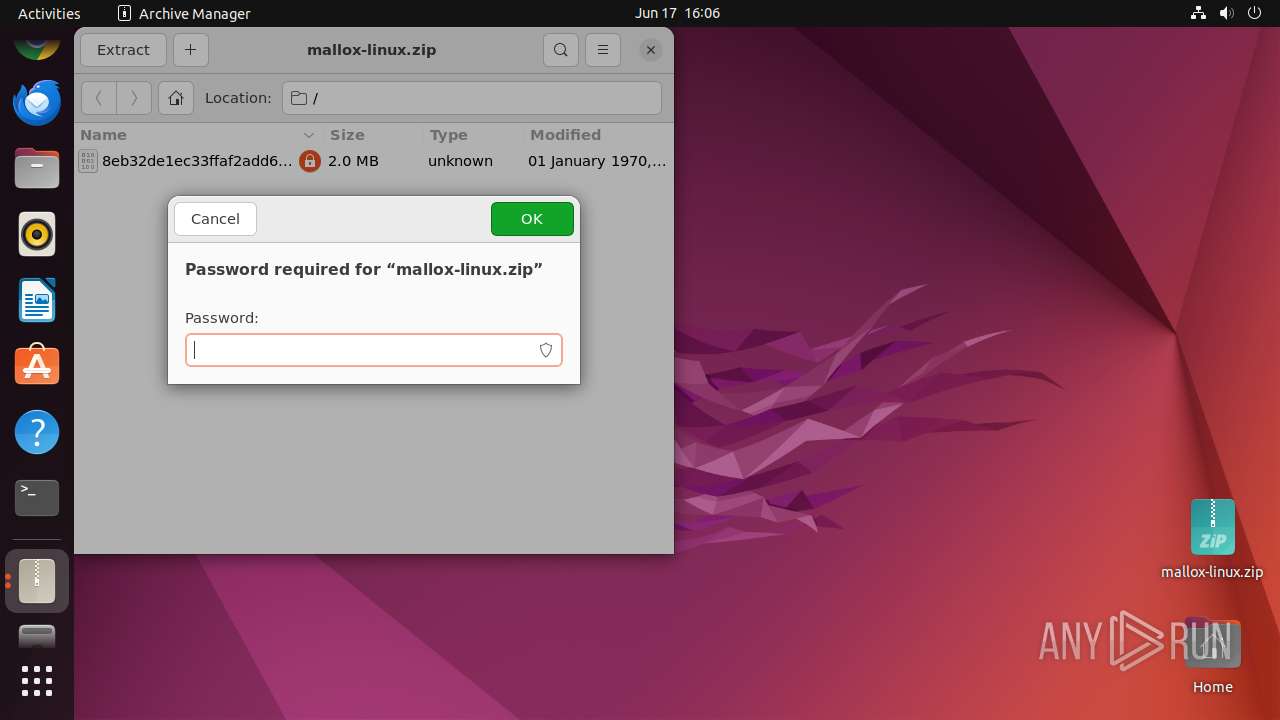
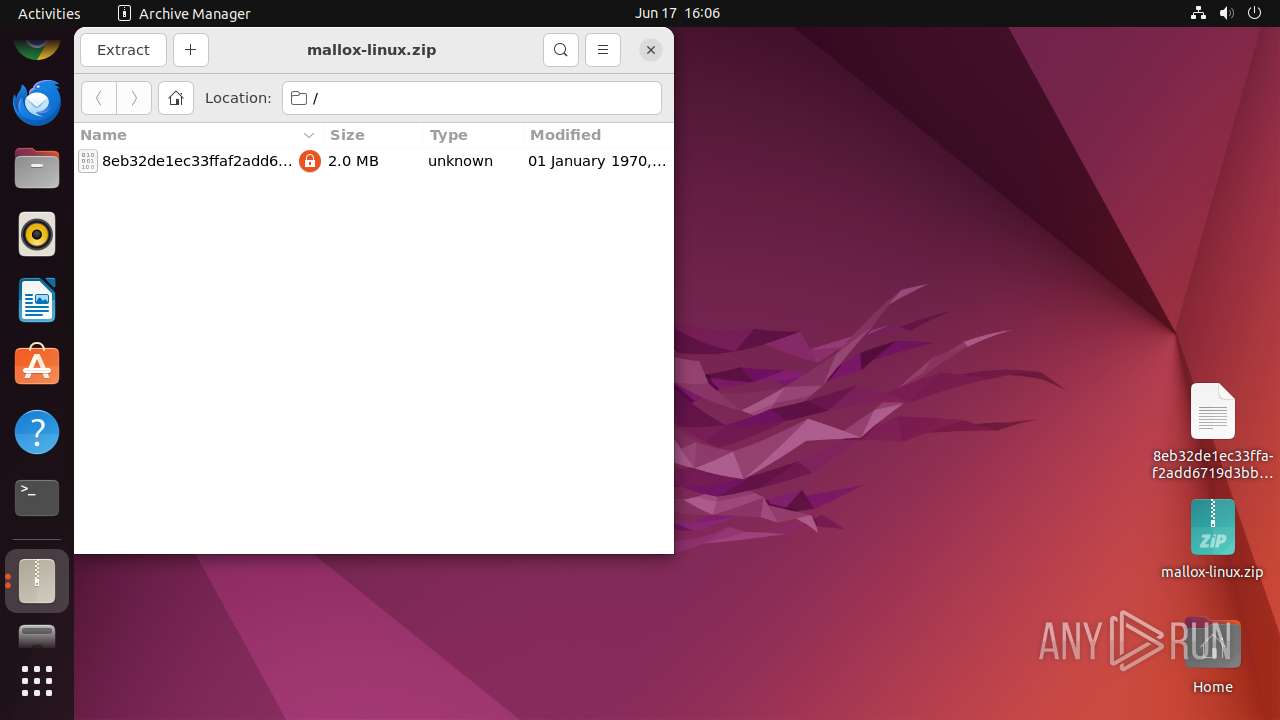
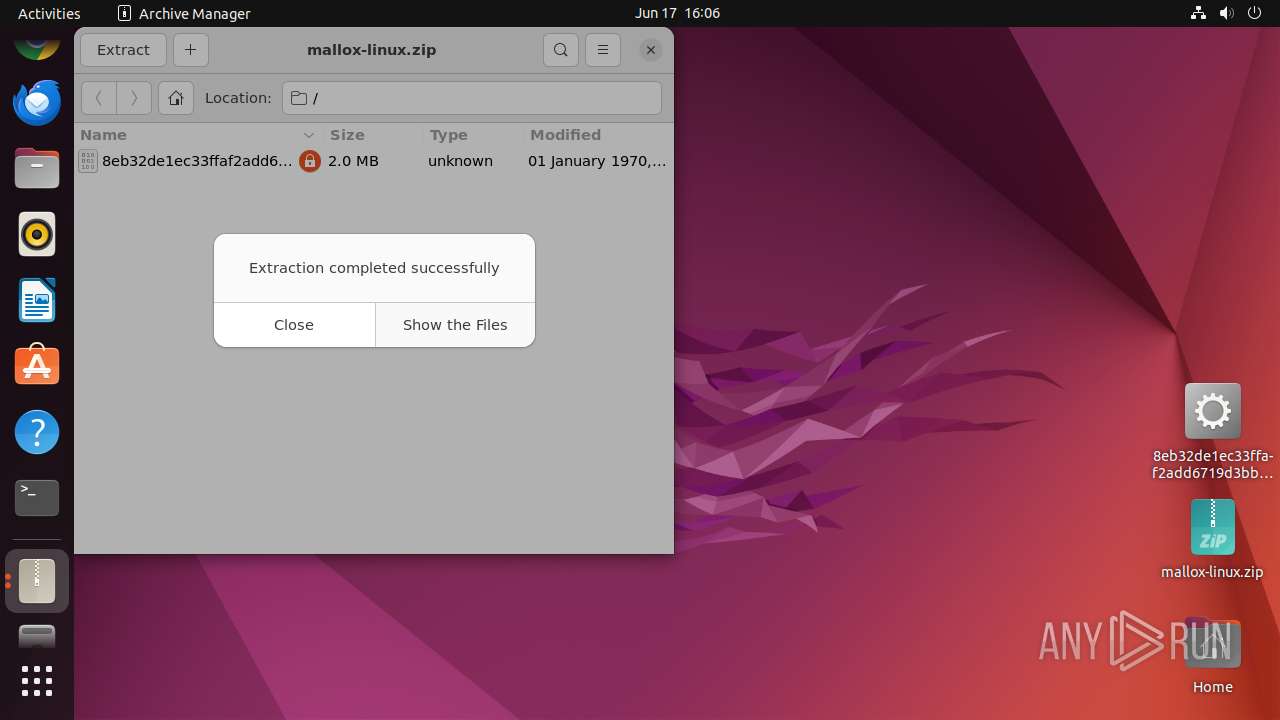
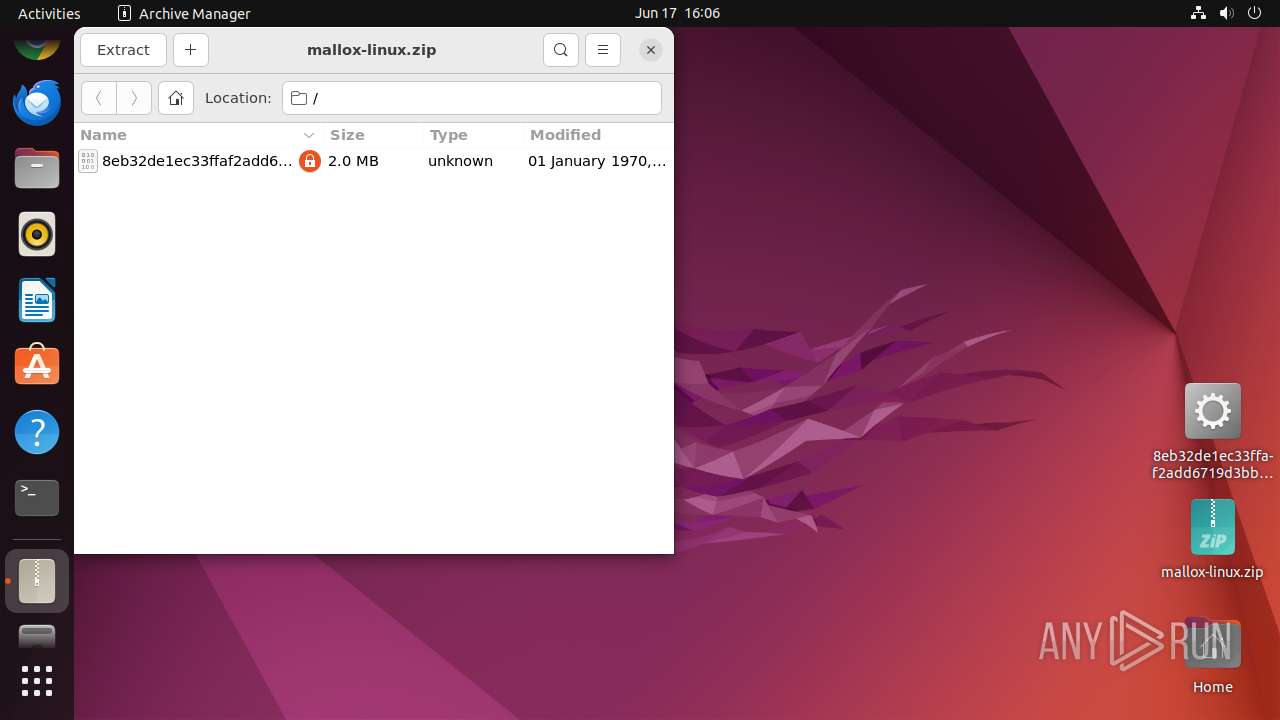
| File name: | mallox-linux.zip |
| Full analysis: | https://app.any.run/tasks/3c2df7e0-fa69-478a-a2c8-2baee8cb3455 |
| Verdict: | Malicious activity |
| Analysis date: | June 17, 2024, 15:06:01 |
| OS: | Ubuntu 22.04.2 |
| Indicators: | |
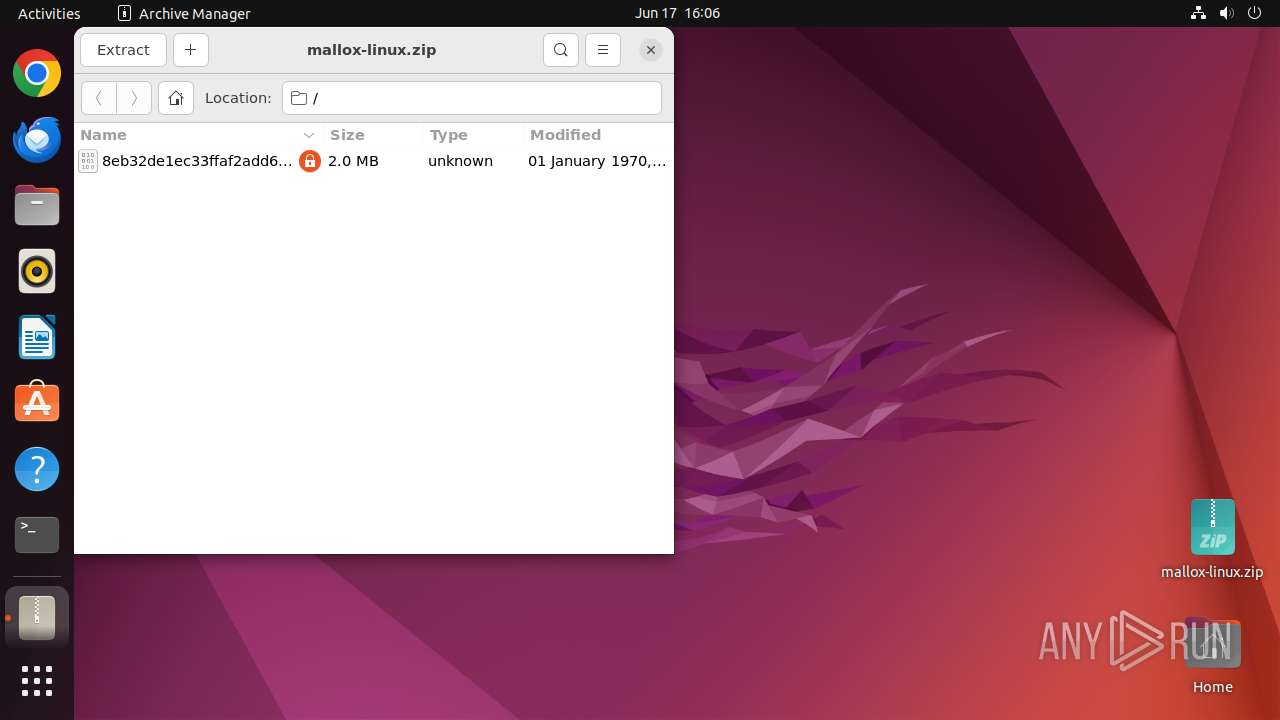
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 9F41AB9D1E98C63872CB681C31FE1953 |
| SHA1: | AA56EE683F841614959930C711BB38E342D77061 |
| SHA256: | E98B35F3D400BA5A8042C3C24EC8B048A4F39E663C2E1A3FB58CC301DA6E87CB |
| SSDEEP: | 49152:n06CkRSLPrBg7k1C+Bkf3ndbTSkpSUz5SdjrwtH3hyxgm+TdRszha+j19I7K2cSp:ukQzKA1RBQ3tpPgVWIxoTdC1d1z2gJn2 |
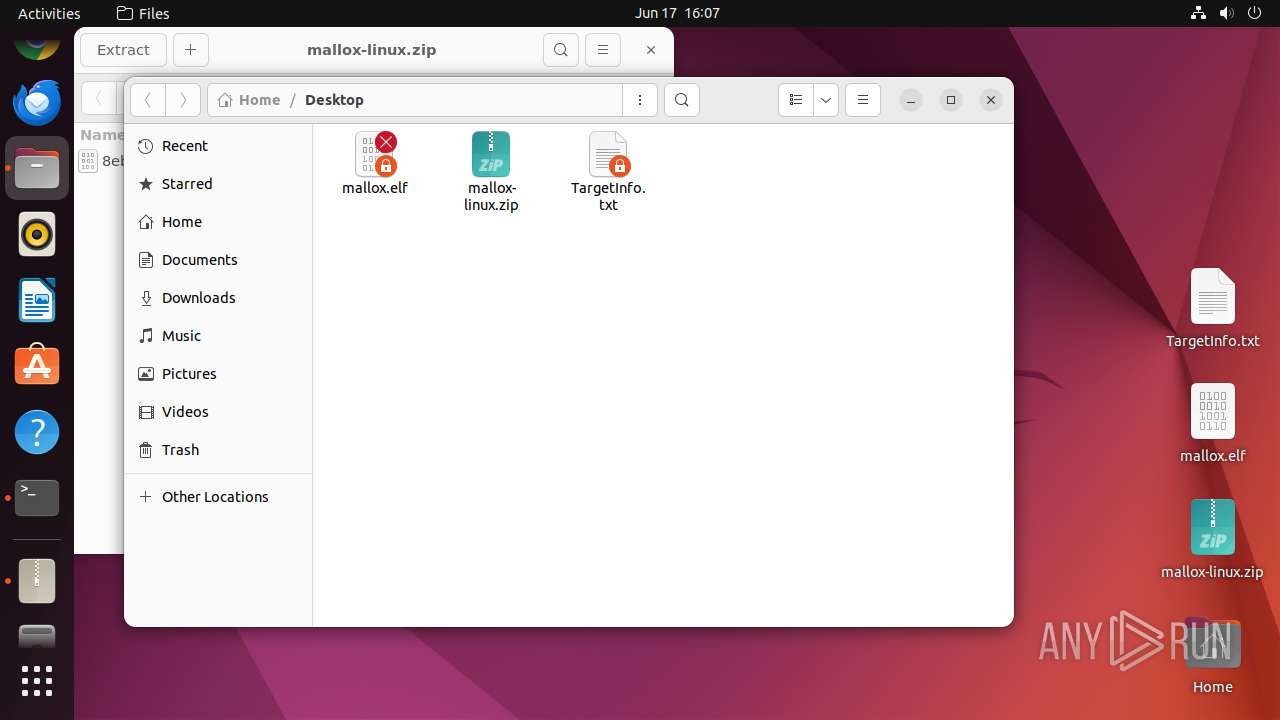
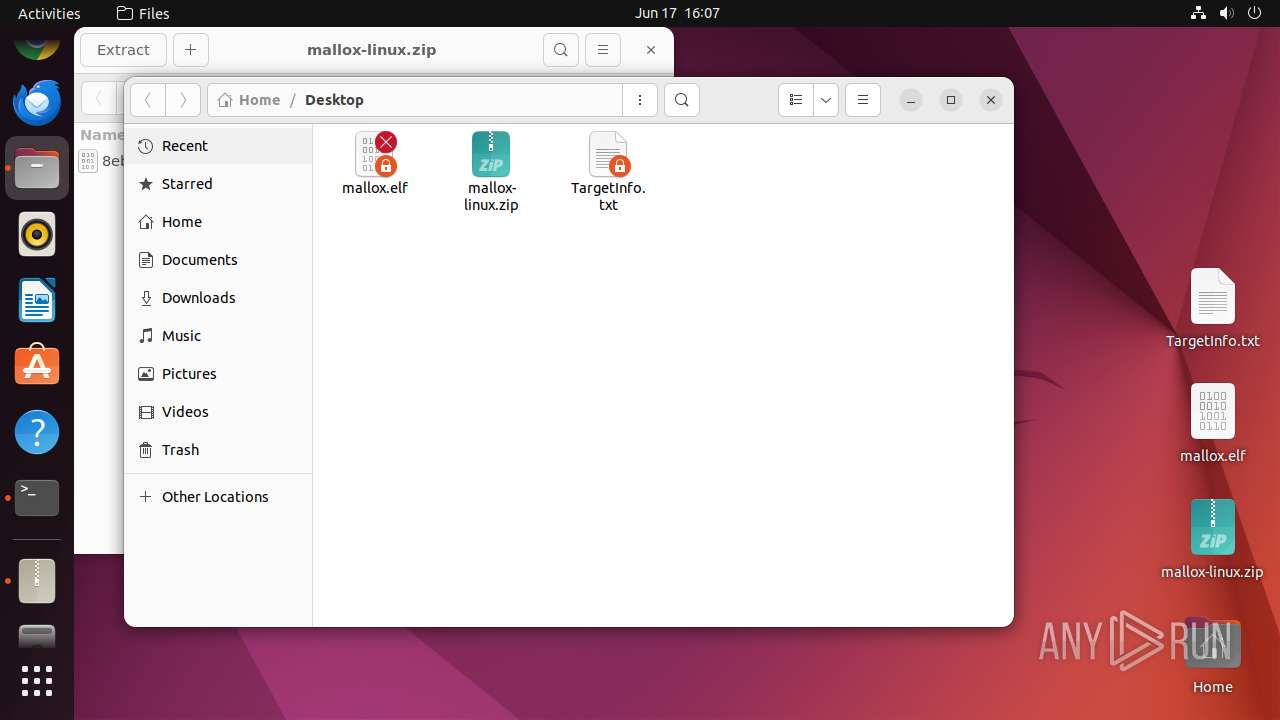
MALICIOUS
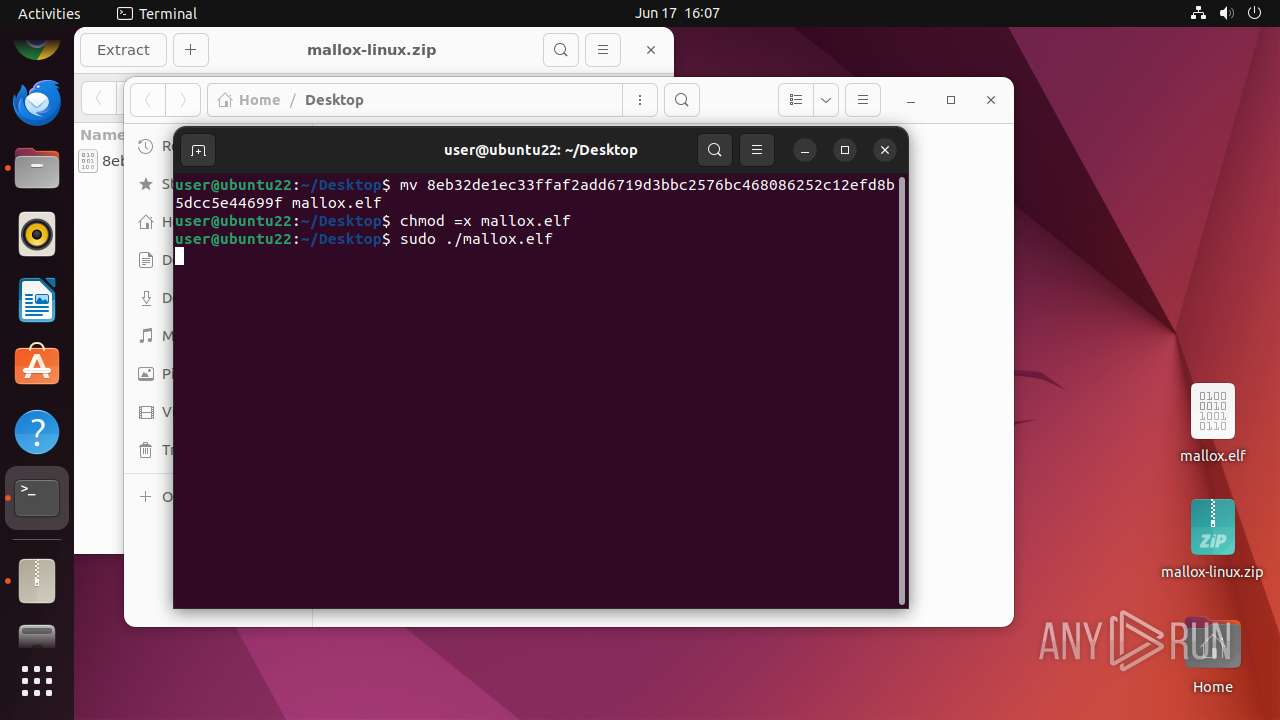
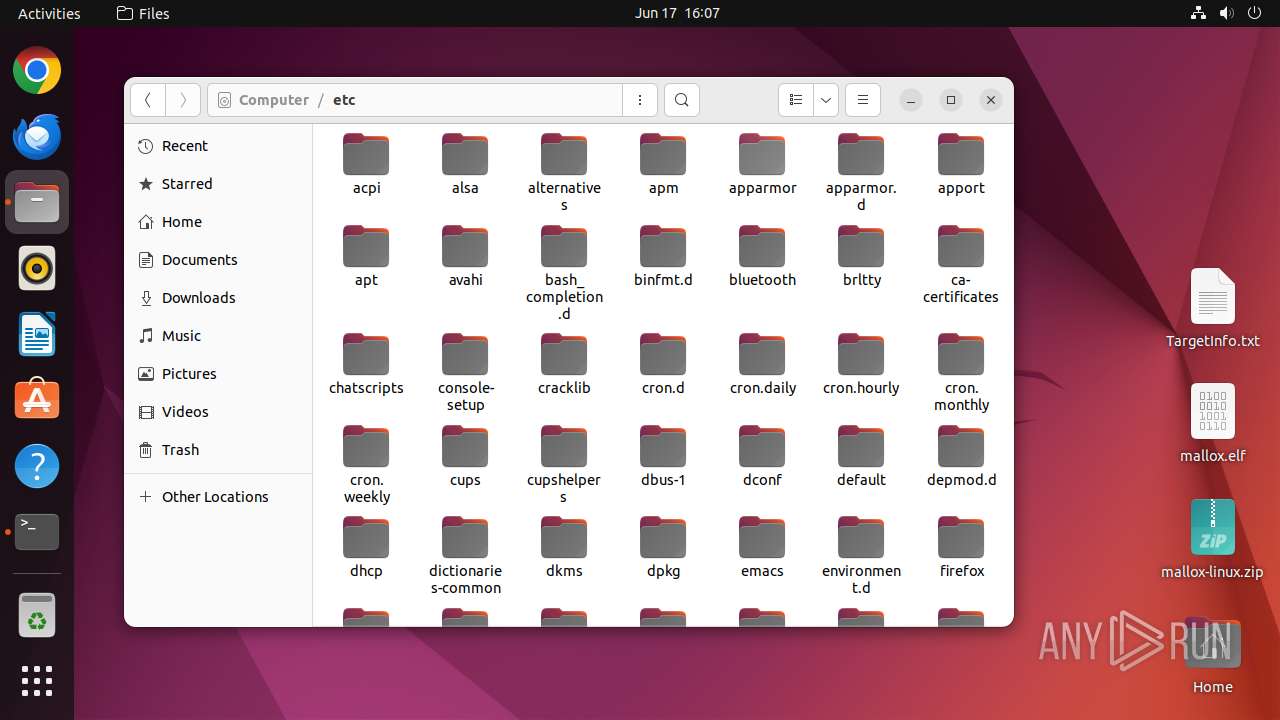
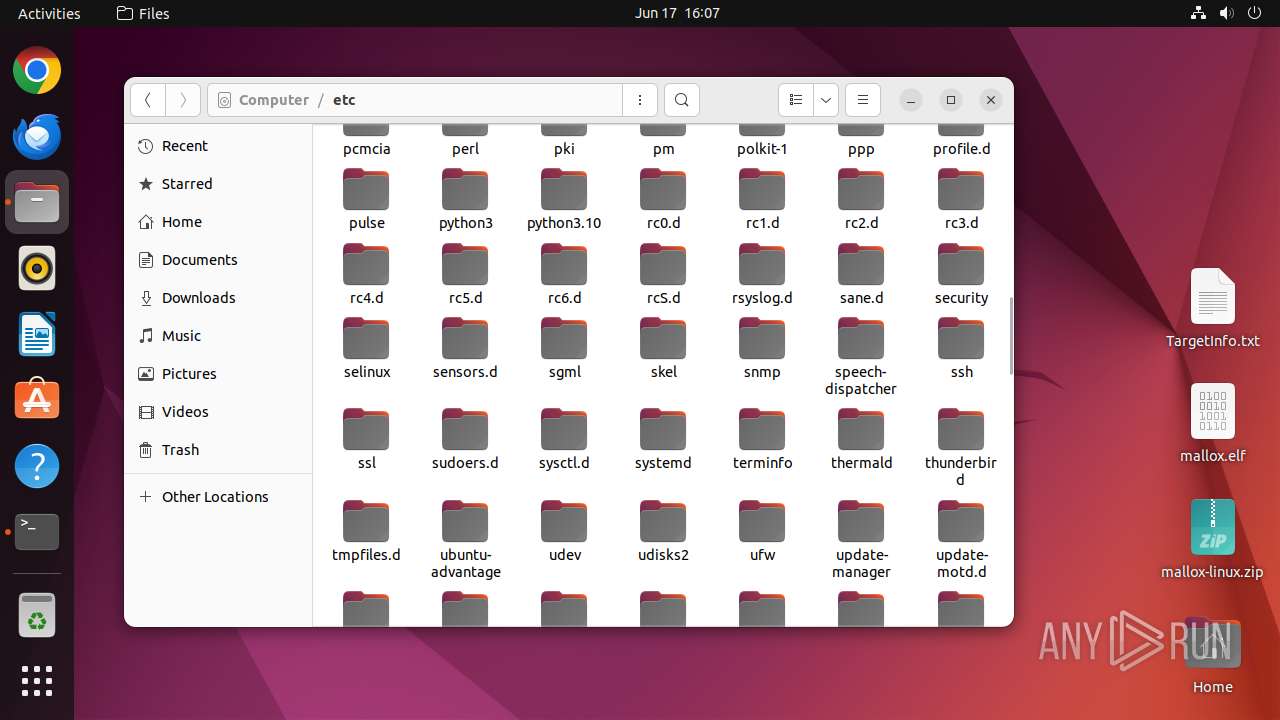
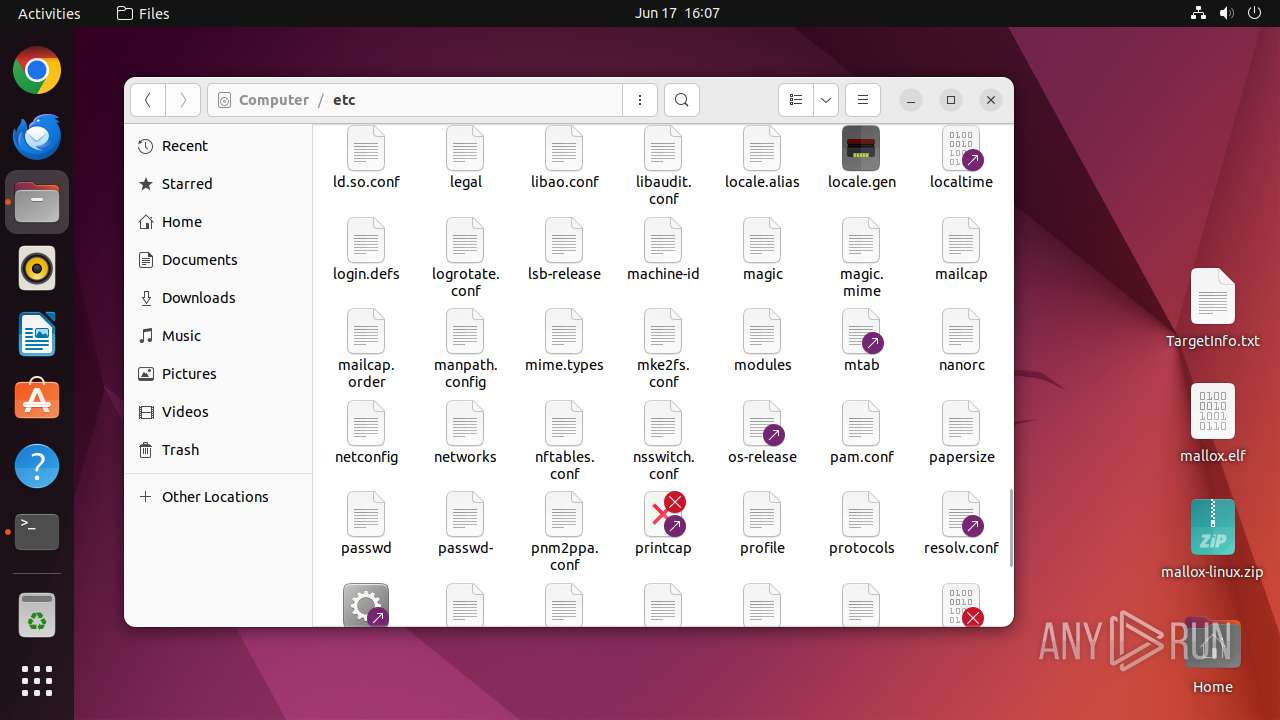
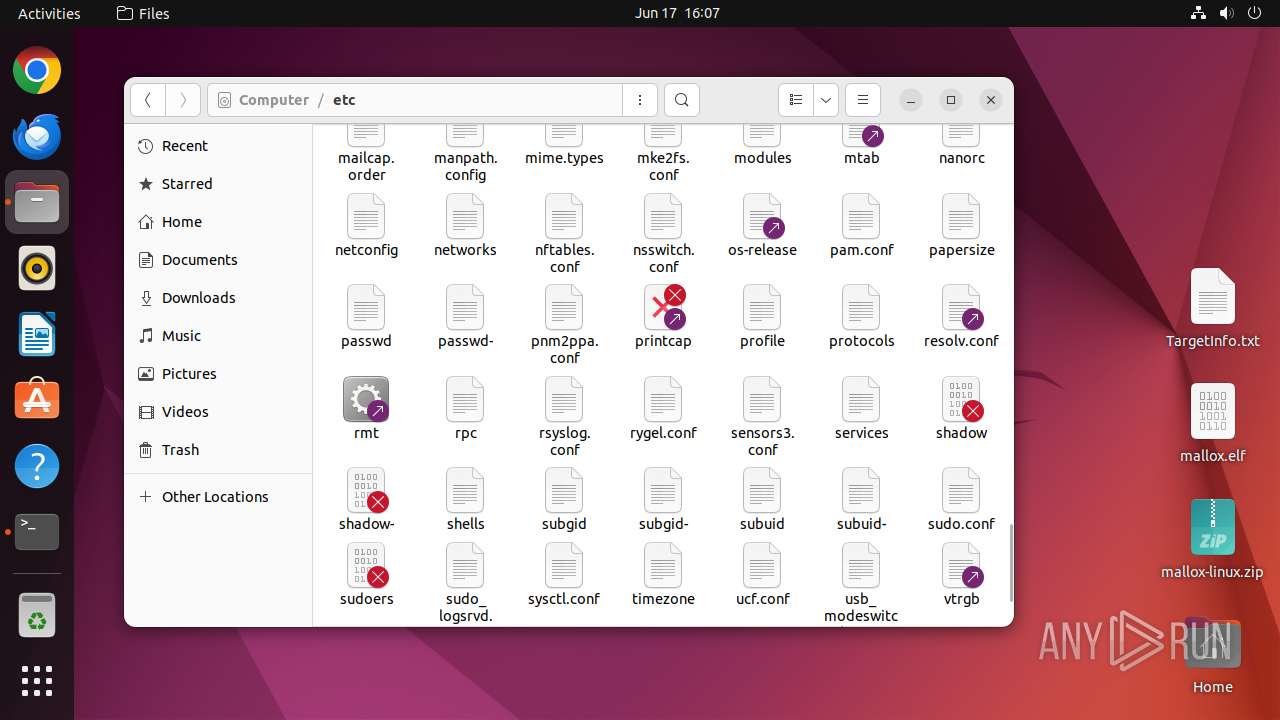
Drops the executable file immediately after the start
- mallox.elf (PID: 13098)
SUSPICIOUS
Modifies bash configuration script
- mallox.elf (PID: 13098)
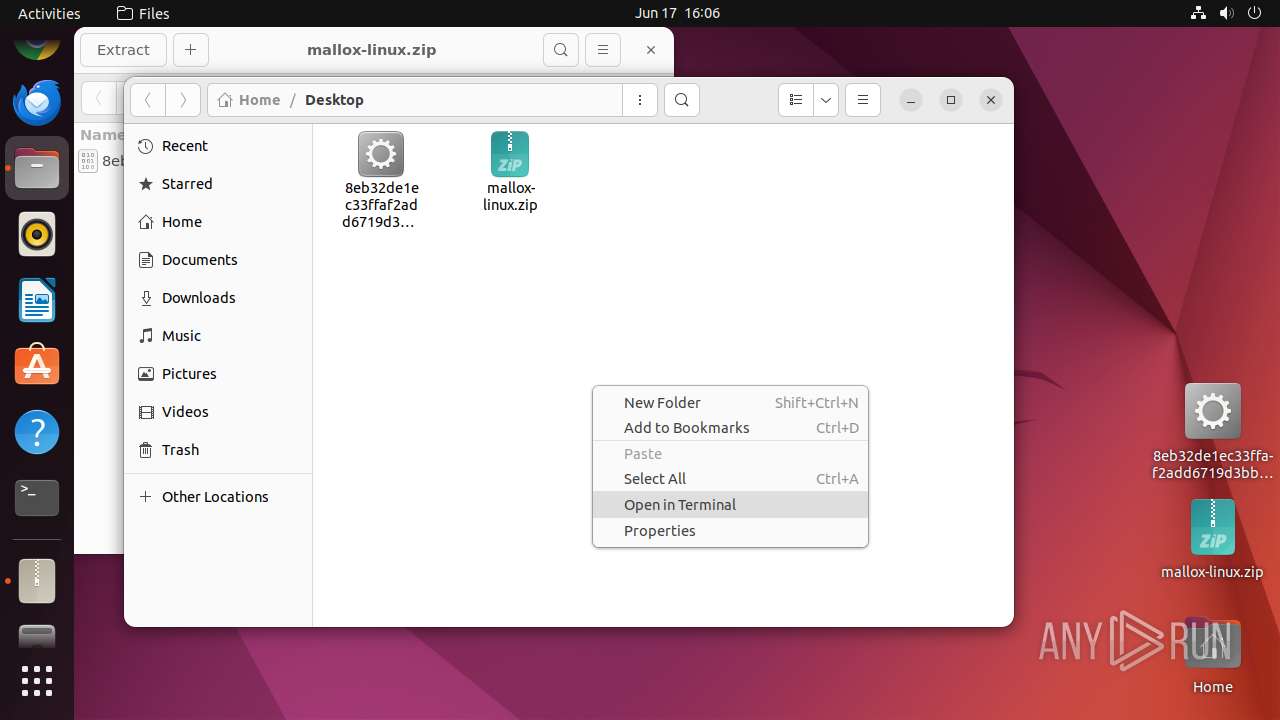
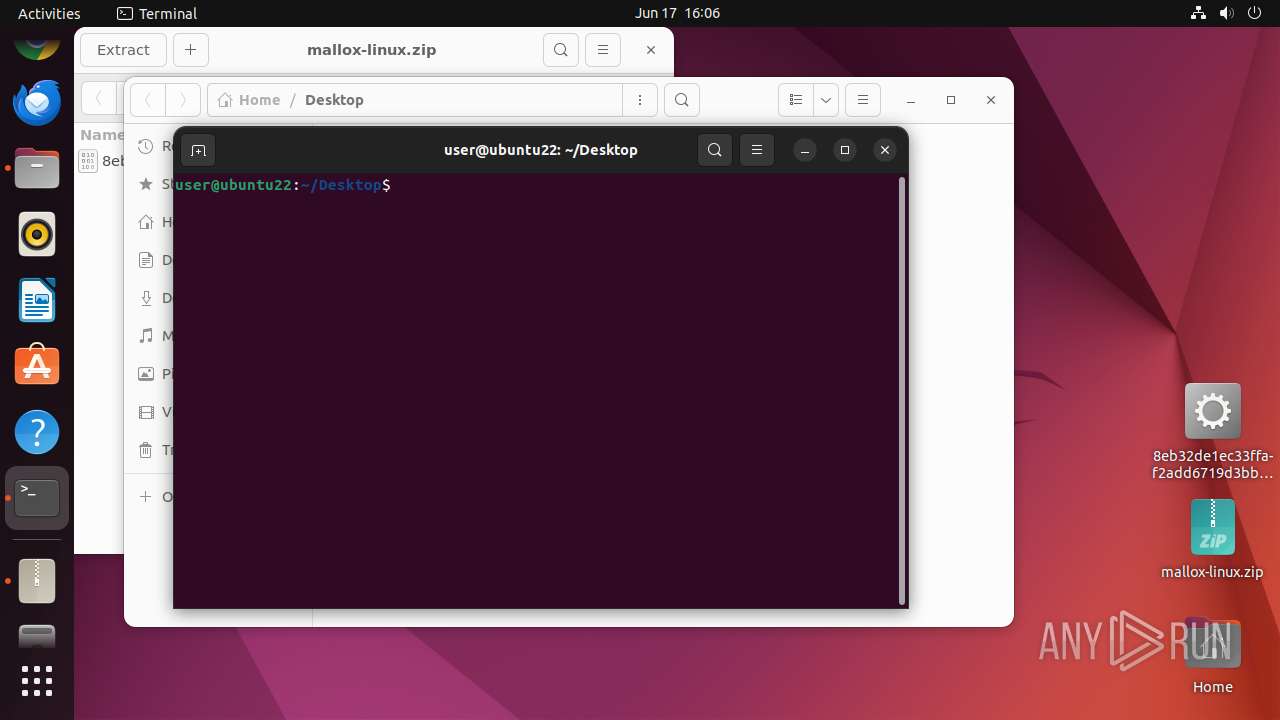
Executes commands using command-line interpreter
- gnome-terminal-server (PID: 13039)
Checks DMI information (probably VM detection)
- systemd-hostnamed (PID: 12980)
INFO
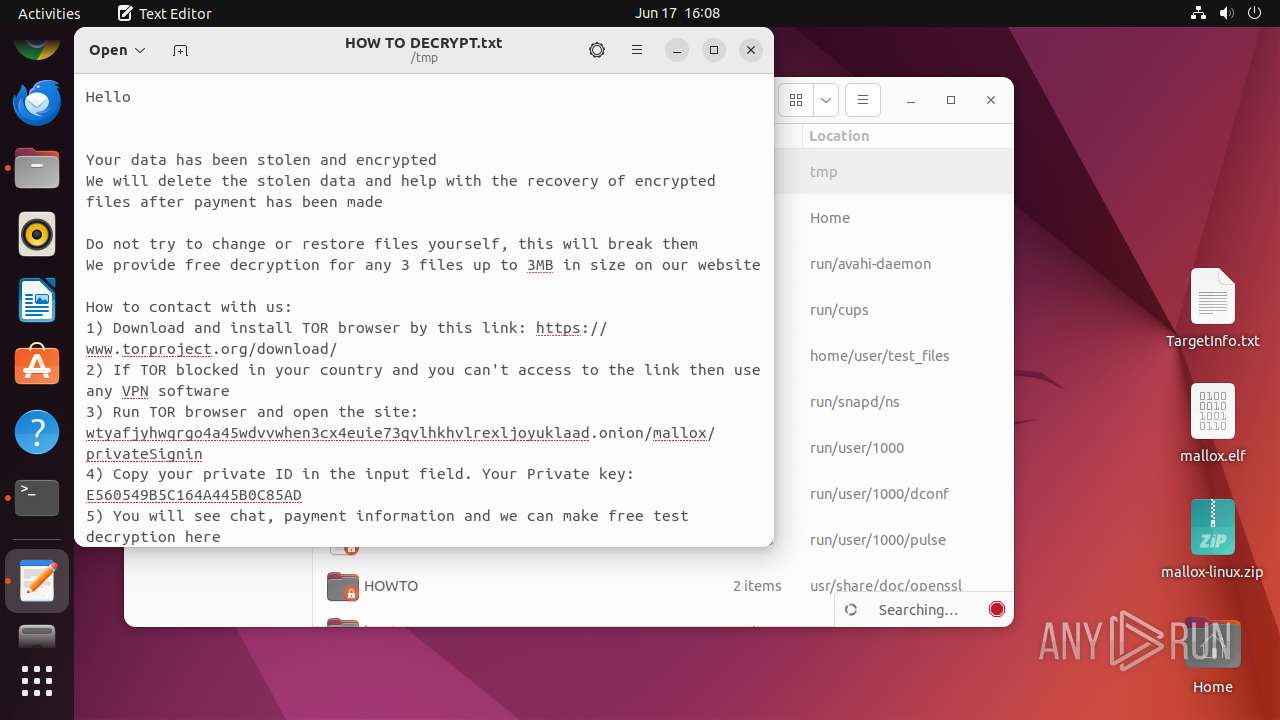
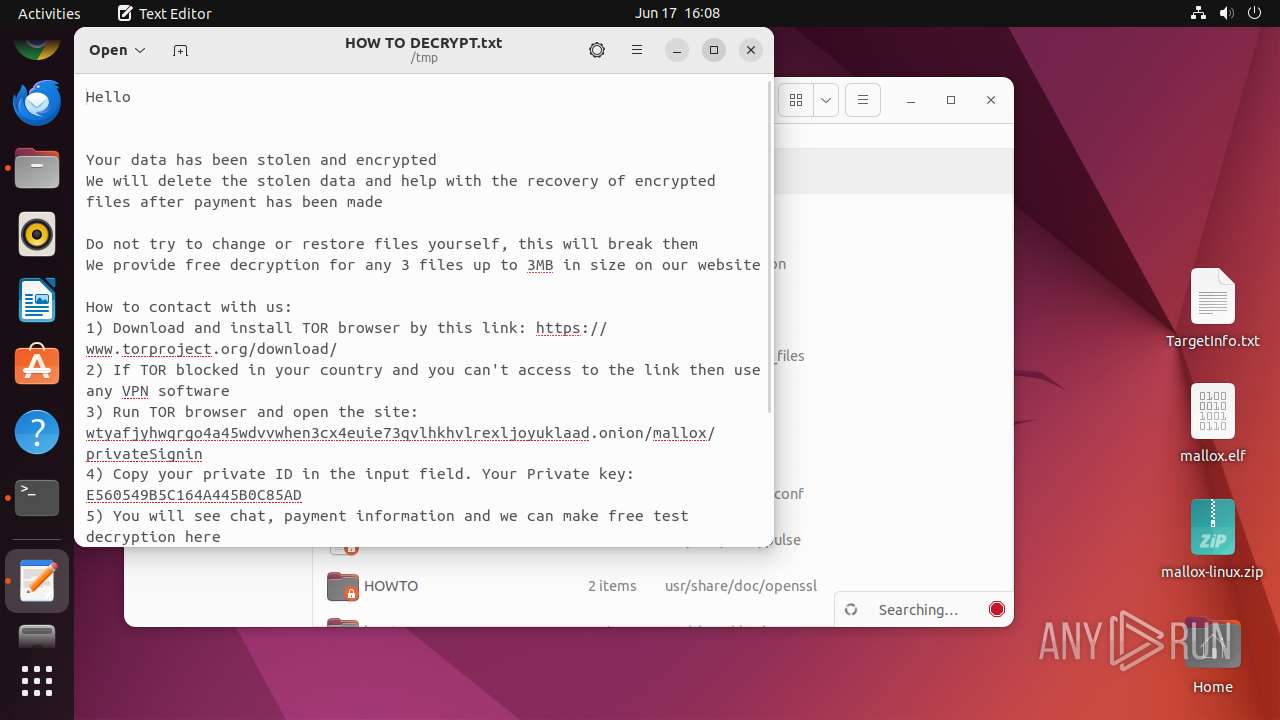
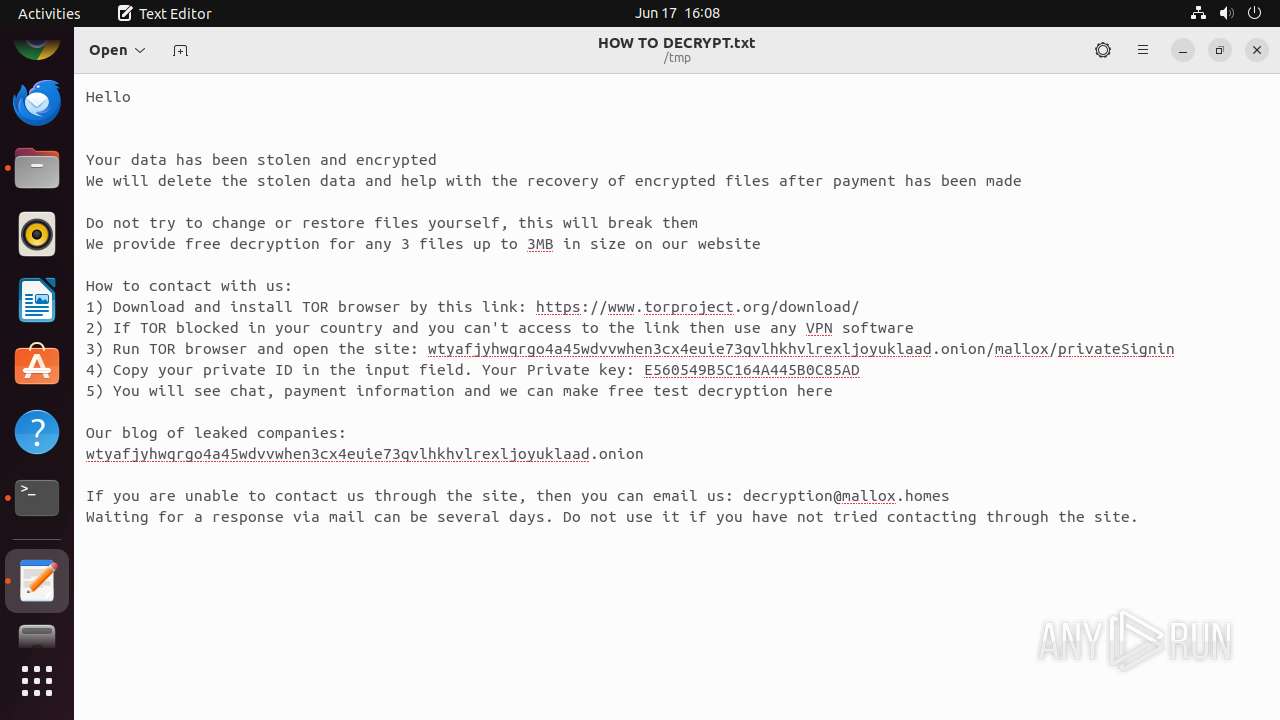
Dropped object may contain TOR URL's
- 7z (PID: 13010)
- mallox.elf (PID: 13098)
The dropped object may contain a URL to Tor Browser
- 7z (PID: 13010)
- mallox.elf (PID: 13098)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0x144fe78c |
| ZipCompressedSize: | 869349 |
| ZipUncompressedSize: | 1991784 |
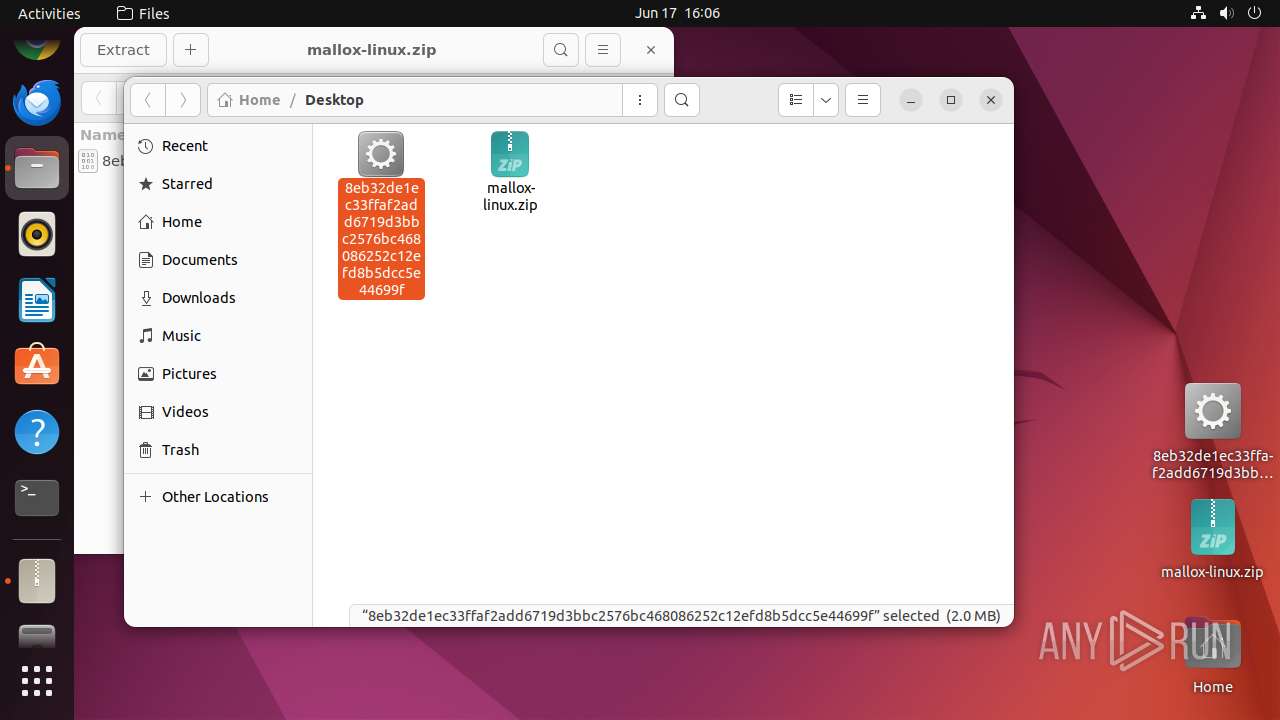
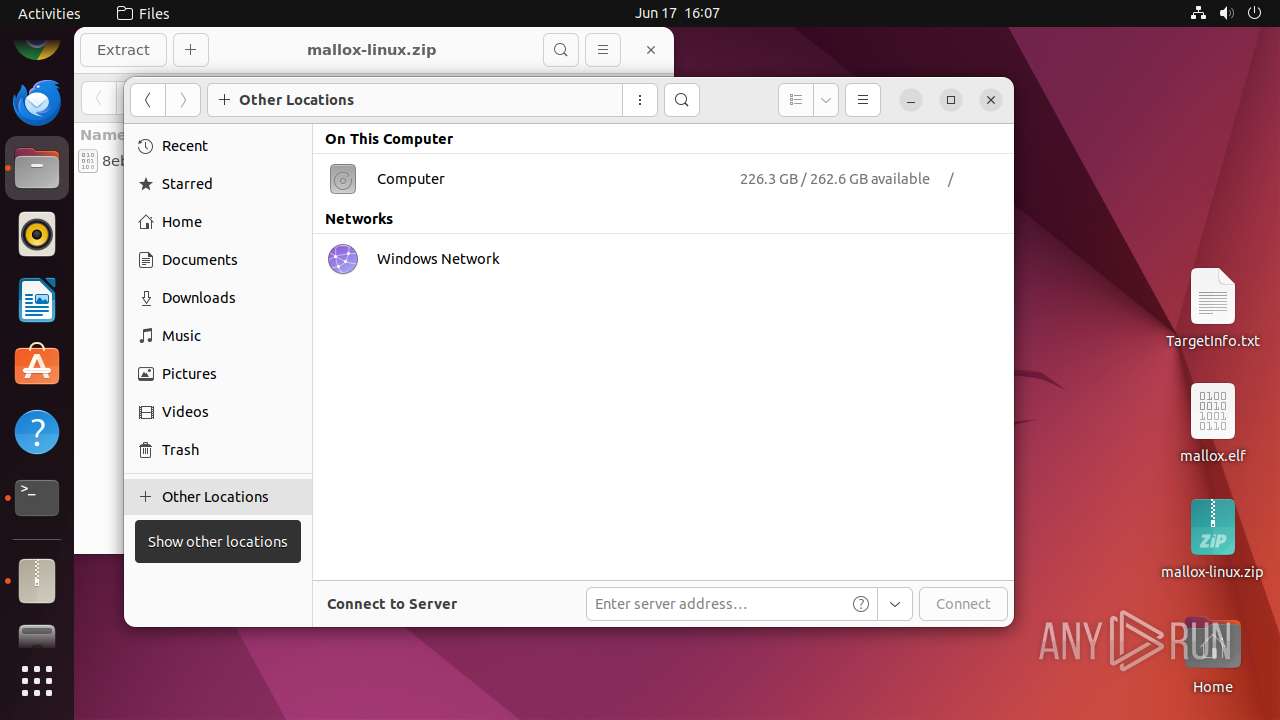
| ZipFileName: | 8eb32de1ec33ffaf2add6719d3bbc2576bc468086252c12efd8b5dcc5e44699f |
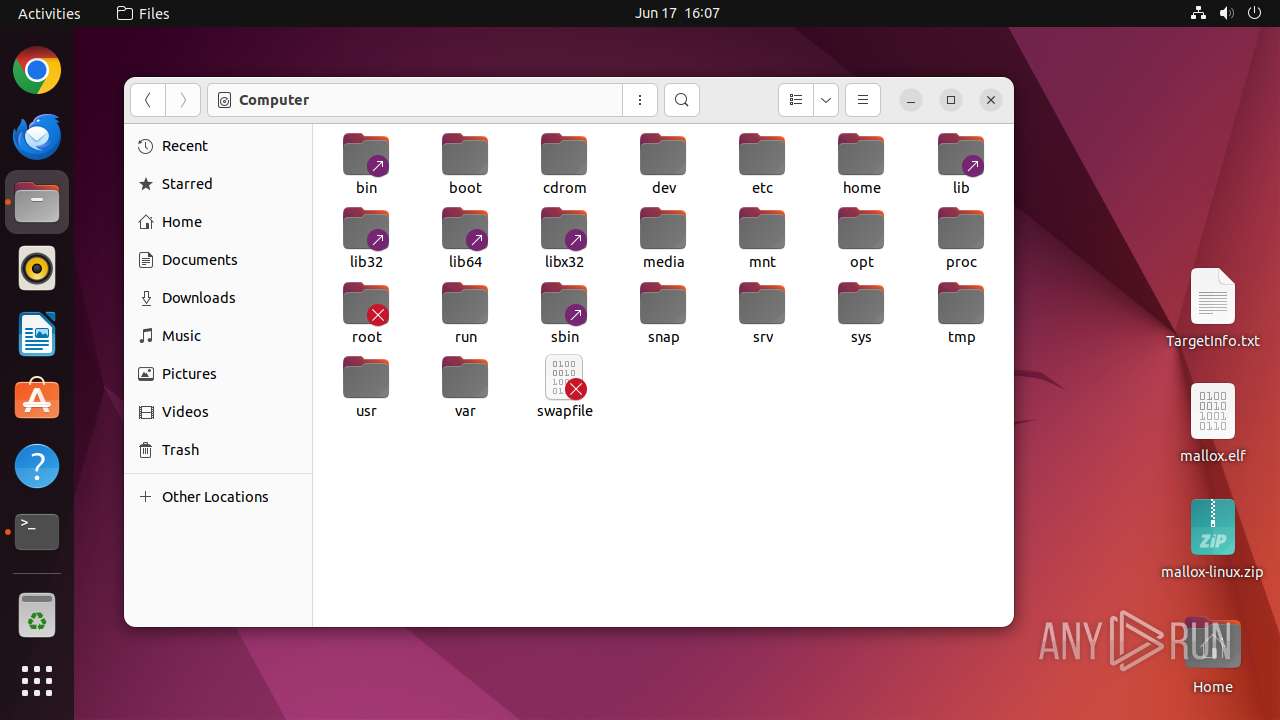
Total processes
265
Monitored processes
48
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 12944 | sh -c "file --mime-type /home/user/Desktop/mallox-linux\.zip" | /bin/sh | — | any-guest-agent |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12945 | file --mime-type /home/user/Desktop/mallox-linux.zip | /usr/bin/file | — | sh |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12946 | /bin/sh -c "DISPLAY=:0 sudo -iu user file-roller /home/user/Desktop/mallox-linux\.zip " | /bin/sh | — | any-guest-agent |
User: root Integrity Level: UNKNOWN | ||||
| 12947 | sudo -iu user file-roller /home/user/Desktop/mallox-linux.zip | /usr/bin/sudo | — | sh |
User: root Integrity Level: UNKNOWN | ||||
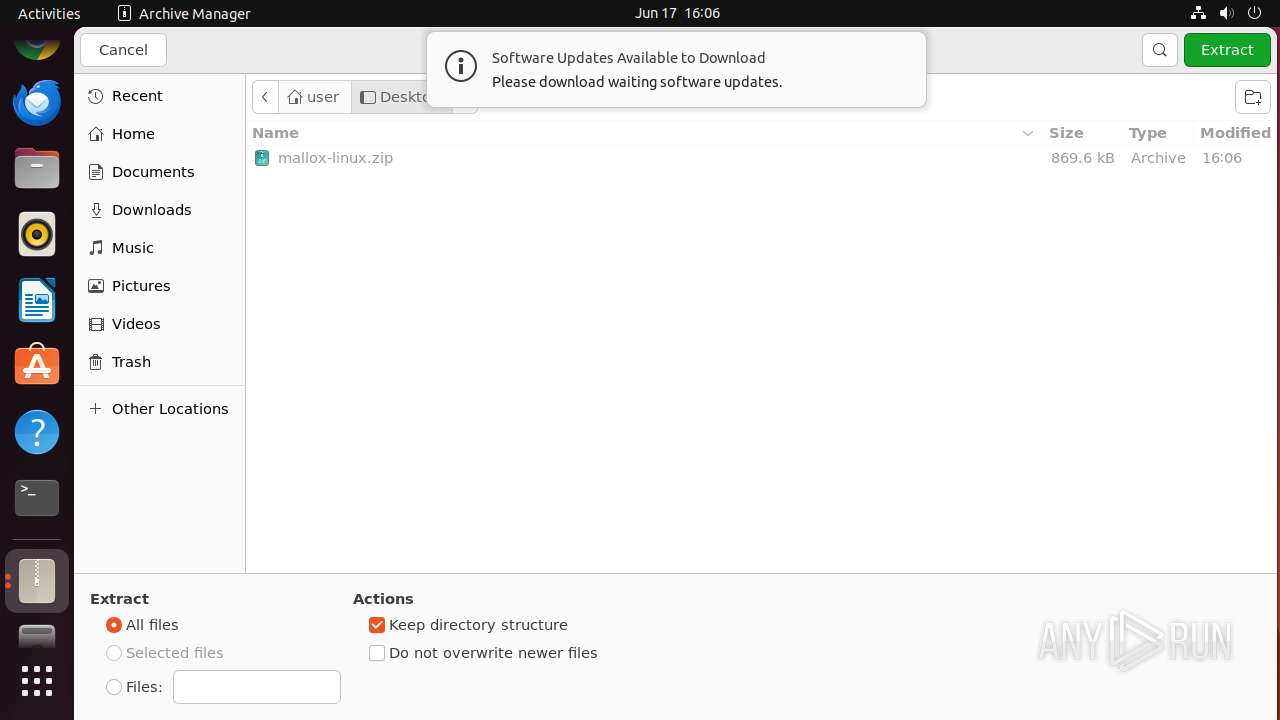
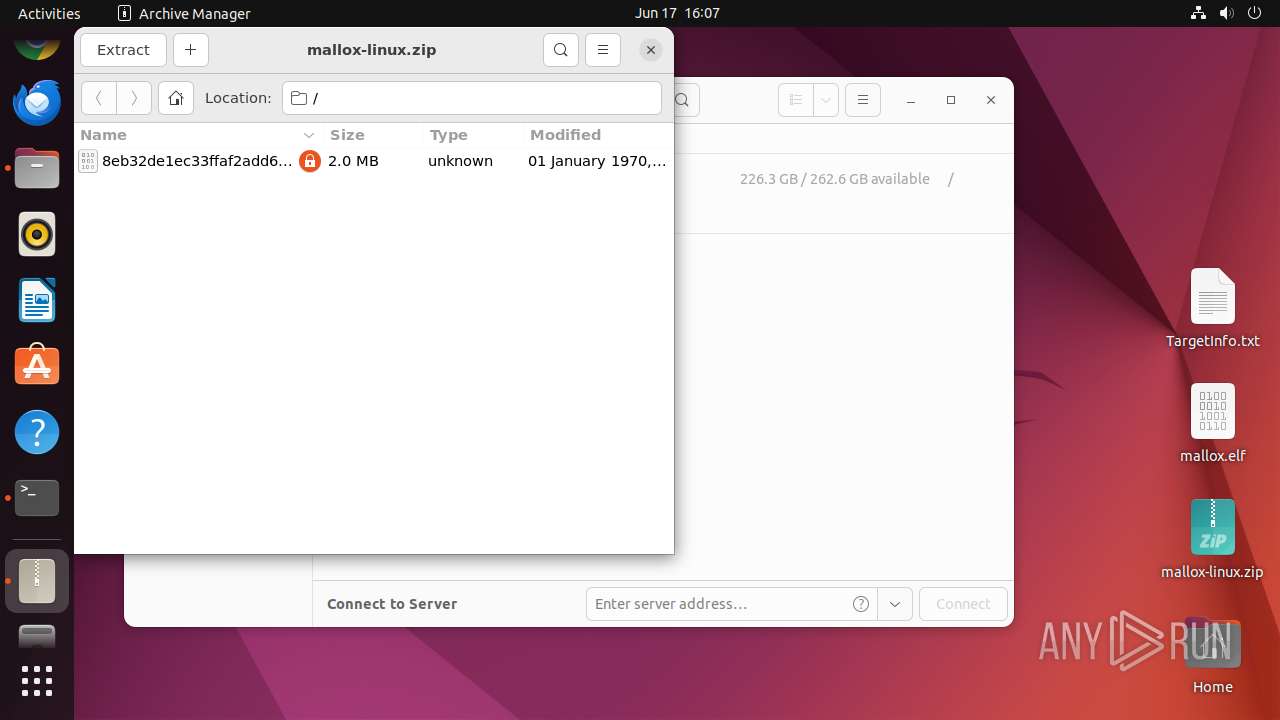
| 12948 | file-roller /home/user/Desktop/mallox-linux.zip | /usr/bin/file-roller | — | sudo |
User: user Integrity Level: UNKNOWN | ||||
| 12949 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | file-roller |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12963 | /usr/lib/p7zip/7z l -slt -bd -y -- /home/user/Desktop/mallox-linux.zip | /usr/lib/p7zip/7z | — | file-roller |
User: user Integrity Level: UNKNOWN Exit code: 482 | ||||
| 12964 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 482 | ||||
| 12965 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 482 | ||||
| 12966 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 482 | ||||
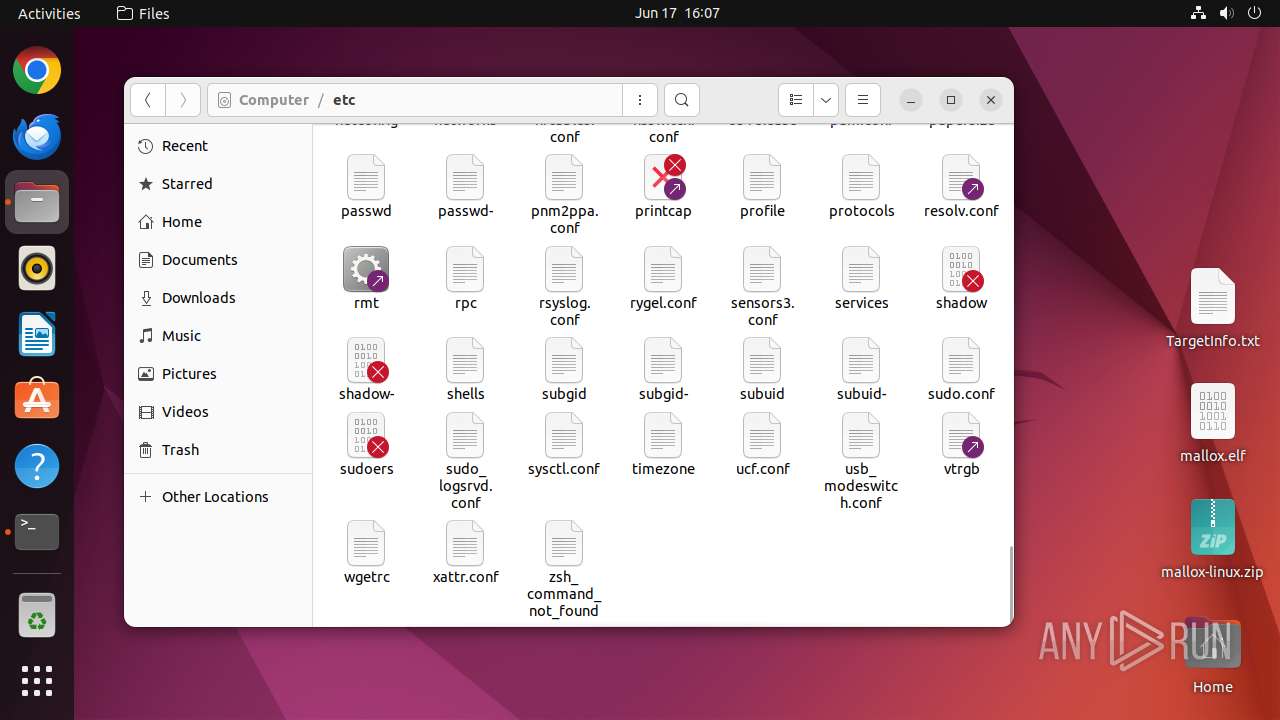
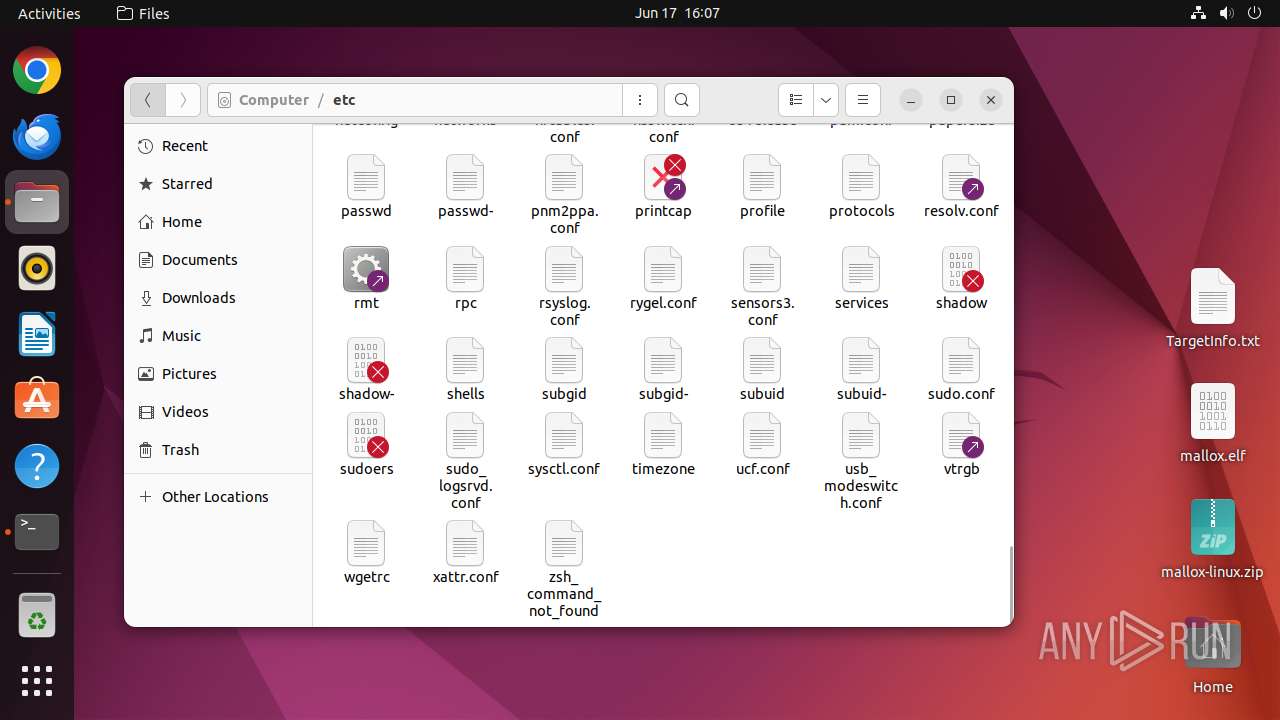
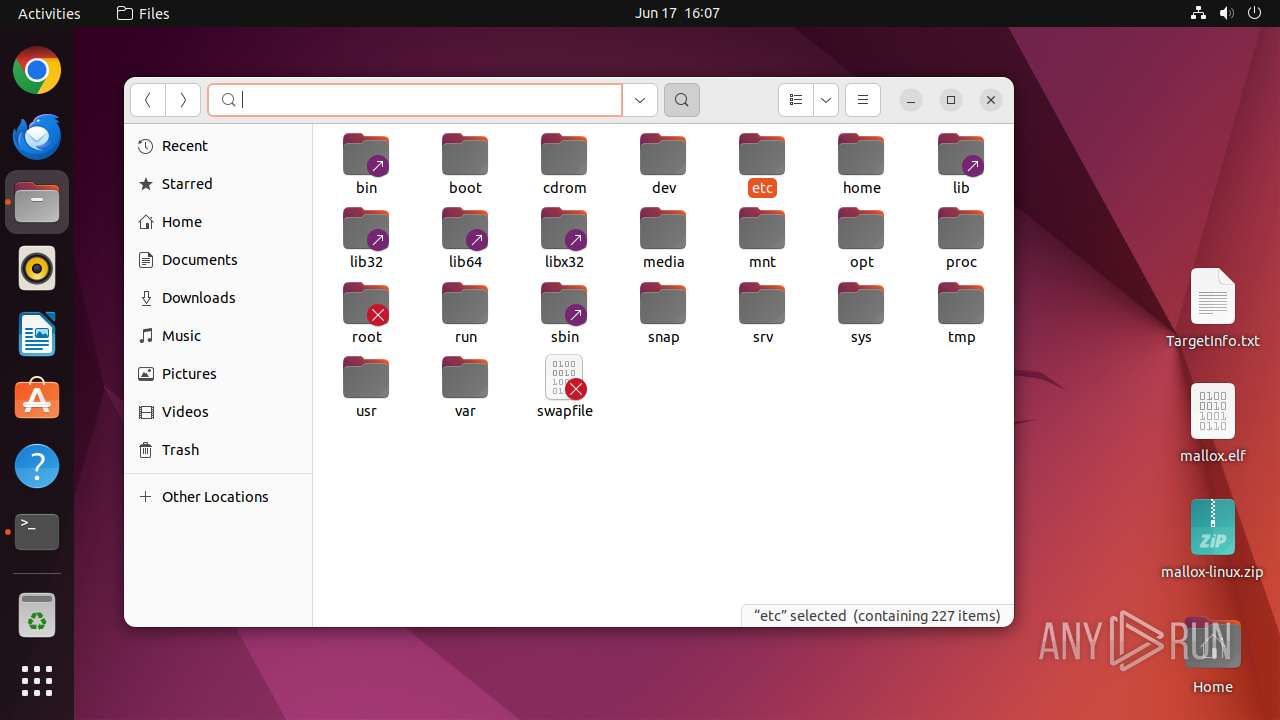
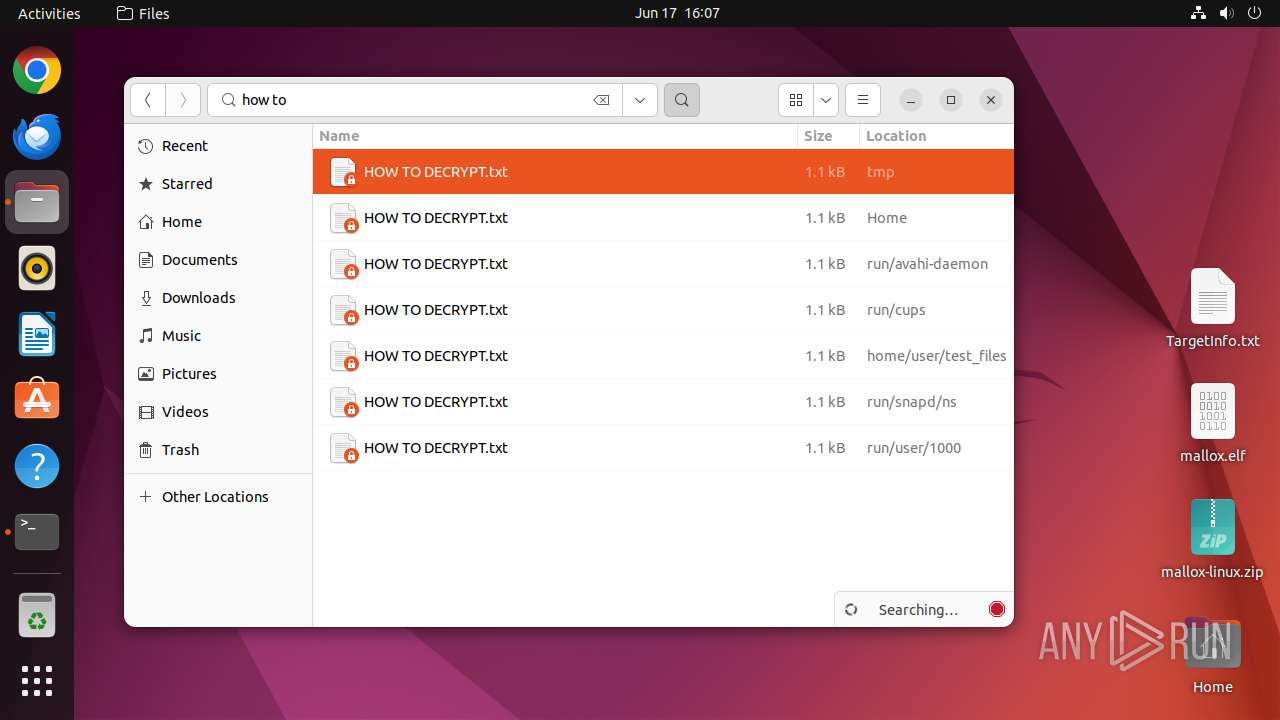
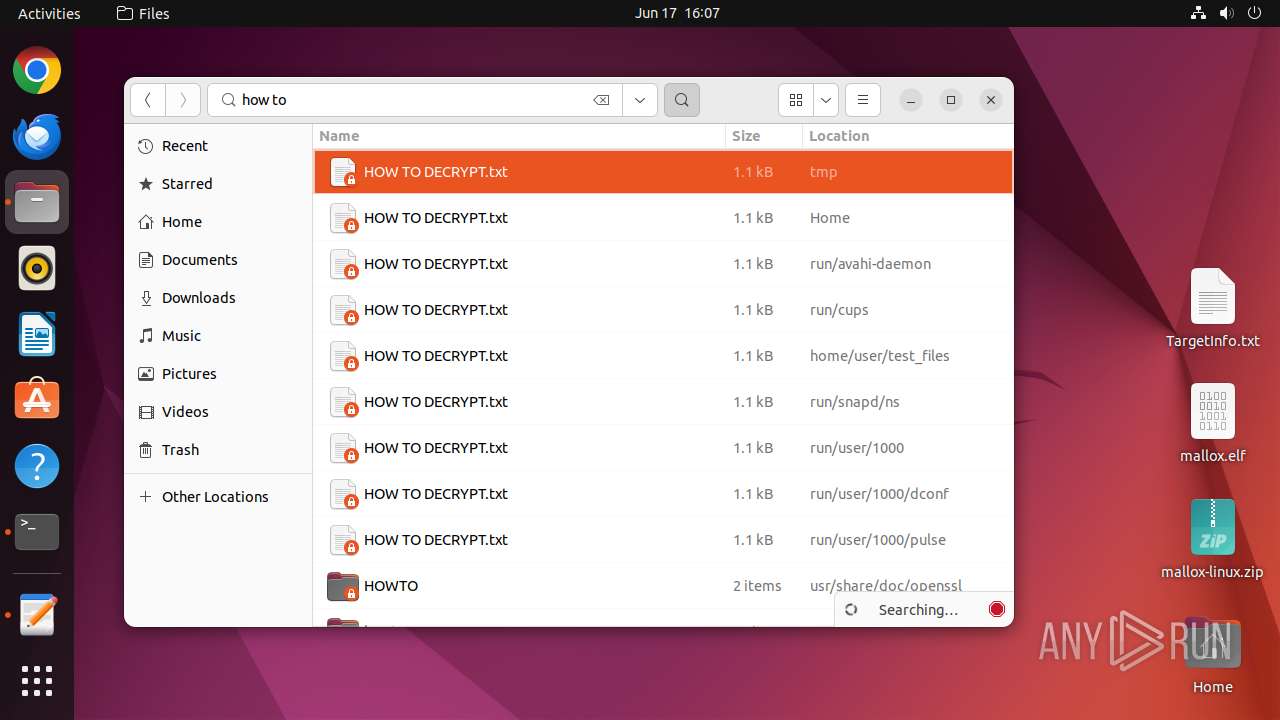
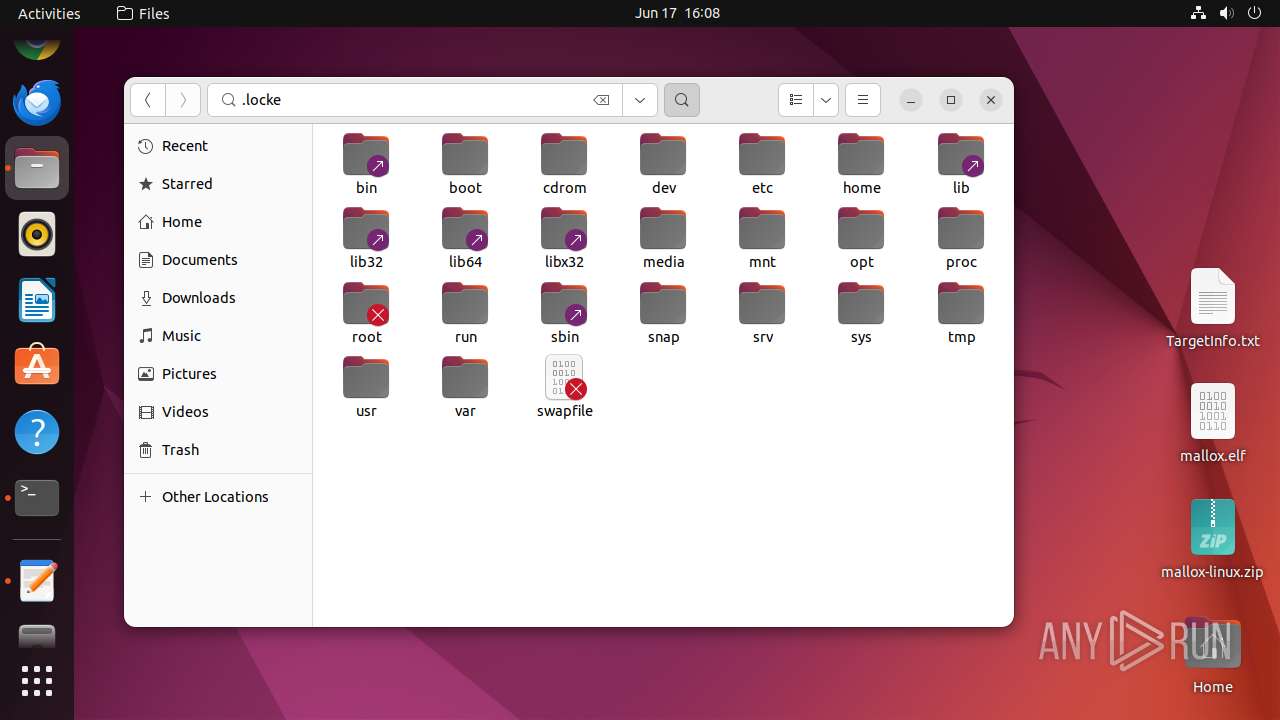
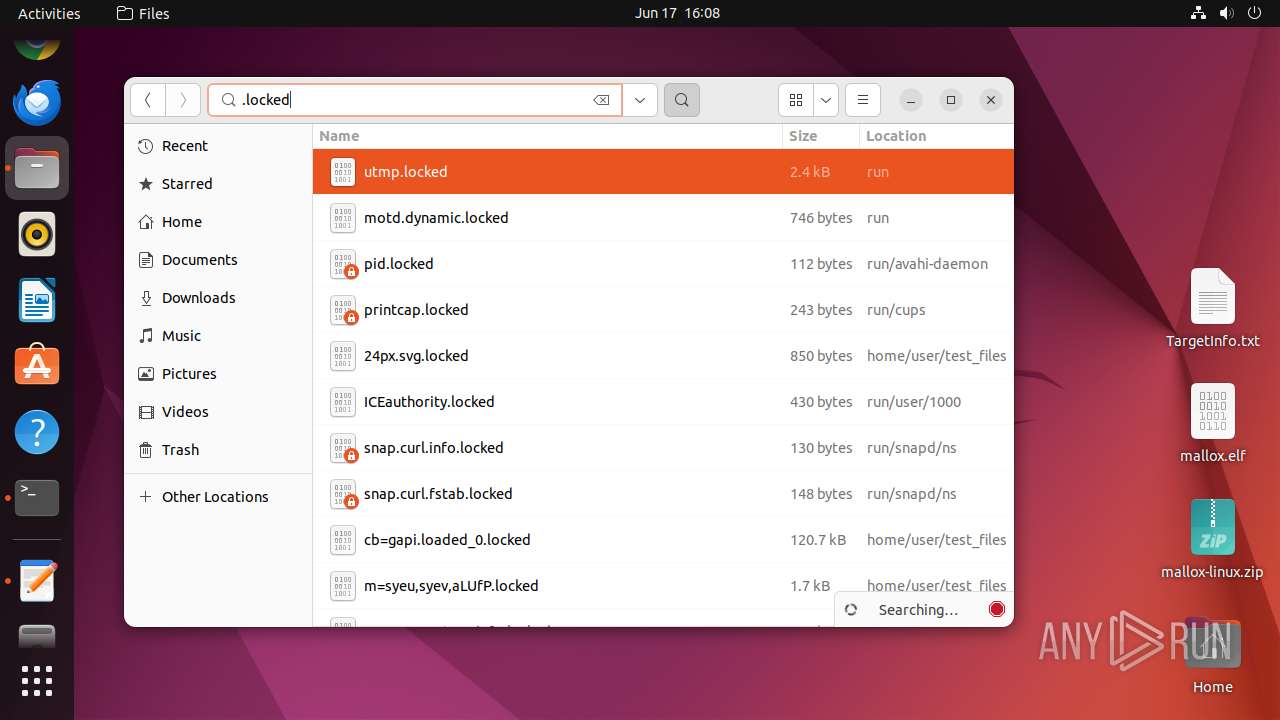
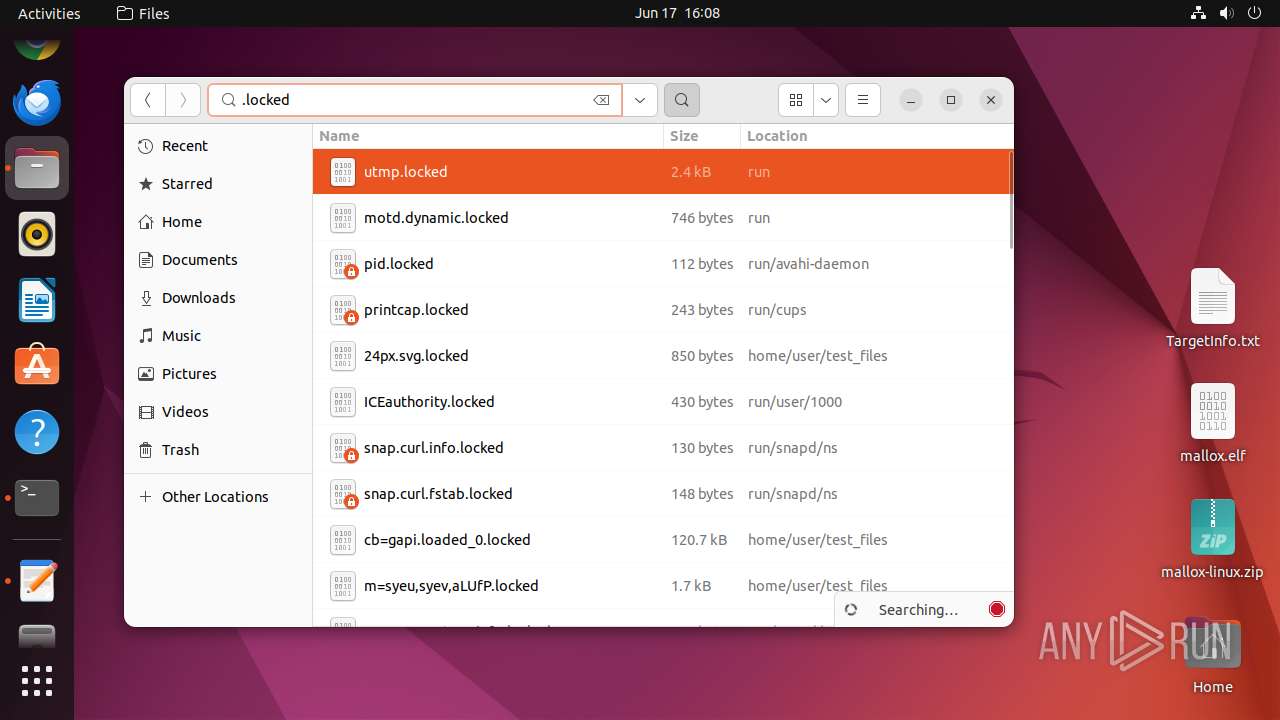
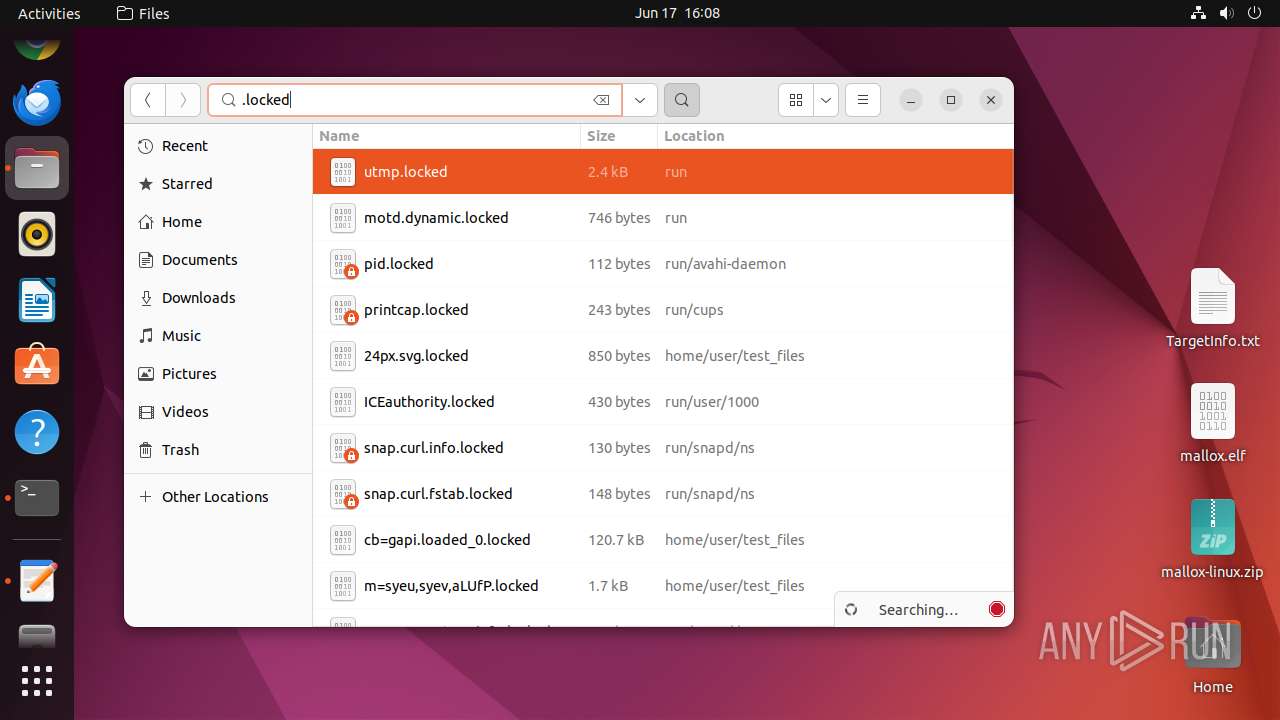
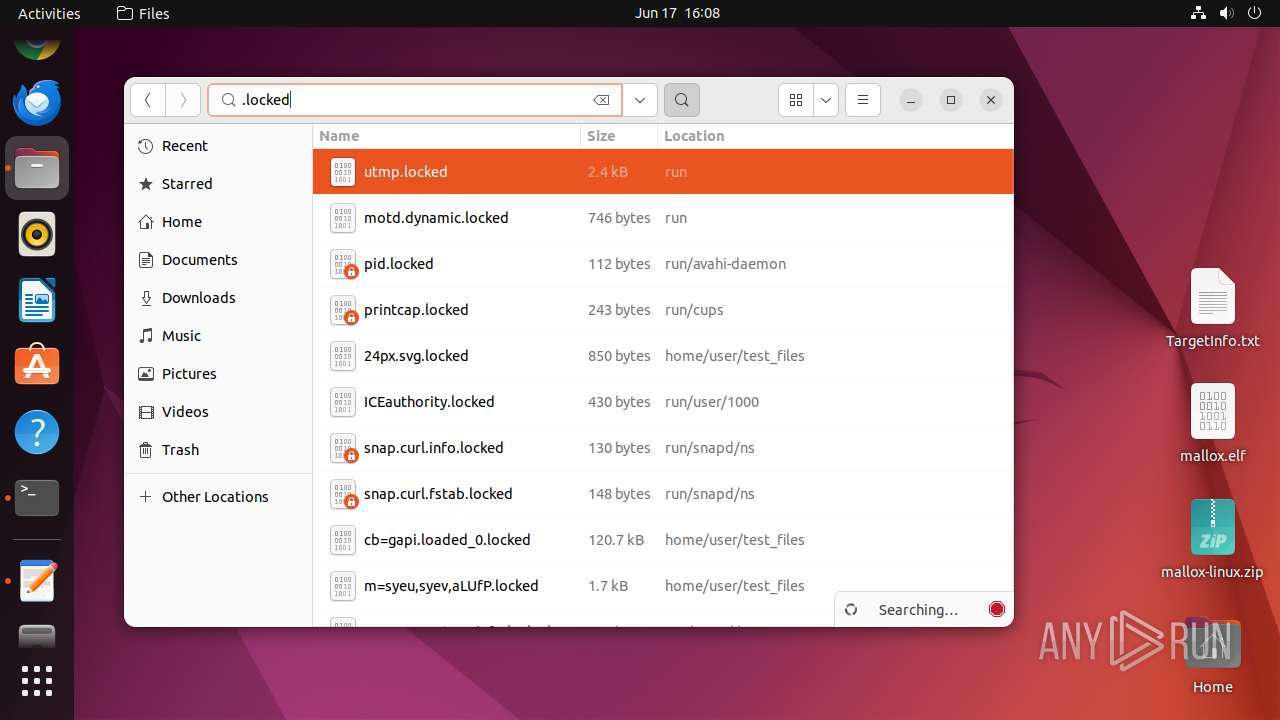
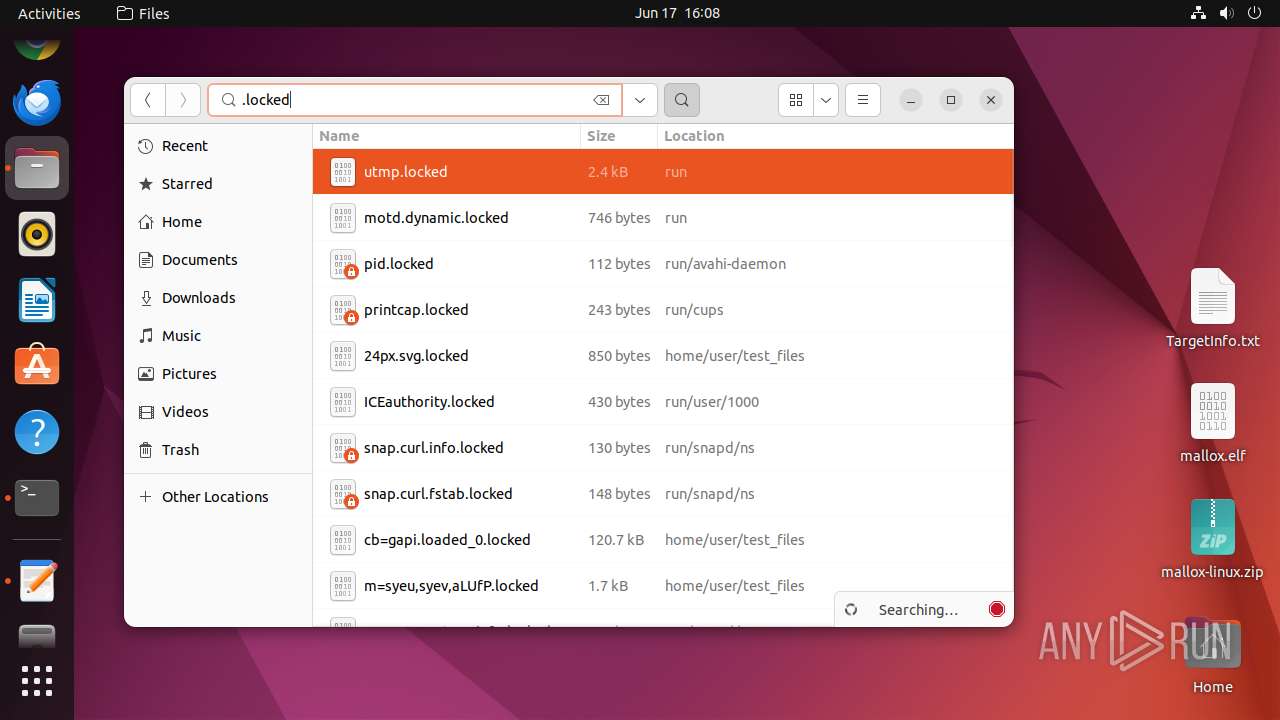
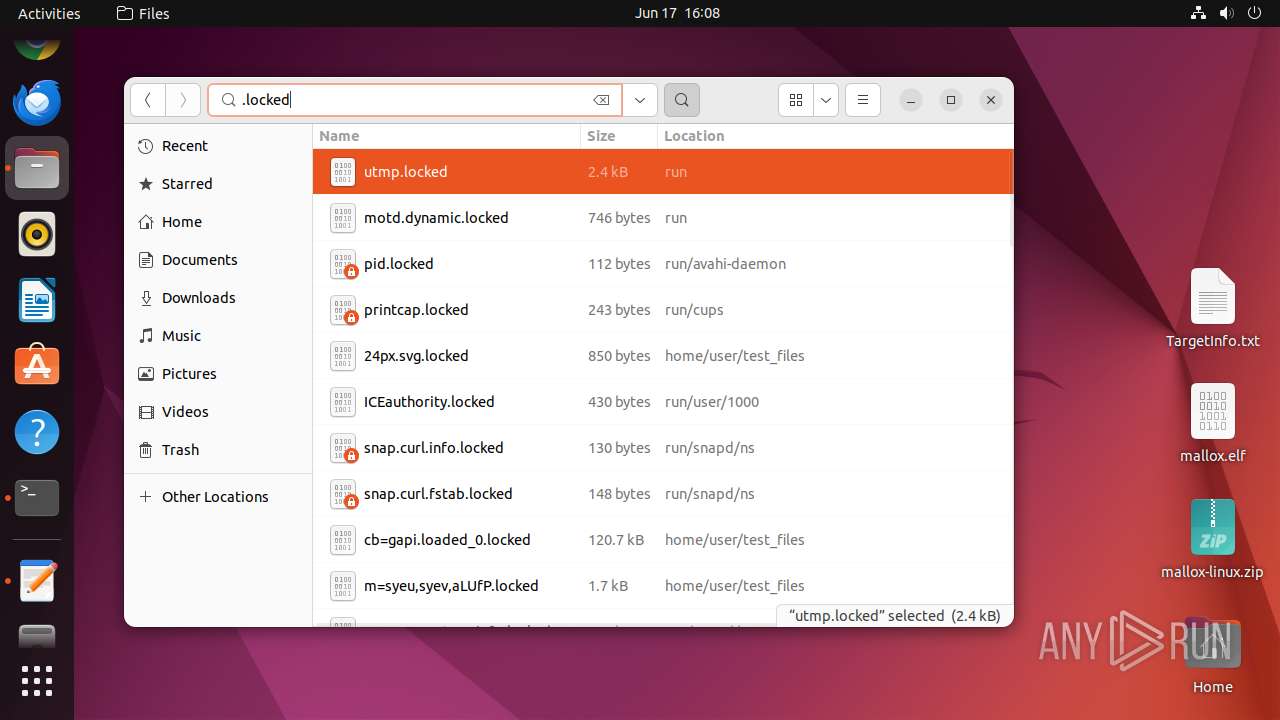
Executable files
0
Suspicious files
188
Text files
308
Unknown types
2
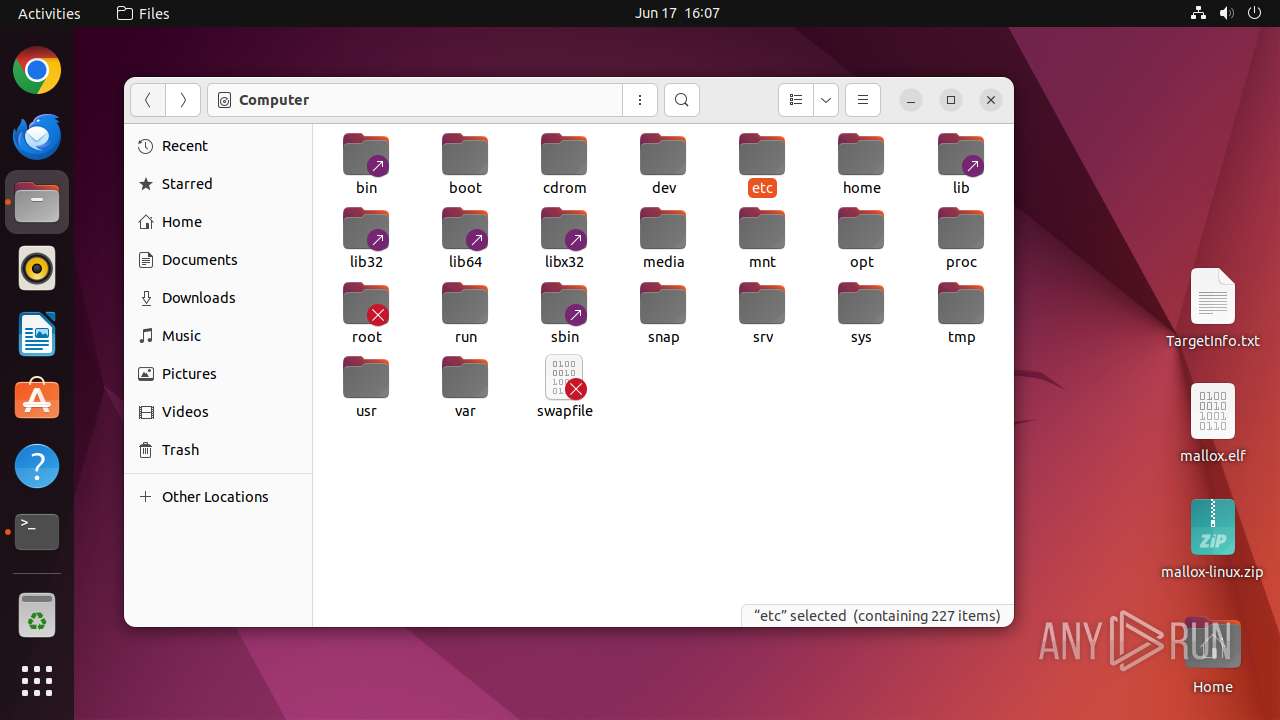
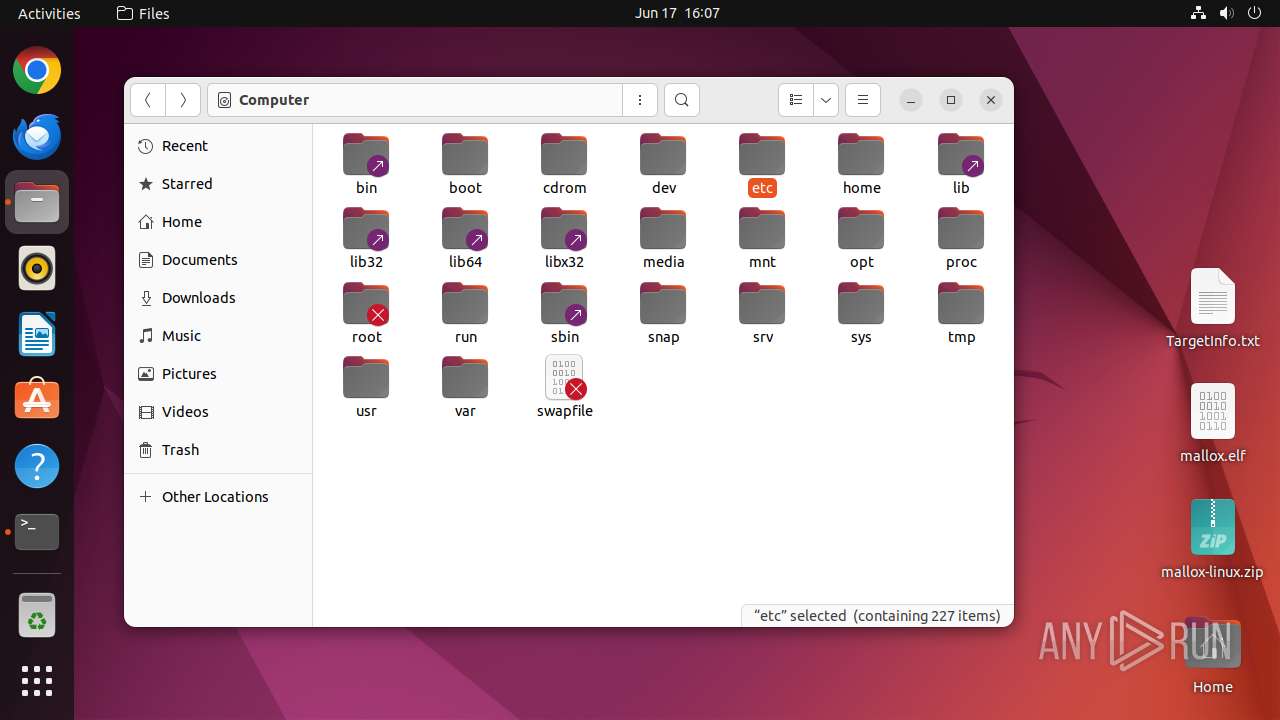
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 12948 | file-roller | /home/user/.local/share/recently-used.xbel | xml | |
MD5:— | SHA256:— | |||
