| File name: | instbeta.exe |
| Full analysis: | https://app.any.run/tasks/0ea3fd04-a81e-40cd-8103-1e9ed89e1351 |
| Verdict: | Malicious activity |
| Analysis date: | June 28, 2019, 05:01:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F3E4718E8BB91248C9C0DDBCB604EB8F |
| SHA1: | 59FF294DD0CF60DC198295A79D516C109E6CD75A |
| SHA256: | E88714CE266E76AE871E96C6F1587793E0E88FF0136EA393DFC46CA0205CE039 |
| SSDEEP: | 98304:Mnh6FCbH0dtNFhwK11GOZz0q1m2A1fsC3Be7m6H2:MnoFCr0dt1wKKO9u2kfUm1 |
MALICIOUS
Runs PING.EXE for delay simulation
- cmd.exe (PID: 3252)
- cmd.exe (PID: 3488)
Loads dropped or rewritten executable
- instbeta.exe (PID: 2728)
Application was dropped or rewritten from another process
- instbeta.exe (PID: 3448)
- instbeta.exe (PID: 2728)
- VCardParser.exe (PID: 3136)
- VcCleanup.exe (PID: 2936)
SUSPICIOUS
Executable content was dropped or overwritten
- instbeta.exe (PID: 2728)
- instbeta.exe (PID: 3084)
Creates files in the program directory
- instbeta.exe (PID: 3084)
Starts CMD.EXE for commands execution
- VcCleanup.exe (PID: 2936)
- VCardParser.exe (PID: 3136)
Low-level read access rights to disk partition
- instbeta.exe (PID: 2728)
Reads Internet Cache Settings
- instbeta.exe (PID: 2728)
Creates files in the user directory
- instbeta.exe (PID: 2728)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:09:30 20:01:44+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 190976 |
| InitializedDataSize: | 82432 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d549 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Sep-2018 18:01:44 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 30-Sep-2018 18:01:44 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002E924 | 0x0002EA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.69845 |
.rdata | 0x00030000 | 0x00009A8C | 0x00009C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.13014 |
.data | 0x0003A000 | 0x000203A0 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.23545 |
.gfids | 0x0005B000 | 0x000000E8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.09308 |
.rsrc | 0x0005C000 | 0x000077A4 | 0x00007800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.15539 |
.reloc | 0x00064000 | 0x00001FDC | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.67876 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.22792 | 1600 | Latin 1 / Western European | Chinese - PRC | RT_MANIFEST |
2 | 4.56733 | 4264 | Latin 1 / Western European | Process Default Language | RT_ICON |
3 | 4.60391 | 1128 | Latin 1 / Western European | Process Default Language | RT_ICON |
7 | 5.24197 | 182 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
8 | 5.27357 | 214 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
9 | 5.38938 | 202 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
10 | 5.08077 | 118 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
11 | 5.36199 | 642 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
12 | 4.71863 | 148 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
13 | 4.78806 | 120 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
45
Monitored processes
9
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2728 | "C:\ProgramData\instbeta.exe" | C:\ProgramData\instbeta.exe | instbeta.exe | ||||||||||||
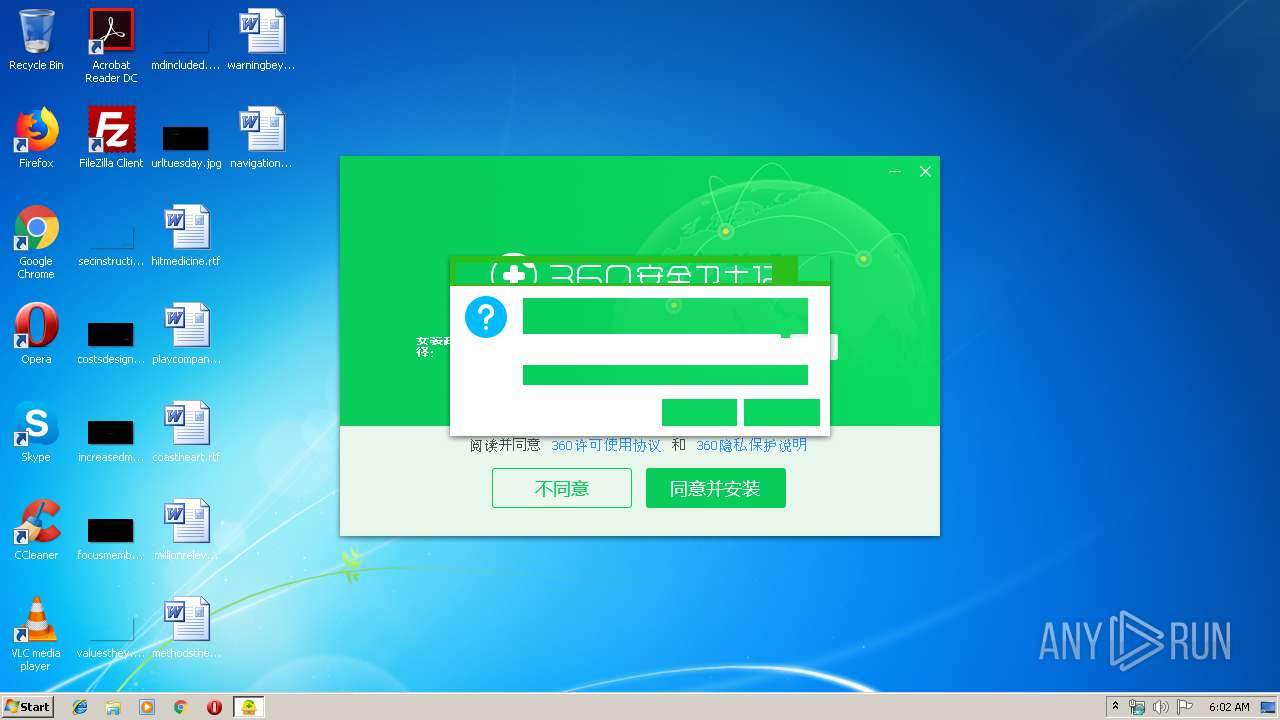
User: admin Company: 360.cn Integrity Level: HIGH Description: 360 安全卫士在线安装程序 Exit code: 1 Version: 12, 0, 0, 1061 Modules
| |||||||||||||||
| 2936 | "C:\ProgramData\VcCleanup.exe" | C:\ProgramData\VcCleanup.exe | — | instbeta.exe | |||||||||||
User: admin Company: Alibaba Group. Integrity Level: MEDIUM Description: DingTalk Exit code: 0 Version: 3.5.6.1 Modules
| |||||||||||||||
| 3084 | "C:\Users\admin\AppData\Local\Temp\instbeta.exe" | C:\Users\admin\AppData\Local\Temp\instbeta.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3108 | ping -n 244 127.0.0.1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3136 | "C:\ProgramData\VCardParser.exe" | C:\ProgramData\VCardParser.exe | — | instbeta.exe | |||||||||||
User: admin Company: Alibaba Group. Integrity Level: MEDIUM Description: DingTalk Exit code: 0 Version: 3.5.6.1 Modules
| |||||||||||||||
| 3148 | ping -n 239 127.0.0.1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3252 | cmd.exe /c ping -n 244 127.0.0.1>nul & exit | C:\Windows\system32\cmd.exe | — | VcCleanup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3448 | "C:\ProgramData\instbeta.exe" | C:\ProgramData\instbeta.exe | — | instbeta.exe | |||||||||||
User: admin Company: 360.cn Integrity Level: MEDIUM Description: 360 安全卫士在线安装程序 Exit code: 3221226540 Version: 12, 0, 0, 1061 Modules
| |||||||||||||||
| 3488 | cmd.exe /c ping -n 239 127.0.0.1>nul & exit | C:\Windows\system32\cmd.exe | — | VCardParser.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
173
Read events
145
Write events
28
Delete events
0
Modification events
| (PID) Process: | (3084) instbeta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3084) instbeta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2728) instbeta.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\instbeta_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2728) instbeta.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\instbeta_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2728) instbeta.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\instbeta_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2728) instbeta.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\instbeta_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2728) instbeta.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\instbeta_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2728) instbeta.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\instbeta_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2728) instbeta.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\instbeta_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2728) instbeta.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\instbeta_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
5
Suspicious files
1
Text files
4
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2728 | instbeta.exe | C:\Users\admin\AppData\Local\Temp\{3DC36261-C578-4765-AC07-62EB35ED5A47}.tmp | — | |
MD5:— | SHA256:— | |||
| 2728 | instbeta.exe | C:\Users\admin\AppData\Local\Temp\{7F833D16-304E-4b7f-A89F-2C94375C3BD0}.tmp | — | |
MD5:— | SHA256:— | |||
| 3084 | instbeta.exe | C:\ProgramData\VcCleanup.exe | executable | |
MD5:— | SHA256:— | |||
| 3084 | instbeta.exe | C:\ProgramData\instbeta.exe | executable | |
MD5:— | SHA256:— | |||
| 2728 | instbeta.exe | C:\Users\admin\AppData\Local\Temp\{840DB619-6AC6-45db-B8F6-AF75E6CE50BD}.tmp | image | |
MD5:402C9D31E2079948E743562CB48AF2A6 | SHA256:D82DF7AFA80AB17CF1D298488C66902F192034B6BB18176F5BD5C5B74E348E79 | |||
| 2728 | instbeta.exe | C:\Users\admin\AppData\Local\Temp\{A62B1893-BF43-46ee-A675-1F3380DC6254}.tmp | image | |
MD5:— | SHA256:— | |||
| 2728 | instbeta.exe | C:\Users\admin\AppData\Local\Temp\{509348A6-836F-4a36-AECA-3861C243338F}.tmp | image | |
MD5:— | SHA256:— | |||
| 2728 | instbeta.exe | C:\Users\admin\AppData\Local\Temp\{A44B7723-4283-41b8-B9C0-6B1983C61382}.tmp\themes\NewInstallAir\NewInstallAir.ui | compressed | |
MD5:— | SHA256:— | |||
| 2728 | instbeta.exe | C:\Users\admin\AppData\Local\Temp\{A44B7723-4283-41b8-B9C0-6B1983C61382}.tmp\themes\theme_NewInstallAir.xml | xml | |
MD5:— | SHA256:— | |||
| 2728 | instbeta.exe | C:\Users\admin\AppData\Local\Temp\{E29B865B-082E-4e5b-8C9E-F08A1E1493FB}.tmp\360P2SP.dll | executable | |
MD5:D875875EB3282B692AB10E946EA22361 | SHA256:0ECA2E140F973B2011C633D4D92E512A1F77E1DA610CFE0F4538C0B451270016 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
6
DNS requests
6
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2728 | instbeta.exe | GET | — | 171.8.167.89:80 | http://s.360.cn/safe/instcomp.htm?soft=1000&status=12&m=cfe1ce9b8f5123cc37f394accff90c49&from=safebeta_new&vv=10&ver=12.0.0.1061 | CN | — | — | whitelisted |
2728 | instbeta.exe | GET | — | 171.8.167.89:80 | http://s.360.cn/safe/instcomp.htm?soft=1000&status=1&m=cfe1ce9b8f5123cc37f394accff90c49&from=safebeta_new&vv=10&ver=12.0.0.1061 | CN | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2728 | instbeta.exe | 1.192.136.170:3478 | st.p.360.cn | No.31,Jin-rong Street | CN | unknown |
2728 | instbeta.exe | 171.8.167.89:80 | s.360.cn | No.31,Jin-rong Street | CN | suspicious |
2728 | instbeta.exe | 180.153.230.26:443 | pinst.360.cn | China Telecom (Group) | CN | unknown |
2728 | instbeta.exe | 180.163.229.164:80 | tr.p.360.cn | China Telecom (Group) | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
st.p.360.cn |
| whitelisted |
tr.p.360.cn |
| suspicious |
agt.p.360.cn |
| whitelisted |
s.360.cn |
| whitelisted |
pinst.360.cn |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2728 | instbeta.exe | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag false change port flag false) |
2728 | instbeta.exe | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag true change port flag false) |
2728 | instbeta.exe | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag false change port flag true) |