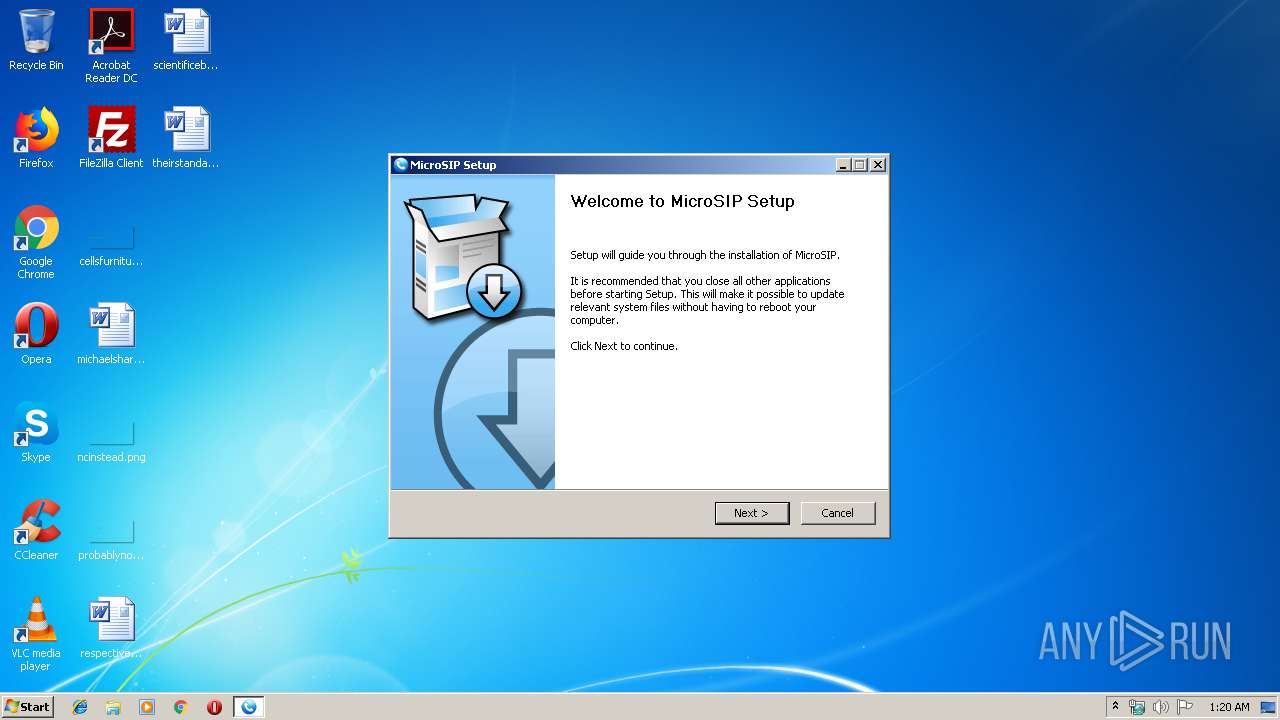
| File name: | MicroSIP-3.19.21.exe |
| Full analysis: | https://app.any.run/tasks/256a3133-af9c-483a-a32e-bb6db2d0c6be |
| Verdict: | Malicious activity |
| Analysis date: | November 19, 2019, 01:20:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | C956888498509D7BD9129FC082295280 |
| SHA1: | D04D4AB1B0E9EF2A2C3F5A6B3DC51D1B589EA6C8 |
| SHA256: | E963B2E42CCC2BFDD78DFD1F015B197A0F8177434EBD71B9C66DAB03CB956B68 |
| SSDEEP: | 196608:UrBMkj3YB2lCLJfXBP300sb4PPp8LdMXpsEw9yClJ:kIB2mfxf60Pp8mXpsvyCv |
MALICIOUS
Loads dropped or rewritten executable
- MicroSIP-3.19.21.exe (PID: 2952)
- MicroSIP.exe (PID: 3916)
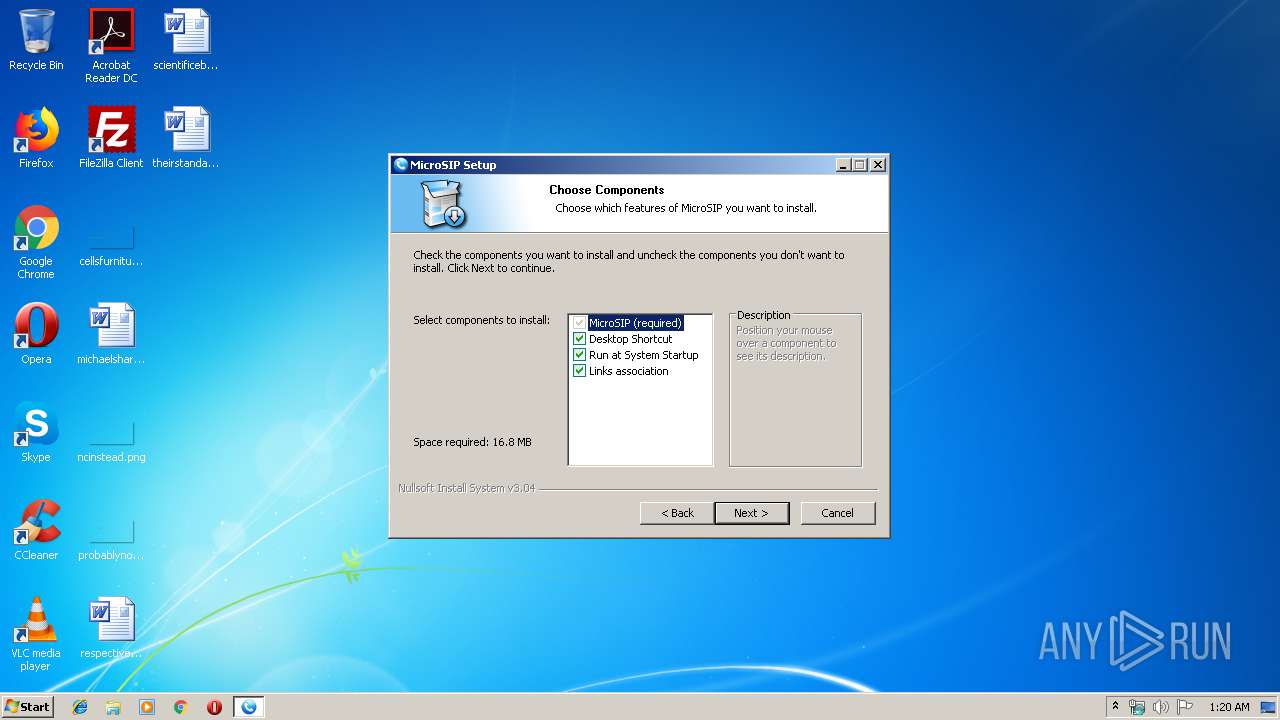
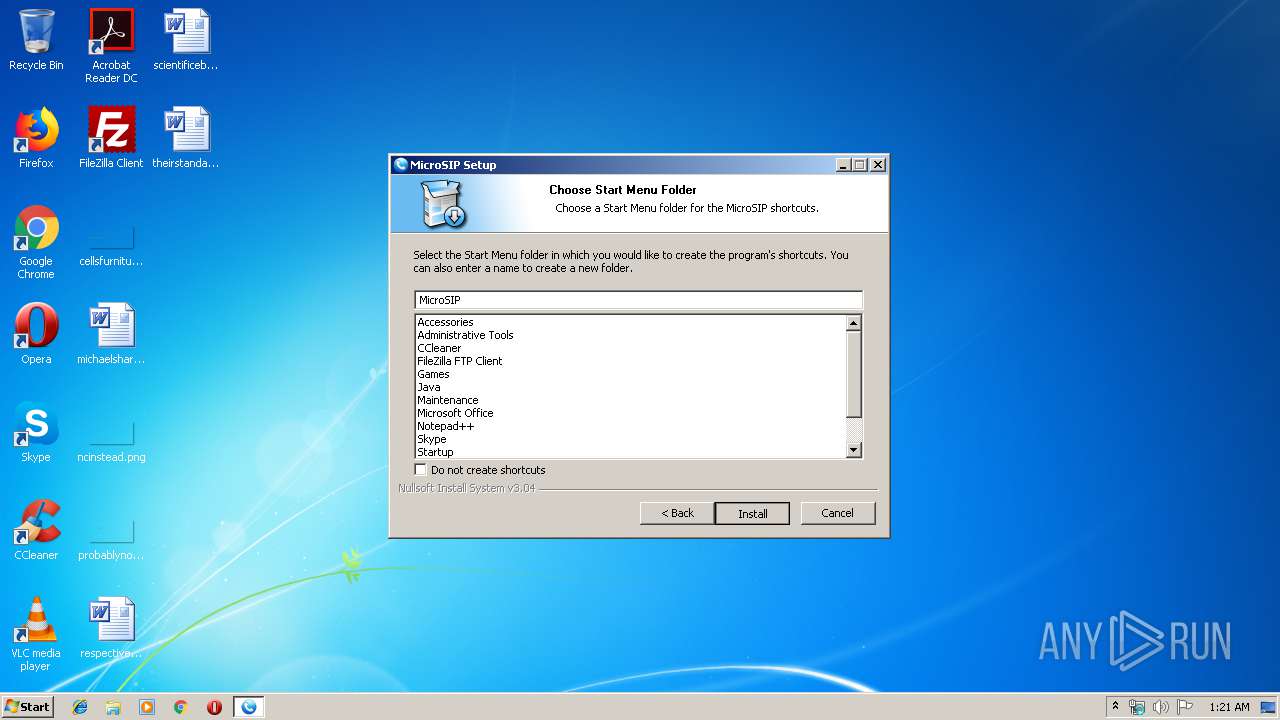
Writes to a start menu file
- MicroSIP-3.19.21.exe (PID: 2952)
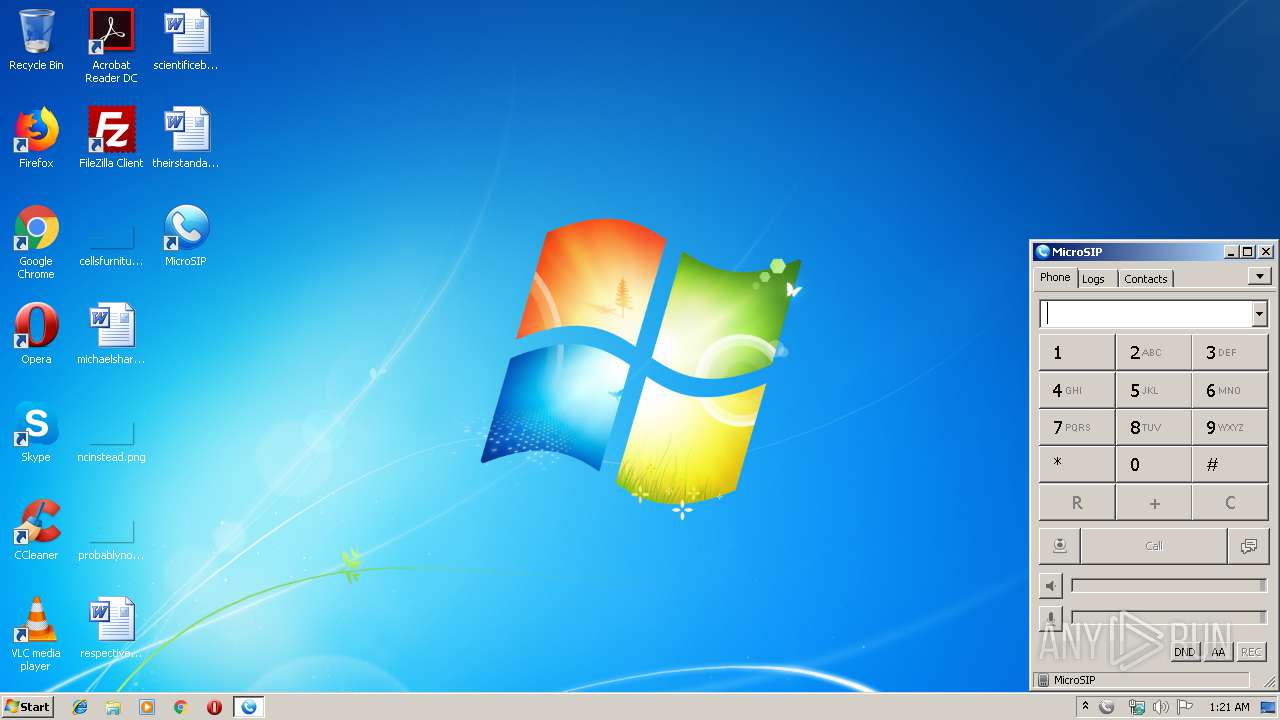
Application was dropped or rewritten from another process
- MicroSIP.exe (PID: 3916)
SUSPICIOUS
Modifies the open verb of a shell class
- MicroSIP-3.19.21.exe (PID: 2952)
Executable content was dropped or overwritten
- MicroSIP-3.19.21.exe (PID: 2952)
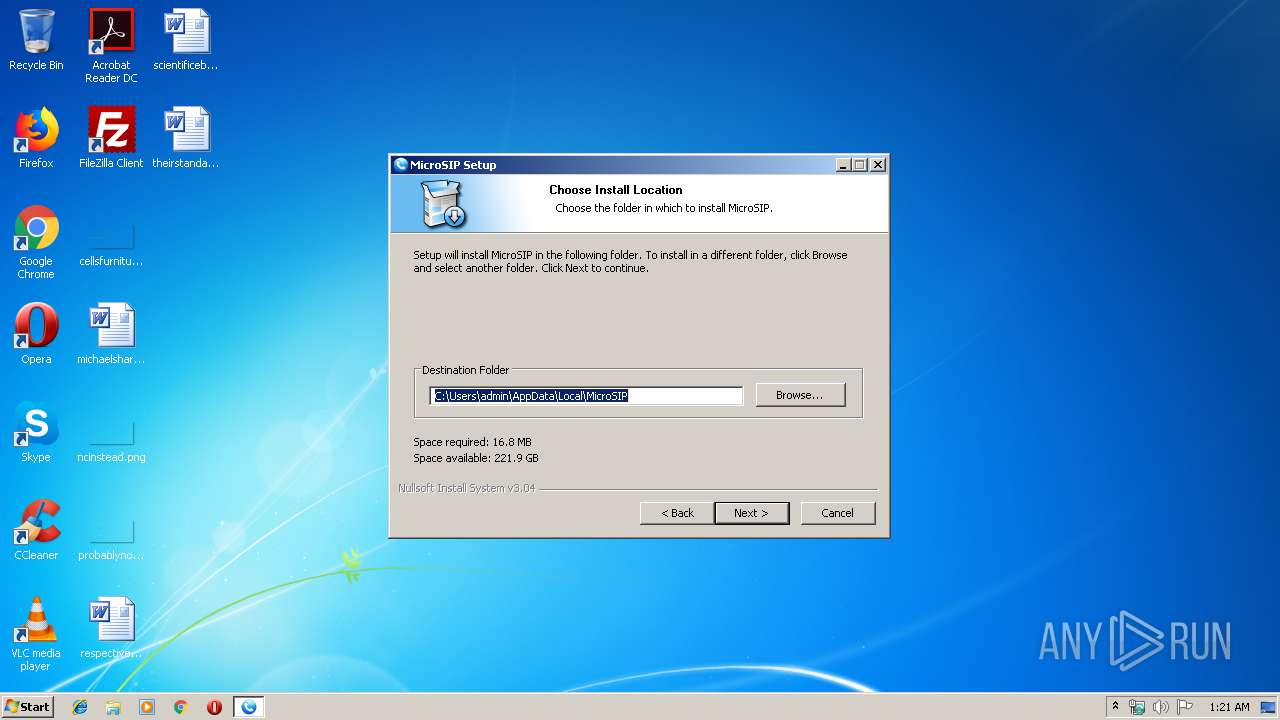
Creates a software uninstall entry
- MicroSIP-3.19.21.exe (PID: 2952)
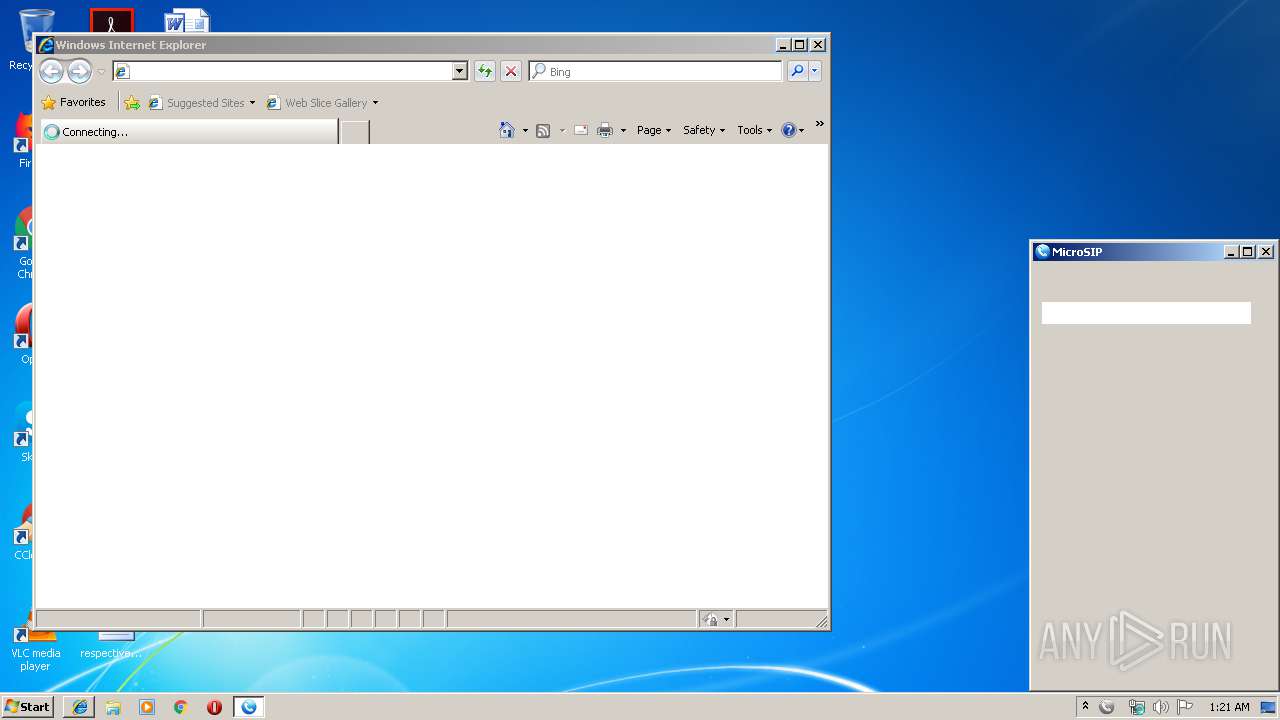
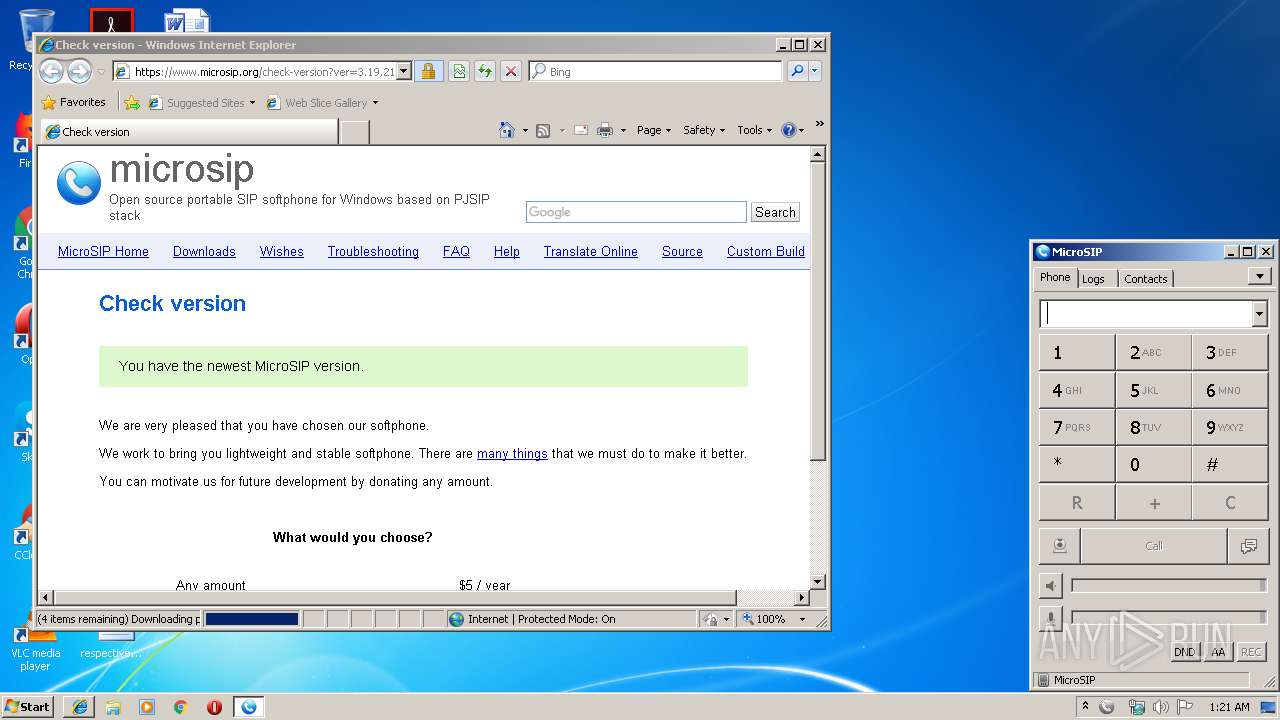
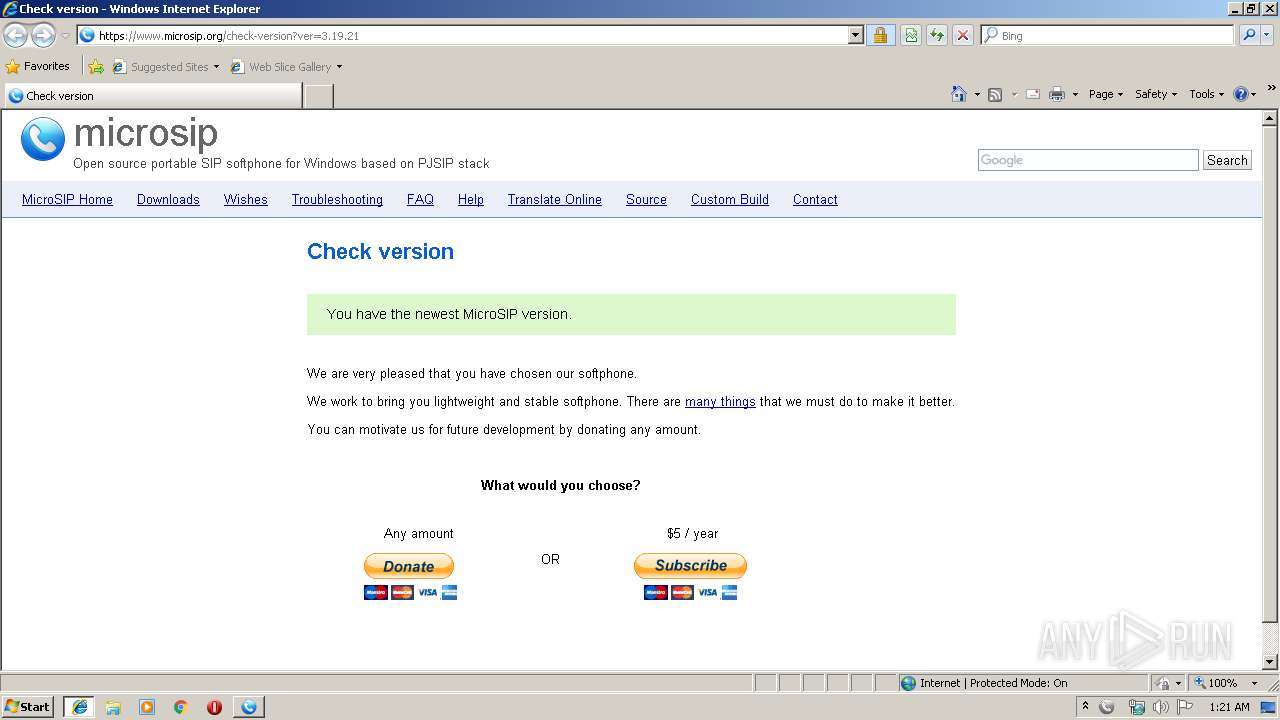
Starts Internet Explorer
- MicroSIP-3.19.21.exe (PID: 2952)
Creates files in the user directory
- MicroSIP.exe (PID: 3916)
- MicroSIP-3.19.21.exe (PID: 2952)
Reads Internet Cache Settings
- MicroSIP.exe (PID: 3916)
INFO
Dropped object may contain Bitcoin addresses
- MicroSIP-3.19.21.exe (PID: 2952)
Application launched itself
- iexplore.exe (PID: 1972)
Changes internet zones settings
- iexplore.exe (PID: 1972)
Reads Internet Cache Settings
- iexplore.exe (PID: 2128)
Reads internet explorer settings
- iexplore.exe (PID: 2128)
Creates files in the user directory
- iexplore.exe (PID: 2128)
Reads settings of System Certificates
- iexplore.exe (PID: 1972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:15 23:24:46+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x338f |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.19.21.0 |
| ProductVersionNumber: | 3.19.21.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Unknown (0452) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | www.microsip.org |
| FileDescription: | MicroSIP Setup |
| FileVersion: | 3.19.21 |
| LegalCopyright: | www.microsip.org |
| ProductDescription: | MicroSIP Setup |
| ProductName: | MicroSIP |
| ProductVersion: | 3.19.21 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Dec-2018 22:24:46 |
| Detected languages: |
|
| CompanyName: | www.microsip.org |
| FileDescription: | MicroSIP Setup |
| FileVersion: | 3.19.21 |
| LegalCopyright: | www.microsip.org |
| ProductDescription: | MicroSIP Setup |
| ProductName: | MicroSIP |
| ProductVersion: | 3.19.21 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Dec-2018 22:24:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006627 | 0x00006800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45178 |
.rdata | 0x00008000 | 0x000014A2 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.02518 |
.data | 0x0000A000 | 0x0002AFF8 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.03532 |
.ndata | 0x00035000 | 0x00032000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00067000 | 0x00020798 | 0x00020800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.16703 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29611 | 1059 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 6.31545 | 16936 | UNKNOWN | English - United States | RT_ICON |
3 | 6.47006 | 9640 | UNKNOWN | English - United States | RT_ICON |
4 | 6.58558 | 6760 | UNKNOWN | English - United States | RT_ICON |
5 | 6.79888 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 6.91099 | 2440 | UNKNOWN | English - United States | RT_ICON |
7 | 6.87824 | 1720 | UNKNOWN | English - United States | RT_ICON |
8 | 6.65883 | 1128 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.95626 | 118 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
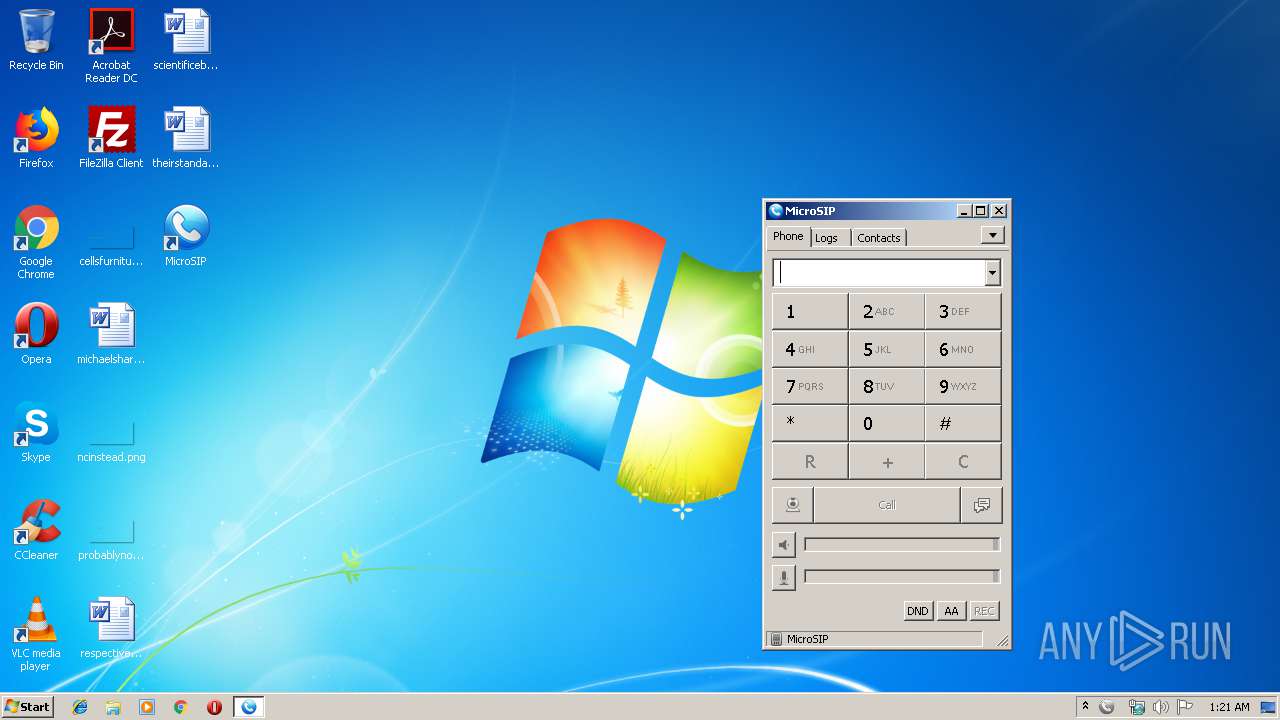
Total processes
38
Monitored processes
4
Malicious processes
2
Suspicious processes
0
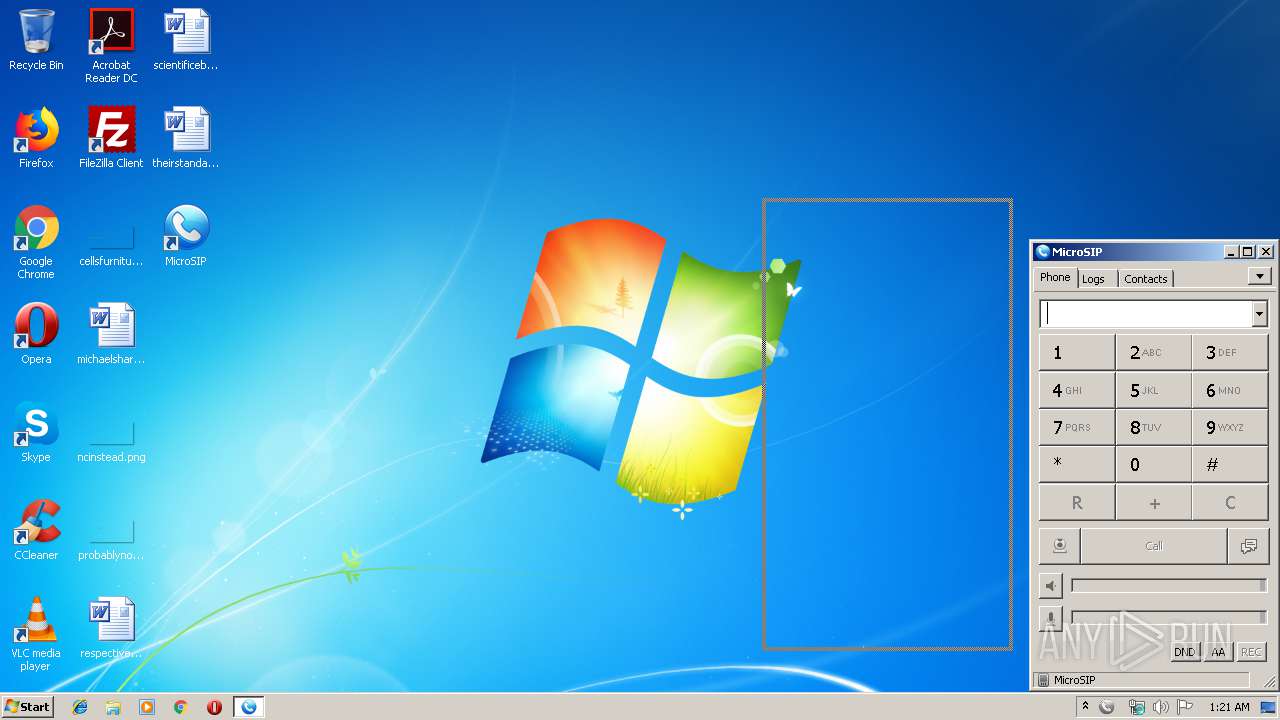
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1972 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | MicroSIP-3.19.21.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2128 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1972 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2952 | "C:\Users\admin\AppData\Local\Temp\MicroSIP-3.19.21.exe" | C:\Users\admin\AppData\Local\Temp\MicroSIP-3.19.21.exe | explorer.exe | ||||||||||||
User: admin Company: www.microsip.org Integrity Level: MEDIUM Description: MicroSIP Setup Exit code: 0 Version: 3.19.21 Modules
| |||||||||||||||
| 3916 | C:\Users\admin\AppData\Local\MicroSIP\MicroSIP.exe | C:\Users\admin\AppData\Local\MicroSIP\MicroSIP.exe | MicroSIP-3.19.21.exe | ||||||||||||
User: admin Company: www.microsip.org Integrity Level: MEDIUM Description: MicroSIP Exit code: 0 Version: 3.19.21 Modules
| |||||||||||||||
Total events
1 187
Read events
1 074
Write events
112
Delete events
1
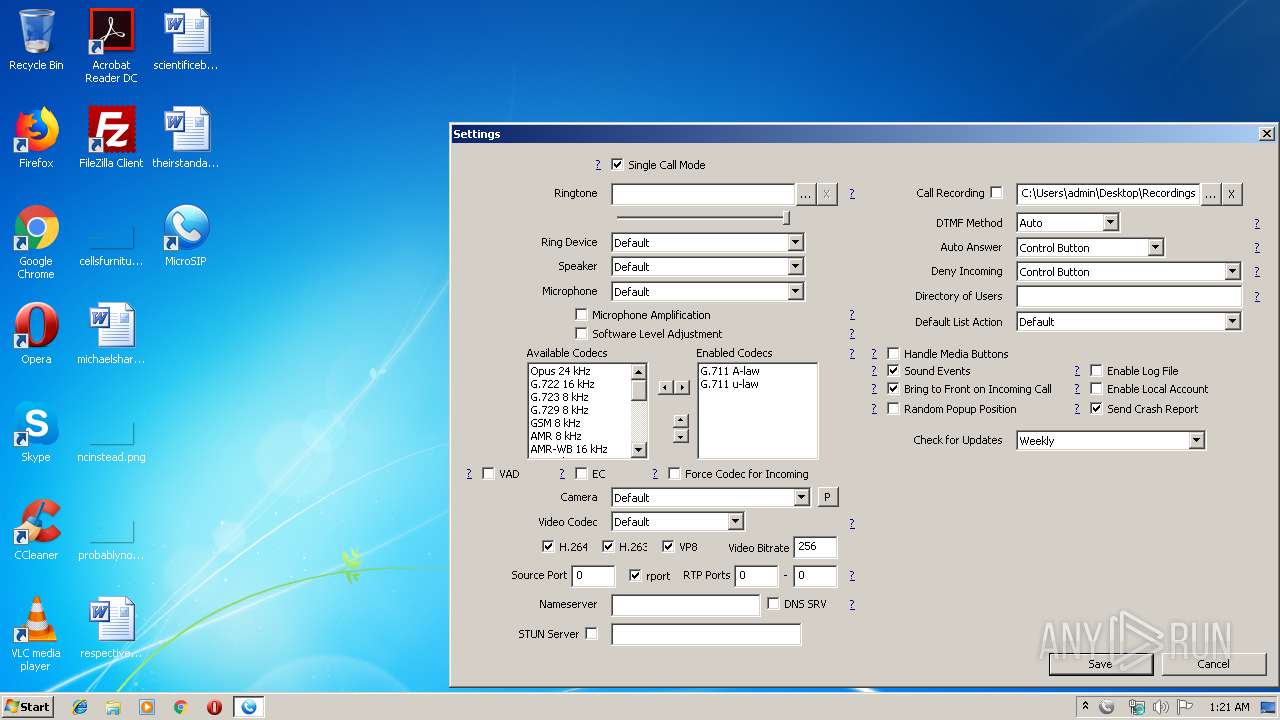
Modification events
| (PID) Process: | (2952) MicroSIP-3.19.21.exe | Key: | HKEY_CURRENT_USER\Software\MicroSIP |
| Operation: | write | Name: | |
Value: C:\Users\admin\AppData\Local\MicroSIP | |||
| (PID) Process: | (2952) MicroSIP-3.19.21.exe | Key: | HKEY_CURRENT_USER\Software\MicroSIP\Capabilities |
| Operation: | write | Name: | ApplicationDescription |
Value: Softphone | |||
| (PID) Process: | (2952) MicroSIP-3.19.21.exe | Key: | HKEY_CURRENT_USER\Software\MicroSIP\Capabilities |
| Operation: | write | Name: | ApplicationName |
Value: MicroSIP | |||
| (PID) Process: | (2952) MicroSIP-3.19.21.exe | Key: | HKEY_CURRENT_USER\Software\MicroSIP\Capabilities\UrlAssociations |
| Operation: | write | Name: | tel |
Value: MicroSIP | |||
| (PID) Process: | (2952) MicroSIP-3.19.21.exe | Key: | HKEY_CURRENT_USER\Software\MicroSIP\Capabilities\UrlAssociations |
| Operation: | write | Name: | callto |
Value: MicroSIP | |||
| (PID) Process: | (2952) MicroSIP-3.19.21.exe | Key: | HKEY_CURRENT_USER\Software\MicroSIP\Capabilities\UrlAssociations |
| Operation: | write | Name: | sip |
Value: MicroSIP | |||
| (PID) Process: | (2952) MicroSIP-3.19.21.exe | Key: | HKEY_CLASSES_ROOT\MicroSIP |
| Operation: | write | Name: | |
Value: Internet Call Protocol | |||
| (PID) Process: | (2952) MicroSIP-3.19.21.exe | Key: | HKEY_CLASSES_ROOT\MicroSIP\DefaultIcon |
| Operation: | write | Name: | |
Value: C:\Users\admin\AppData\Local\MicroSIP\MicroSIP.exe,0 | |||
| (PID) Process: | (2952) MicroSIP-3.19.21.exe | Key: | HKEY_CLASSES_ROOT\MicroSIP\shell\open\command |
| Operation: | write | Name: | |
Value: "C:\Users\admin\AppData\Local\MicroSIP\MicroSIP.exe" "%1" | |||
| (PID) Process: | (2952) MicroSIP-3.19.21.exe | Key: | HKEY_CURRENT_USER\Software\RegisteredApplications |
| Operation: | write | Name: | MicroSIP |
Value: SOFTWARE\MicroSIP\Capabilities | |||
Executable files
11
Suspicious files
3
Text files
256
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2952 | MicroSIP-3.19.21.exe | C:\Users\admin\AppData\Local\Temp\nscB3AB.tmp\modern-header.bmp | image | |
MD5:7F2CF7FC6EE45076F9A871CF553DEF53 | SHA256:33FD79634BC585E46E8CCD8BC7242CDD2133376A6DC1196C5C9D752E8ADEABCE | |||
| 2952 | MicroSIP-3.19.21.exe | C:\Users\admin\AppData\Local\Temp\nscB3AB.tmp\LangDLL.dll | executable | |
MD5:AB1DB56369412FE8476FEFFFD11E4CC0 | SHA256:6F14C8F01F50A30743DAC68C5AC813451463DFB427EB4E35FCDFE2410E1A913B | |||
| 2952 | MicroSIP-3.19.21.exe | C:\Users\admin\AppData\Local\MicroSIP\microsip.exe | executable | |
MD5:— | SHA256:— | |||
| 2952 | MicroSIP-3.19.21.exe | C:\Users\admin\AppData\Local\Temp\nscB3AB.tmp\modern-wizard.bmp | image | |
MD5:32D872B48C1106D505F5C727D1F5A4A3 | SHA256:5C5E3E1BADA532E95AEA8846336B0F5F17CC9C49BCD020064CD3EBE4A5D86922 | |||
| 2952 | MicroSIP-3.19.21.exe | C:\Users\admin\AppData\Local\MicroSIP\SDL2.dll | executable | |
MD5:70353A2E0375015D2A15E7AB5C7ADCE7 | SHA256:AFEDDF0FFDC0DBA31883EFA7D41727E0D1042A02471AAD241CF415E903169FE7 | |||
| 2952 | MicroSIP-3.19.21.exe | C:\Users\admin\AppData\Local\MicroSIP\swscale-4.dll | executable | |
MD5:62C0267FE5C7133EB74FD52324A3B7F6 | SHA256:4992639DF7187DFF687AE00403D587B3ADC721F8C23CA395E71EC6628E38E743 | |||
| 2952 | MicroSIP-3.19.21.exe | C:\Users\admin\AppData\Local\MicroSIP\ringing.wav | wav | |
MD5:B3295F1191AEAD89915F232A0AC1151A | SHA256:09F83C6D05BCBE78C32B7815609F89284C3E0A9D2D11E36388C8163FAE21F2C0 | |||
| 2952 | MicroSIP-3.19.21.exe | C:\Users\admin\AppData\Local\MicroSIP\avformat-57.dll | executable | |
MD5:11DF4D971CFC63A4FAC48E1A0478FC99 | SHA256:DF599C6944C31FD3EA212A1B080DD851D823886BBBC59A9814A910C793426E65 | |||
| 2952 | MicroSIP-3.19.21.exe | C:\Users\admin\AppData\Local\MicroSIP\hangup.wav | wav | |
MD5:EE8D73CB7474A62E91EE3F2245C80F43 | SHA256:27D45BAEEC5FD291703D4EF8596C58215E1E3416F76C4D3ECD640C0B05A176EE | |||
| 2952 | MicroSIP-3.19.21.exe | C:\Users\admin\AppData\Local\MicroSIP\ringtone.wav | wav | |
MD5:F6C7C5E7AC3A119B1EE99F35A34B00BF | SHA256:A2EFA78855ED15DD4E882E4ADDE00764D3EC59936ECAD9FB953F0963A83AB740 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
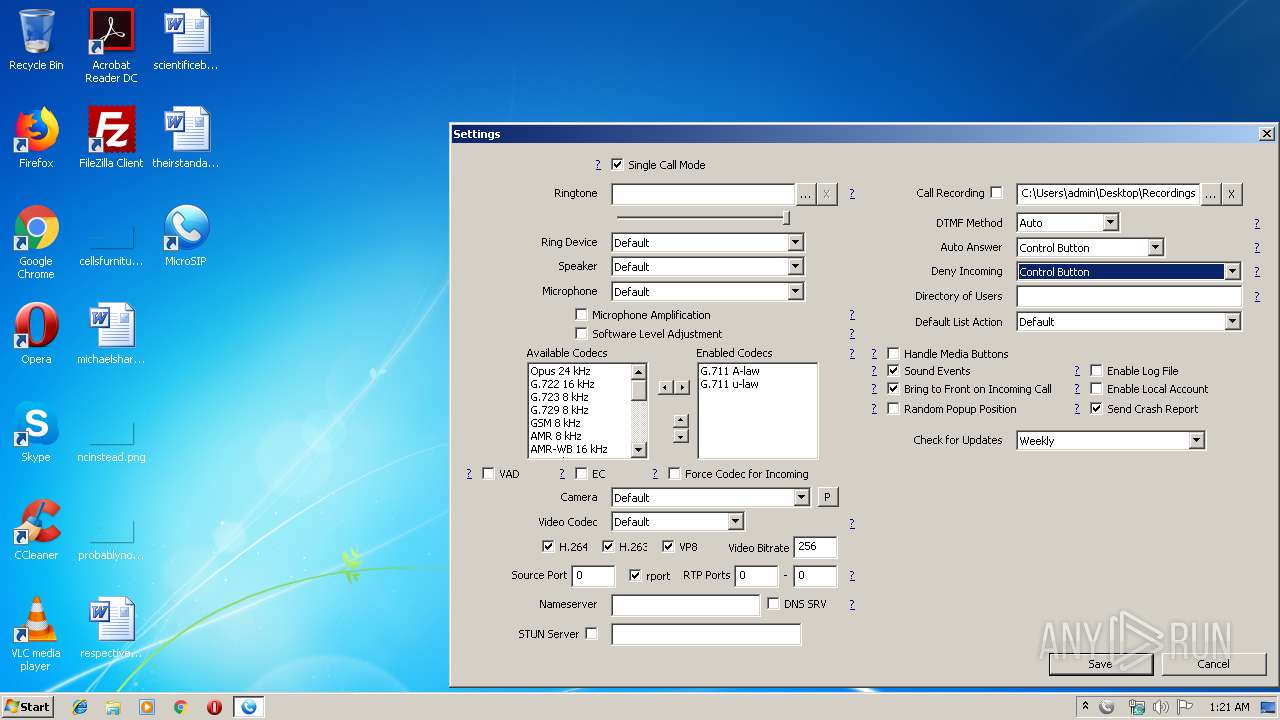
HTTP(S) requests
3
TCP/UDP connections
13
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2128 | iexplore.exe | GET | 301 | 104.28.18.51:80 | http://www.microsip.org/check-version?ver=3.19.21 | US | — | — | malicious |
3916 | MicroSIP.exe | GET | 200 | 104.28.19.51:80 | http://update.microsip.org/softphone-update.txt?version=3.19.21&client=MicroSIP | US | — | — | suspicious |
1972 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1972 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2128 | iexplore.exe | 104.28.18.51:80 | www.microsip.org | Cloudflare Inc | US | shared |
3916 | MicroSIP.exe | 104.28.19.51:80 | www.microsip.org | Cloudflare Inc | US | shared |
2128 | iexplore.exe | 104.28.18.51:443 | www.microsip.org | Cloudflare Inc | US | shared |
2128 | iexplore.exe | 216.58.207.68:443 | www.google.com | Google Inc. | US | whitelisted |
2128 | iexplore.exe | 172.217.22.34:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2128 | iexplore.exe | 216.58.205.238:443 | cse.google.com | Google Inc. | US | whitelisted |
2128 | iexplore.exe | 172.217.22.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2128 | iexplore.exe | 23.210.248.226:443 | www.paypalobjects.com | Akamai International B.V. | NL | whitelisted |
1972 | iexplore.exe | 104.28.18.51:443 | www.microsip.org | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
www.microsip.org |
| malicious |
update.microsip.org |
| suspicious |
pagead2.googlesyndication.com |
| whitelisted |
www.google.com |
| malicious |
cse.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.paypalobjects.com |
| whitelisted |