| 13010 | 7z | /home/user/Desktop/8eb32de1ec33ffaf2add6719d3bbc2576bc468086252c12efd8b5dcc5e44699f | binary | |
MD5:— | SHA256:— | |||
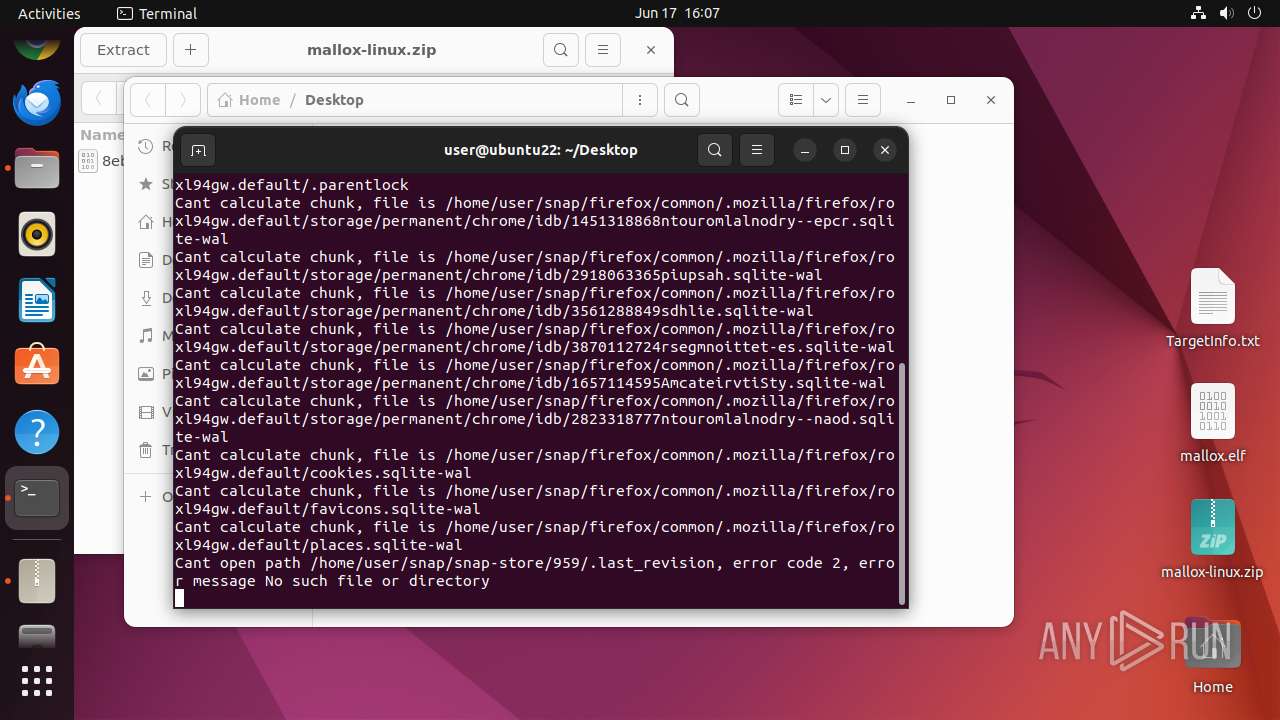
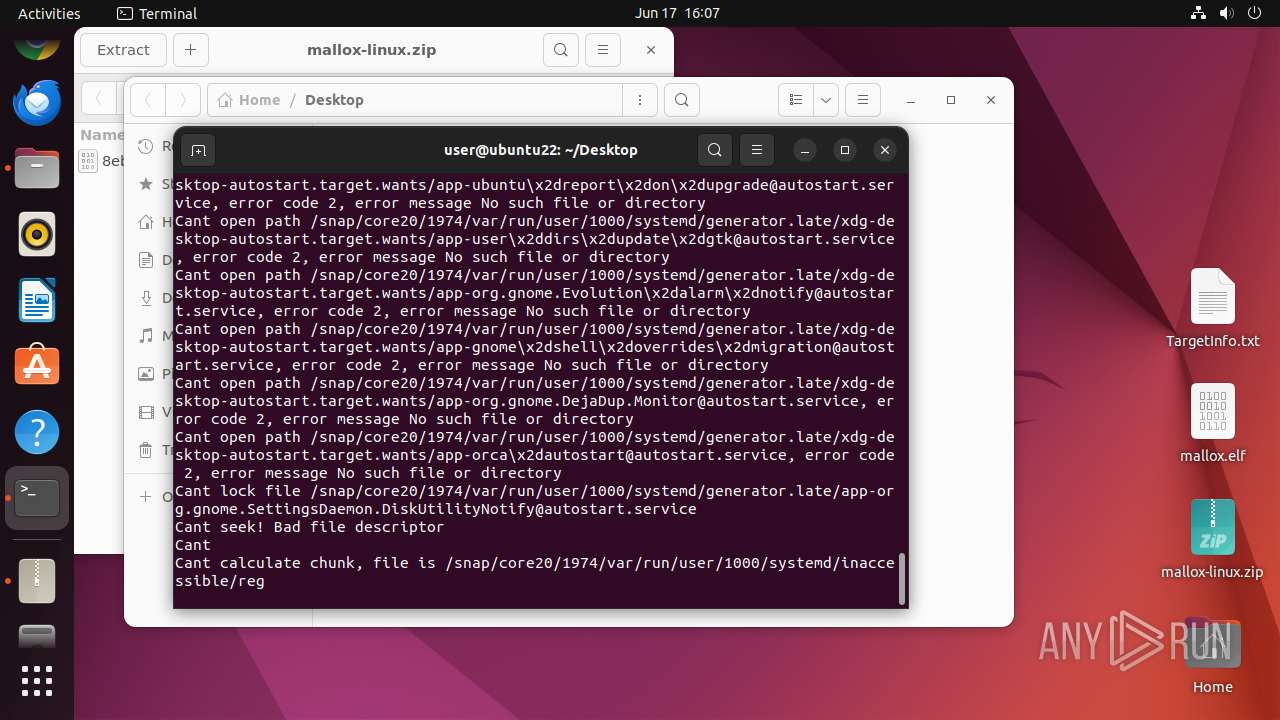
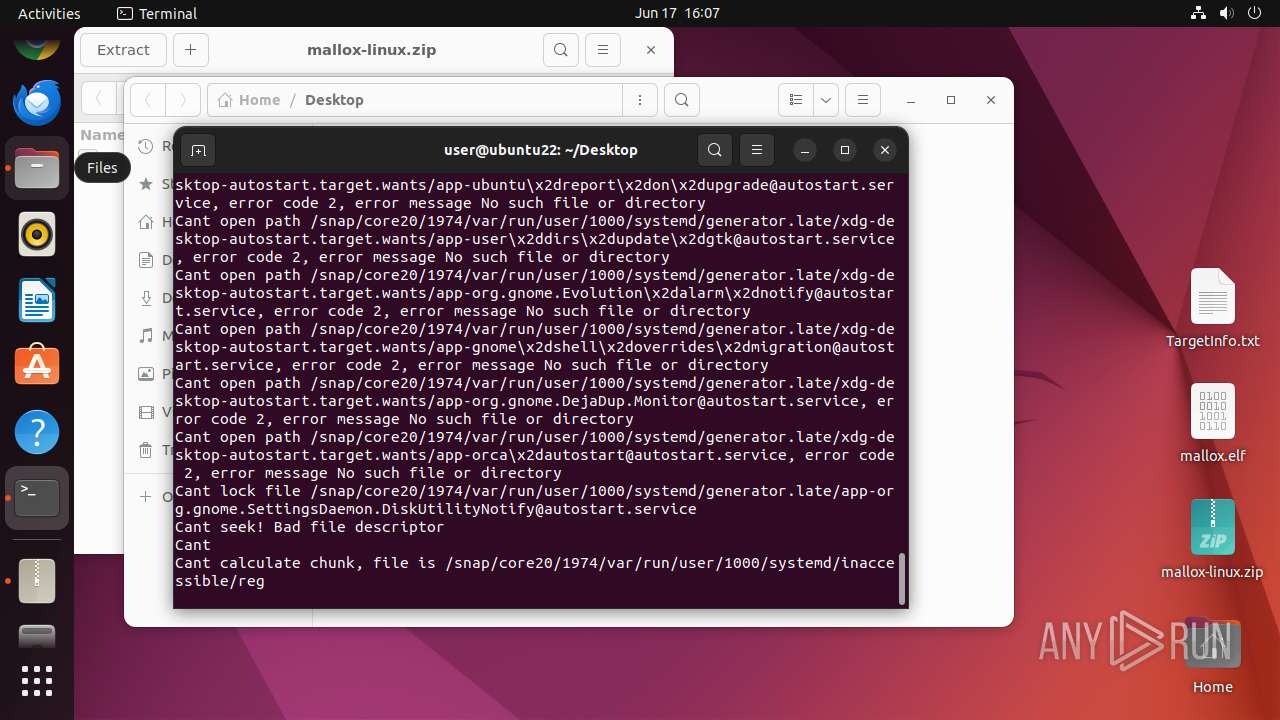
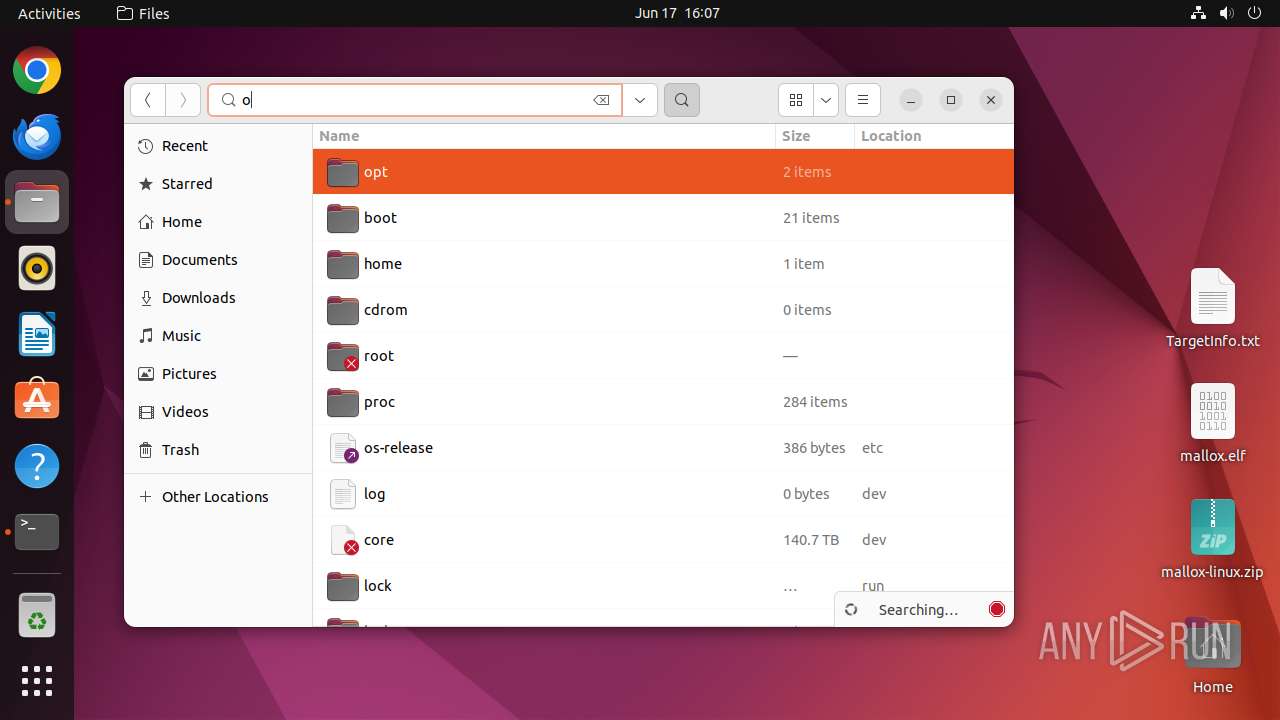
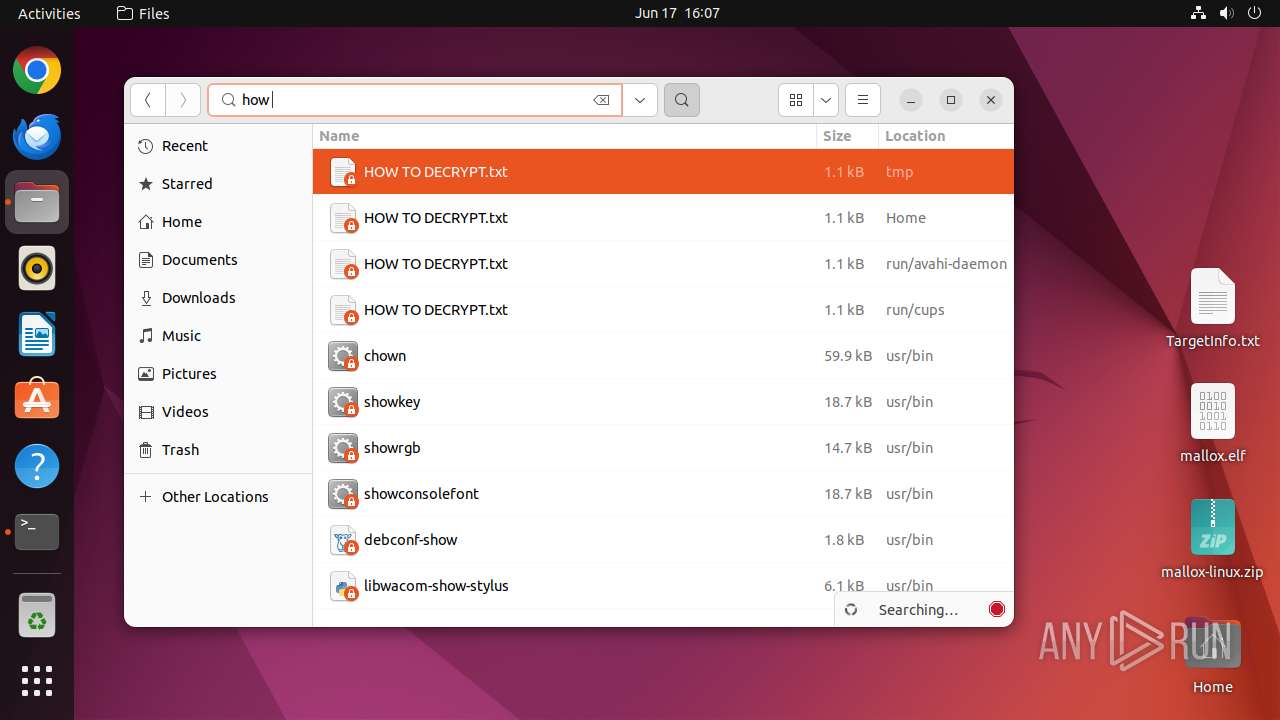
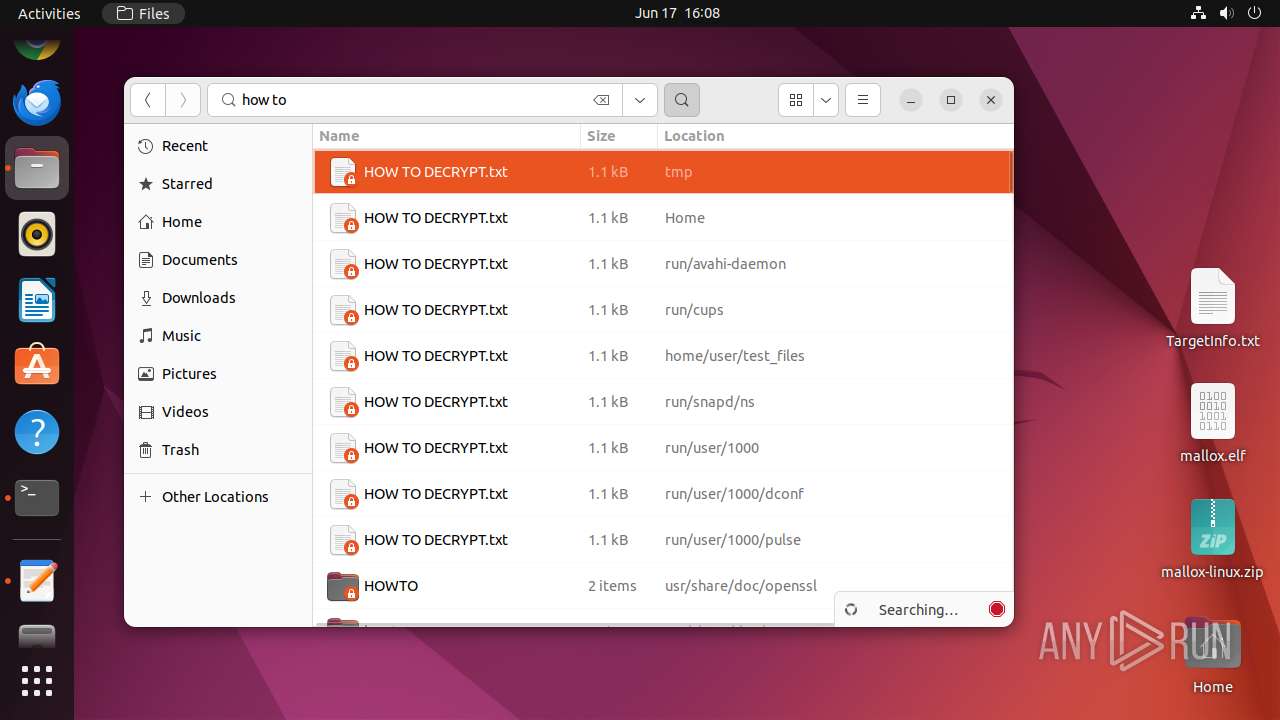
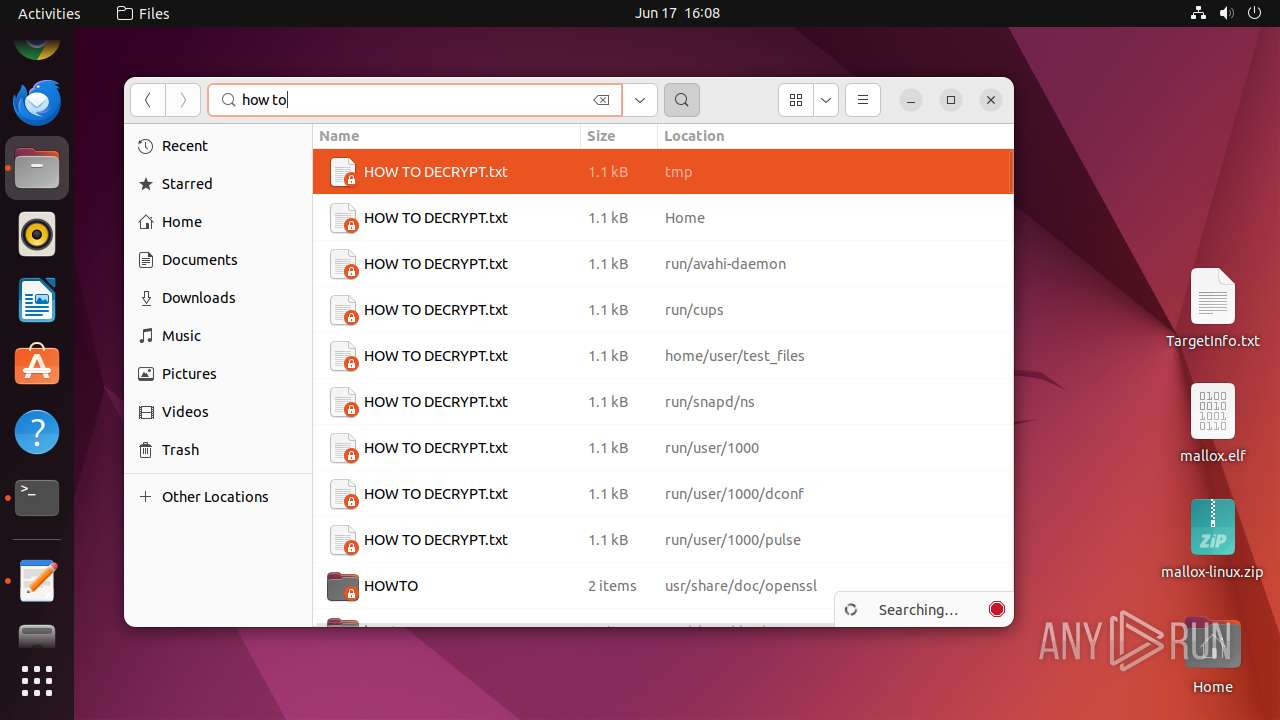
| 13098 | mallox.elf | /home/user/Desktop/TargetInfo.txt | text | |
MD5:— | SHA256:— | |||
| 13098 | mallox.elf | /home/user/test_files/HOW TO DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 13098 | mallox.elf | /home/user/.pki/nssdb/HOW TO DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 13098 | mallox.elf | /home/user/.cache/ubuntu-report/HOW TO DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 13098 | mallox.elf | /home/user/.cache/gnome-desktop-thumbnailer/gstreamer-1.0/HOW TO DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 13098 | mallox.elf | /home/user/.cache/gnome-software/screenshots/624x351/HOW TO DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 13098 | mallox.elf | /home/user/.cache/gnome-software/icons/HOW TO DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 13098 | mallox.elf | /home/user/.cache/gnome-software/odrs/HOW TO DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
18
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 91.189.91.98:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | unknown |
13098 | mallox.elf | GET | 200 | 104.26.12.205:80 | http://api.ipify.org/ | unknown | — | — | unknown |
13098 | mallox.elf | GET | 200 | 104.26.13.205:80 | http://api.ipify.org/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
470 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 91.189.91.98:80 | — | Canonical Group Limited | US | unknown |
— | — | 91.189.91.96:80 | — | Canonical Group Limited | US | unknown |
485 | snapd | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
485 | snapd | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
485 | snapd | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
12988 | gvfsd-smb-browse | 192.168.100.255:137 | — | — | — | whitelisted |
13098 | mallox.elf | 104.26.12.205:80 | api.ipify.org | CLOUDFLARENET | US | unknown |
13098 | mallox.elf | 104.26.13.205:80 | api.ipify.org | CLOUDFLARENET | US | unknown |
— | — | 91.215.85.142:80 | — | — | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.snapcraft.io |
| unknown |
238.100.168.192.in-addr.arpa |
| unknown |
connectivity-check.ubuntu.com |
| unknown |
api.ipify.org |
| shared |
changelogs.ubuntu.com |
| unknown |