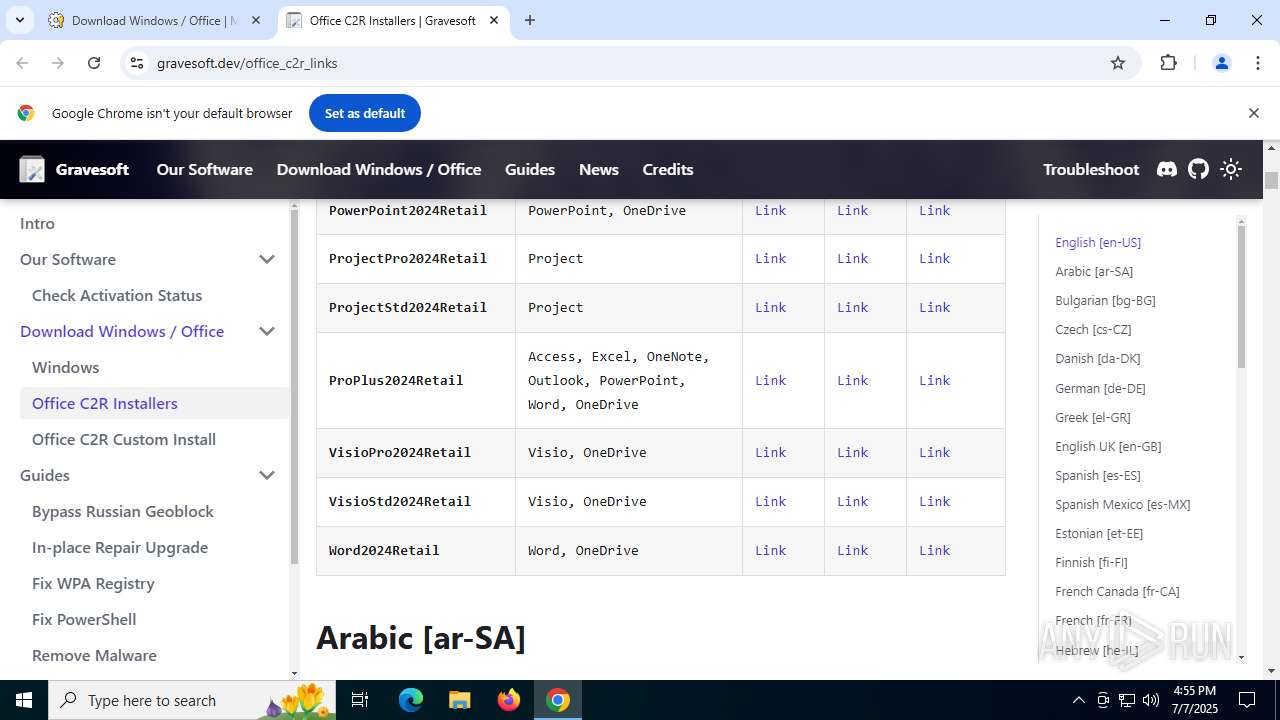
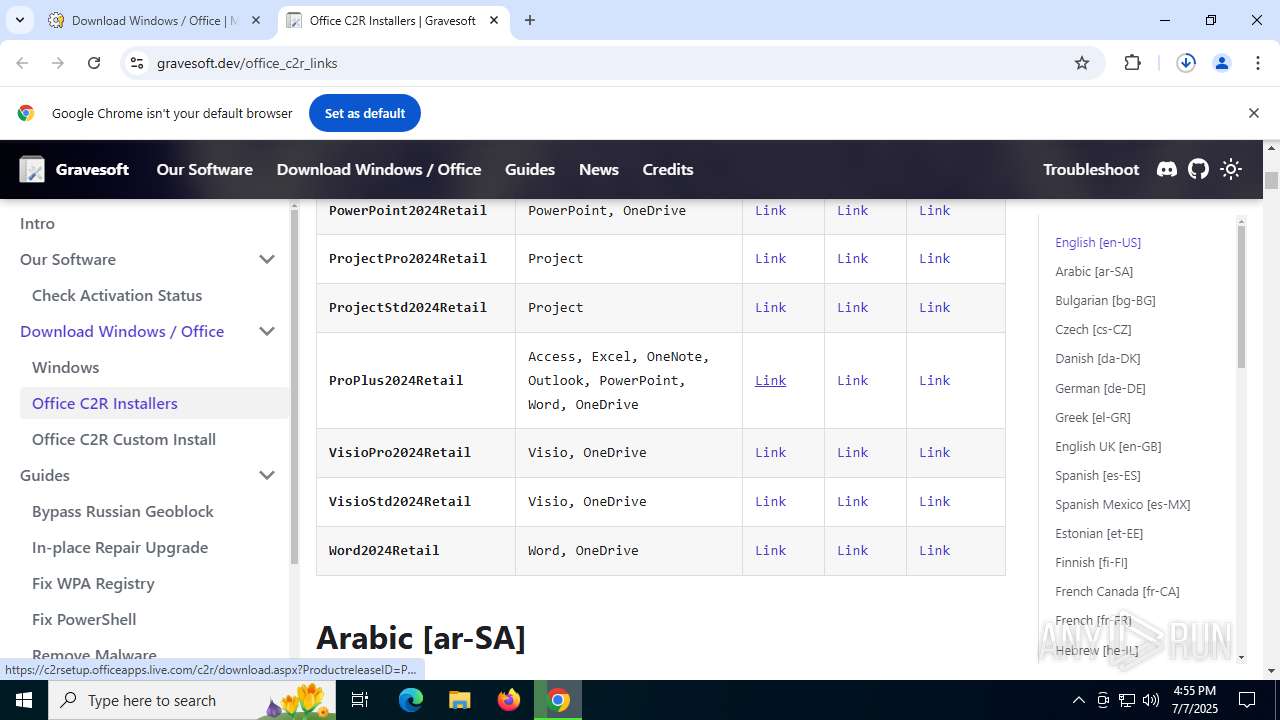
| URL: | https://massgrave.dev/genuine-installation-media |
| Full analysis: | https://app.any.run/tasks/fa4df19f-cc7d-4b1d-81d4-103f97a43d9e |
| Verdict: | Malicious activity |
| Analysis date: | July 07, 2025, 16:54:44 |
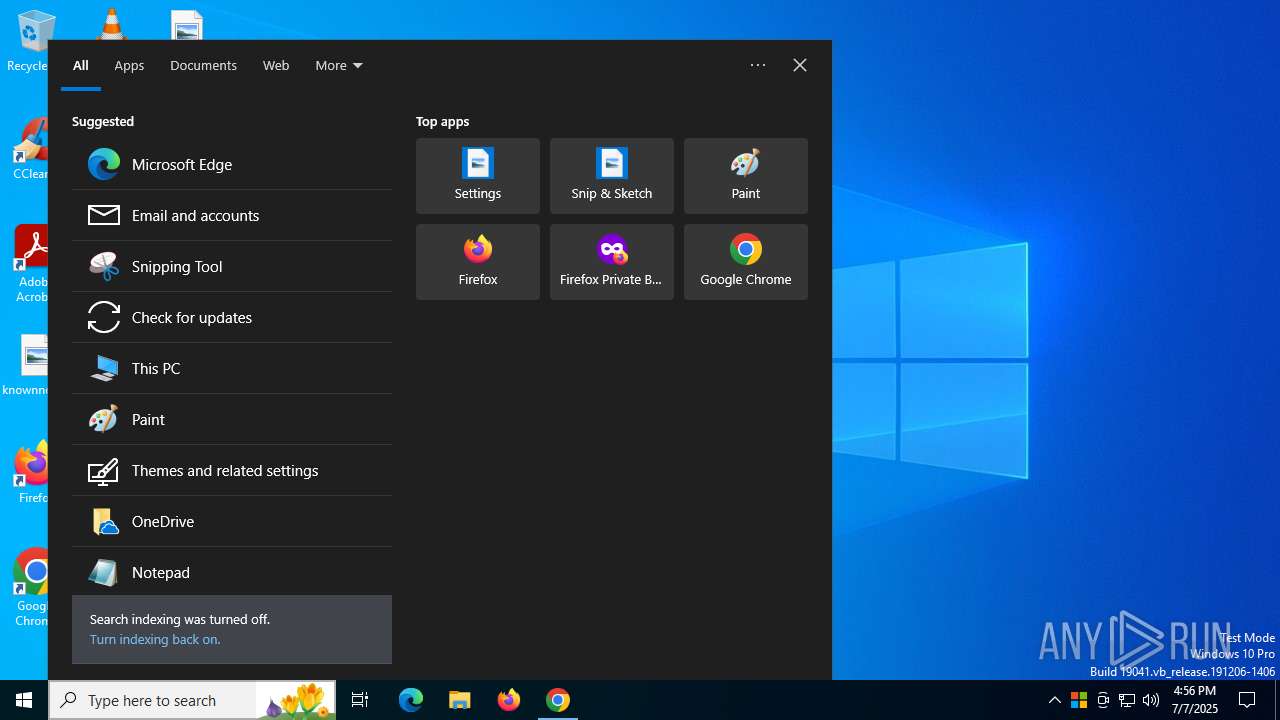
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 57C1962782FCC9E86122CFBA0402FAE4 |
| SHA1: | 18B9A2E3A54301F32705529C5757DD3A83F39714 |
| SHA256: | E9682AA8DCCD905D8056E3268135F08A66328B99B5D7887441FCC4AB131193A3 |
| SSDEEP: | 3:N8a0KAMLtK4RL+6E:2a0KK4RL+v |
MALICIOUS
Scans artifacts that could help determine the target
- OfficeSetup.exe (PID: 4832)
- OfficeSetup.exe (PID: 7116)
- OfficeC2RClient.exe (PID: 3668)
SUSPICIOUS
Application launched itself
- OfficeSetup.exe (PID: 3860)
- OfficeSetup.exe (PID: 7116)
Process drops legitimate windows executable
- chrome.exe (PID: 2848)
- OfficeClickToRun.exe (PID: 6700)
- OfficeClickToRun.exe (PID: 7508)
Reads security settings of Internet Explorer
- OfficeSetup.exe (PID: 7116)
- OfficeSetup.exe (PID: 4832)
- OfficeC2RClient.exe (PID: 3668)
Executable content was dropped or overwritten
- OfficeClickToRun.exe (PID: 6700)
- OfficeClickToRun.exe (PID: 7508)
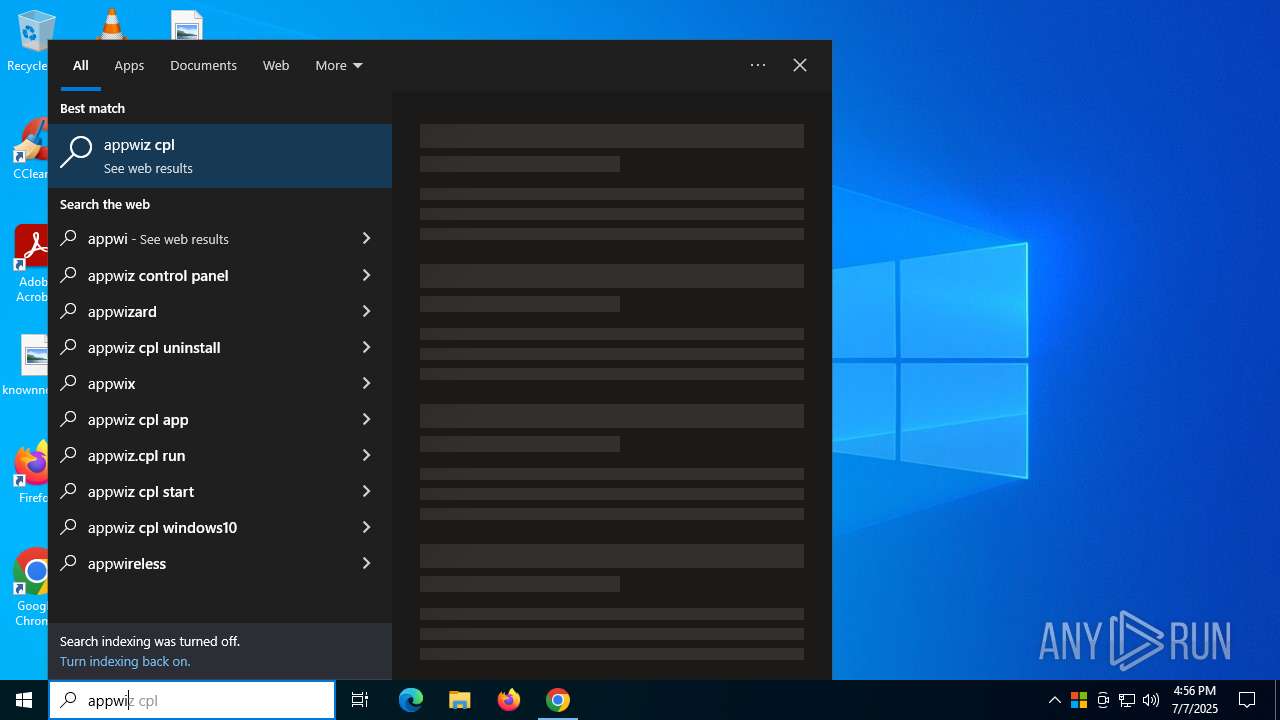
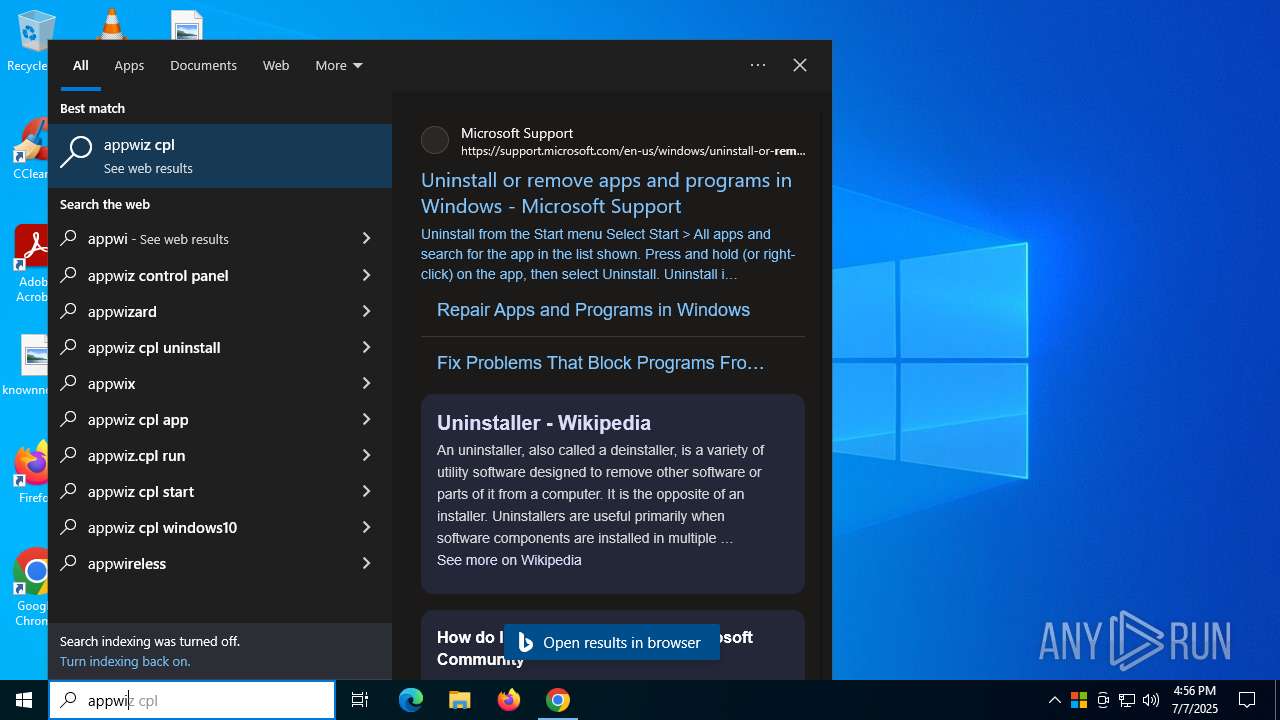
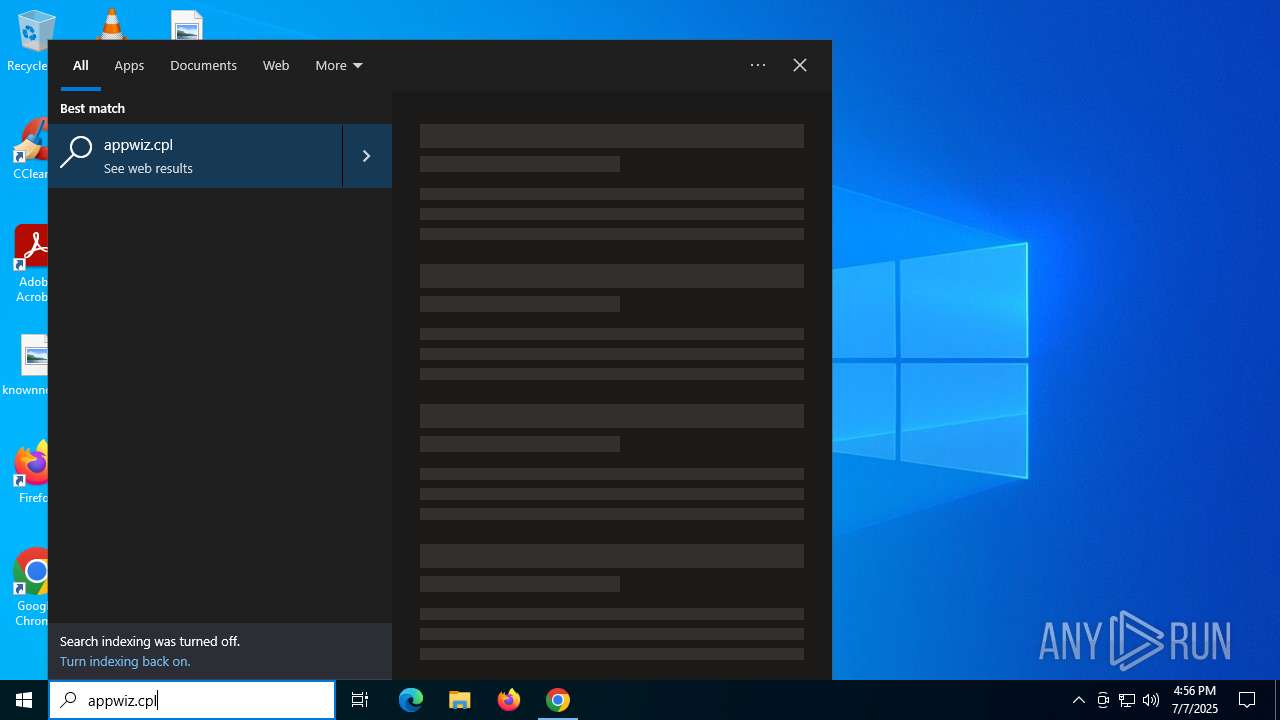
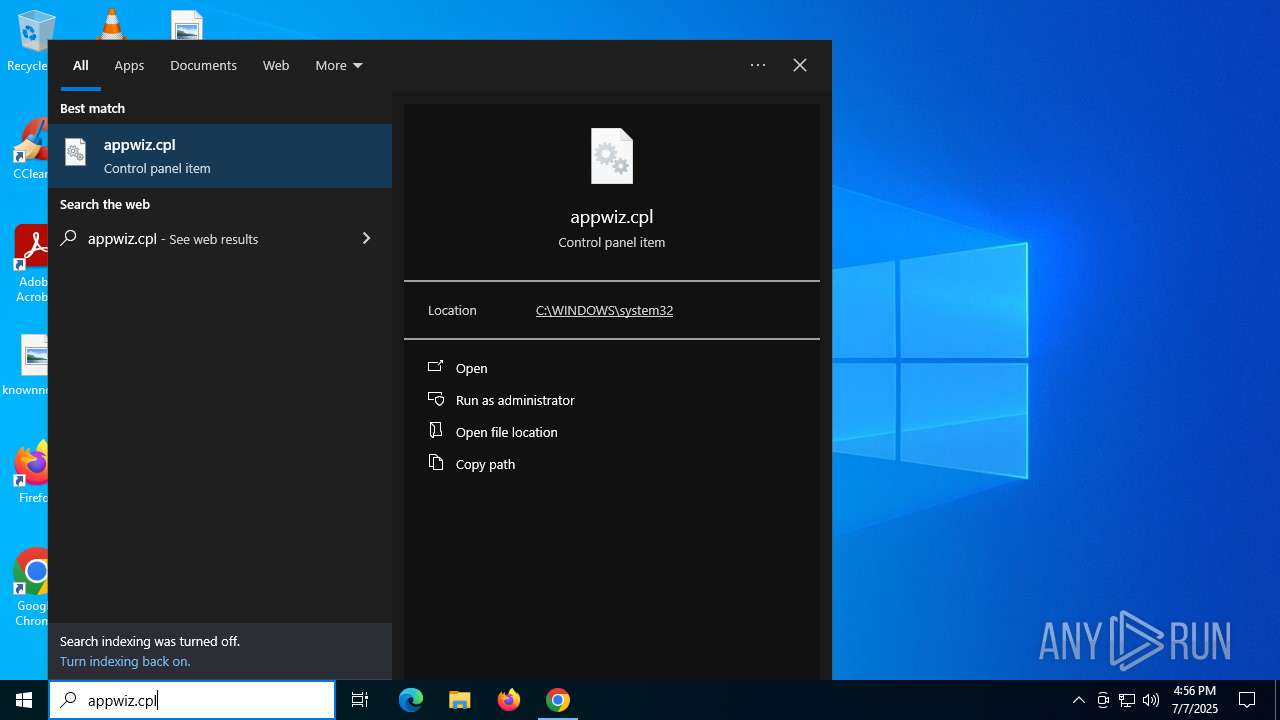
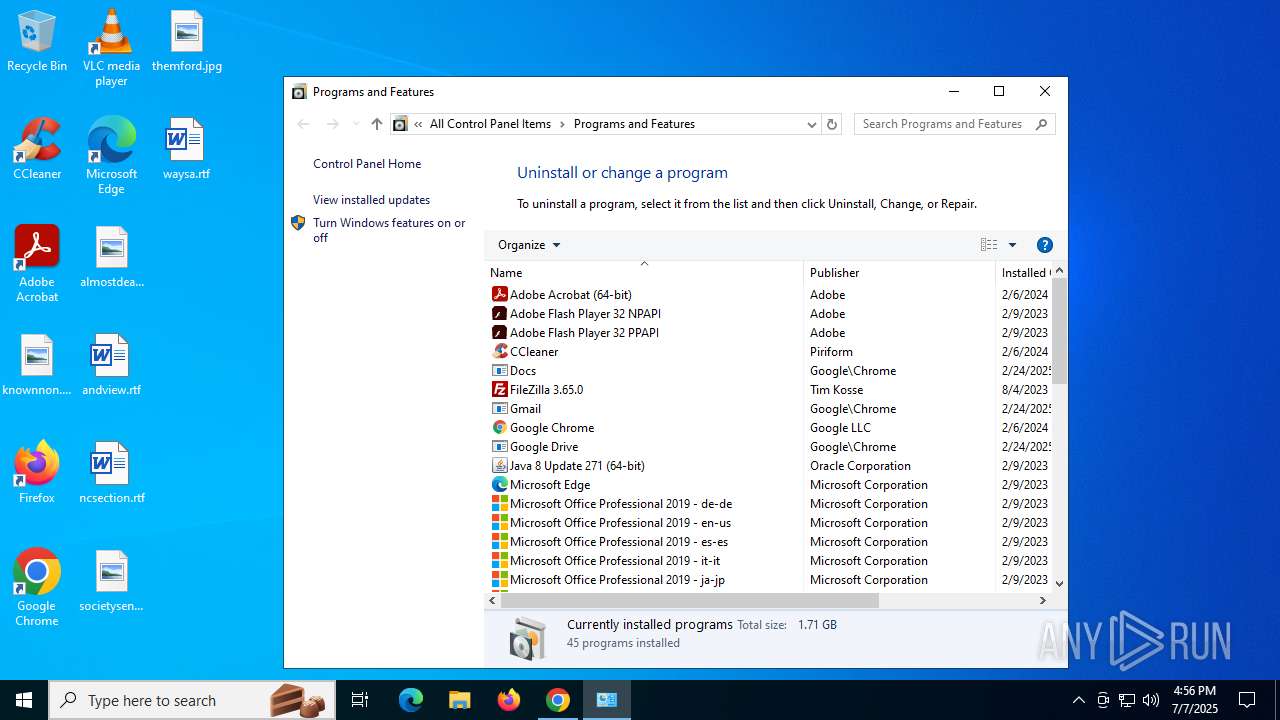
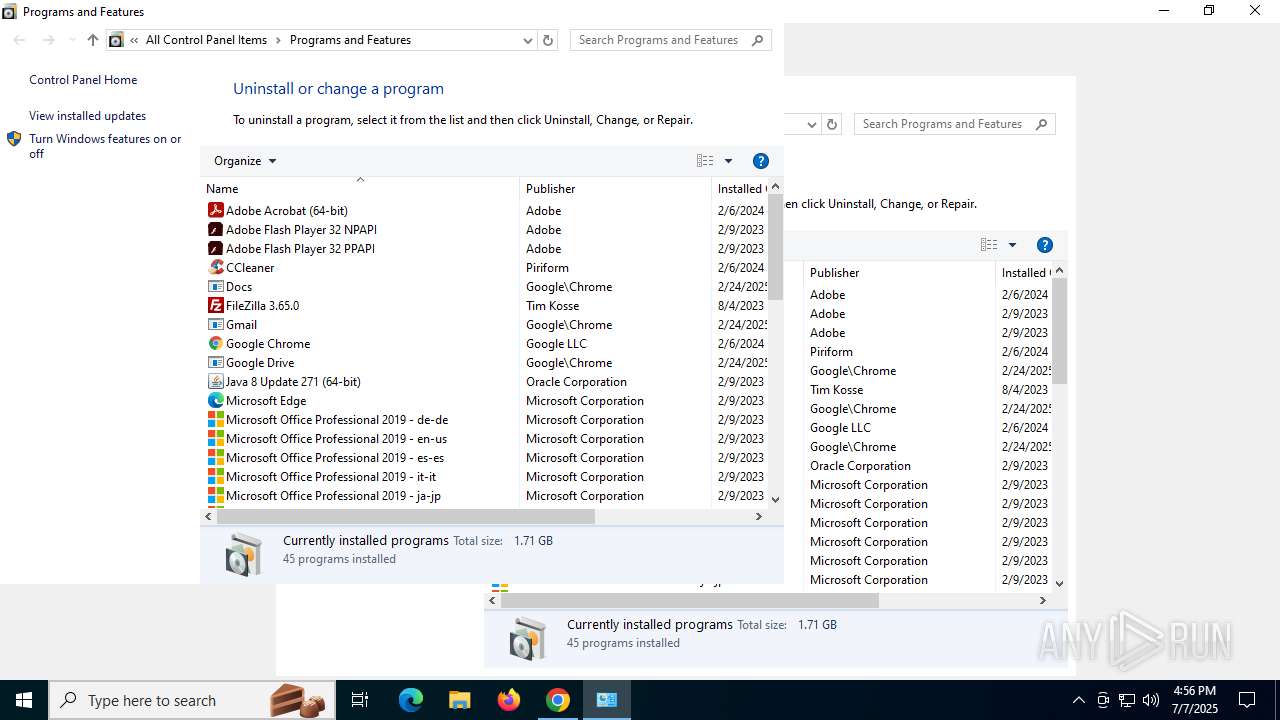
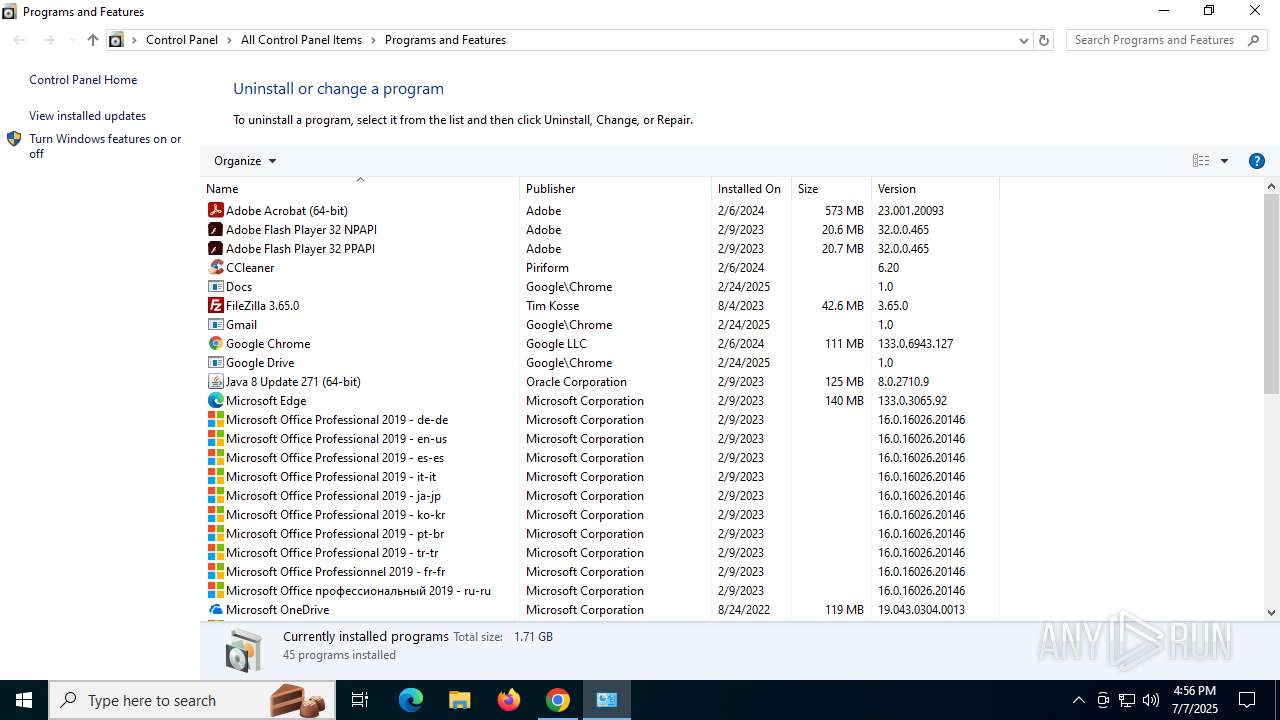
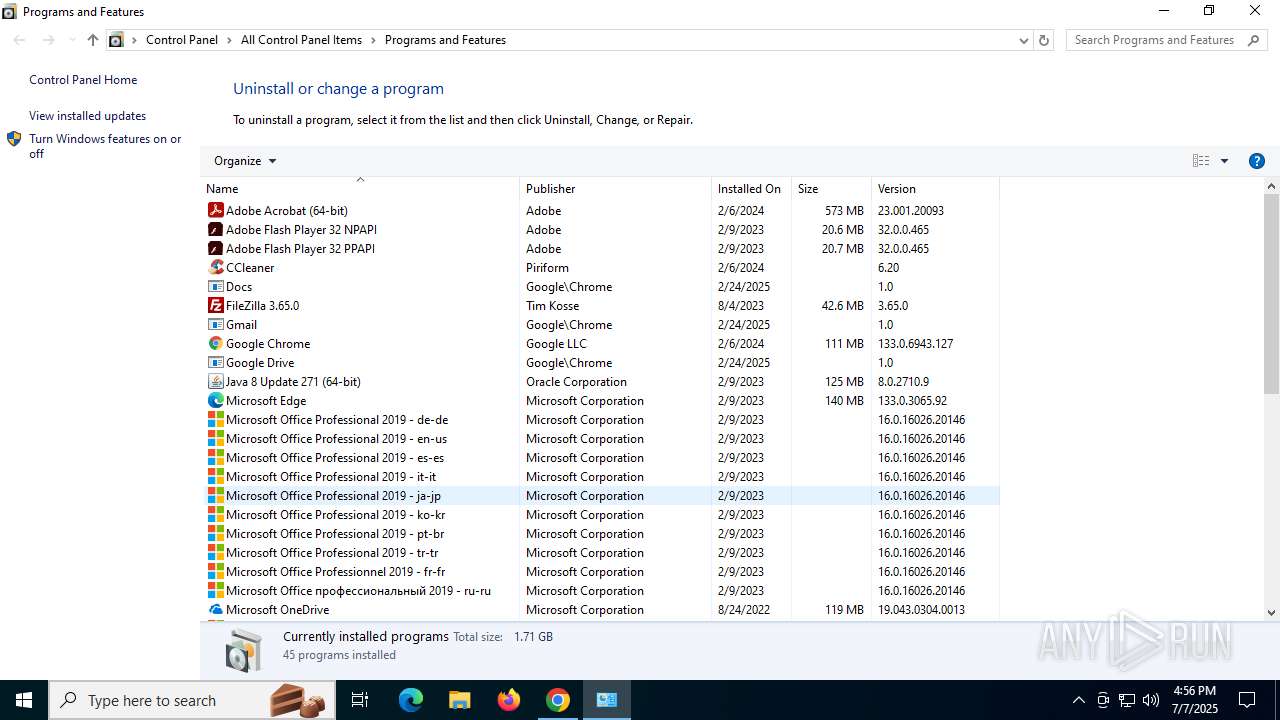
Searches for installed software
- OfficeSetup.exe (PID: 4832)
- explorer.exe (PID: 7660)
The process drops C-runtime libraries
- OfficeClickToRun.exe (PID: 6700)
INFO
Application launched itself
- chrome.exe (PID: 2848)
Executable content was dropped or overwritten
- chrome.exe (PID: 2848)
Reads the machine GUID from the registry
- OfficeSetup.exe (PID: 7116)
- OfficeSetup.exe (PID: 4832)
- OfficeClickToRun.exe (PID: 6700)
- OfficeClickToRun.exe (PID: 7508)
- OfficeClickToRun.exe (PID: 7676)
Reads Microsoft Office registry keys
- OfficeSetup.exe (PID: 7116)
- OfficeSetup.exe (PID: 4832)
- OfficeClickToRun.exe (PID: 6700)
- OfficeClickToRun.exe (PID: 7508)
- OfficeClickToRun.exe (PID: 7676)
- OfficeC2RClient.exe (PID: 3668)
Checks supported languages
- OfficeSetup.exe (PID: 7116)
- OfficeSetup.exe (PID: 3860)
- OfficeSetup.exe (PID: 4832)
- OfficeClickToRun.exe (PID: 6700)
- OfficeClickToRun.exe (PID: 7508)
- OfficeClickToRun.exe (PID: 7676)
- OfficeC2RClient.exe (PID: 3668)
Process checks whether UAC notifications are on
- OfficeSetup.exe (PID: 7116)
Process checks computer location settings
- OfficeSetup.exe (PID: 7116)
- OfficeSetup.exe (PID: 4832)
- OfficeC2RClient.exe (PID: 3668)
Checks proxy server information
- OfficeSetup.exe (PID: 7116)
- OfficeClickToRun.exe (PID: 6700)
- OfficeSetup.exe (PID: 4832)
- OfficeClickToRun.exe (PID: 7508)
- OfficeClickToRun.exe (PID: 7676)
- slui.exe (PID: 7288)
- OfficeC2RClient.exe (PID: 3668)
Reads the computer name
- OfficeSetup.exe (PID: 7116)
- OfficeSetup.exe (PID: 4832)
- OfficeClickToRun.exe (PID: 6700)
- OfficeClickToRun.exe (PID: 7508)
- OfficeClickToRun.exe (PID: 7676)
- OfficeC2RClient.exe (PID: 3668)
Reads the software policy settings
- OfficeSetup.exe (PID: 7116)
- OfficeSetup.exe (PID: 4832)
- OfficeClickToRun.exe (PID: 6700)
- OfficeClickToRun.exe (PID: 7508)
- OfficeClickToRun.exe (PID: 7676)
- slui.exe (PID: 7288)
Creates files or folders in the user directory
- OfficeSetup.exe (PID: 7116)
- OfficeSetup.exe (PID: 4832)
- OfficeClickToRun.exe (PID: 6700)
- OfficeClickToRun.exe (PID: 7676)
- OfficeC2RClient.exe (PID: 3668)
Reads CPU info
- OfficeSetup.exe (PID: 7116)
- OfficeSetup.exe (PID: 4832)
Reads Environment values
- OfficeSetup.exe (PID: 4832)
- OfficeSetup.exe (PID: 7116)
- OfficeC2RClient.exe (PID: 3668)
Create files in a temporary directory
- OfficeSetup.exe (PID: 4832)
- OfficeSetup.exe (PID: 7116)
- OfficeClickToRun.exe (PID: 6700)
- OfficeClickToRun.exe (PID: 7676)
- OfficeC2RClient.exe (PID: 3668)
The sample compiled with Italian language support
- OfficeClickToRun.exe (PID: 6700)
The sample compiled with english language support
- OfficeClickToRun.exe (PID: 6700)
The sample compiled with arabic language support
- OfficeClickToRun.exe (PID: 6700)
Creates files in the program directory
- OfficeClickToRun.exe (PID: 6700)
- OfficeClickToRun.exe (PID: 7508)
The sample compiled with french language support
- OfficeClickToRun.exe (PID: 6700)
The sample compiled with bulgarian language support
- OfficeClickToRun.exe (PID: 6700)
The sample compiled with german language support
- OfficeClickToRun.exe (PID: 6700)
The sample compiled with czech language support
- OfficeClickToRun.exe (PID: 6700)
The sample compiled with spanish language support
- OfficeClickToRun.exe (PID: 6700)
The sample compiled with Indonesian language support
- OfficeClickToRun.exe (PID: 6700)
The sample compiled with japanese language support
- OfficeClickToRun.exe (PID: 6700)
The sample compiled with polish language support
- OfficeClickToRun.exe (PID: 6700)
The sample compiled with portuguese language support
- OfficeClickToRun.exe (PID: 6700)
The sample compiled with slovak language support
- OfficeClickToRun.exe (PID: 6700)
The sample compiled with russian language support
- OfficeClickToRun.exe (PID: 6700)
The sample compiled with turkish language support
- OfficeClickToRun.exe (PID: 6700)
The sample compiled with swedish language support
- OfficeClickToRun.exe (PID: 6700)
The sample compiled with chinese language support
- OfficeClickToRun.exe (PID: 6700)
Executes as Windows Service
- OfficeClickToRun.exe (PID: 7508)
The sample compiled with korean language support
- OfficeClickToRun.exe (PID: 6700)
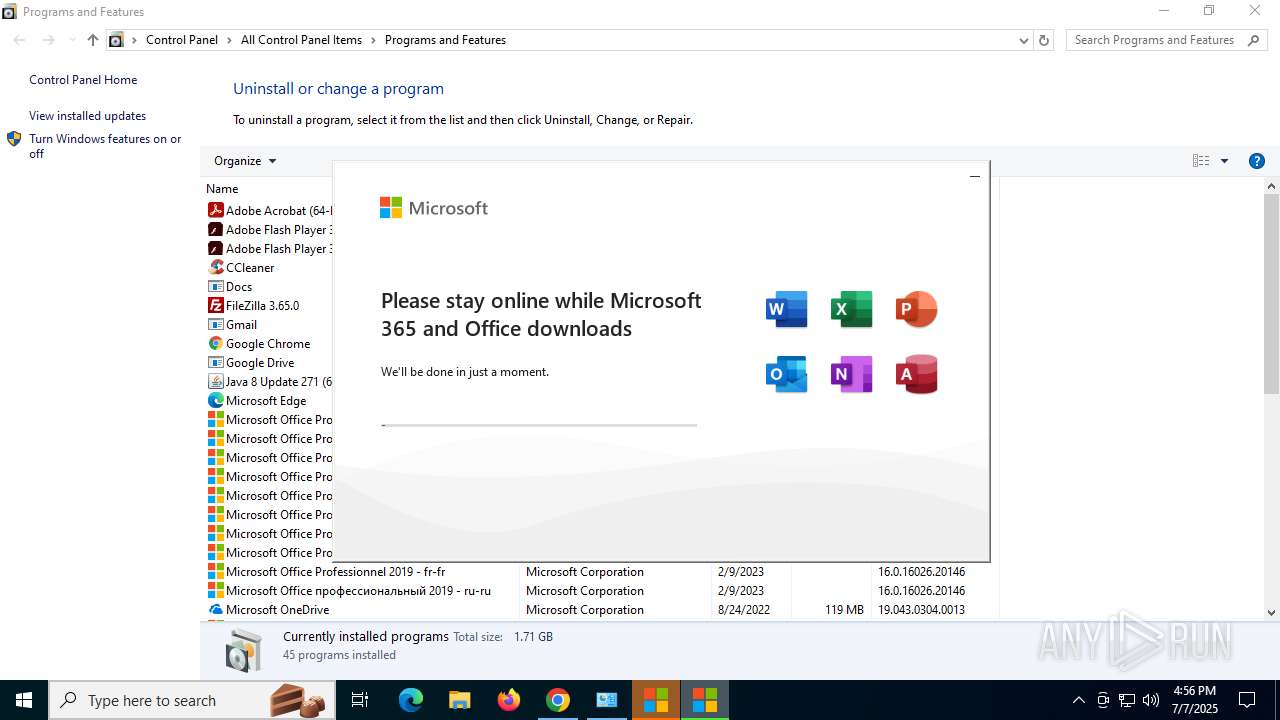
Manual execution by a user
- OfficeC2RClient.exe (PID: 3668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
188
Monitored processes
36
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=6480,i,7159950851712394021,8127213774245742804,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=6308 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1760 | C:\WINDOWS\system32\DllHost.exe /Processid:{338B40F9-9D68-4B53-A793-6B9AA0C5F63B} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=6028,i,7159950851712394021,8127213774245742804,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=500 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --field-trial-handle=1776,i,7159950851712394021,8127213774245742804,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3096 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=4576,i,7159950851712394021,8127213774245742804,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3792 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --field-trial-handle=3052,i,7159950851712394021,8127213774245742804,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2892 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://massgrave.dev/genuine-installation-media" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=5176,i,7159950851712394021,8127213774245742804,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4336 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 3668 | "C:\Program Files\Common Files\Microsoft Shared\ClickToRun\OfficeC2RClient.exe" /progressandlaunch AppTargets="root\office16\excel.exe|root\office16\msaccess.exe|root\office16\onenote.exe|root\office16\outlook.exe|root\office16\powerpnt.exe|root\office16\winword.exe" ManualUpgrade=False ScenarioToTrack="Scenario:{477E0208-58BD-4F33-978A-09BCC9AA9EB1}@INSTALL" | C:\Program Files\Common Files\microsoft shared\ClickToRun\OfficeC2RClient.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office Click-to-Run Client Version: 16.0.18925.20138 Modules
| |||||||||||||||
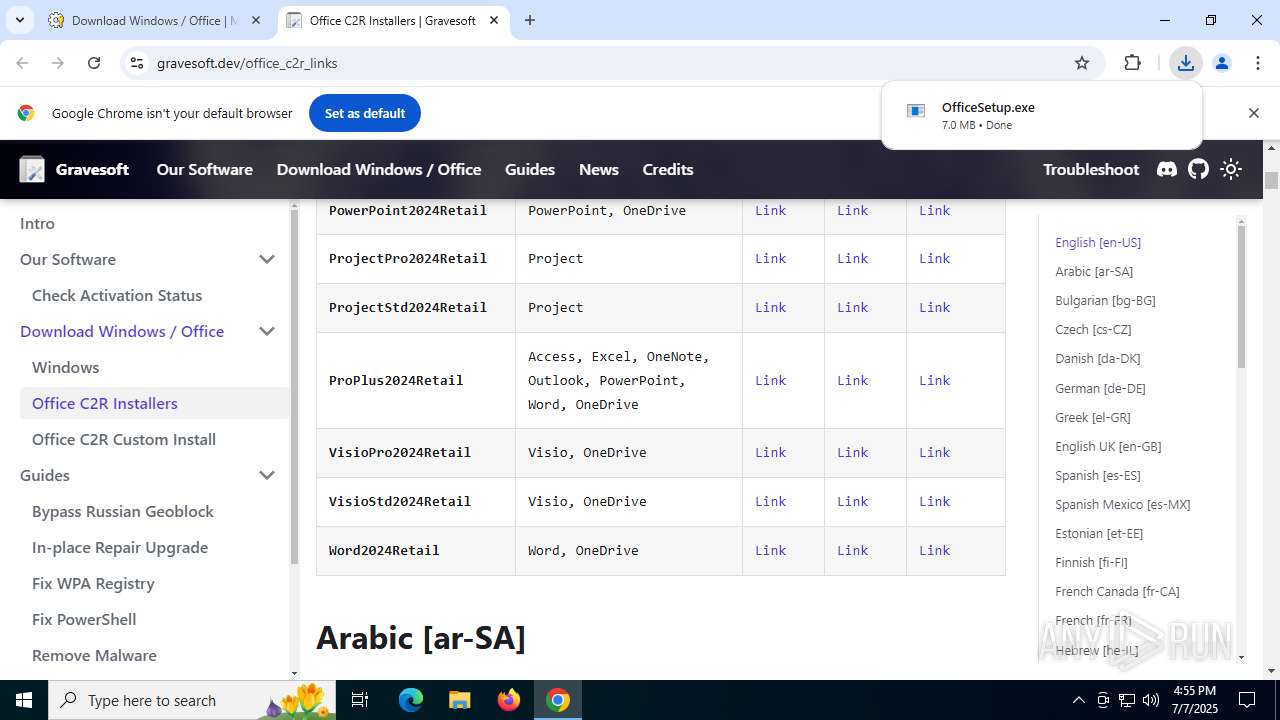
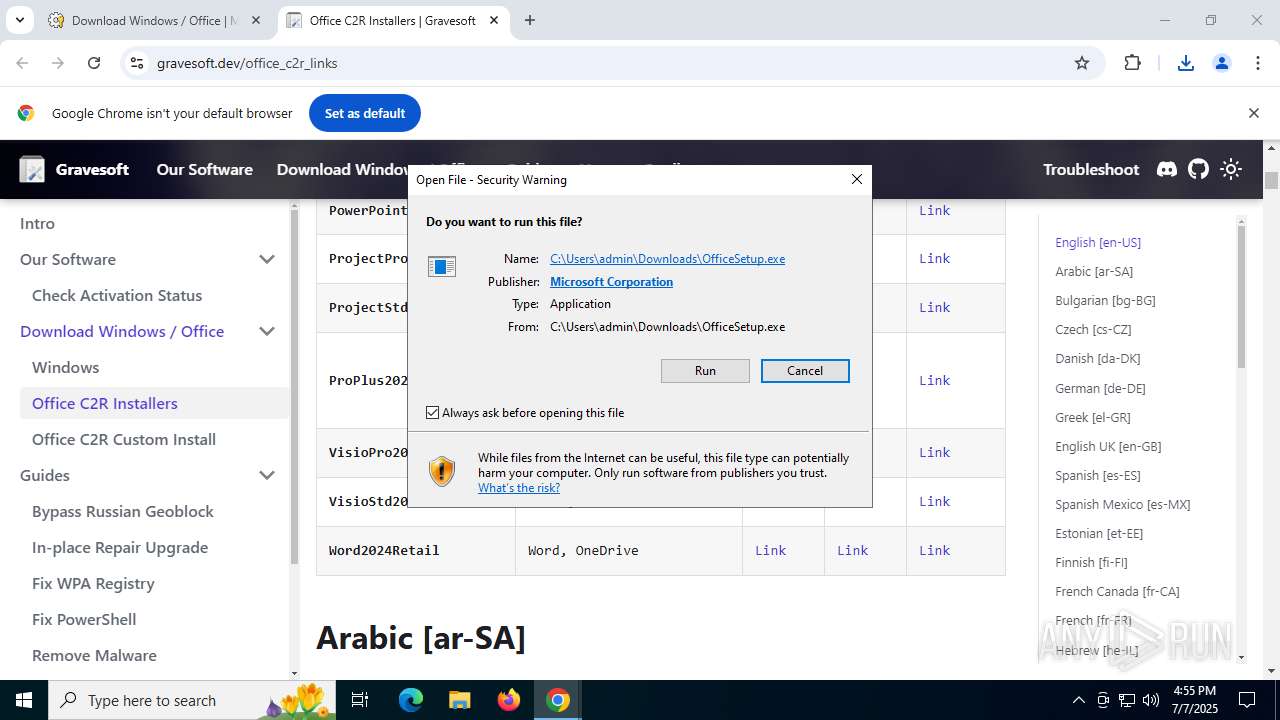
| 3860 | "C:\Users\admin\Downloads\OfficeSetup.exe" | C:\Users\admin\Downloads\OfficeSetup.exe | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft 365 and Office Version: 16.0.18925.20138 Modules
| |||||||||||||||
Total events
94 541
Read events
93 946
Write events
365
Delete events
230
Modification events
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (4832) OfficeSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (4832) OfficeSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 1 | |||
| (PID) Process: | (7116) OfficeSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\Internet\WebServiceCache\AllUsers\officeclient.microsoft.com\config16--syslcid=1033&build=16.0.18925&crev=3 |
| Operation: | write | Name: | Last |
Value: 0 | |||
| (PID) Process: | (7116) OfficeSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\Internet\WebServiceCache\AllUsers\officeclient.microsoft.com\config16--syslcid=1033&build=16.0.18925&crev=3\0 |
| Operation: | write | Name: | FilePath |
Value: officeclient.microsoft.com\277A7375-55E7-46D5-B5CE-3713EDBA28AA | |||
| (PID) Process: | (7116) OfficeSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\Internet\WebServiceCache\AllUsers\officeclient.microsoft.com\config16--syslcid=1033&build=16.0.18925&crev=3\0 |
| Operation: | write | Name: | StartDate |
Value: 707C09F65FEFDB01 | |||
Executable files
413
Suspicious files
430
Text files
619
Unknown types
79
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF1757f3.TMP | — | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF175813.TMP | — | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF175822.TMP | — | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF175832.TMP | — | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF175832.TMP | — | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF175832.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
256
TCP/UDP connections
277
DNS requests
198
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
3948 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
4832 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 420 b | whitelisted |
2848 | chrome.exe | GET | 200 | 23.48.23.166:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | DE | binary | 824 b | whitelisted |
4832 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
2848 | chrome.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Windows%20Code%20Signing%20PCA%202024.crl | DE | binary | 781 b | whitelisted |
4832 | OfficeSetup.exe | HEAD | 200 | 199.232.214.172:80 | http://f.c2r.ts.cdn.office.net/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v64_16.0.18925.20138.cab | US | — | — | whitelisted |
4832 | OfficeSetup.exe | HEAD | 200 | 199.232.214.172:80 | http://f.c2r.ts.cdn.office.net/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v64_16.0.16026.20146.cab | US | — | — | whitelisted |
4832 | OfficeSetup.exe | HEAD | 200 | 199.232.214.172:80 | http://f.c2r.ts.cdn.office.net/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v64_16.0.18925.20138.cab | US | — | — | whitelisted |
6224 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://f.c2r.ts.cdn.office.net/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v64_16.0.18925.20138.cab | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6128 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5876 | chrome.exe | 216.58.212.138:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
5876 | chrome.exe | 104.21.22.3:443 | massgrave.dev | CLOUDFLARENET | — | unknown |
5876 | chrome.exe | 142.250.186.78:80 | clients2.google.com | GOOGLE | US | whitelisted |
5876 | chrome.exe | 64.233.166.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
5876 | chrome.exe | 104.16.80.73:443 | static.cloudflareinsights.com | CLOUDFLARENET | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
massgrave.dev |
| unknown |
accounts.google.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
cloudflareinsights.com |
| whitelisted |
a.nel.cloudflare.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5876 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
5876 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
— | — | Potentially Bad Traffic | ET ATTACK_RESPONSE PowerShell NoProfile Command Received In Powershell Stagers |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
— | — | Misc activity | ET INFO EXE - Served Attached HTTP |