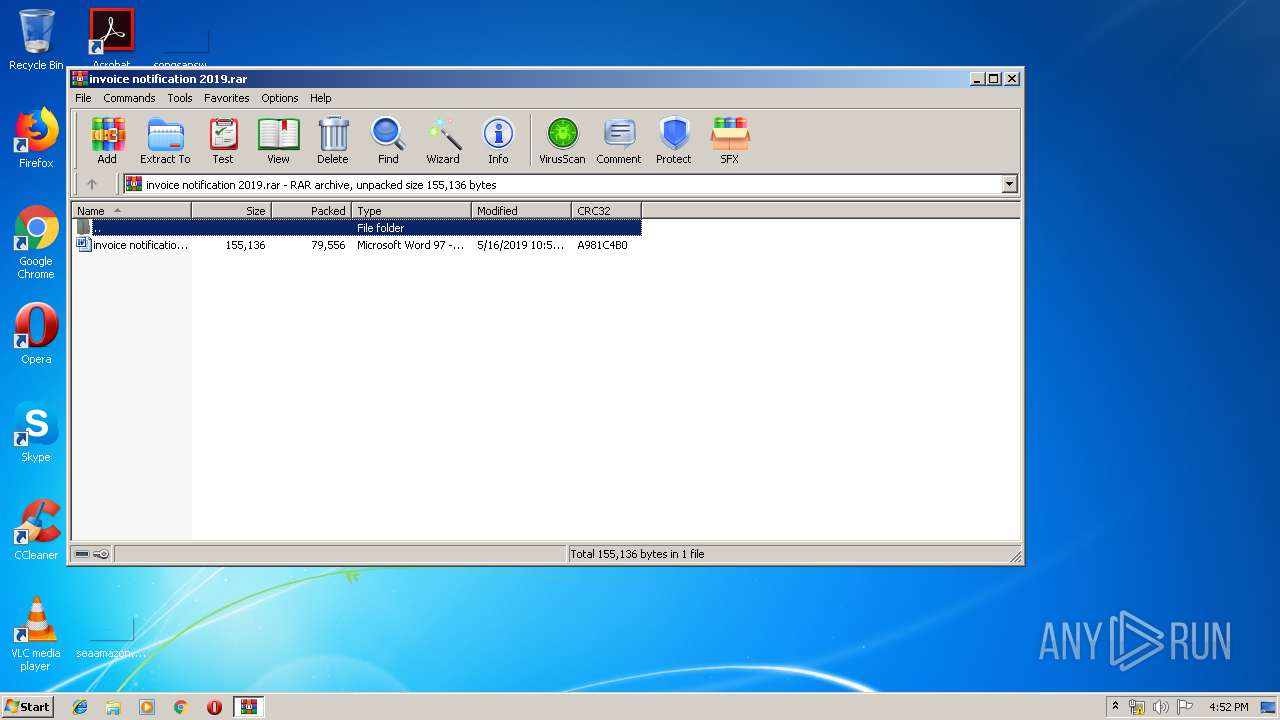
| File name: | invoice notification 2019.rar |
| Full analysis: | https://app.any.run/tasks/d4a6aefc-141e-4fb0-9643-853ca84b1b61 |
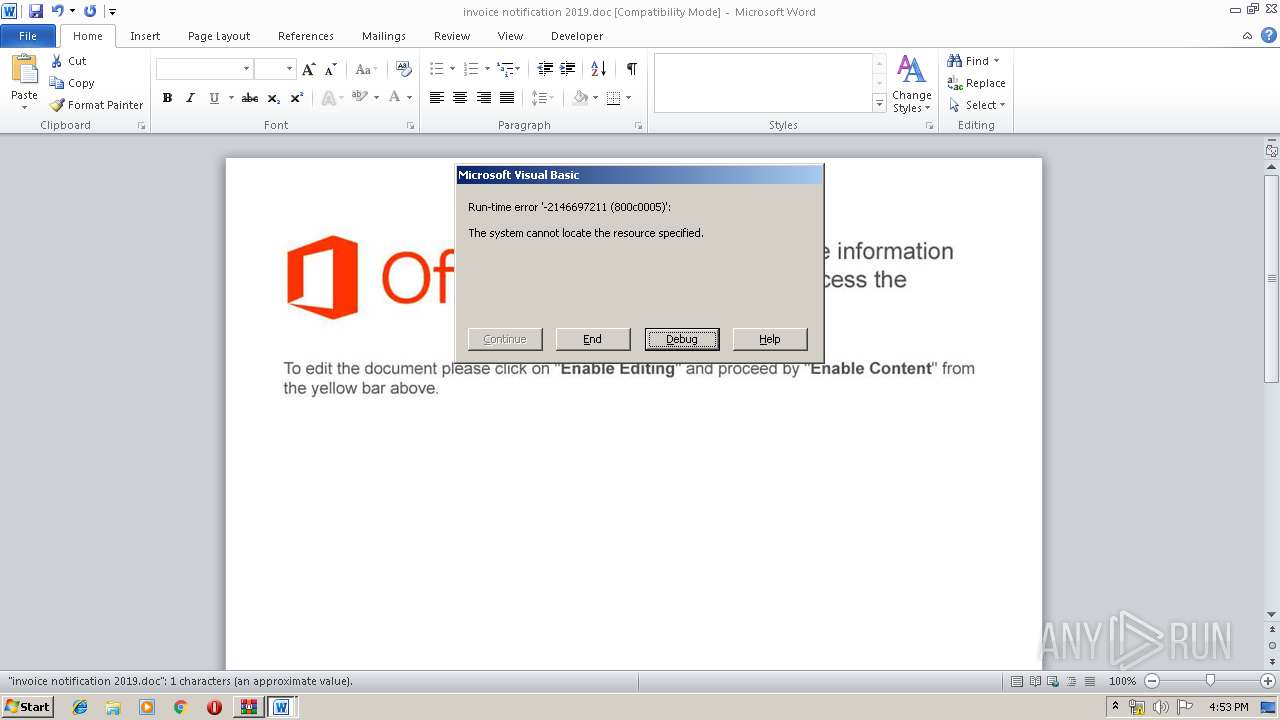
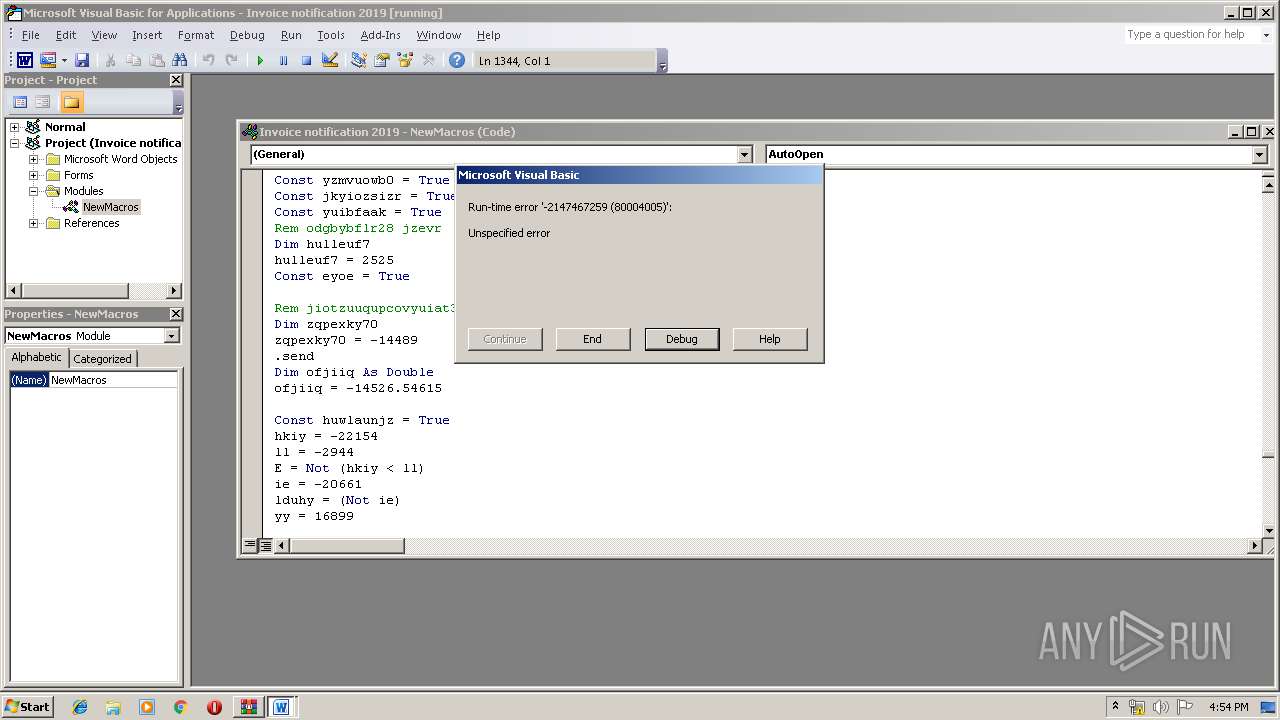
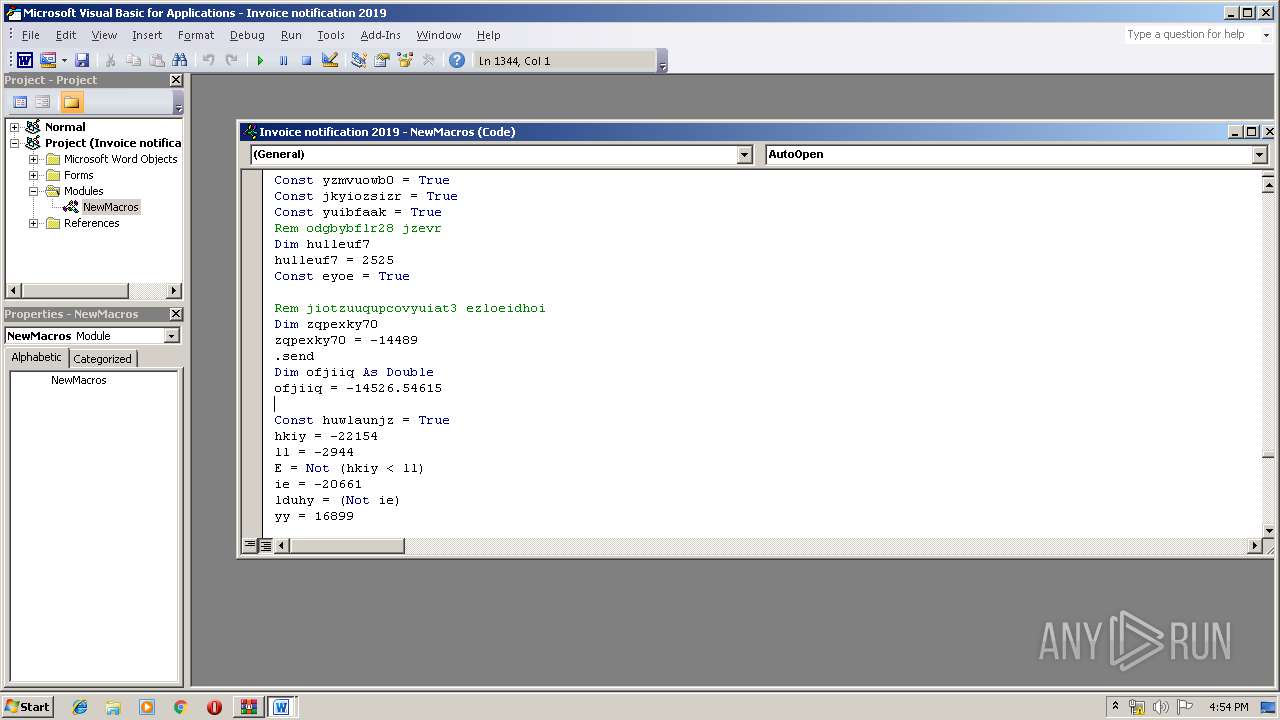
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 15:52:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 39CC38757ABFAB02ACDB0705F587B6DB |
| SHA1: | E8B97C3FFB1A7FBFF72A04468C7E94D2929343C3 |
| SHA256: | E9440422F51B1DC00BC9A8164C9DE32146FB22A28EE50E56805405BC3D510A3A |
| SSDEEP: | 1536:VOEFXDWWTidMIYGmJ2owpnLS8iiywz4gph9SU2Ig3:9DWKW7YGm8owJ9kwsgph9Fjg3 |
MALICIOUS
No malicious indicators.SUSPICIOUS
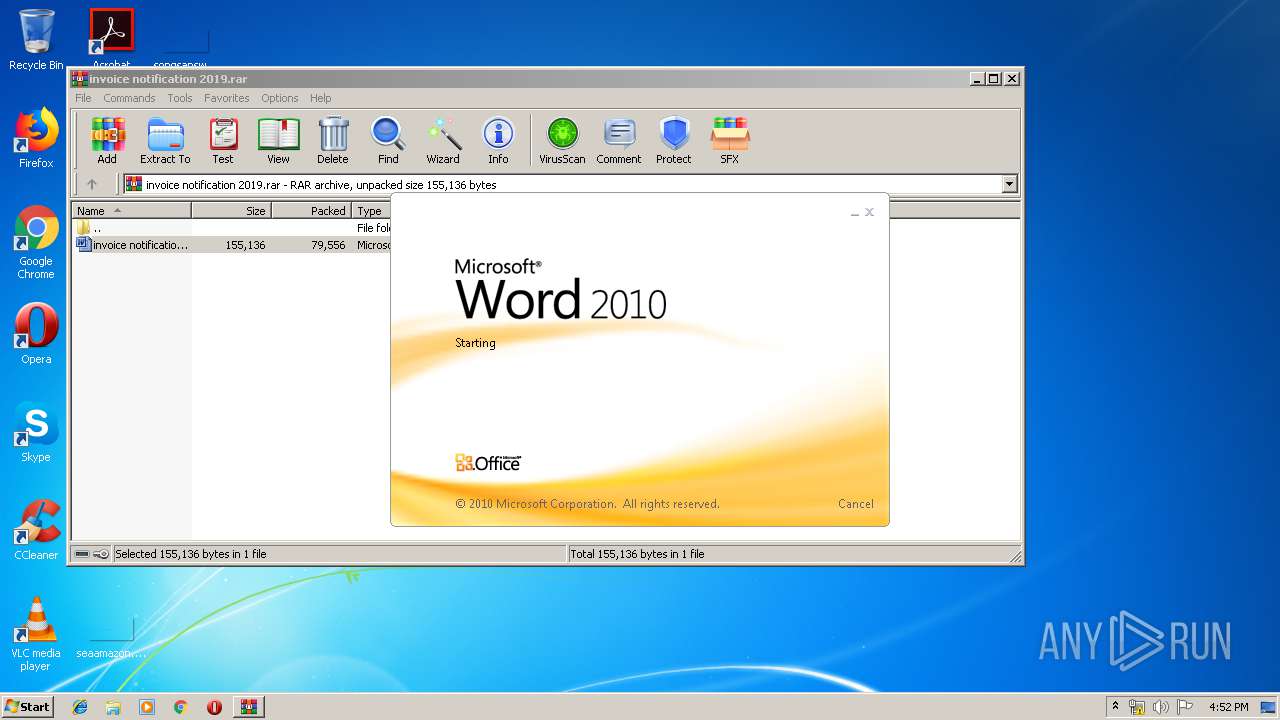
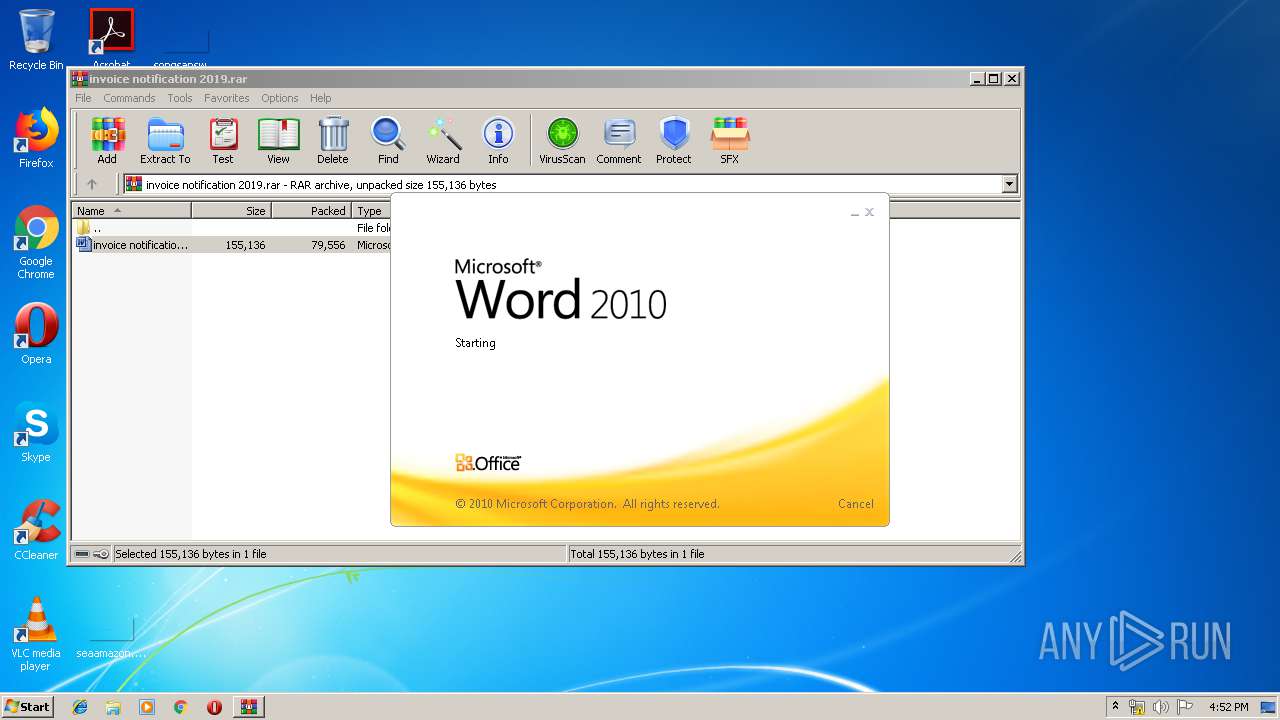
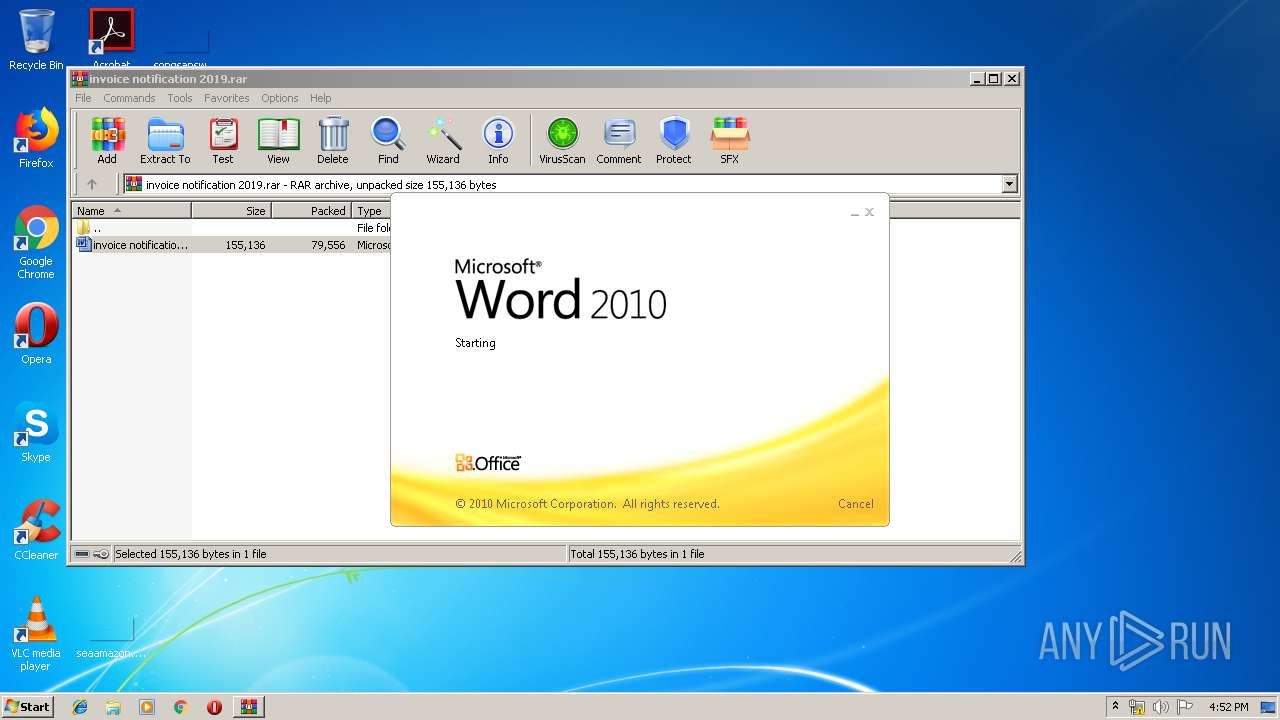
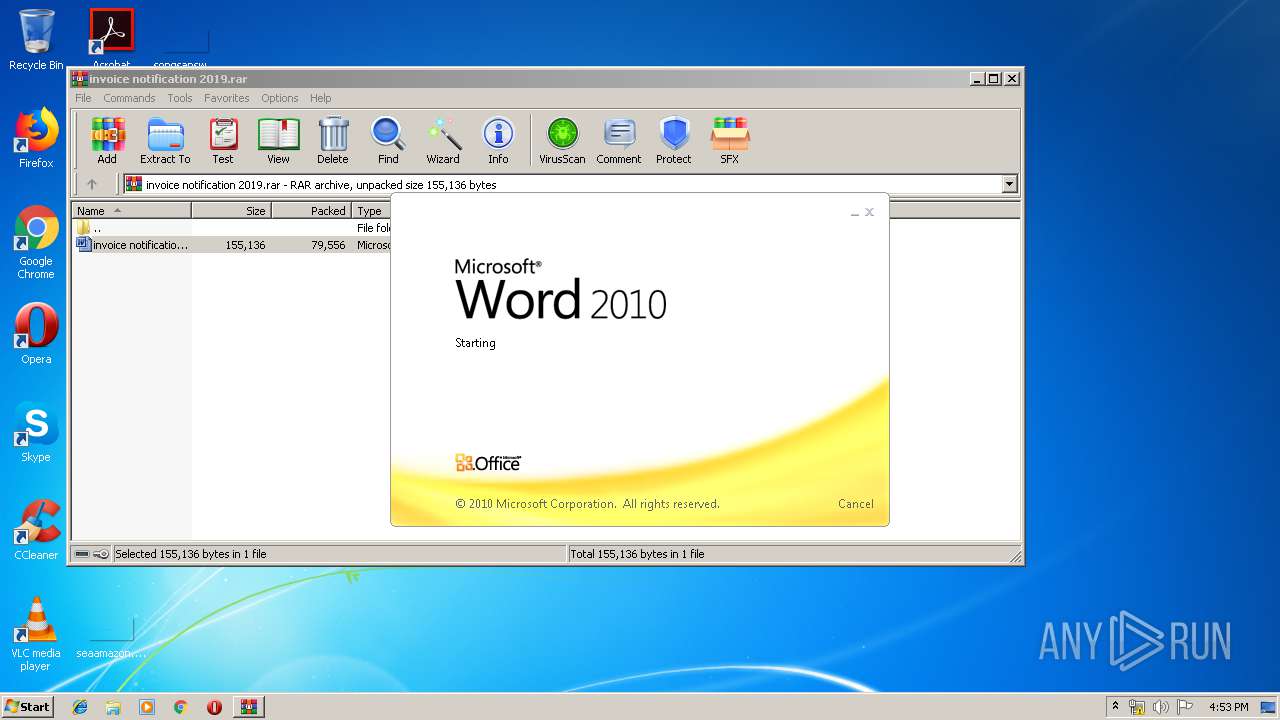
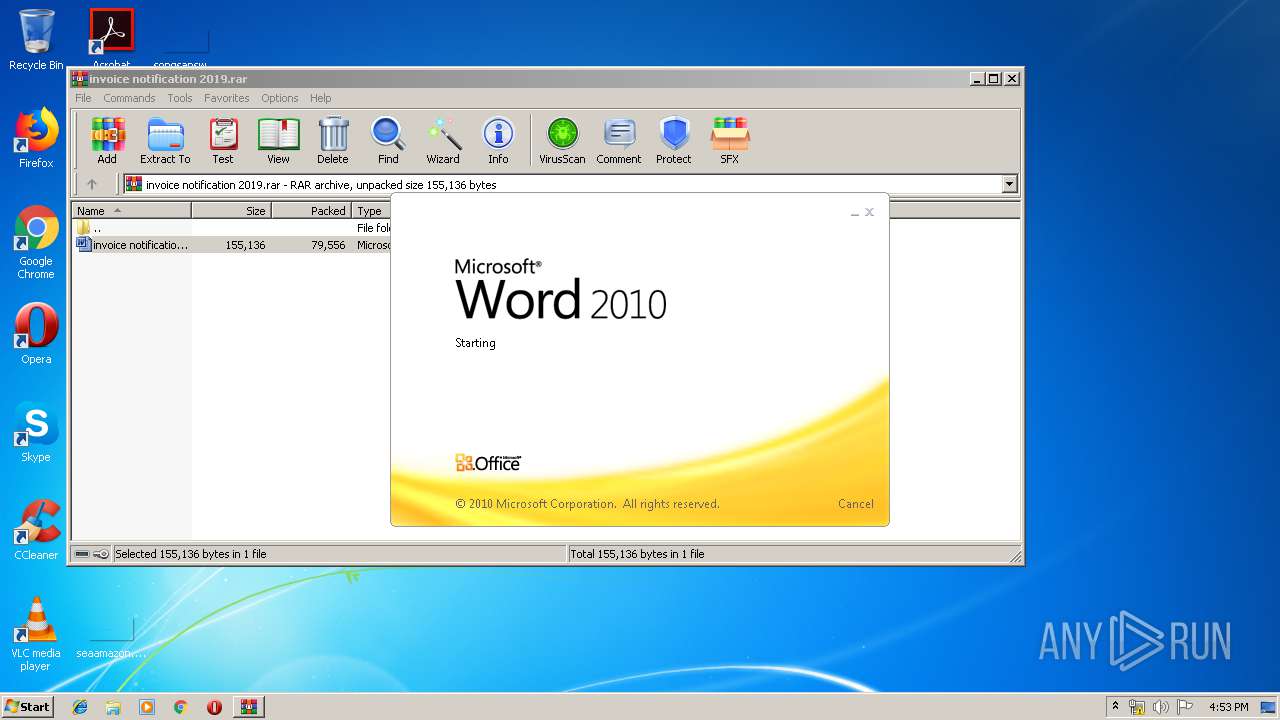
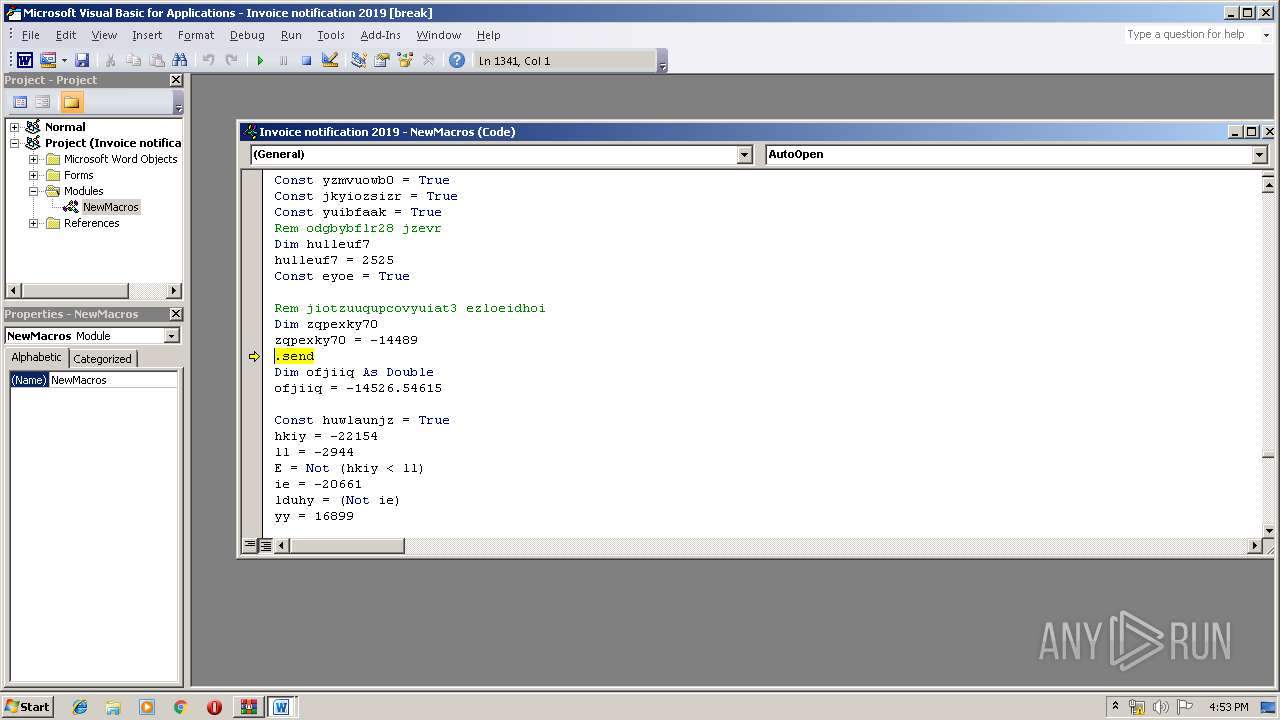
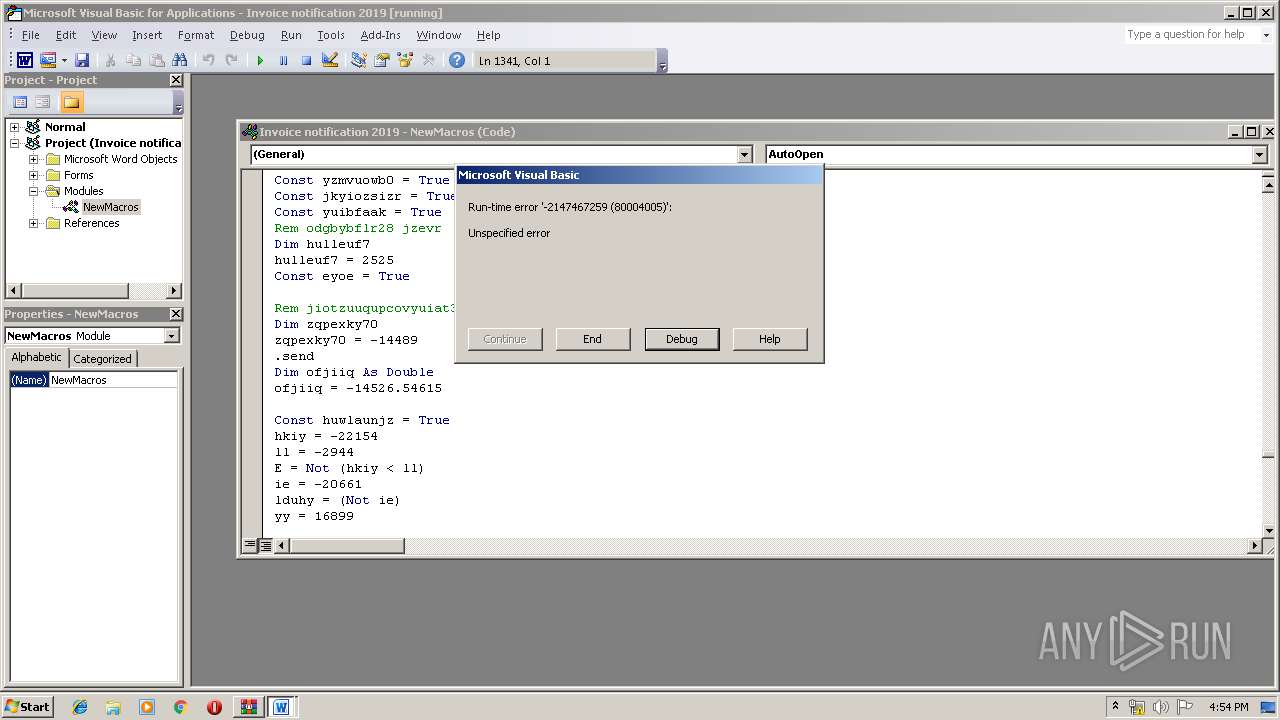
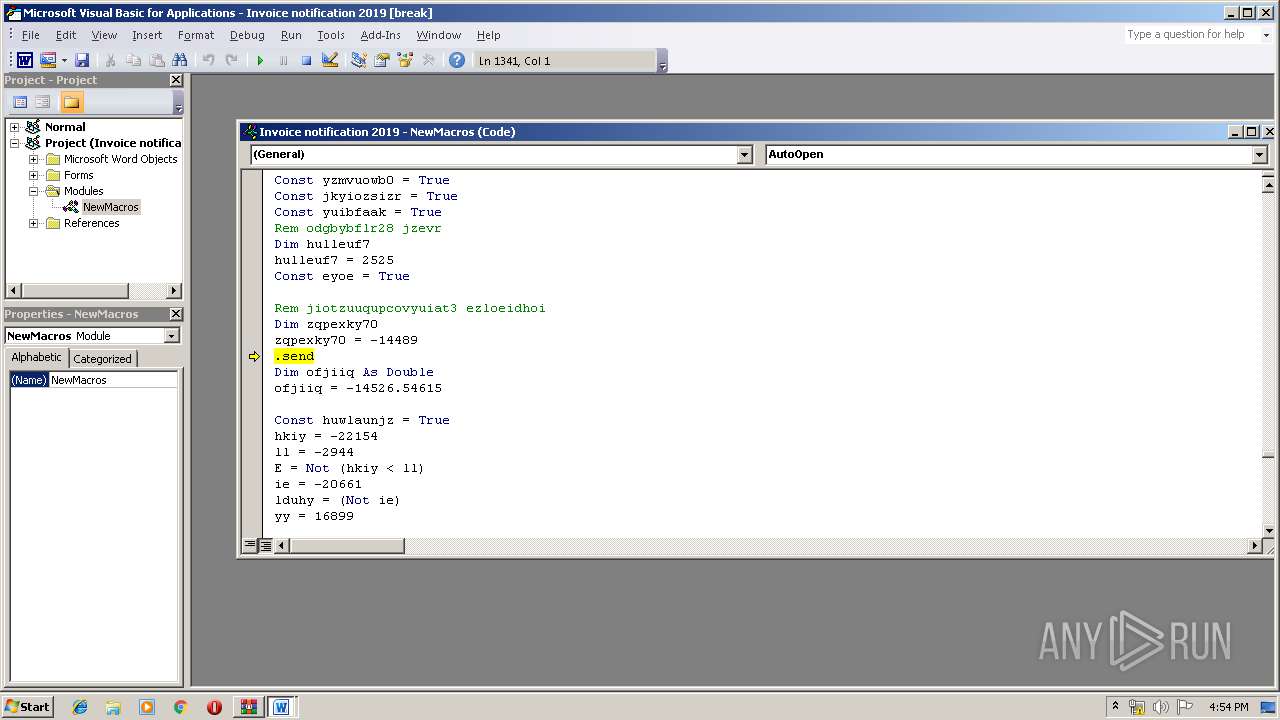
Starts Microsoft Office Application
