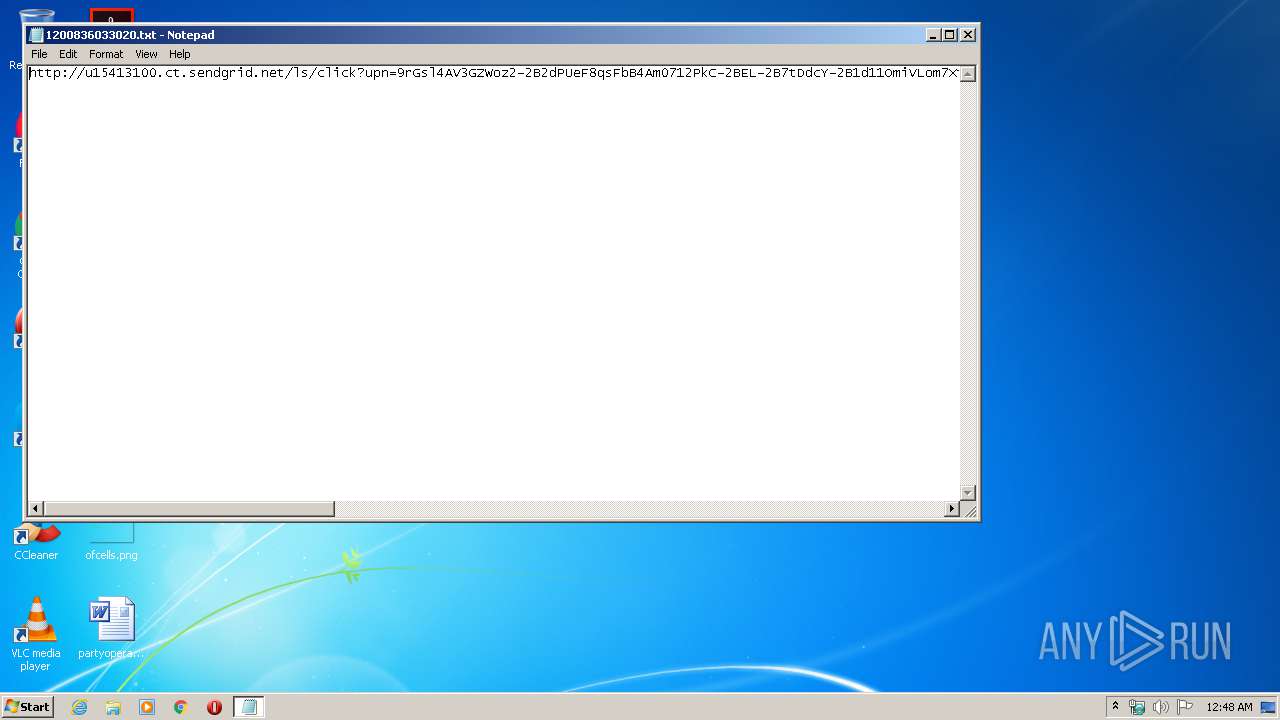
| File name: | 1200836033020.txt |
| Full analysis: | https://app.any.run/tasks/343928bd-7032-4dc5-a6dc-2f26c07af937 |
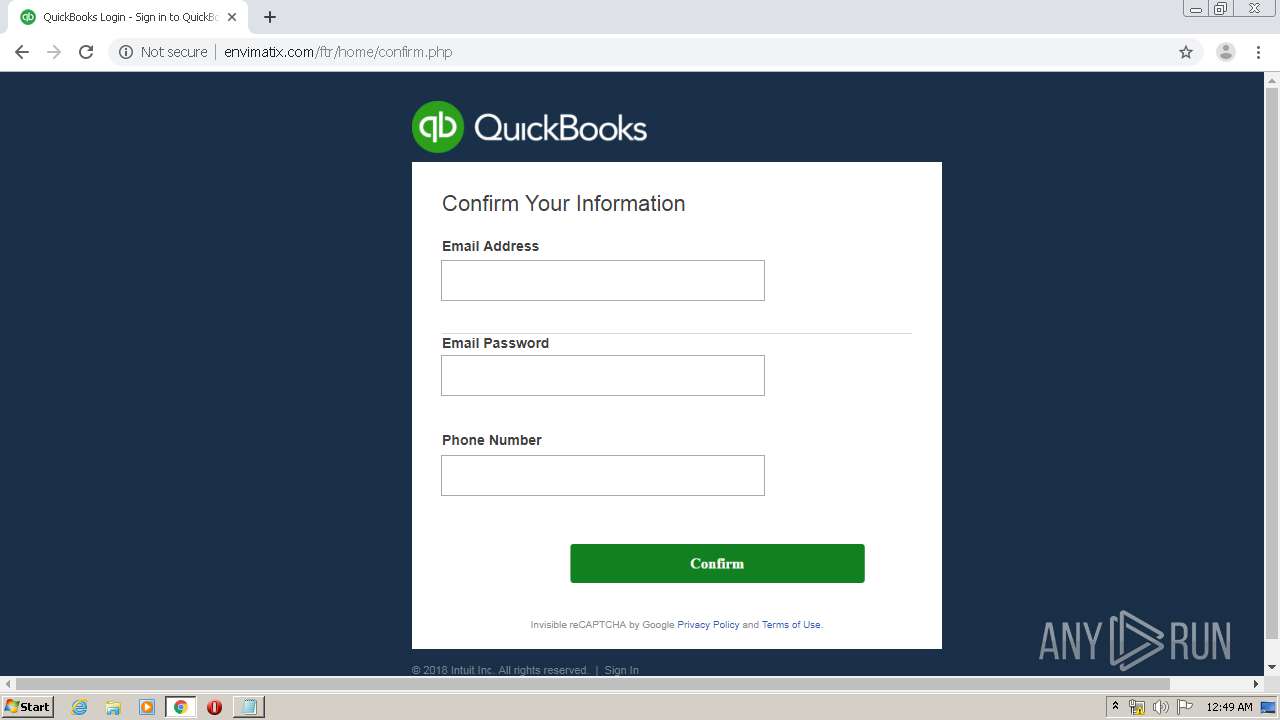
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 23:48:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with no line terminators |
| MD5: | 80647D3E0963958C6F24E0D4D11B9BCA |
| SHA1: | 561F8EE4CE3F7E2F5C925D98413789E65C50F3E4 |
| SHA256: | E89050F01A54DA54FC69C3045887EAD8C530881D23D28CAE29B5A50F6D7A14DE |
| SSDEEP: | 6:CVRlY6x9k6Xsutjn00wJUmsMUBD9T1xHL9rZcRTdea0/5eIkQvWLDCeTf7m:kRaS9k68utjnjCYBD9T1xBZcSa0/5PcS |
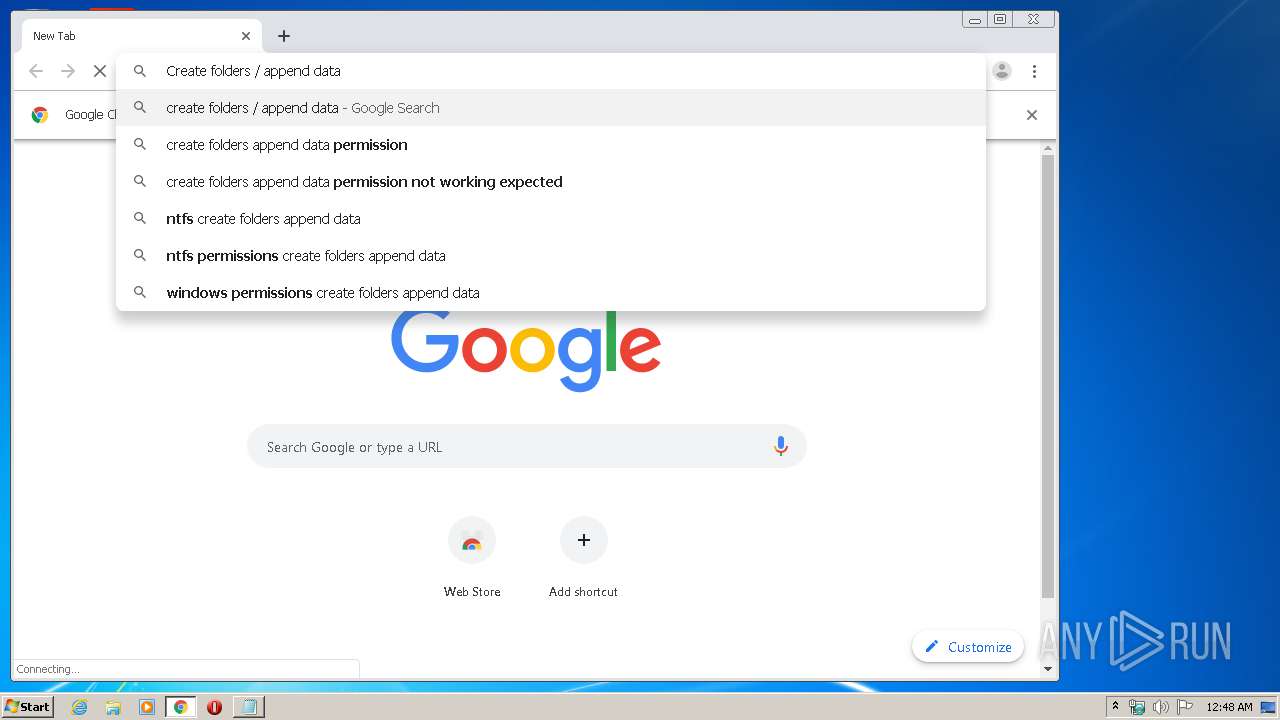
MALICIOUS
No malicious indicators.SUSPICIOUS
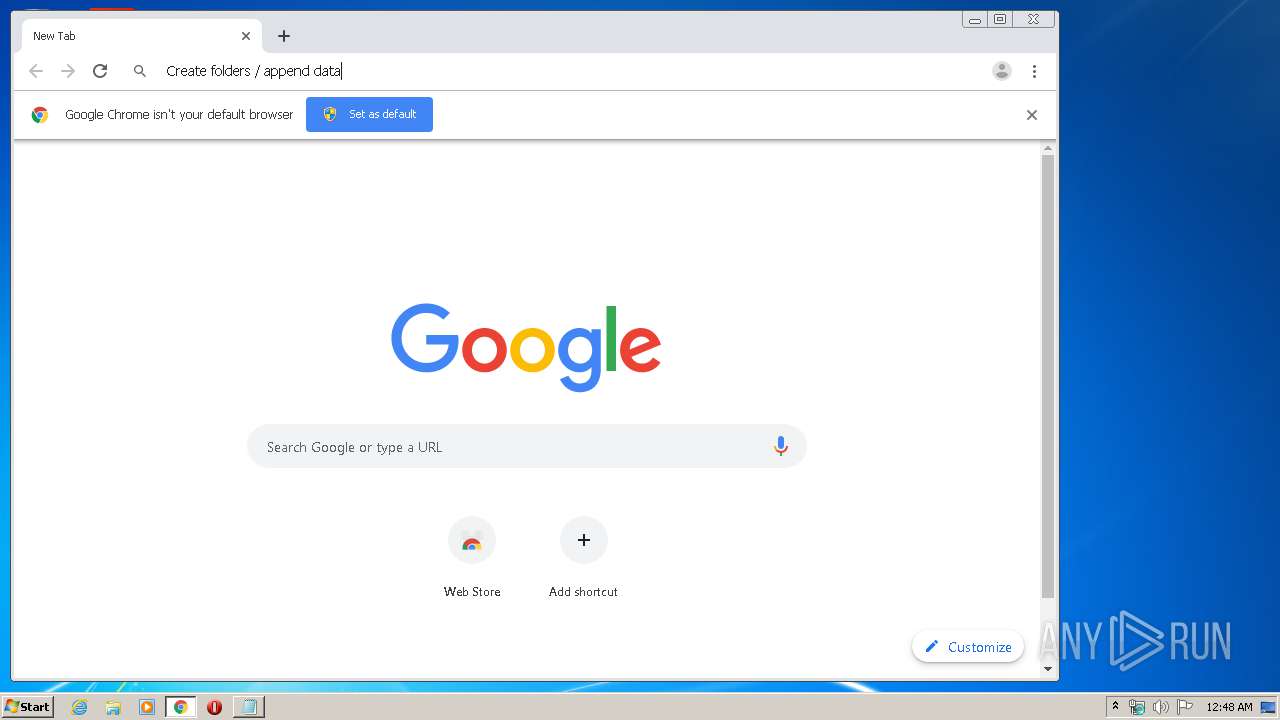
Modifies files in Chrome extension folder
- chrome.exe (PID: 3912)
INFO
Reads the hosts file
- chrome.exe (PID: 3912)
- chrome.exe (PID: 3828)
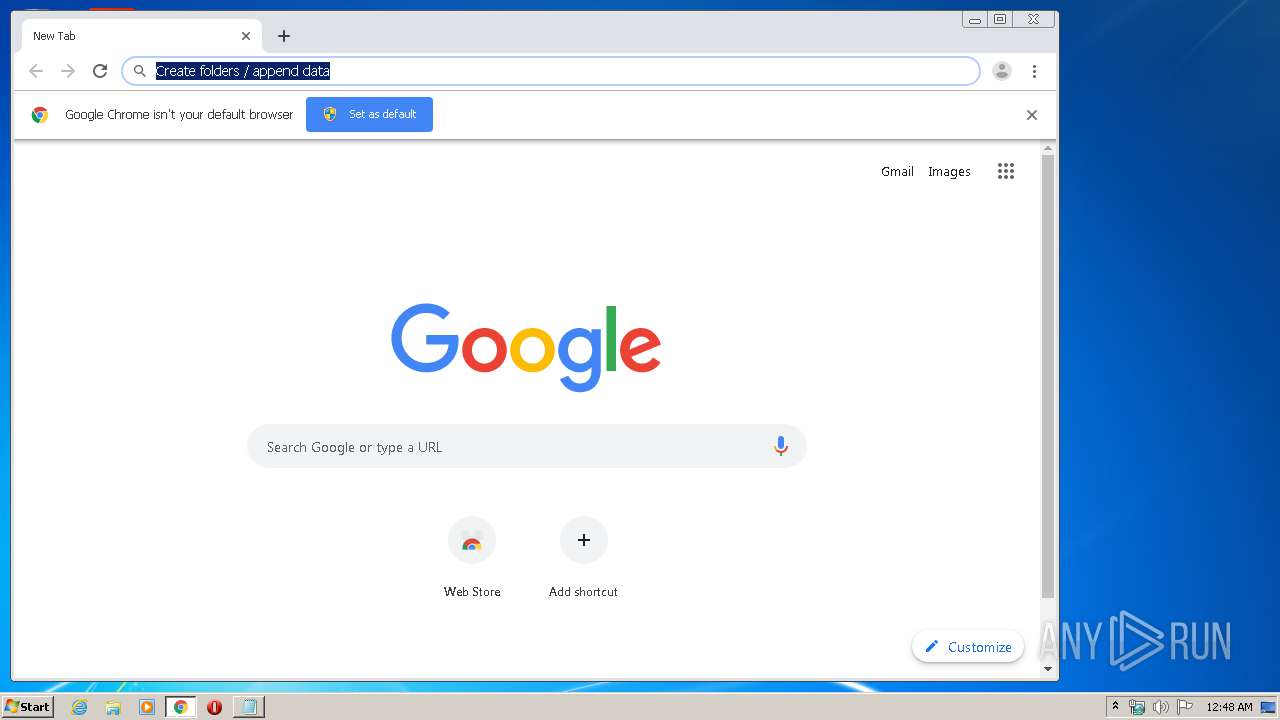
Manual execution by user
- chrome.exe (PID: 3912)
Application launched itself
- chrome.exe (PID: 3912)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
69
Monitored processes
33
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,11926166613281834992,6991204714206838944,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17338222292321711666 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3588 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa8a9d0,0x6fa8a9e0,0x6fa8a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,11926166613281834992,6991204714206838944,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10498470929215545787 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4128 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,11926166613281834992,6991204714206838944,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14211098568252897438 --mojo-platform-channel-handle=3688 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,11926166613281834992,6991204714206838944,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8488039246832576837 --mojo-platform-channel-handle=3696 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,11926166613281834992,6991204714206838944,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3410317960367878989 --mojo-platform-channel-handle=3468 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3676 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,11926166613281834992,6991204714206838944,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7708092554100027160 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2264 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1800 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,11926166613281834992,6991204714206838944,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=3252648291243968050 --mojo-platform-channel-handle=3028 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,11926166613281834992,6991204714206838944,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12987056041381829284 --mojo-platform-channel-handle=3616 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
614
Read events
532
Write events
77
Delete events
5
Modification events
| (PID) Process: | (1676) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3912-13230085704953625 |
Value: 259 | |||
| (PID) Process: | (3912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3912) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
21
Text files
245
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E828549-F48.pma | — | |
MD5:— | SHA256:— | |||
| 3912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFa686cc.TMP | — | |
MD5:— | SHA256:— | |||
| 3912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\64560137-ab68-47b6-8db9-22ffb1c5aca7.tmp | — | |
MD5:— | SHA256:— | |||
| 3912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RFa68853.TMP | text | |
MD5:— | SHA256:— | |||
| 3912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RFa68768.TMP | text | |
MD5:— | SHA256:— | |||
| 3912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa6898b.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
35
DNS requests
22
Threats
7
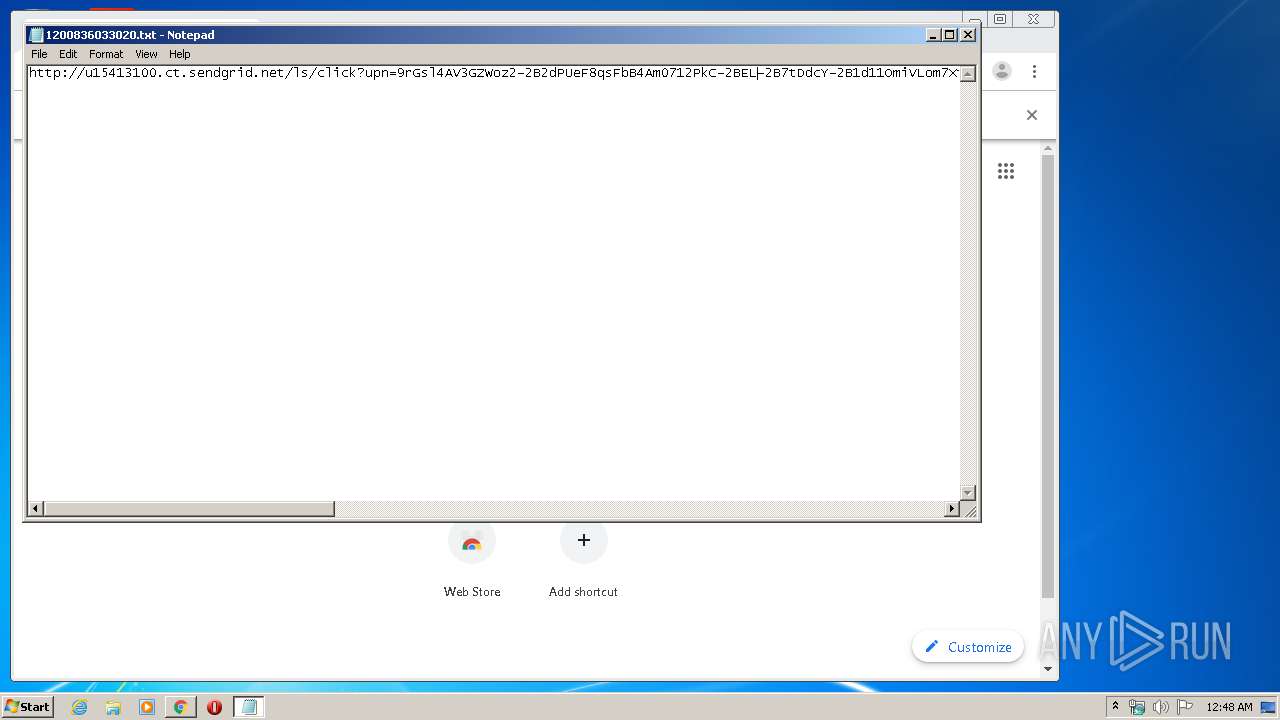
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
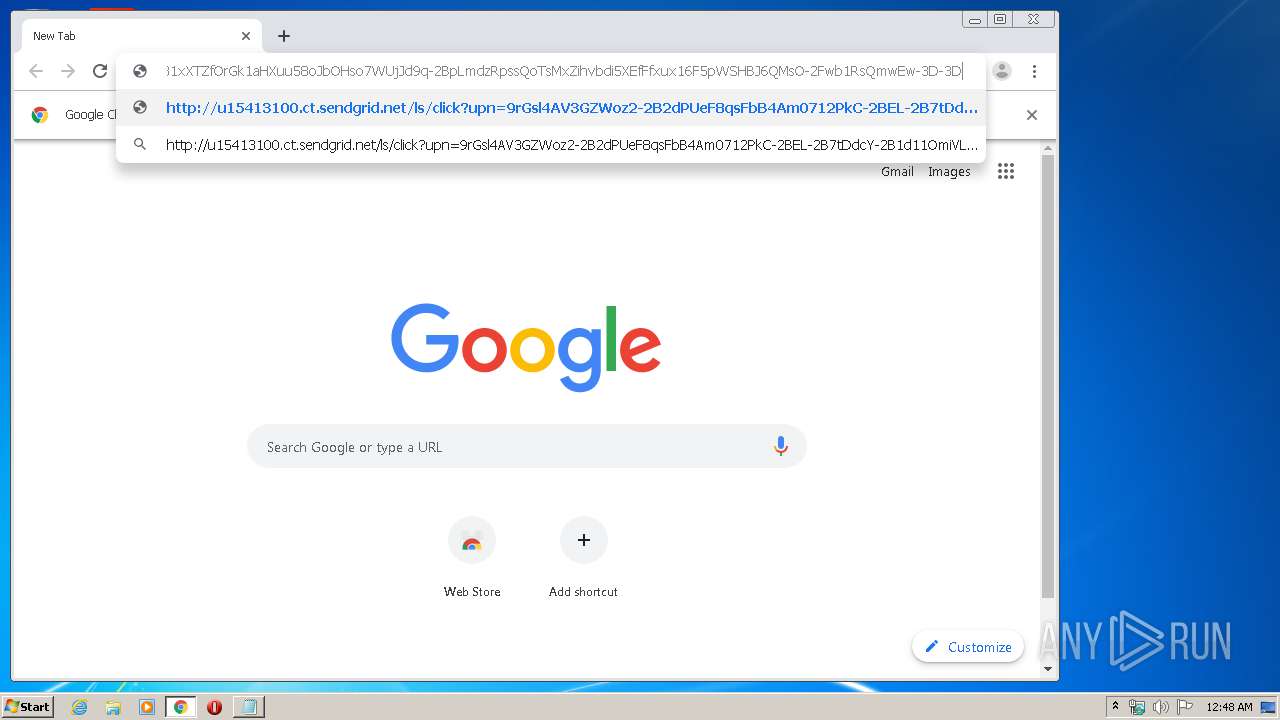
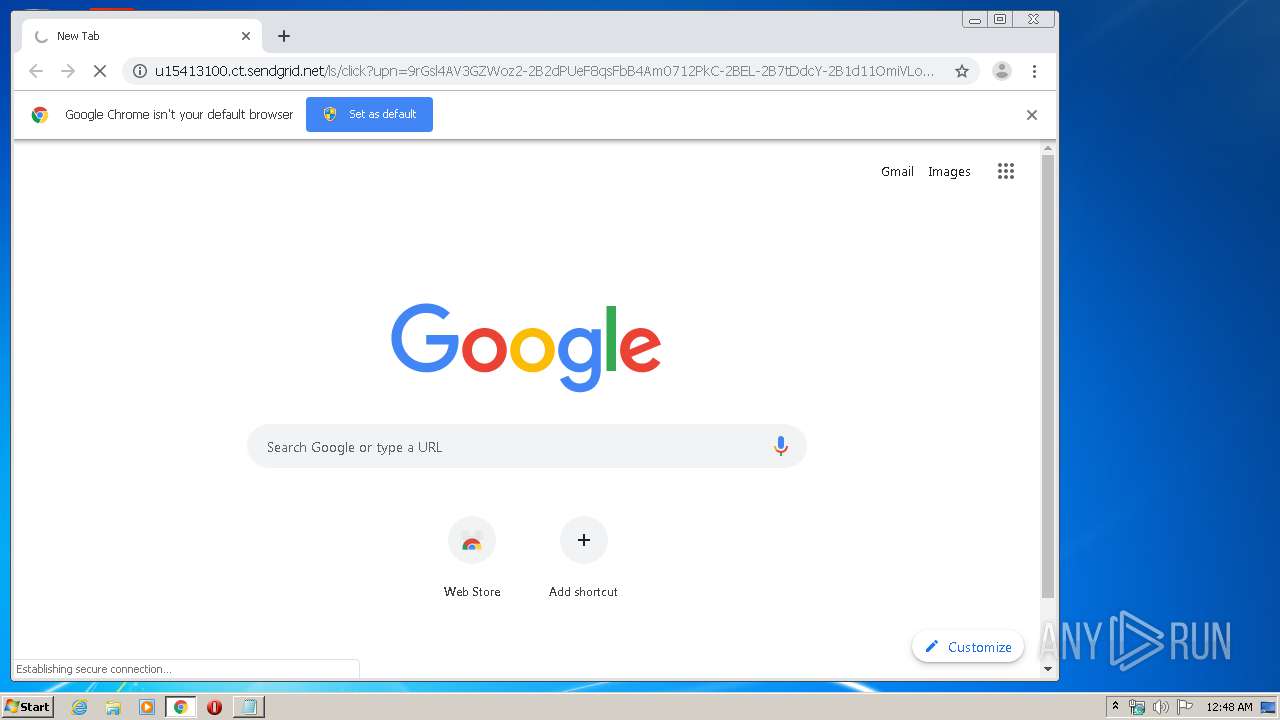
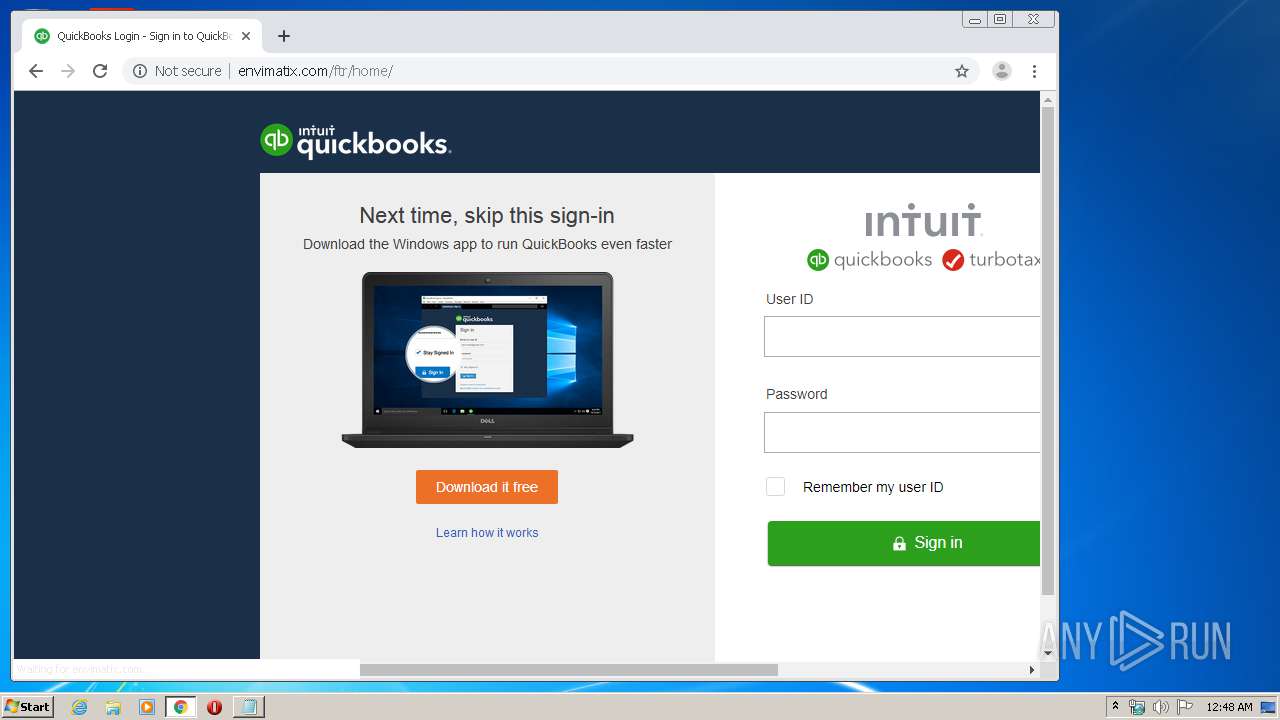
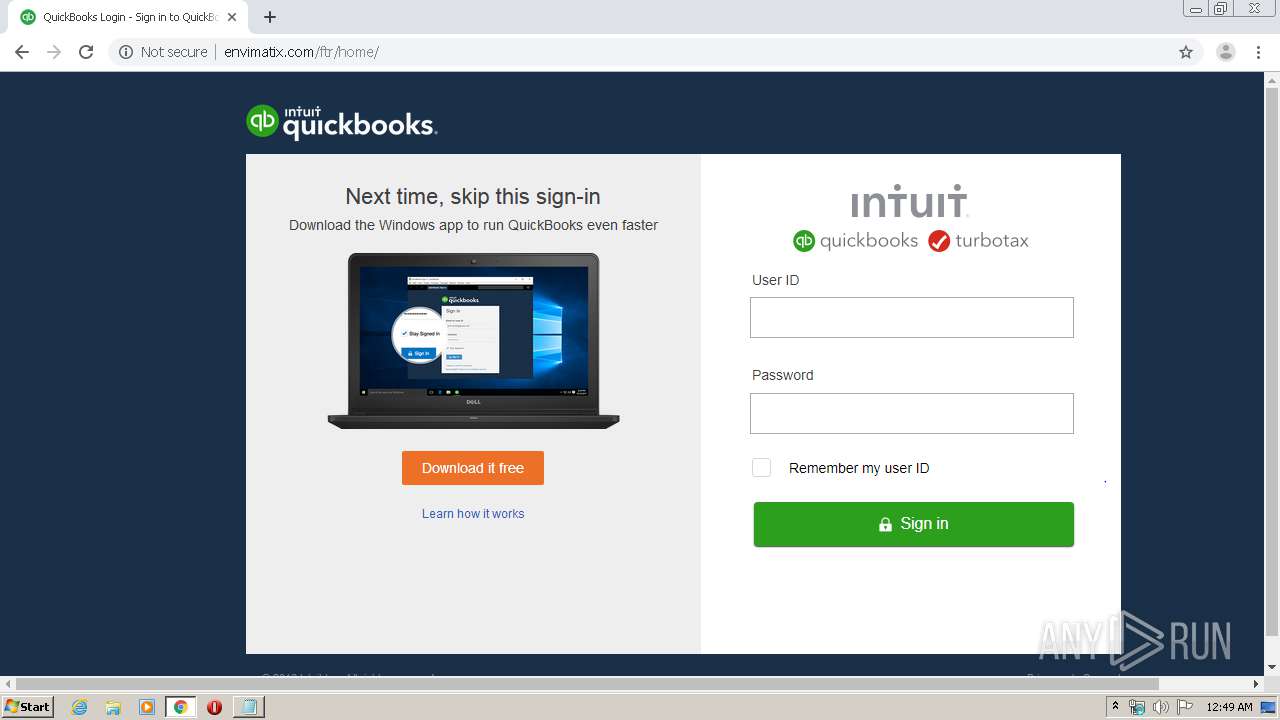
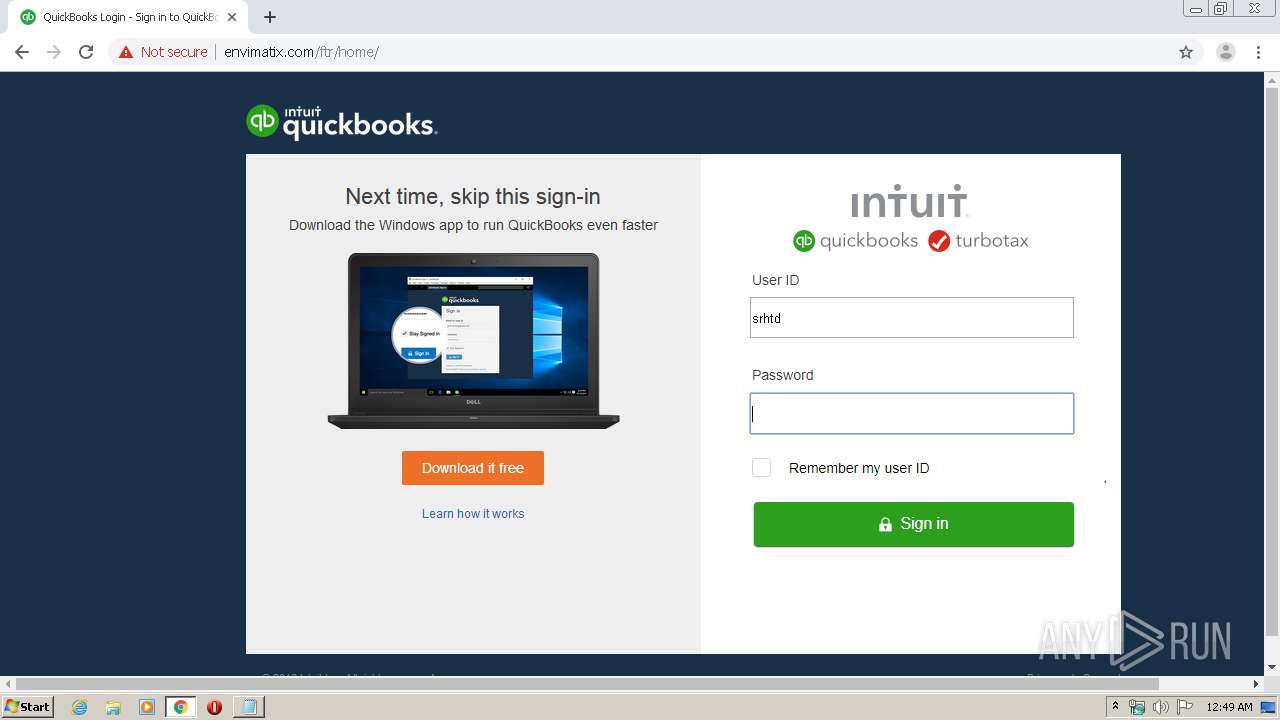
3828 | chrome.exe | GET | 302 | 167.89.115.54:80 | http://u15413100.ct.sendgrid.net/ls/click?upn=9rGsl4AV3GZWoz2-2B2dPUeF8qsFbB4Am0712PkC-2BEL-2B7tDdcY-2B1d11OmiVLom7Xtd85RW_cM6NFmvP8q1sSZv2eCve-2FxBgsljtWegSbBl-2FtLkrGAnL5g0eAh7yxrrzIvJ3R-2FTMT8QVxty92Ebk6vz5GxTc2hnG-2BQv-2FKhCPAGWAHnCXI9CftJT4uFn-2Bxl44Ht81xXTZfOrGk1aHXuu58oJbOHso7WUjJd9q-2BpLmdzRpssQoTsMxZihvbdi5XEfFfxux16F5pWSHBJ6QMsO-2Fwb1RsQmwEw-3D-3D | US | — | — | suspicious |
3828 | chrome.exe | GET | 200 | 69.65.10.202:80 | http://envimatix.com/ftr/home/images/id.PNG | US | image | 4.42 Kb | suspicious |
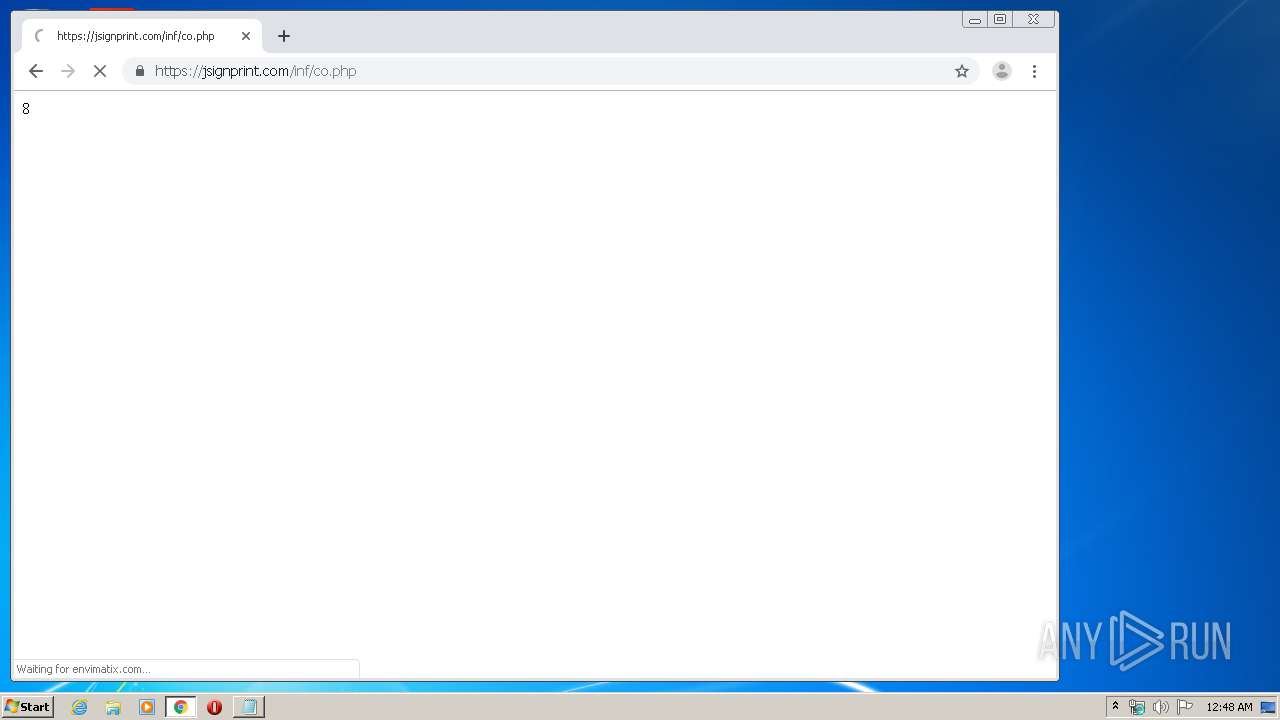
3828 | chrome.exe | GET | 200 | 69.65.10.202:80 | http://envimatix.com/ftr/home/ | US | html | 736 b | suspicious |
3828 | chrome.exe | GET | 200 | 69.65.10.202:80 | http://envimatix.com/ftr/home/images/main.PNG | US | image | 115 Kb | suspicious |
3828 | chrome.exe | GET | 200 | 69.65.10.202:80 | http://envimatix.com/ftr/home/images/sign.PNG | US | image | 1.90 Kb | suspicious |
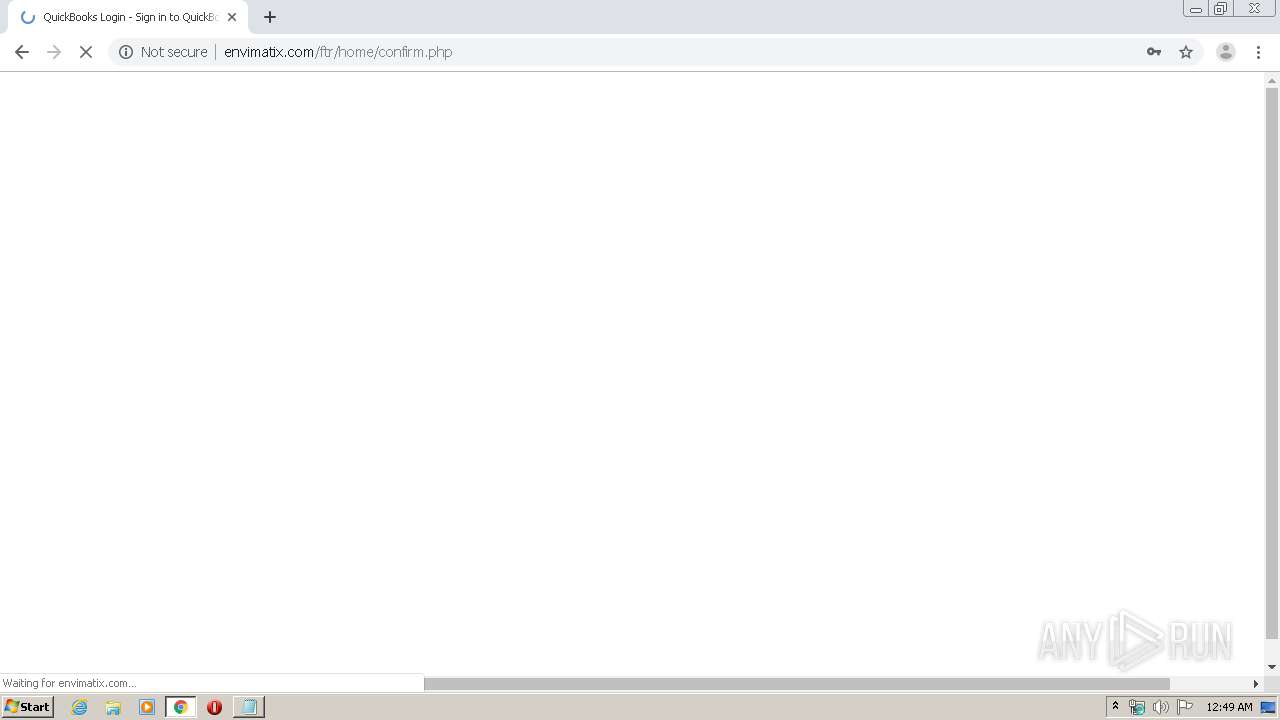
3828 | chrome.exe | POST | 302 | 69.65.10.202:80 | http://envimatix.com/ftr/home/log.php | US | — | — | suspicious |
3828 | chrome.exe | GET | 200 | 69.65.10.202:80 | http://envimatix.com/ftr/home/images/main2.PNG | US | image | 41.2 Kb | suspicious |
3828 | chrome.exe | GET | 200 | 69.65.10.202:80 | http://envimatix.com/ftr/home/images/co.PNG | US | image | 2.10 Kb | suspicious |
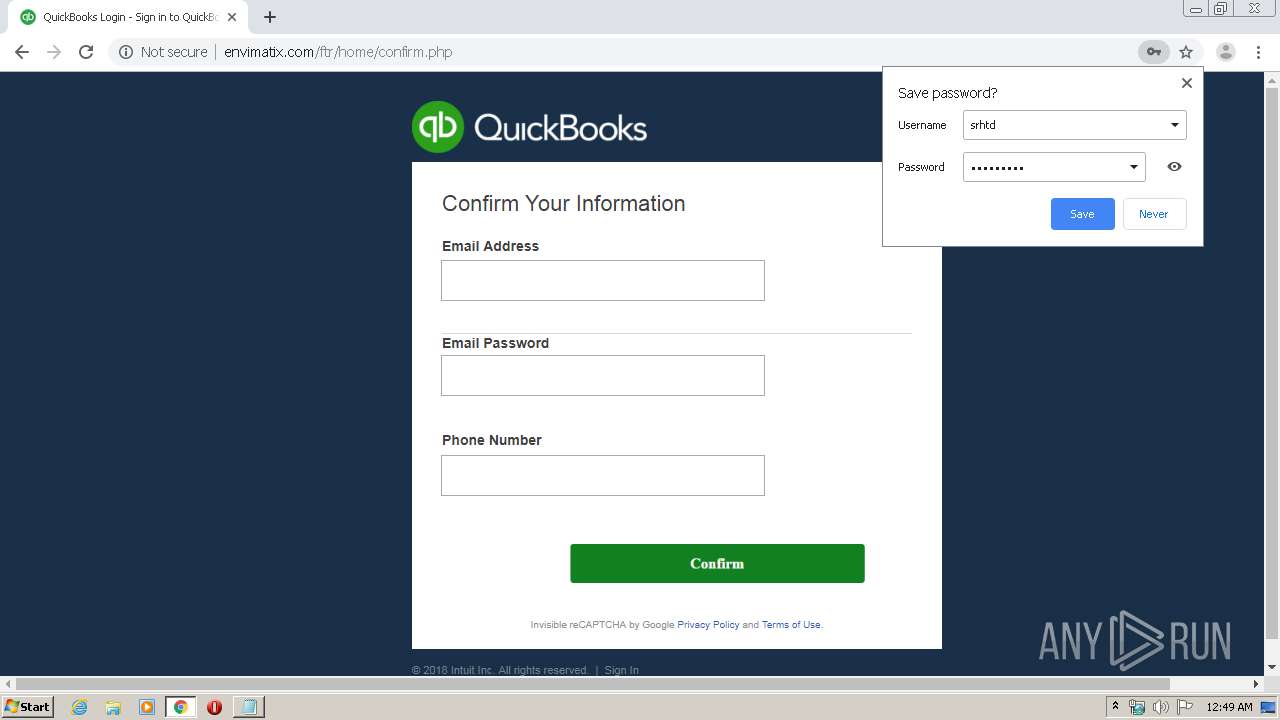
3828 | chrome.exe | GET | 200 | 69.65.10.202:80 | http://envimatix.com/ftr/home/confirm.php | US | html | 846 b | suspicious |
3828 | chrome.exe | GET | 301 | 69.65.10.202:80 | http://envimatix.com/ftr/home | US | html | 238 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3828 | chrome.exe | 172.217.23.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3828 | chrome.exe | 69.16.211.136:443 | jsignprint.com | Liquid Web, L.L.C | US | unknown |
3828 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3828 | chrome.exe | 216.58.210.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3828 | chrome.exe | 172.217.22.3:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3828 | chrome.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3828 | chrome.exe | 172.217.21.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3828 | chrome.exe | 172.217.23.110:443 | apis.google.com | Google Inc. | US | whitelisted |
3828 | chrome.exe | 172.217.16.174:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
3828 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
www.google.com |
| malicious |
www.google.co.uk |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3828 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Chalbhai Phishing Landing Oct 23 2017 |
3828 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Successful Generic Phish (302) 2016-12-16 |
3828 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Chalbhai Phishing Landing Oct 23 2017 |
3828 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Common Unhidebody Function Observed in Phishing Landing |
3828 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Generic Chalbhai Phishing Landing 2018-08-30 |
2 ETPRO signatures available at the full report