| download: | UniSignCRSV3Setup.exe |
| Full analysis: | https://app.any.run/tasks/8f94af08-8fa4-4972-8f46-e0ea99da3224 |
| Verdict: | Malicious activity |
| Analysis date: | February 05, 2019, 14:03:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | F8969BB47D1EB7C55EED39A81ED1D420 |
| SHA1: | 4986C0FCDA19E1077A105D5F25F7A4FE52B21899 |
| SHA256: | E94C3C16CB8704F4FA665CE12DEBE04490766EFEC64138C98B9C2CB33DCB7478 |
| SSDEEP: | 196608:JR+WdSaQ5sZRC7zTtFG4FbPV5F0AdE+kdmzaLnA4f3Dt:ayQ6Zs3RjT0AdE/+EAgzt |
MALICIOUS
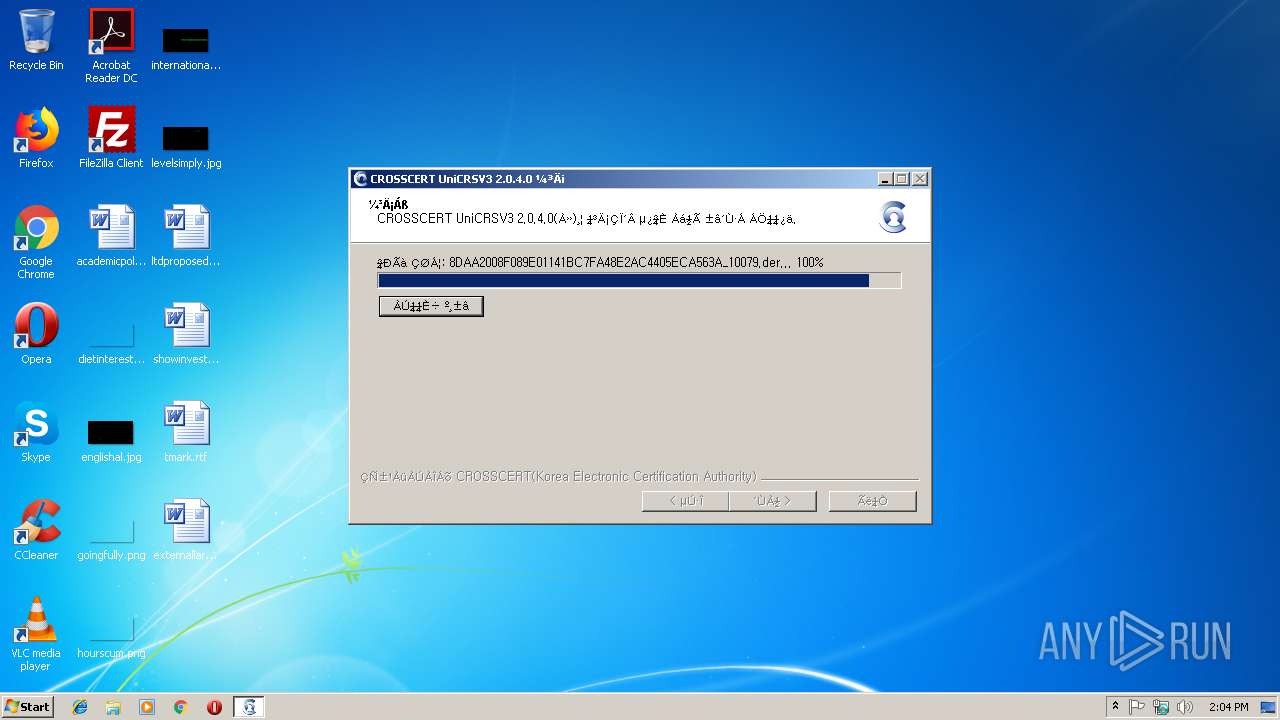
Loads dropped or rewritten executable
- UniSignCRSV3Setup.exe (PID: 3764)
- certutil.exe (PID: 3996)
- UniCRSLocalServer.exe (PID: 3936)
Changes the autorun value in the registry
- UniSignCRSV3Setup.exe (PID: 3764)
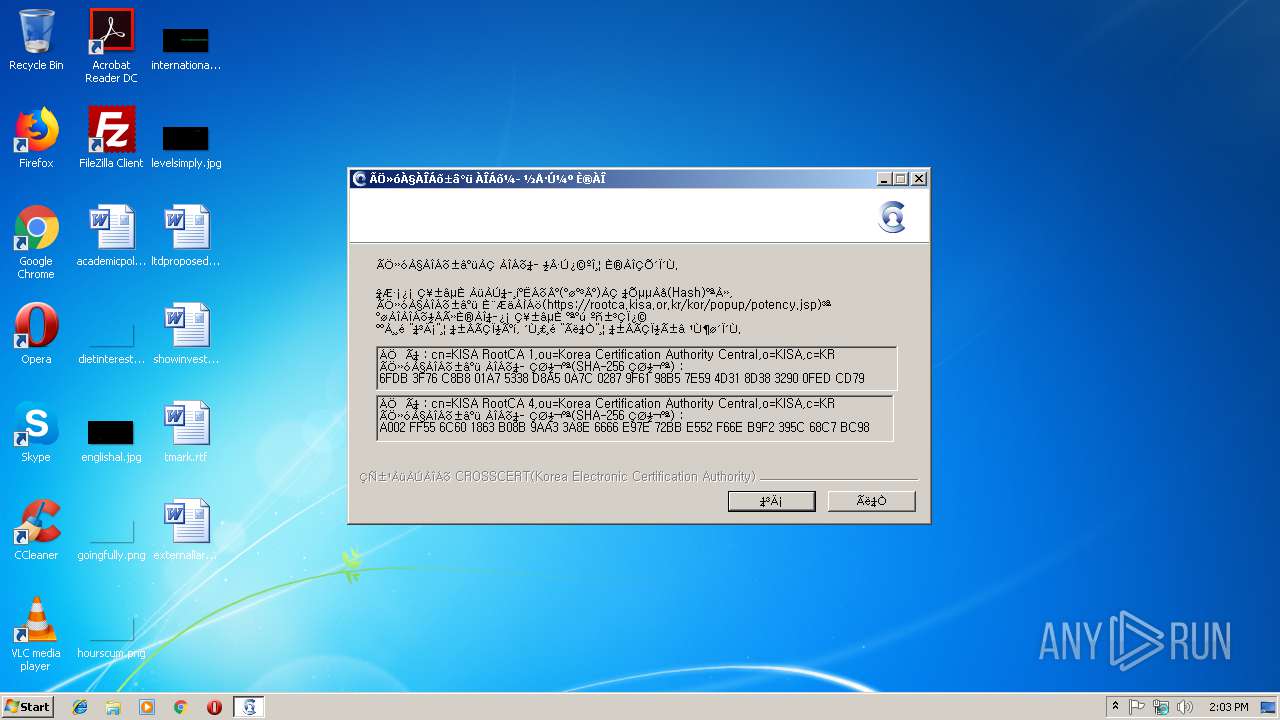
Changes settings of System certificates
- UniSignCRSV3Setup.exe (PID: 3764)
Application was dropped or rewritten from another process
- certutil.exe (PID: 3996)
- CCDaemon.exe (PID: 3336)
- UniCRSLocalServer.exe (PID: 3936)
SUSPICIOUS
Executable content was dropped or overwritten
- UniSignCRSV3Setup.exe (PID: 3764)
Creates files in the user directory
- certutil.exe (PID: 3996)
Creates files in the program directory
- UniSignCRSV3Setup.exe (PID: 3764)
Modifies the open verb of a shell class
- UniSignCRSV3Setup.exe (PID: 3764)
Creates a software uninstall entry
- UniSignCRSV3Setup.exe (PID: 3764)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:52+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 164864 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30fa |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:52 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005C4C | 0x00005E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44011 |
.rdata | 0x00007000 | 0x0000129C | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04684 |
.data | 0x00009000 | 0x00025C58 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.801 |
.ndata | 0x0002F000 | 0x0000A000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00039000 | 0x000019C8 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.26257 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21482 | 958 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 1.7815 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.68176 | 494 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.86295 | 228 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.92694 | 218 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
38
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3172 | "C:\Users\admin\AppData\Local\Temp\UniSignCRSV3Setup.exe" | C:\Users\admin\AppData\Local\Temp\UniSignCRSV3Setup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3336 | "C:\Program Files\Crosscert\UniSignCRSV3\CCDaemon.exe" | C:\Program Files\Crosscert\UniSignCRSV3\CCDaemon.exe | — | UniSignCRSV3Setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3764 | "C:\Users\admin\AppData\Local\Temp\UniSignCRSV3Setup.exe" | C:\Users\admin\AppData\Local\Temp\UniSignCRSV3Setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3936 | "C:\Program Files\Crosscert\UniSignCRSV3\UniCRSLocalServer.exe" | C:\Program Files\Crosscert\UniSignCRSV3\UniCRSLocalServer.exe | UniSignCRSV3Setup.exe | ||||||||||||
User: admin Company: CrossCert Integrity Level: HIGH Description: UniCRSLocalServer Exit code: 0 Version: 2.0.4.0 Modules
| |||||||||||||||
| 3996 | C:\Users\admin\AppData\Local\Temp\nsd7A62.tmp\certutil.exe -A -n CrossCert_Trust_Root -t TCu,Cu,Tuw -i C:\Users\admin\AppData\Local\Temp\nsd7A62.tmp\rootca.der -d "C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles/qldyz51w.default" | C:\Users\admin\AppData\Local\Temp\nsd7A62.tmp\certutil.exe | — | UniSignCRSV3Setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
358
Read events
346
Write events
12
Delete events
0
Modification events
| (PID) Process: | (3764) UniSignCRSV3Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\7972D337BFC4775CEED41080885A209C1ED0C89A |
| Operation: | write | Name: | Blob |
Value: 0300000001000000140000007972D337BFC4775CEED41080885A209C1ED0C89A20000000010000009B030000308203973082027FA003020102020900FABC4A24BD2E9B71300D06092A864886F70D01010B0500305A310B3009060355040613024B5231123010060355040A0C0943726F73734365727431153013060355040B0C0C4163637265646974656443413120301E06035504030C1743726F7373636572745F54727573745F526F6F745F4341301E170D3136303631333031323930365A170D3236303631313031323930365A305A310B3009060355040613024B5231123010060355040A0C0943726F73734365727431153013060355040B0C0C4163637265646974656443413120301E06035504030C1743726F7373636572745F54727573745F526F6F745F434130820122300D06092A864886F70D01010105000382010F003082010A0282010100C445055EAEA8FADE039FEC27D3B9EF41364BF0EBD699554580643C170E89646FC6D9555318790696D2DDEE3A0C63BB352B220C08979C454816B55CD3A0B298D98A25DAC1993643A40D1F57C6F358EB632DA7A385CCE842F3D82DDDA54E189B32377CA7AC80DB17B458136CE715C573AF1D2BE9BAC90A361820EA86054ABAF0B23B2AA16E2302725B29F5F55C049FCE010F175CDB46BB438BD157DA7133308AD117F19381F3C9BA001511CA40EB292133CD70028EEEA732A03B80046EF053487BB1BD8902AD7BA5207A35055A70B29BBB7DBA642014E00E2C594F85C12A59AEBD6D9EDF63E9CF125E8704AC5B3145691507BE9B5FCCD871F21FC9DC341026DF6B0203010001A360305E300F0603551D130101FF040530030101FF301D0603551D0E04160414B1AF7232AE2391DFA15ECD56D1D174C71CEF6C57301F0603551D23041830168014B1AF7232AE2391DFA15ECD56D1D174C71CEF6C57300B0603551D0F040403020106300D06092A864886F70D01010B050003820101005265816E91F4DC1D0914A0B0E53313B2A14F409ACC368F76267BB925F115930E4D4BA6AFCC9011C3C496F8BD739016A2030FB5D27160CB4922AAE06DEB245C72CCF621BCD46794BB24F1F2921732502ACF0A7A3B8436F82D37EABDCEA922C05BF519AA127B505234541E0A5AB89EF2609CACC7CB99F8F4E036CA8310E6CC6C2D631A57B9DF97F04938FA7CB880AF7B226001A96E246E39B9E04175664539B12C69303B10DAB44FC3D6DD80824BBE3EA7AB33F9B9148DCA75BC72F13360A8BB3A62F83522B6873F74BA8E157979963388762B924178627A7CED7E910404FB545EA2199A09DF858C1B902D0703201C86C8C9494DD6D8F96793A7B55E2DB88399D2 | |||
| (PID) Process: | (3764) UniSignCRSV3Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\UniCRSV3 |
| Operation: | write | Name: | URL Protocol |
Value: | |||
| (PID) Process: | (3764) UniSignCRSV3Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\UniCRSV3\shell\open\command |
| Operation: | write | Name: | |
Value: "C:\Program Files\Crosscert\UniSignCRSV3\UniCRSLocalServer.exe" "%1" | |||
| (PID) Process: | (3764) UniSignCRSV3Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
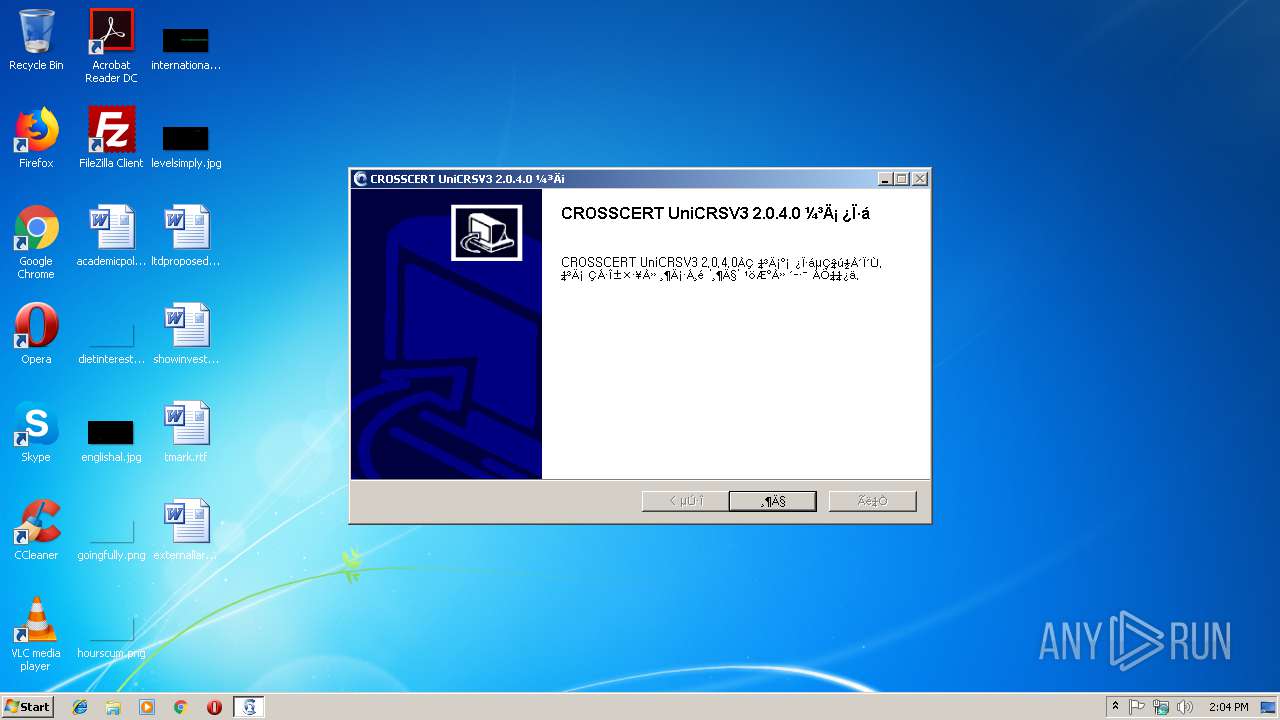
| Operation: | write | Name: | CROSSCERT UniCRSV3 |
Value: C:\Program Files\Crosscert\UniSignCRSV3\UniCRSLocalServer.exe | |||
| (PID) Process: | (3764) UniSignCRSV3Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | CROSSCERT UniCRSV3 Daemon |
Value: C:\Program Files\Crosscert\UniSignCRSV3\CCDaemon.exe | |||
| (PID) Process: | (3764) UniSignCRSV3Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CROSSCERT UniCRSV3 |
| Operation: | write | Name: | DisplayName |
Value: CROSSCERT UniCRSV3 2.0.4.0 | |||
| (PID) Process: | (3764) UniSignCRSV3Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CROSSCERT UniCRSV3 |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\Crosscert\UniSignCRSV3\uninst.exe | |||
| (PID) Process: | (3764) UniSignCRSV3Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CROSSCERT UniCRSV3 |
| Operation: | write | Name: | DisplayVersion |
Value: 2.0.4.0 | |||
| (PID) Process: | (3764) UniSignCRSV3Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CROSSCERT UniCRSV3 |
| Operation: | write | Name: | URLInfoAbout |
Value: http://open.crosscert.com | |||
| (PID) Process: | (3764) UniSignCRSV3Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CROSSCERT UniCRSV3 |
| Operation: | write | Name: | Publisher |
Value: Crosscert | |||
Executable files
33
Suspicious files
3
Text files
25
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3764 | UniSignCRSV3Setup.exe | C:\Users\admin\AppData\Local\Temp\nsd7A62.tmp\InstallOptions.dll | executable | |
MD5:325B008AEC81E5AAA57096F05D4212B5 | SHA256:C9CD5C9609E70005926AE5171726A4142FFBCCCC771D307EFCD195DAFC1E6B4B | |||
| 3764 | UniSignCRSV3Setup.exe | C:\Users\admin\AppData\Local\Temp\nsd7A62.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 3764 | UniSignCRSV3Setup.exe | C:\Users\admin\AppData\Local\Temp\nsd7A62.tmp\certutil.exe | executable | |
MD5:2082A7E8E938936ABADA0B1591135D82 | SHA256:C10CAC71859C851EBB08C72D79A8D443FACA9877A60087DF0AB8BECF5B723FC7 | |||
| 3764 | UniSignCRSV3Setup.exe | C:\Users\admin\AppData\Local\Temp\nsd7A62.tmp\nssutil3.dll | executable | |
MD5:FDD40C46FD6FC24BECB71905F3352749 | SHA256:FBE4770A1BAB99040C5AD09C600AA28B2C7FC818ED5A968113FBE15C58F2F55B | |||
| 3764 | UniSignCRSV3Setup.exe | C:\Users\admin\AppData\Local\Temp\nsd7A62.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 3764 | UniSignCRSV3Setup.exe | C:\Users\admin\AppData\Local\Temp\nsd7A62.tmp\rootca.der | der | |
MD5:ED3F57367C2BF68A74F94CD84EE7997F | SHA256:4FF058DE730604C1741382846FEE7448ECC85B69949A8F90BC636FA4169E320D | |||
| 3764 | UniSignCRSV3Setup.exe | C:\Users\admin\AppData\Local\Temp\nsd7A62.tmp\sqlite3.dll | executable | |
MD5:C99FED8482D49DF31ADF27A0FD87BF8A | SHA256:5CF15F255F3ADECF82A08C6E06777A7413A531189C5C8F5FA1310A6BDF668049 | |||
| 3764 | UniSignCRSV3Setup.exe | C:\Users\admin\AppData\Local\Temp\nsd7A62.tmp\softokn3.dll | executable | |
MD5:A23D519D4AE5AE1DE899C9DAB32936A8 | SHA256:9DBB449E09957FD126714B9F93EE3B4AD71DDA1A7DE73EBADDFCB02D6693A9C7 | |||
| 3764 | UniSignCRSV3Setup.exe | C:\Users\admin\AppData\Local\Temp\nsd7A62.tmp\smime3.dll | executable | |
MD5:0CCFE10D90748C36FD47FB51DEC1E4EA | SHA256:2FE43E798F3B9391A483D6616D15D652774338A4604FD548F1745B9AD4F10EB8 | |||
| 3764 | UniSignCRSV3Setup.exe | C:\Users\admin\AppData\Local\Temp\nsd7A62.tmp\freebl3.dll | executable | |
MD5:5FF3F2CDB0E2B4D3F6122303C38B065A | SHA256:C6C6CB0E9D16BC13BC75E3512BE04B6D44573EE2593D082EC4FC0368B6553110 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
UniCRSLocalServer.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
UniCRSLocalServer.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|