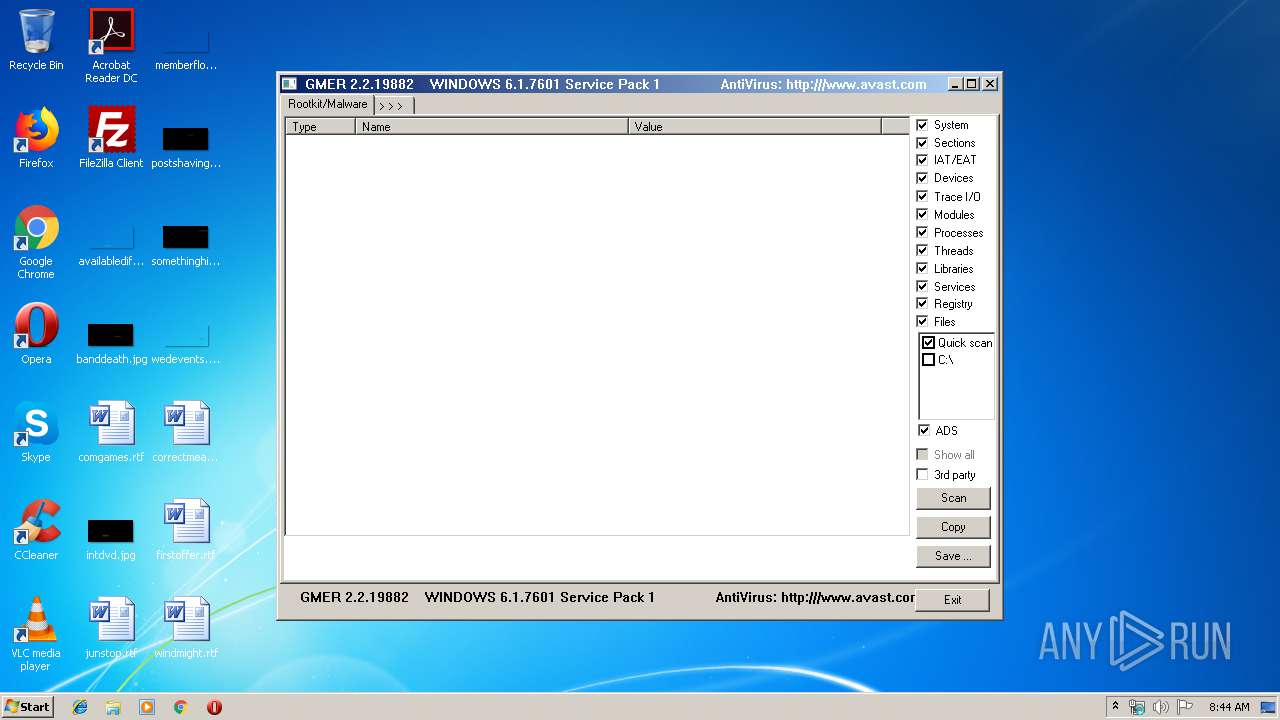
| File name: | gmer.exe |
| Full analysis: | https://app.any.run/tasks/e090f7f0-9734-49f0-b34e-2b2d51e2fb61 |
| Verdict: | Malicious activity |
| Analysis date: | October 17, 2019, 07:44:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | E9DC058440D321AA17D0600B3CA0AB04 |
| SHA1: | 539C228B6B332F5AA523E5CE358C16647D8BBE57 |
| SHA256: | E8A3E804A96C716A3E9B69195DB6FFB0D33E2433AF871E4D4E1EAB3097237173 |
| SSDEEP: | 6144:wW3dQfk45aQOVusKHL7G0FJ6KbJLor/XqNjHtBfLptTksD0c2PMM40:FgkOZHvNJ6KbJE/qNBJT/h2PM |
MALICIOUS
No malicious indicators.SUSPICIOUS
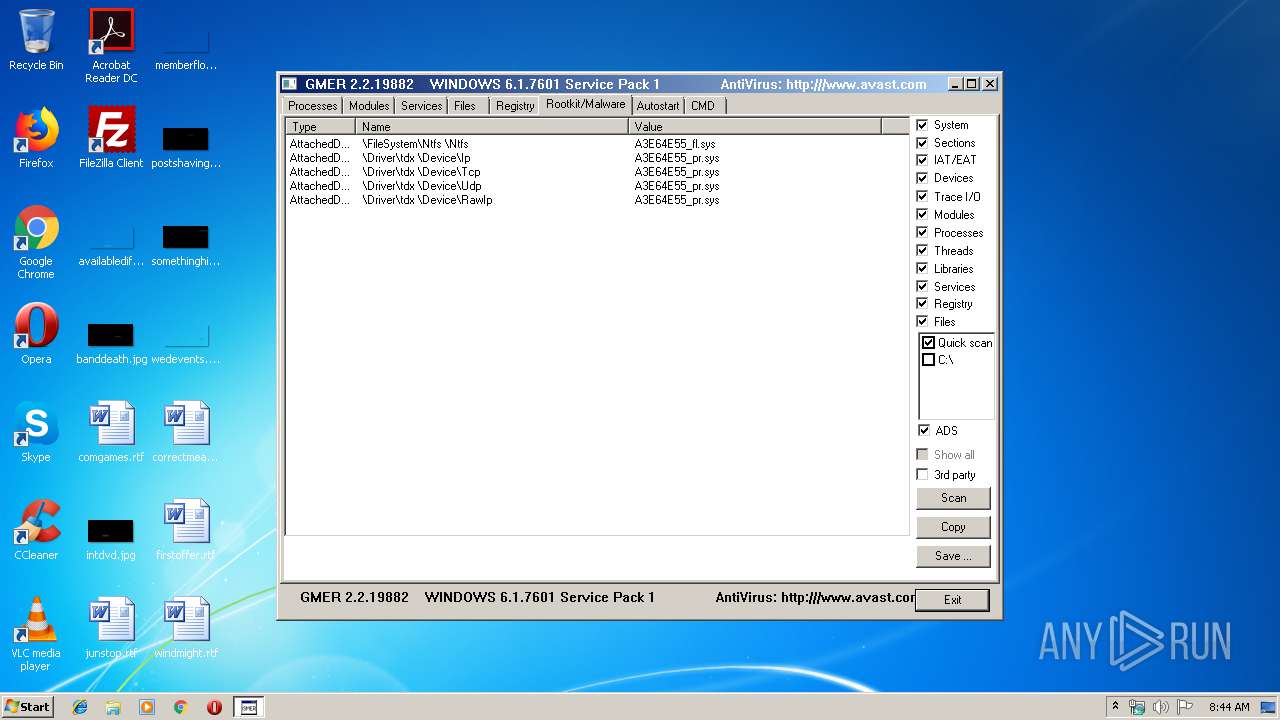
Creates or modifies windows services
- gmer.exe (PID: 3856)
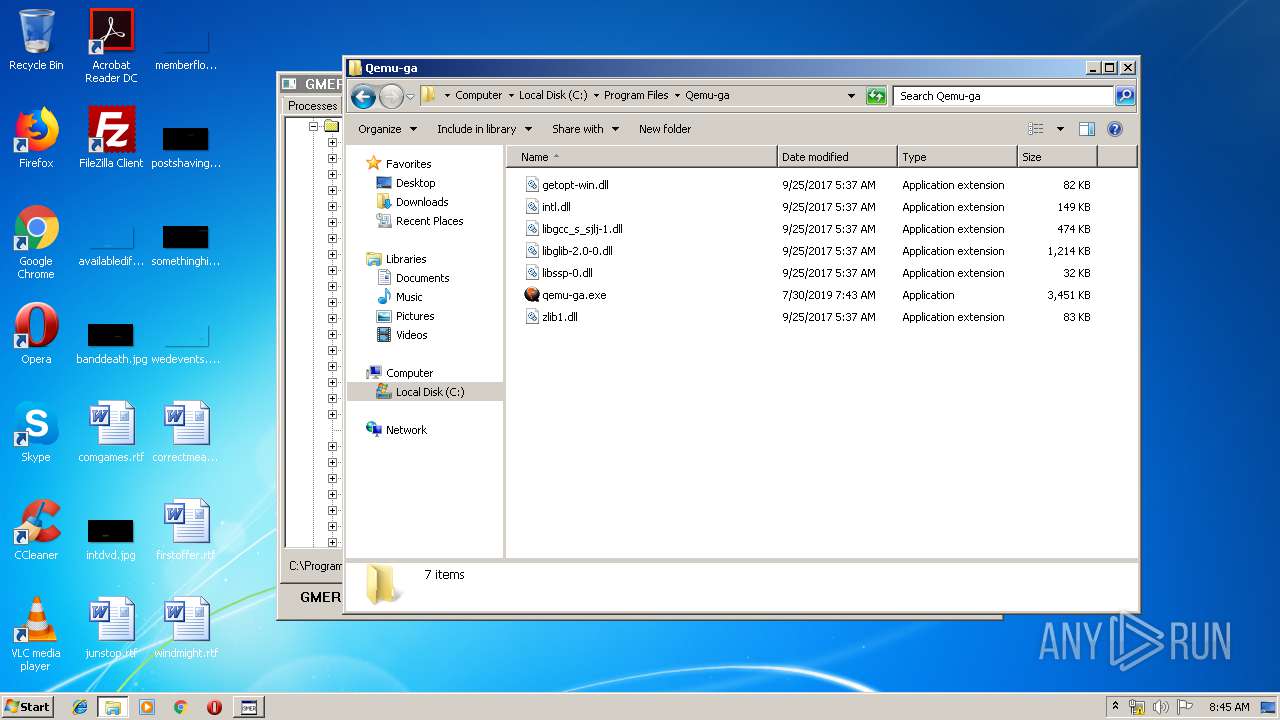
Executable content was dropped or overwritten
- gmer.exe (PID: 3856)
Low-level read access rights to disk partition
- gmer.exe (PID: 3856)
INFO
Manual execution by user
- explorer.exe (PID: 2248)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (43.5) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (42.7) |
| .exe | | | Win32 Executable (generic) (7.2) |
| .exe | | | Generic Win/DOS Executable (3.2) |
| .exe | | | DOS Executable Generic (3.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:03:11 14:53:14+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 376832 |
| InitializedDataSize: | 8192 |
| UninitializedDataSize: | 520192 |
| EntryPoint: | 0xdb470 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.2.19882.0 |
| ProductVersionNumber: | 2.2.19882.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | Polish |
| CharacterSet: | Unicode |
| FileVersion: | 2, 2, 19882 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Mar-2016 13:53:14 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 11-Mar-2016 13:53:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0007F000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00080000 | 0x0005C000 | 0x0005B800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.92656 |
.rsrc | 0x000DC000 | 0x00002000 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.47048 |
Imports
KERNEL32.DLL |
Total processes
40
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2128 | "C:\Users\admin\AppData\Local\Temp\gmer.exe" | C:\Users\admin\AppData\Local\Temp\gmer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 2, 2, 19882 Modules
| |||||||||||||||
| 2248 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3856 | "C:\Users\admin\AppData\Local\Temp\gmer.exe" | C:\Users\admin\AppData\Local\Temp\gmer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 2, 2, 19882 Modules
| |||||||||||||||
Total events
130
Read events
115
Write events
15
Delete events
0
Modification events
| (PID) Process: | (3856) gmer.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\kxldapob |
| Operation: | write | Name: | Type |
Value: 1 | |||
| (PID) Process: | (3856) gmer.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\kxldapob |
| Operation: | write | Name: | ErrorControl |
Value: 1 | |||
| (PID) Process: | (3856) gmer.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\kxldapob |
| Operation: | write | Name: | Start |
Value: 3 | |||
| (PID) Process: | (3856) gmer.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\kxldapob |
| Operation: | write | Name: | ImagePath |
Value: \??\C:\Users\admin\AppData\Local\Temp\kxldapob.sys | |||
| (PID) Process: | (3856) gmer.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\kxldapob |
| Operation: | write | Name: | Group |
Value: Base | |||
| (PID) Process: | (3856) gmer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
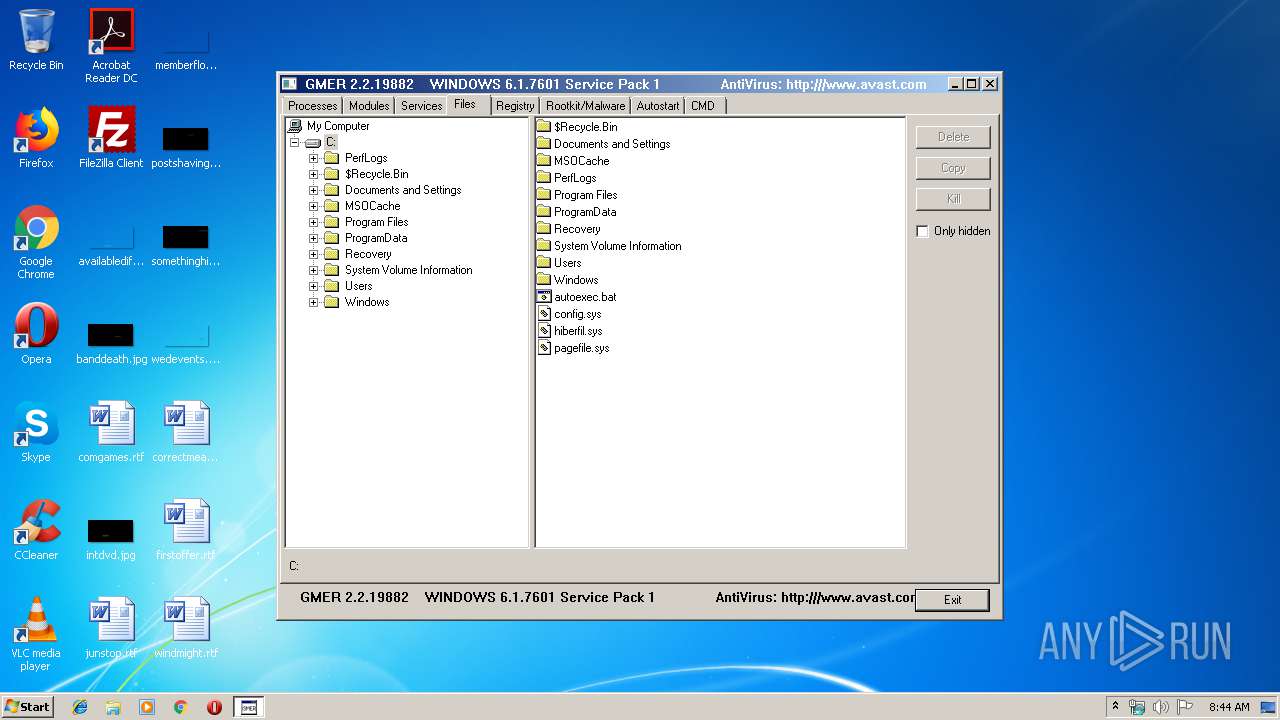
Executable files
2
Suspicious files
6
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3856 | gmer.exe | C:\Users\admin\AppData\Local\Temp\CabB830.tmp | — | |
MD5:— | SHA256:— | |||
| 3856 | gmer.exe | C:\Users\admin\AppData\Local\Temp\TarB831.tmp | — | |
MD5:— | SHA256:— | |||
| 3856 | gmer.exe | C:\Users\admin\AppData\Local\Temp\tmpB8CE.tmp | — | |
MD5:— | SHA256:— | |||
| 3856 | gmer.exe | C:\Users\admin\AppData\Local\Temp\tmpB8FE.tmp | — | |
MD5:— | SHA256:— | |||
| 3856 | gmer.exe | C:\Users\admin\AppData\Local\Temp\tmpB91E.tmp | — | |
MD5:— | SHA256:— | |||
| 3856 | gmer.exe | C:\Users\admin\AppData\Local\Temp\tmpB95E.tmp | — | |
MD5:— | SHA256:— | |||
| 3856 | gmer.exe | C:\Users\admin\AppData\Local\Temp\tmpB99D.tmp | — | |
MD5:— | SHA256:— | |||
| 3856 | gmer.exe | C:\Users\admin\AppData\Local\Temp\tmpB9DD.tmp | — | |
MD5:— | SHA256:— | |||
| 3856 | gmer.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B8CC409ACDBF2A2FE04C56F2875B1FD6 | binary | |
MD5:— | SHA256:— | |||
| 3856 | gmer.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\696F3DE637E6DE85B458996D49D759AD | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3856 | gmer.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | der | 550 b | whitelisted |
3856 | gmer.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | der | 781 b | whitelisted |
3856 | gmer.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/WinPCA.crl | unknown | der | 530 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3856 | gmer.exe | 2.16.186.74:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |