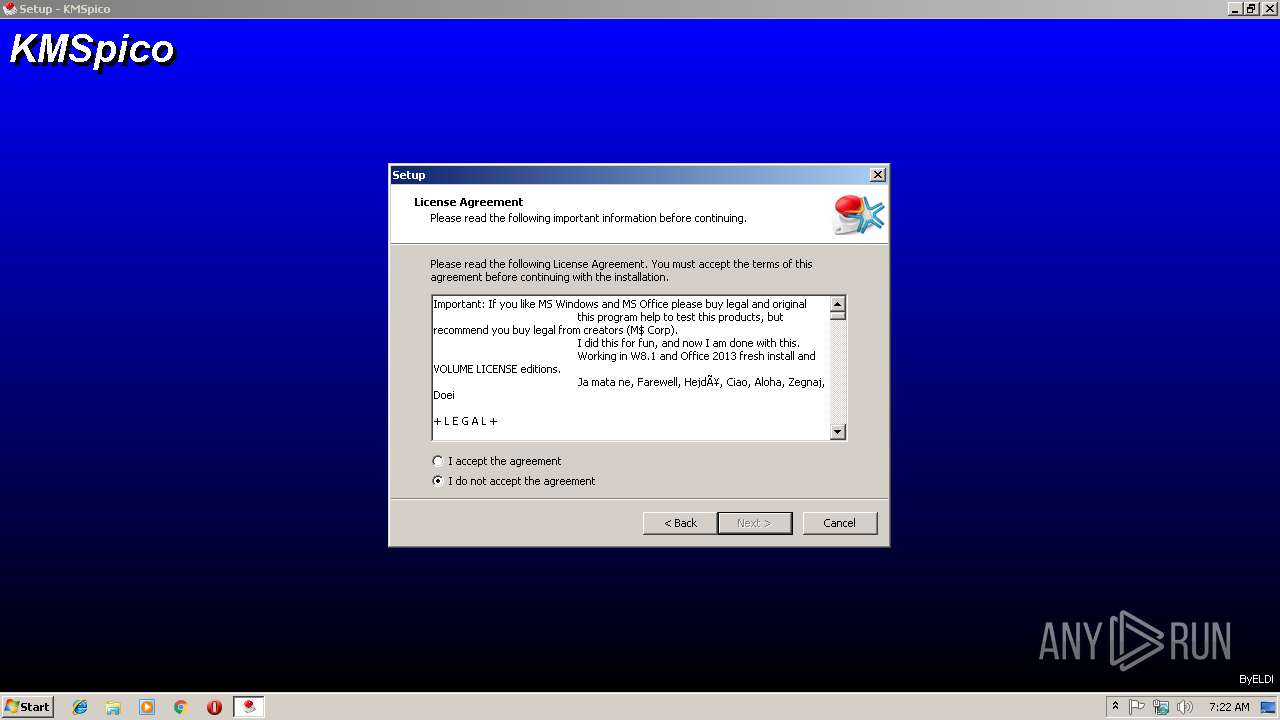
| File name: | KMSPico Setup.10.0.4.exe |
| Full analysis: | https://app.any.run/tasks/57ff11dc-9e90-4719-b34e-58e5a288f238 |
| Verdict: | Suspicious activity |
| Analysis date: | March 05, 2019, 07:21:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive |
| MD5: | BD0E19442031C1DF96ECB5D8A31B8B70 |
| SHA1: | 5DD989186C888F0054C16759643D9DB8FE2621A6 |
| SHA256: | E88A1D92C460DE22835F7E846682A10D6F7E08692E405A3A7E1C33406195CFF5 |
| SSDEEP: | 49152:fP1w+opQ5d8s84TXzXB7/rngVD42U6V3gPc18s9ygwymA00xulQNno/eI0uW5+vu:fqRpMy4V7myKgPUpEgcALkmho/eI0jk2 |
MALICIOUS
Application was dropped or rewritten from another process
- setup.exe (PID: 2384)
- setup.exe (PID: 3296)
- UninsHs.exe (PID: 3652)
- KMSELDI.exe (PID: 3060)
- AutoPico.exe (PID: 2588)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3504)
Loads dropped or rewritten executable
- KMSELDI.exe (PID: 3060)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 316)
SUSPICIOUS
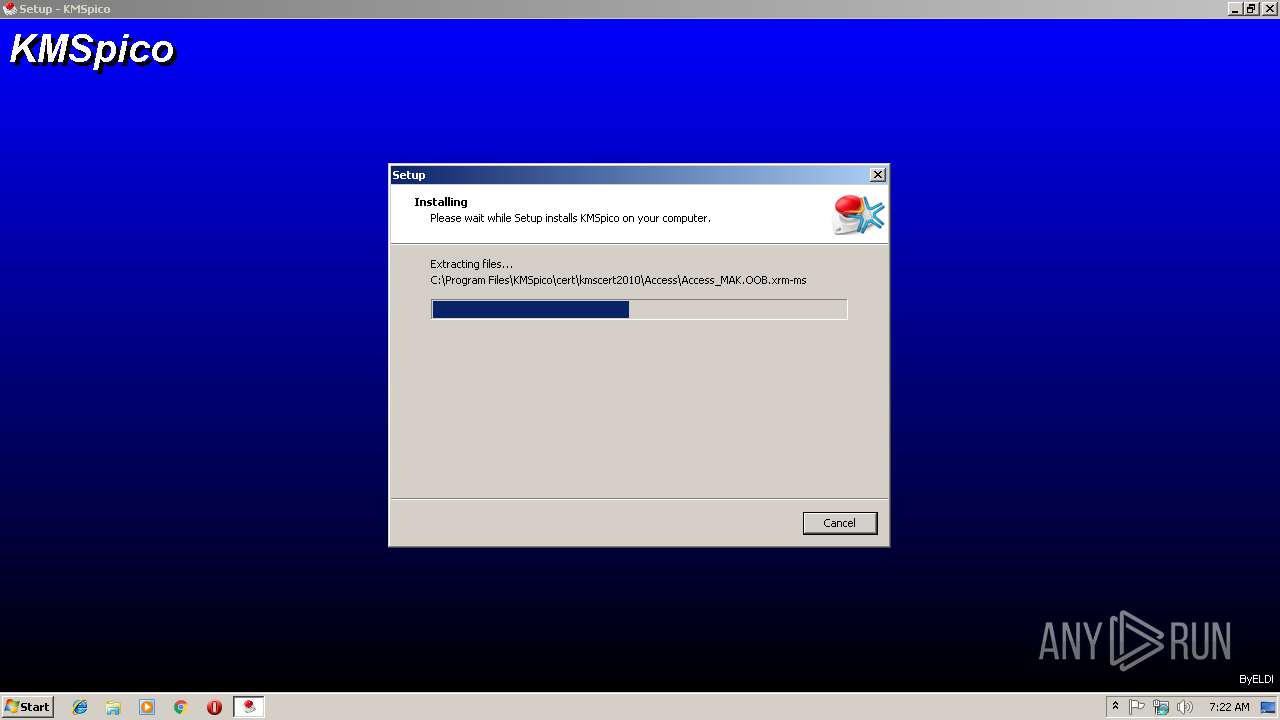
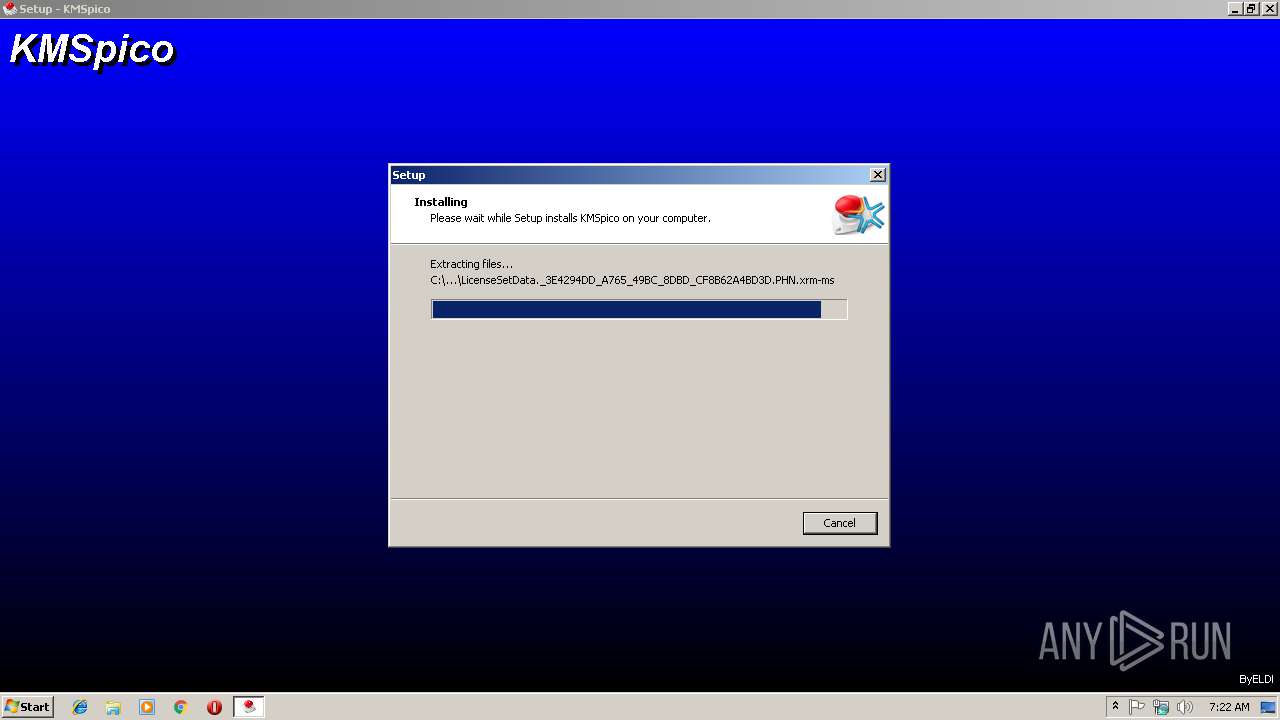
Executable content was dropped or overwritten
- KMSPico Setup.10.0.4.exe (PID: 2940)
- setup.exe (PID: 2384)
- setup.exe (PID: 3296)
- setup.tmp (PID: 3560)
Starts CMD.EXE for commands execution
- setup.tmp (PID: 3560)
Creates files in the Windows directory
- setup.tmp (PID: 3560)
Modifies the phishing filter of IE
- setup.tmp (PID: 3560)
Starts SC.EXE for service management
- cmd.exe (PID: 3436)
Reads Environment values
- KMSELDI.exe (PID: 3060)
- AutoPico.exe (PID: 2588)
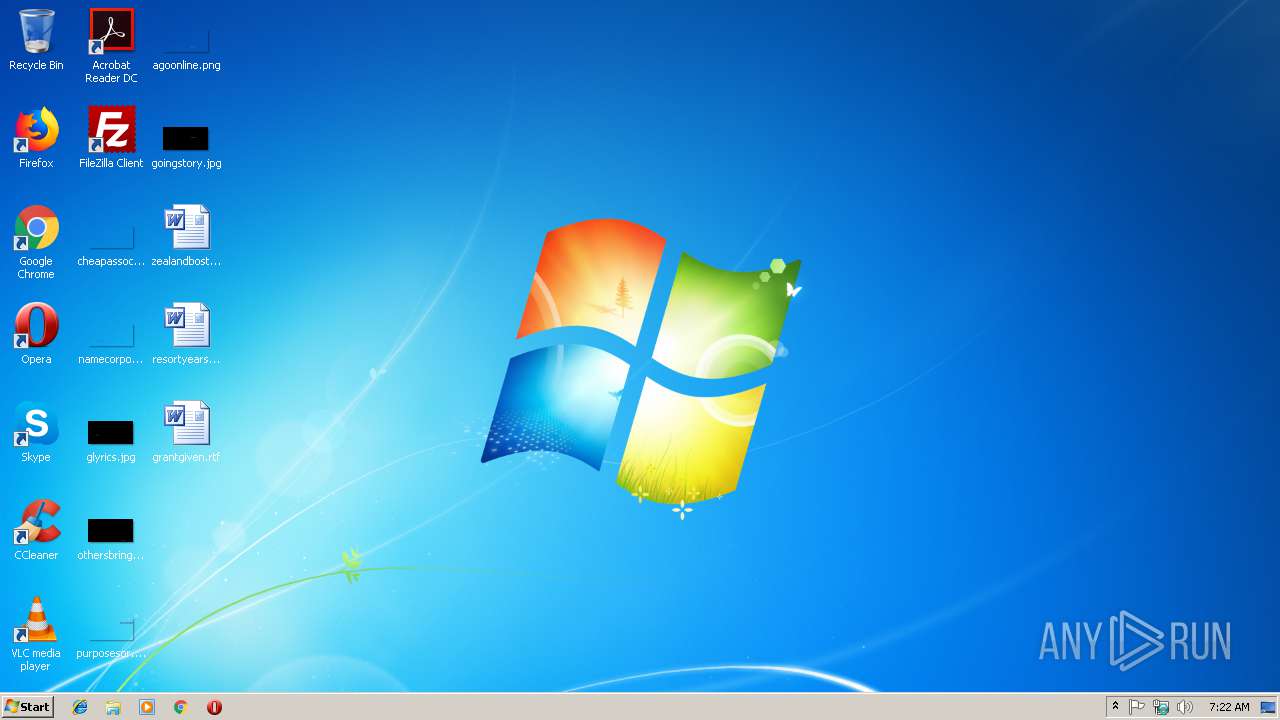
Creates files in the program directory
- AutoPico.exe (PID: 2588)
- KMSELDI.exe (PID: 3060)
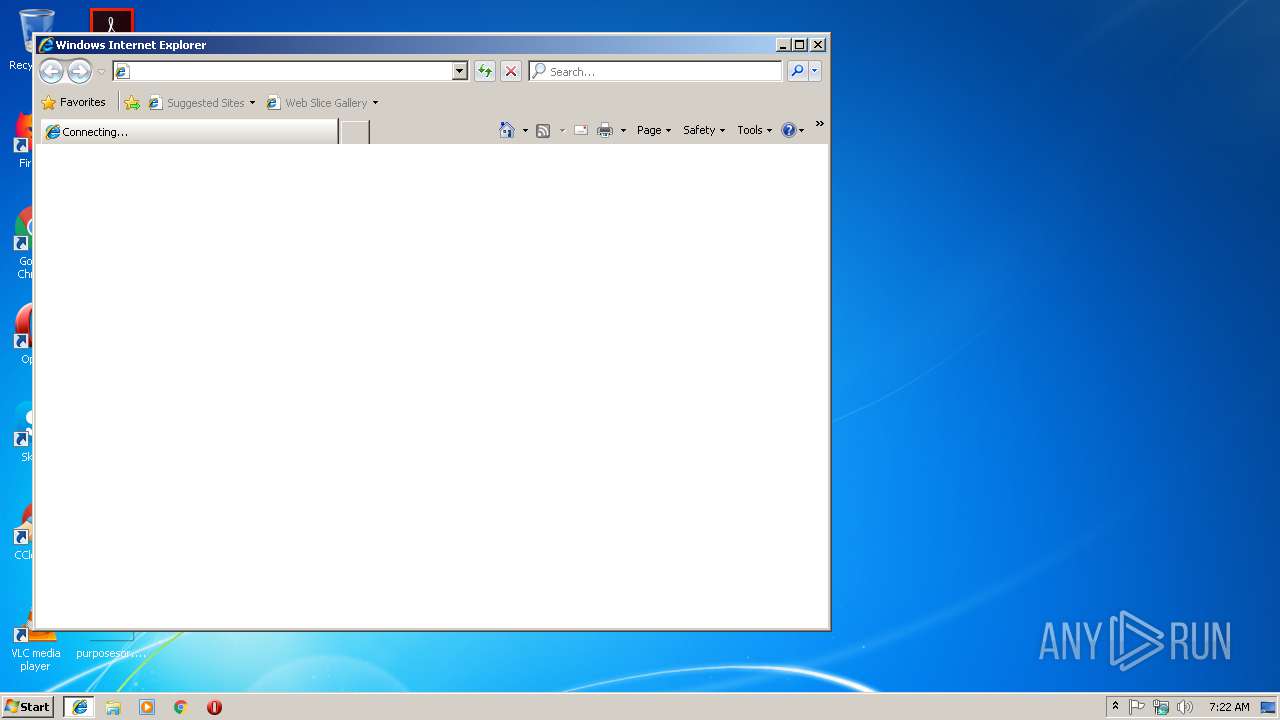
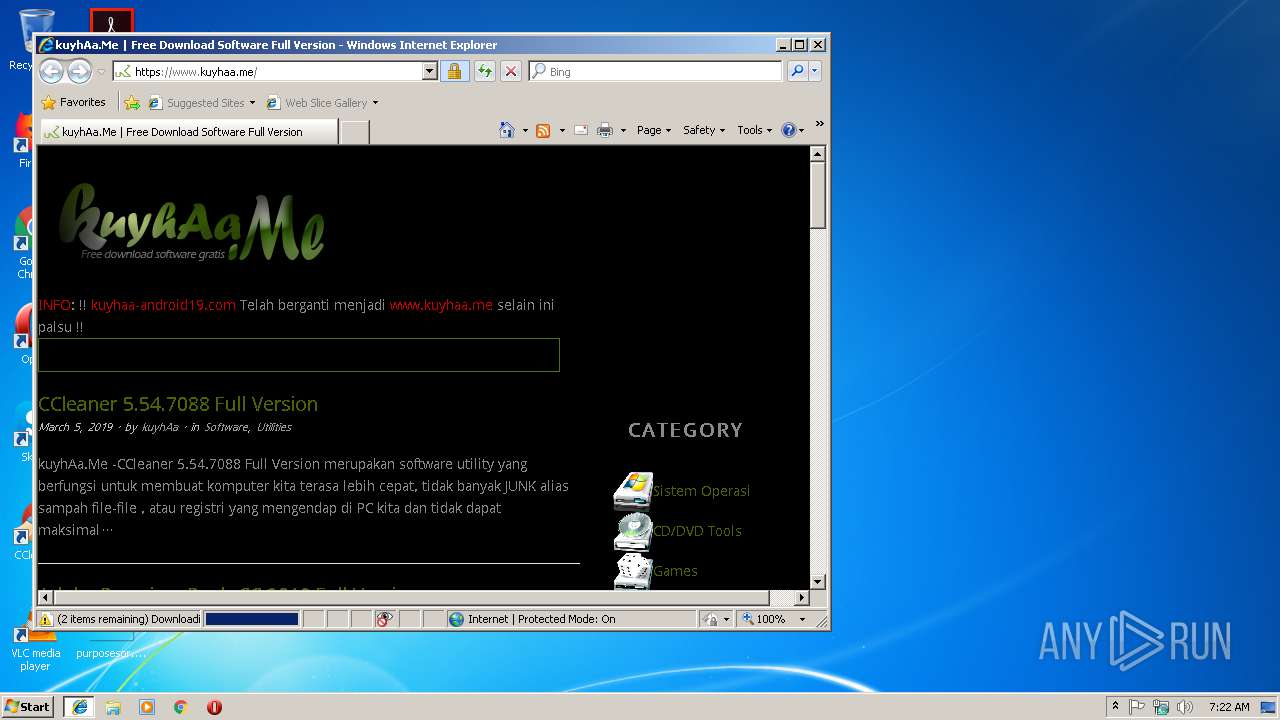
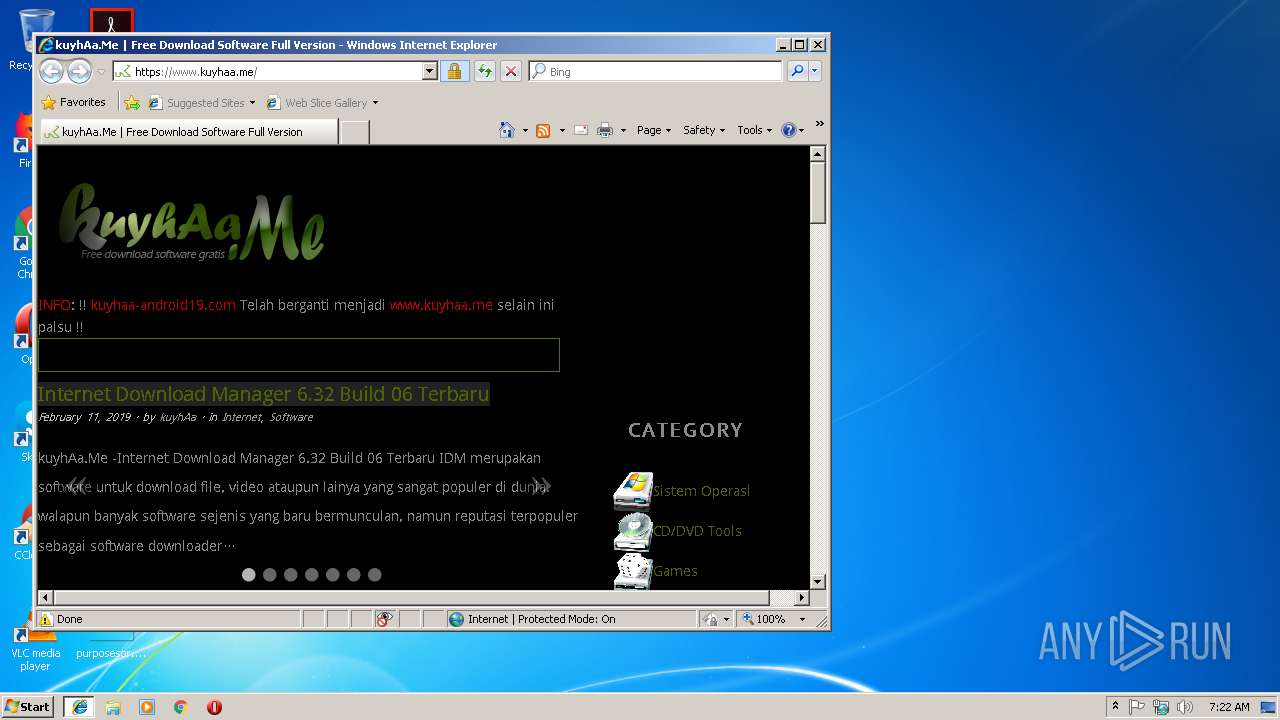
Starts Internet Explorer
- KMSPico Setup.10.0.4.exe (PID: 2940)
INFO
Loads dropped or rewritten executable
- setup.tmp (PID: 3560)
Application was dropped or rewritten from another process
- setup.tmp (PID: 3560)
- setup.tmp (PID: 3948)
Creates a software uninstall entry
- setup.tmp (PID: 3560)
Reads Internet Cache Settings
- iexplore.exe (PID: 3468)
Reads Microsoft Office registry keys
- AutoPico.exe (PID: 2588)
- KMSELDI.exe (PID: 3060)
Changes internet zones settings
- iexplore.exe (PID: 2684)
Application launched itself
- iexplore.exe (PID: 2684)
Reads internet explorer settings
- iexplore.exe (PID: 3468)
Creates files in the user directory
- iexplore.exe (PID: 2684)
- iexplore.exe (PID: 3468)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3020)
Reads settings of System Certificates
- iexplore.exe (PID: 2684)
Creates files in the program directory
- setup.tmp (PID: 3560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:06:10 19:11:07+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 165376 |
| InitializedDataSize: | 44032 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d41b |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Jun-2014 17:11:07 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 10-Jun-2014 17:11:07 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00028553 | 0x00028600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.72377 |
.rdata | 0x0002A000 | 0x00004F53 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.35228 |
.data | 0x0002F000 | 0x000218FC | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.47003 |
.rsrc | 0x00051000 | 0x00004428 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.76082 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.22792 | 1600 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.52412 | 296 | Latin 1 / Western European | Process Default Language | RT_ICON |
3 | 3.91542 | 2216 | Latin 1 / Western European | Process Default Language | RT_ICON |
4 | 3.55205 | 1384 | Latin 1 / Western European | Process Default Language | RT_ICON |
7 | 3.1586 | 482 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.11685 | 460 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 3.15447 | 494 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 2.99727 | 326 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.2036 | 1094 | Latin 1 / Western European | English - United States | RT_STRING |
12 | 3.12889 | 358 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
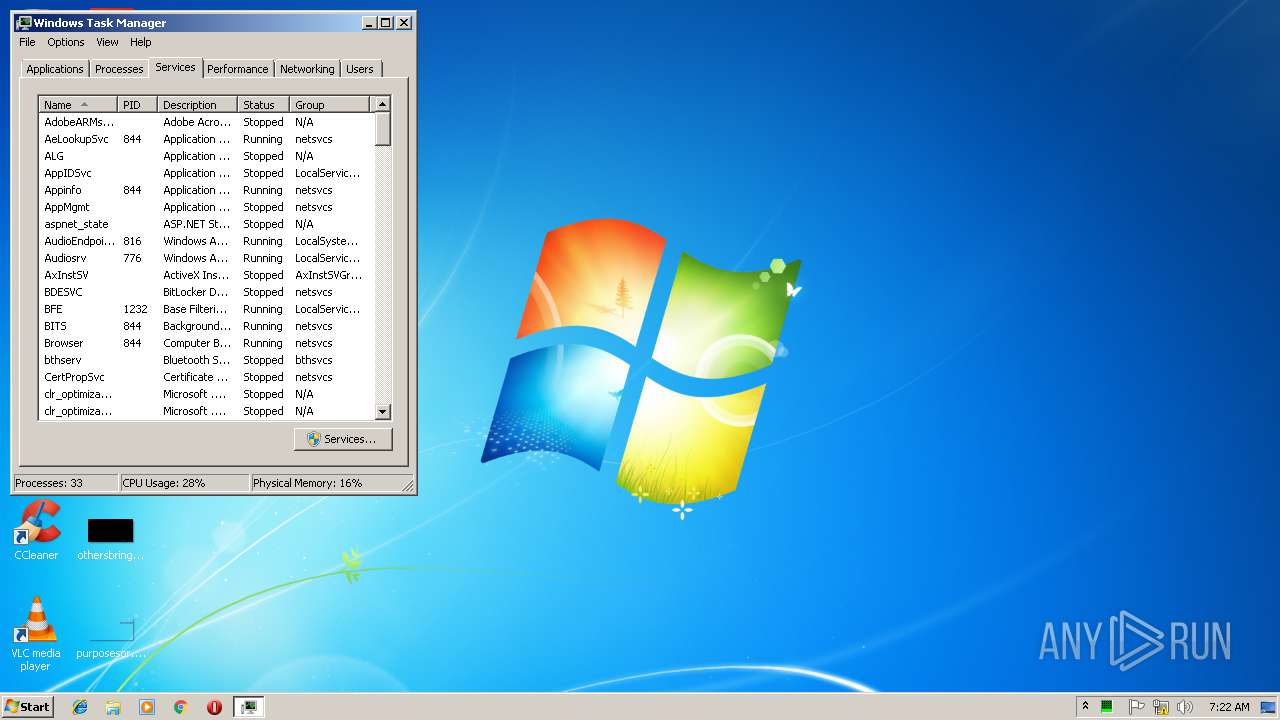
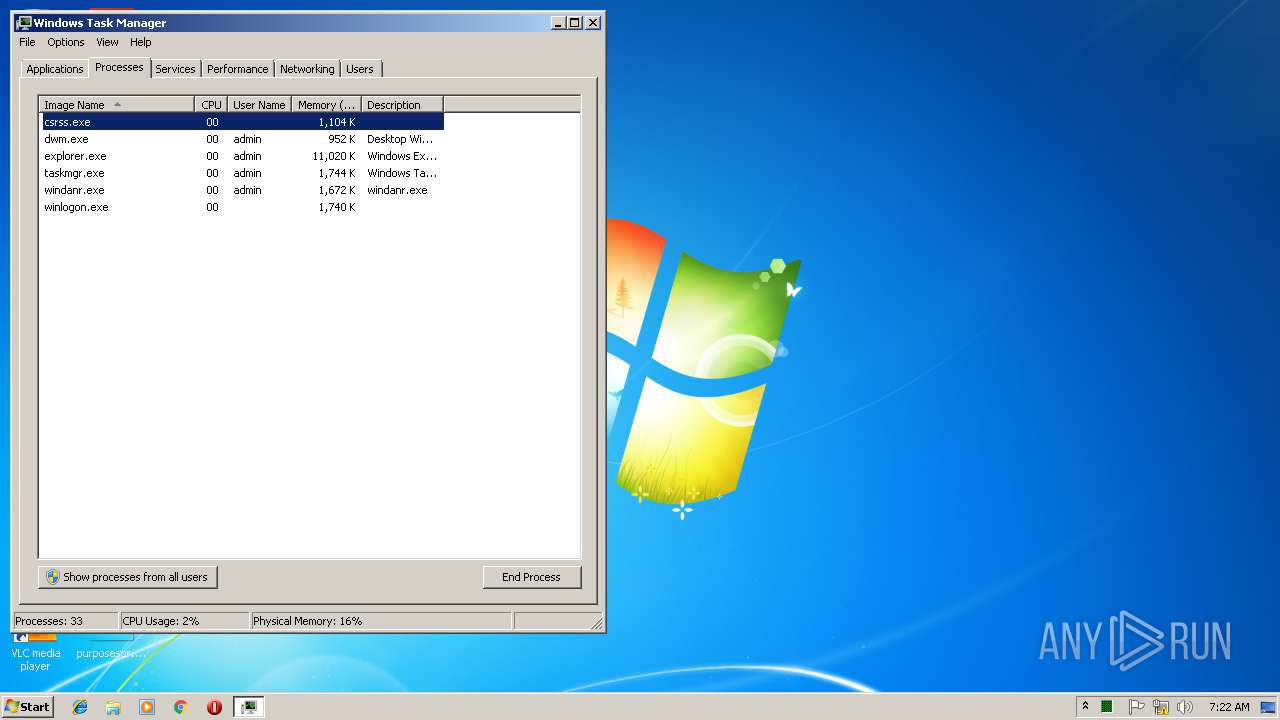
Total processes
53
Monitored processes
16
Malicious processes
3
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | SCHTASKS /Create /TN "AutoPico Daily Restart" /TR "'C:\Program Files\KMSpico\AutoPico.exe' /silent" /SC DAILY /ST 23:59:59 /RU "NT AUTHORITY\SYSTEM" /RL Highest /F | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2384 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\setup.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\setup.exe | KMSPico Setup.10.0.4.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: KMSpico Setup Exit code: 0 Version: 10.0.4 Modules
| |||||||||||||||
| 2588 | "C:\Program Files\KMSpico\AutoPico.exe" /silent | C:\Program Files\KMSpico\AutoPico.exe | setup.tmp | ||||||||||||
User: admin Company: @ByELDI Integrity Level: HIGH Description: AutoPico Exit code: 0 Version: 13.0.0.7 Modules
| |||||||||||||||
| 2592 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2684 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | KMSPico Setup.10.0.4.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2940 | "C:\Users\admin\AppData\Local\Temp\KMSPico Setup.10.0.4.exe" | C:\Users\admin\AppData\Local\Temp\KMSPico Setup.10.0.4.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3020 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 3060 | "C:\Program Files\KMSpico\KMSELDI.exe" /silent /backup | C:\Program Files\KMSpico\KMSELDI.exe | setup.tmp | ||||||||||||
User: admin Company: @ByELDI Integrity Level: HIGH Description: KMS GUI ELDI Exit code: 0 Version: 34.0.0.7 Modules
| |||||||||||||||
| 3296 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\setup.exe" /SPAWNWND=$1014C /NOTIFYWND=$10140 | C:\Users\admin\AppData\Local\Temp\RarSFX0\setup.exe | setup.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: KMSpico Setup Exit code: 0 Version: 10.0.4 Modules
| |||||||||||||||
| 3436 | "C:\Windows\system32\cmd.exe" /C ""C:\Program Files\KMSpico\scripts\Install_Service.cmd"" | C:\Windows\system32\cmd.exe | — | setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 492
Read events
1 404
Write events
81
Delete events
7
Modification events
| (PID) Process: | (2940) KMSPico Setup.10.0.4.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2940) KMSPico Setup.10.0.4.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3560) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: E80D0000F4AAF61E24D3D401 | |||
| (PID) Process: | (3560) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 7232E3B59A811E65255EDD3BCA4F727BCA6D463E1D671BCD853E3660DBD19CE2 | |||
| (PID) Process: | (3560) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3560) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\KMSpico\driver\tap-windows-9.21.0.exe | |||
| (PID) Process: | (3560) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 497ADFAF4724BC3827BE356A2F7C8446F4D8D8C6E68135B65F858E6CD9E5CEBA | |||
| (PID) Process: | (3560) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\System |
| Operation: | write | Name: | EnableSmartScreen |
Value: 0 | |||
| (PID) Process: | (3560) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SmartScreenEnabled |
Value: Off | |||
| (PID) Process: | (3560) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\PhishingFilter |
| Operation: | write | Name: | EnabledV9 |
Value: 0 | |||
Executable files
13
Suspicious files
5
Text files
536
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3560 | setup.tmp | C:\Program Files\KMSpico\is-3UE5G.tmp | — | |
MD5:— | SHA256:— | |||
| 3560 | setup.tmp | C:\Program Files\KMSpico\driver\is-L3ROU.tmp | — | |
MD5:— | SHA256:— | |||
| 3560 | setup.tmp | C:\Program Files\KMSpico\driver\is-RR7OA.tmp | — | |
MD5:— | SHA256:— | |||
| 3560 | setup.tmp | C:\Program Files\KMSpico\is-S3JCG.tmp | — | |
MD5:— | SHA256:— | |||
| 3560 | setup.tmp | C:\Program Files\KMSpico\is-HE45O.tmp | — | |
MD5:— | SHA256:— | |||
| 3560 | setup.tmp | C:\Program Files\KMSpico\is-F2H98.tmp | — | |
MD5:— | SHA256:— | |||
| 3560 | setup.tmp | C:\Windows\system32\is-KKOKU.tmp | — | |
MD5:— | SHA256:— | |||
| 3560 | setup.tmp | C:\Program Files\KMSpico\is-BF2IJ.tmp | — | |
MD5:— | SHA256:— | |||
| 3560 | setup.tmp | C:\Program Files\KMSpico\is-0PLN5.tmp | — | |
MD5:— | SHA256:— | |||
| 3560 | setup.tmp | C:\Program Files\KMSpico\is-HA4V9.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
15
DNS requests
9
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3468 | iexplore.exe | GET | 302 | 172.217.18.115:80 | http://urlaink.kuyhaa-android19.com/VisitLink | US | — | — | malicious |
3468 | iexplore.exe | GET | 301 | 173.212.207.25:80 | http://www.kuyhaa-android19.com/ | DE | html | 185 b | unknown |
2684 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2684 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3468 | iexplore.exe | 172.217.18.115:80 | urlaink.kuyhaa-android19.com | Google Inc. | US | malicious |
3468 | iexplore.exe | 173.212.207.25:80 | www.kuyhaa-android19.com | Contabo GmbH | DE | unknown |
3468 | iexplore.exe | 5.189.183.100:443 | www.kuyhaa.me | Contabo GmbH | DE | unknown |
3468 | iexplore.exe | 216.58.206.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3468 | iexplore.exe | 172.217.22.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3468 | iexplore.exe | 172.217.21.232:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3468 | iexplore.exe | 142.91.159.222:443 | patoris.xyz | — | NL | suspicious |
2684 | iexplore.exe | 5.189.183.100:443 | www.kuyhaa.me | Contabo GmbH | DE | unknown |
3468 | iexplore.exe | 216.58.208.46:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
urlaink.kuyhaa-android19.com |
| malicious |
www.bing.com |
| whitelisted |
www.kuyhaa-android19.com |
| unknown |
www.kuyhaa.me |
| unknown |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
patoris.xyz |
| suspicious |
www.googletagmanager.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3468 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |