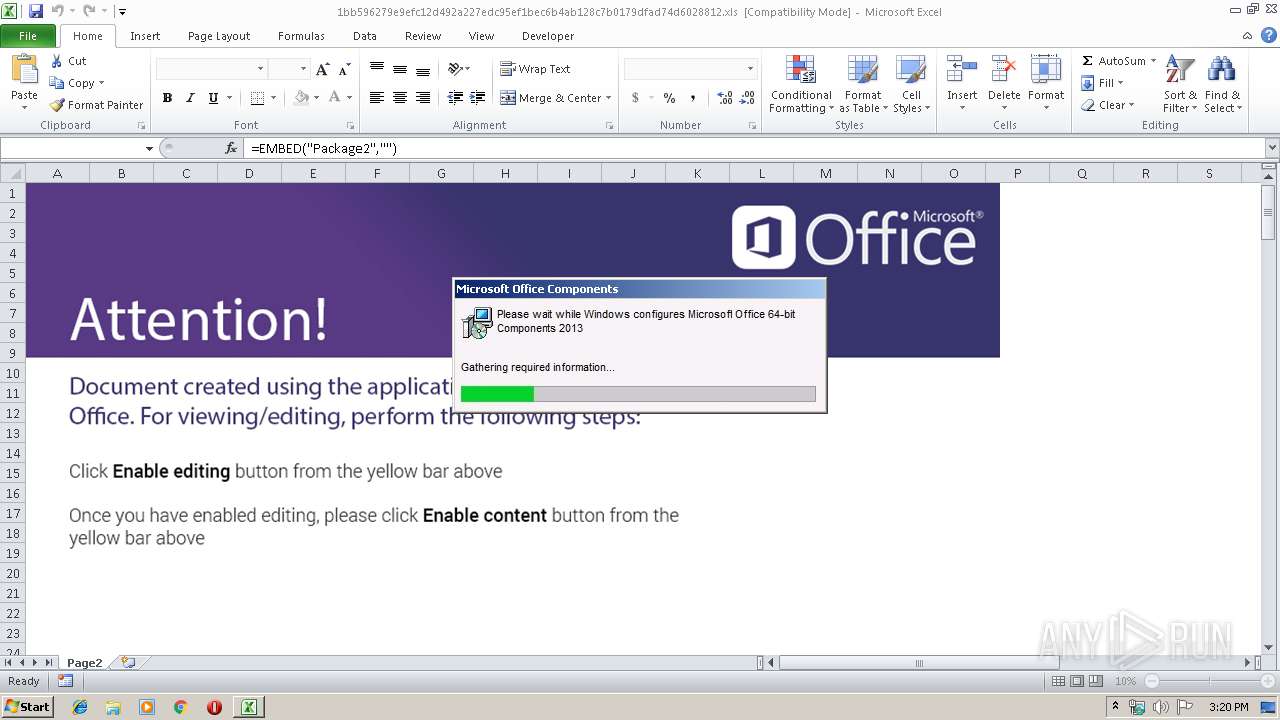
MALICIOUS
Drops known malicious document
- WinRAR.exe (PID: 2916)
- EXCEL.EXE (PID: 3152)
Loads dropped or rewritten executable
- EXCEL.EXE (PID: 3152)
Executable content was dropped or overwritten
- EXCEL.EXE (PID: 3152)
SUSPICIOUS
No suspicious indicators.INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 3152)
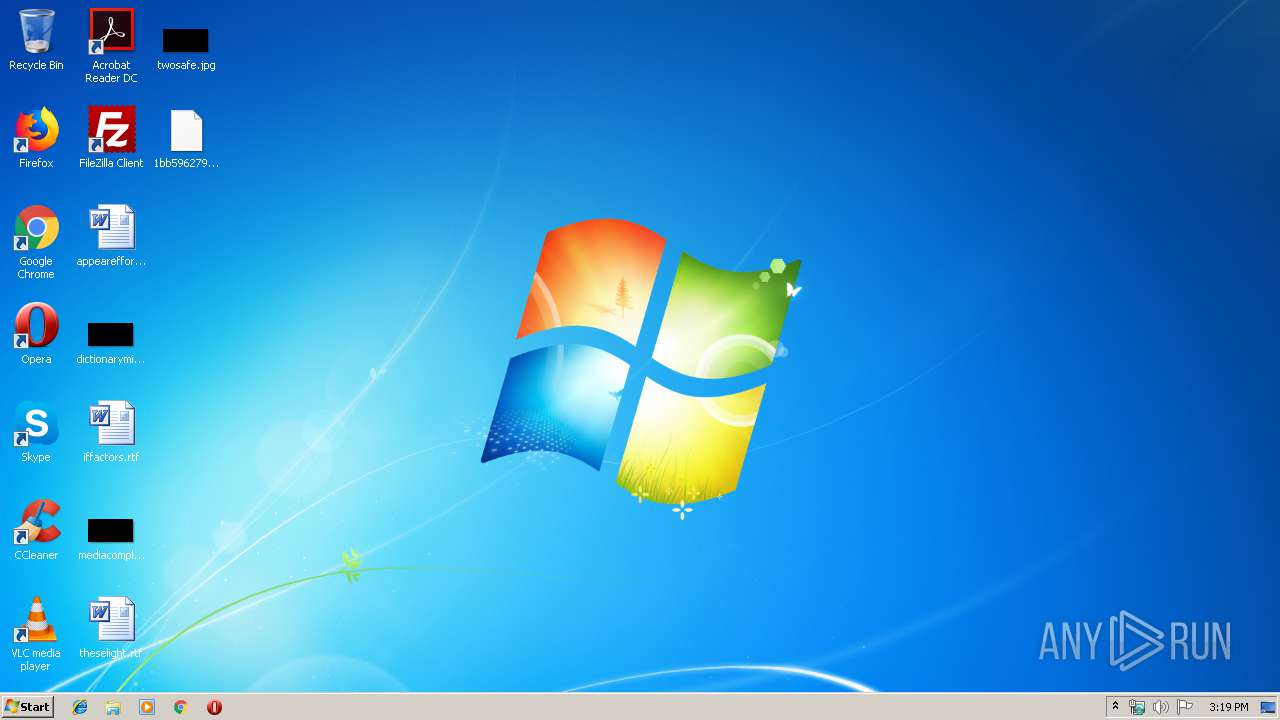
Manual execution by user
- EXCEL.EXE (PID: 3152)
Creates files in the user directory
- EXCEL.EXE (PID: 3152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
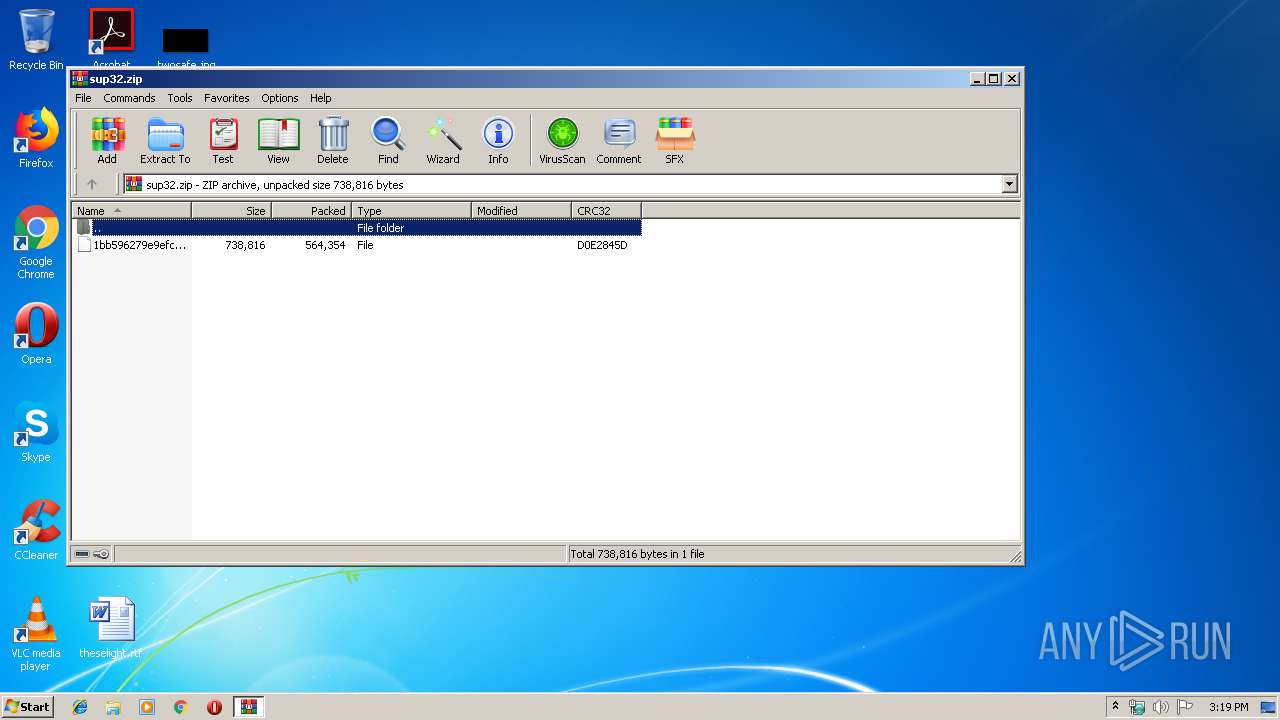
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:00:00 00:00:00 |
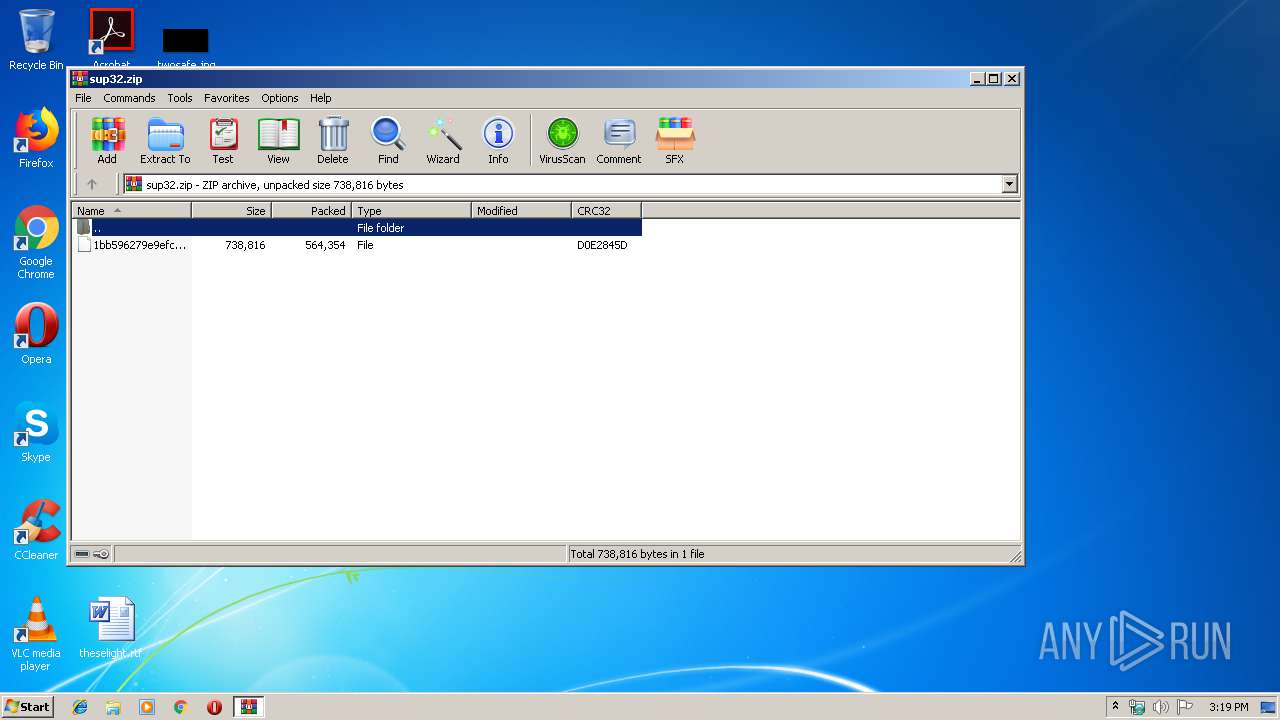
| ZipCRC: | 0xd0e2845d |
| ZipCompressedSize: | 564354 |
| ZipUncompressedSize: | 738816 |
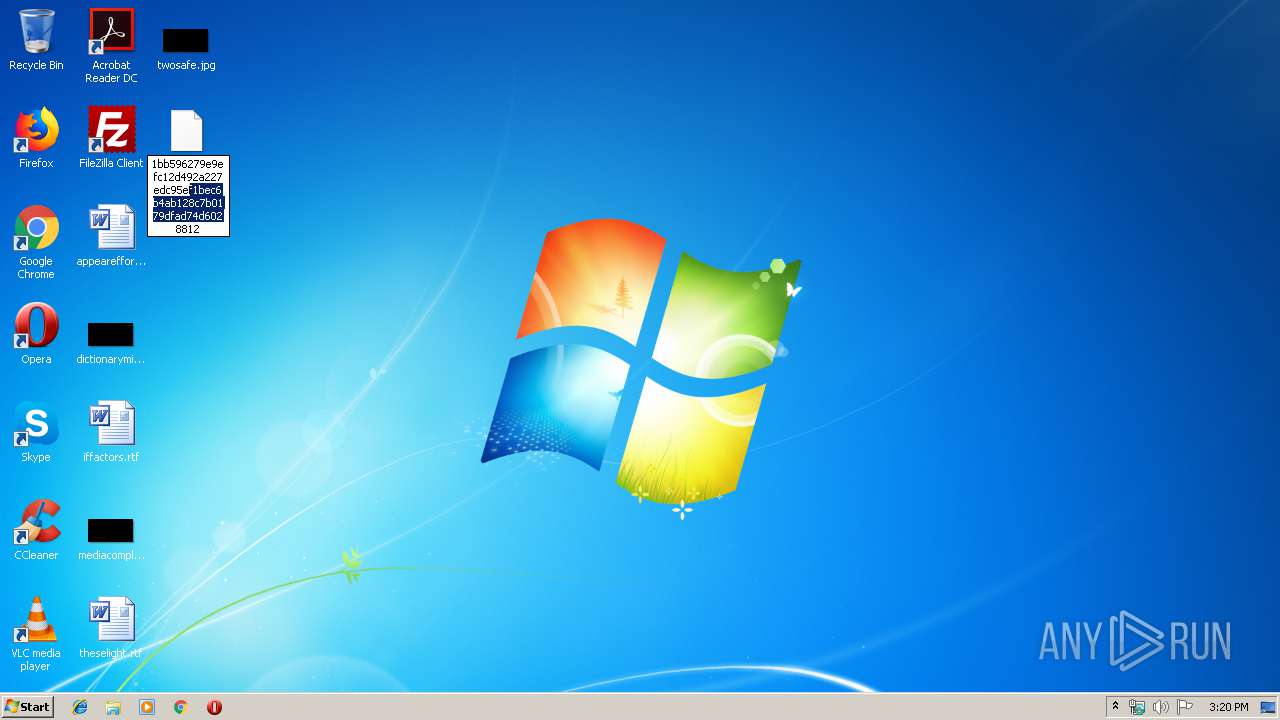
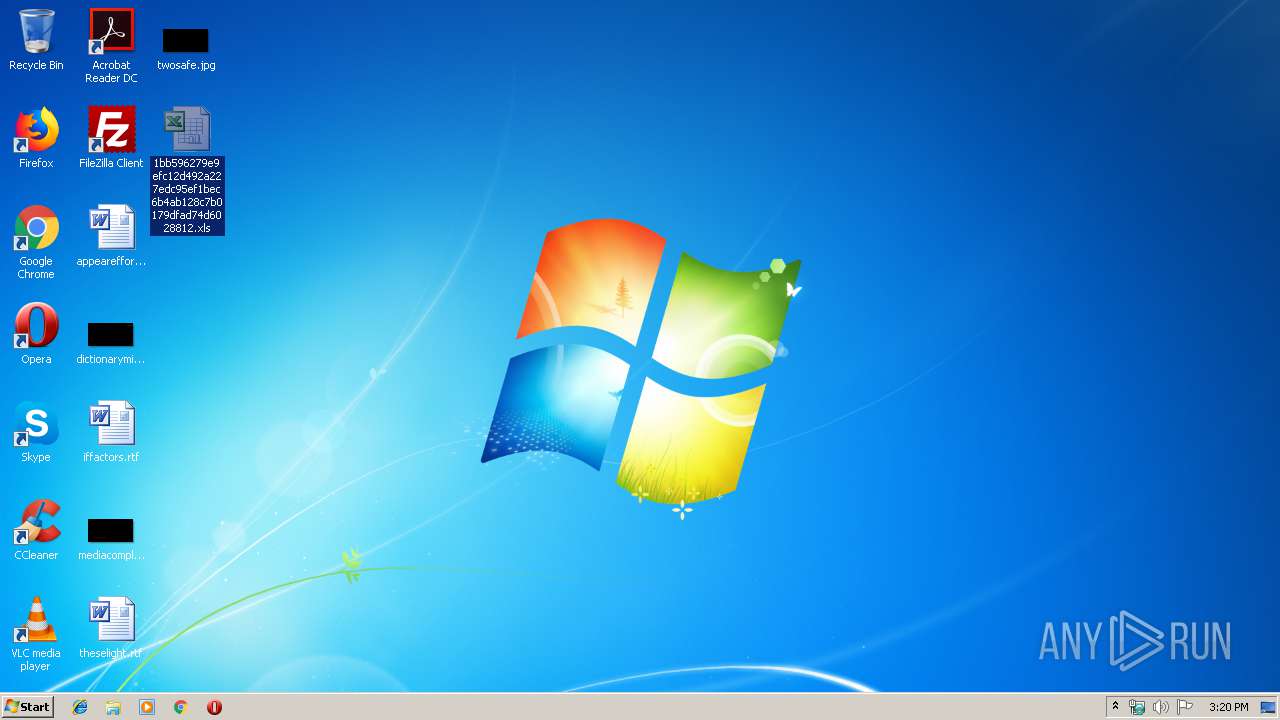
| ZipFileName: | 1bb596279e9efc12d492a227edc95ef1bec6b4ab128c7b0179dfad74d6028812 |
Total processes
35
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
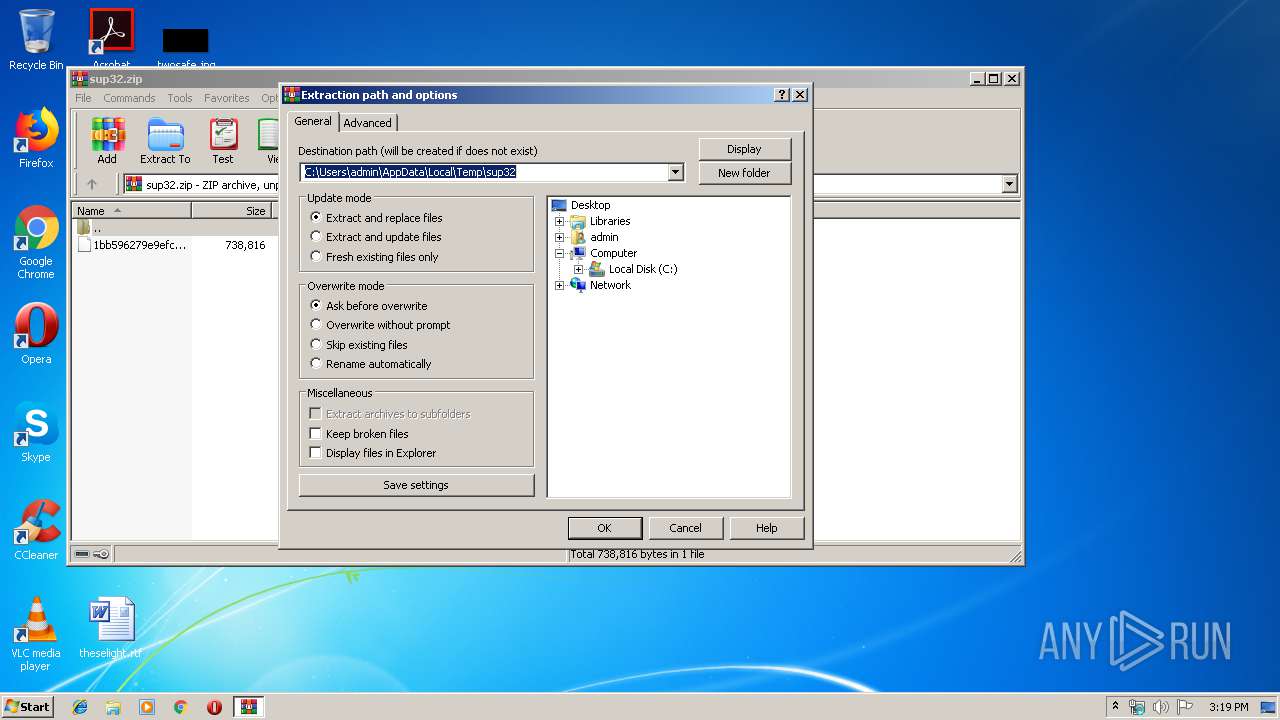
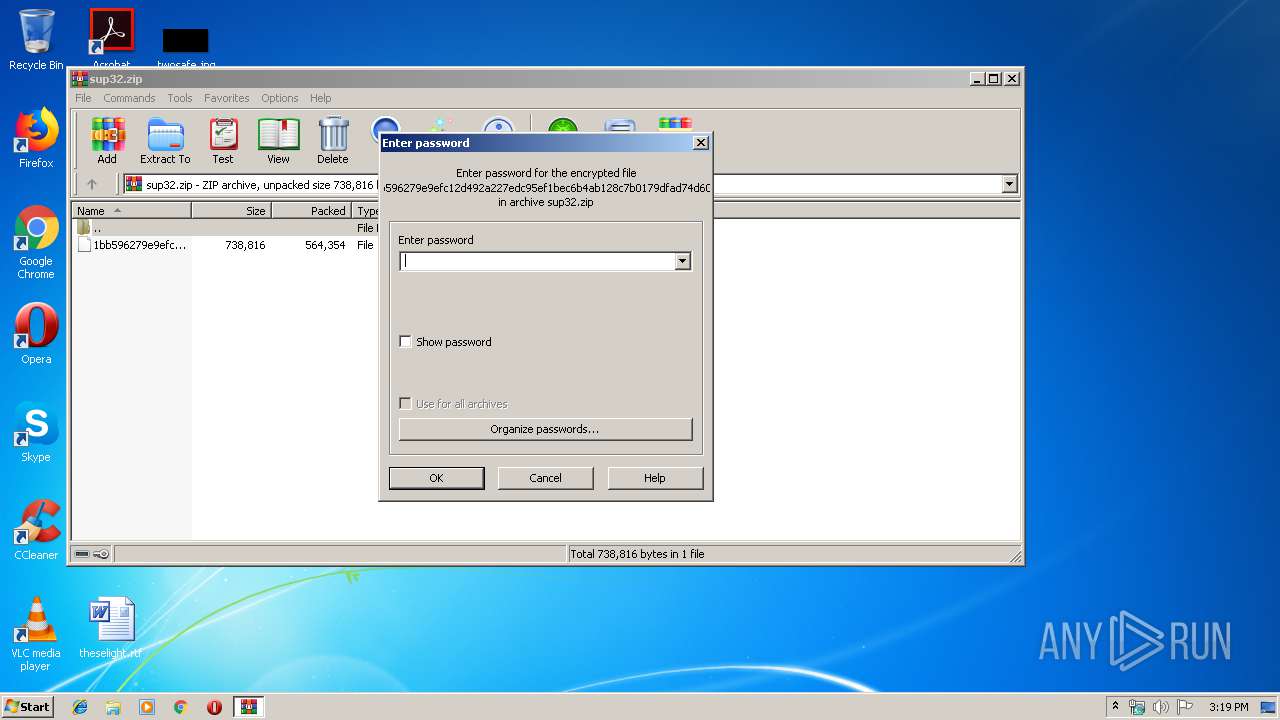
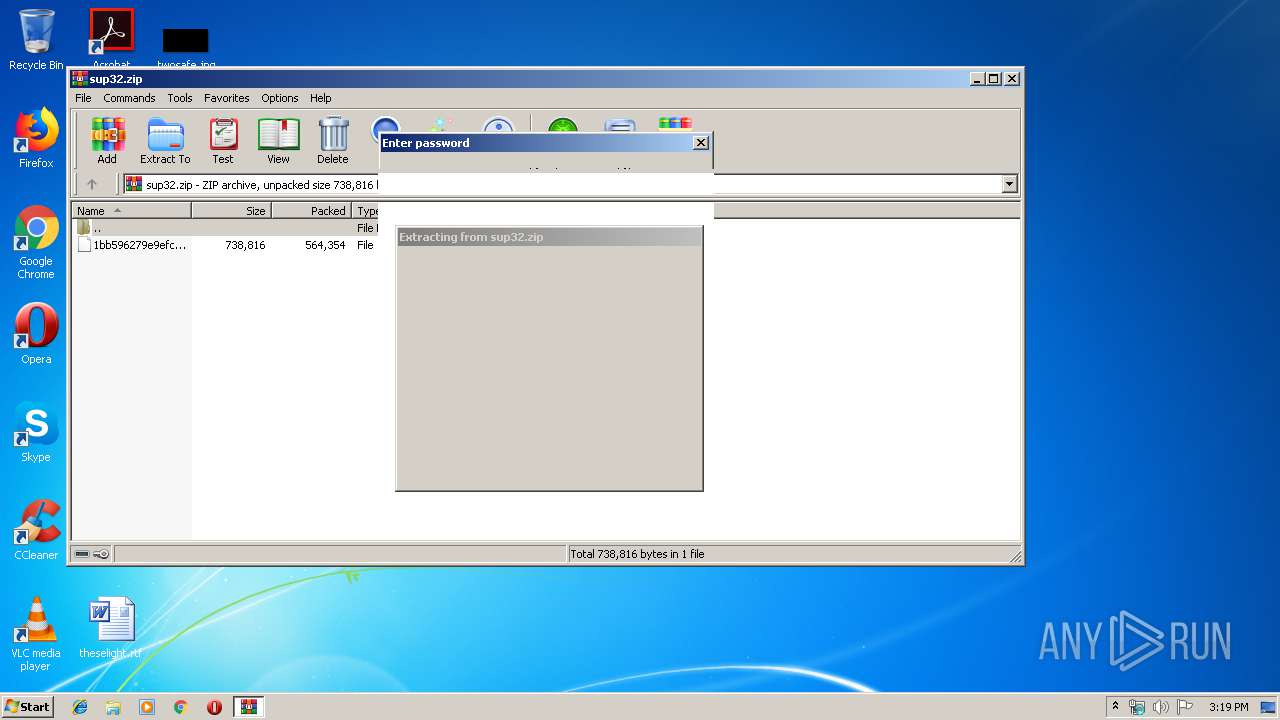
| 2916 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\sup32.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
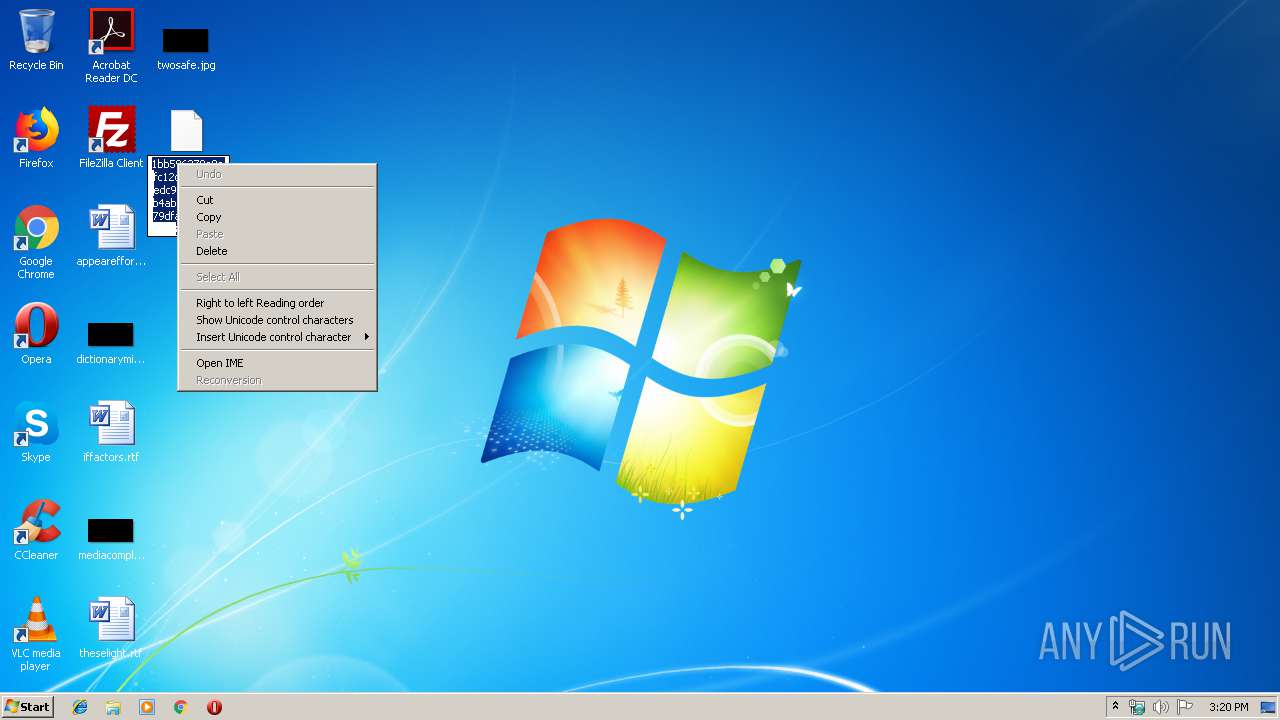
| 3152 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 200
Read events
1 059
Write events
122
Delete events
19
Modification events
| (PID) Process: | (2916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2916) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sup32.zip | |||
| (PID) Process: | (2916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (2916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
1
Suspicious files
4
Text files
2
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3152 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRFDA6.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3152 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\VB71F.tmp | — | |
MD5:— | SHA256:— | |||
| 3152 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\VB71E.tmp | — | |
MD5:— | SHA256:— | |||
| 3152 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DF0A077B0D3FBC1E3F.TMP | — | |
MD5:— | SHA256:— | |||
| 3152 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\C7021000 | — | |
MD5:— | SHA256:— | |||
| 3152 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DFD3CDB65CD88C83C3.TMP | — | |
MD5:— | SHA256:— | |||
| 3152 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~$favorite.xlsx | — | |
MD5:— | SHA256:— | |||
| 3152 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DF7385DD647C988A6F.TMP | — | |
MD5:— | SHA256:— | |||
| 2916 | WinRAR.exe | C:\Users\admin\Desktop\1bb596279e9efc12d492a227edc95ef1bec6b4ab128c7b0179dfad74d6028812 | document | |
MD5:— | SHA256:— | |||
| 3152 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\6D227277.emf | emf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3152 | EXCEL.EXE | 96.44.166.189:443 | windows-msd-update.com | QuadraNet, Inc | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
windows-msd-update.com |
| unknown |