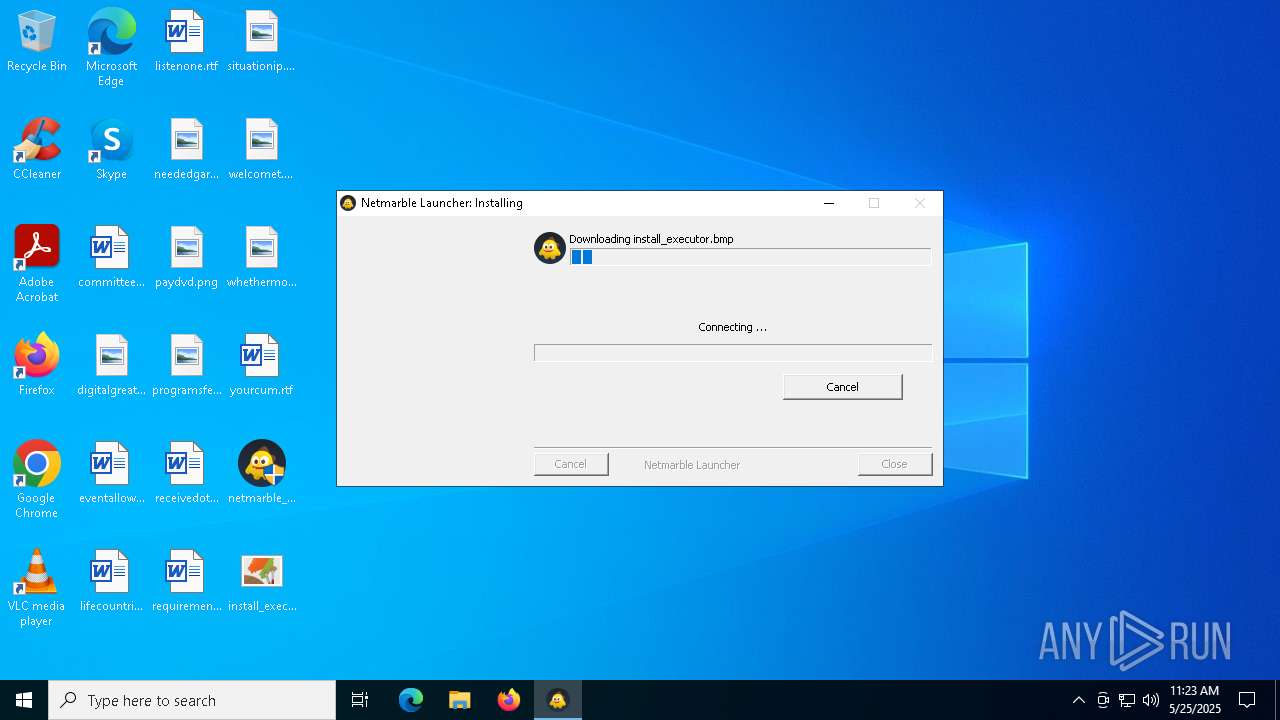
| File name: | netmarble_sololv_A_installer_16129.exe |
| Full analysis: | https://app.any.run/tasks/3a2aa1b1-a36e-4997-86f5-b494fce58715 |
| Verdict: | Malicious activity |
| Analysis date: | May 25, 2025, 11:23:12 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 66FA3768FA3CDD32FD6996ED4FA8680D |
| SHA1: | FDD88EB979285A76F298671721BAA422A8938DDB |
| SHA256: | E8CA8FA665C4DB5200CB303B012D0C667352295C097A7675BEA45B954CA69040 |
| SSDEEP: | 6144:b0wiXMlrOY8PZ5frVtvKD4oTDnwtWhwZoIRMWmdmWtHX:iXsEZ5frVtvKdPnc8wNRk |
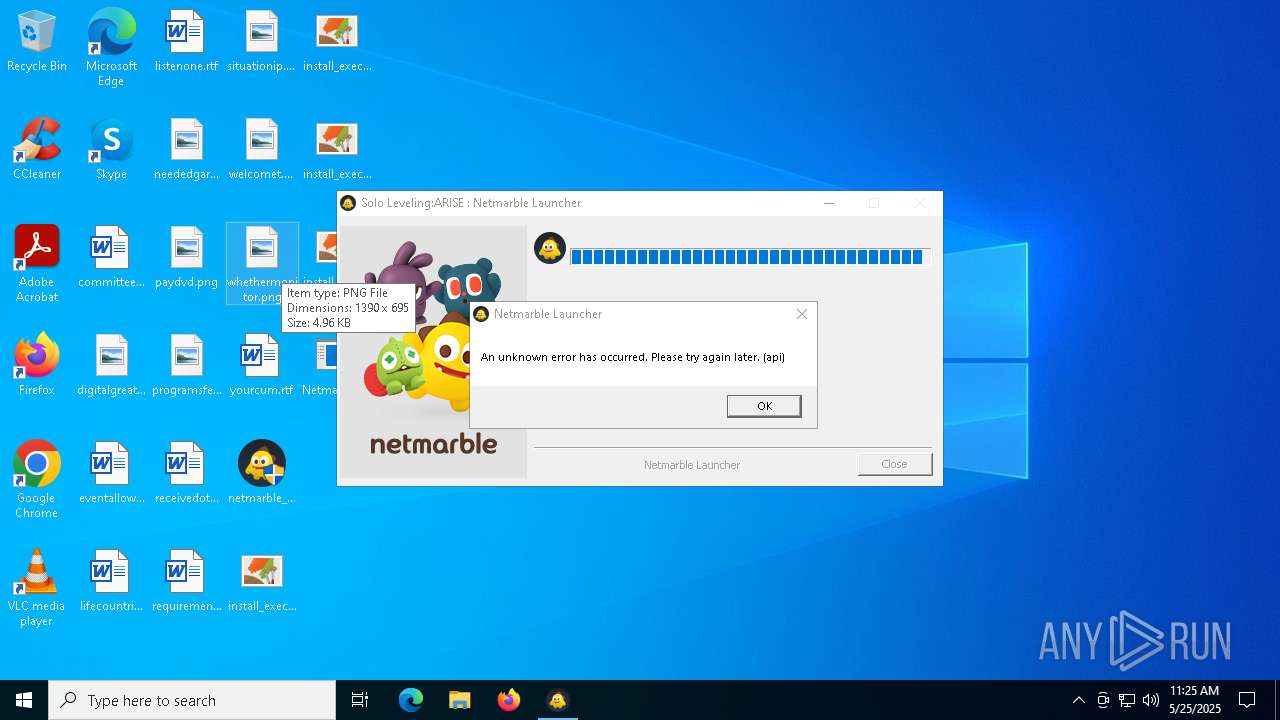
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- netmarble_sololv_A_installer_16129.exe (PID: 7572)
Reads security settings of Internet Explorer
- netmarble_sololv_A_installer_16129.exe (PID: 7572)
There is functionality for taking screenshot (YARA)
- netmarble_sololv_A_installer_16129.exe (PID: 7572)
INFO
Checks supported languages
- netmarble_sololv_A_installer_16129.exe (PID: 7572)
Create files in a temporary directory
- netmarble_sololv_A_installer_16129.exe (PID: 7572)
Reads the computer name
- netmarble_sololv_A_installer_16129.exe (PID: 7572)
Checks proxy server information
- netmarble_sololv_A_installer_16129.exe (PID: 7572)
- slui.exe (PID: 4488)
The sample compiled with english language support
- netmarble_sololv_A_installer_16129.exe (PID: 7572)
Reads the machine GUID from the registry
- netmarble_sololv_A_installer_16129.exe (PID: 7572)
Reads the software policy settings
- netmarble_sololv_A_installer_16129.exe (PID: 7572)
- slui.exe (PID: 4488)
Creates files or folders in the user directory
- netmarble_sololv_A_installer_16129.exe (PID: 7572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:09:25 21:57:46+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 27136 |
| InitializedDataSize: | 186880 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x352d |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
131
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4488 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
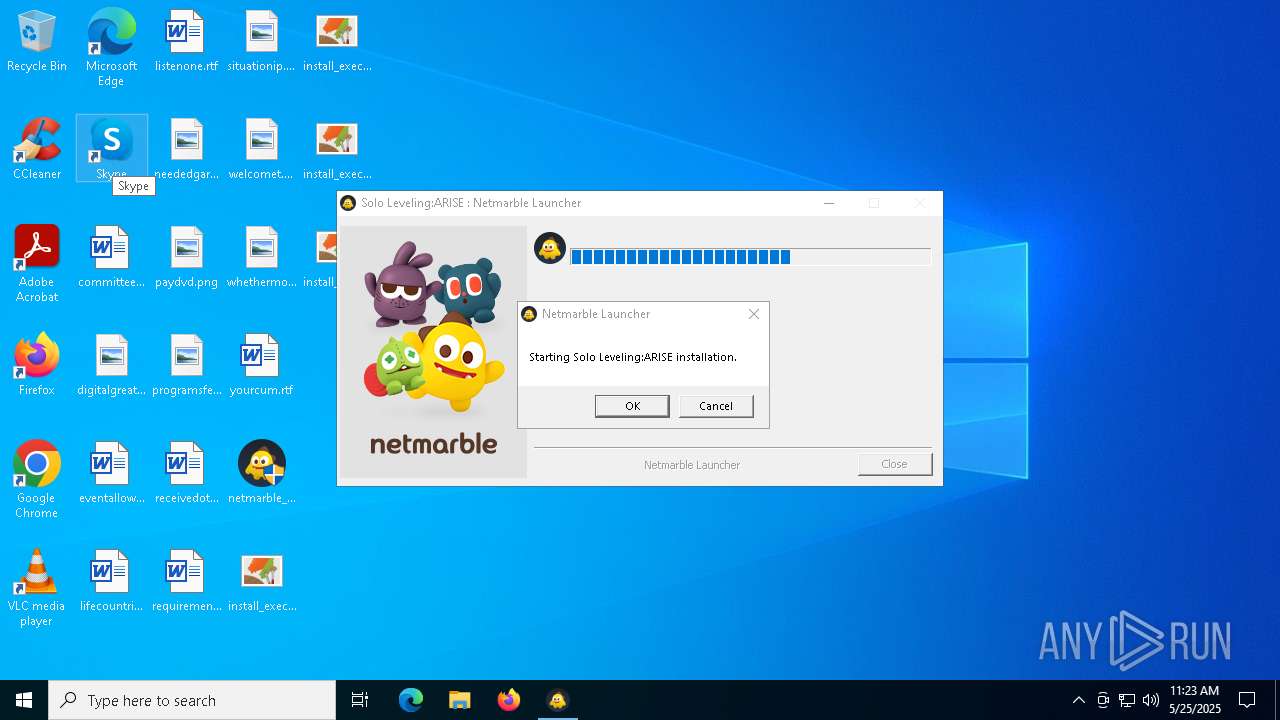
| 7472 | "C:\Users\admin\Desktop\netmarble_sololv_A_installer_16129.exe" | C:\Users\admin\Desktop\netmarble_sololv_A_installer_16129.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 7572 | "C:\Users\admin\Desktop\netmarble_sololv_A_installer_16129.exe" | C:\Users\admin\Desktop\netmarble_sololv_A_installer_16129.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 2 Modules
| |||||||||||||||
Total events
6 831
Read events
6 828
Write events
3
Delete events
0
Modification events
| (PID) Process: | (7572) netmarble_sololv_A_installer_16129.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7572) netmarble_sololv_A_installer_16129.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7572) netmarble_sololv_A_installer_16129.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
2
Suspicious files
2
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7572 | netmarble_sololv_A_installer_16129.exe | C:\Users\admin\AppData\Local\Temp\nskC391.tmp\INetC.dll | executable | |
MD5:40D7ECA32B2F4D29DB98715DD45BFAC5 | SHA256:85E03805F90F72257DD41BFDAA186237218BBB0EC410AD3B6576A88EA11DCCB9 | |||
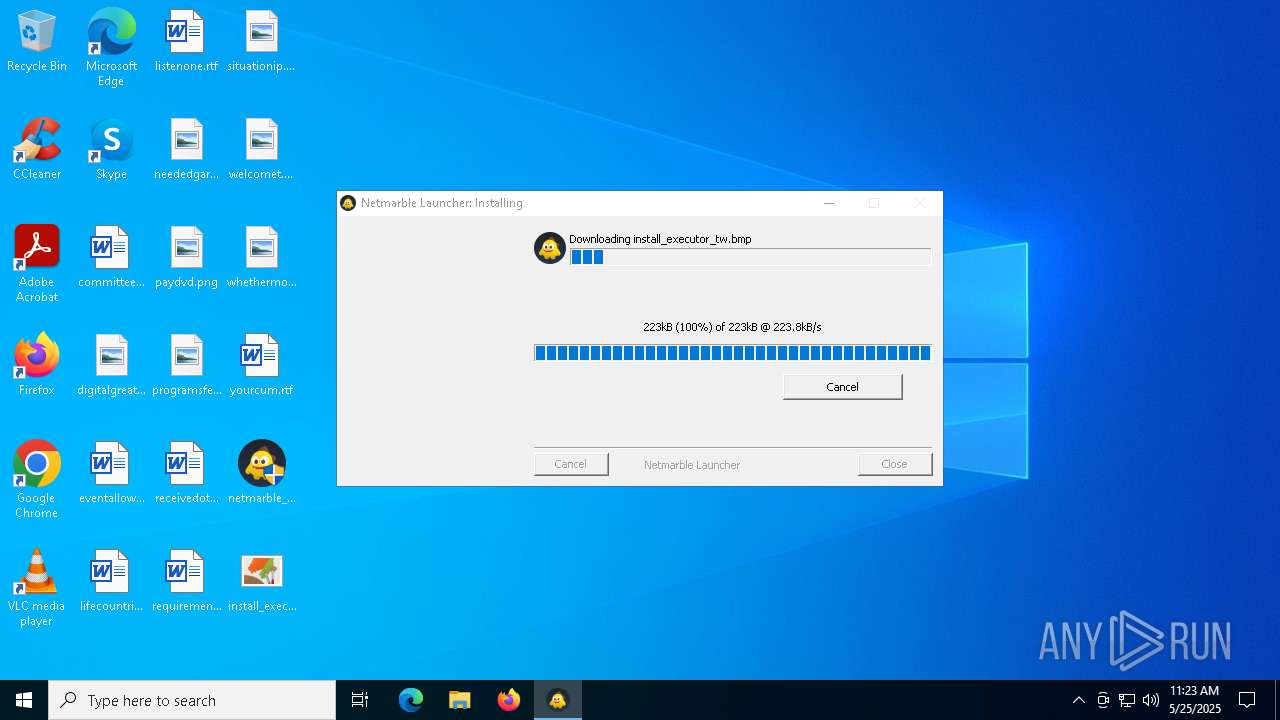
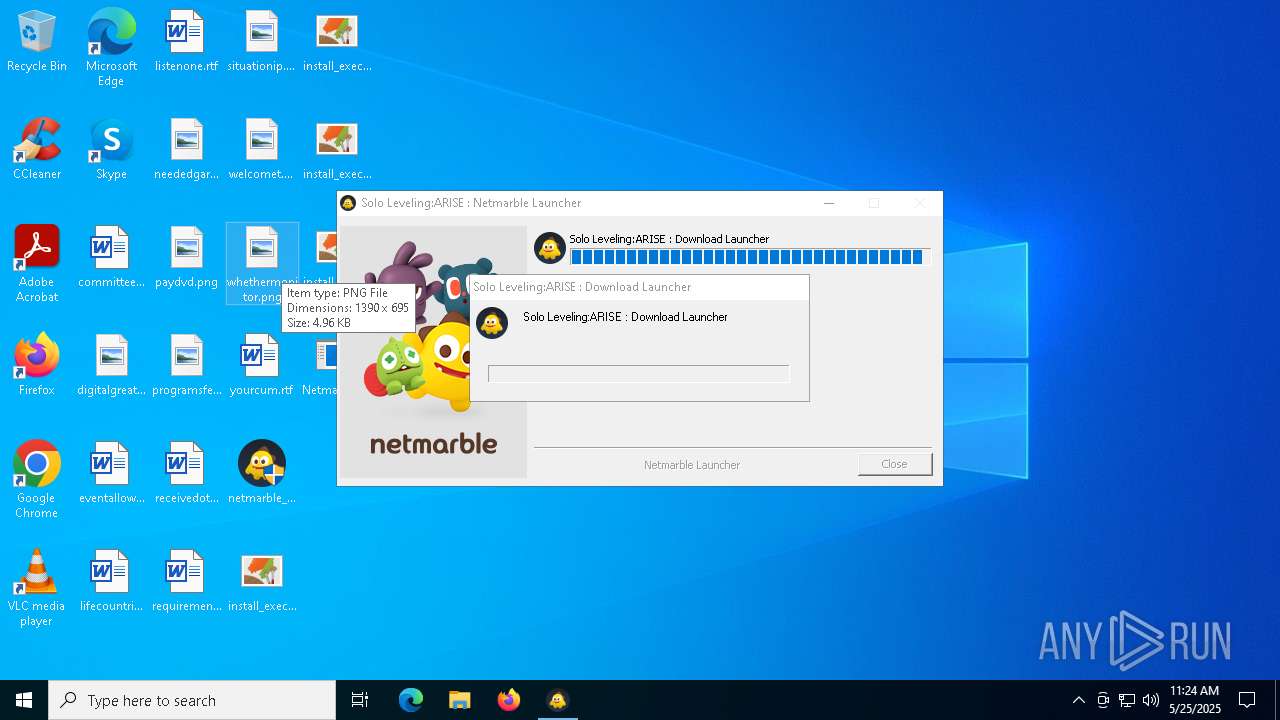
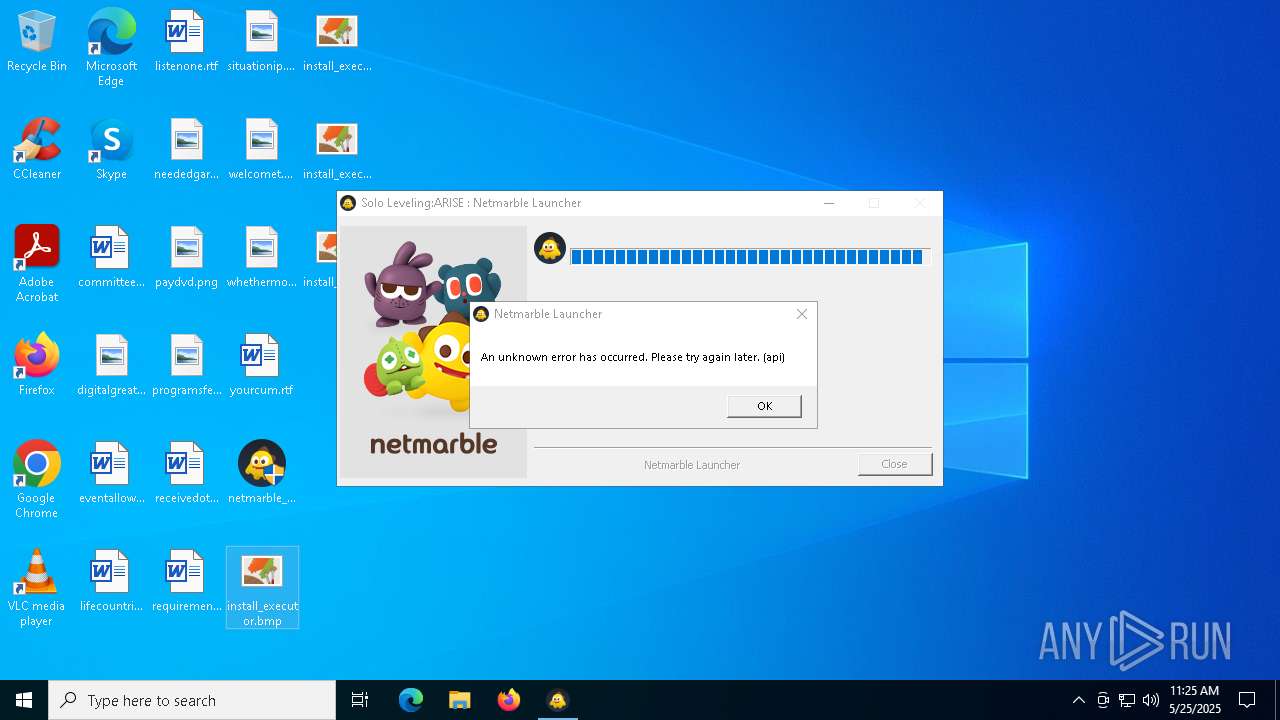
| 7572 | netmarble_sololv_A_installer_16129.exe | C:\Users\admin\Desktop\install_executor_ko.bmp | image | |
MD5:A0F3AC3BD2F523C5B51A93EF366AEDAA | SHA256:CAAD87B9DD7288BAF7154E7935B42F7AD9A2243B98F5AFB73B29162514298558 | |||
| 7572 | netmarble_sololv_A_installer_16129.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\install_executor[1].bmp | image | |
MD5:37F2D2343740B8FE09472EA61569AA74 | SHA256:201C4E43041F2A215B76E360D57EFF9BC4B632A6DFB9D5C5379992274DB6BF9D | |||
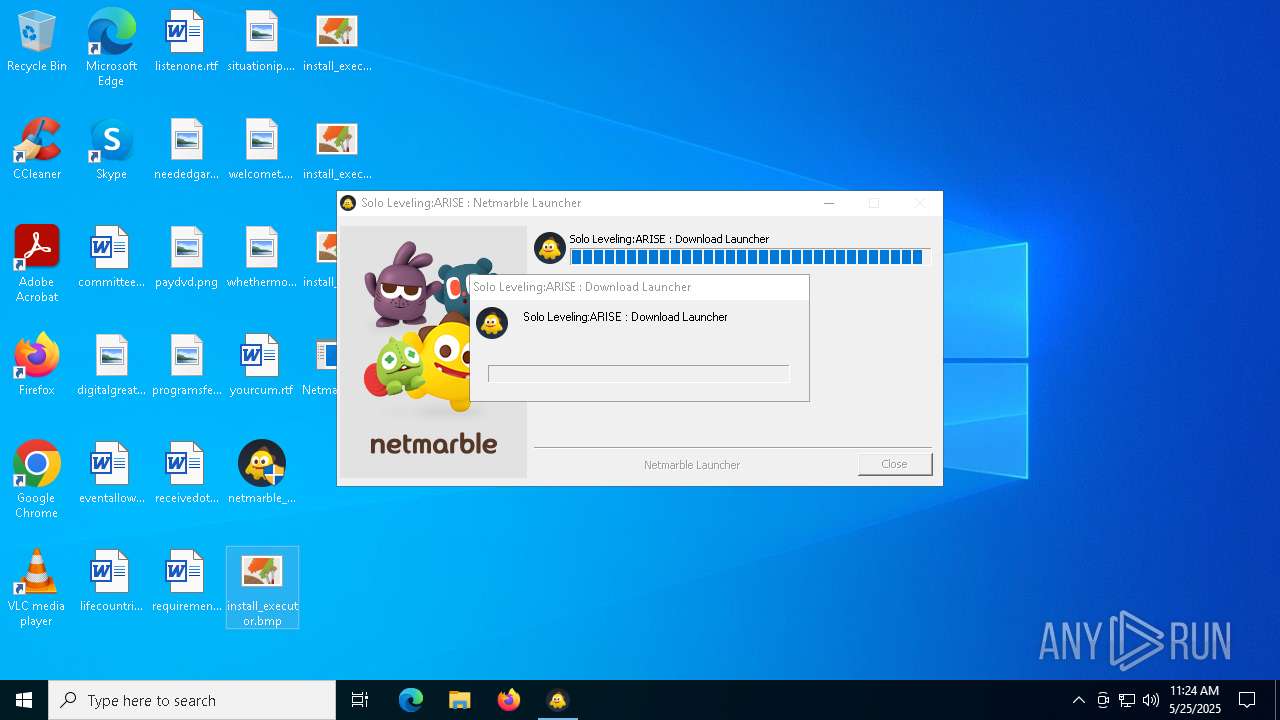
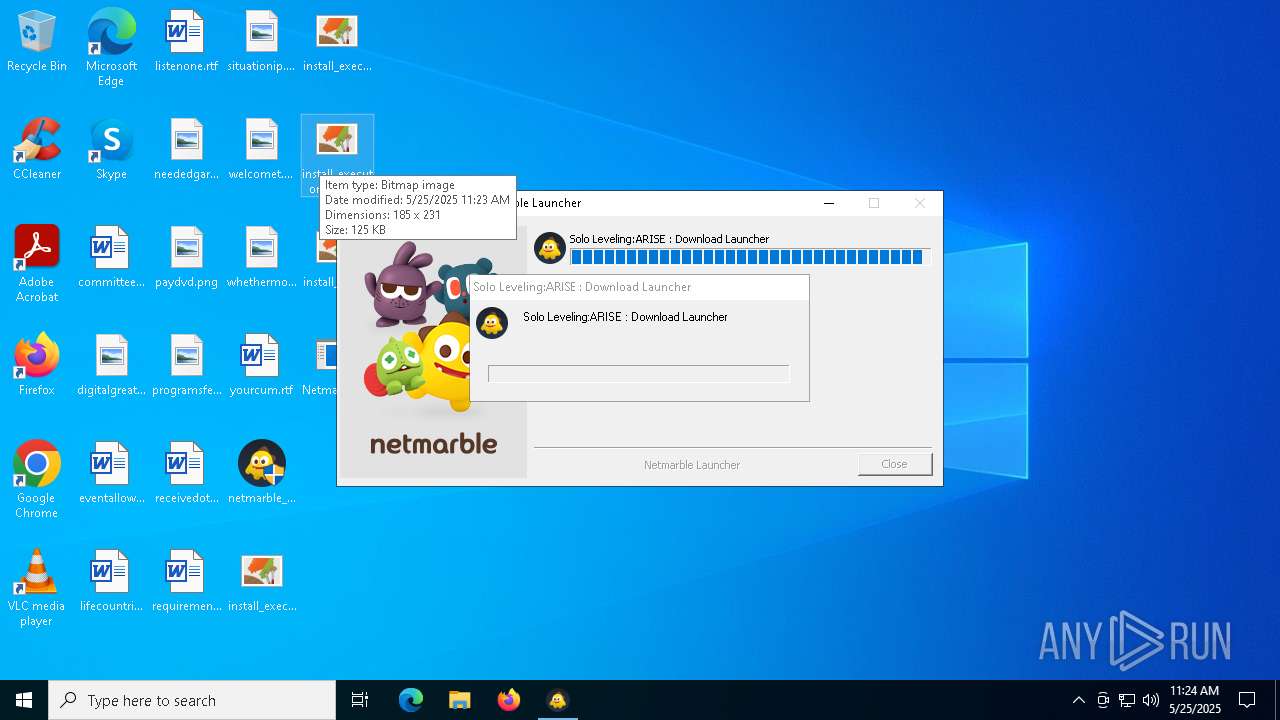
| 7572 | netmarble_sololv_A_installer_16129.exe | C:\Users\admin\Desktop\install_executor.bmp | image | |
MD5:37F2D2343740B8FE09472EA61569AA74 | SHA256:201C4E43041F2A215B76E360D57EFF9BC4B632A6DFB9D5C5379992274DB6BF9D | |||
| 7572 | netmarble_sololv_A_installer_16129.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\E4DJRUXW\install_executor_cn[1].bmp | image | |
MD5:A7195998D7F70373FD8389BF5609E37B | SHA256:3F53704EE0FCE9934C547E227D22A371503A4335677F84A3F20D1BC94366E3DD | |||
| 7572 | netmarble_sololv_A_installer_16129.exe | C:\Users\admin\Desktop\install_executor_cn.bmp | image | |
MD5:A7195998D7F70373FD8389BF5609E37B | SHA256:3F53704EE0FCE9934C547E227D22A371503A4335677F84A3F20D1BC94366E3DD | |||
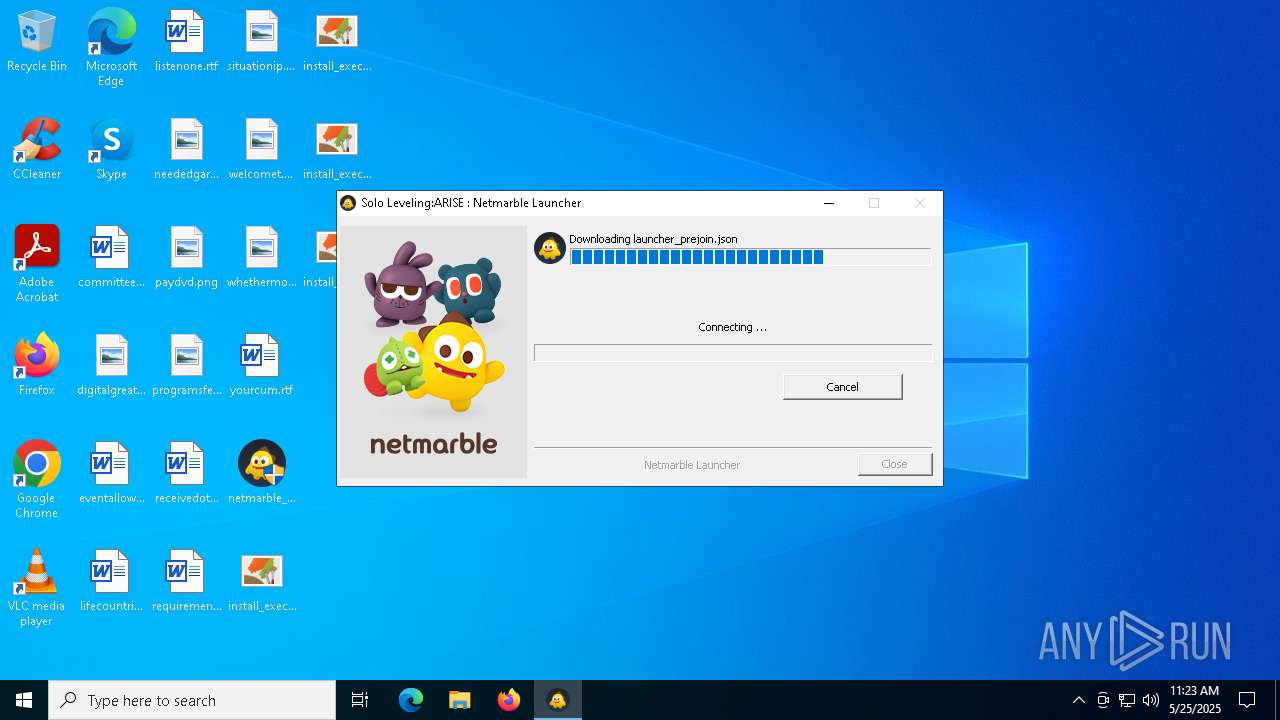
| 7572 | netmarble_sololv_A_installer_16129.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\AH8CR9J5\current[1].json | binary | |
MD5:A70044EACA03A1E36A0D32FBFB9B8378 | SHA256:0914F93E61B6BA44927527D1D68B011781460179382C697F86522335B40C4105 | |||
| 7572 | netmarble_sololv_A_installer_16129.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\install_executor_ko[1].bmp | image | |
MD5:A0F3AC3BD2F523C5B51A93EF366AEDAA | SHA256:CAAD87B9DD7288BAF7154E7935B42F7AD9A2243B98F5AFB73B29162514298558 | |||
| 7572 | netmarble_sololv_A_installer_16129.exe | C:\Users\admin\Desktop\install_executor_tw.bmp | image | |
MD5:FE8935E80091A32907EB27C43F68CD99 | SHA256:EADD66551D972986C99B5F012C1F593B07F3C6879AFBB794967686F995F0D575 | |||
| 7572 | netmarble_sololv_A_installer_16129.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\install_executor_tw[1].bmp | image | |
MD5:FE8935E80091A32907EB27C43F68CD99 | SHA256:EADD66551D972986C99B5F012C1F593B07F3C6879AFBB794967686F995F0D575 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
51
DNS requests
22
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 193.108.153.170:443 | https://sgimage.netmarble.com/cpp/launcher/installer/image/install_executor_cn.bmp | unknown | image | 125 Kb | whitelisted |
— | — | POST | 200 | 40.126.31.130:443 | https://login.live.com/RST2.srf | unknown | — | — | whitelisted |
— | — | POST | 400 | 40.126.31.130:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
— | — | POST | 400 | 40.126.31.73:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
— | — | POST | 400 | 20.190.159.128:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
— | — | POST | 400 | 40.126.31.3:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
— | — | POST | 400 | 20.190.159.75:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
— | — | POST | 400 | 20.190.159.4:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
— | — | POST | 400 | 40.126.31.128:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2432 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7572 | netmarble_sololv_A_installer_16129.exe | 193.108.153.170:443 | sgimage.netmarble.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
sgimage.netmarble.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
apis.netmarble.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
— | — | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
— | — | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
— | — | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
— | — | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
— | — | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
— | — | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
— | — | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |