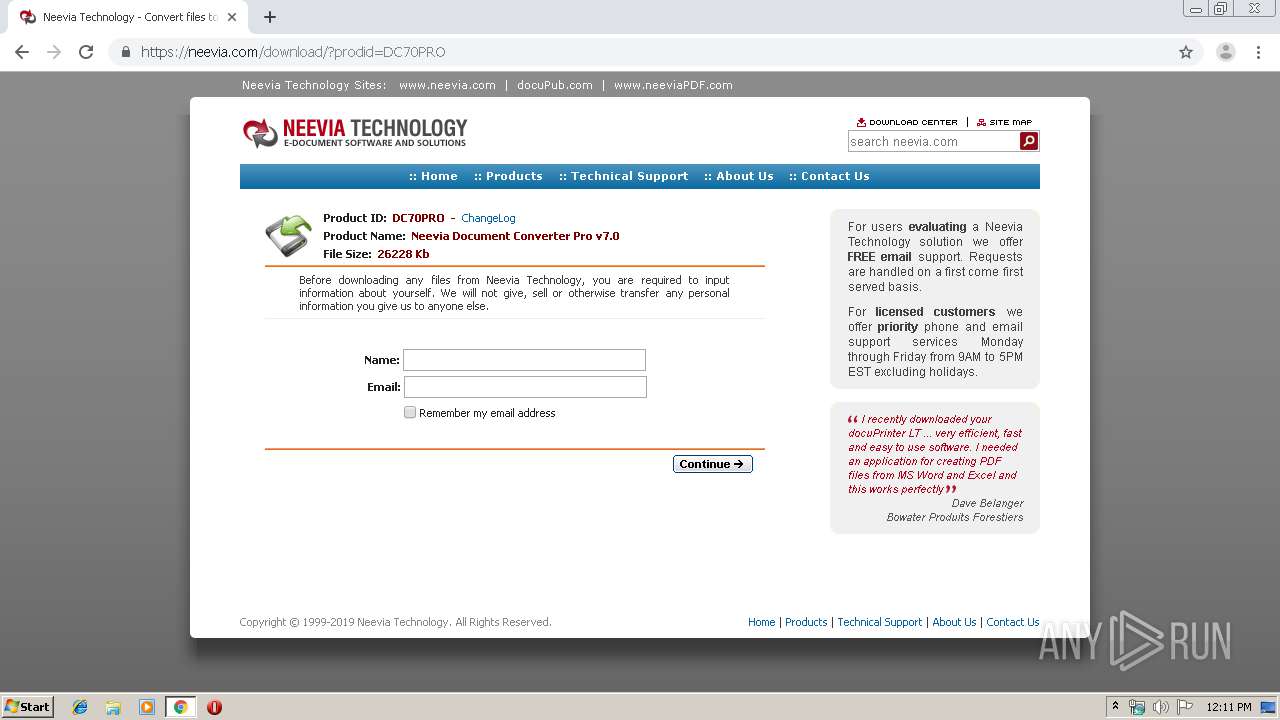
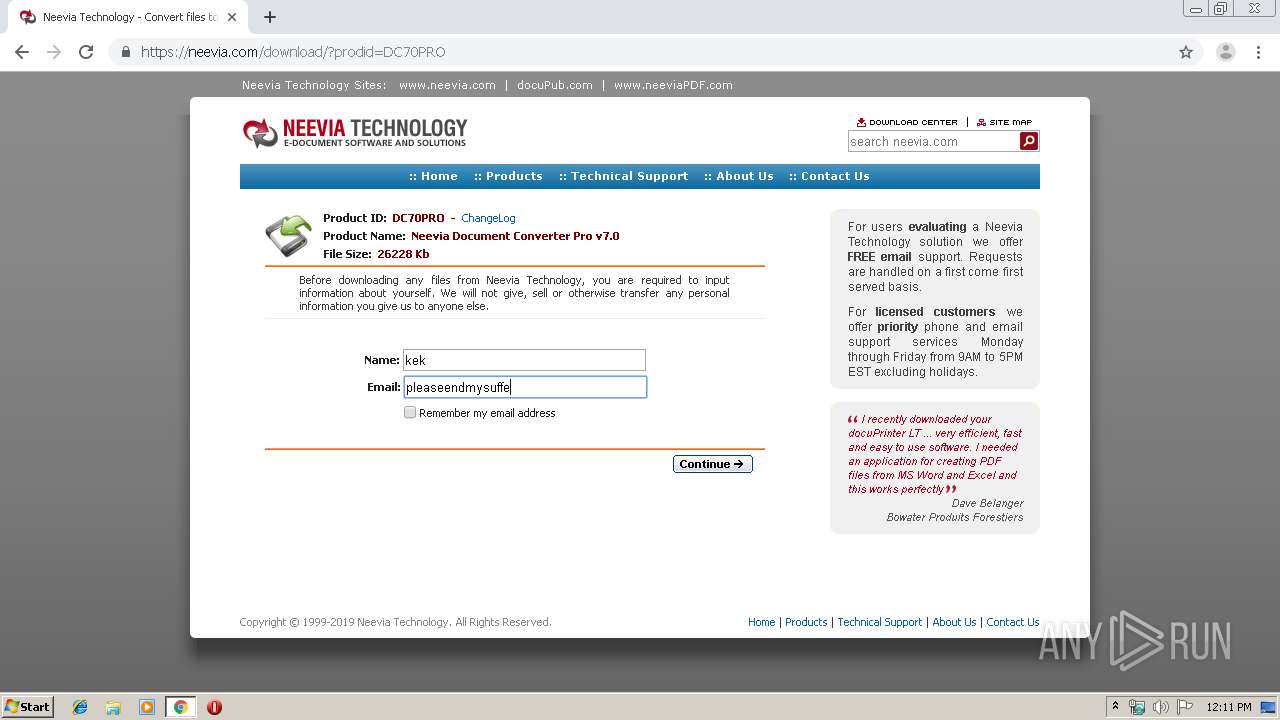
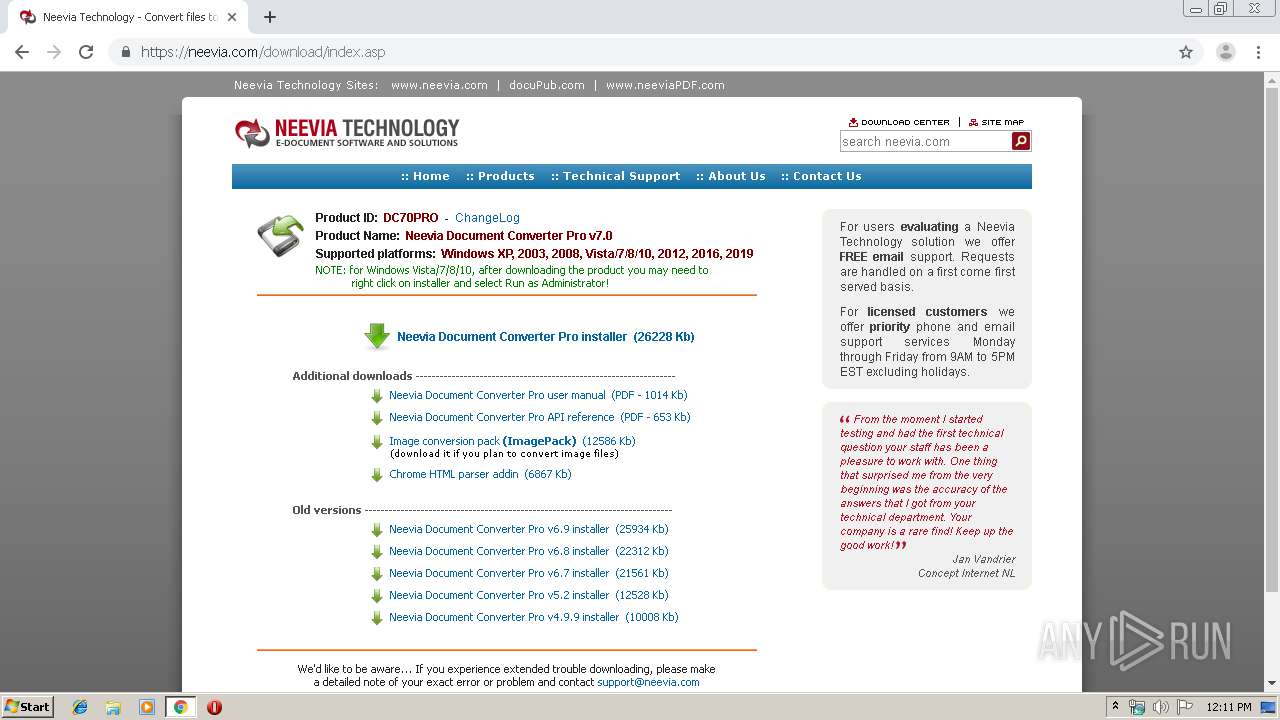
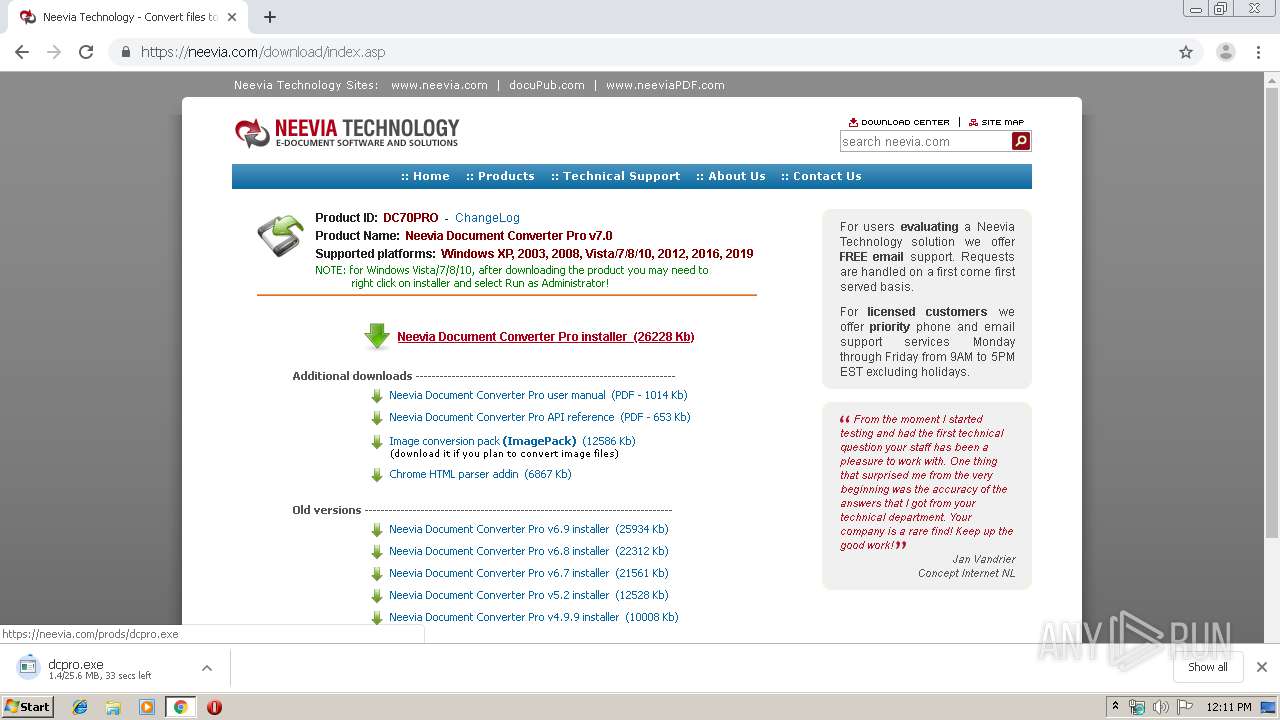
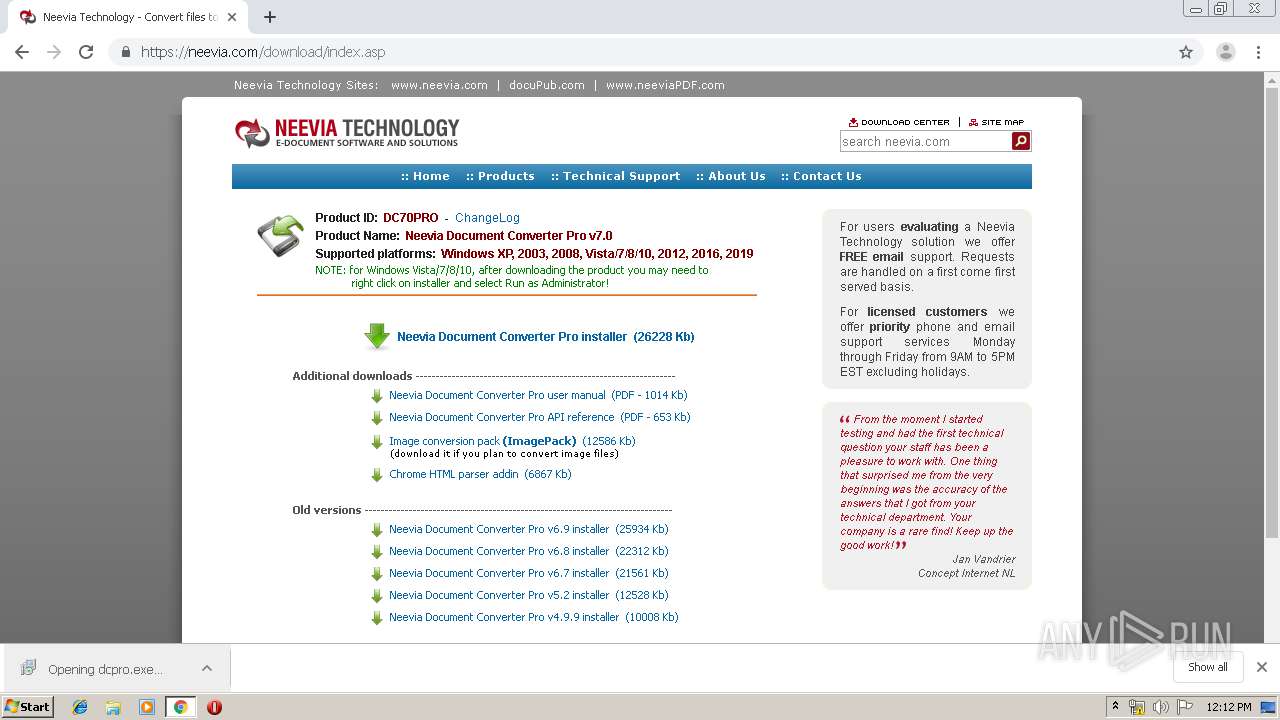
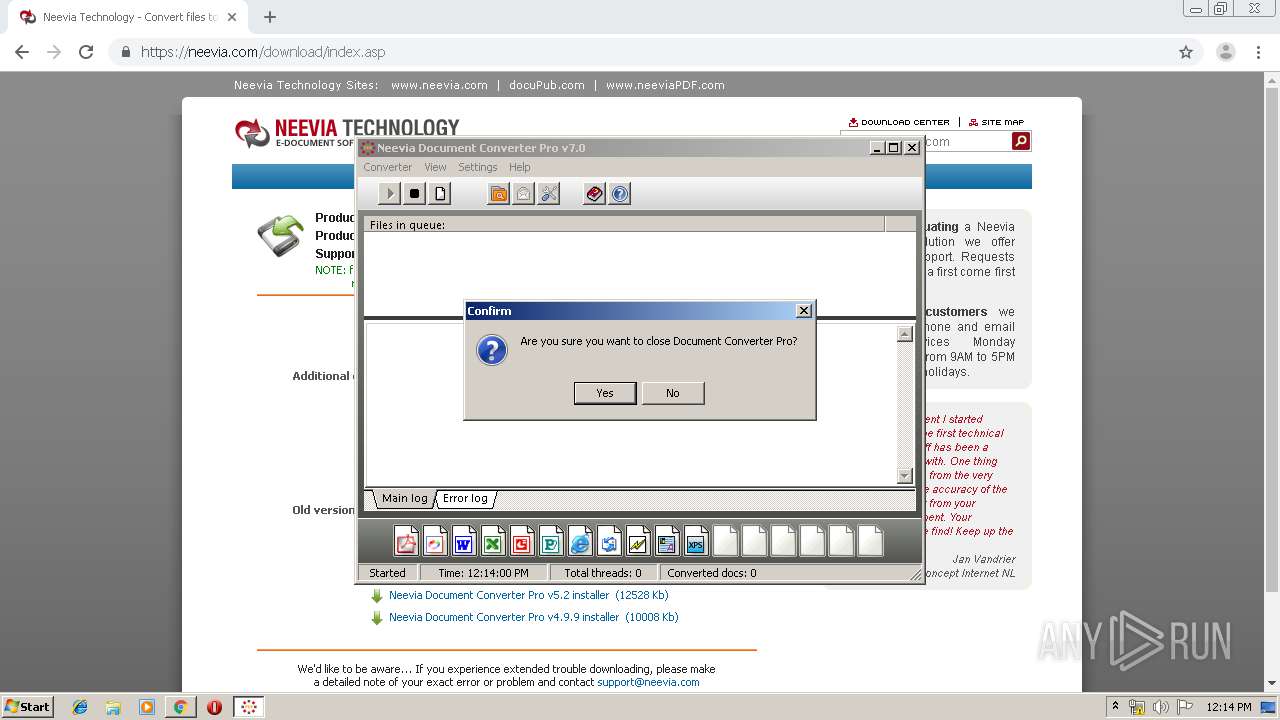
| URL: | http://www.Neevia.com |
| Full analysis: | https://app.any.run/tasks/e5c27ed4-d504-4d8e-8912-d99044a845a4 |
| Verdict: | Malicious activity |
| Analysis date: | September 15, 2019, 11:10:50 |
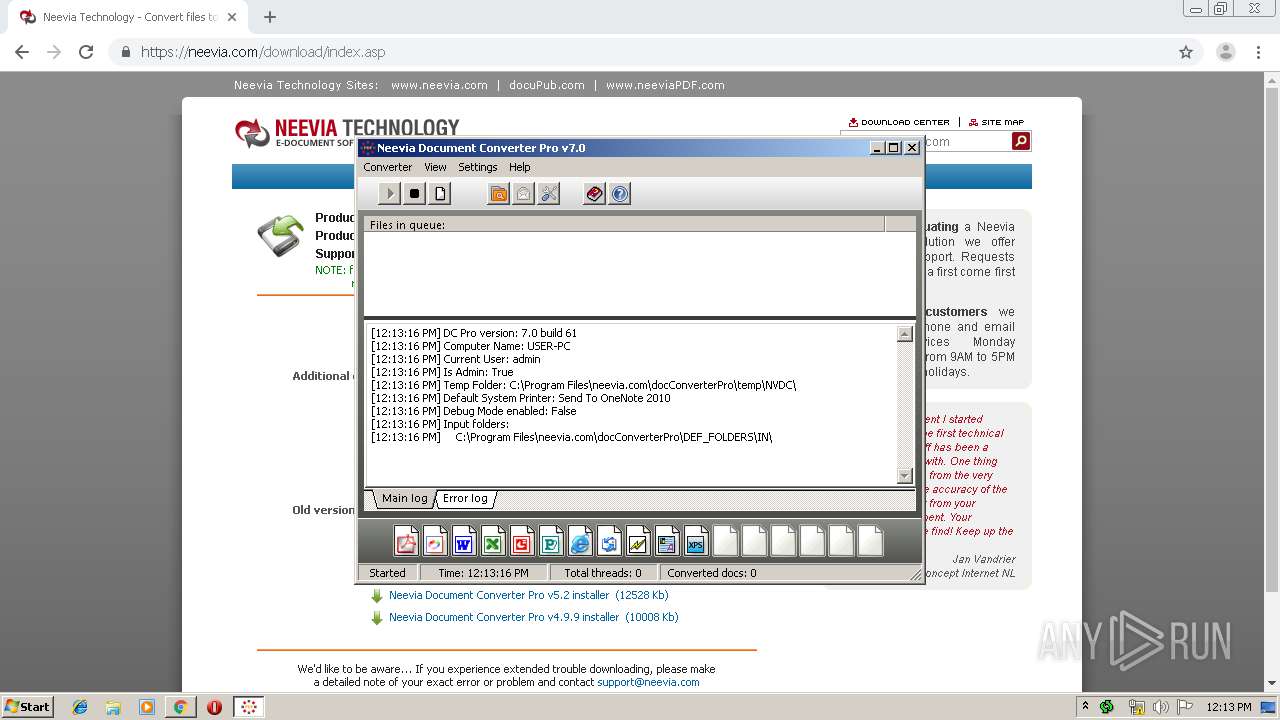
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C4B08DDB79A60DC4655239D6C6D4AA57 |
| SHA1: | FA31635404AD9C4980435C3971BB0D5F6FC532E1 |
| SHA256: | E89600FED9C98BC2F6E933FC6E3151657E1EA41139ECA0C42F757EFB2358475B |
| SSDEEP: | 3:N1KJS4U2xK:Cc4Ux |
MALICIOUS
Application was dropped or rewritten from another process
- dcpro.exe (PID: 3320)
- fontmap.exe (PID: 3600)
- fontmap.exe (PID: 2344)
- dcpro.exe (PID: 3924)
- fontmap.exe (PID: 1492)
- fontmap.exe (PID: 3196)
- fontmap.exe (PID: 1428)
- fontmap.exe (PID: 2400)
- fontmap.exe (PID: 2956)
- fontmap.exe (PID: 4032)
- fontmap.exe (PID: 1860)
- fontmap.exe (PID: 3696)
- dConverter.exe (PID: 2896)
- fontmap.exe (PID: 2800)
- dConverter.exe (PID: 3076)
- fontmap.exe (PID: 2368)
- fontmap.exe (PID: 2872)
- gswin32c.exe (PID: 3872)
- dcomperm.exe (PID: 2636)
- dcomperm.exe (PID: 3556)
- setacl.exe (PID: 2536)
- setacl.exe (PID: 1536)
- docuDriver.exe (PID: 912)
- docConverter.dll (PID: 2964)
- PDFinfo.dll (PID: 780)
- rescache.lib (PID: 2112)
- dConverter.exe (PID: 3200)
- dConverter.exe (PID: 3104)
- dConverter.exe (PID: 3388)
- rescache.lib (PID: 2860)
Starts NET.EXE for service management
- dcpro.tmp (PID: 2848)
Registers / Runs the DLL via REGSVR32.EXE
- dcpro.tmp (PID: 2848)
Loads dropped or rewritten executable
- spoolsv.exe (PID: 1204)
- gswin32c.exe (PID: 3872)
- dConverter.exe (PID: 3076)
- regsvr32.exe (PID: 3704)
- regsvr32.exe (PID: 1784)
- svchost.exe (PID: 852)
- regsvr32.exe (PID: 2420)
- regsvr32.exe (PID: 2728)
- regsvr32.exe (PID: 3128)
- dConverter.exe (PID: 3388)
- dConverter.exe (PID: 3200)
- dConverter.exe (PID: 3104)
SUSPICIOUS
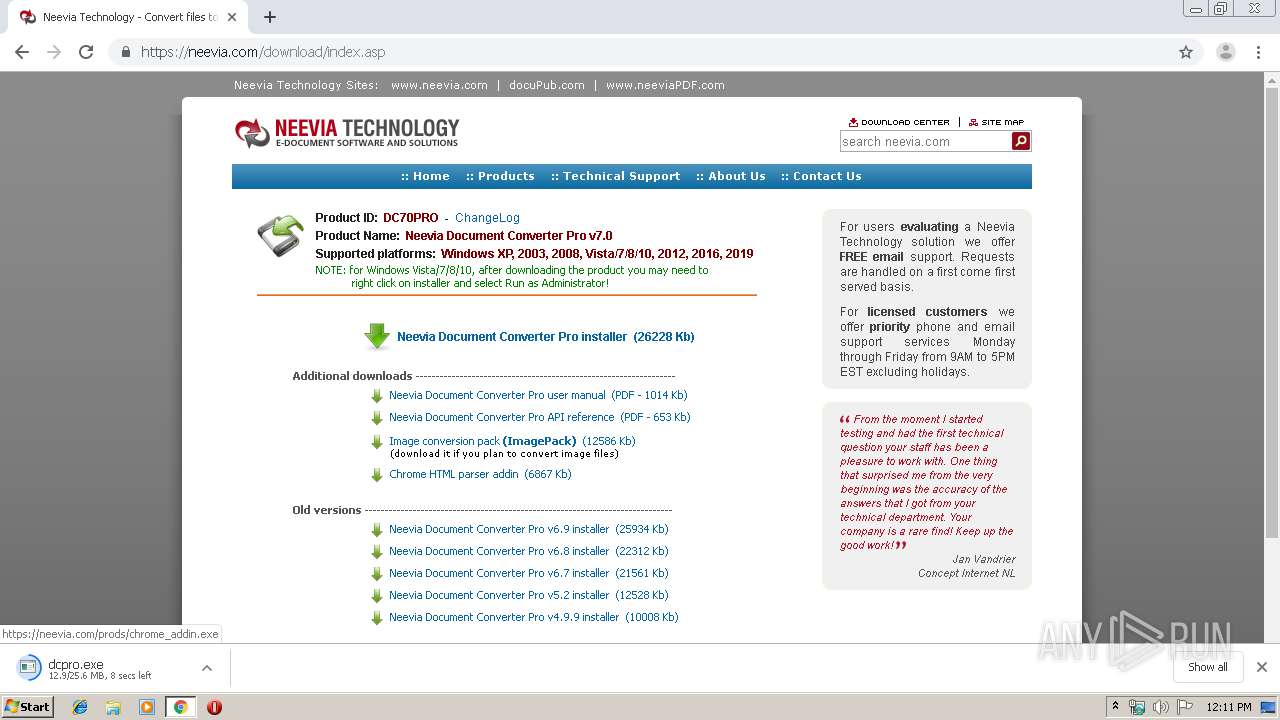
Modifies files in Chrome extension folder
- chrome.exe (PID: 3548)
Reads Windows owner or organization settings
- dcpro.tmp (PID: 2848)
Reads the Windows organization settings
- dcpro.tmp (PID: 2848)
Executable content was dropped or overwritten
- chrome.exe (PID: 2880)
- chrome.exe (PID: 3548)
- dcpro.exe (PID: 3320)
- dcpro.tmp (PID: 2848)
- dcpro.exe (PID: 3924)
- docuDriver.exe (PID: 912)
- spoolsv.exe (PID: 1204)
