| File name: | 02516937 |
| Full analysis: | https://app.any.run/tasks/7a89cb7d-7c52-4d93-9acf-1bd8488cf28d |
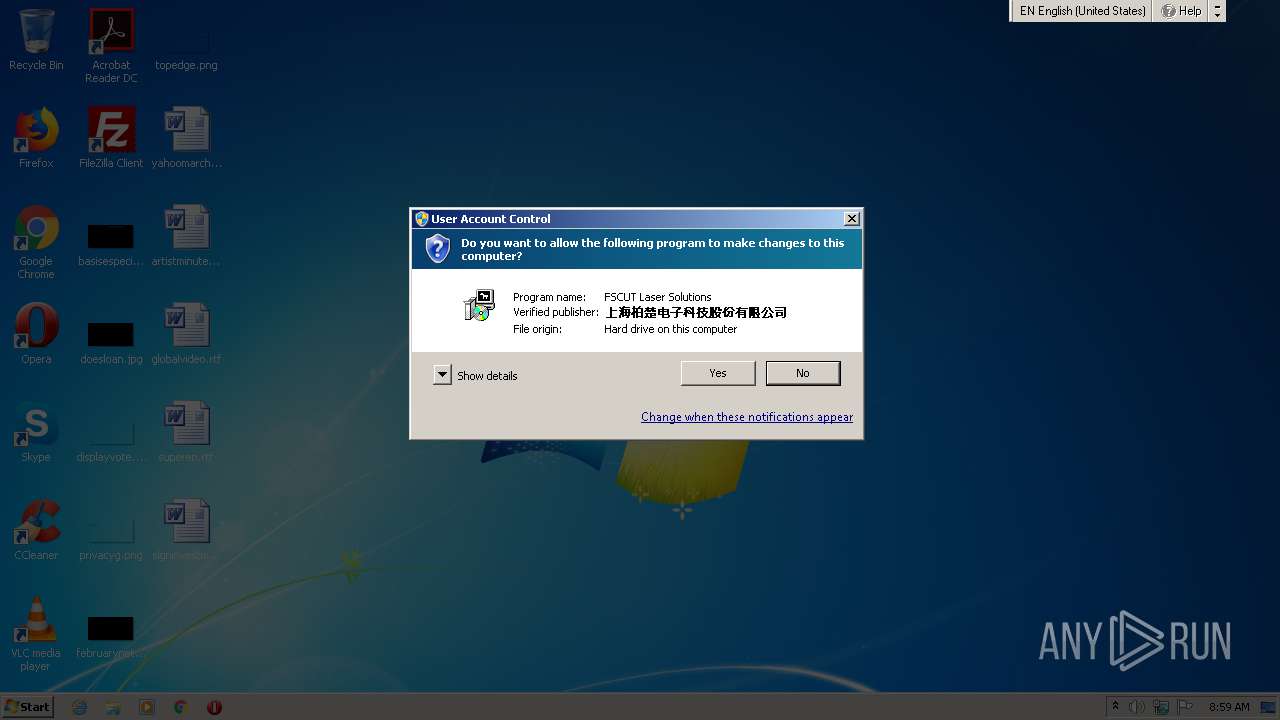
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2021, 07:59:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 697FCFDB843A36EA350F5D3FBC5A5B59 |
| SHA1: | A59F9A6057F28DD03A626FEF408B1754A7D4C7AE |
| SHA256: | E95AF1654E3E67DE365C7894D2499E94B16D634AC4E4A3ADD20FC34F58936AF3 |
| SSDEEP: | 49152:opdLp7bL5S4Wgzj3CXw5G5lHQGxeIKhMjPzC+8+0KL/fV5KNxvCJl0e6M6Jb9DQ:oXL15S9GjSXAG5tXxe3SjPzX8+bL/9Yu |
MALICIOUS
Application was dropped or rewritten from another process
- nsBABD.tmp (PID: 1708)
- nsB889.tmp (PID: 868)
- nsB57B.tmp (PID: 1840)
- nsBCE1.tmp (PID: 3900)
- nsC0BB.tmp (PID: 3648)
- nsC281.tmp (PID: 2908)
- nsBE97.tmp (PID: 1380)
- nsC438.tmp (PID: 2724)
- nsC65C.tmp (PID: 2892)
- nsC812.tmp (PID: 2648)
- FsdcSvc.exe (PID: 3392)
- FsdcSvc.exe (PID: 3640)
- fsdc.exe (PID: 1704)
Drops executable file immediately after starts
- 02516937.exe (PID: 2508)
Loads dropped or rewritten executable
- 02516937.exe (PID: 2508)
Changes settings of System certificates
- fsdc.exe (PID: 1704)
SUSPICIOUS
Drops a file that was compiled in debug mode
- 02516937.exe (PID: 2508)
Creates files in the program directory
- 02516937.exe (PID: 2508)
- fsdc.exe (PID: 1704)
Uses NETSH.EXE for network configuration
- nsB889.tmp (PID: 868)
- nsB57B.tmp (PID: 1840)
- nsBE97.tmp (PID: 1380)
- nsBCE1.tmp (PID: 3900)
- nsC0BB.tmp (PID: 3648)
- nsC281.tmp (PID: 2908)
- nsC438.tmp (PID: 2724)
- nsC65C.tmp (PID: 2892)
- nsBABD.tmp (PID: 1708)
Creates a directory in Program Files
- 02516937.exe (PID: 2508)
- fsdc.exe (PID: 1704)
Executable content was dropped or overwritten
- 02516937.exe (PID: 2508)
Starts application with an unusual extension
- 02516937.exe (PID: 2508)
Executed as Windows Service
- FsdcSvc.exe (PID: 3640)
Reads CPU info
- fsdc.exe (PID: 1704)
Low-level read access rights to disk partition
- fsdc.exe (PID: 1704)
Adds / modifies Windows certificates
- fsdc.exe (PID: 1704)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x3312 |
| UninitializedDataSize: | 1024 |
| InitializedDataSize: | 118784 |
| CodeSize: | 25088 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2020:08:01 04:42:47+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Aug-2020 02:42:47 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 01-Aug-2020 02:42:47 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000060D5 | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.41767 |
.rdata | 0x00008000 | 0x00001274 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.06107 |
.data | 0x0000A000 | 0x0001A838 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.99516 |
.ndata | 0x00025000 | 0x0000C000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00031000 | 0x000007E0 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.94469 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29035 | 843 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 2.16096 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
75
Monitored processes
24
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 544 | netsh advfirewall firewall add rule dir = in action = allow name = "UDP 7088" protocol = UDP localport = 7088 | C:\Windows\system32\netsh.exe | — | nsC0BB.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 868 | "C:\Users\admin\AppData\Local\Temp\nslB309.tmp\nsB889.tmp" netsh advfirewall firewall set rule name = all protocol = TCP localport = 9527 new action = allow | C:\Users\admin\AppData\Local\Temp\nslB309.tmp\nsB889.tmp | — | 02516937.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 1148 | netsh advfirewall firewall set rule name = all protocol = TCP localport = 9527 new action = allow | C:\Windows\system32\netsh.exe | — | nsB889.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1380 | "C:\Users\admin\AppData\Local\Temp\nslB309.tmp\nsBE97.tmp" netsh advfirewall firewall set rule name = all protocol = UDP localport = 7088 new action = allow | C:\Users\admin\AppData\Local\Temp\nslB309.tmp\nsBE97.tmp | — | 02516937.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 1704 | "C:\Program Files\Friendess\Share\fsdc\V2.3.3.5\fsdc.exe" | C:\Program Files\Friendess\Share\fsdc\V2.3.3.5\fsdc.exe | FsdcSvc.exe | ||||||||||||
User: SYSTEM Company: Friendess, Inc. Integrity Level: SYSTEM Exit code: 0 Version: 2.3.3.5 Modules
| |||||||||||||||
| 1708 | "C:\Users\admin\AppData\Local\Temp\nslB309.tmp\nsBABD.tmp" netsh advfirewall firewall add rule dir = in action = allow name = "TCP 9527" protocol = TCP localport = 9527 | C:\Users\admin\AppData\Local\Temp\nslB309.tmp\nsBABD.tmp | — | 02516937.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1720 | netsh advfirewall firewall add rule dir = in action = allow name = "UDP 7089" protocol = UDP localport = 7089 | C:\Windows\system32\netsh.exe | — | nsC65C.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1840 | "C:\Users\admin\AppData\Local\Temp\nslB309.tmp\nsB57B.tmp" netsh advfirewall firewall delete rule name = "TCP 9527" | C:\Users\admin\AppData\Local\Temp\nslB309.tmp\nsB57B.tmp | — | 02516937.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 2088 | netsh advfirewall firewall delete rule name = "UDP 7088" | C:\Windows\system32\netsh.exe | — | nsBCE1.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2176 | netsh advfirewall firewall add rule dir = in action = allow name = "TCP 9527" protocol = TCP localport = 9527 | C:\Windows\system32\netsh.exe | — | nsBABD.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
825
Read events
414
Write events
411
Delete events
0
Modification events
| (PID) Process: | (2404) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2404) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (2404) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (2404) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (2404) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
| (PID) Process: | (2404) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-1 |
Value: IPsec Relying Party | |||
| (PID) Process: | (2404) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-2 |
Value: Provides IPsec based enforcement for Network Access Protection | |||
| (PID) Process: | (2404) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-4 |
Value: 1.0 | |||
| (PID) Process: | (2404) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-3 |
Value: Microsoft Corporation | |||
| (PID) Process: | (2404) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\tsgqec.dll,-100 |
Value: RD Gateway Quarantine Enforcement Client | |||
Executable files
21
Suspicious files
11
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2508 | 02516937.exe | C:\Program Files\Friendess\Share\fsdc\FsdcSvc.exe | executable | |
MD5:— | SHA256:— | |||
| 2508 | 02516937.exe | C:\Program Files\Friendess\Share\fsdc\V2.3.3.5\fsdc.exe | executable | |
MD5:— | SHA256:— | |||
| 2508 | 02516937.exe | C:\Users\admin\AppData\Local\Temp\nslB309.tmp\nsBABD.tmp | executable | |
MD5:— | SHA256:— | |||
| 2508 | 02516937.exe | C:\Users\admin\AppData\Local\Temp\nslB309.tmp\nsB57B.tmp | executable | |
MD5:— | SHA256:— | |||
| 2508 | 02516937.exe | C:\Users\admin\AppData\Local\Temp\nslB309.tmp\nsB889.tmp | executable | |
MD5:— | SHA256:— | |||
| 2508 | 02516937.exe | C:\Users\admin\AppData\Local\Temp\nslB309.tmp\nsBCE1.tmp | executable | |
MD5:— | SHA256:— | |||
| 2508 | 02516937.exe | C:\Users\admin\AppData\Local\Temp\nslB309.tmp\nsBE97.tmp | executable | |
MD5:— | SHA256:— | |||
| 2508 | 02516937.exe | C:\Users\admin\AppData\Local\Temp\nslB309.tmp\nsC0BB.tmp | executable | |
MD5:— | SHA256:— | |||
| 2508 | 02516937.exe | C:\Program Files\Friendess\Share\fsdc\V2.3.3.5\7z.dll | executable | |
MD5:9954584250324791BEBDE54E8264A97C | SHA256:B5B25E9FB4A5175EF0D21C7C7F9D51D7D3F4000E147440571FF57FCB46DCAEA2 | |||
| 2508 | 02516937.exe | C:\Program Files\Friendess\Share\fsdc\V2.3.3.5\RunFSDC.exe | executable | |
MD5:0E01F285864D82253A89AE13B8D9E449 | SHA256:139D34B8CC4D69D42B15DD2D56BF79CC2D4BE080C63AACE95D0BEA3BD08000CF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
9
DNS requests
4
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1704 | fsdc.exe | 47.102.130.53:443 | hdauth.fscut.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | suspicious |
1704 | fsdc.exe | 10.1.1.81:80 | share.fscut.com | — | — | unknown |
1704 | fsdc.exe | 47.103.37.176:80 | www.fscut.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
— | — | 10.1.1.81:80 | share.fscut.com | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hdauth.fscut.com |
| suspicious |
www.fscut.com |
| unknown |
share.fscut.com |
| unknown |
Threats
Process | Message |
|---|---|
fsdc.exe | TcpConnectThread |
fsdc.exe | Connected |
fsdc.exe | TcpConnectThread |
fsdc.exe | Connected |
fsdc.exe | TcpConnectThread |
fsdc.exe | Connected |
fsdc.exe | TcpConnectThread |
fsdc.exe | Connected |
fsdc.exe | TcpConnectThread |
fsdc.exe | Connected |