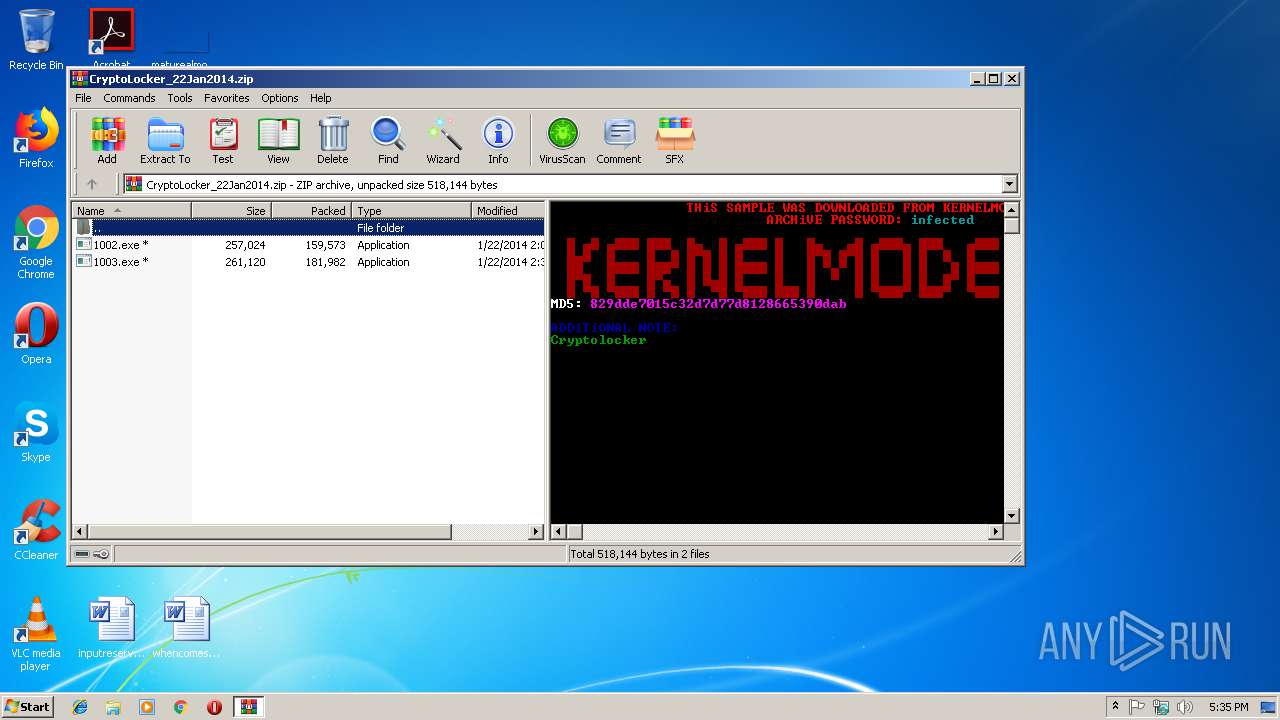
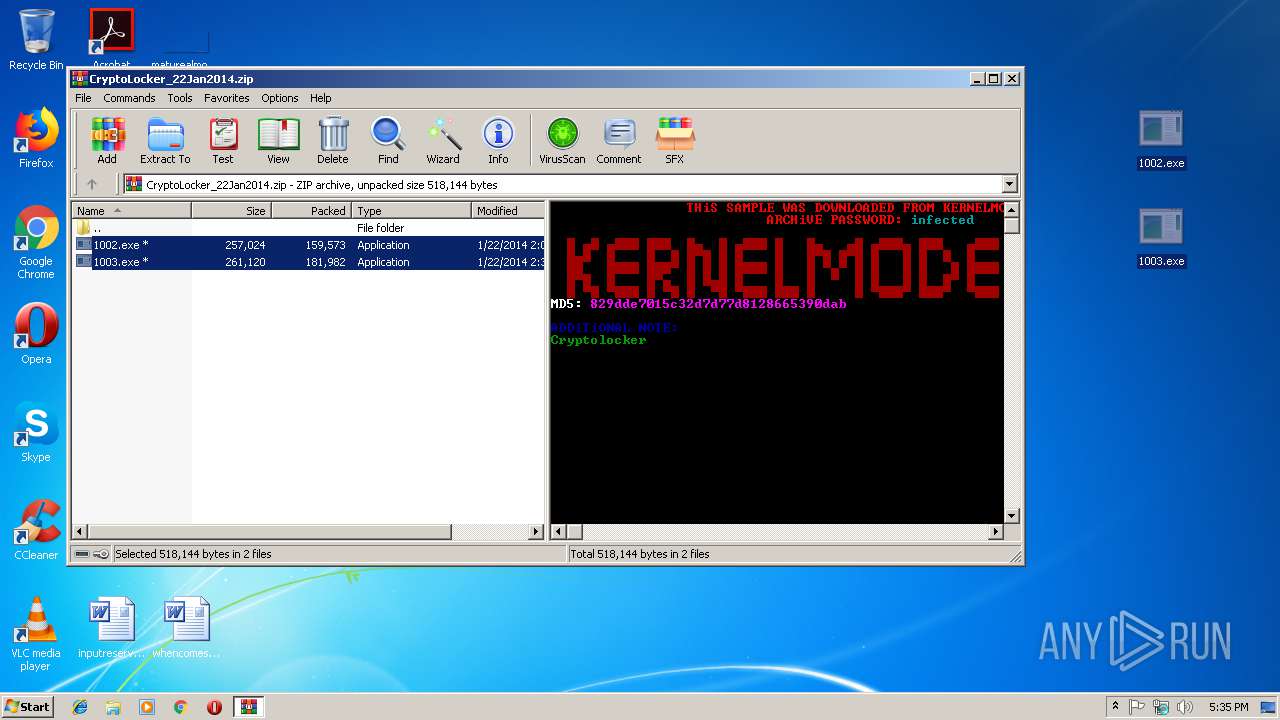
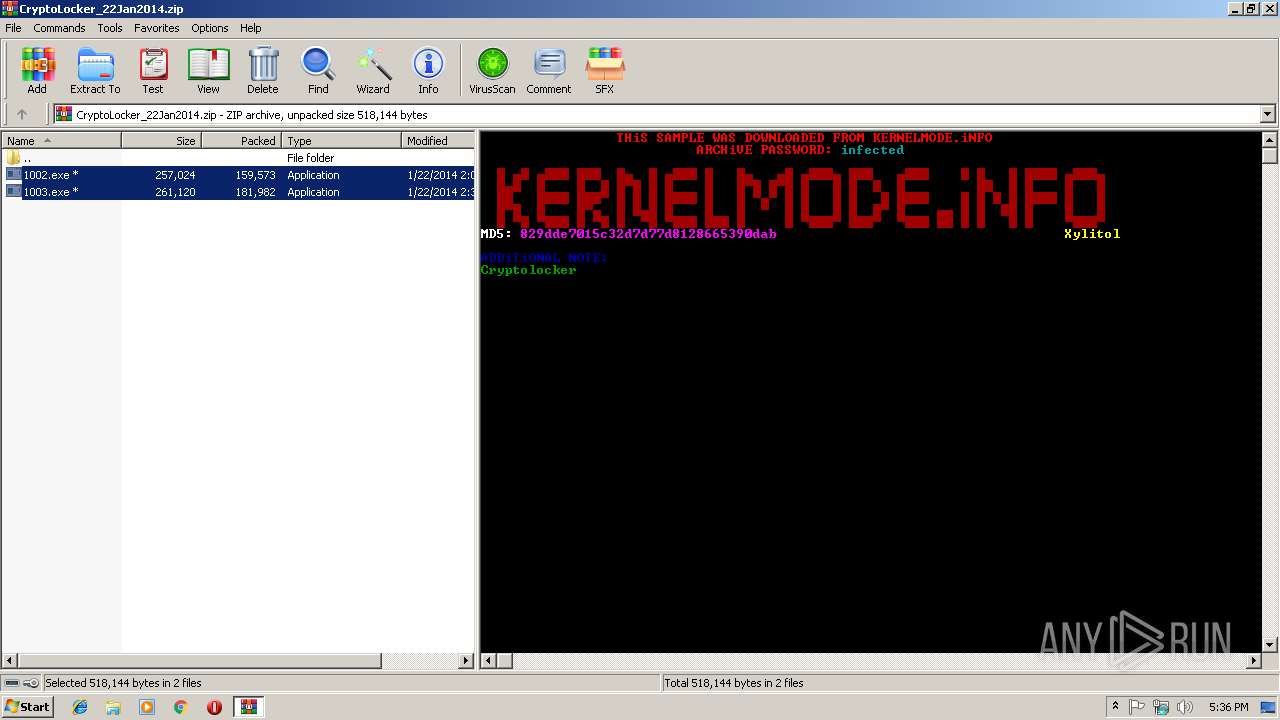
| download: | CryptoLocker_22Jan2014.zip |
| Full analysis: | https://app.any.run/tasks/3635670f-c52e-4765-a933-40825396830e |
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2019, 17:35:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 3C877DFD0D60572BE7C939C08C39866D |
| SHA1: | 07789609B3DFF0B2F2B0ACADC4A57E1C50E9EEA3 |
| SHA256: | E908DCA957B9CB7759FEEABEF0F2921E3CB236368ACC5E124E87AF0492308B14 |
| SSDEEP: | 6144:PSozcLbI3ddbOWmhDSVcblDJkEtQJgadWBGLRJPsMhSLNIPMbKrd1ygGQCcG1CgH:KJLs3dd6WUqcxDvcgad0EcISiP2wo5H |
MALICIOUS
Changes the autorun value in the registry
- 1003.exe (PID: 3396)
- 1003.exe (PID: 3616)
- 1002.exe (PID: 3920)
- 2C28475F30.exe (PID: 2344)
Application was dropped or rewritten from another process
- 1003.exe (PID: 3396)
- 1003.exe (PID: 3616)
- 1002.exe (PID: 3920)
- 2C28475F30.exe (PID: 2344)
SUSPICIOUS
Starts itself from another location
- 1003.exe (PID: 3396)
Executable content was dropped or overwritten
- 1003.exe (PID: 3396)
Uses TASKKILL.EXE to kill process
- 1003.exe (PID: 3396)
Creates files in the user directory
- 1003.exe (PID: 3396)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2014:01:22 15:31:29 |
| ZipCRC: | 0xbbccb18d |
| ZipCompressedSize: | 181982 |
| ZipUncompressedSize: | 261120 |
| ZipFileName: | 1003.exe |
Total processes
38
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
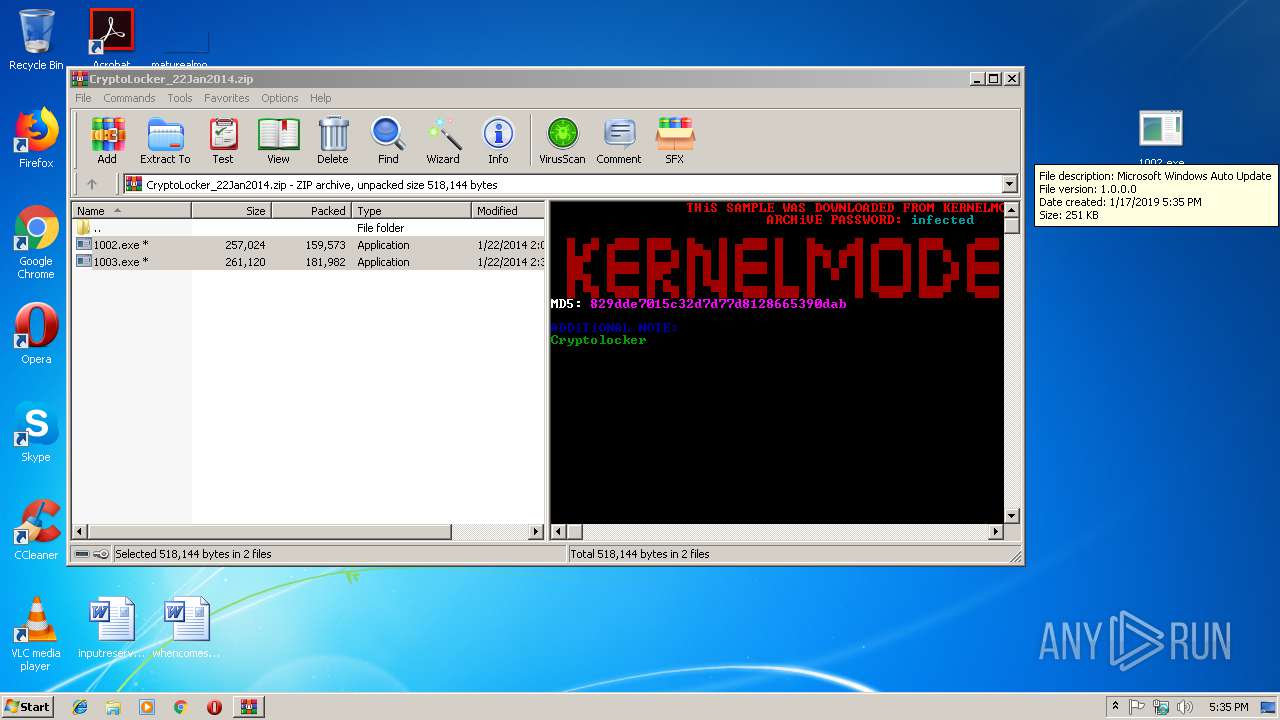
| 2344 | "C:\Users\admin\AppData\Roaming\2C28475F30.exe" | C:\Users\admin\AppData\Roaming\2C28475F30.exe | 1003.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Microsoft Windows Auto Update Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2508 | "taskkill" /F /IM 1003.exe | C:\Windows\system32\taskkill.exe | — | 1003.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
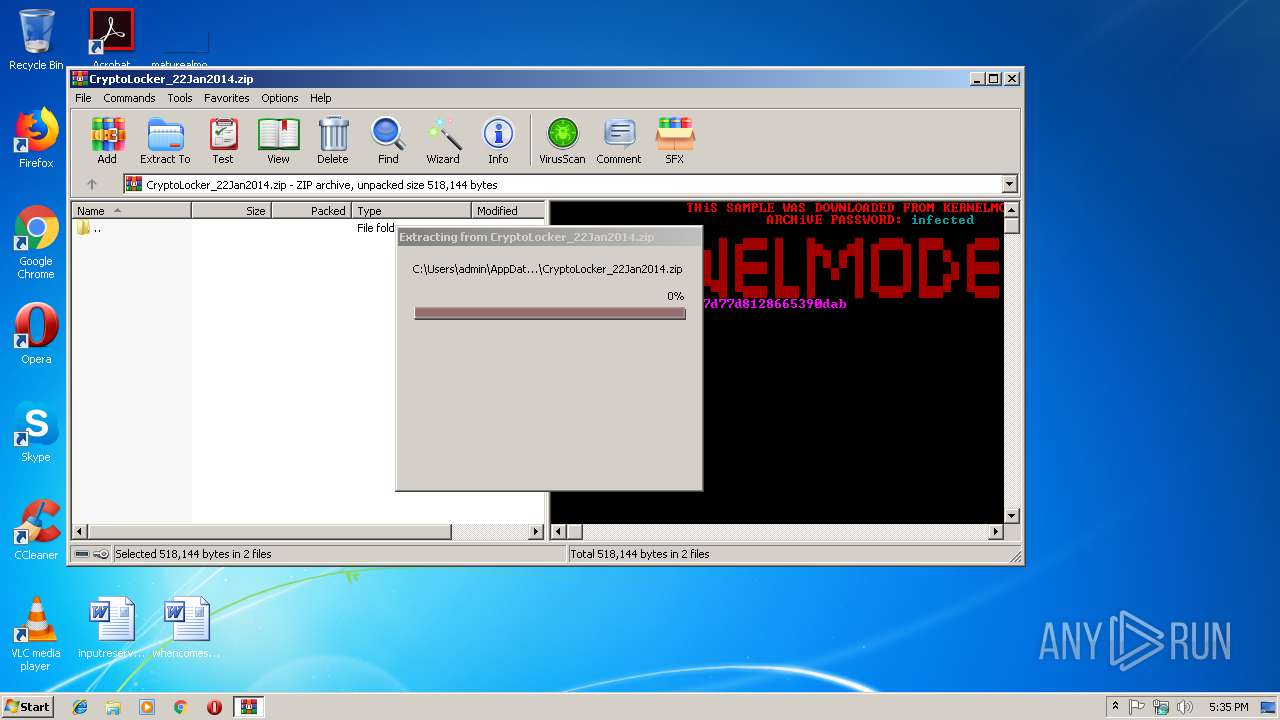
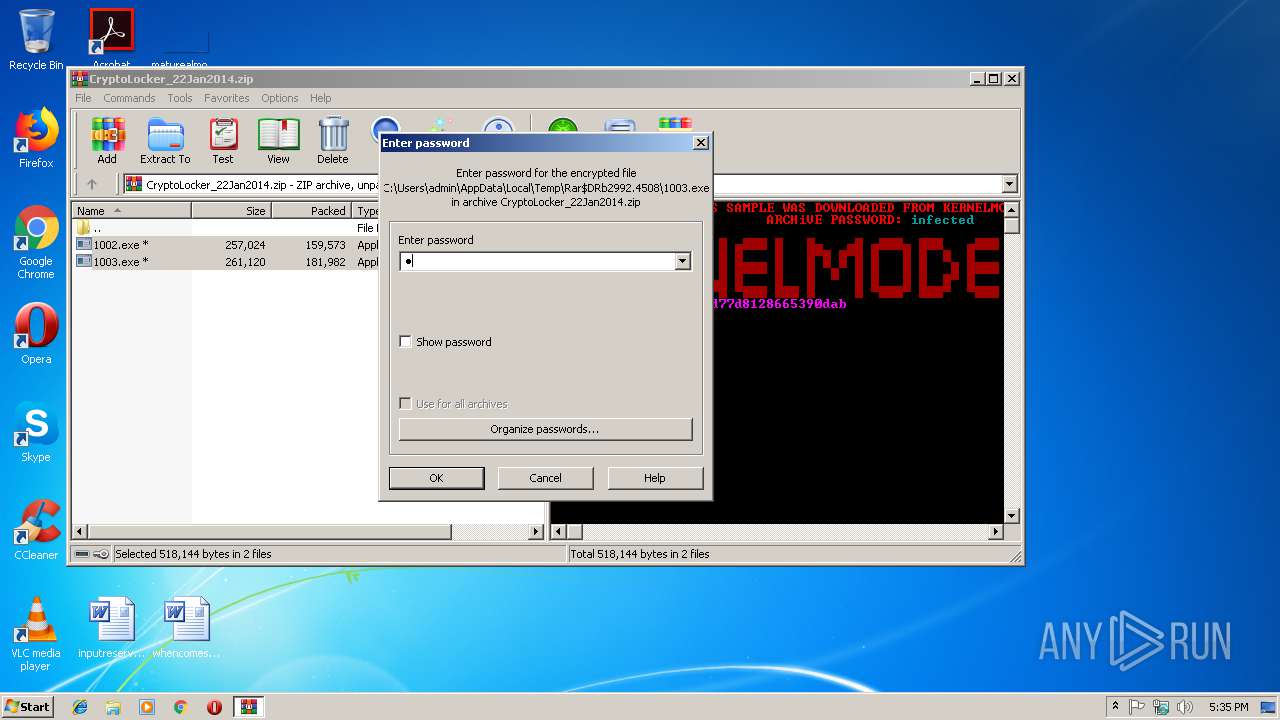
| 2992 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\CryptoLocker_22Jan2014.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3396 | "C:\Users\admin\Desktop\1003.exe" | C:\Users\admin\Desktop\1003.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Microsoft Windows Auto Update Exit code: 1 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3616 | "C:\Users\admin\Desktop\1003.exe" | C:\Users\admin\Desktop\1003.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Microsoft Windows Auto Update Exit code: 1 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3920 | "C:\Users\admin\Desktop\1002.exe" | C:\Users\admin\Desktop\1002.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Microsoft Windows Auto Update Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
937
Read events
878
Write events
59
Delete events
0
Modification events
| (PID) Process: | (2992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2992) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\CryptoLocker_22Jan2014.zip | |||
| (PID) Process: | (2992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3396) 1003.exe | Key: | HKEY_CURRENT_USER\Software\2C28475F30\Keys |
| Operation: | write | Name: | |
Value: | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2992 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2992.4508\1003.exe | — | |
MD5:— | SHA256:— | |||
| 2992 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2992.4508\1002.exe | — | |
MD5:— | SHA256:— | |||
| 3396 | 1003.exe | C:\Users\admin\AppData\Roaming\2C28475F30.exe | executable | |
MD5:0246BB54723BD4A49444AA4CA254845A | SHA256:8CF50AE247445DE2E570F19705236ED4B1E19F75CA15345E5F00857243BC0E9B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
6
Threats
4
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
cabin.su |
| malicious |
wrax.ru |
| malicious |
icals.ru |
| malicious |
hips.su |
| malicious |
yot.su |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |