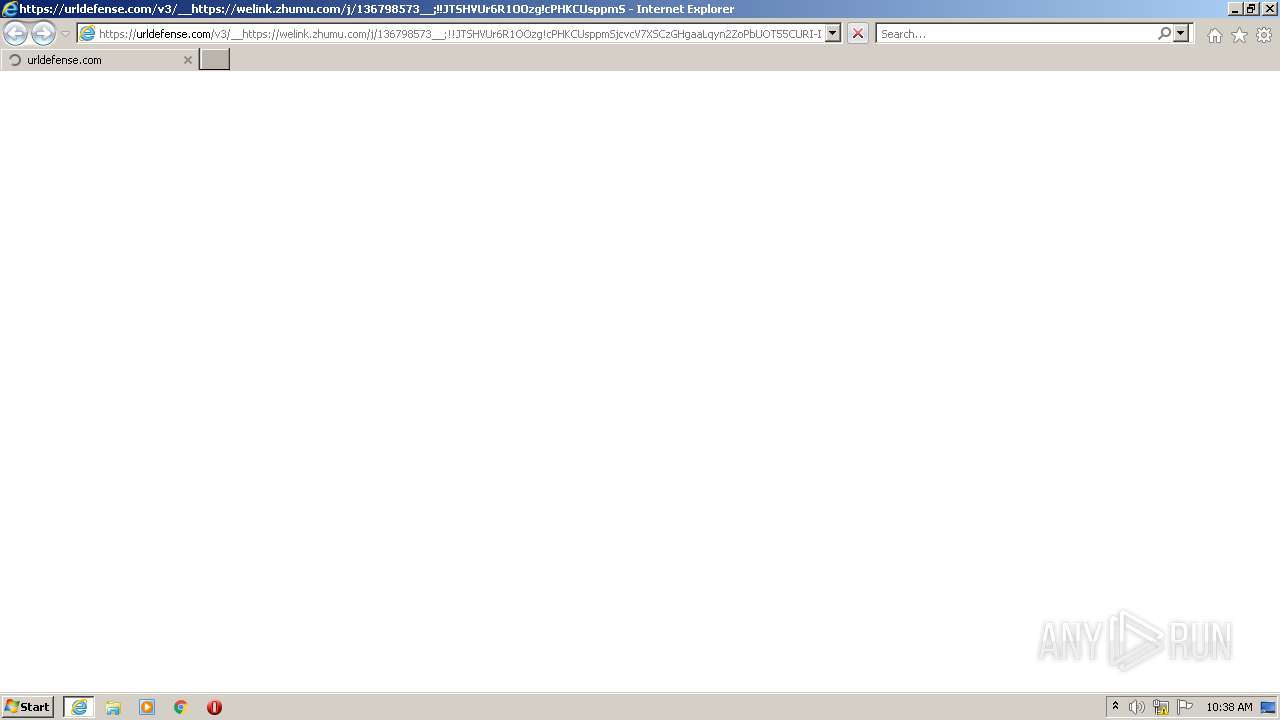
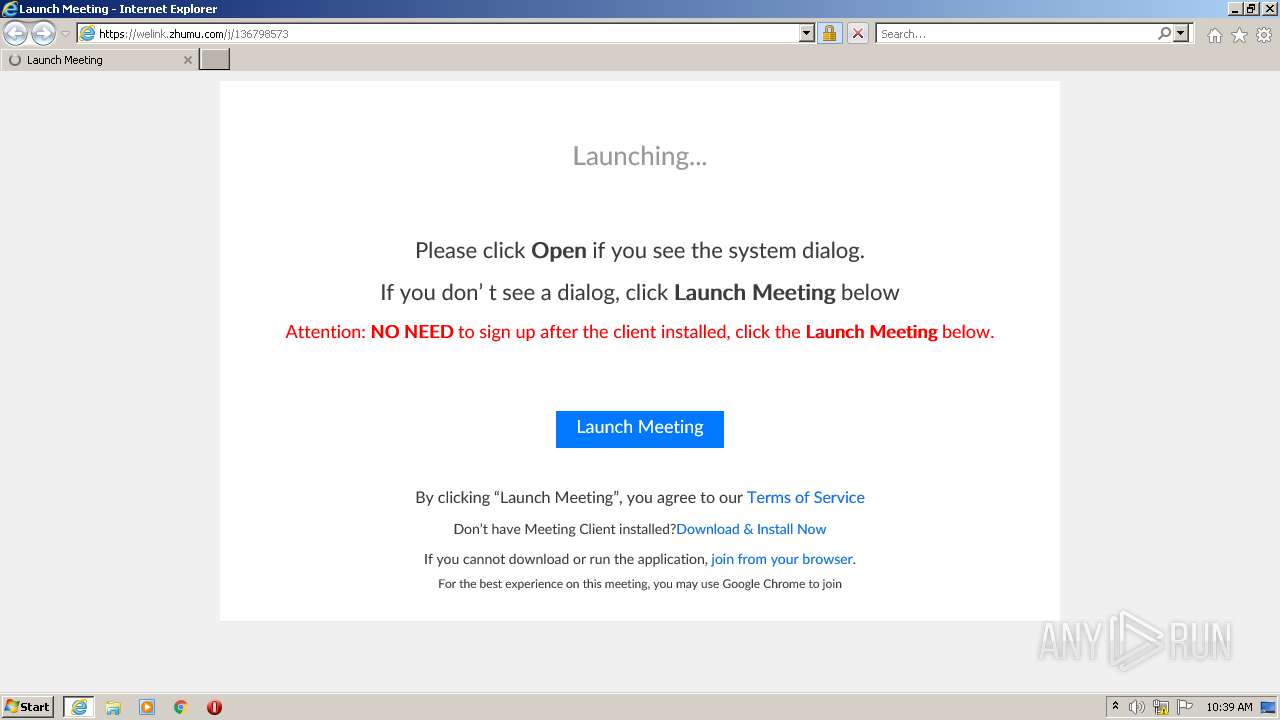
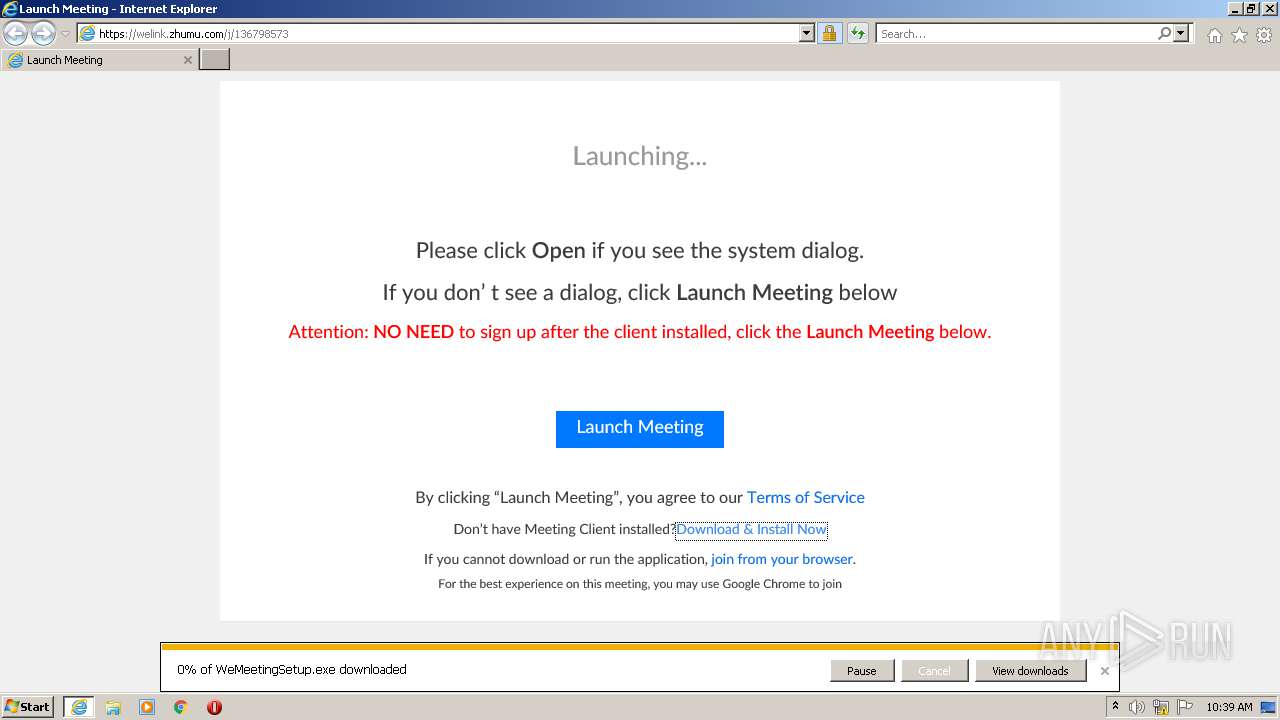
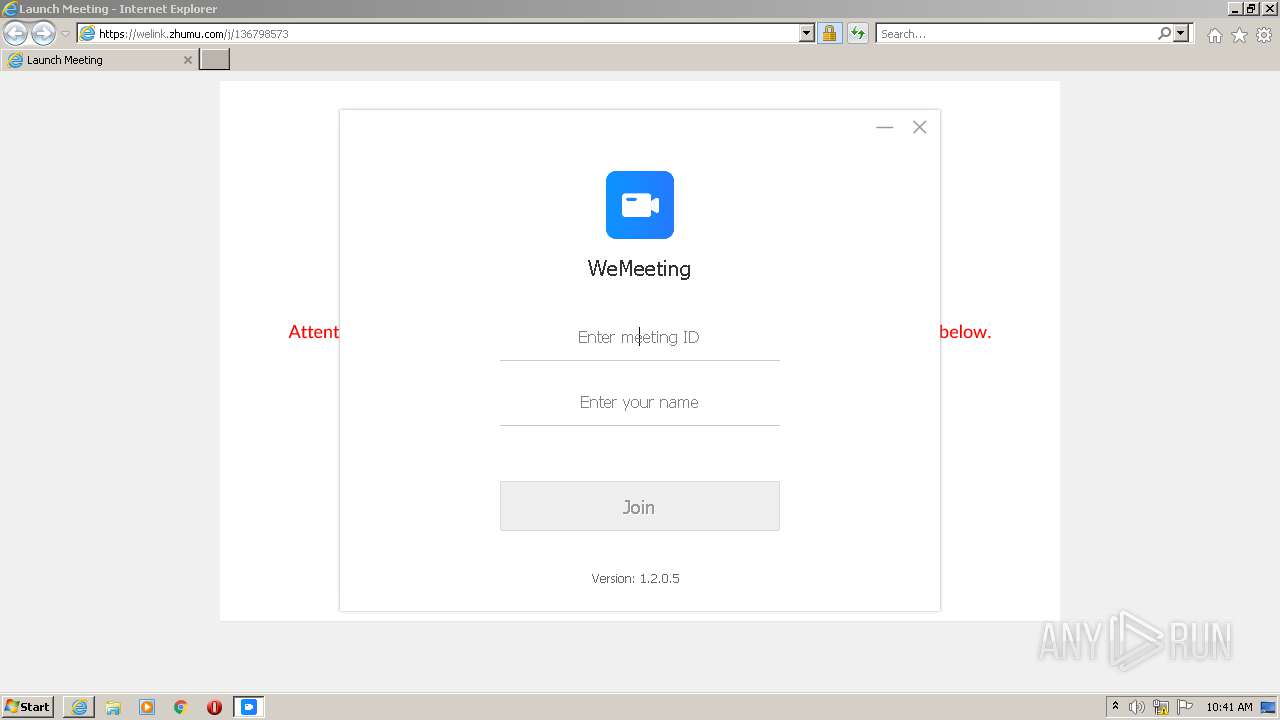
| URL: | https://urldefense.com/v3/__https://welink.zhumu.com/j/136798573__;!!JTSHVUr6R1OOzg!cPHKCUsppmSjcvcV7XSCzGHgaaLqyn2ZoPbUOT55CURI-IdQINvCEpKuKzOV$ |
| Full analysis: | https://app.any.run/tasks/6224a498-72fa-4acf-9333-8f18c7b5366c |
| Verdict: | Malicious activity |
| Analysis date: | July 29, 2021, 09:38:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CEC1DFF22DB8493AF0D2A529C4DA22F8 |
| SHA1: | 41DFBFB64AB7C337F2AF2A675B49FFEE9CF8E7B3 |
| SHA256: | E9A08249363862024865AEC2AD78296B1D6A1F4E87675F09A2C5C3F300358950 |
| SSDEEP: | 3:N8U2DAL5IKTWK66NR05fwCUWDd2ReEGxKm/wit2G+94AX2HwqxcCsIsCsroQufqt:2UJtIrhVvPMRqP/ZtI9vvRBuf8 |
MALICIOUS
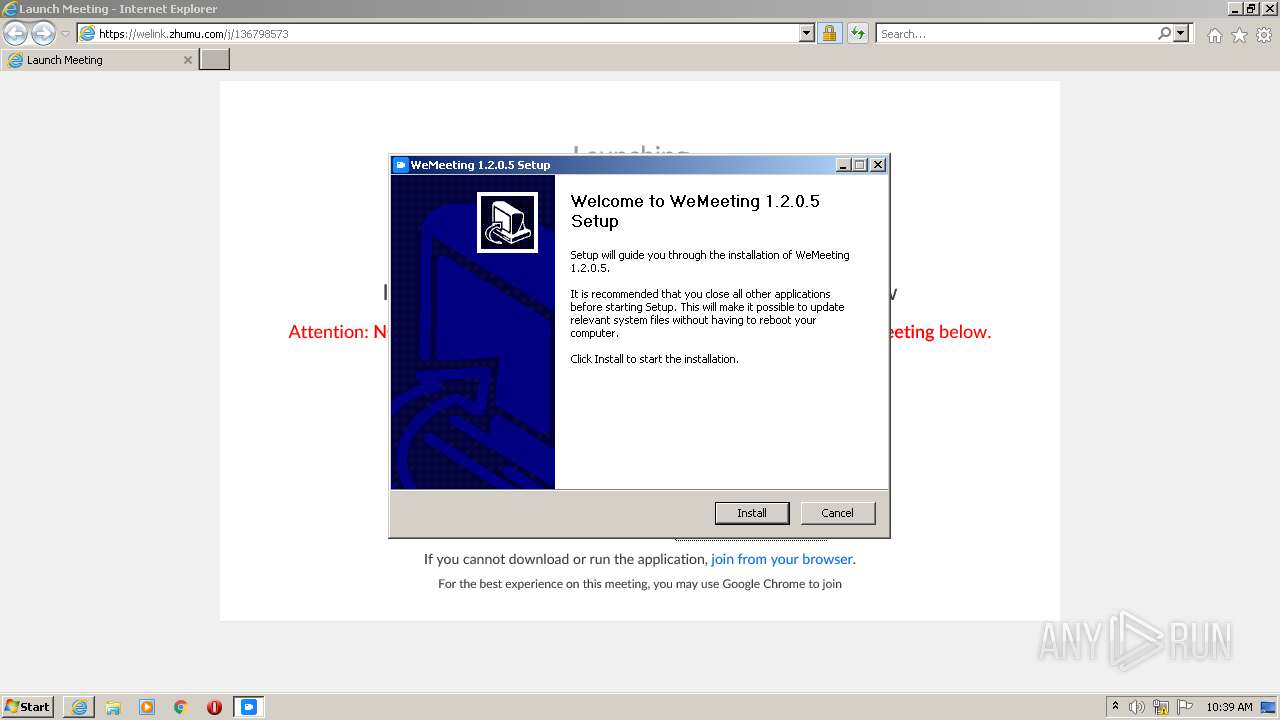
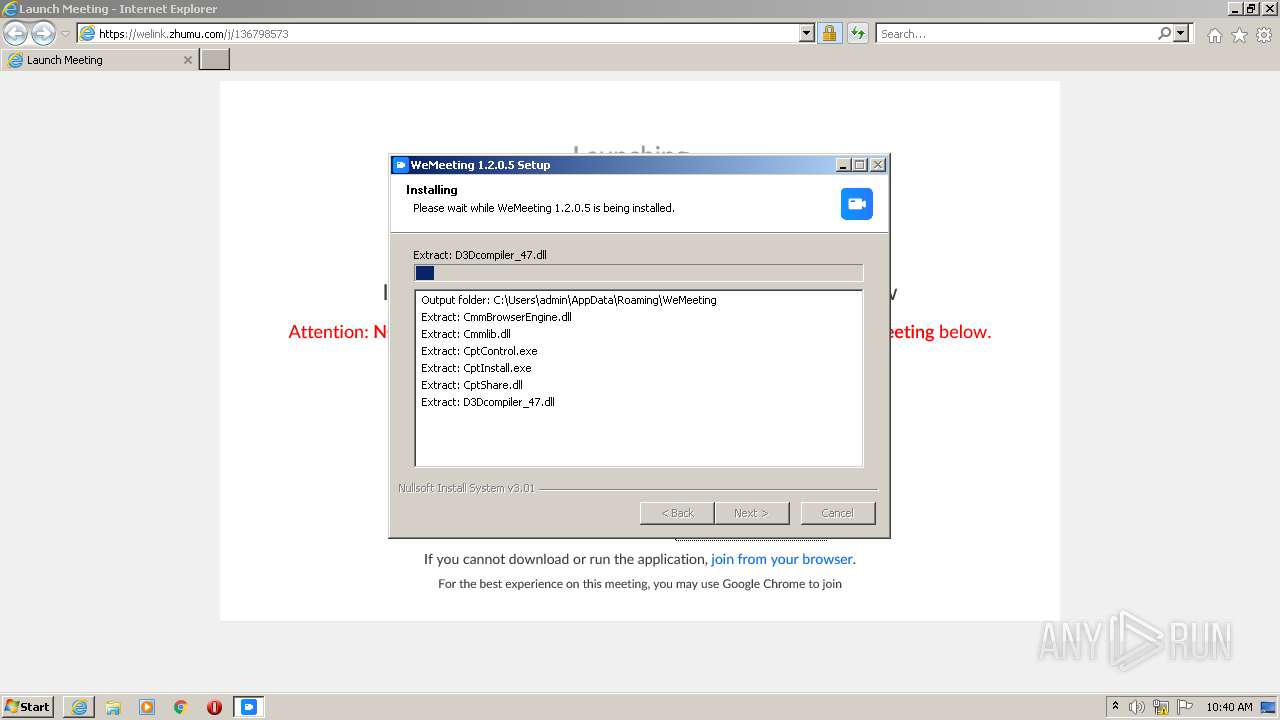
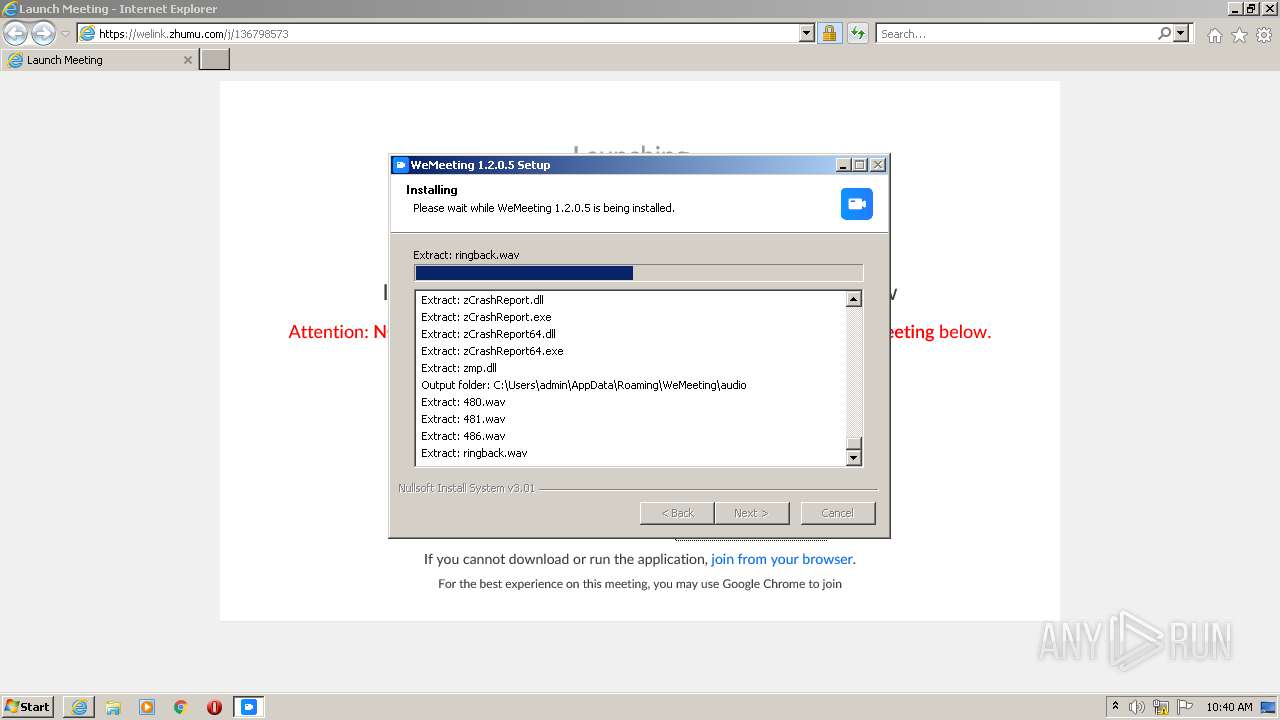
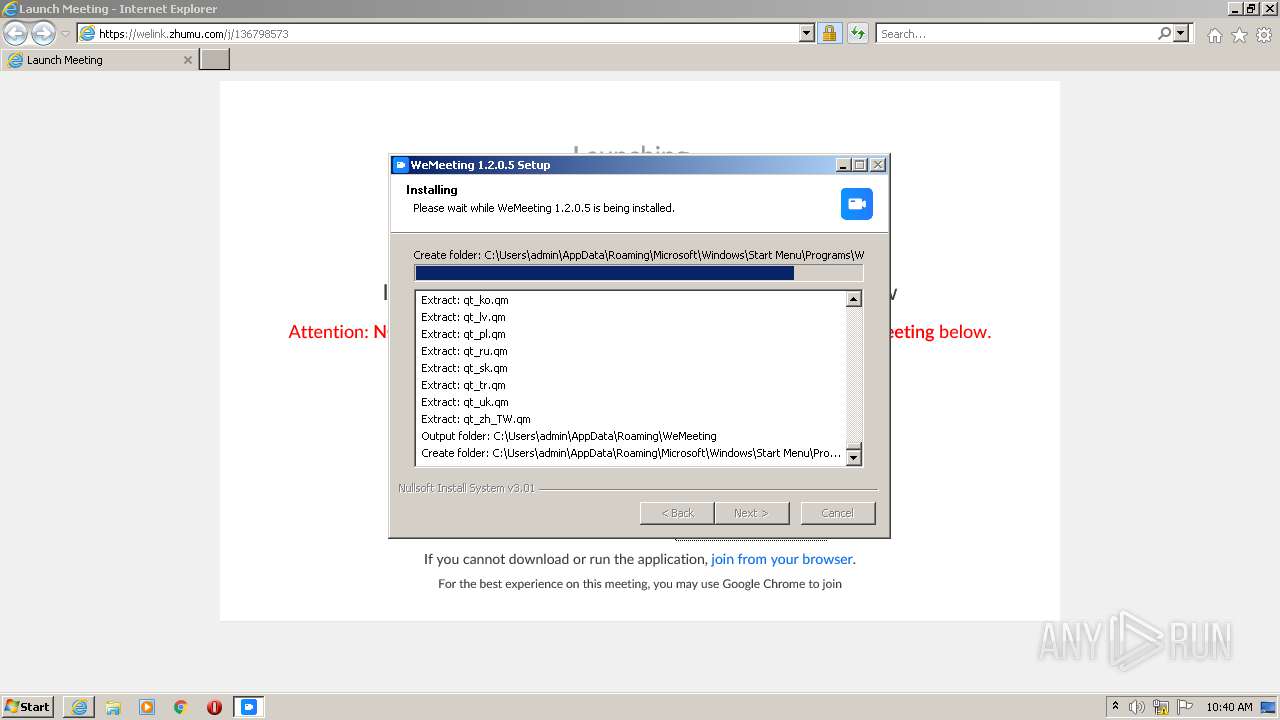
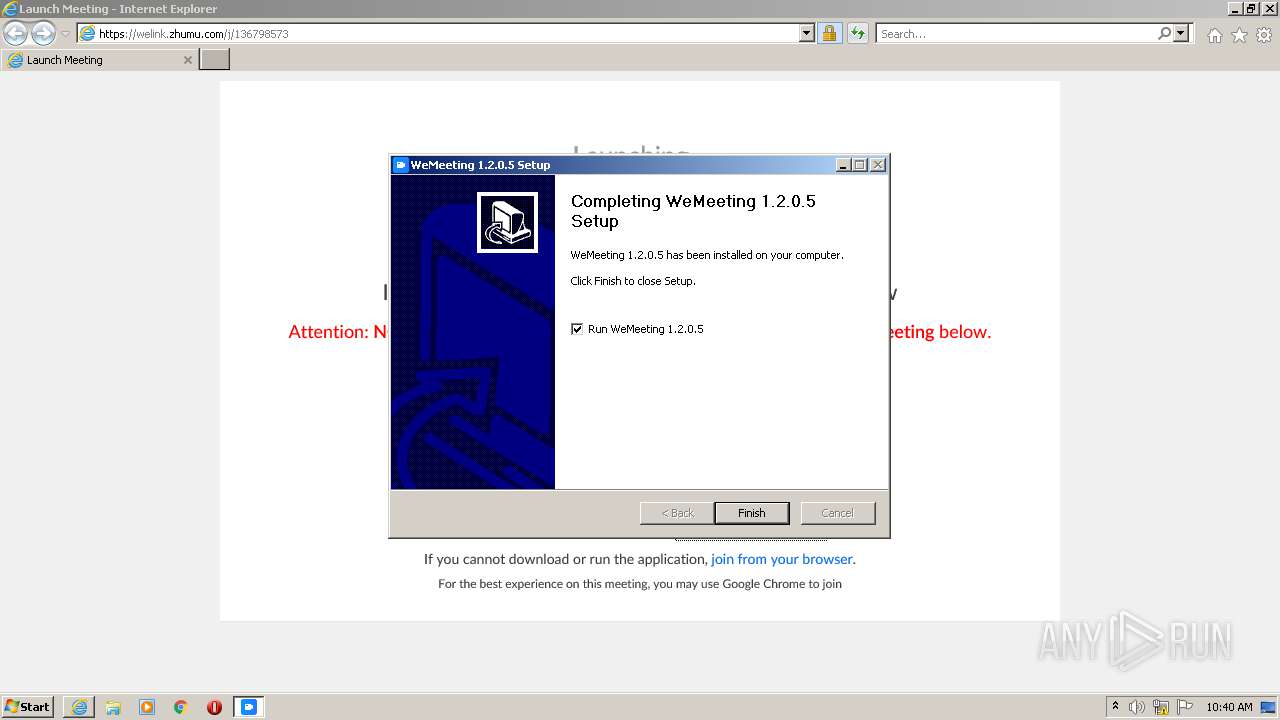
Application was dropped or rewritten from another process
- WeMeetingSetup.exe (PID: 3268)
- PreConfig.exe (PID: 3244)
- WeMeeting.exe (PID: 1576)
- PreConfigAdmin.exe (PID: 3796)
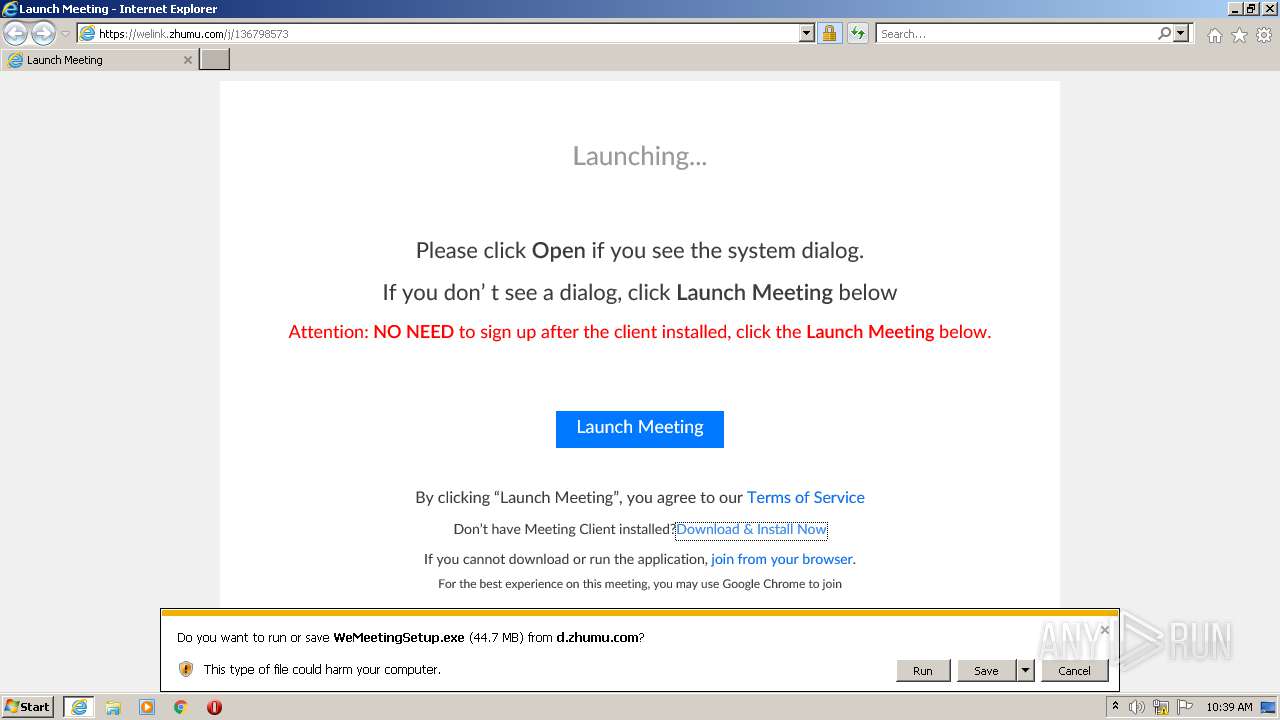
Drops executable file immediately after starts
- WeMeetingSetup.exe (PID: 3268)
Loads dropped or rewritten executable
- WeMeetingSetup.exe (PID: 3268)
- WeMeeting.exe (PID: 1576)
SUSPICIOUS
Executable content was dropped or overwritten
- iexplore.exe (PID: 3920)
- WeMeetingSetup.exe (PID: 3268)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3920)
Checks supported languages
- WeMeetingSetup.exe (PID: 3268)
- PreConfig.exe (PID: 3244)
- WeMeeting.exe (PID: 1576)
Reads the computer name
- WeMeetingSetup.exe (PID: 3268)
- PreConfig.exe (PID: 3244)
- WeMeeting.exe (PID: 1576)
Drops a file that was compiled in debug mode
- WeMeetingSetup.exe (PID: 3268)
Drops a file with too old compile date
- WeMeetingSetup.exe (PID: 3268)
Creates a software uninstall entry
- WeMeetingSetup.exe (PID: 3268)
Creates files in the user directory
- PreConfig.exe (PID: 3244)
- WeMeeting.exe (PID: 1576)
- WeMeetingSetup.exe (PID: 3268)
Drops a file with a compile date too recent
- WeMeetingSetup.exe (PID: 3268)
Changes default file association
- WeMeetingSetup.exe (PID: 3268)
INFO
Reads the computer name
- iexplore.exe (PID: 2808)
- iexplore.exe (PID: 3920)
Checks supported languages
- iexplore.exe (PID: 2808)
- iexplore.exe (PID: 3920)
Changes internet zones settings
- iexplore.exe (PID: 2808)
Reads settings of System Certificates
- iexplore.exe (PID: 3920)
- iexplore.exe (PID: 2808)
- WeMeeting.exe (PID: 1576)
Application launched itself
- iexplore.exe (PID: 2808)
Checks Windows Trust Settings
- iexplore.exe (PID: 3920)
- iexplore.exe (PID: 2808)
- WeMeeting.exe (PID: 1576)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2808)
Reads internet explorer settings
- iexplore.exe (PID: 3920)
Changes settings of System certificates
- iexplore.exe (PID: 2808)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2808)
Creates files in the user directory
- iexplore.exe (PID: 2808)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2808)
- WeMeetingSetup.exe (PID: 3268)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
46
Monitored processes
6
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1576 | "C:\Users\admin\AppData\Roaming\WeMeeting\WeMeeting.exe" | C:\Users\admin\AppData\Roaming\WeMeeting\WeMeeting.exe | WeMeetingSetup.exe | ||||||||||||
User: admin Company: Huawei Integrity Level: MEDIUM Description: WeMeeting Exit code: 0 Version: 1.2.0.5 Modules
| |||||||||||||||
| 2808 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://urldefense.com/v3/__https://welink.zhumu.com/j/136798573__;!!JTSHVUr6R1OOzg!cPHKCUsppmSjcvcV7XSCzGHgaaLqyn2ZoPbUOT55CURI-IdQINvCEpKuKzOVf7f81a39-5f63-5b42-9efd-1f13b5431005quot; | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3244 | "C:\Users\admin\AppData\Roaming\WeMeeting\PreConfig.exe" english | C:\Users\admin\AppData\Roaming\WeMeeting\PreConfig.exe | — | WeMeetingSetup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
| |||||||||||||||
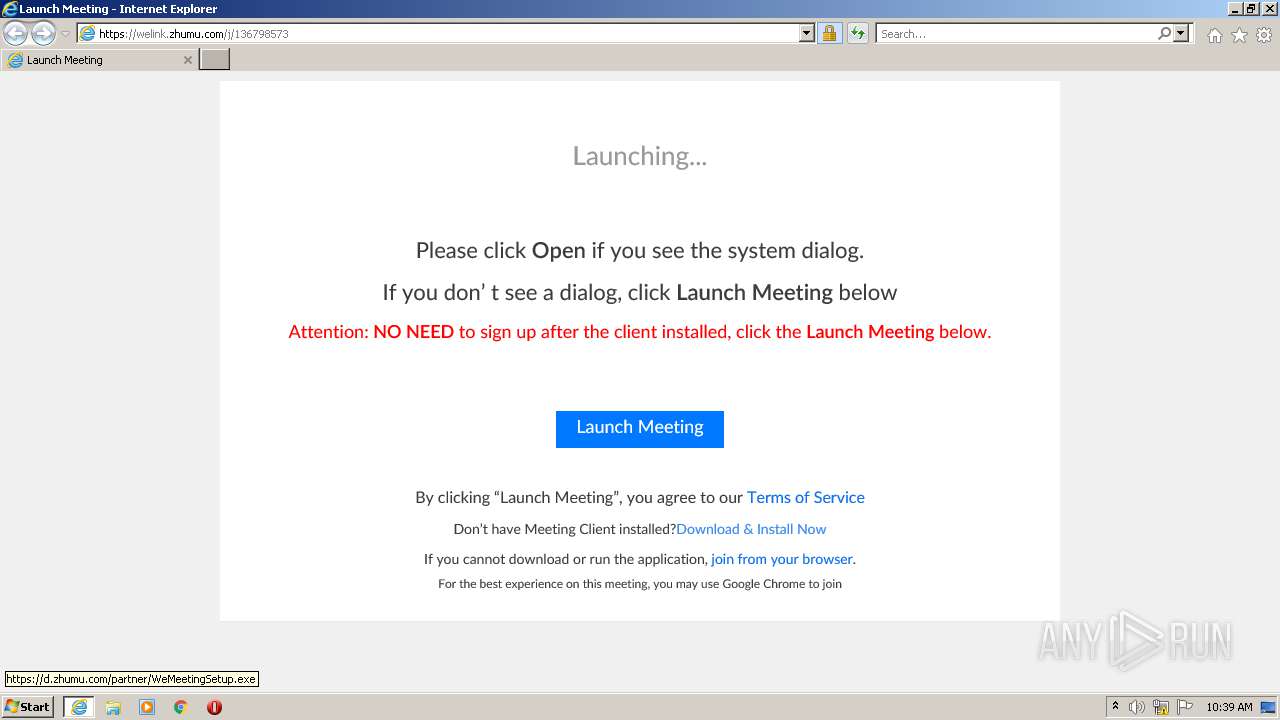
| 3268 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\WeMeetingSetup.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\WeMeetingSetup.exe | iexplore.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3796 | C:\Users\admin\AppData\Roaming\WeMeeting\PreConfigAdmin.exe | C:\Users\admin\AppData\Roaming\WeMeeting\PreConfigAdmin.exe | — | PreConfig.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3920 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2808 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
22 565
Read events
22 335
Write events
220
Delete events
10
Modification events
| (PID) Process: | (2808) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2808) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2808) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30901341 | |||
| (PID) Process: | (2808) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2808) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30901341 | |||
| (PID) Process: | (2808) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2808) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2808) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2808) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2808) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
111
Suspicious files
76
Text files
36
Unknown types
62
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_BACC6CD2B29F18349081C9FD2343833B | binary | |
MD5:— | SHA256:— | |||
| 2808 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 3920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\72BA427A91F50409B9EAC87F2B59B951_14541052F51AB35E7EEB1FA45936A529 | der | |
MD5:— | SHA256:— | |||
| 2808 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 3920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_D14B79B440CDC26D7D21C81855E2C04D | der | |
MD5:— | SHA256:— | |||
| 3920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\72BA427A91F50409B9EAC87F2B59B951_14541052F51AB35E7EEB1FA45936A529 | binary | |
MD5:— | SHA256:— | |||
| 3920 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\136798573[1].htm | html | |
MD5:— | SHA256:— | |||
| 3920 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\launch.min[1].js | text | |
MD5:— | SHA256:— | |||
| 3920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_D14B79B440CDC26D7D21C81855E2C04D | binary | |
MD5:— | SHA256:— | |||
| 3920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\00773B6FF14642B6FCE564FCC68E5B58 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
47
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3920 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEBN9U5yqfDGppDNwGWiEeo0%3D | US | der | 727 b | whitelisted |
3920 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ5rEWLwbJFq%2FmAU80sm7E%3D | US | der | 471 b | whitelisted |
3920 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://status.rapidssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRhhZrQET0hvbSHUJmNfBKqR%2FiT7wQUU8oXWfxrwAMhLxqu5KqoHIJW2nUCEA6y7CiRe5jMk9hdX1H1SYI%3D | US | der | 471 b | shared |
2808 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2808 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2808 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAxq6XzO1ZmDhpCgCp6lMhQ%3D | US | der | 471 b | whitelisted |
3920 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQh80WaEMqmyEvaHjlisSfVM4p8SAQUF9nWJSdn%2BTHCSUPZMDZEjGypT%2BsCEQCggUQ1i8HsVWj6t3pjeTok | US | der | 472 b | whitelisted |
3920 | iexplore.exe | GET | 200 | 8.253.207.121:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b769f77acfc87c05 | US | compressed | 4.70 Kb | whitelisted |
2808 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
3920 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAilokbNS1yMg9cCtLurU0k%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3920 | iexplore.exe | 52.71.28.102:443 | urldefense.com | Amazon.com, Inc. | US | suspicious |
3920 | iexplore.exe | 151.139.128.14:80 | ocsp.usertrust.com | Highwinds Network Group, Inc. | US | suspicious |
2808 | iexplore.exe | 13.107.22.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2808 | iexplore.exe | 72.21.91.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3920 | iexplore.exe | 8.210.48.175:443 | welink.zhumu.com | Level 3 Communications, Inc. | US | unknown |
3920 | iexplore.exe | 72.21.91.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3920 | iexplore.exe | 79.133.177.232:443 | d.zhumu.com | SOT LINE Limited Company | RU | malicious |
2808 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2808 | iexplore.exe | 204.79.197.200:443 | ieonline.microsoft.com | Microsoft Corporation | US | whitelisted |
2808 | iexplore.exe | 23.15.254.176:443 | go.microsoft.com | Akamai Technologies, Inc. | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
urldefense.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
welink.zhumu.com |
| unknown |
meeting.zhumu.me |
| unknown |
status.rapidssl.com |
| shared |