- WinRAR.exe (PID: 3532)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 1008)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
34
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
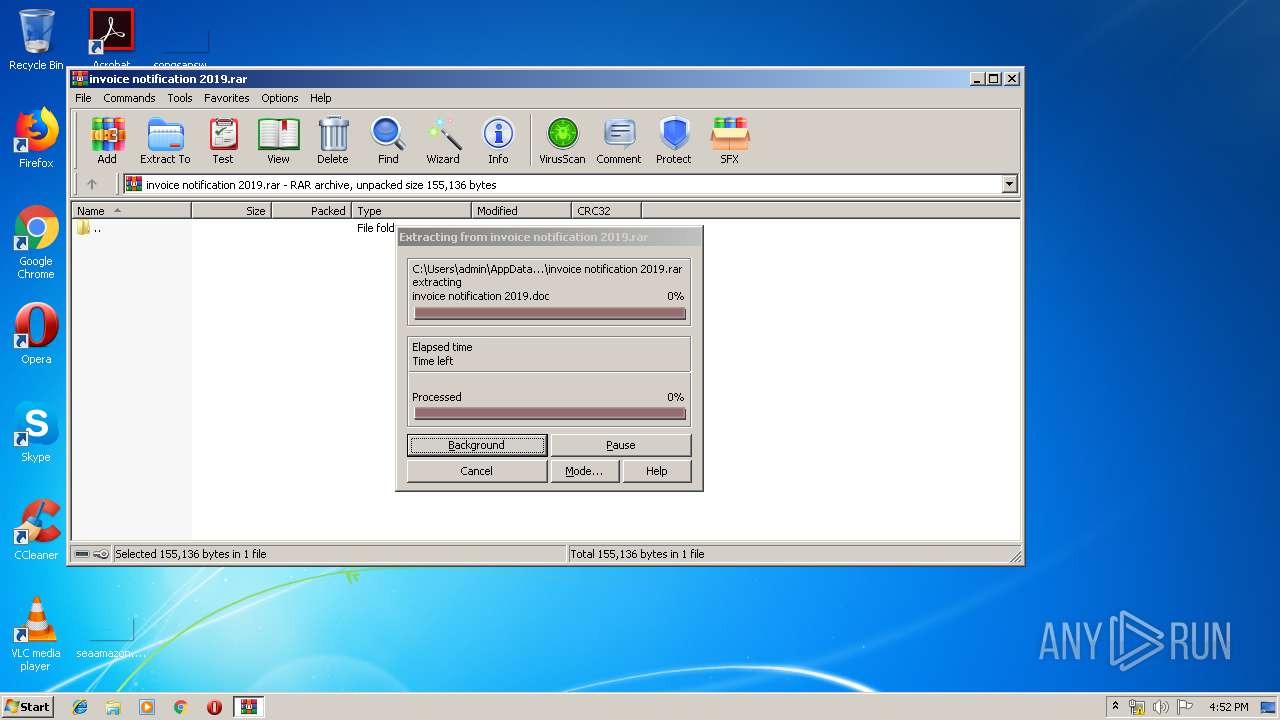
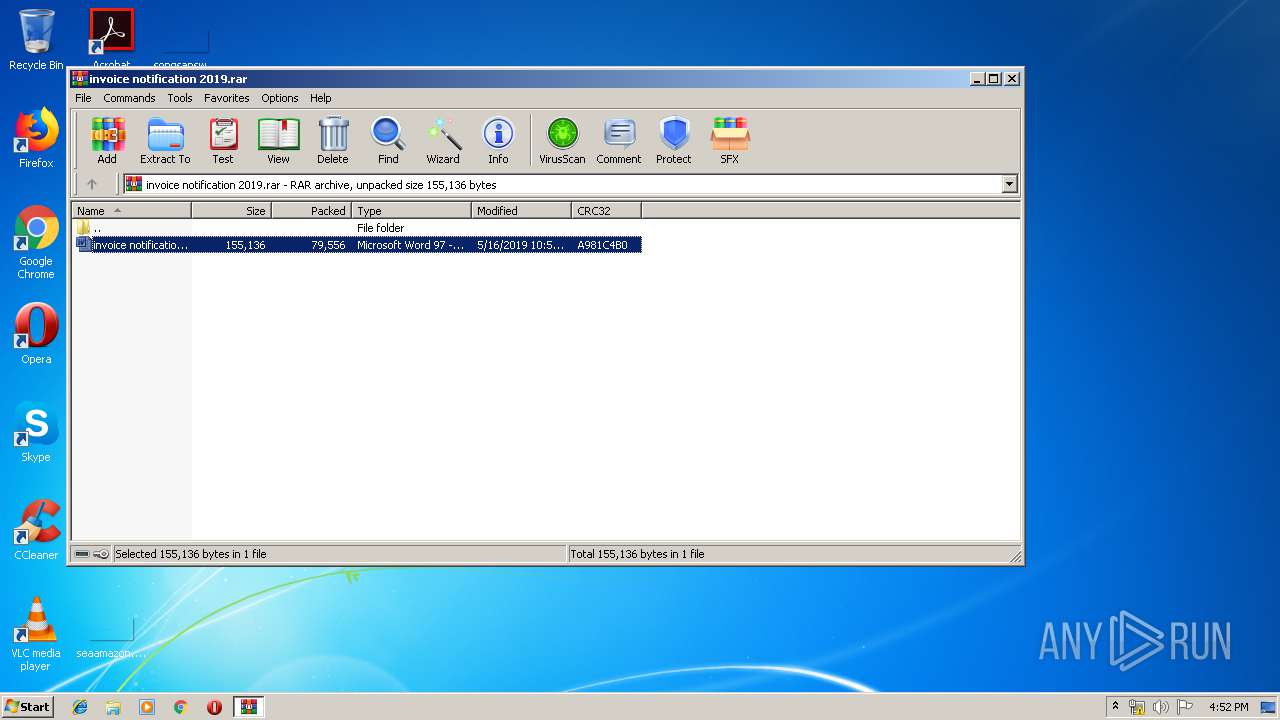
| 1008 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIa3532.7086\invoice notification 2019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3532 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\invoice notification 2019.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
1 551
Read events
1 211
Write events
335
Delete events
5
Modification events
| (PID) Process: | (3532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3532) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\invoice notification 2019.rar | |||
| (PID) Process: | (3532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3532) WinRAR.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1320419358 | |||
| (PID) Process: | (1008) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | %v6 |
Value: 25763600F0030000010000000000000000000000 | |||
Executable files
0
Suspicious files
1
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1008 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR12A5.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1008 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Rar$DIa3532.7086\~$voice notification 2019.doc | pgc | |
MD5:— | SHA256:— | |||
| 1008 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3532 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa3532.7086\invoice notification 2019.doc | document | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
3
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1008 | WINWORD.EXE | 47.245.58.124:443 | kentona.su | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
kentona.su |
| malicious |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |