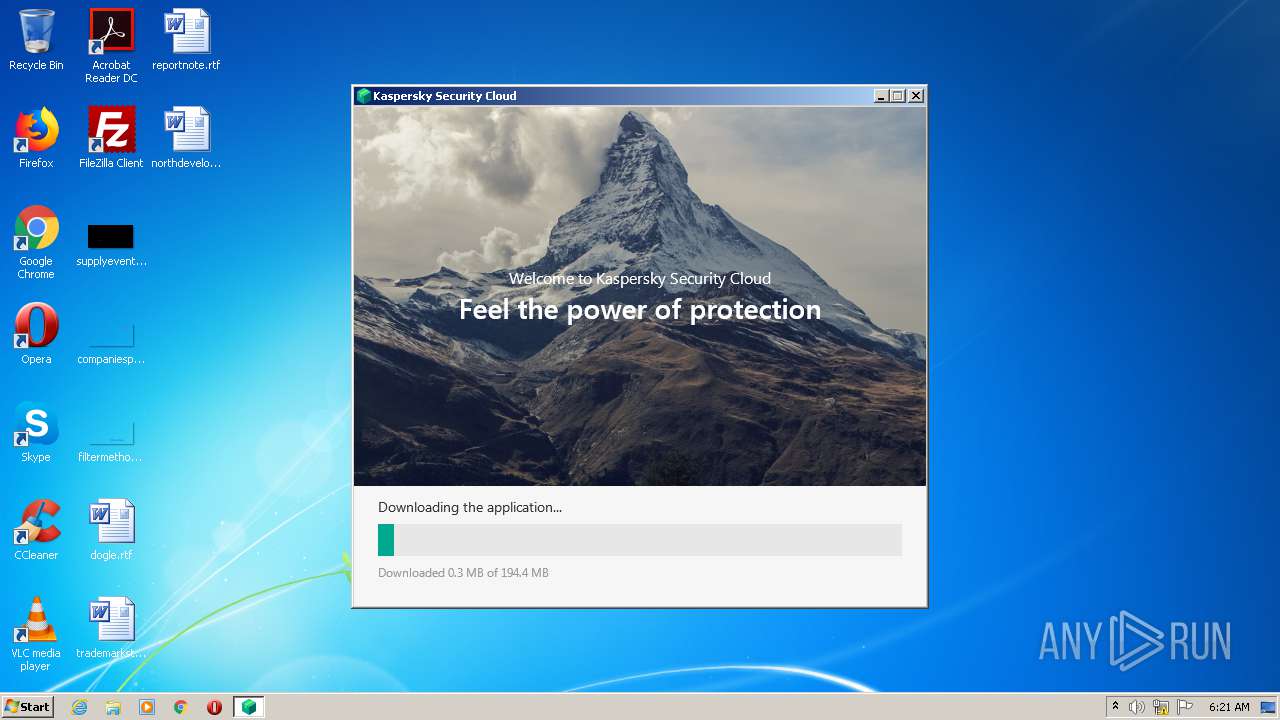
| File name: | ks4.021.2.16.590en_25092.exe |
| Full analysis: | https://app.any.run/tasks/d148fd4e-38dd-47b2-8c41-bd8d2f0f2b12 |
| Verdict: | Malicious activity |
| Analysis date: | December 24, 2020, 06:20:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 18642459A5CBC9A59ED00667B8131F03 |
| SHA1: | 5EF51343E717E57D33E2990F8EF0C3794290D2BB |
| SHA256: | E8EB70D4087C54986E903D90170AE2C93F1DBD5828D3E3B1E71B98458A458693 |
| SSDEEP: | 49152:4lINc3mvkxc9HnIZKj9DVvBtXLbASEi5MltSCQCTLXKILG9/acv+1Jy0:qINc3v2HnIYjVVvBtXLbASEi4ECFuILR |
MALICIOUS
Loads dropped or rewritten executable
- ks4.021.2.16.590en_25092.exe (PID: 2420)
- ks4.021.2.16.590en_25092.exe (PID: 2656)
- TEST_WPF.EXE (PID: 2288)
- msiexec.exe (PID: 2180)
- msiexec.exe (PID: 3760)
- msiexec.exe (PID: 2416)
- regsvr32.exe (PID: 3800)
- plugins-setup.exe (PID: 3192)
- plugins-setup.exe (PID: 3168)
- plugins-setup.exe (PID: 2940)
- plugins-setup.exe (PID: 3580)
- msiexec.exe (PID: 2292)
- avpui.exe (PID: 2340)
- avp.exe (PID: 2544)
Drops executable file immediately after starts
- ks4.021.2.16.590en_25092.exe (PID: 2656)
- MsiExec.exe (PID: 4020)
- DrvInst.exe (PID: 3572)
- upgrade_launcher.exe (PID: 2044)
- kpm.exe (PID: 1860)
Application was dropped or rewritten from another process
- TEST_WPF.EXE (PID: 2288)
- plugins-setup.exe (PID: 3192)
- plugins-setup.exe (PID: 2940)
- plugins-setup.exe (PID: 3168)
- plugins-setup.exe (PID: 3580)
- avp.exe (PID: 2544)
- avpui.exe (PID: 2340)
- upgrade_launcher.exe (PID: 2044)
- kpm.exe (PID: 1860)
- {24FC0D32-5603-4001-9D49-989027CAC3FE}.exe (PID: 3228)
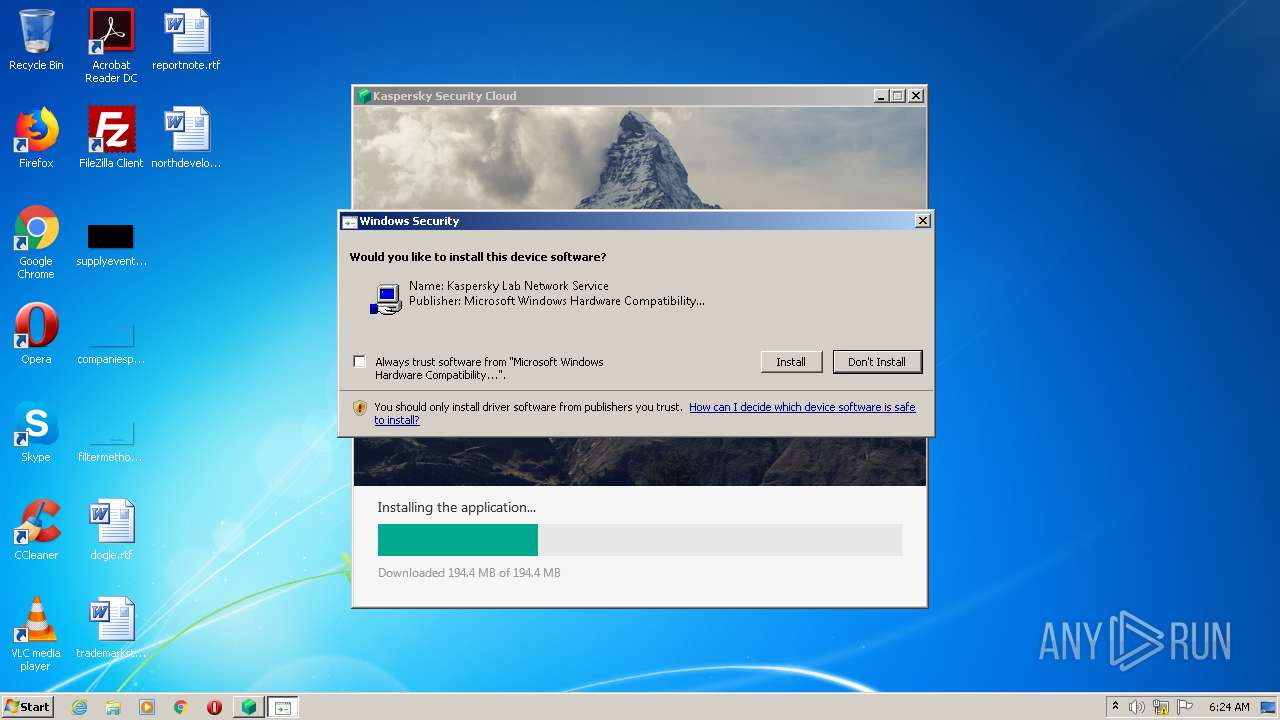
Changes settings of System certificates
- ks4.021.2.16.590en_25092.exe (PID: 2656)
- MsiExec.exe (PID: 3408)
- avp.exe (PID: 2544)
- MsiExec.exe (PID: 1772)
Registers / Runs the DLL via REGSVR32.EXE
- MsiExec.exe (PID: 4020)
Application was injected by another process
- services.exe (PID: 472)
Runs injected code in another process
- avp.exe (PID: 2544)
Loads the Task Scheduler COM API
- upgrade_launcher.exe (PID: 2044)
Changes the autorun value in the registry
- DrvInst.exe (PID: 2264)
SUSPICIOUS
Drops a file that was compiled in debug mode
- ks4.021.2.16.590en_25092.exe (PID: 2420)
- ks4.021.2.16.590en_25092.exe (PID: 2656)
- msiexec.exe (PID: 4044)
- MsiExec.exe (PID: 4020)
- MsiExec.exe (PID: 3408)
- DrvInst.exe (PID: 3572)
- avp.exe (PID: 2544)
- upgrade_launcher.exe (PID: 2044)
- DrvInst.exe (PID: 2396)
- MsiExec.exe (PID: 1772)
- MsiExec.exe (PID: 3592)
- DrvInst.exe (PID: 2264)
- kpm.exe (PID: 1860)
Drops a file with too old compile date
- ks4.021.2.16.590en_25092.exe (PID: 2420)
- ks4.021.2.16.590en_25092.exe (PID: 2656)
- msiexec.exe (PID: 4044)
- MsiExec.exe (PID: 3408)
- MsiExec.exe (PID: 4020)
- DrvInst.exe (PID: 3572)
- MsiExec.exe (PID: 3592)
Creates files in the user directory
- ks4.021.2.16.590en_25092.exe (PID: 2420)
- avpui.exe (PID: 2340)
Executable content was dropped or overwritten
- ks4.021.2.16.590en_25092.exe (PID: 2420)
- ks4.021.2.16.590en_25092.exe (PID: 2656)
- msiexec.exe (PID: 4044)
- MsiExec.exe (PID: 4020)
- MsiExec.exe (PID: 3408)
- DrvInst.exe (PID: 3572)
- avp.exe (PID: 2544)
- MsiExec.exe (PID: 3592)
- MsiExec.exe (PID: 1772)
- DrvInst.exe (PID: 2396)
- upgrade_launcher.exe (PID: 2044)
- DrvInst.exe (PID: 2264)
- kpm.exe (PID: 1860)
Creates files in the program directory
- ks4.021.2.16.590en_25092.exe (PID: 2656)
- msiexec.exe (PID: 2124)
- plugins-setup.exe (PID: 2940)
- plugins-setup.exe (PID: 3168)
- plugins-setup.exe (PID: 3580)
- avp.exe (PID: 2544)
- upgrade_launcher.exe (PID: 2044)
Application launched itself
- ks4.021.2.16.590en_25092.exe (PID: 2420)
Adds / modifies Windows certificates
- ks4.021.2.16.590en_25092.exe (PID: 2656)
- MsiExec.exe (PID: 3408)
Creates files in the Windows directory
- MsiExec.exe (PID: 4020)
- msiexec.exe (PID: 4044)
- DrvInst.exe (PID: 3572)
- DrvInst.exe (PID: 2264)
- DrvInst.exe (PID: 2396)
- kpm.exe (PID: 1860)
- {24FC0D32-5603-4001-9D49-989027CAC3FE}.exe (PID: 3228)
Removes files from Windows directory
- MsiExec.exe (PID: 4020)
- DrvInst.exe (PID: 3572)
- DrvInst.exe (PID: 2264)
- DrvInst.exe (PID: 2396)
Creates files in the driver directory
- MsiExec.exe (PID: 4020)
- DrvInst.exe (PID: 3572)
- DrvInst.exe (PID: 2264)
- DrvInst.exe (PID: 2396)
Creates a directory in Program Files
- msiexec.exe (PID: 4044)
- MsiExec.exe (PID: 3408)
- MsiExec.exe (PID: 3592)
- avp.exe (PID: 2544)
- upgrade_launcher.exe (PID: 2044)
Drops a file with a compile date too recent
- msiexec.exe (PID: 4044)
- MsiExec.exe (PID: 3408)
- DrvInst.exe (PID: 3572)
- MsiExec.exe (PID: 3592)
- DrvInst.exe (PID: 2264)
- kpm.exe (PID: 1860)
Executed via COM
- DrvInst.exe (PID: 3572)
- DrvInst.exe (PID: 2264)
- DrvInst.exe (PID: 2396)
Creates or modifies windows services
- services.exe (PID: 472)
- avp.exe (PID: 2544)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 3572)
Changes default file association
- msiexec.exe (PID: 4044)
- MsiExec.exe (PID: 4020)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 3760)
- msiexec.exe (PID: 2180)
- msiexec.exe (PID: 2124)
- regsvr32.exe (PID: 3800)
- msiexec.exe (PID: 2416)
- msiexec.exe (PID: 2292)
Executed as Windows Service
- vssvc.exe (PID: 2496)
- avp.exe (PID: 2544)
Low-level read access rights to disk partition
- avp.exe (PID: 2544)
Reads Windows owner or organization settings
- avpui.exe (PID: 2340)
Reads the Windows organization settings
- avpui.exe (PID: 2340)
INFO
Reads settings of System Certificates
- ks4.021.2.16.590en_25092.exe (PID: 2420)
- ks4.021.2.16.590en_25092.exe (PID: 2656)
- msiexec.exe (PID: 4044)
- MsiExec.exe (PID: 3408)
- MsiExec.exe (PID: 4020)
- avp.exe (PID: 2544)
Application launched itself
- msiexec.exe (PID: 4044)
- MsiExec.exe (PID: 4020)
Loads dropped or rewritten executable
- msiexec.exe (PID: 4044)
- MsiExec.exe (PID: 3408)
- MsiExec.exe (PID: 4020)
- MsiExec.exe (PID: 3592)
- MsiExec.exe (PID: 1772)
Creates files in the program directory
- MsiExec.exe (PID: 4020)
- MsiExec.exe (PID: 3408)
- msiexec.exe (PID: 4044)
- MsiExec.exe (PID: 1772)
- MsiExec.exe (PID: 3592)
Dropped object may contain Bitcoin addresses
- MsiExec.exe (PID: 3408)
- avp.exe (PID: 2544)
- MsiExec.exe (PID: 3592)
Creates or modifies windows services
- MsiExec.exe (PID: 4020)
- msiexec.exe (PID: 4044)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2496)
Searches for installed software
- DrvInst.exe (PID: 3572)
Creates a software uninstall entry
- msiexec.exe (PID: 4044)
Changes settings of System certificates
- DrvInst.exe (PID: 3572)
Reads the hosts file
- avp.exe (PID: 2544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:09:01 10:23:07+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 297984 |
| InitializedDataSize: | 2528256 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x23ca |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 21.2.16.590 |
| ProductVersionNumber: | 21.2.16.590 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Kaspersky |
| FileDescription: | Kaspersky Security Cloud [21.2.16.590.0.4.0] |
| FileVersion: | 21.2.16.590 |
| LegalCopyright: | © 2020 AO Kaspersky Lab |
| LegalTrademarks: | Registered trademarks and service marks are the property of their respective owners |
| ProductName: | Kaspersky Security Cloud |
| ProductVersion: | 21.2.16.590 |
| InternalName: | Setup |
| OriginalFileName: | Setup.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Sep-2021 08:23:07 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Kaspersky |
| FileDescription: | Kaspersky Security Cloud [21.2.16.590.0.4.0] |
| FileVersion: | 21.2.16.590 |
| LegalCopyright: | © 2020 AO Kaspersky Lab |
| LegalTrademarks: | Registered trademarks and service marks are the property of their respective owners |
| ProductName: | Kaspersky Security Cloud |
| ProductVersion: | 21.2.16.590 |
| InternalName: | Setup |
| OriginalFilename: | Setup.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 01-Sep-2021 08:23:07 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00048AFE | 0x00048C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.6739 |
.rdata | 0x0004A000 | 0x000166D8 | 0x00016800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.22777 |
.data | 0x00061000 | 0x00005C38 | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.40147 |
.rsrc | 0x00067000 | 0x0024C1F4 | 0x0024C200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.68517 |
.reloc | 0x002B4000 | 0x00004454 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.54909 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.27937 | 1606 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.03205 | 67624 | Latin 1 / Western European | Process Default Language | RT_ICON |
3 | 3.34315 | 16936 | Latin 1 / Western European | Process Default Language | RT_ICON |
4 | 3.49595 | 9640 | Latin 1 / Western European | Process Default Language | RT_ICON |
5 | 2.89003 | 104 | Latin 1 / Western European | Process Default Language | RT_GROUP_ICON |
6 | 3.94447 | 2440 | Latin 1 / Western European | Process Default Language | RT_ICON |
7 | 4.26631 | 1128 | Latin 1 / Western European | Process Default Language | RT_ICON |
DYNAMIC.INI | 3.13372 | 98 | Latin 1 / Western European | UNKNOWN | DOWNLOADER.INI |
STATIC.INI | 3.53627 | 786 | Latin 1 / Western European | UNKNOWN | DOWNLOADER.INI |
GETSI.Z | 7.99838 | 110893 | Latin 1 / Western European | UNKNOWN | SZIP |
Imports
KERNEL32.dll |
RPCRT4.dll (delay-loaded) |
Total processes
73
Monitored processes
31
Malicious processes
20
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 472 | C:\Windows\system32\services.exe | C:\Windows\System32\services.exe | wininit.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Services and Controller app Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1772 | C:\Windows\system32\MsiExec.exe -Embedding A730FC7B51312317E60FAD5385C0C21B M Global\MSI0000 | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1860 | /-localization=en /-parent=saas /-promoScenario=ProductBundleInstall /s /-retrymsi | C:\ProgramData\Kaspersky Lab\AVP21.2\Temp\kpm.exe | avp.exe | ||||||||||||
User: SYSTEM Company: Kaspersky Integrity Level: SYSTEM Description: Kaspersky Password Manager [9.0.2.767.0.703.0] Exit code: 0 Version: 9.0.2.767 Modules
| |||||||||||||||
| 2044 | "C:\Program Files\Kaspersky Lab\Kaspersky Security Cloud 21.2\upgrade_launcher.exe" /initUpgrade | C:\Program Files\Kaspersky Lab\Kaspersky Security Cloud 21.2\upgrade_launcher.exe | avp.exe | ||||||||||||
User: SYSTEM Company: AO Kaspersky Lab Integrity Level: SYSTEM Description: Kaspersky Upgrade Launcher Exit code: 0 Version: 1.0.0.179 Modules
| |||||||||||||||
| 2124 | "C:\Windows\system32\msiexec.exe" /y "C:\Program Files\Kaspersky Lab\Kaspersky Security Cloud 21.2\mcou.dll" | C:\Windows\system32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2180 | "C:\Windows\system32\msiexec.exe" /y "C:\Program Files\Kaspersky Lab\Kaspersky Security Cloud 21.2\task_scheduler_handler.dll" | C:\Windows\system32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2264 | DrvInst.exe "2" "211" "ROOT\NET\0000" "C:\Windows\INF\oem5.inf" "kltap.inf:kltap:kltap.ndi:15.59.46.455:kltap" "6a39d1357" "000004B8" "000005E8" "000005EC" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2288 | "C:\Users\admin\AppData\Local\Temp\47731565-45B0-11EB-AEEC-12A9866C77DE\TEST_WPF.EXE" "C:\Users\admin\AppData\Local\Temp\365137740B54BE11EACE219A68C677ED\setup.dll" | C:\Users\admin\AppData\Local\Temp\47731565-45B0-11EB-AEEC-12A9866C77DE\TEST_WPF.EXE | — | ks4.021.2.16.590en_25092.exe | |||||||||||
User: admin Integrity Level: HIGH Description: test_wpf Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2292 | "C:\Windows\system32\msiexec.exe" /y "C:\Windows\system32\klfphc.dll" | C:\Windows\system32\msiexec.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2340 | "C:\Program Files\Kaspersky Lab\Kaspersky Security Cloud 21.2\avpui.exe" -hideuntilnavigate | C:\Program Files\Kaspersky Lab\Kaspersky Security Cloud 21.2\avpui.exe | avp.exe | ||||||||||||
User: admin Company: AO Kaspersky Lab Integrity Level: MEDIUM Description: Kaspersky Anti-Virus Exit code: 0 Version: 21.2.16.590 Modules
| |||||||||||||||
Total events
11 920
Read events
4 863
Write events
6 958
Delete events
99
Modification events
| (PID) Process: | (2420) ks4.021.2.16.590en_25092.exe | Key: | HKEY_CURRENT_USER\Software\KasperskyLab\IEOverride\Main |
| Operation: | write | Name: | Enable Browser Extensions |
Value: no | |||
| (PID) Process: | (2420) ks4.021.2.16.590en_25092.exe | Key: | HKEY_CURRENT_USER\Software\KasperskyLab\IEOverride\Main |
| Operation: | write | Name: | UseSWRender |
Value: 1 | |||
| (PID) Process: | (2420) ks4.021.2.16.590en_25092.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2420) ks4.021.2.16.590en_25092.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2420) ks4.021.2.16.590en_25092.exe | Key: | HKEY_CURRENT_USER\Software\KasperskyLabSetup\Setup21.2.16.590.0.4.0 |
| Operation: | write | Name: | TrashFiles |
Value: C:\ProgramData\Kaspersky Lab Setup Files\SAAS21.2.16.590.0.4.0
| |||
| (PID) Process: | (2420) ks4.021.2.16.590en_25092.exe | Key: | HKEY_CURRENT_USER\Software\KasperskyLabSetup\Setup21.2.16.590.0.4.0 |
| Operation: | write | Name: | TrashFiles |
Value: C:\ProgramData\Kaspersky Lab Setup Files\SAAS21.2.16.590.0.4.0
C:\ProgramData\Kaspersky Lab Setup Files
| |||
| (PID) Process: | (2420) ks4.021.2.16.590en_25092.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2420) ks4.021.2.16.590en_25092.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2420) ks4.021.2.16.590en_25092.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2420) ks4.021.2.16.590en_25092.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
531
Suspicious files
175
Text files
971
Unknown types
165
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2420 | ks4.021.2.16.590en_25092.exe | C:\Users\admin\AppData\Local\Temp\Cab8CBE.tmp | — | |
MD5:— | SHA256:— | |||
| 2420 | ks4.021.2.16.590en_25092.exe | C:\Users\admin\AppData\Local\Temp\Tar8CBF.tmp | — | |
MD5:— | SHA256:— | |||
| 2420 | ks4.021.2.16.590en_25092.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\X3PWIF8E.txt | — | |
MD5:— | SHA256:— | |||
| 2656 | ks4.021.2.16.590en_25092.exe | C:\Users\admin\AppData\Local\Temp\kl-setup-2020-12-24-06-21-39_SAAS.21.2.16.590.log | — | |
MD5:— | SHA256:— | |||
| 2420 | ks4.021.2.16.590en_25092.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_592839A8569F831D0F2306AE4BB5C24B | binary | |
MD5:— | SHA256:— | |||
| 2656 | ks4.021.2.16.590en_25092.exe | C:\ProgramData\Kaspersky Lab Setup Files\SAAS21.2.16.590.0.4.0\common.z | — | |
MD5:— | SHA256:— | |||
| 2656 | ks4.021.2.16.590en_25092.exe | C:\ProgramData\Kaspersky Lab Setup Files\SAAS21.2.16.590.0.4.0\coreproduct.z | — | |
MD5:— | SHA256:— | |||
| 2656 | ks4.021.2.16.590en_25092.exe | C:\ProgramData\Kaspersky Lab Setup Files\SAAS21.2.16.590.0.4.0\eula_gdpr_en.txt | gmc | |
MD5:— | SHA256:— | |||
| 2656 | ks4.021.2.16.590en_25092.exe | C:\Users\admin\AppData\Local\Temp\47731565-45B0-11EB-AEEC-12A9866C77DE\TEST_WPF.EXE | executable | |
MD5:— | SHA256:— | |||
| 2420 | ks4.021.2.16.590en_25092.exe | C:\Users\admin\AppData\Local\Temp\EE93DEF20B54BE11EACE219A68C677ED\setup.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
30
DNS requests
32
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2544 | avp.exe | HEAD | 200 | 130.117.190.203:80 | http://touch.kaspersky.com/ | unknown | — | — | whitelisted |
2420 | ks4.021.2.16.590en_25092.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEArLKLpGXuU5CHZ0cPPNxhI%3D | US | der | 471 b | whitelisted |
2544 | avp.exe | GET | 200 | 93.159.228.11:80 | http://pki.kaspersky.com/level1/cdp/KasperskyLabPublicServicesRootCertificationAuthority.crl | RU | der | 835 b | whitelisted |
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEArLKLpGXuU5CHZ0cPPNxhI%3D | US | der | 471 b | whitelisted |
2544 | avp.exe | GET | 200 | 93.159.228.11:80 | http://pki.kaspersky.com/level3/cdp/KasperskyLabUCPServiceCertificationAuthority.crl | RU | der | 2.37 Kb | whitelisted |
2420 | ks4.021.2.16.590en_25092.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEArLKLpGXuU5CHZ0cPPNxhI%3D | US | der | 471 b | whitelisted |
2656 | ks4.021.2.16.590en_25092.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
2544 | avp.exe | GET | 200 | 93.159.228.11:80 | http://pki.kaspersky.com/level2/cdp/KasperskyLabPublicServicesPolicyCertificationAuthority.crl | RU | der | 837 b | whitelisted |
2656 | ks4.021.2.16.590en_25092.exe | GET | 301 | 81.19.104.200:80 | http://redirect.kaspersky.com/slideshow_default | ES | html | 246 b | suspicious |
2656 | ks4.021.2.16.590en_25092.exe | GET | 301 | 81.19.104.200:80 | http://redirect.kaspersky.com/slideshow_default | ES | html | 246 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2420 | ks4.021.2.16.590en_25092.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2656 | ks4.021.2.16.590en_25092.exe | 81.19.104.200:443 | redirect.kaspersky.com | NTT America, Inc. | ES | suspicious |
2656 | ks4.021.2.16.590en_25092.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2656 | ks4.021.2.16.590en_25092.exe | 81.19.104.200:80 | redirect.kaspersky.com | NTT America, Inc. | ES | suspicious |
2656 | ks4.021.2.16.590en_25092.exe | 193.45.6.4:443 | dm.s.kaspersky-labs.com | Telia Company AB | SE | suspicious |
2656 | ks4.021.2.16.590en_25092.exe | 77.74.178.29:443 | www.not.existing.kaspersky.com | Kaspersky Lab AO | RU | malicious |
2544 | avp.exe | 130.117.190.203:80 | touch.kaspersky.com | Cogent Communications | — | suspicious |
2544 | avp.exe | 130.117.190.215:443 | — | Cogent Communications | — | unknown |
2544 | avp.exe | 13.69.68.25:443 | ipm-klca.kaspersky.com | Microsoft Corporation | NL | unknown |
2544 | avp.exe | 67.26.72.113:443 | ipm.kaspersky.com | Level 3 Communications, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dm.s.kaspersky-labs.com |
| suspicious |
ocsp.digicert.com |
| whitelisted |
redirect.kaspersky.com |
| suspicious |
www.not.existing.kaspersky.com |
| malicious |
touch.kaspersky.com |
| whitelisted |
ksn-tcert-geo.kaspersky-labs.com |
| unknown |
ipm-klca.kaspersky.com |
| suspicious |
pki.kaspersky.com |
| whitelisted |
ipm.kaspersky.com |
| suspicious |
statistic.content.ipm-klca.kaspersky.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2656 | ks4.021.2.16.590en_25092.exe | Misc activity | APP [PTsecurity] Kaspersky Downloader |
2656 | ks4.021.2.16.590en_25092.exe | Misc activity | APP [PTsecurity] Kaspersky Downloader |
2656 | ks4.021.2.16.590en_25092.exe | Misc activity | APP [PTsecurity] Kaspersky Downloader |
3 ETPRO signatures available at the full report
Process | Message |
|---|---|
avp.exe | rmt Name resolution: register property PR_REMOTE_MANAGER_PROP |
avp.exe | |
avp.exe | rmt Name resolution: find property PR_REMOTE_MANAGER_PROP, 12582912 |
avp.exe | |
avp.exe | rmt Name resolution: find property by id 1355283260 |
avp.exe | |
avp.exe | rmt Name resolution: property registered successfully, id 1355283260 |
avp.exe | |
avp.exe | rmt Name resolution: register property cpnPRAGUE_REMOTE_API |
avp.exe | |