- rescache.lib (PID: 2112)
Creates COM task schedule object
- regsvr32.exe (PID: 3128)
- regsvr32.exe (PID: 3704)
- regsvr32.exe (PID: 2728)
- regsvr32.exe (PID: 1784)
Creates files in the Windows directory
- dConverter.exe (PID: 2896)
- docuDriver.exe (PID: 912)
- spoolsv.exe (PID: 1204)
- dConverter.exe (PID: 3076)
- dConverter.exe (PID: 3388)
- dConverter.exe (PID: 3200)
- dConverter.exe (PID: 3104)
Removes files from Windows directory
- spoolsv.exe (PID: 1204)
Starts application with an unusual extension
- dcpro.tmp (PID: 2848)
- dConverter.exe (PID: 3076)
- dConverter.exe (PID: 3104)
Uses RUNDLL32.EXE to load library
- dcpro.tmp (PID: 2848)
Creates files in the program directory
- fontmap.exe (PID: 2872)
- dConverter.exe (PID: 3076)
- rescache.lib (PID: 2112)
- dConverter.exe (PID: 3388)
- dConverter.exe (PID: 3104)
Executed via COM
- WINWORD.EXE (PID: 2480)
- POWERPNT.EXE (PID: 1876)
- EXCEL.EXE (PID: 3648)
- MSPUB.EXE (PID: 2404)
- iexplore.exe (PID: 2988)
- WINWORD.EXE (PID: 2936)
Checks supported languages
- POWERPNT.EXE (PID: 1876)
Creates files in the user directory
- MSPUB.EXE (PID: 2404)
INFO
Reads the hosts file
- chrome.exe (PID: 3548)
- chrome.exe (PID: 2880)
Application launched itself
- chrome.exe (PID: 3548)
- iexplore.exe (PID: 2988)
Reads Internet Cache Settings
- chrome.exe (PID: 3548)
Changes settings of System certificates
- chrome.exe (PID: 3548)
Application was dropped or rewritten from another process
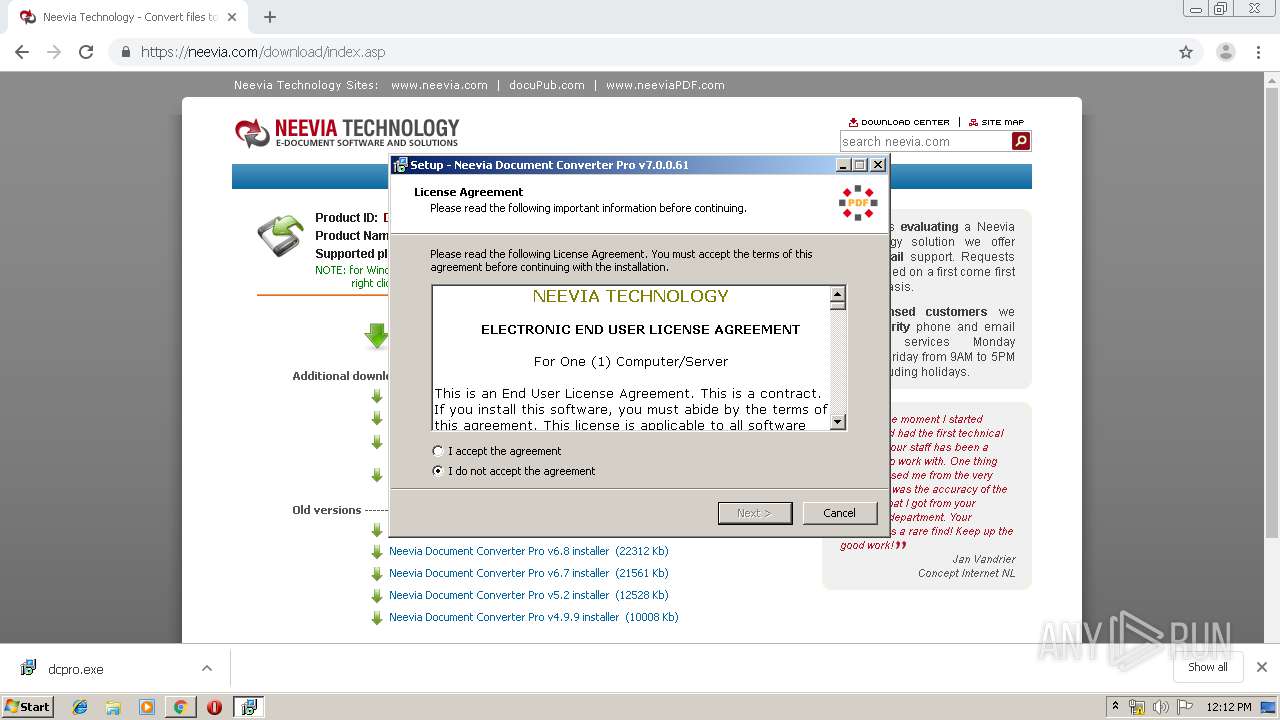
- dcpro.tmp (PID: 2848)
- dcpro.tmp (PID: 2968)
Creates a software uninstall entry
- dcpro.tmp (PID: 2848)
Creates files in the program directory
- dcpro.tmp (PID: 2848)
Loads dropped or rewritten executable
- dcpro.tmp (PID: 2848)
Creates files in the user directory
- WINWORD.EXE (PID: 2480)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 3648)
- POWERPNT.EXE (PID: 1876)
- WINWORD.EXE (PID: 2480)
- MSPUB.EXE (PID: 2404)
- WINWORD.EXE (PID: 2936)
Changes internet zones settings
- iexplore.exe (PID: 2988)
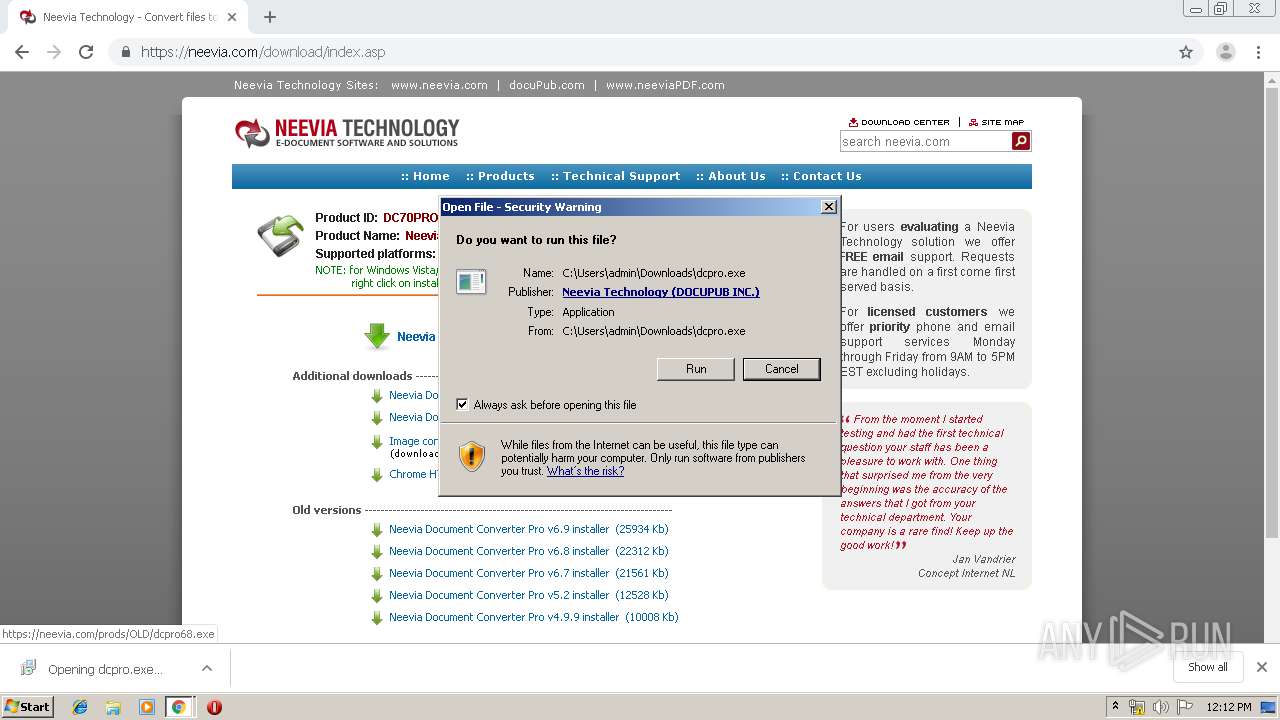
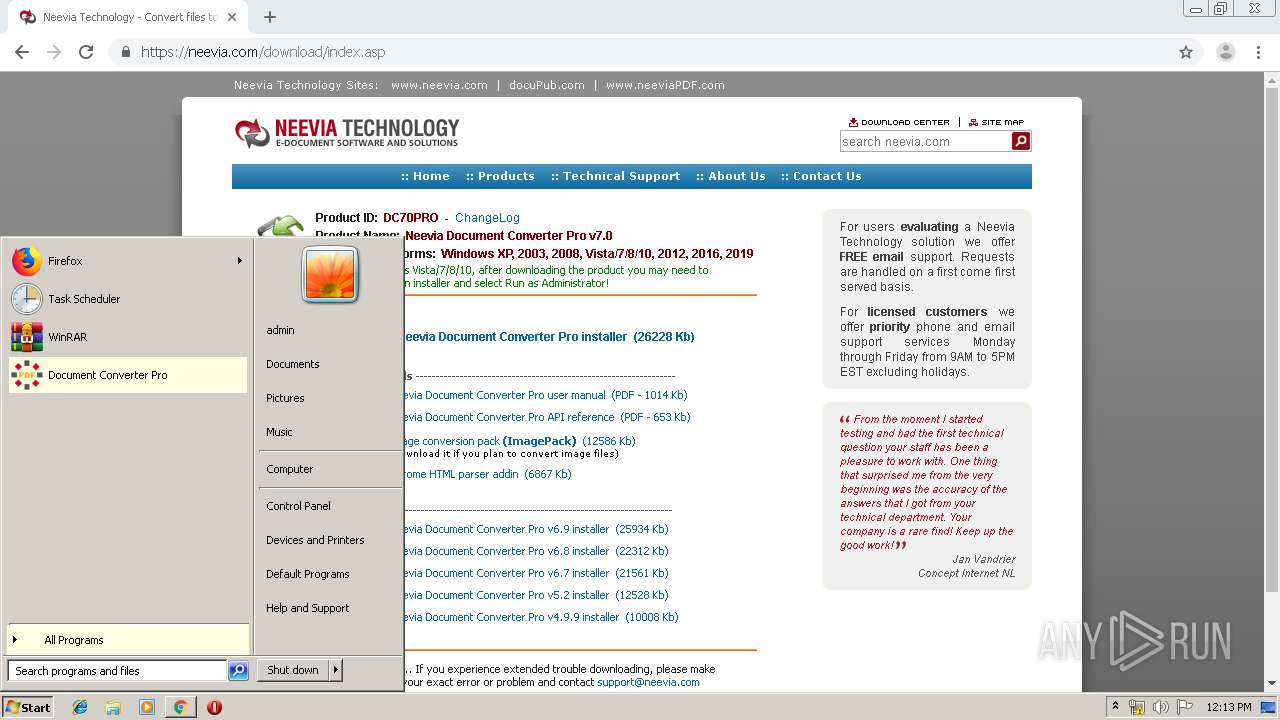
Manual execution by user
- dConverter.exe (PID: 3104)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
122
Monitored processes
73
Malicious processes
11
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,7523516151248779238,15739629041188525296,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10464795113714779987 --mojo-platform-channel-handle=3740 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 780 | "C:\Program Files\neeviaPDF.com\PDFinfo\COMobj\PDFinfo.dll" /regserver | C:\Program Files\neeviaPDF.com\PDFinfo\COMobj\PDFinfo.dll | — | dcpro.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 3.5.0.0 Modules
| |||||||||||||||
| 852 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 912 | "C:\Program Files\neevia.com\docConverterPro\temp\docuDriver.exe" converter "C:\Program Files\neevia.com\docConverterPro" "Neevia Converter" | C:\Program Files\neevia.com\docConverterPro\temp\docuDriver.exe | dcpro.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1204 | C:\Windows\System32\spoolsv.exe | C:\Windows\System32\spoolsv.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Spooler SubSystem App Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1304 | "C:\Windows\system32\net.exe" stop /Y NVDCPservice | C:\Windows\system32\net.exe | — | dcpro.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,7523516151248779238,15739629041188525296,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12299167962063335171 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1428 | "C:\Program Files\neevia.com\docConverterPro\modules\fontmap.exe" /auto /killtask dcconfig.exe end | C:\Program Files\neevia.com\docConverterPro\modules\fontmap.exe | — | dcpro.tmp | |||||||||||
User: admin Company: Neevia Technology Integrity Level: HIGH Description: Tools Exit code: 0 Version: 7.0.0.0 Modules
| |||||||||||||||
| 1492 | "C:\Program Files\neevia.com\docConverterPro\modules\fontmap.exe" /auto /killtask docconverter.dll end | C:\Program Files\neevia.com\docConverterPro\modules\fontmap.exe | — | dcpro.tmp | |||||||||||
User: admin Company: Neevia Technology Integrity Level: HIGH Description: Tools Exit code: 0 Version: 7.0.0.0 Modules
| |||||||||||||||
| 1536 | "C:\Program Files\neevia.com\docConverterPro\modules\setacl.exe" -on "C:\Program Files\neevia.com\docConverterPro\temp" -ot file -actn ace -ace "n:administrators;p:full" -ace "n:everyone;p:full" -ace "n:system;p:full" | C:\Program Files\neevia.com\docConverterPro\modules\setacl.exe | — | dcpro.tmp | |||||||||||
User: admin Company: Integrity Level: HIGH Description: SetACL 2 Exit code: 0 Version: 2, 0, 2, 0 Modules
| |||||||||||||||
Total events
5 967
Read events
4 476
Write events
1 444
Delete events
47
Modification events
| (PID) Process: | (3548) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3548) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3548) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3548) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3548) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3548-13213019465692000 |
Value: 259 | |||
| (PID) Process: | (3548) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3548) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3548) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3548) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
57
Suspicious files
34
Text files
503
Unknown types
325
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7466941f-cfea-4223-99bb-c074b30ac76e.tmp | — | |
MD5:— | SHA256:— | |||
| 3548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF169bf6.TMP | text | |
MD5:— | SHA256:— | |||
| 3548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF169c44.TMP | text | |
MD5:— | SHA256:— | |||
| 3548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
31
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2880 | chrome.exe | GET | 302 | 172.217.22.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 513 b | whitelisted |
2880 | chrome.exe | GET | 302 | 216.242.118.92:80 | http://www.neevia.com/ | US | html | 139 b | suspicious |
3548 | chrome.exe | GET | 200 | 91.199.212.52:80 | http://crt.comodoca.com/COMODORSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
2880 | chrome.exe | GET | 200 | 173.194.187.6:80 | http://r1---sn-4g5e6ns6.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=85.17.73.119&mm=28&mn=sn-4g5e6ns6&ms=nvh&mt=1568545482&mv=u&mvi=0&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
2988 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2880 | chrome.exe | 216.242.118.92:80 | www.neevia.com | BroadbandONE, Inc. | US | unknown |
2880 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2880 | chrome.exe | 172.217.23.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
2880 | chrome.exe | 216.242.118.92:443 | www.neevia.com | BroadbandONE, Inc. | US | unknown |
2880 | chrome.exe | 172.217.16.206:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2880 | chrome.exe | 172.217.22.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2880 | chrome.exe | 173.194.76.154:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
2880 | chrome.exe | 172.217.22.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
2880 | chrome.exe | 172.217.22.4:443 | www.google.com | Google Inc. | US | whitelisted |
2880 | chrome.exe | 172.217.23.131:443 | www.google.nl | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.neevia.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
neevia.com |
| malicious |
www.google-analytics.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
www.google.com |
| malicious |
www.google.nl |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |