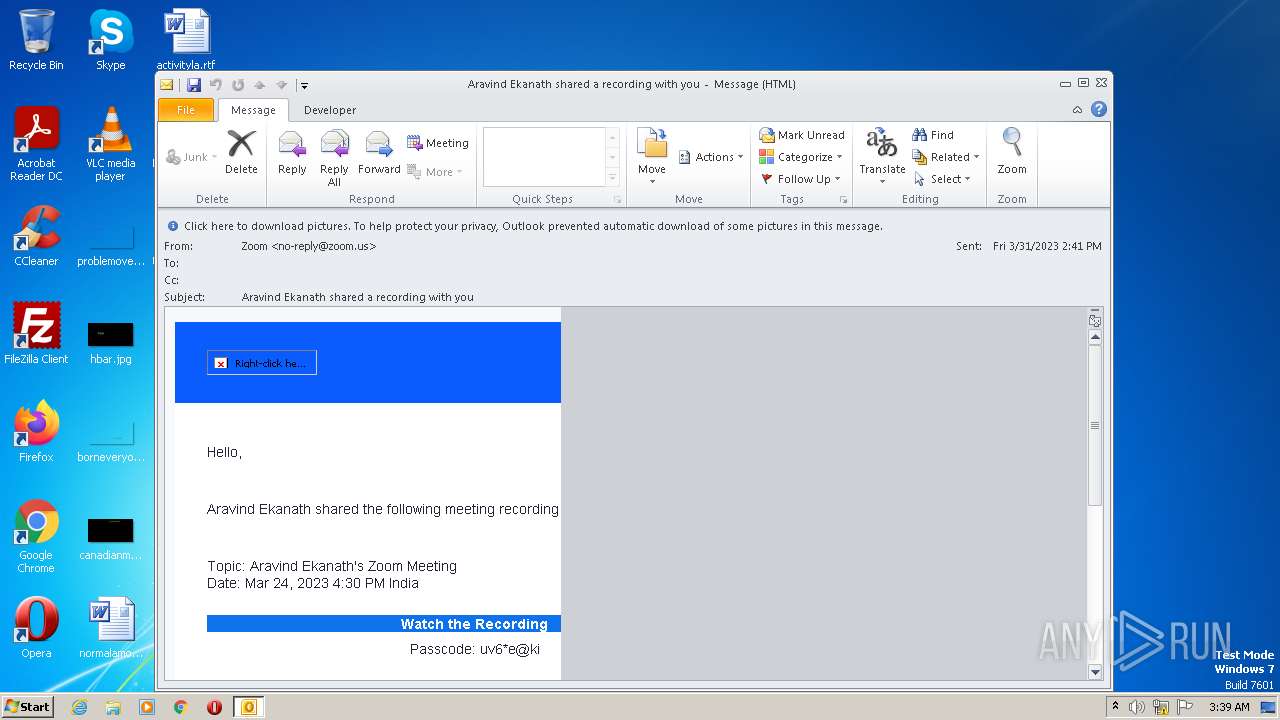
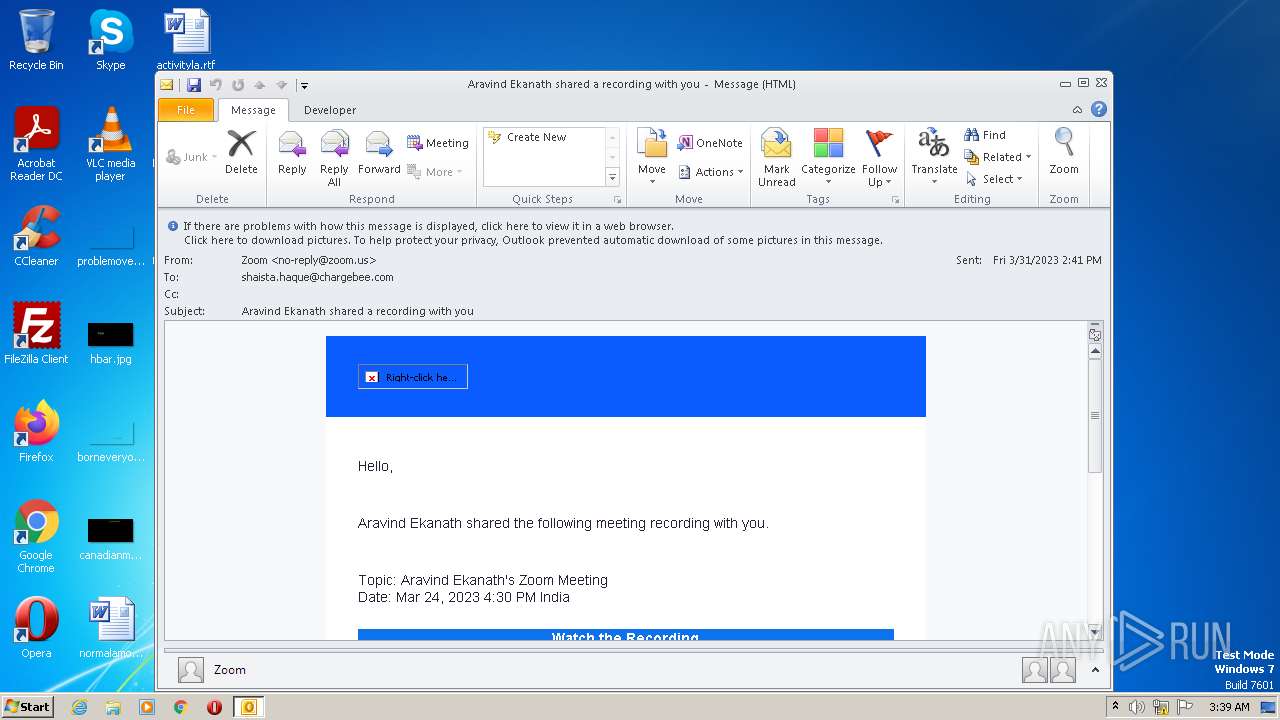
| File name: | Aravind Ekanath shared a recording with you.eml |
| Full analysis: | https://app.any.run/tasks/6ed58d12-f44f-4f8f-a177-a343472d823b |
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2023, 02:39:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | SMTP mail, ASCII text, with CRLF line terminators |
| MD5: | 8B9C21D1371F6852B41C4251F45889C3 |
| SHA1: | 8DF73735BBE38874A146814CD11CA605E1DE57DF |
| SHA256: | E8FAFED4DBE6AB6CCDBD7D973C606358B3C1D1DB70A3803466E88A18B1CDE1ED |
| SSDEEP: | 384:hjmLxTn5aBLofyGQfN+CWxo/8OfzGEy4+pba:hCLx1ado6qsfqJa |
MALICIOUS
No malicious indicators.SUSPICIOUS
Searches for installed software
- OUTLOOK.EXE (PID: 1900)
Reads the Internet Settings
- OUTLOOK.EXE (PID: 1900)
INFO
Checks supported languages
- OUTLOOK.EXE (PID: 1900)
The process checks LSA protection
- OUTLOOK.EXE (PID: 1900)
Reads the computer name
- OUTLOOK.EXE (PID: 1900)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 1900)
Reads the machine GUID from the registry
- OUTLOOK.EXE (PID: 1900)
Checks proxy server information
- OUTLOOK.EXE (PID: 1900)
Create files in a temporary directory
- OUTLOOK.EXE (PID: 1900)
- iexplore.exe (PID: 3296)
- iexplore.exe (PID: 3380)
Process checks computer location settings
- OUTLOOK.EXE (PID: 1900)
Creates files or folders in the user directory
- OUTLOOK.EXE (PID: 1900)
Application launched itself
- iexplore.exe (PID: 3296)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 7) (100) |
|---|
Total processes
43
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1900 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\Aravind Ekanath shared a recording with you.eml" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3296 | "C:\Program Files\Internet Explorer\iexplore.exe" https://zoom.us/ | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3380 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3296 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
70 948
Read events
69 664
Write events
1 242
Delete events
42
Modification events
| (PID) Process: | (1900) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (1900) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: On | |||
| (PID) Process: | (1900) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: On | |||
| (PID) Process: | (1900) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: On | |||
| (PID) Process: | (1900) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: On | |||
| (PID) Process: | (1900) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: On | |||
| (PID) Process: | (1900) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: On | |||
| (PID) Process: | (1900) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: On | |||
| (PID) Process: | (1900) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: On | |||
| (PID) Process: | (1900) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: On | |||
Executable files
0
Suspicious files
138
Text files
804
Unknown types
100
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1900 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRF618.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1900 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 1900 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1900 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 3380 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3380 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | der | |
MD5:— | SHA256:— | |||
| 3380 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:— | SHA256:— | |||
| 1900 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{465091BB-0542-44C3-B769-6FCC2E17E8A9}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:4C61C12EDBC453D7AE184976E95258E1 | SHA256:296526F9A716C1AA91BA5D6F69F0EB92FDF79C2CB2CFCF0CEB22B7CCBC27035F | |||
| 1900 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_WorkHours_1_E93876B551243045BFF0537063356CB6.dat | xml | |
MD5:807EF0FC900FEB3DA82927990083D6E7 | SHA256:4411E7DC978011222764943081500FFF0E43CBF7CCD44264BD1AB6306CA68913 | |||
| 1900 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_TCPrefs_2_CA7361A785CF8741BEA0E11E9ECE9DA5.dat | xml | |
MD5:F194B1FA12F9B6F46A47391FAE8BEEC2 | SHA256:FCD8D7E030BE6EA7588E5C6CB568E3F1BDFC263942074B693942A27DF9521A74 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
427
DNS requests
63
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1900 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3380 | iexplore.exe | GET | — | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?b3ad64231adb6d32 | US | — | — | whitelisted |
3380 | iexplore.exe | GET | — | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | — | — | whitelisted |
3380 | iexplore.exe | GET | — | 108.138.2.173:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | — | — | whitelisted |
3380 | iexplore.exe | GET | — | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSnxLiz3Fu1WB6n1%2FE6xWn1b0jXiQQUdIWAwGbH3zfez70pN6oDHb7tzRcCEAbCsehAv%2FkAxBfkV5KvfLI%3D | US | — | — | whitelisted |
3380 | iexplore.exe | GET | — | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?90f8681d4da85877 | US | — | — | whitelisted |
3380 | iexplore.exe | GET | — | 52.222.250.174:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEjgLnWaIozse2b%2BczaaODg8%3D | US | — | — | shared |
3380 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
3380 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3380 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEG%2BwCexAj3cmEm%2BEDt%2B13CU%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3380 | iexplore.exe | 18.66.147.95:443 | static.ada.support | AMAZON-02 | US | suspicious |
3380 | iexplore.exe | 52.84.151.14:443 | file-paa.zoom.us | AMAZON-02 | US | unknown |
3380 | iexplore.exe | 54.84.181.84:443 | rewards.zoom.us | AMAZON-AES | US | unknown |
3380 | iexplore.exe | 52.222.250.185:80 | ocsp.rootg2.amazontrust.com | AMAZON-02 | US | whitelisted |
3380 | iexplore.exe | 34.98.108.207:443 | cdn.solvvy.com | GOOGLE | US | unknown |
3380 | iexplore.exe | 52.222.250.174:80 | ocsp.rootg2.amazontrust.com | AMAZON-02 | US | whitelisted |
3380 | iexplore.exe | 108.138.2.173:80 | o.ss2.us | AMAZON-02 | US | unknown |
— | — | 64.4.26.155:80 | config.messenger.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3380 | iexplore.exe | 170.114.52.2:443 | zoom.us | — | US | suspicious |
3380 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
zoom.us |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
st3.zoom.us |
| whitelisted |
explore.zoom.us |
| whitelisted |
st1.zoom.us |
| whitelisted |
st2.zoom.us |
| whitelisted |
cdn.cookielaw.org |
| whitelisted |
file-paa.zoom.us |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3380 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3380 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3380 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3380 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3380 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3380 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3380 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3380 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3380 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3380 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |