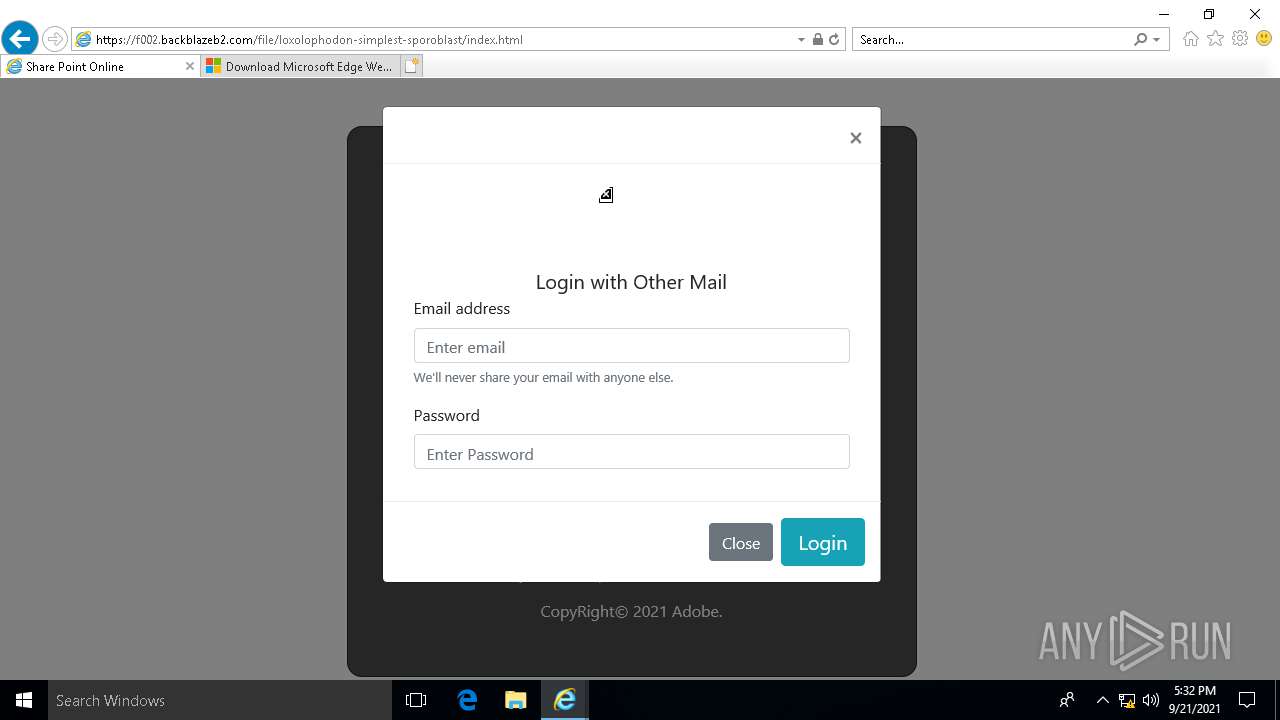
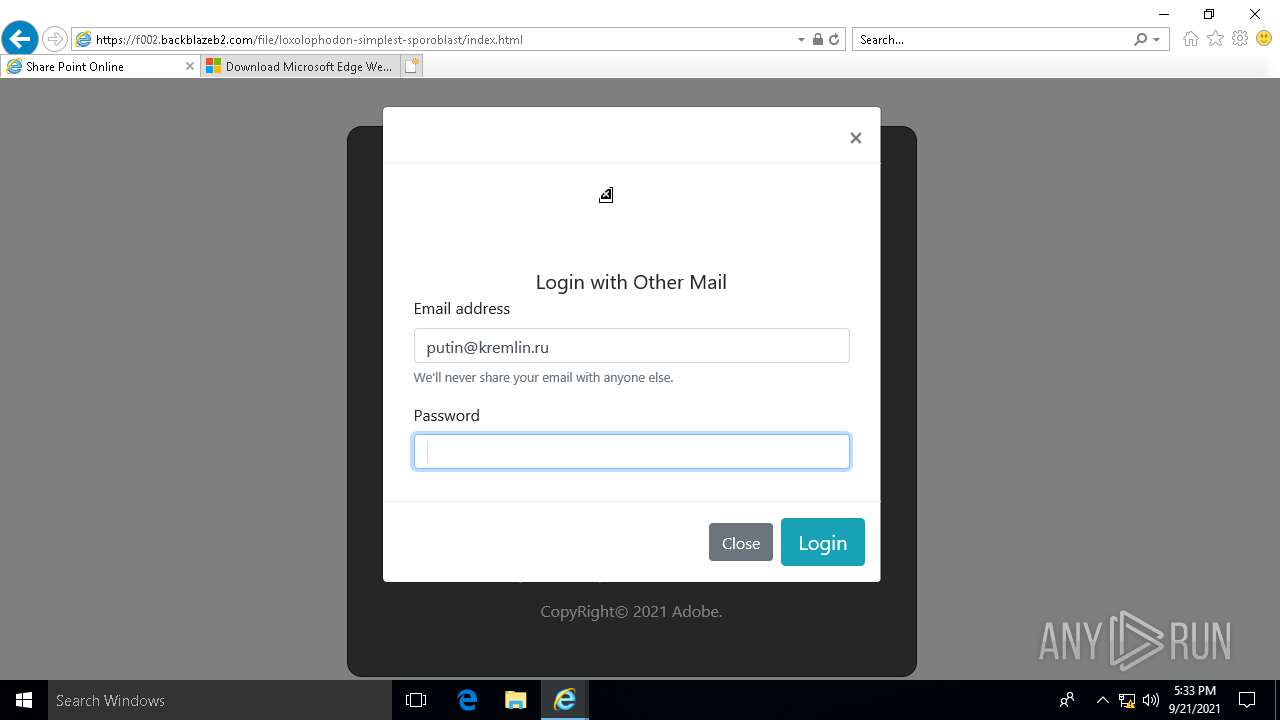
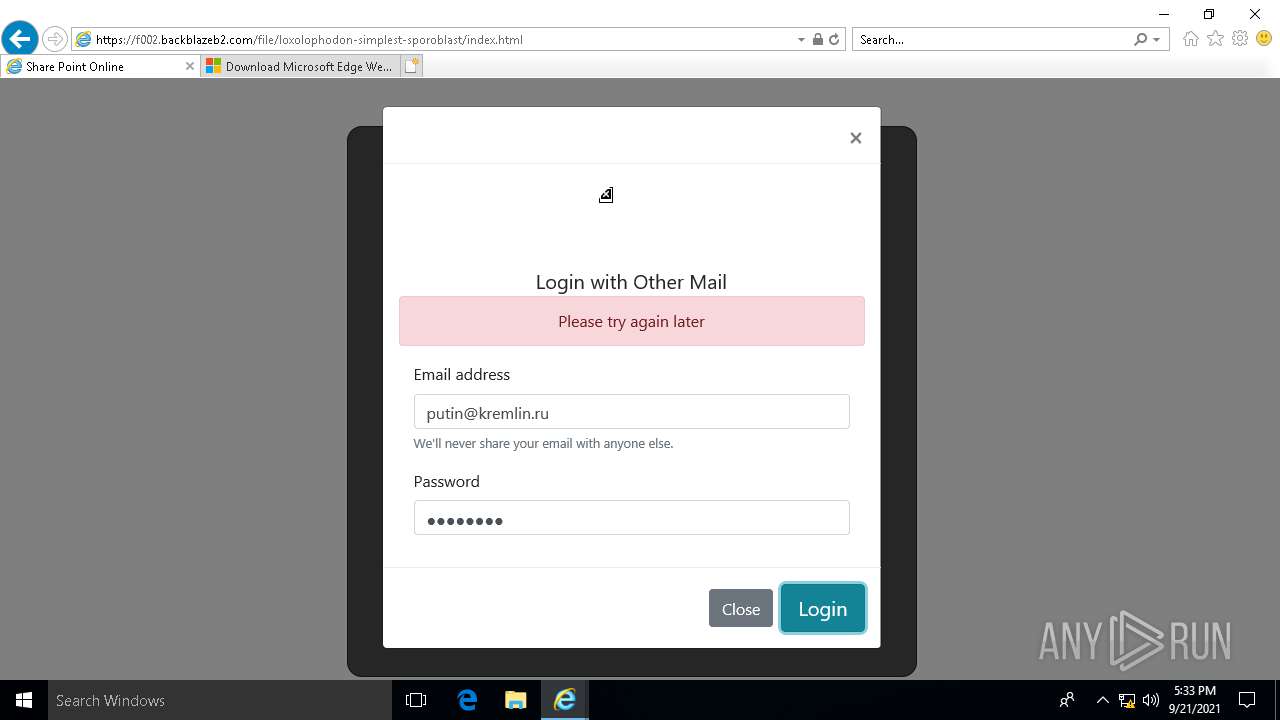
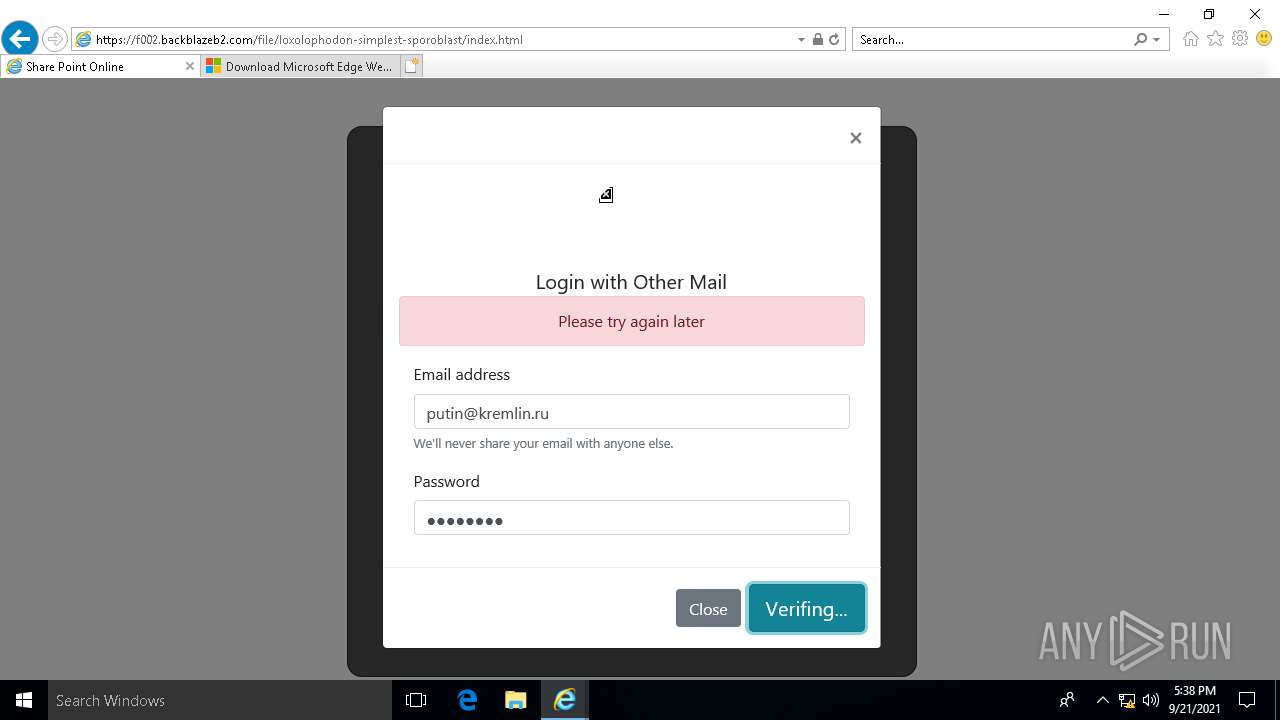
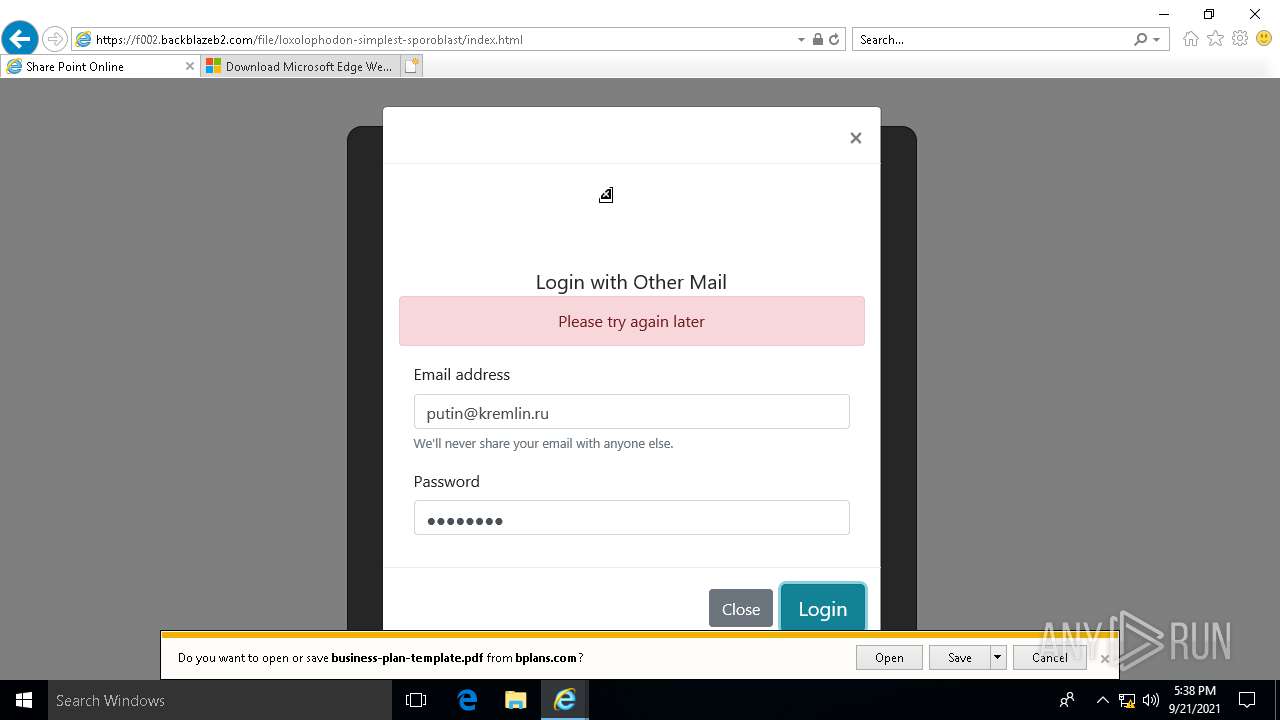
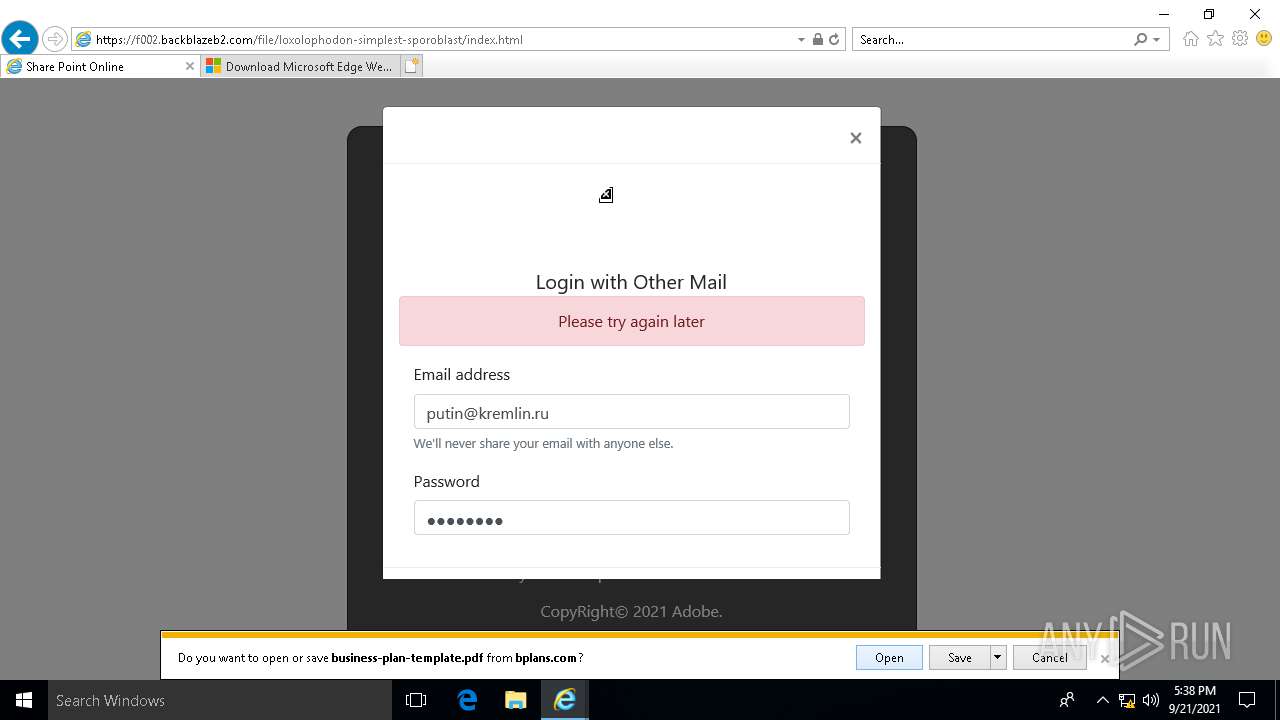
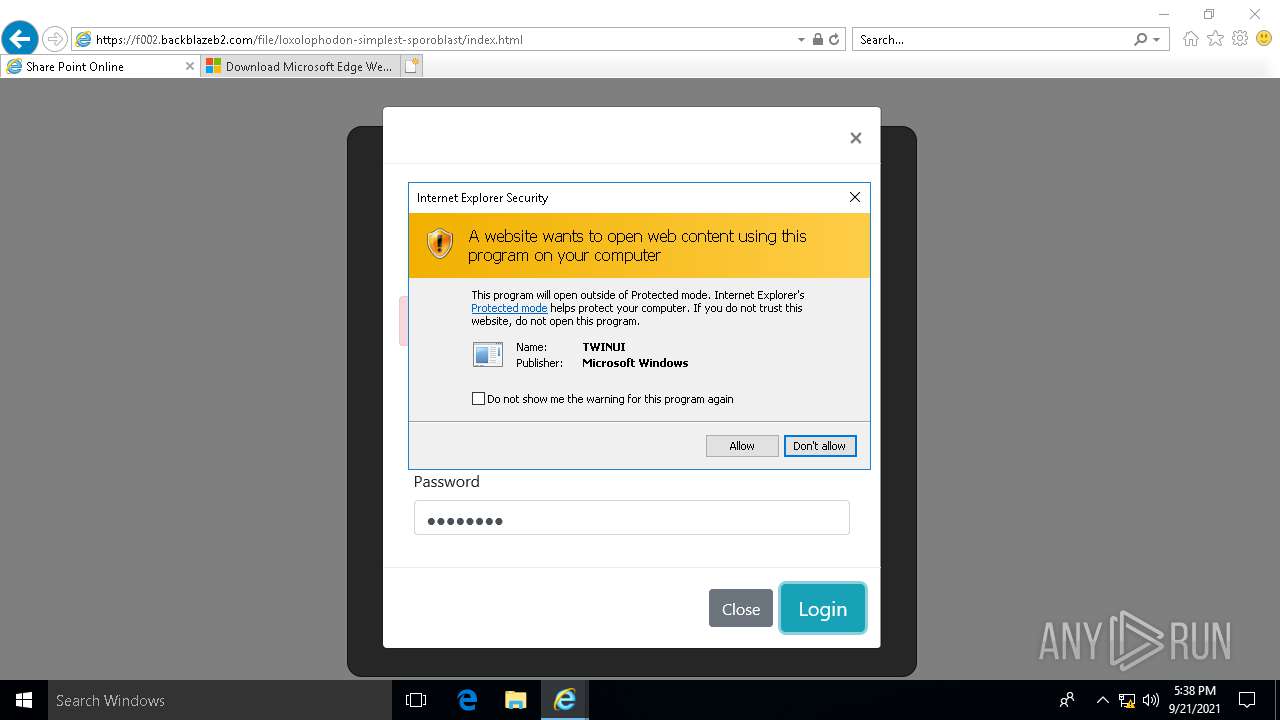
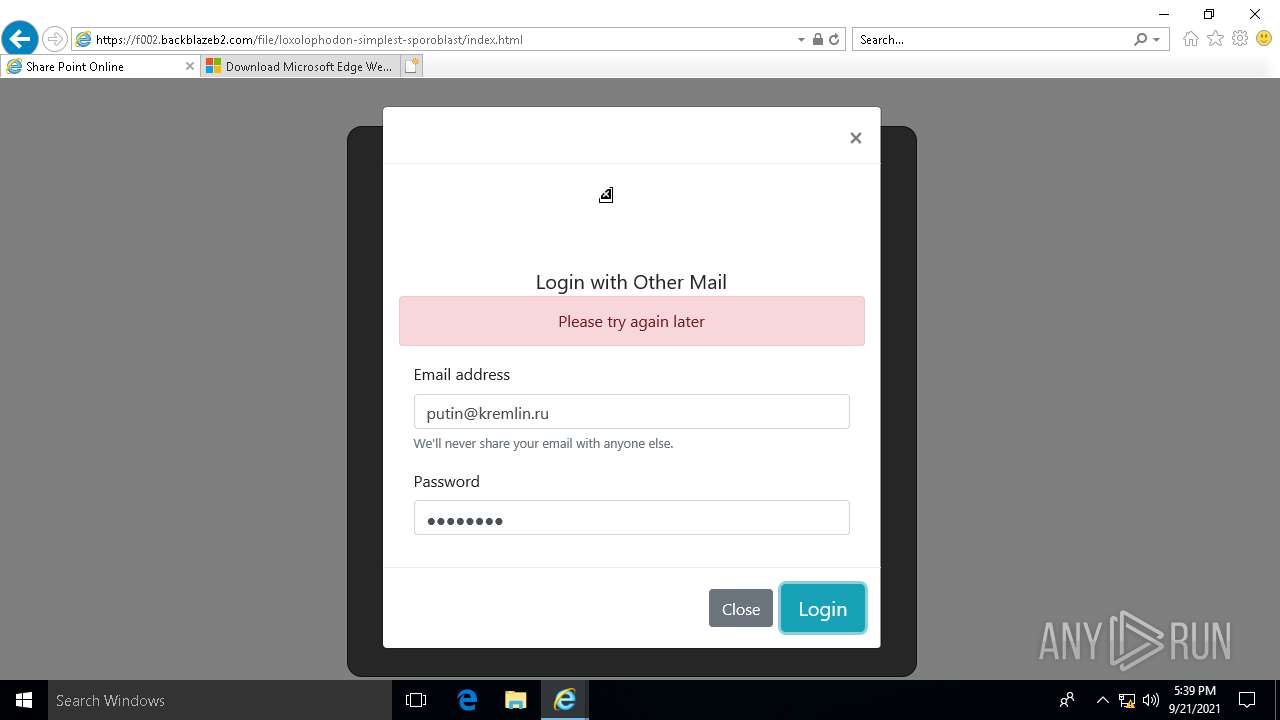
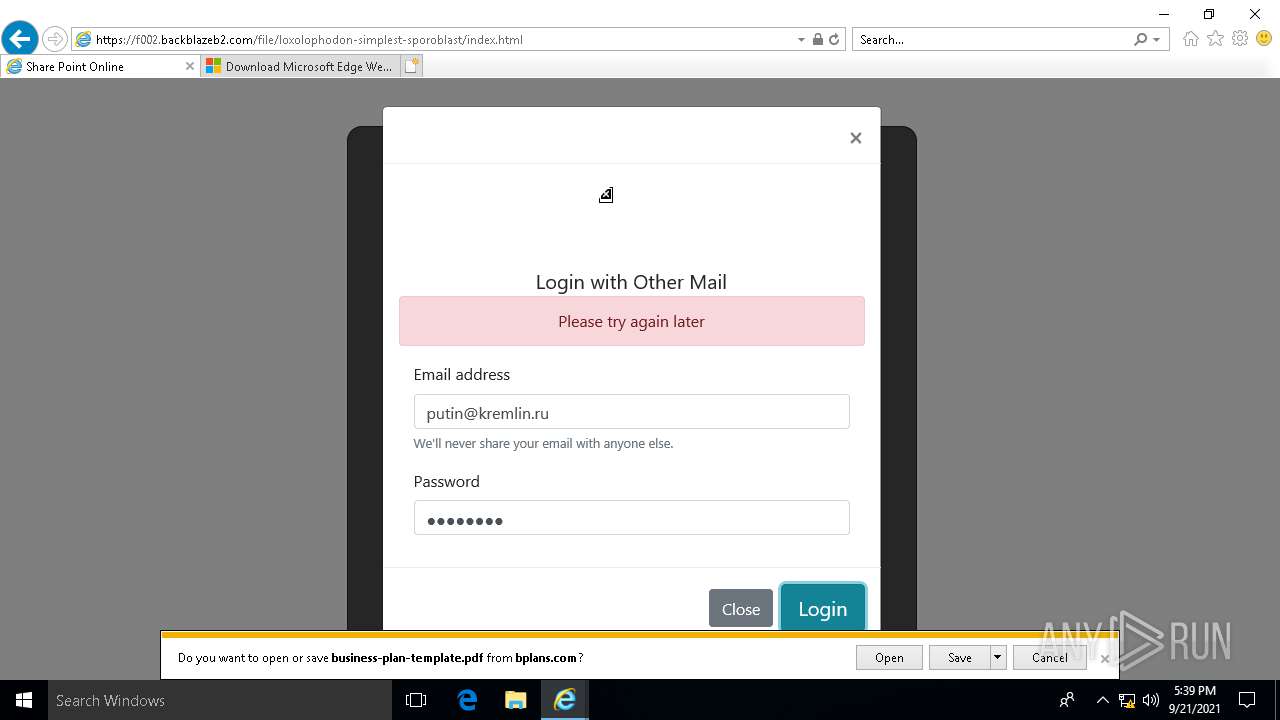
| URL: | https://f002.backblazeb2.com/file/loxolophodon-simplest-sporoblast/index.html |
| Full analysis: | https://app.any.run/tasks/5497ac8e-1da7-43ce-b432-7e94d8d79480 |
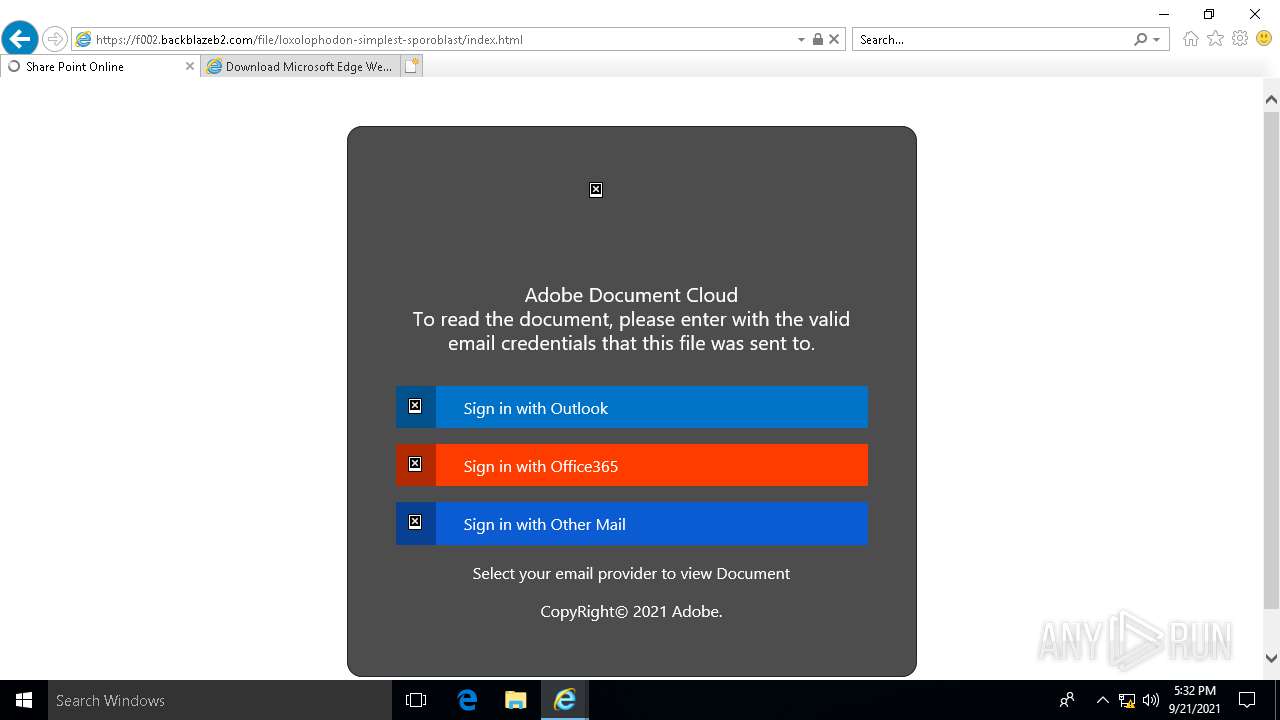
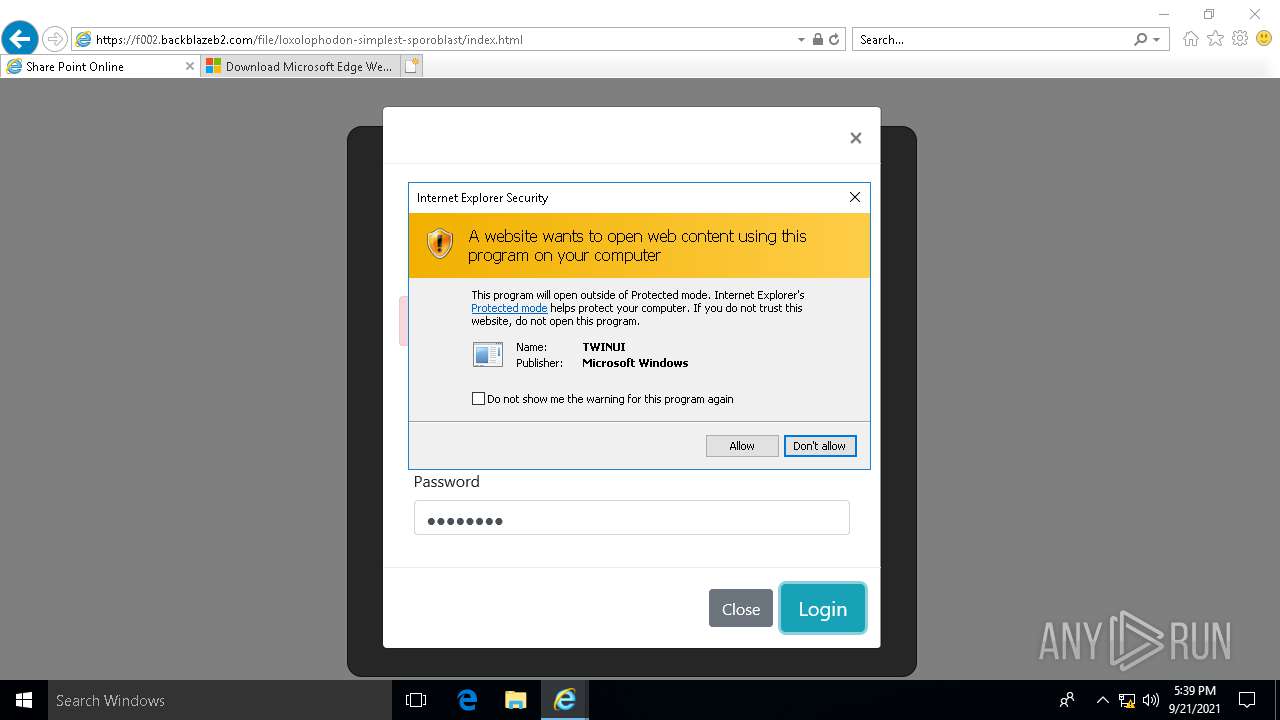
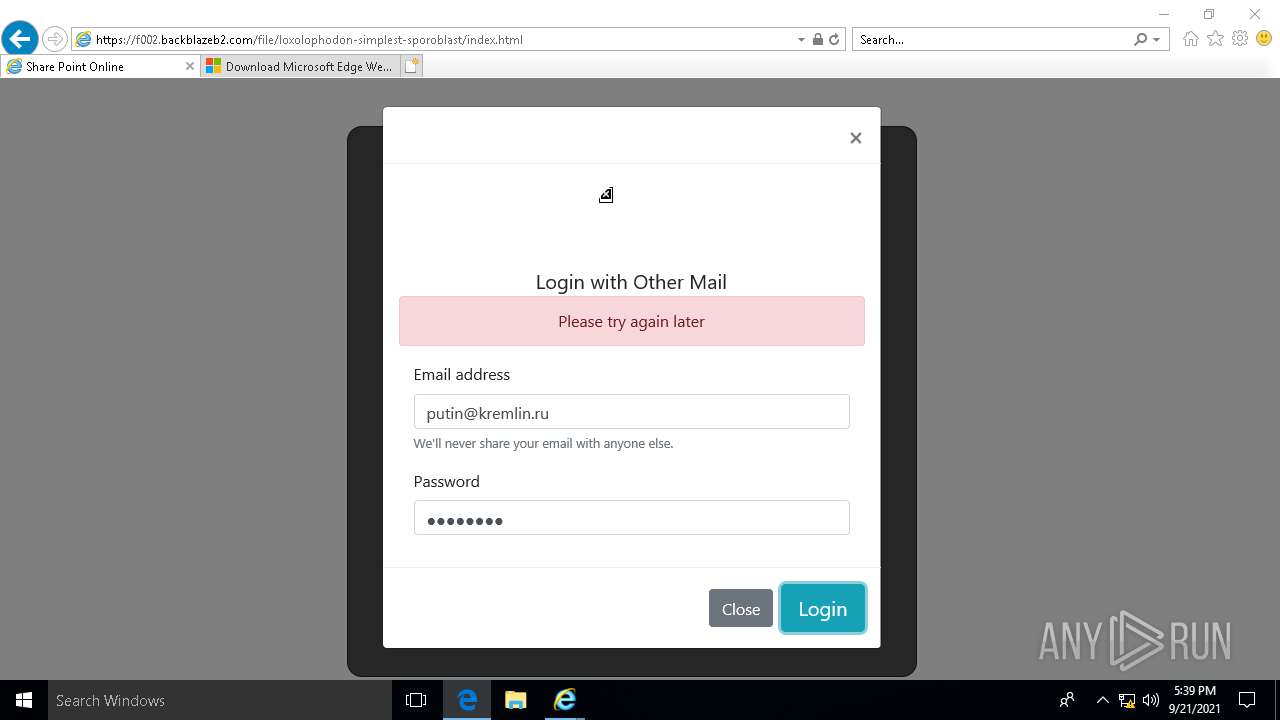
| Verdict: | Malicious activity |
| Analysis date: | September 21, 2021, 17:32:21 |
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Indicators: | |
| MD5: | 0B0E2159D3C7206A1312602E0B6A978A |
| SHA1: | CC57F869576FD7AE8301C9EF27C43708EB6649EA |
| SHA256: | E8C4A0FF439D8EC991AA0327A7F0C3DF0F41D4588AE40703E7E6FA28B624DAE4 |
| SSDEEP: | 3:N8n9oX3ZzonIj9ISzKe1aG:29oXJjKe8G |
MALICIOUS
Scans artifacts that could help determine the target
- iexplore.exe (PID: 5372)
SUSPICIOUS
Reads Microsoft Outlook installation path
- IEXPLORE.EXE (PID: 4392)
- IEXPLORE.EXE (PID: 2544)
Executed via COM
- ApplicationFrameHost.exe (PID: 4328)
- MicrosoftEdge.exe (PID: 5588)
- browser_broker.exe (PID: 5208)
- MicrosoftEdgeCP.exe (PID: 3704)
- MicrosoftEdgeCP.exe (PID: 4628)
- MicrosoftPdfReader.exe (PID: 5520)
- MicrosoftEdgeCP.exe (PID: 3012)
- MicrosoftEdgeCP.exe (PID: 3848)
Reads the computer name
- MicrosoftEdge.exe (PID: 5588)
- MicrosoftEdgeCP.exe (PID: 3704)
- browser_broker.exe (PID: 5208)
- MicrosoftEdgeCP.exe (PID: 4628)
- MicrosoftEdgeCP.exe (PID: 3012)
- MicrosoftPdfReader.exe (PID: 5520)
- MicrosoftEdgeCP.exe (PID: 3848)
Checks supported languages
- MicrosoftEdge.exe (PID: 5588)
- browser_broker.exe (PID: 5208)
- MicrosoftEdgeCP.exe (PID: 3704)
- MicrosoftEdgeCP.exe (PID: 4628)
- MicrosoftEdgeCP.exe (PID: 3012)
- MicrosoftPdfReader.exe (PID: 5520)
- MicrosoftEdgeCP.exe (PID: 3848)
INFO
Reads the computer name
- IEXPLORE.EXE (PID: 4392)
- iexplore.exe (PID: 5372)
- IEXPLORE.EXE (PID: 2544)
- ApplicationFrameHost.exe (PID: 4328)
Checks supported languages
- IEXPLORE.EXE (PID: 4392)
- iexplore.exe (PID: 5372)
- IEXPLORE.EXE (PID: 2544)
- ApplicationFrameHost.exe (PID: 4328)
Reads settings of System Certificates
- IEXPLORE.EXE (PID: 4392)
- IEXPLORE.EXE (PID: 2544)
- iexplore.exe (PID: 5372)
Reads internet explorer settings
- IEXPLORE.EXE (PID: 4392)
- IEXPLORE.EXE (PID: 2544)
Changes internet zones settings
- iexplore.exe (PID: 5372)
Checks Windows Trust Settings
- IEXPLORE.EXE (PID: 4392)
- iexplore.exe (PID: 5372)
- IEXPLORE.EXE (PID: 2544)
Reads the software policy settings
- IEXPLORE.EXE (PID: 4392)
- iexplore.exe (PID: 5372)
- IEXPLORE.EXE (PID: 2544)
Modifies the phishing filter of IE
- iexplore.exe (PID: 5372)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 5372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
106
Monitored processes
11
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2544 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:5372 CREDAT:9476 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3012 | "C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftEdgeCP.exe" -ServerName:ContentProcess.AppX6z3cwk4fvgady6zya12j1cw28d228a7k.mca | C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftEdgeCP.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Content Process Exit code: 0 Version: 11.00.16299.402 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3704 | "C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftEdgeCP.exe" -ServerName:ContentProcess.AppX6z3cwk4fvgady6zya12j1cw28d228a7k.mca | C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftEdgeCP.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Content Process Exit code: 1 Version: 11.00.16299.402 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3848 | "C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftEdgeCP.exe" -ServerName:ContentProcess.AppX6z3cwk4fvgady6zya12j1cw28d228a7k.mca | C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftEdgeCP.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Content Process Exit code: 0 Version: 11.00.16299.402 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4328 | C:\WINDOWS\system32\ApplicationFrameHost.exe -Embedding | C:\WINDOWS\system32\ApplicationFrameHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Application Frame Host Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4392 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:5372 CREDAT:9474 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4628 | "C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftEdgeCP.exe" -ServerName:ContentProcess.AppX6z3cwk4fvgady6zya12j1cw28d228a7k.mca | C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftEdgeCP.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Content Process Exit code: 0 Version: 11.00.16299.402 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5208 | C:\WINDOWS\system32\browser_broker.exe -Embedding | C:\WINDOWS\system32\browser_broker.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Browser_Broker Exit code: 2147500037 Version: 11.00.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5372 | "C:\Program Files\internet explorer\iexplore.exe" "https://f002.backblazeb2.com/file/loxolophodon-simplest-sporoblast/index.html" | C:\Program Files\internet explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5520 | "C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftPdfReader.exe" -ServerName:PdfReader.AppXt4g7dx0jktgcrhe5cw5qf7t4q86jznsh.mca | C:\WINDOWS\SystemApps\Microsoft.MicrosoftEdge_8wekyb3d8bbwe\MicrosoftPdfReader.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft PDF Reader Component Exit code: 1 Version: 11.00.16299.402 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
19 350
Read events
18 778
Write events
560
Delete events
12
Modification events
| (PID) Process: | (5372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkLowPart |
Value: 956341420 | |||
| (PID) Process: | (5372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkHighPart |
Value: 148313293 | |||
| (PID) Process: | (5372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (5372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30912270 | |||
| (PID) Process: | (5372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (5372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (5372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
0
Suspicious files
67
Text files
102
Unknown types
62
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4392 | IEXPLORE.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\644B8874112055B5E195ECB0E8F243A4 | binary | |
MD5:— | SHA256:— | |||
| 4392 | IEXPLORE.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:— | SHA256:— | |||
| 4392 | IEXPLORE.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\517663DFCF7D11043E01F2CB03FE0BFD | binary | |
MD5:— | SHA256:— | |||
| 4392 | IEXPLORE.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\80237EE4964FC9C409AAF55BF996A292_D46D6FA25B74360E1349F9015B5CCE53 | der | |
MD5:— | SHA256:— | |||
| 4392 | IEXPLORE.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:— | SHA256:— | |||
| 4392 | IEXPLORE.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\517663DFCF7D11043E01F2CB03FE0BFD | der | |
MD5:— | SHA256:— | |||
| 4392 | IEXPLORE.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\644B8874112055B5E195ECB0E8F243A4 | der | |
MD5:— | SHA256:— | |||
| 4392 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\2WUUROS3\index[1].htm | html | |
MD5:— | SHA256:— | |||
| 4392 | IEXPLORE.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\80237EE4964FC9C409AAF55BF996A292_D46D6FA25B74360E1349F9015B5CCE53 | binary | |
MD5:— | SHA256:— | |||
| 4392 | IEXPLORE.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F07644E38ED7C9F37D11EEC6D4335E02_3B9C2111EAE052C5BA0EC1CBB6D70DEA | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
68
TCP/UDP connections
196
DNS requests
96
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2544 | IEXPLORE.EXE | GET | 302 | 104.126.25.23:80 | http://go.microsoft.com/fwlink/?LinkId=838604 | US | — | — | whitelisted |
4392 | IEXPLORE.EXE | GET | 200 | 23.205.154.137:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgQ1W1lpapa7oF1p167WpoReBQ%3D%3D | US | der | 503 b | shared |
4392 | IEXPLORE.EXE | GET | 200 | 23.205.154.179:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | US | der | 1.16 Kb | whitelisted |
4392 | IEXPLORE.EXE | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | der | 471 b | whitelisted |
4392 | IEXPLORE.EXE | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
4392 | IEXPLORE.EXE | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
4392 | IEXPLORE.EXE | GET | 200 | 142.250.72.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQD%2FlD3sEhDdGAoAAAAA%2FPSV | US | der | 472 b | whitelisted |
4392 | IEXPLORE.EXE | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEASDadw4Hj8omz0LYxoxgB8%3D | US | der | 278 b | whitelisted |
2544 | IEXPLORE.EXE | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
4392 | IEXPLORE.EXE | GET | 200 | 142.250.72.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4392 | IEXPLORE.EXE | 206.190.215.16:443 | f002.backblazeb2.com | Unwired | US | suspicious |
4392 | IEXPLORE.EXE | 23.205.154.179:80 | crl.identrust.com | NTT America, Inc. | US | unknown |
4392 | IEXPLORE.EXE | 104.80.96.219:80 | x1.c.lencr.org | Akamai Technologies, Inc. | NL | unknown |
5372 | iexplore.exe | 206.190.215.16:443 | f002.backblazeb2.com | Unwired | US | suspicious |
4392 | IEXPLORE.EXE | 23.205.154.137:80 | r3.o.lencr.org | NTT America, Inc. | US | unknown |
4392 | IEXPLORE.EXE | 13.68.247.210:443 | urs.microsoft.com | Microsoft Corporation | US | unknown |
4392 | IEXPLORE.EXE | 142.250.188.234:443 | ajax.googleapis.com | Google Inc. | US | unknown |
2544 | IEXPLORE.EXE | 104.126.25.23:80 | go.microsoft.com | GTT Communications Inc. | US | unknown |
4392 | IEXPLORE.EXE | 72.21.91.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2544 | IEXPLORE.EXE | 104.126.25.23:443 | go.microsoft.com | GTT Communications Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
f002.backblazeb2.com |
| suspicious |
crl.identrust.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
urs.microsoft.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2544 | IEXPLORE.EXE | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |