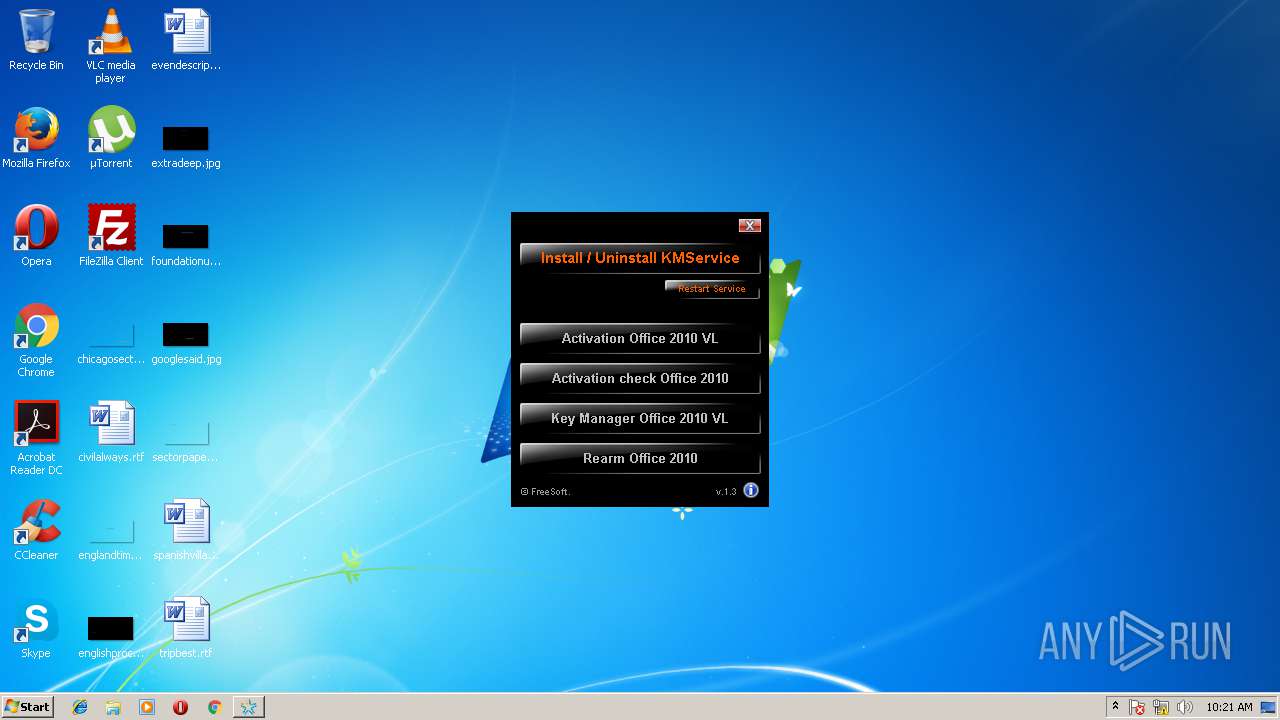
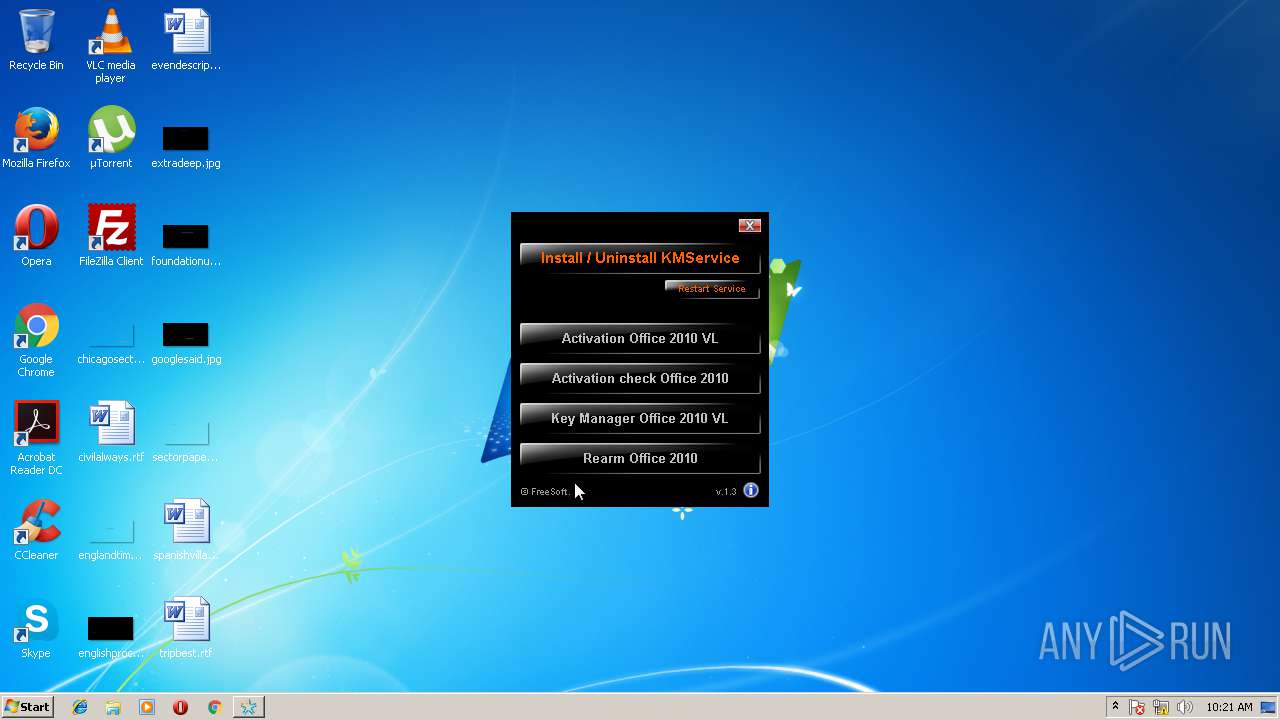
| File name: | mini-KMS_Activator_v1.3_Office2010_VL_ENG.exe |
| Full analysis: | https://app.any.run/tasks/edf2e5af-a41d-45e4-b8e5-7128529762d9 |
| Verdict: | Malicious activity |
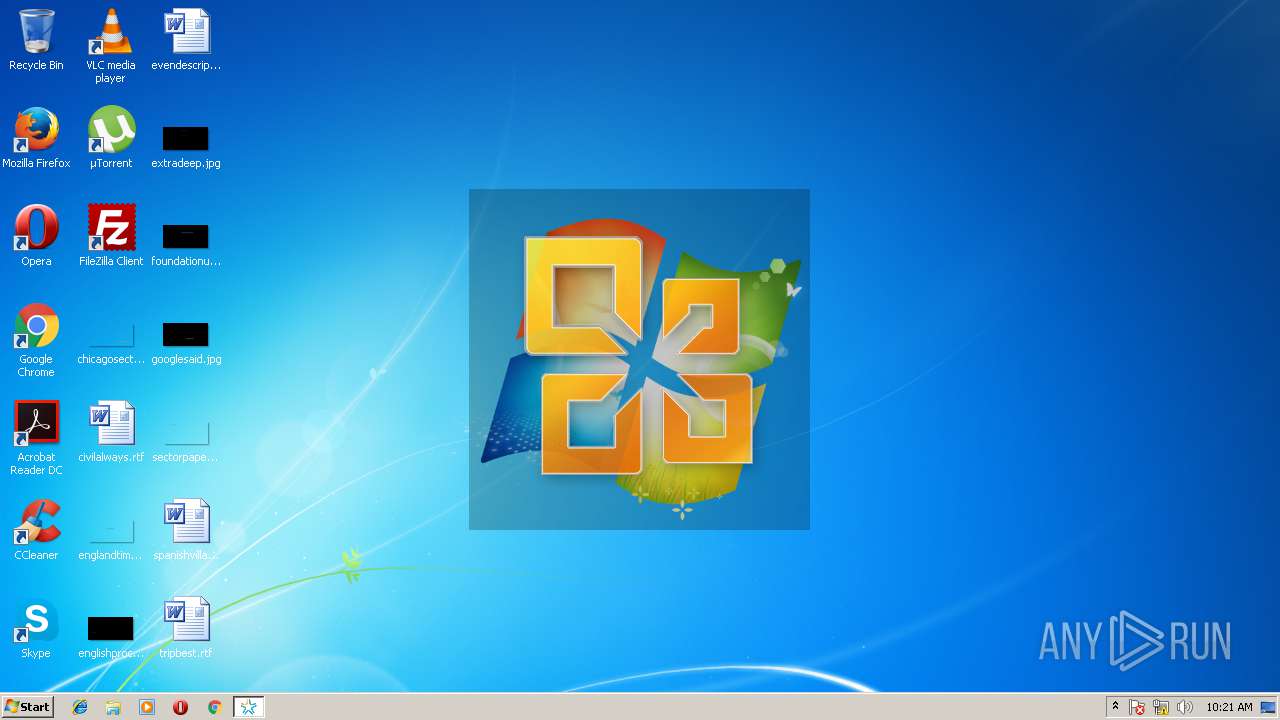
| Analysis date: | March 19, 2018, 10:21:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | BE7563A984DC5168CE14181B90432859 |
| SHA1: | B98280F7310095DA26DE3E448BEB489998F74C54 |
| SHA256: | E9045C4012CDFD4F2911DB303478527E2006AA3B148DFDBACAE85B4EE3B52E5E |
| SSDEEP: | 24576:kF8B9/XCfoX5IgBIeepfBLwtQVReC5Tt9T:I8j+g+XZd5TtN |
MALICIOUS
Application was dropped or rewritten from another process
- autorun.exe (PID: 3556)
- cscript.exe (PID: 3176)
- choice.exe (PID: 2316)
- srvany.exe (PID: 3012)
- KMService.exe (PID: 3408)
SUSPICIOUS
Starts CMD.EXE for commands execution
- mini-KMS_Activator_v1.3_Office2010_VL_ENG.exe (PID: 3460)
- autorun.exe (PID: 3556)
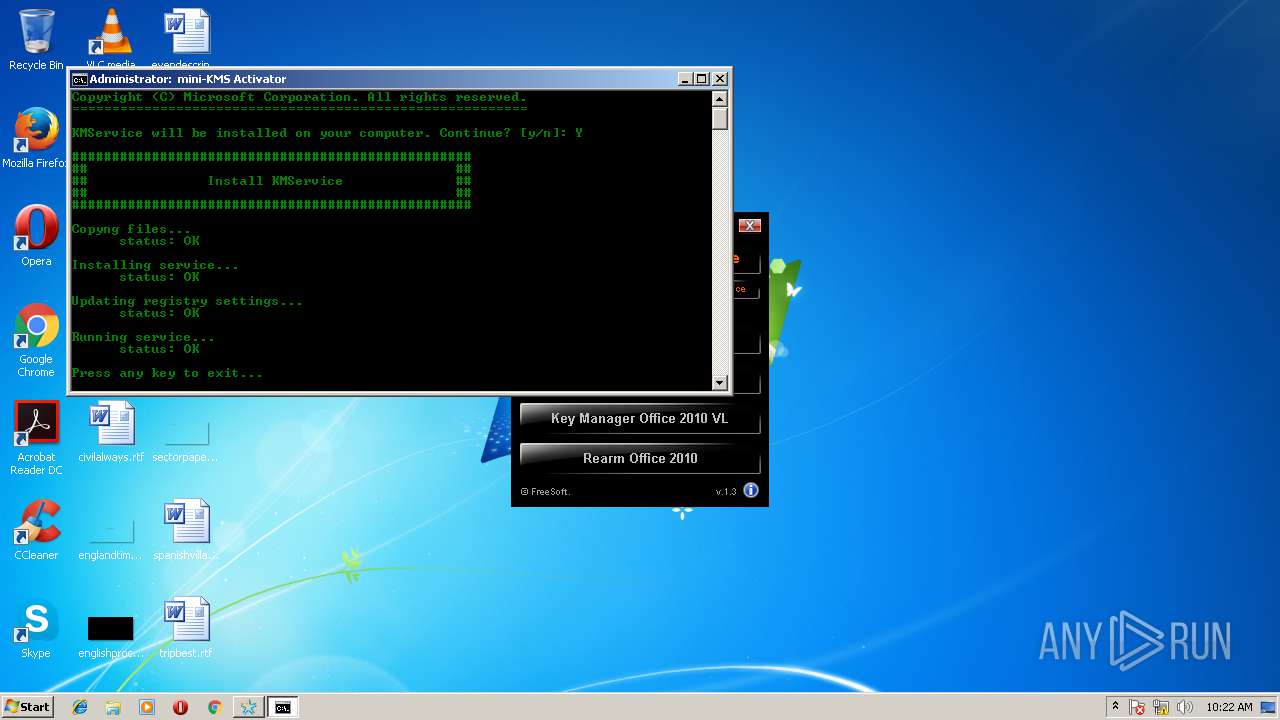
Starts SC.EXE for service management
- cmd.exe (PID: 3104)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3104)
Modifies files in the system directory
- cmd.exe (PID: 3104)
- rundll32.exe (PID: 4084)
Creates files in the Windows directory
- cmd.exe (PID: 3104)
- rundll32.exe (PID: 4084)
Creates or modifies windows services
- rundll32.exe (PID: 4084)
INFO
Loads rich edit control libraries
- autorun.exe (PID: 3556)
Dropped object may contain URL's
- mini-KMS_Activator_v1.3_Office2010_VL_ENG.exe (PID: 3460)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:02:07 07:33:08+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 1015808 |
| InitializedDataSize: | 32768 |
| UninitializedDataSize: | 1536000 |
| EntryPoint: | 0x26e620 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.3.0.0 |
| ProductVersionNumber: | 1.3.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug, Pre-release, Private build |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | FreeSoft |
| FileDescription: | mini-KMS Activator |
| FileVersion: | 1,3,0,0 |
| ProductName: | mini-KMS Activator v1.3 Office2010 VL ENG |
| InternalName: | mini-KMS_Activator_v1.3_Office2010_VL_ENG.exe |
| ProductVersion: | 1,3,0,0 |
| LegalCopyright: | © 2010, FreeSoft |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Feb-2009 06:33:08 |
| Detected languages: |
|
| CompanyName: | FreeSoft |
| FileDescription: | mini-KMS Activator |
| FileVersion: | 1,3,0,0 |
| ProductName: | mini-KMS Activator v1.3 Office2010 VL ENG |
| InternalName: | mini-KMS_Activator_v1.3_Office2010_VL_ENG.exe |
| ProductVersion: | 1,3,0,0 |
| LegalCopyright: | © 2010, FreeSoft |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 07-Feb-2009 06:33:08 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00177000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00178000 | 0x000F8000 | 0x000F7200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99977 |
.rsrc | 0x00270000 | 0x00008000 | 0x00007400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.25271 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.09999 | 668 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 4.23303 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 3.21662 | 1736 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 1.98904 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 3.87329 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 4.15792 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 4.74851 | 2440 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 5.0637 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
B | 7.83659 | 1130 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
F | 0 | 2462227 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
COMCTL32.dll |
GDI32.dll |
KERNEL32.DLL |
MSVCRT.dll |
OLE32.dll |
SHELL32.dll |
USER32.dll |
Total processes
50
Monitored processes
13
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2004 | "C:\Users\admin\AppData\Local\Temp\mini-KMS_Activator_v1.3_Office2010_VL_ENG.exe" | C:\Users\admin\AppData\Local\Temp\mini-KMS_Activator_v1.3_Office2010_VL_ENG.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
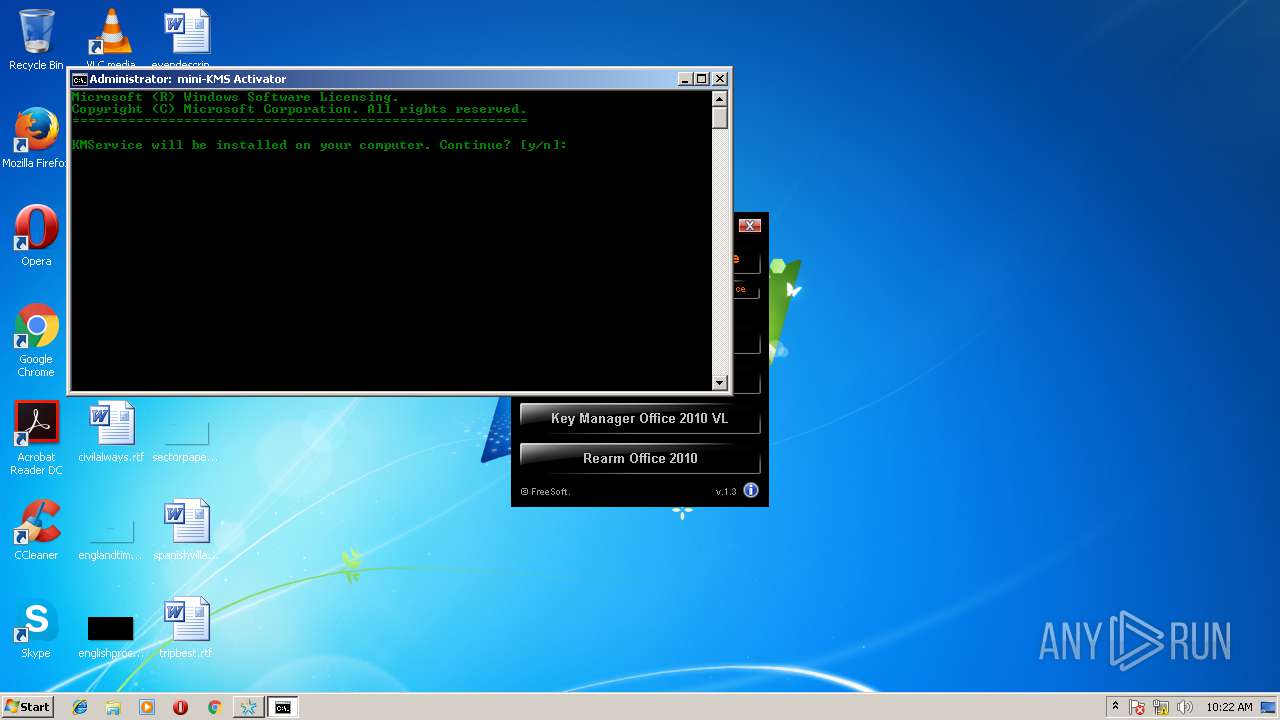
| 2316 | choice /C YN /N /M "KMService will be installed on your computer. Continue? [y/n]: " | C:\Users\admin\AppData\Local\Temp\C9C2.tmp\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Предложение пользователю для выбора Exit code: 1 Version: 5.2.3790.0 (srv03_rtm.030324-2048) Modules
| |||||||||||||||
| 2548 | cmd /c ""C:\Users\admin\AppData\Local\Temp\C9C2.tmp\Run.cmd" " | C:\Windows\system32\cmd.exe | — | mini-KMS_Activator_v1.3_Office2010_VL_ENG.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2640 | sc start KMService | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3012 | C:\Windows\system32\srvany.exe | C:\Windows\system32\srvany.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 3104 | cmd /c ""C:\Users\admin\AppData\Local\Temp\C9C2.tmp\Scripts.cmd" KMSIns" | C:\Windows\system32\cmd.exe | autorun.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3176 | cscript HS_MESSAGE.vbs "Did you run the program as Administrator? " "Activation Tool" Q YESNO 30 | C:\Users\admin\AppData\Local\Temp\C9C2.tmp\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 6 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3408 | C:\Windows\KMService.exe | C:\Windows\KMService.exe | — | srvany.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 3460 | "C:\Users\admin\AppData\Local\Temp\mini-KMS_Activator_v1.3_Office2010_VL_ENG.exe" | C:\Users\admin\AppData\Local\Temp\mini-KMS_Activator_v1.3_Office2010_VL_ENG.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3556 | autorun.exe | C:\Users\admin\AppData\Local\Temp\C9C2.tmp\autorun.exe | cmd.exe | ||||||||||||
User: admin Company: Linasoft Integrity Level: HIGH Description: AutoPlay Menu Loader Exit code: 0 Version: 1.1.1.1 Modules
| |||||||||||||||
Total events
730
Read events
712
Write events
18
Delete events
0
Modification events
| (PID) Process: | (3460) mini-KMS_Activator_v1.3_Office2010_VL_ENG.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3460) mini-KMS_Activator_v1.3_Office2010_VL_ENG.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3556) autorun.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3556) autorun.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (4084) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.app.log |
Value: 4096 | |||
| (PID) Process: | (4084) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\KMService |
| Operation: | write | Name: | Description |
Value: Software licensing service | |||
| (PID) Process: | (4084) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\KMService |
| Operation: | write | Name: | DisplayName |
Value: KMService | |||
| (PID) Process: | (4084) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\KMService |
| Operation: | write | Name: | Start |
Value: 2 | |||
| (PID) Process: | (4084) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\KMService |
| Operation: | write | Name: | Type |
Value: 16 | |||
| (PID) Process: | (4084) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\KMService |
| Operation: | write | Name: | ErrorControl |
Value: 1 | |||
Executable files
12
Suspicious files
0
Text files
12
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3556 | autorun.exe | C:\Users\admin\AppData\Local\Temp\apmF799.tmp | — | |
MD5:— | SHA256:— | |||
| 3556 | autorun.exe | C:\Users\admin\AppData\Local\Temp\apmF79A.tmp | — | |
MD5:— | SHA256:— | |||
| 3460 | mini-KMS_Activator_v1.3_Office2010_VL_ENG.exe | C:\Users\admin\AppData\Local\Temp\C9C2.tmp\slerror.xml | text | |
MD5:DF1EF05879E06C5F09F3E1022F37B5CB | SHA256:D49ADF2DABBBF6AA43CE4E336AF4F768207DF75302EBF568A94A5350AAC988C5 | |||
| 3460 | mini-KMS_Activator_v1.3_Office2010_VL_ENG.exe | C:\Users\admin\AppData\Local\Temp\C9C2.tmp\Run.cmd | text | |
MD5:0B851D375A6A8A8B04431D9635371F85 | SHA256:706D9DDF9C333F9C77238D22500DFB294776220625755E5668DFF80246FC48FA | |||
| 3460 | mini-KMS_Activator_v1.3_Office2010_VL_ENG.exe | C:\Users\admin\AppData\Local\Temp\C9C2.tmp\PortQry.exe | executable | |
MD5:C6AC67F4076CA431ACC575912C194245 | SHA256:FB6CEBADD49D202C8C7B5CDD641BD16AAC8258429E8FACE365A94BD32E253B00 | |||
| 3460 | mini-KMS_Activator_v1.3_Office2010_VL_ENG.exe | C:\Users\admin\AppData\Local\Temp\C9C2.tmp\ospprearm.exe | executable | |
MD5:7FFAE006610A85317FBB092A2D65D1A9 | SHA256:F10ACD6E32BC4D7CC74FEB9E84FEC18A77AEB2838EBF2AA7E3280BA1C7F3FCA2 | |||
| 3460 | mini-KMS_Activator_v1.3_Office2010_VL_ENG.exe | C:\Users\admin\AppData\Local\Temp\C9C2.tmp\cscript.exe | executable | |
MD5:34098403F9D8F71CE2EC749122168E89 | SHA256:12DF0B06A9B56DCE3EFDB85984F84B387B1A5B61C9EBBF5A3BD61A5FBB996F60 | |||
| 3460 | mini-KMS_Activator_v1.3_Office2010_VL_ENG.exe | C:\Users\admin\AppData\Local\Temp\C9C2.tmp\hidcon.exe | executable | |
MD5:B2DADAB18C318443301D0087CD7200BA | SHA256:B88A4D442BCD94457FC75DC5A541DC3437FD01091A2B6500569C699260E65238 | |||
| 3460 | mini-KMS_Activator_v1.3_Office2010_VL_ENG.exe | C:\Users\admin\AppData\Local\Temp\C9C2.tmp\choice.exe | executable | |
MD5:A704D22D57B62553E27AD261276B0625 | SHA256:5632B9495ED595712EB7DFAD4E6D166A70B68FD3AF2F7D72BEFF57AF2385F7E6 | |||
| 3460 | mini-KMS_Activator_v1.3_Office2010_VL_ENG.exe | C:\Users\admin\AppData\Local\Temp\C9C2.tmp\autorun.exe | executable | |
MD5:C98D6ABC5AE3FCD85F2AE09D95F584CB | SHA256:C8D480B605A9E3C13F411CD3A6DA44ED460704F3E529719BDC536D983CEB024D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report