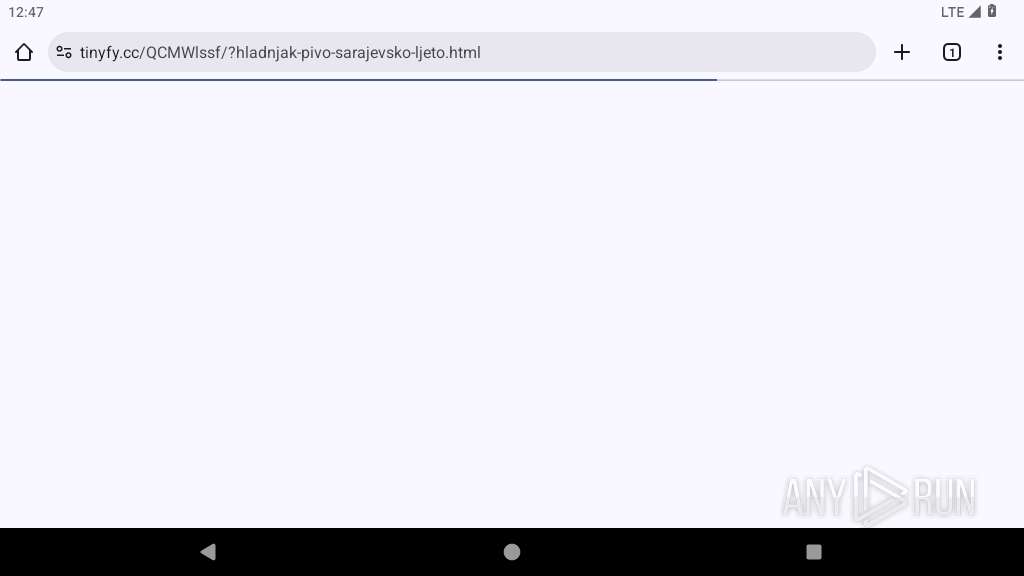
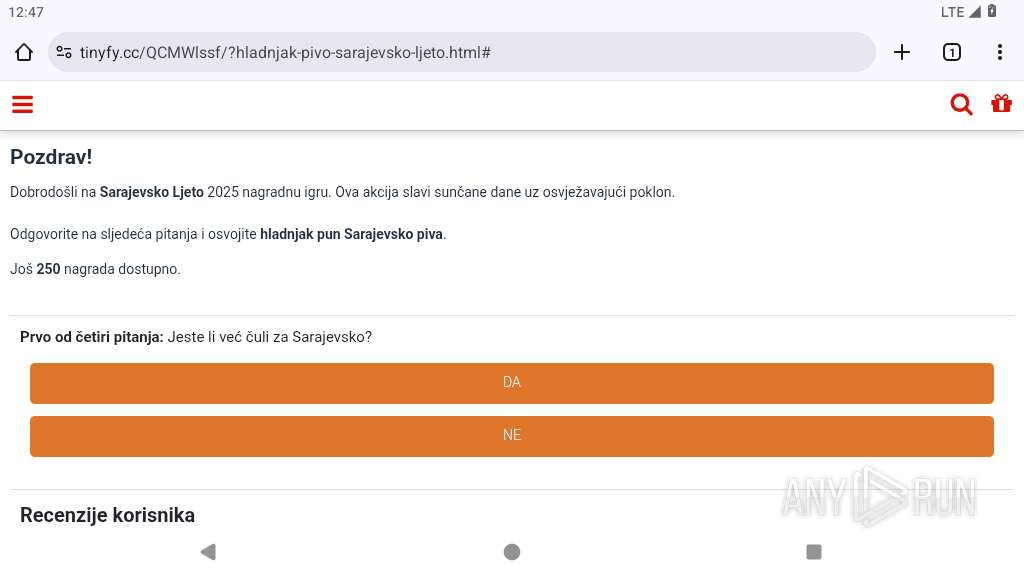
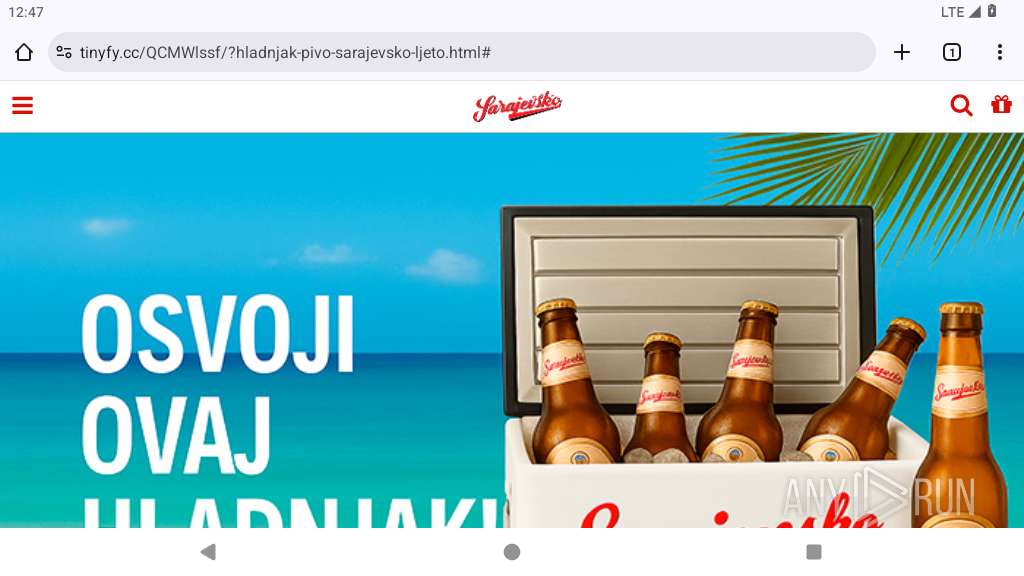
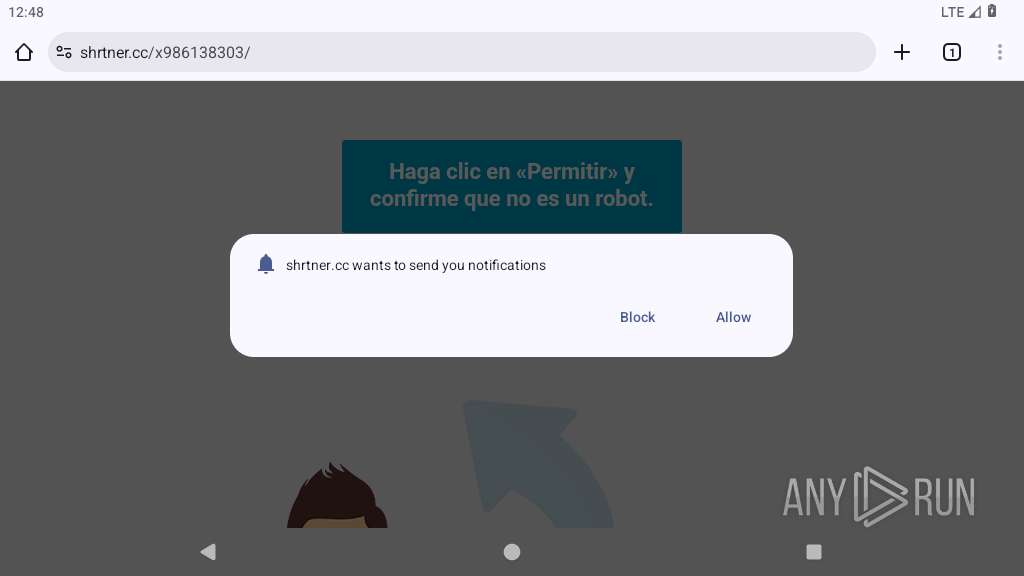
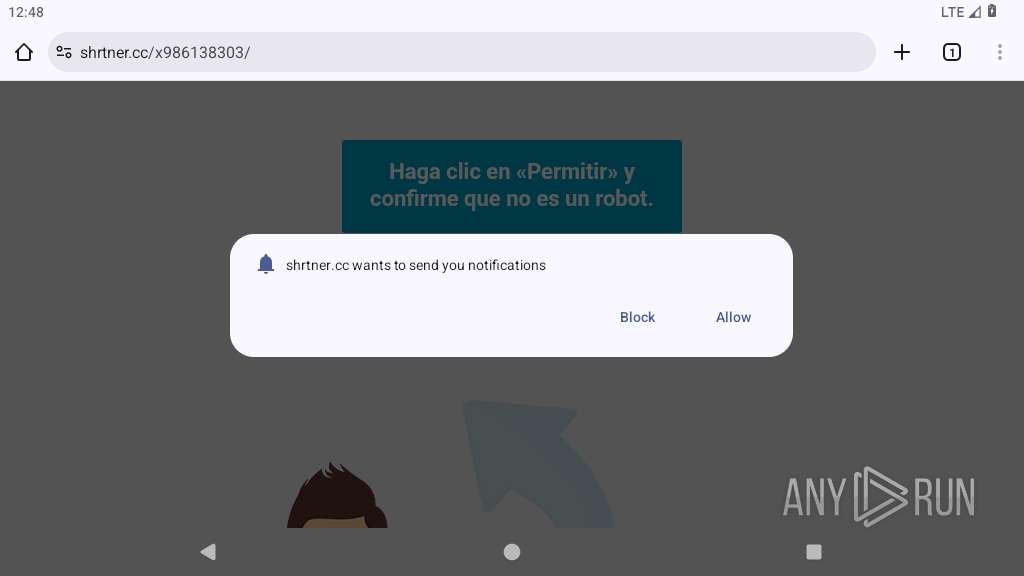
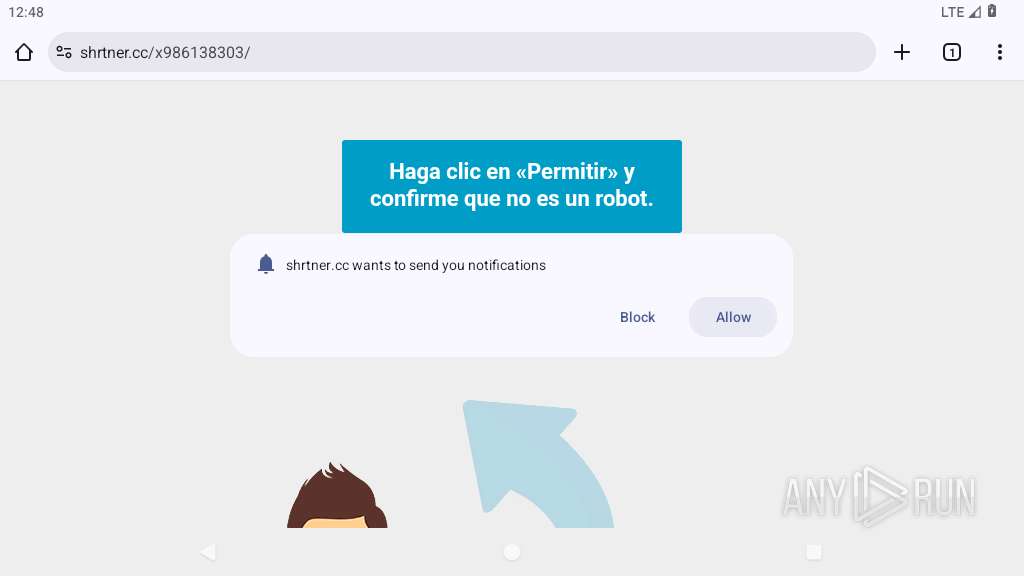
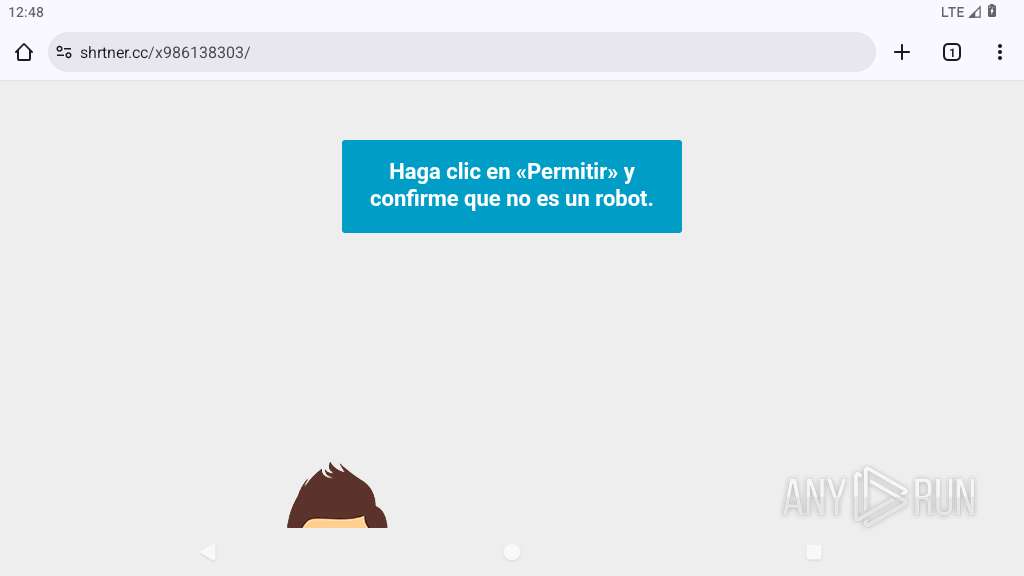
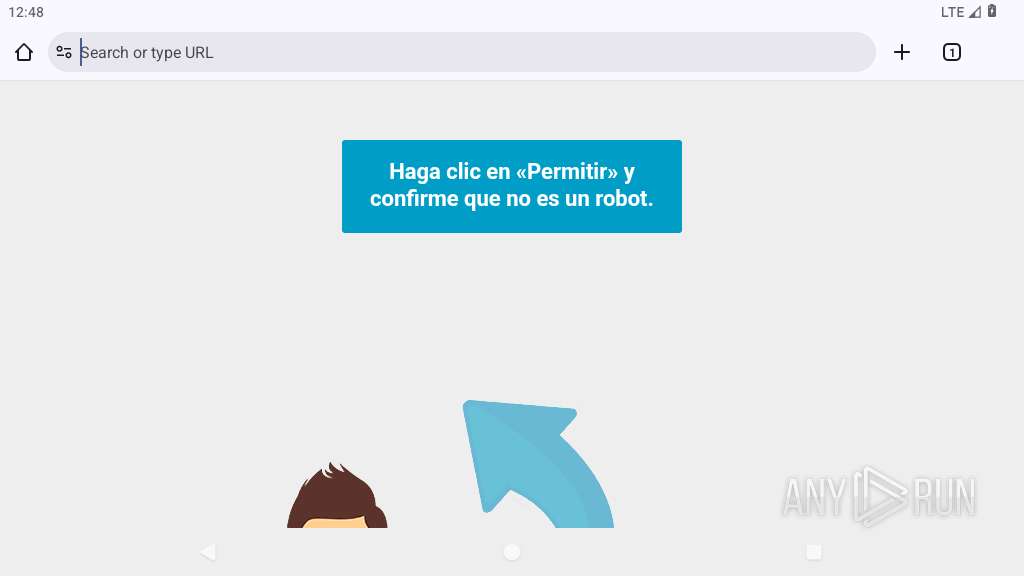
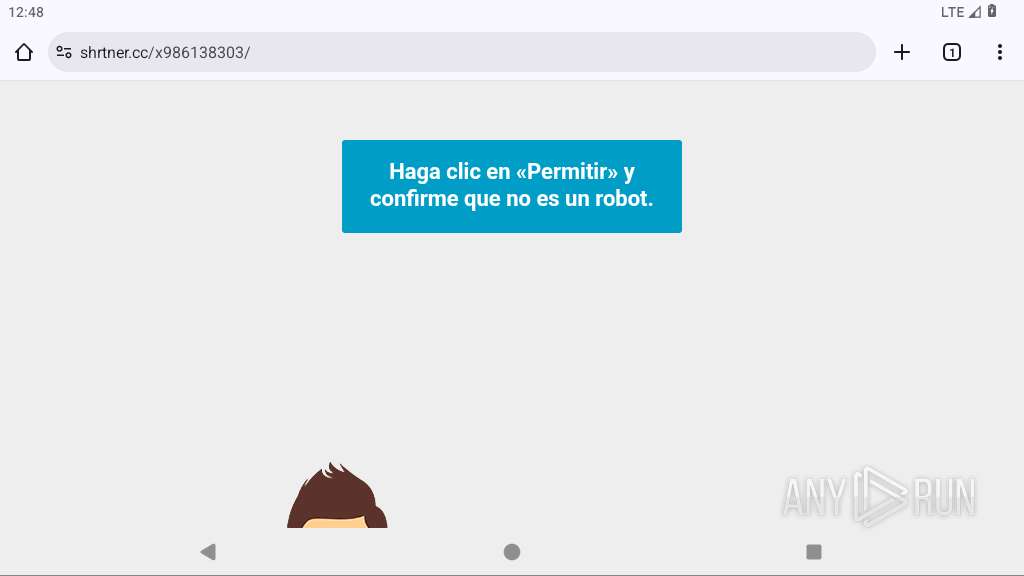
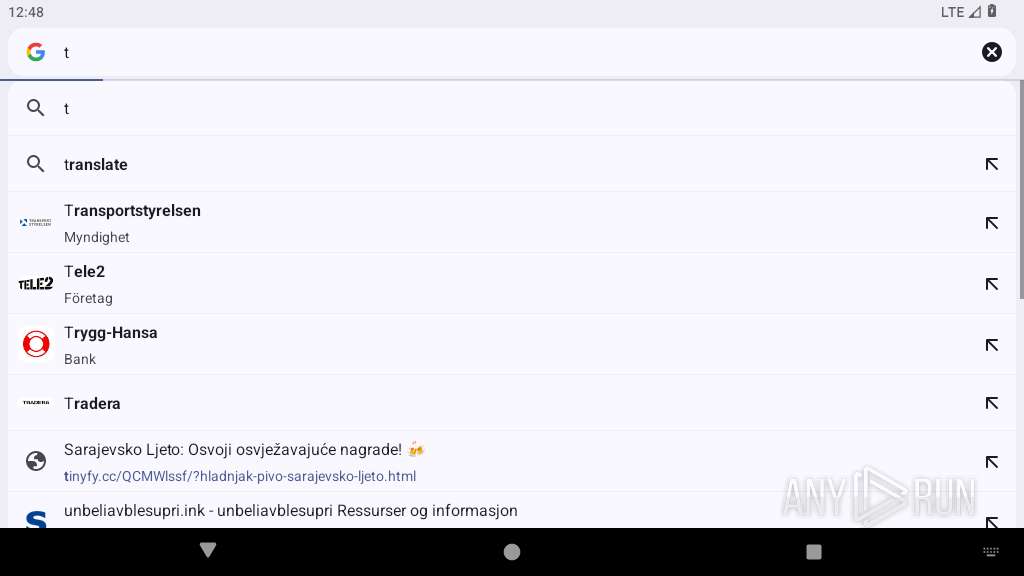
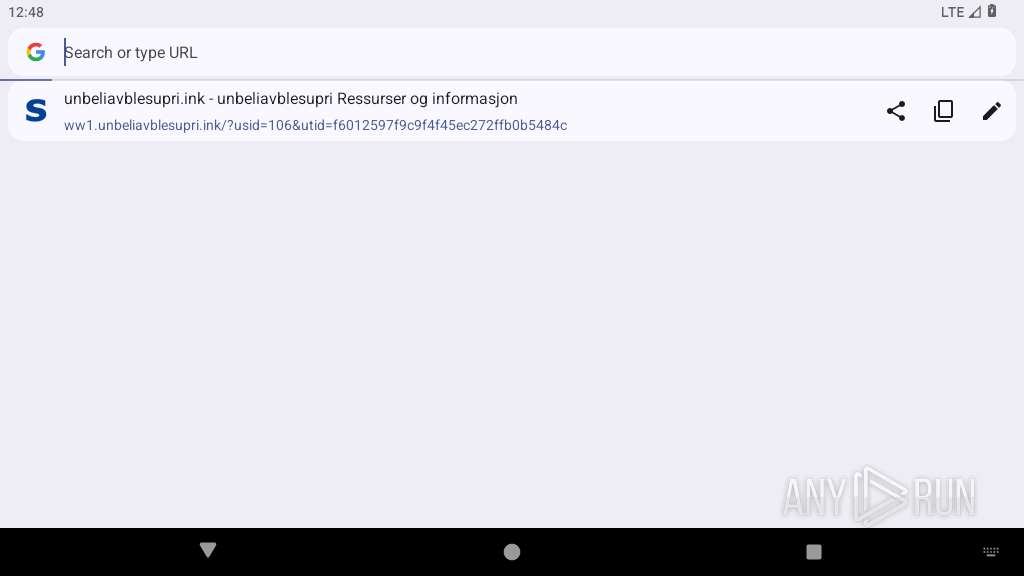
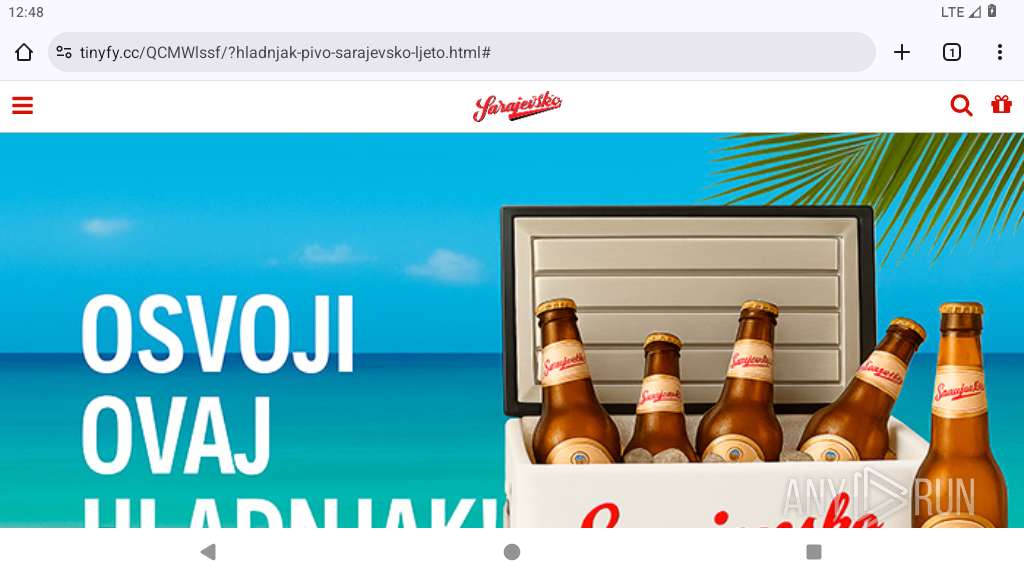
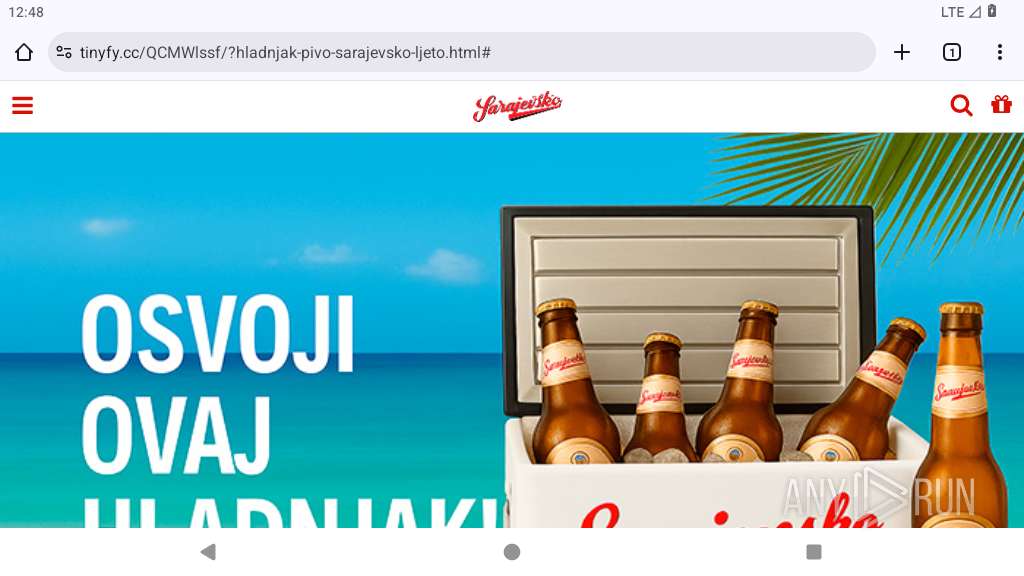
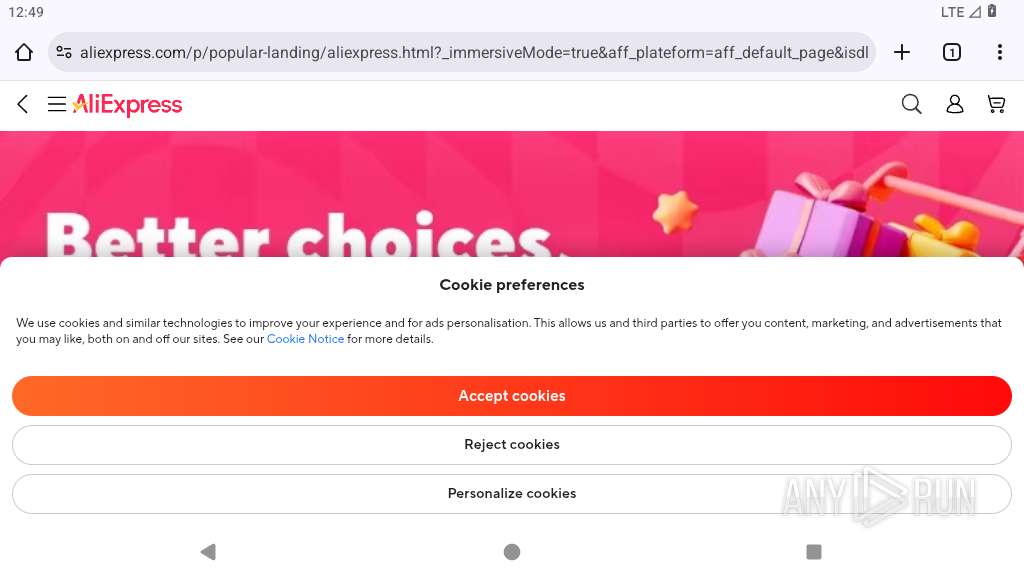
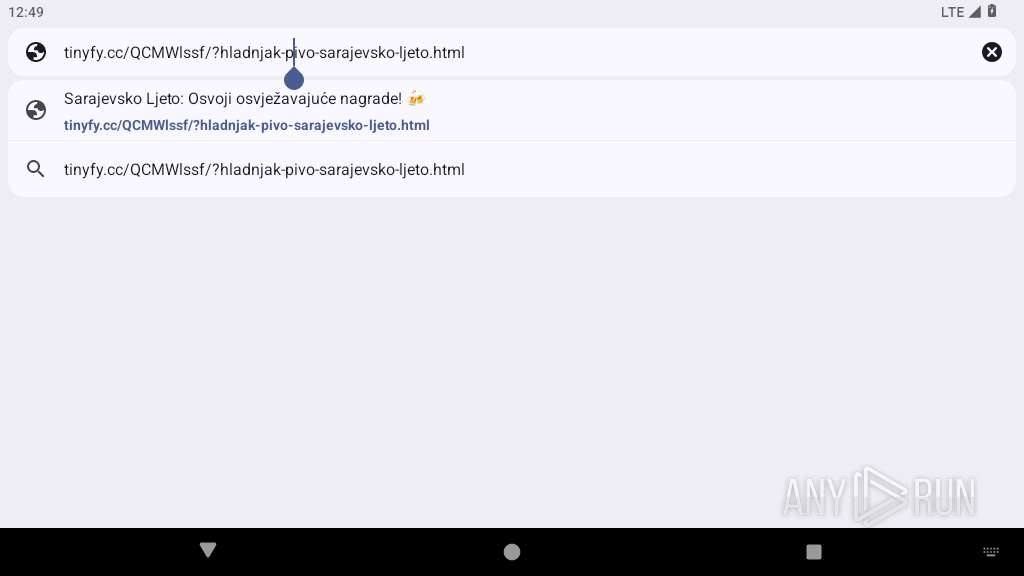
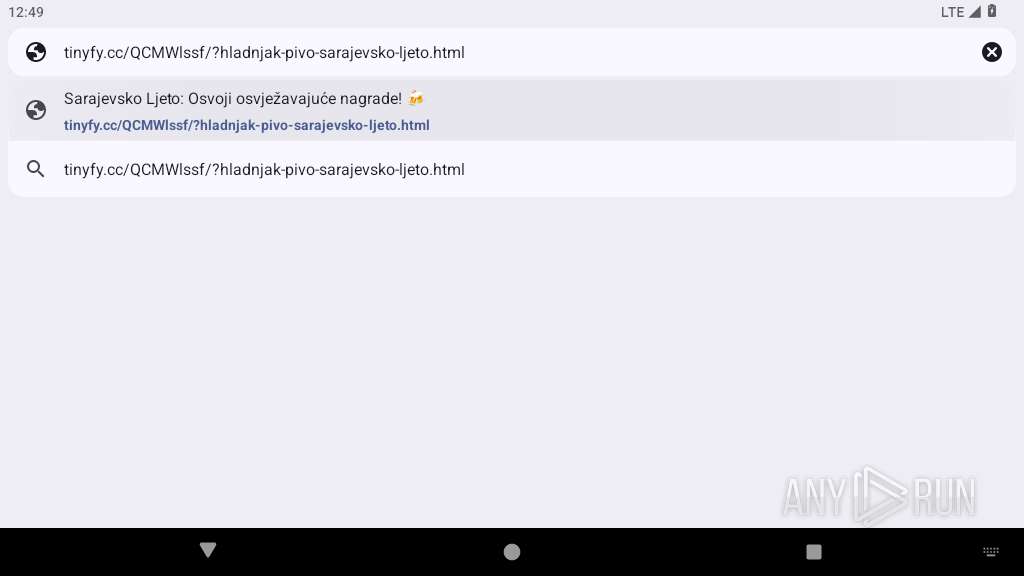
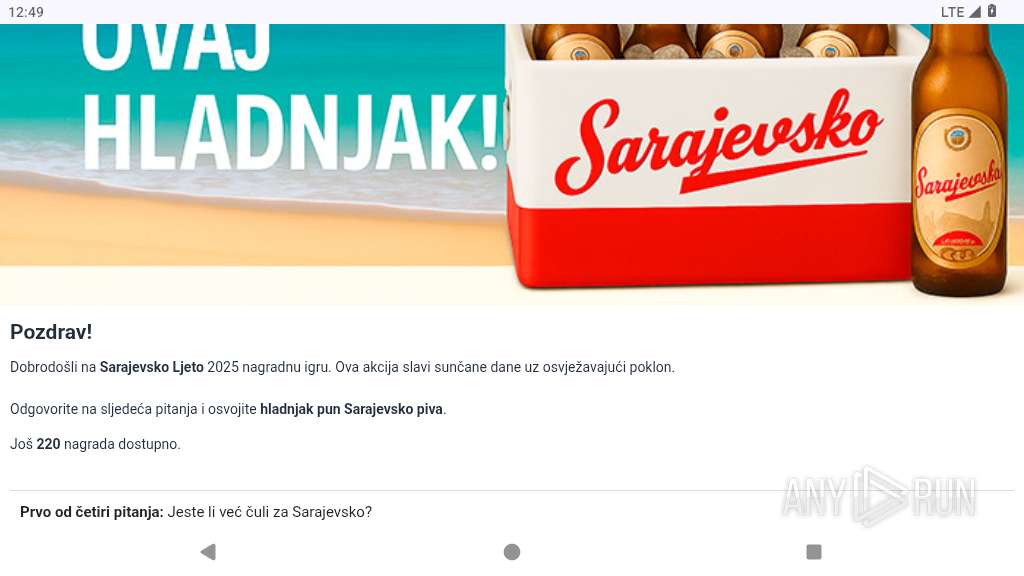
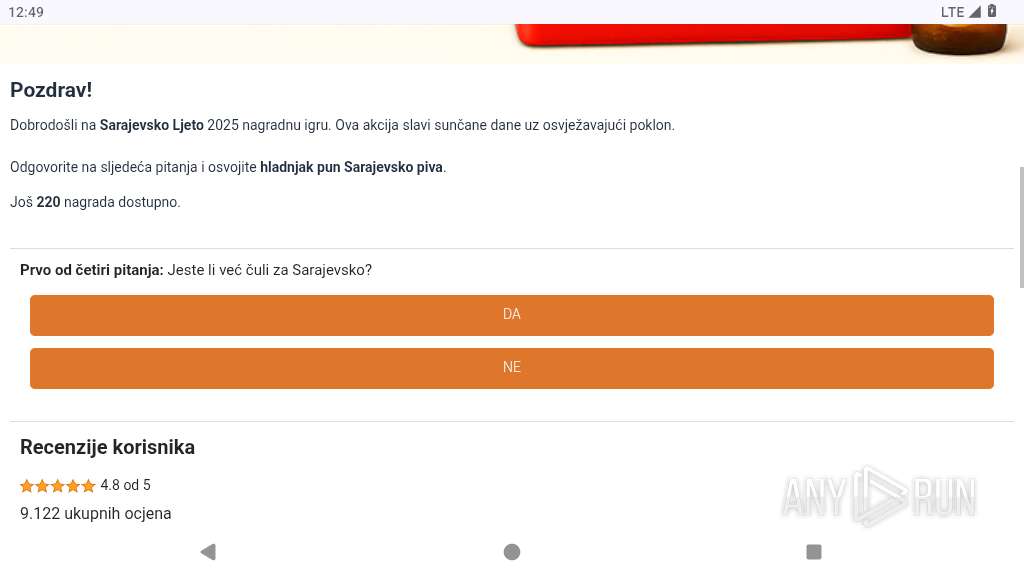
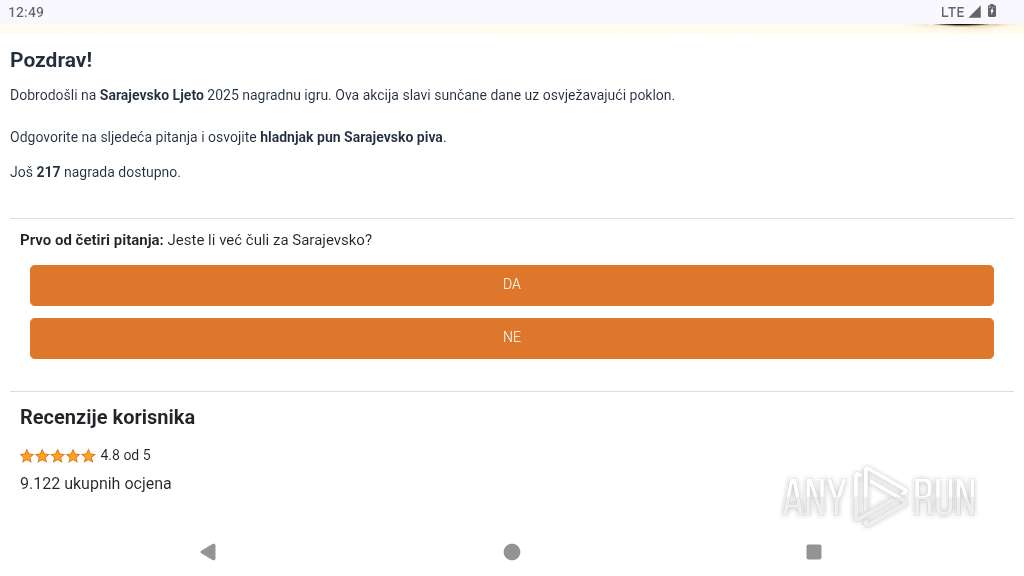
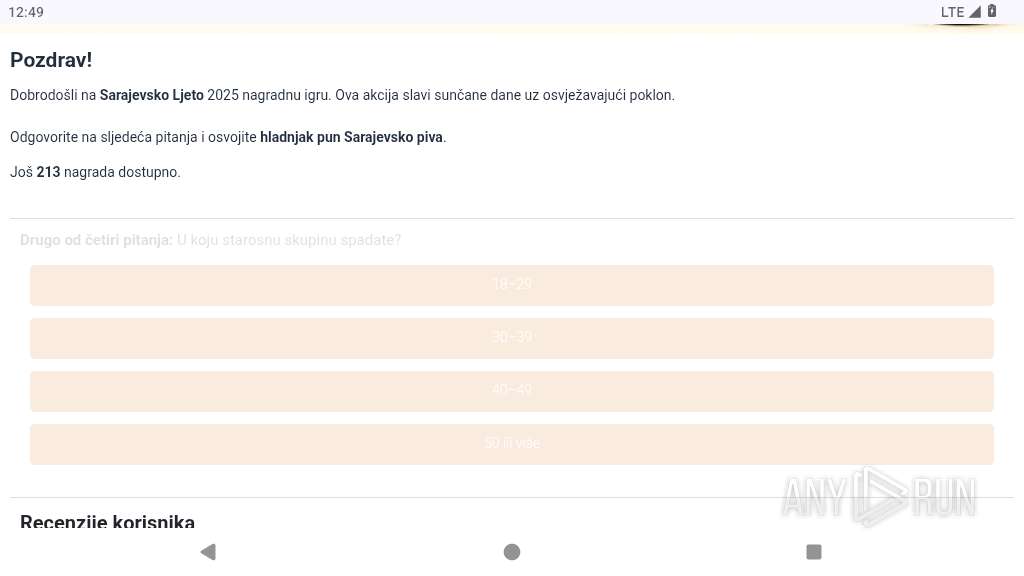
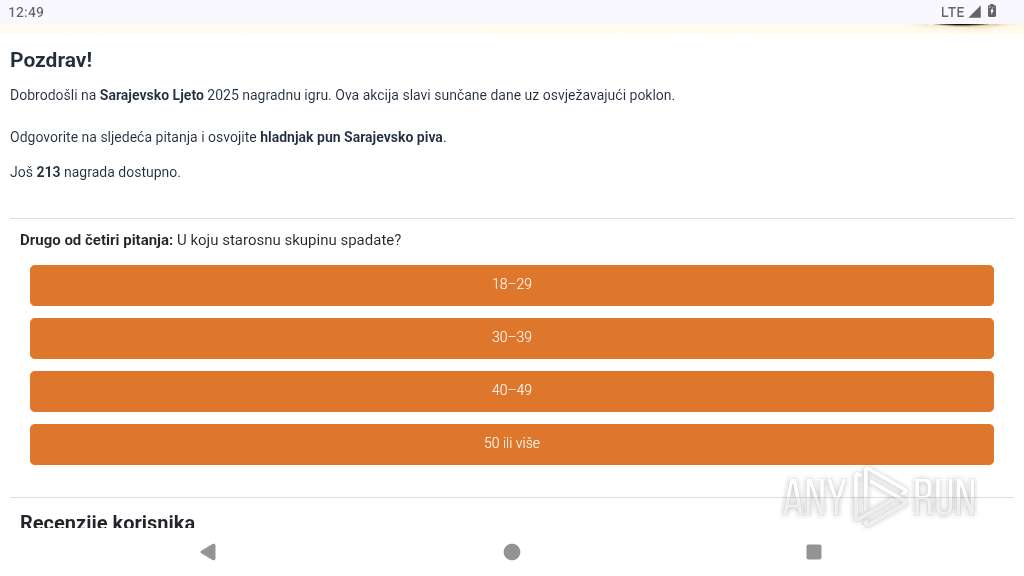
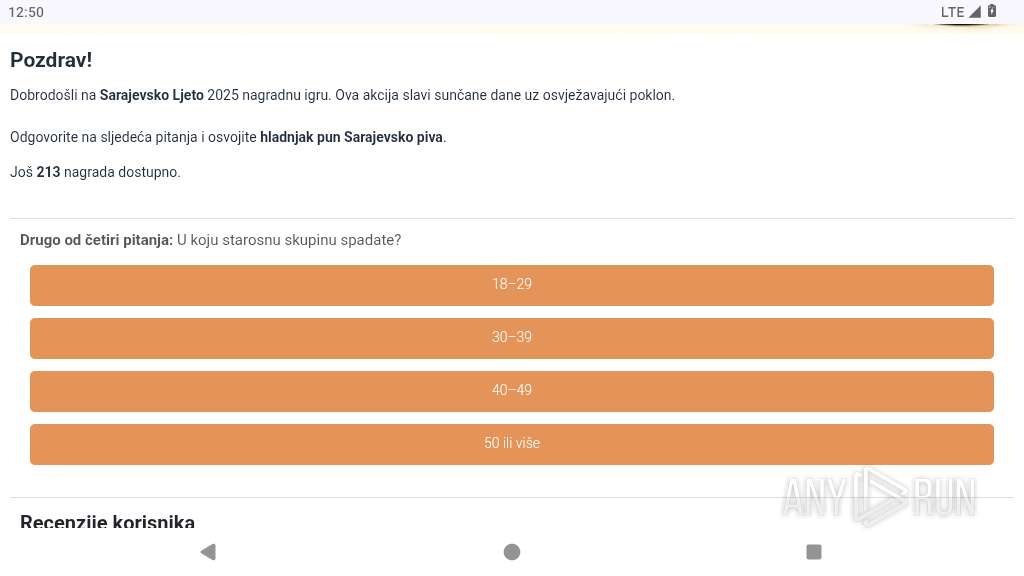
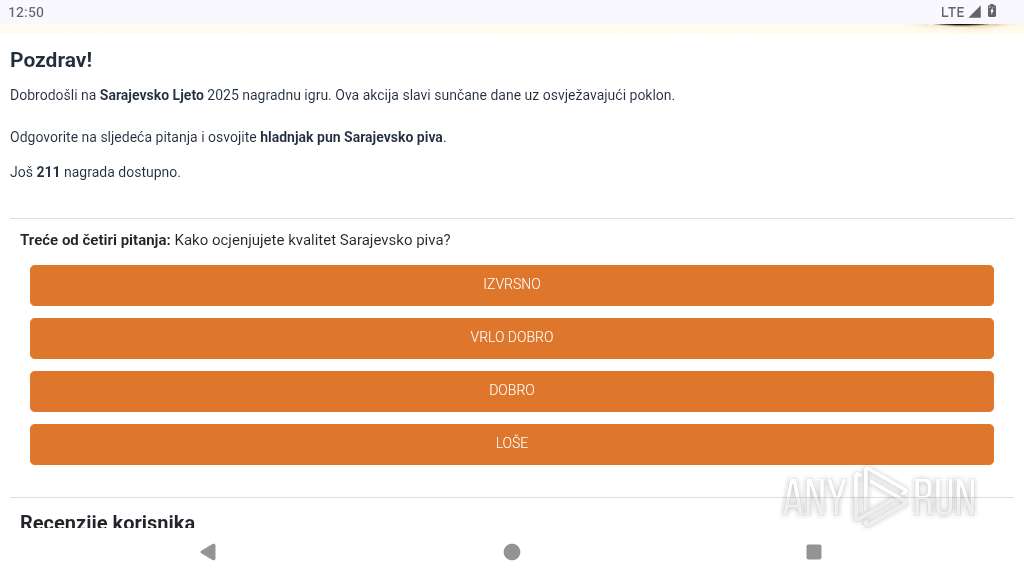
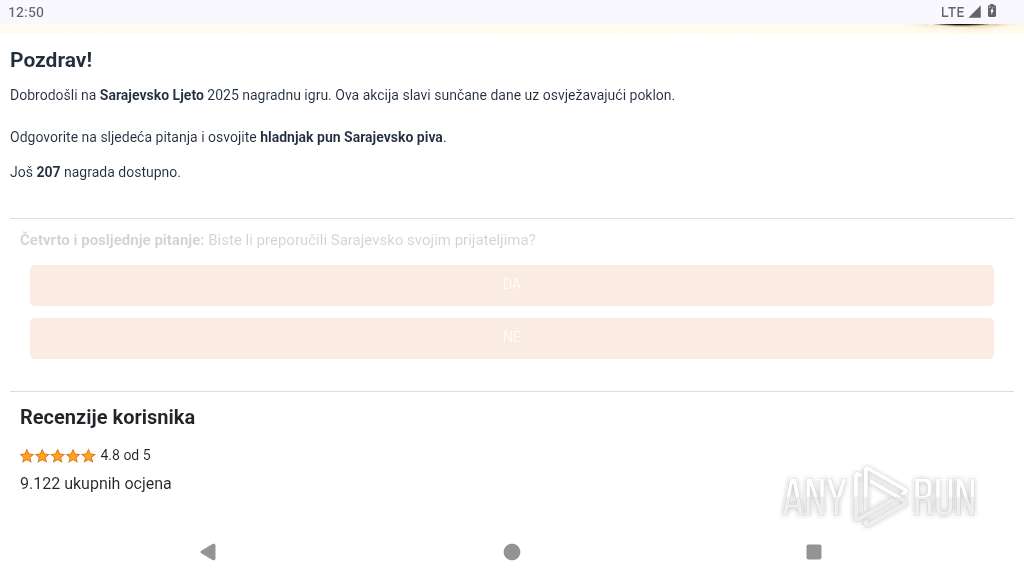
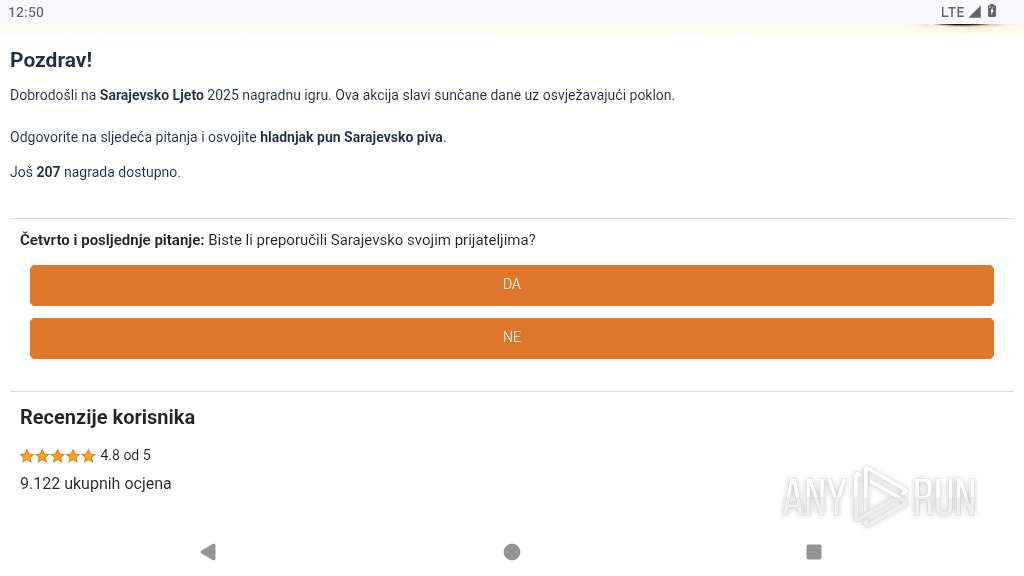
| URL: | tinyfy.cc/QCMWlssf/?hladnjak-pivo-sarajevsko-ljeto.html |
| Full analysis: | https://app.any.run/tasks/0b984d04-5eaa-4d4b-a7fa-c920aa3823c9 |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2025, 12:46:58 |
| OS: | Android 14 |
| Tags: | |
| Indicators: | |
| MD5: | DDBFD7F3BCC64E318B0D280EB673E4D1 |
| SHA1: | 2C8A4054834E88959356F073DE687EB5B1B2FF62 |
| SHA256: | E932F4196280D21B837E3E30C8080AE4DAF36BFEEB81447A3D45292C6AAED588 |
| SSDEEP: | 3:uyGvfy7dbWf1KQX3aiLQ:uyjif1yf |
MALICIOUS
PHISHING has been detected (SURICATA)
- app_process64 (PID: 2219)
SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
146
Monitored processes
23
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2219 | org.chromium.chrome | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2260 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2270 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a73 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2312 | <pre-initialized> | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2333 | com.android.adservices.api | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2384 | com.android.traceur | /system/bin/app_process64 | — | app_process64 |
User: u0_a54 Integrity Level: UNKNOWN Exit code: 512 | ||||
| 2406 | com.android.providers.partnerbookmarks | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2423 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a73 Integrity Level: UNKNOWN Exit code: 9 | ||||
| 2475 | /system/bin/dmesgd | /system/bin/dmesgd | — | init |
User: dmesgd Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2476 | dmesg | /system/bin/toybox | — | dmesgd |
User: dmesgd Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
3
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2480 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.32wZBT/manifest.json | binary | |
MD5:— | SHA256:— | |||
| 2480 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.32wZBT/_metadata/verified_contents.json | ini | |
MD5:— | SHA256:— | |||
| 2480 | app_process64 | /data/data/org.chromium.chrome/app_chrome/component_crx_cache/2638e3c2d1fa1d417bfdc31dd21bc938f106d3b436a6488b41b014ca9e2b7541 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
118
DNS requests
156
Threats
179
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 142.250.185.99:80 | http://connectivitycheck.gstatic.com/generate_204 | unknown | — | — | whitelisted |
2219 | app_process64 | GET | 200 | 172.217.16.206:80 | http://clients2.google.com/time/1/current?cup2key=9:VIX-c1Ema1ixN35nSVAnDPFEyRZH7vccrfiqXFNPhYg&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2219 | app_process64 | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
451 | mdnsd | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 216.239.35.12:123 | time.android.com | — | — | whitelisted |
— | — | 142.250.185.99:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
— | — | 142.250.185.164:443 | www.google.com | GOOGLE | US | whitelisted |
— | — | 108.177.15.81:443 | staging-remoteprovisioning.sandbox.googleapis.com | GOOGLE | US | whitelisted |
2219 | app_process64 | 172.217.16.206:80 | clients2.google.com | GOOGLE | US | whitelisted |
2219 | app_process64 | 142.250.185.164:443 | www.google.com | GOOGLE | US | whitelisted |
2219 | app_process64 | 74.125.133.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
2219 | app_process64 | 104.17.25.14:443 | cdnjs.cloudflare.com | — | — | whitelisted |
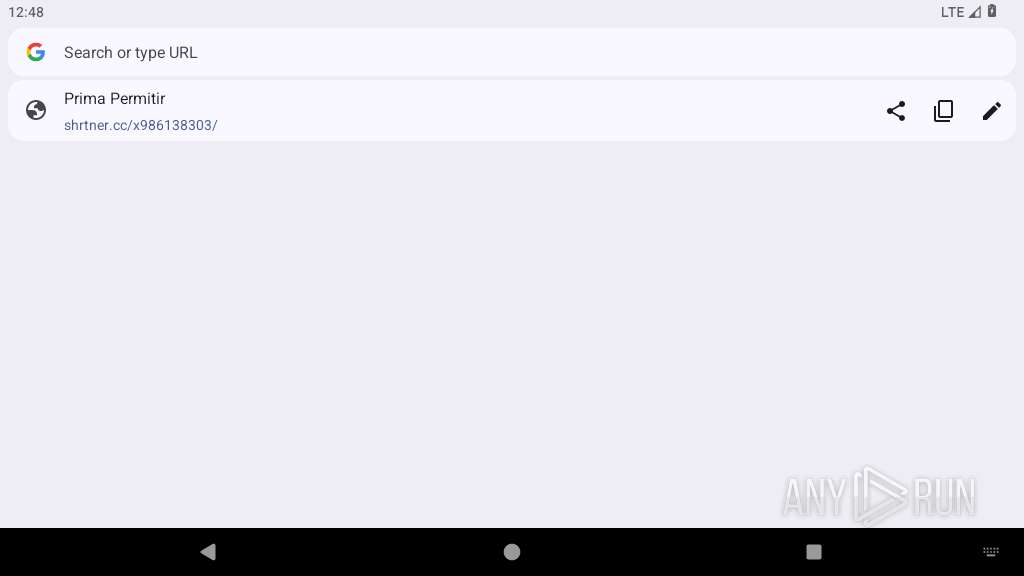
2219 | app_process64 | 188.114.96.3:443 | tinyfy.cc | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivitycheck.gstatic.com |
| whitelisted |
www.google.com |
| whitelisted |
google.com |
| whitelisted |
time.android.com |
| whitelisted |
staging-remoteprovisioning.sandbox.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
tinyfy.cc |
| unknown |
accounts.google.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Android Device Connectivity Check |
2219 | app_process64 | Potentially Bad Traffic | ET DNS Query for .cc TLD |
2219 | app_process64 | Potentially Bad Traffic | ET DNS Query for .cc TLD |
2219 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2219 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2219 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2219 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2219 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2219 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
2219 | app_process64 | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |