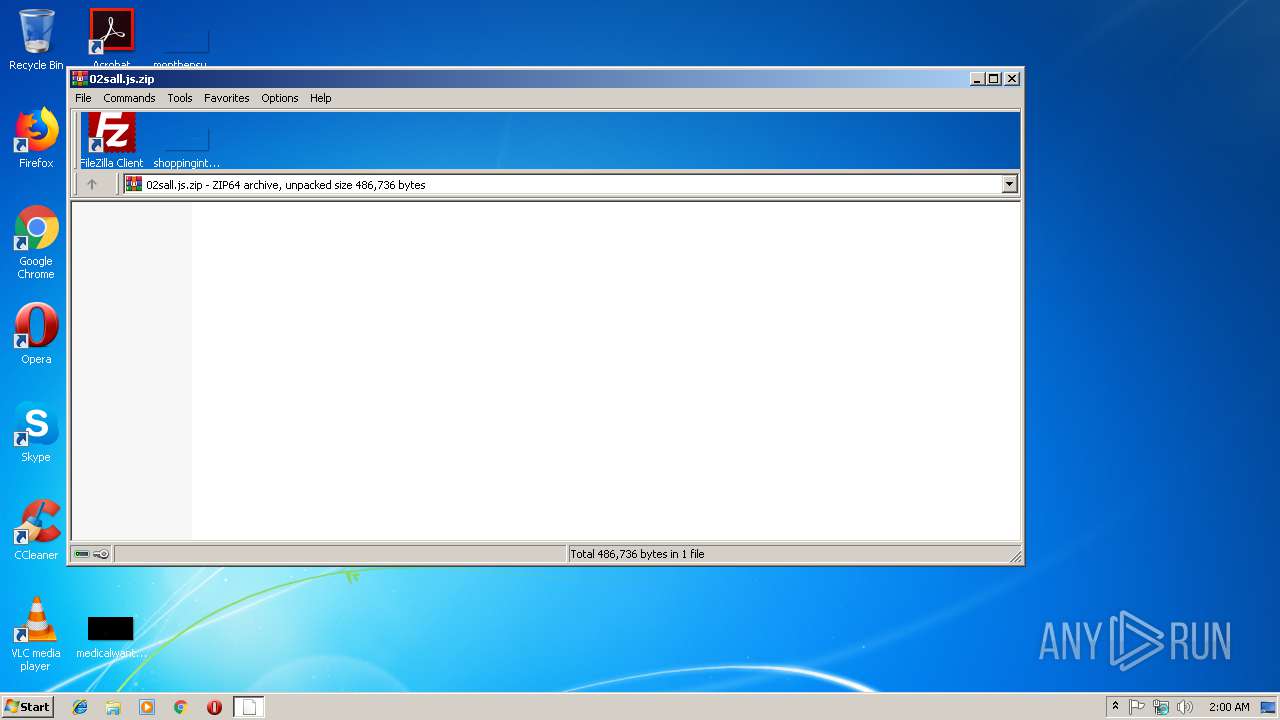
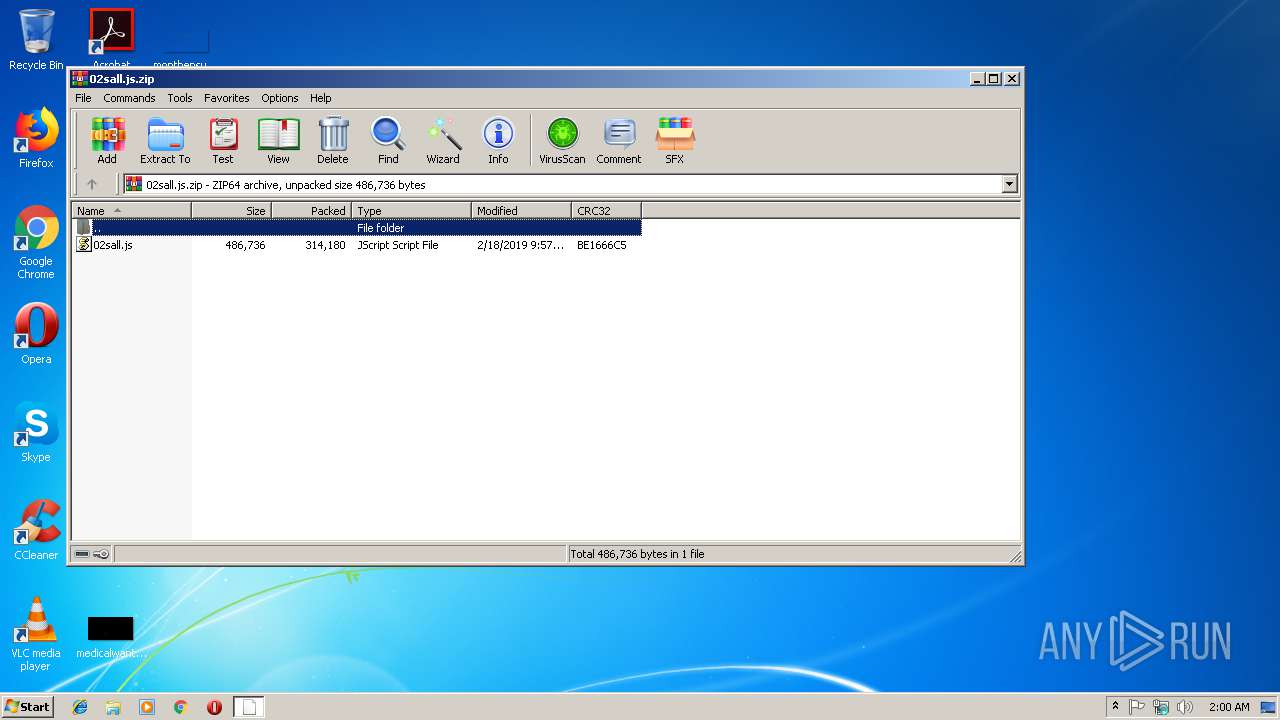
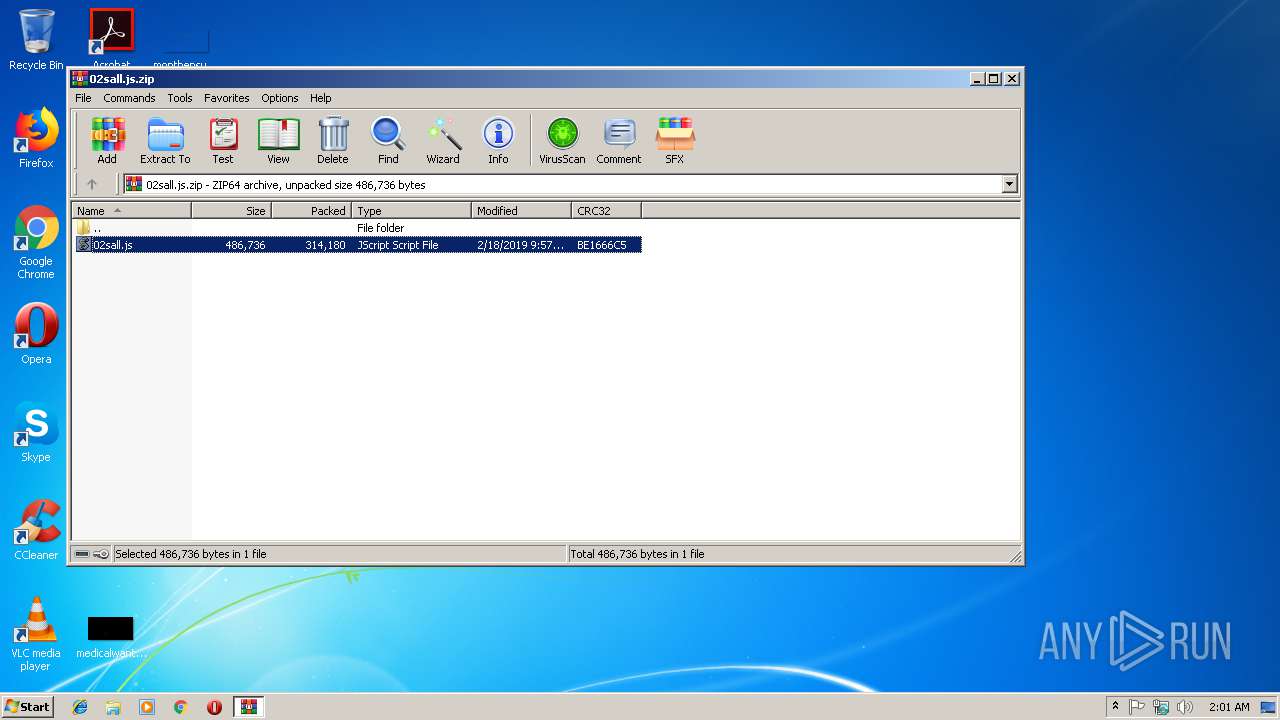
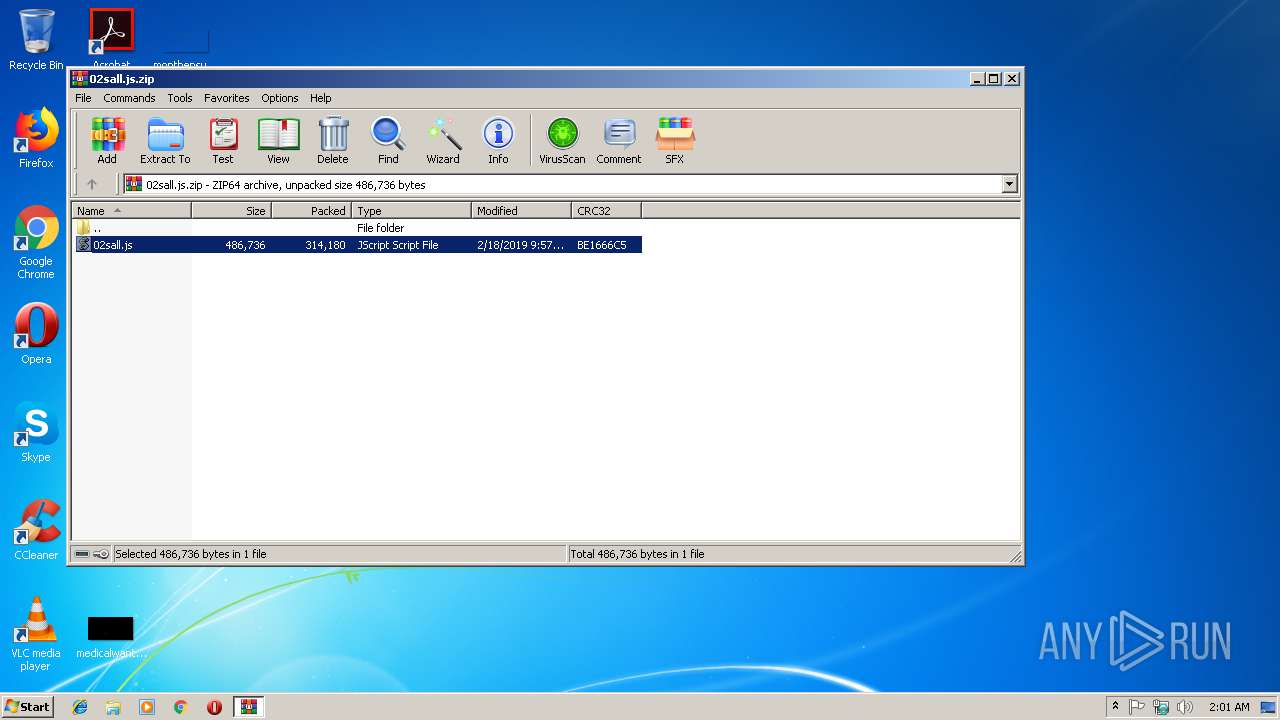
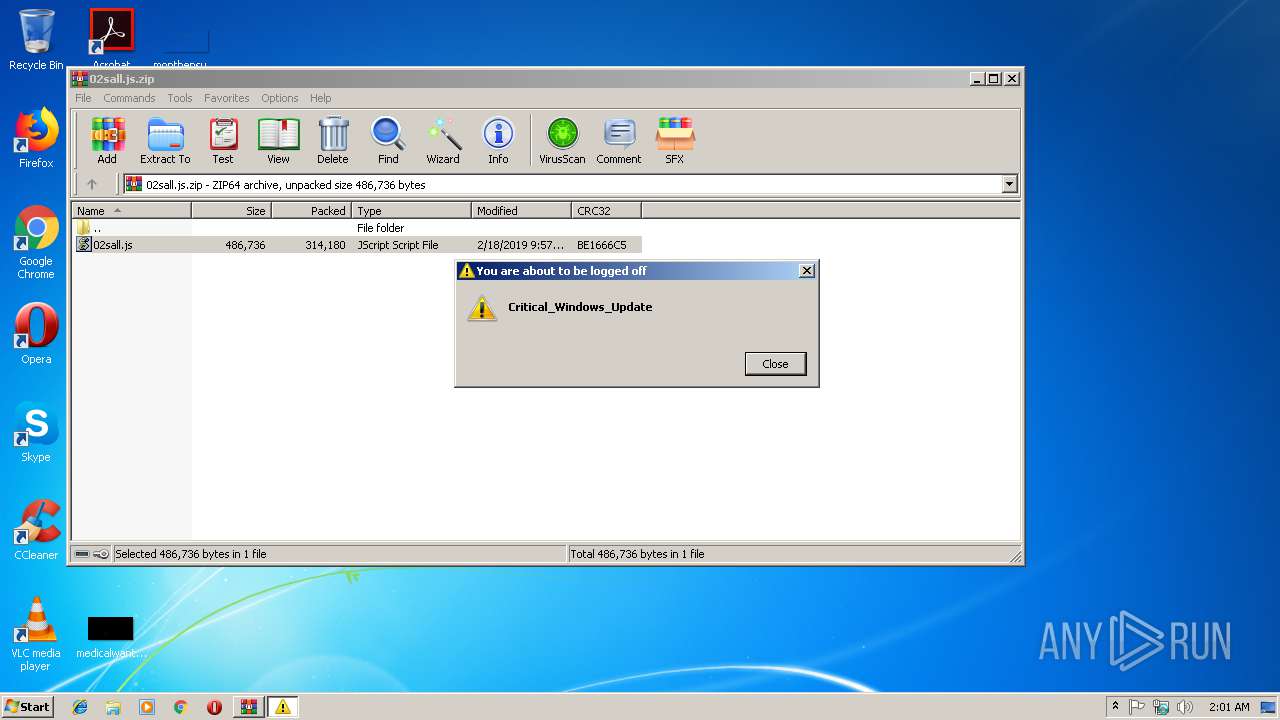
| File name: | 02sall.js.zip |
| Full analysis: | https://app.any.run/tasks/842e4d00-234e-47f4-99b1-defdb8679fbe |
| Verdict: | Malicious activity |
| Analysis date: | March 15, 2019, 02:00:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v4.5 to extract |
| MD5: | 1B004C4CCE7A015A29566F178124A087 |
| SHA1: | 6338BAF2A38EFB5EEB9E9FFC9D6352EBD939DFD3 |
| SHA256: | E8A647981C6105A69DAA8A8EAF0075580F90F30E0A9C094C8028ADA5F19B577A |
| SSDEEP: | 6144:ztO/FA739quJkJ8B5aNcnTVIORt8LvPf1j79KZ6GuhtqlggnrSAaNgO8aDFLc:BO/F4taJCwNcTkvPdj70ZVuhzy+Aug8K |
MALICIOUS
Changes settings of System certificates
- WScript.exe (PID: 2204)
SUSPICIOUS
Executes scripts
- WinRAR.exe (PID: 2856)
Uses NETSH.EXE for network configuration
- WScript.exe (PID: 2204)
Creates files in the user directory
- powershell.exe (PID: 2616)
Adds / modifies Windows certificates
- WScript.exe (PID: 2204)
Executes PowerShell scripts
- WScript.exe (PID: 2204)
Uses REG.EXE to modify Windows registry
- WScript.exe (PID: 2204)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 45 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:02:18 15:57:26 |
| ZipCRC: | 0xbe1666c5 |
| ZipCompressedSize: | 4294967295 |
| ZipUncompressedSize: | 4294967295 |
| ZipFileName: | 02sall.js |
Total processes
46
Monitored processes
8
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2204 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa2856.27704\02sall.js" | C:\Windows\System32\WScript.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2244 | "C:\Windows\System32\reg.exe" add HKLM\SYSTEM\CurrentControlSet\services\Tcpip\Parameters /v DefaultTTL /t REG_DWORD /d 0x40 /f | C:\Windows\System32\reg.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2616 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -enc RwBlAHQALQBXAE0ASQBPAGIAagBlAGMAdAAgAC0AQwBsAGEAcwBzACAAJwBXAGkAbgAzADIAXwBOAGUAdAB3AG8AcgBrAEEAZABhAHAAdABlAHIAQwBvAG4AZgBpAGcAdQByAGEAdABpAG8AbgAnACAAfAAgAEYAbwByAEUAYQBjAGgALQBPAGIAagBlAGMAdAAgAHsATgBlAHcALQBJAHQAZQBtAFAAcgBvAHAAZQByAHQAeQAgAC0AUABhAHQAaAAgACIASABLAEwATQA6AFwAUwBZAFMAVABFAE0AXABDAHUAcgByAGUAbgB0AEMAbwBuAHQAcgBvAGwAUwBlAHQAXABzAGUAcgB2AGkAYwBlAHMAXABUAGMAcABpAHAAXABQAGEAcgBhAG0AZQB0AGUAcgBzAFwASQBuAHQAZQByAGYAYQBjAGUAcwBcACQAKAAkAF8ALgBTAGUAdAB0AGkAbgBnAEkARAApACIAIAAtAE4AYQBtAGUAIAAnAE0AVABVACcAIAAtAFAAcgBvAHAAZQByAHQAeQBUAHkAcABlACAARABXAE8AUgBEACAALQBWAGEAbAB1AGUAIAAxADQANAAwAH0A | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2856 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\02sall.js.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3020 | "C:\Windows\System32\reg.exe" add HKLM\SYSTEM\CurrentControlSet\services\Tcpip\Parameters /v Tcp1323Opts /t REG_DWORD /d 0x02 /f | C:\Windows\System32\reg.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3024 | "C:\Windows\System32\netsh.exe" interface tcp set heuristics ws=disabled | C:\Windows\System32\netsh.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3076 | "C:\Windows\System32\shutdown.exe" /r /f /c "Critical_Windows_Update" /t 120 | C:\Windows\System32\shutdown.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3812 | "C:\Windows\System32\reg.exe" add HKLM\Software\ttl /v ttl /t REG_DWORD /d 0x40 /f | C:\Windows\System32\reg.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
901
Read events
743
Write events
157
Delete events
1
Modification events
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\02sall.js.zip | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\wshext.dll,-4804 |
Value: JScript Script File | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2204 | WScript.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\Windows6.1-KB3033929-x86[1].msu | — | |
MD5:— | SHA256:— | |||
| 2204 | WScript.exe | C:\Users\admin\AppData\Local\VirtualStore\Windows\System32\IsAdm.txt | — | |
MD5:— | SHA256:— | |||
| 2616 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\80L1K8OFYHZZWQD1OB02.temp | — | |
MD5:— | SHA256:— | |||
| 2856 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2856.27704\02sall.js | text | |
MD5:— | SHA256:— | |||
| 2616 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2616 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1bb11c.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2204 | WScript.exe | 2.18.233.19:443 | download.microsoft.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.microsoft.com |
| whitelisted |