| File name: | 2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar |
| Full analysis: | https://app.any.run/tasks/1c4d6958-2cbd-4e76-8131-893990610efe |
| Verdict: | Malicious activity |
| Analysis date: | July 06, 2025, 01:20:37 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 6 sections |
| MD5: | 81B9D58D6D5D085BA840F3ADA667C105 |
| SHA1: | 5C3D7B216496F25A60C44C3D6669D7895E74AE3C |
| SHA256: | E9652B40127AB420CA6E68C69D9C09A9E108B542964F715B8F6EBFEBFB2FD2C2 |
| SSDEEP: | 98304:Kcd2o1kcaCJr/VzkvddwCXkFqdz3aC3bww/Al+Biyz6oqV2kMmLYvI9yf+8Gm1MS:YwaTb2OaZ2CTyY/Gtx++oMaB7qE3DVt |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- 2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar.exe (PID: 768)
Application launched itself
- 2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar.exe (PID: 768)
Process drops legitimate windows executable
- 2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar.exe (PID: 768)
Process drops python dynamic module
- 2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar.exe (PID: 768)
The process drops C-runtime libraries
- 2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar.exe (PID: 768)
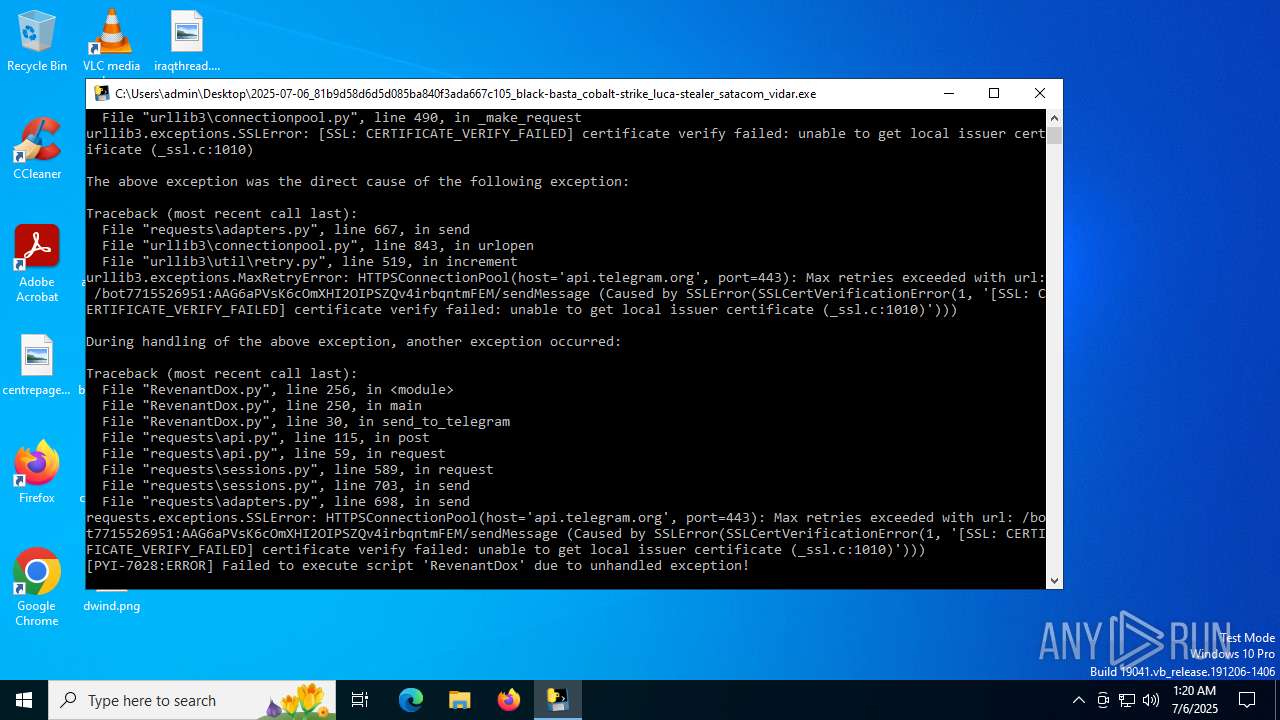
Loads Python modules
- 2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar.exe (PID: 7028)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- 2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar.exe (PID: 7028)
INFO
Checks supported languages
- 2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar.exe (PID: 768)
- 2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar.exe (PID: 7028)
Reads the computer name
- 2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar.exe (PID: 768)
The sample compiled with english language support
- 2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar.exe (PID: 768)
Create files in a temporary directory
- 2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar.exe (PID: 768)
Checks proxy server information
- 2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar.exe (PID: 7028)
- slui.exe (PID: 7100)
Reads the software policy settings
- slui.exe (PID: 7100)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:03:05 22:53:26+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.41 |
| CodeSize: | 176640 |
| InitializedDataSize: | 152576 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc380 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
134
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 768 | "C:\Users\admin\Desktop\2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar.exe" | C:\Users\admin\Desktop\2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 1100 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7028 | "C:\Users\admin\Desktop\2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar.exe" | C:\Users\admin\Desktop\2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar.exe | 2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 7100 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 934
Read events
3 934
Write events
0
Delete events
0
Modification events
Executable files
113
Suspicious files
1
Text files
21
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 768 | 2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar.exe | C:\Users\admin\AppData\Local\Temp\_MEI7682\Crypto\Cipher\_raw_ofb.pyd | executable | |
MD5:4D9182783EF19411EBD9F1F864A2EF2F | SHA256:C9F4C5FFCDD4F8814F8C07CE532A164AB699AE8CDE737DF02D6ECD7B5DD52DBD | |||
| 768 | 2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar.exe | C:\Users\admin\AppData\Local\Temp\_MEI7682\Crypto\Cipher\_raw_aesni.pyd | executable | |
MD5:BBEA5FFAE18BF0B5679D5C5BCD762D5A | SHA256:1F4288A098DA3AAC2ADD54E83C8C9F2041EC895263F20576417A92E1E5B421C1 | |||
| 768 | 2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar.exe | C:\Users\admin\AppData\Local\Temp\_MEI7682\Crypto\Cipher\_Salsa20.pyd | executable | |
MD5:371776A7E26BAEB3F75C93A8364C9AE0 | SHA256:15257E96D1CA8480B8CB98F4C79B6E365FE38A1BA9638FC8C9AB7FFEA79C4762 | |||
| 768 | 2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar.exe | C:\Users\admin\AppData\Local\Temp\_MEI7682\Crypto\Cipher\_ARC4.pyd | executable | |
MD5:6176101B7C377A32C01AE3EDB7FD4DE6 | SHA256:EFEA361311923189ECBE3240111EFBA329752D30457E0DBE9628A82905CD4BDB | |||
| 768 | 2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar.exe | C:\Users\admin\AppData\Local\Temp\_MEI7682\Crypto\Cipher\_raw_arc2.pyd | executable | |
MD5:D2175300E065347D13211F5BF7581602 | SHA256:94556934E3F9EE73C77552D2F3FC369C02D62A4C9E7143E472F8E3EE8C00AEE1 | |||
| 768 | 2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar.exe | C:\Users\admin\AppData\Local\Temp\_MEI7682\Crypto\Cipher\_raw_aes.pyd | executable | |
MD5:F751792DF10CDEED391D361E82DAF596 | SHA256:9524D1DADCD2F2B0190C1B8EDE8E5199706F3D6C19D3FB005809ED4FEBF3E8B5 | |||
| 768 | 2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar.exe | C:\Users\admin\AppData\Local\Temp\_MEI7682\Crypto\Hash\_BLAKE2s.pyd | executable | |
MD5:9D28433EA8FFBFE0C2870FEDA025F519 | SHA256:FC296145AE46A11C472F99C5BE317E77C840C2430FBB955CE3F913408A046284 | |||
| 768 | 2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar.exe | C:\Users\admin\AppData\Local\Temp\_MEI7682\Crypto\Cipher\_chacha20.pyd | executable | |
MD5:CB5238E2D4149636377F9A1E2AF6DC57 | SHA256:A8D3BB9CD6A78EBDB4F18693E68B659080D08CB537F9630D279EC9F26772EFC7 | |||
| 768 | 2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar.exe | C:\Users\admin\AppData\Local\Temp\_MEI7682\Crypto\Cipher\_pkcs1_decode.pyd | executable | |
MD5:D9E7218460AEE693BEA07DA7C2B40177 | SHA256:38E423D3BCC32EE6730941B19B7D5D8872C0D30D3DD8F9AAE1442CB052C599AD | |||
| 768 | 2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar.exe | C:\Users\admin\AppData\Local\Temp\_MEI7682\Crypto\Cipher\_raw_cbc.pyd | executable | |
MD5:20708935FDD89B3EDDEEA27D4D0EA52A | SHA256:11DD1B49F70DB23617E84E08E709D4A9C86759D911A24EBDDFB91C414CC7F375 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
49
DNS requests
17
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
1268 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
— | — | POST | 200 | 20.190.159.73:443 | https://login.live.com/RST2.srf | US | xml | 1.24 Kb | whitelisted |
— | — | POST | 400 | 20.190.159.130:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | whitelisted |
— | — | POST | 400 | 20.190.159.73:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | whitelisted |
— | — | POST | 200 | 20.190.159.131:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 16.7 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
api.telegram.org |
| whitelisted |
client.wns.windows.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
7028 | 2025-07-06_81b9d58d6d5d085ba840f3ada667c105_black-basta_cobalt-strike_luca-stealer_satacom_vidar.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |