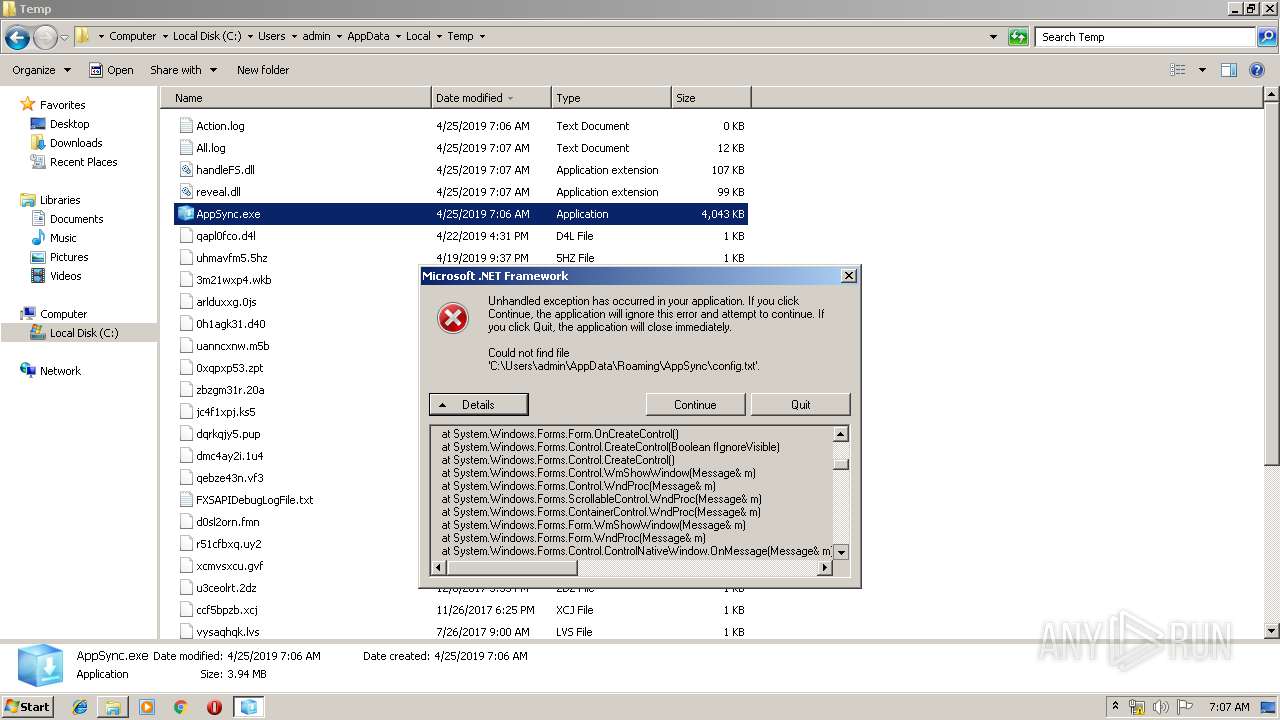
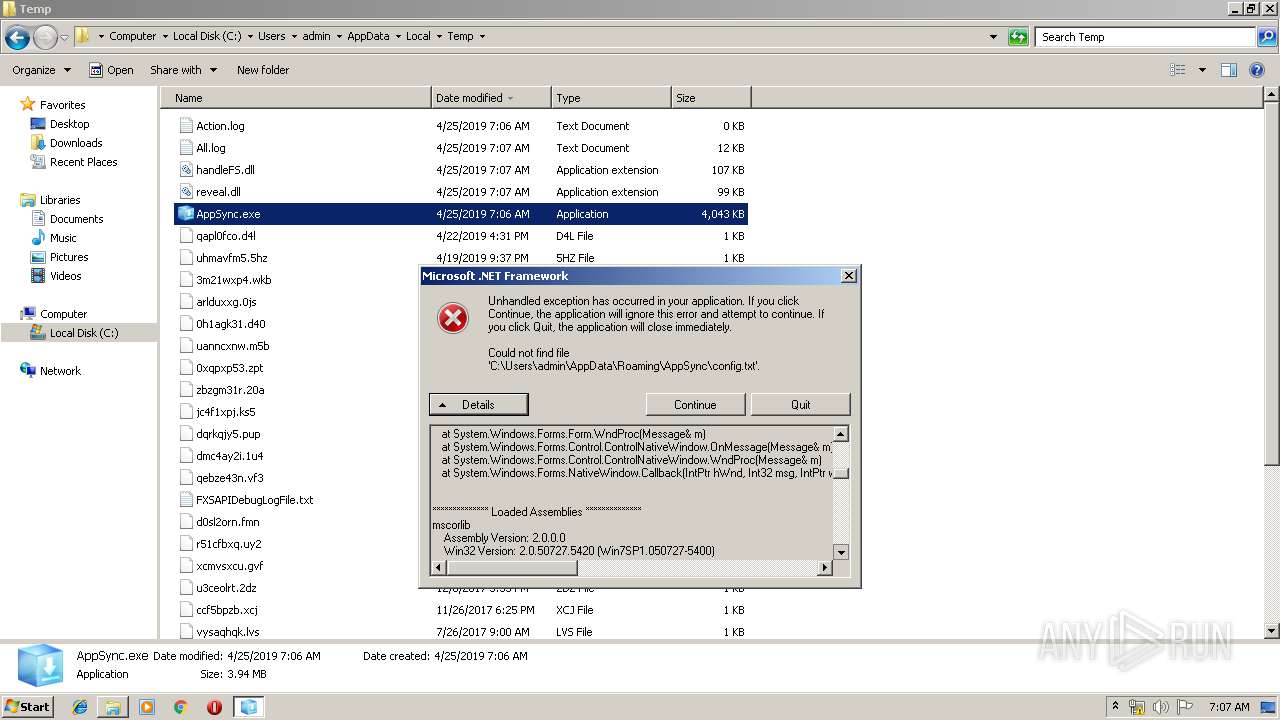
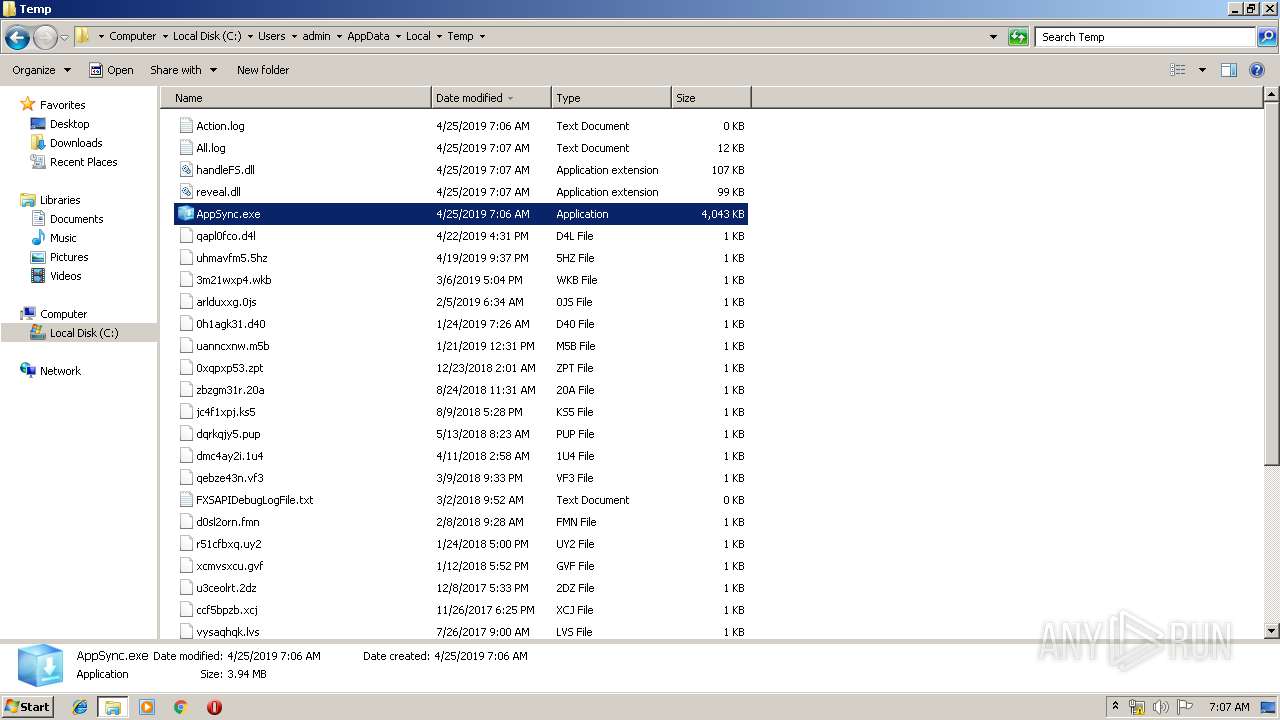
| File name: | AppSync.exe |
| Full analysis: | https://app.any.run/tasks/9f34e0fa-95f2-459e-9d32-b23558845a9f |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2019, 06:06:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 7AC9CE6A69F0448EC8BD0EBBFF3FBB09 |
| SHA1: | 7EB2161D66D1BD1BB105FB6089D4C3622493D93B |
| SHA256: | E87B23079EFF1CA296159506531EA8B02F18EFC347FC7DEA68C6ACFDD30E3BF8 |
| SSDEEP: | 49152:1MNmOHmulr6r4YN8yIZSLZXyrXRlVL9wLLNDyy67VTvdfKSD:1WmOH3lr6UYyRlx3 |
MALICIOUS
Loads dropped or rewritten executable
- explorer.exe (PID: 252)
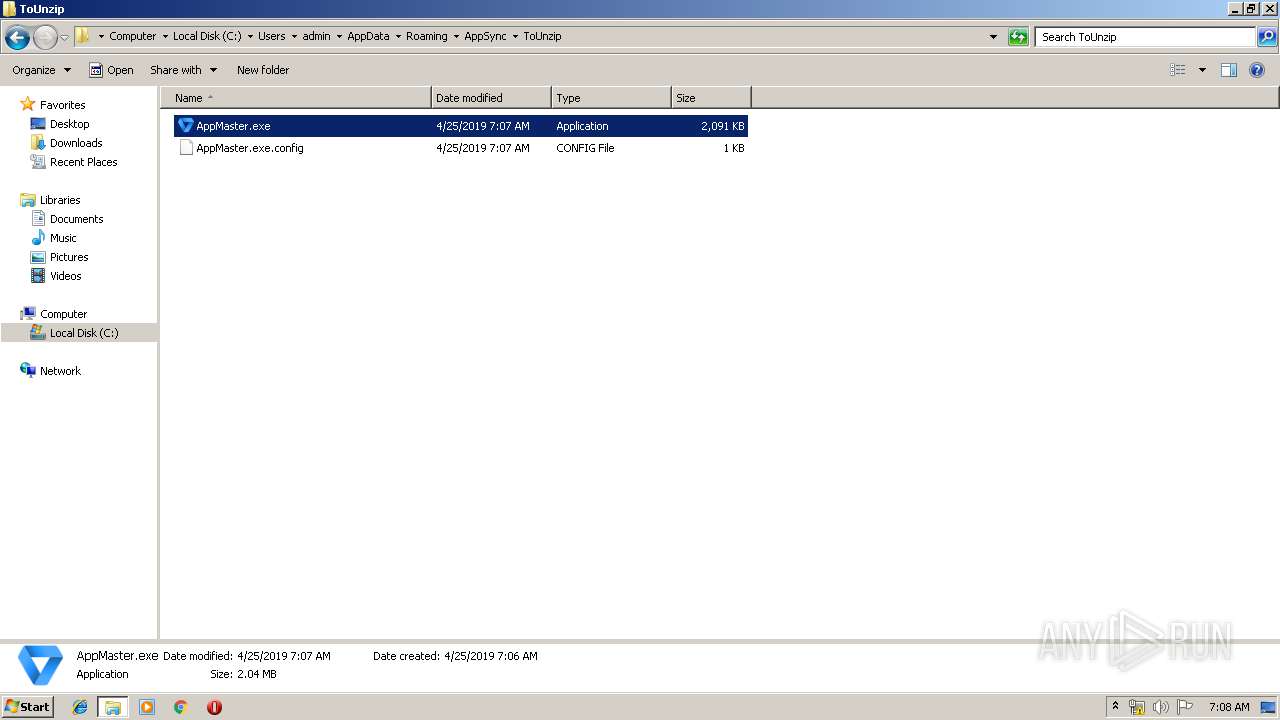
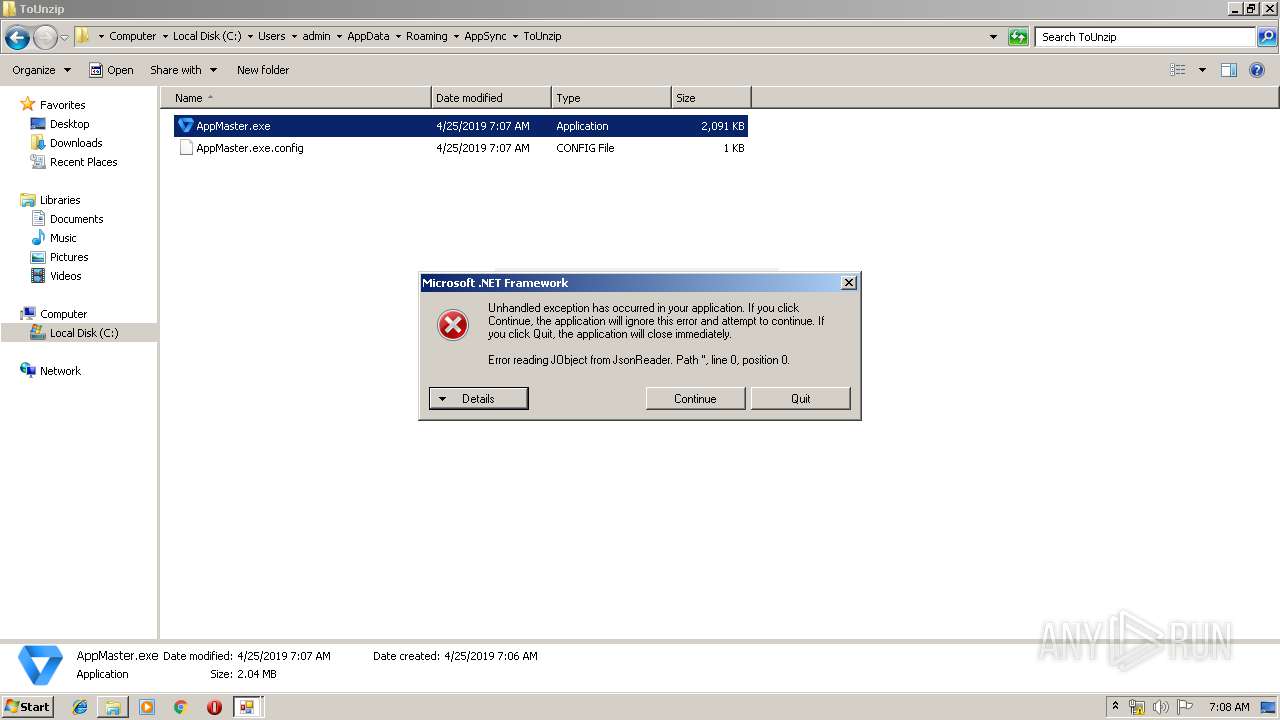
Application was dropped or rewritten from another process
- AppMaster.exe (PID: 4072)
SUSPICIOUS
Changes IE settings (feature browser emulation)
- AppSync.exe (PID: 2004)
- AppSync.exe (PID: 3092)
- AppMaster.exe (PID: 4072)
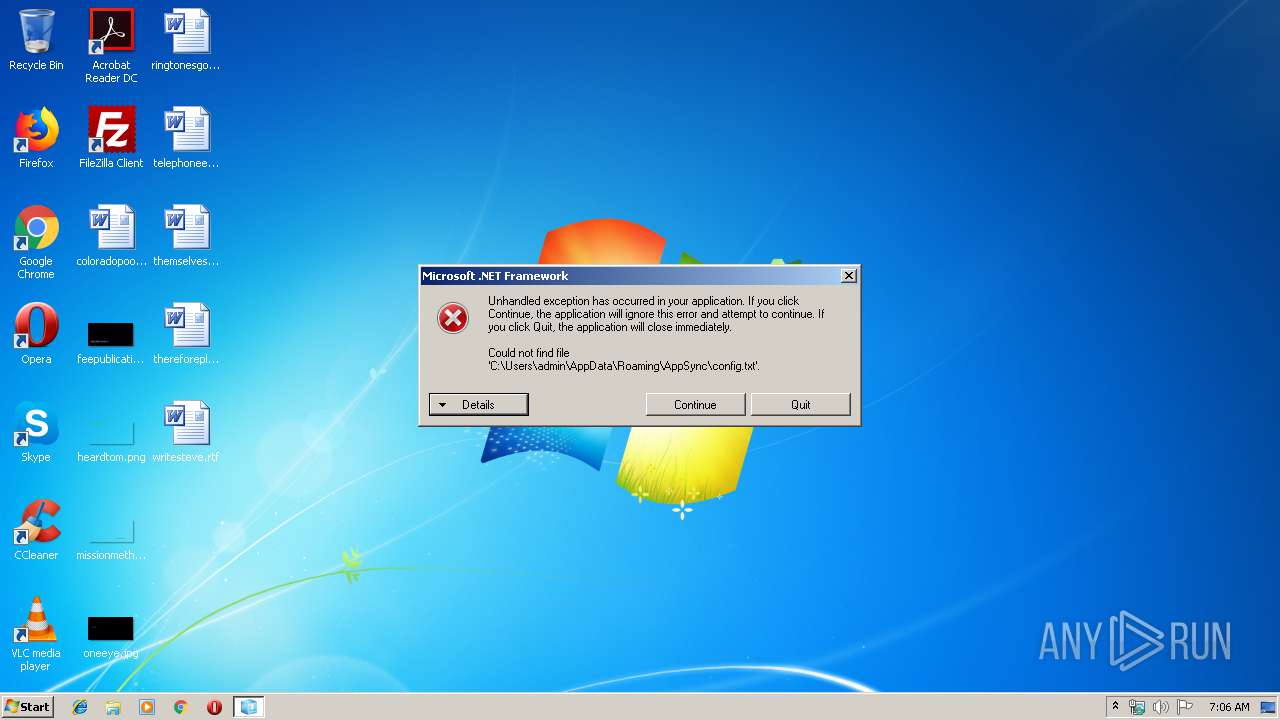
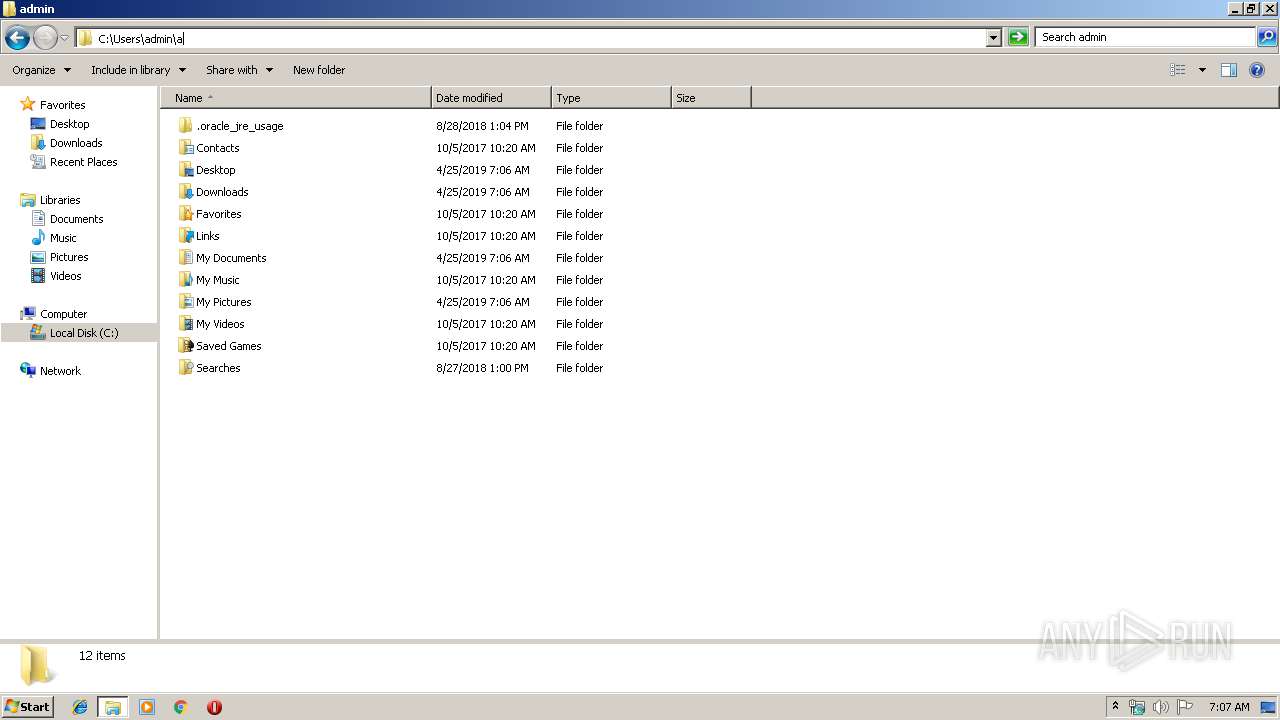
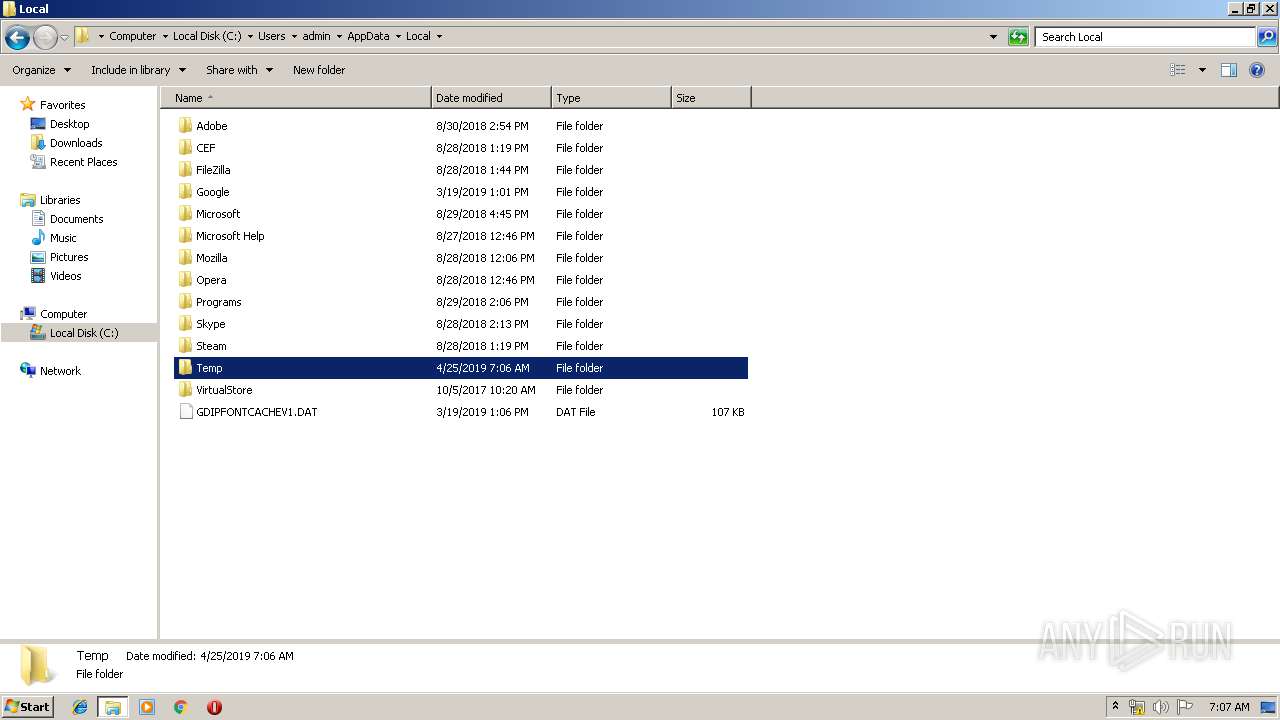
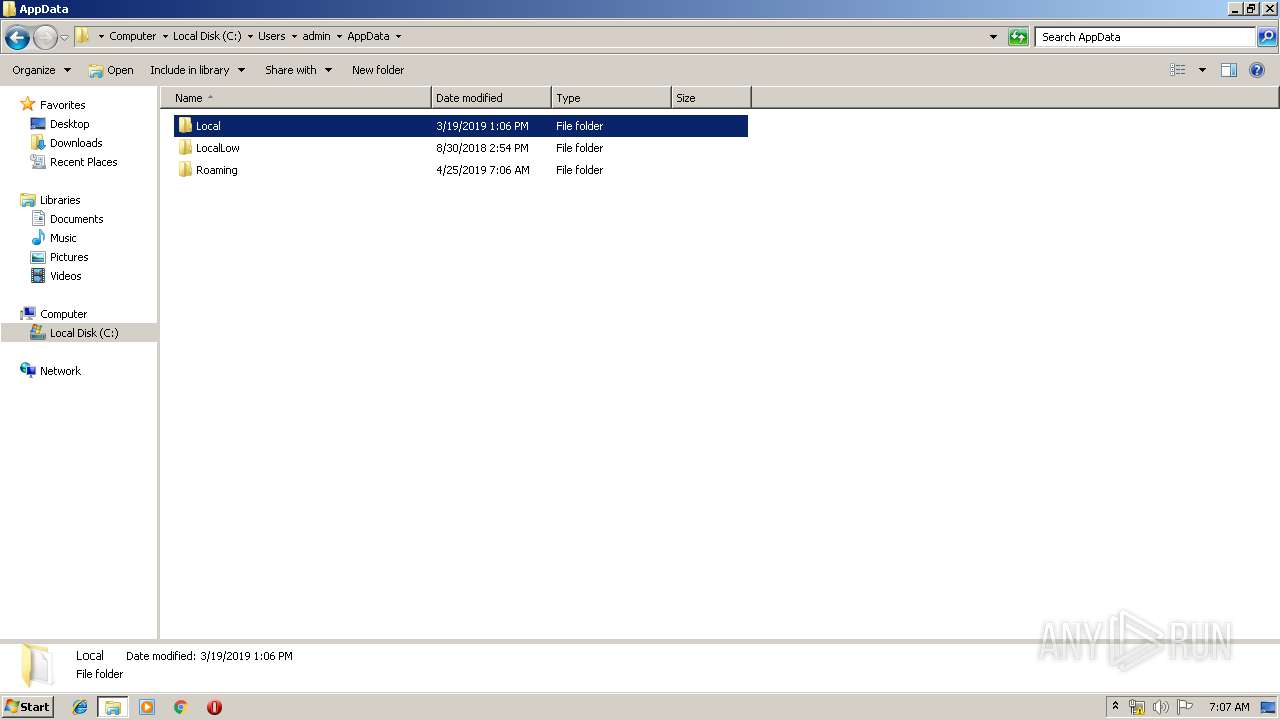
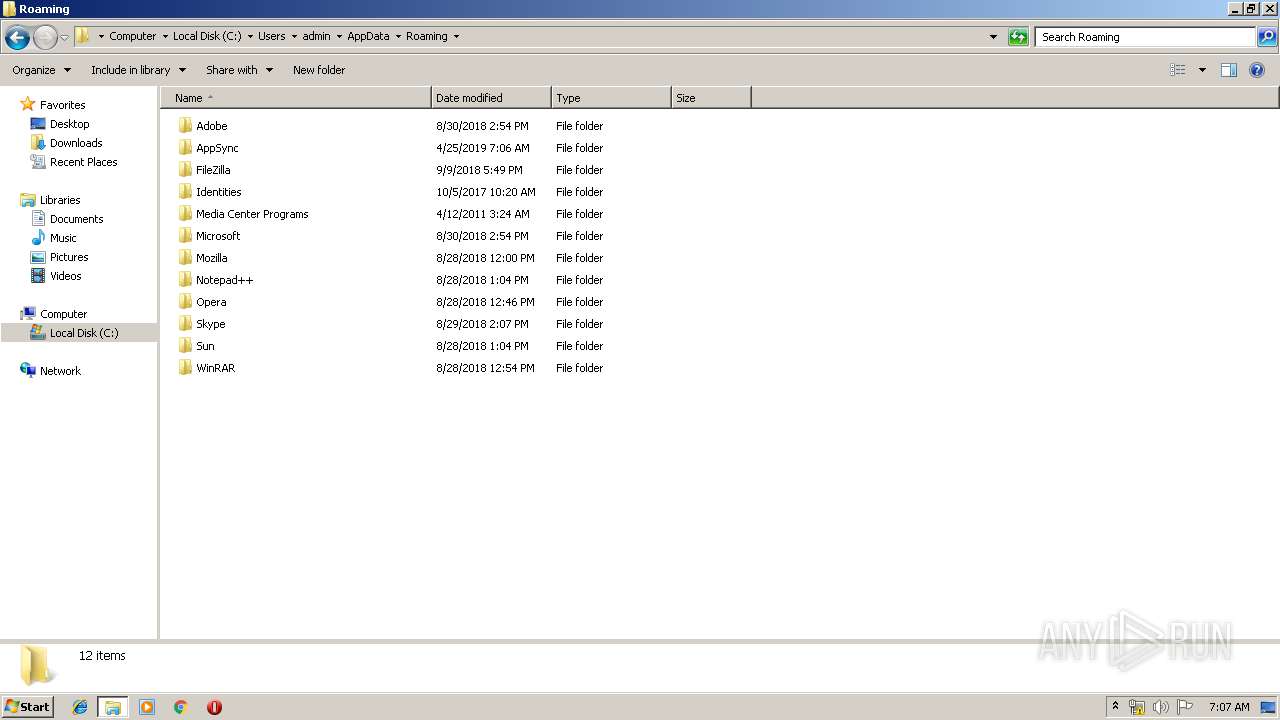
Creates files in the user directory
- AppSync.exe (PID: 3092)
Reads Internet Cache Settings
- explorer.exe (PID: 252)
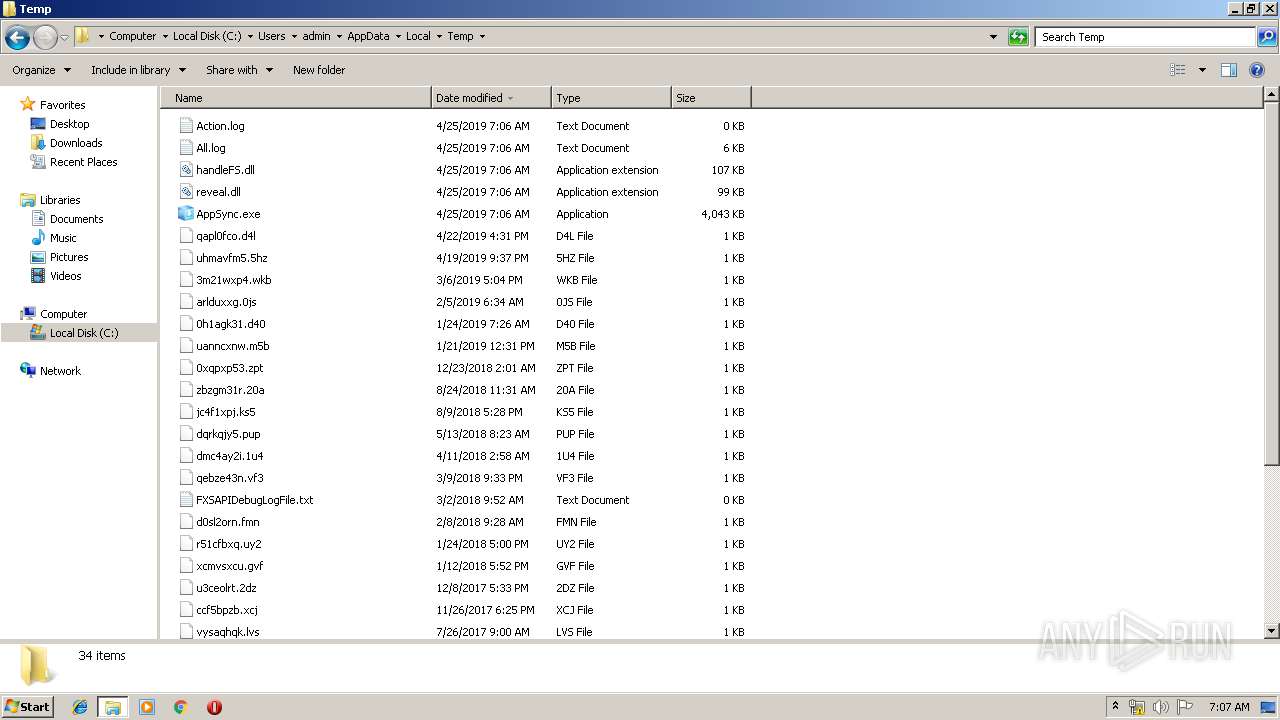
Executable content was dropped or overwritten
- AppSync.exe (PID: 3092)
- AppSync.exe (PID: 2004)
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 252)
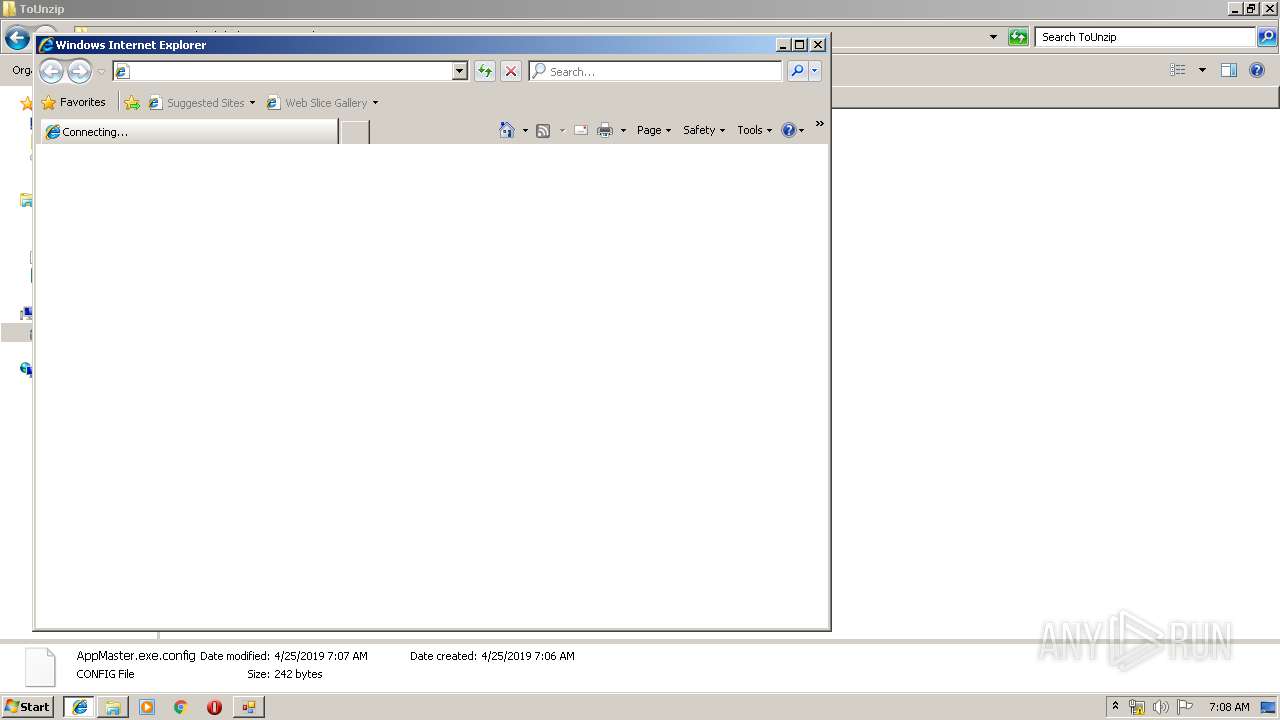
Starts Internet Explorer
- rundll32.exe (PID: 2280)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 1692)
- iexplore.exe (PID: 3964)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1692)
Changes internet zones settings
- iexplore.exe (PID: 1692)
Creates files in the user directory
- iexplore.exe (PID: 3964)
Reads internet explorer settings
- iexplore.exe (PID: 3964)
Reads settings of System Certificates
- iexplore.exe (PID: 1692)
Changes settings of System certificates
- iexplore.exe (PID: 1692)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:10:08 15:58:03+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 3758592 |
| InitializedDataSize: | 373248 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x39792e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
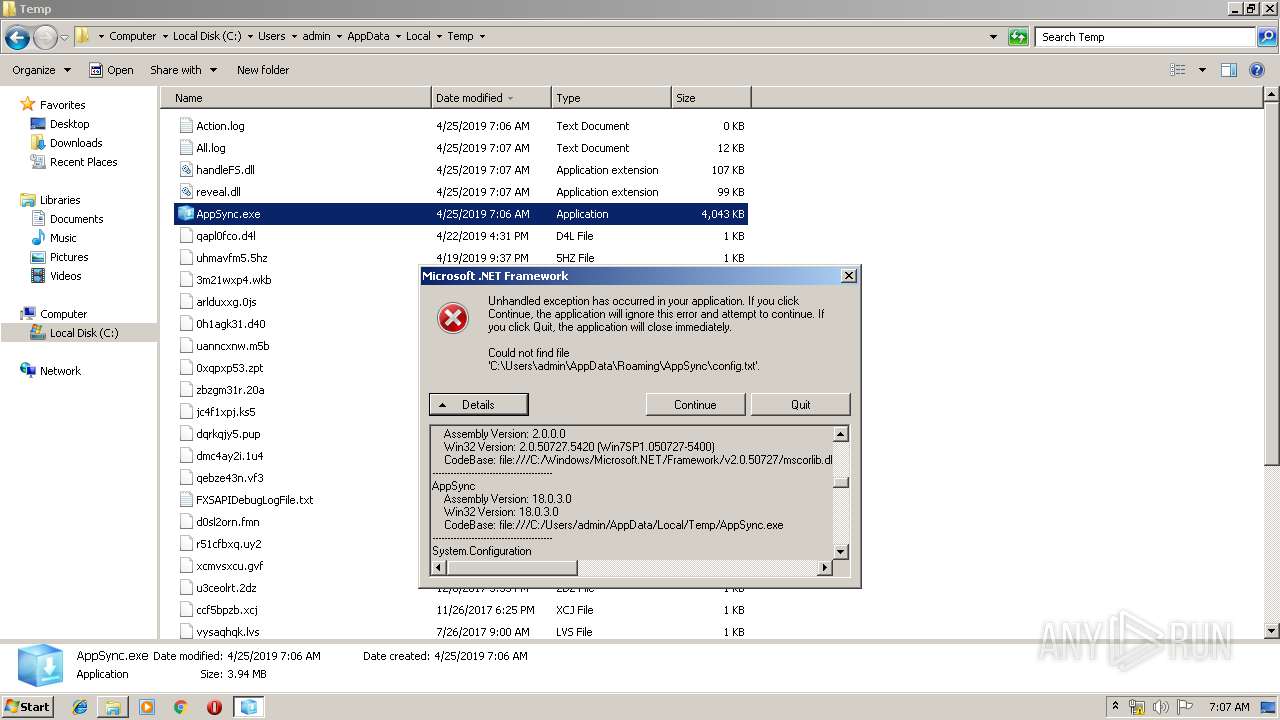
| FileVersionNumber: | 18.0.3.0 |
| ProductVersionNumber: | 18.0.3.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | AppSync |
| FileVersion: | 18.0.3.0 |
| InternalName: | AppSync.exe |
| LegalCopyright: | Copyright © 2017 |
| LegalTrademarks: | - |
| OriginalFileName: | AppSync.exe |
| ProductName: | AppSync |
| ProductVersion: | 18.0.3.0 |
| AssemblyVersion: | 18.0.3.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-Oct-2018 13:58:03 |
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 08-Oct-2018 13:58:03 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x003959E9 | 0x00395A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.92174 |
.rsrc | 0x00398000 | 0x0005AE38 | 0x0005B000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.47052 |
.reloc | 0x003F4000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0980042 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25872 | 888 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 6.58775 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 6.72077 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 6.7467 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 6.84873 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 6.72054 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.76511 | 90 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
44
Monitored processes
8
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1692 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2004 | "C:\Users\admin\AppData\Local\Temp\AppSync.exe" | C:\Users\admin\AppData\Local\Temp\AppSync.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: AppSync Exit code: 0 Version: 18.0.3.0 Modules
| |||||||||||||||
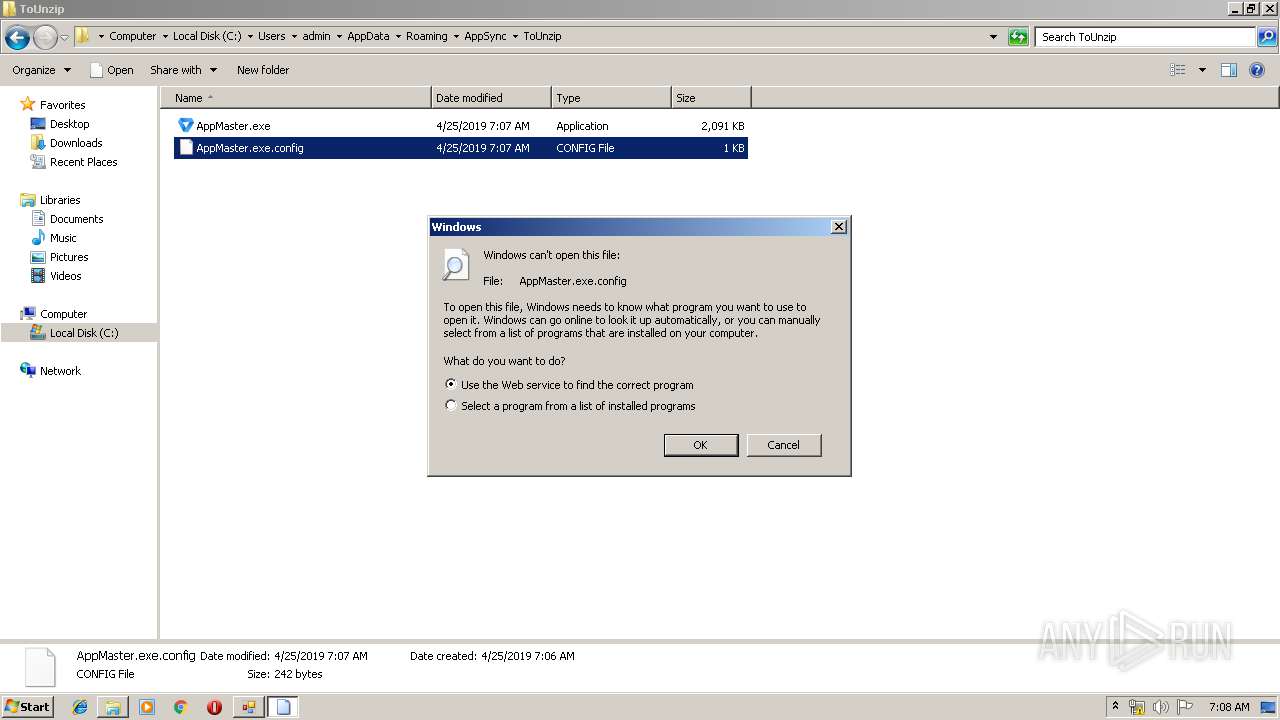
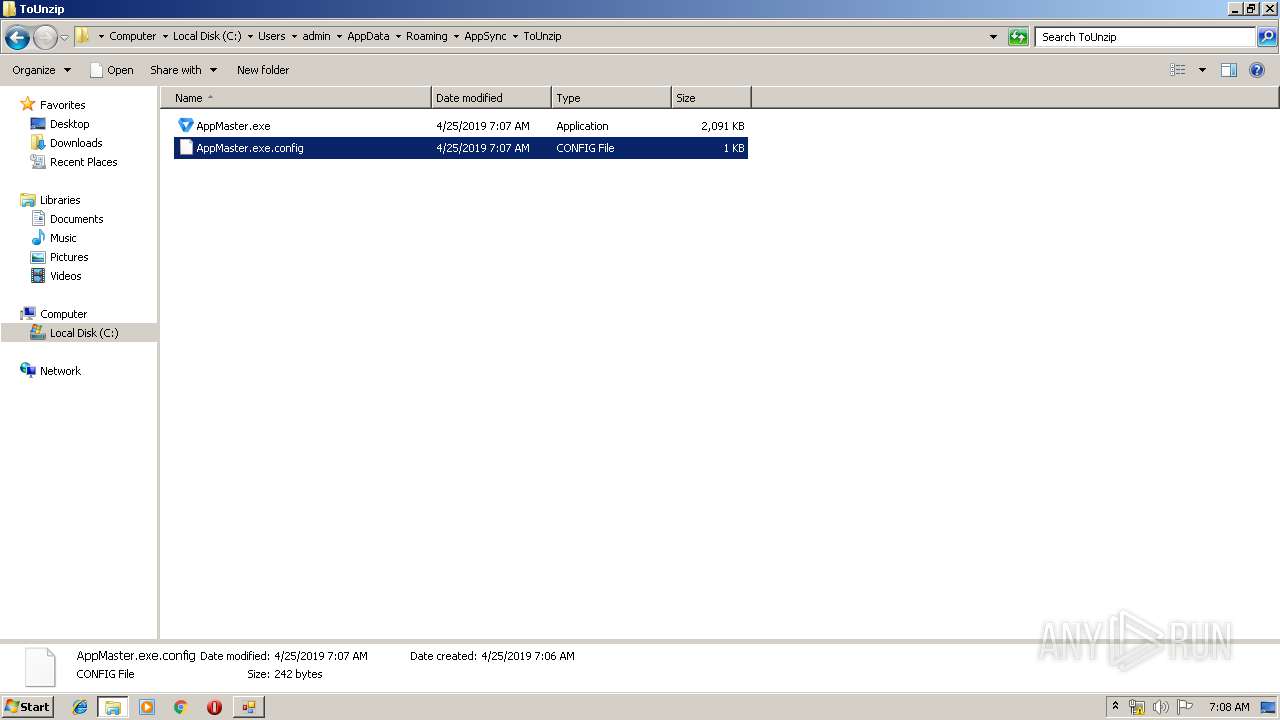
| 2280 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Roaming\AppSync\ToUnzip\AppMaster.exe.config | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3092 | "C:\Users\admin\AppData\Local\Temp\AppSync.exe" | C:\Users\admin\AppData\Local\Temp\AppSync.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: AppSync Exit code: 0 Version: 18.0.3.0 Modules
| |||||||||||||||
| 3340 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3964 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1692 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4072 | "C:\Users\admin\AppData\Roaming\AppSync\ToUnzip\AppMaster.exe" | C:\Users\admin\AppData\Roaming\AppSync\ToUnzip\AppMaster.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: AppMaster Exit code: 0 Version: 11.0.0.0 Modules
| |||||||||||||||
Total events
2 242
Read events
1 651
Write events
586
Delete events
5
Modification events
| (PID) Process: | (3092) AppSync.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3092) AppSync.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_BROWSER_EMULATION |
| Operation: | write | Name: | AppSync.exe |
Value: 8000 | |||
| (PID) Process: | (3092) AppSync.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_ENABLE_CLIPCHILDREN_OPTIMIZATION |
| Operation: | write | Name: | AppSync.exe |
Value: 1 | |||
| (PID) Process: | (3092) AppSync.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_AJAX_CONNECTIONEVENTS |
| Operation: | write | Name: | AppSync.exe |
Value: 1 | |||
| (PID) Process: | (3092) AppSync.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_GPU_RENDERING |
| Operation: | write | Name: | AppSync.exe |
Value: 1 | |||
| (PID) Process: | (3092) AppSync.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_WEBOC_DOCUMENT_ZOOM |
| Operation: | write | Name: | AppSync.exe |
Value: 1 | |||
| (PID) Process: | (3092) AppSync.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_NINPUT_LEGACYMODE |
| Operation: | write | Name: | AppSync.exe |
Value: 0 | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\NccQngn\Ybpny\Grzc\NccFlap.rkr |
Value: 000000000000000000000000421C0000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 0000000004000000020000008D8A00000200000002000000724300004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000120200000000CC0B120200000000CC0B12020400050005001F02280C12020800050005001F026CE71F020100000154001F0200000100B8139D75444812020C0003000300000000000500280C12020000000005000000CC0B120201000000C8E91F02C0E91F0200000000C8FDDE02C0FCDE0244E71F023DA9457600000000FBFFFF7F68E71F02987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF00000000000000000000000035EE190651EE190635EE1906000000000000000000000000080000002E006C006E006B0000005300630068006500640075006C00650072002E006C006E006B00000014000000140050000000070000000200060026030200A5863C750800000064021400E72F1B77B5863C753F030000CC04140000001400A86D150011000000B8451700B045170005000000F8F3DD0270E80000F28635BB20E81F028291457670E81F0224E81F022795457600000000ECD2DD024CE81F02CD944576ECD2DD02F8E81F0260CEDD02E19445760000000060CEDD02F8E81F0254E81F020200000002000000724300004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000120200000000CC0B120200000000CC0B12020400050005001F02280C12020800050005001F026CE71F020100000154001F0200000100B8139D75444812020C0003000300000000000500280C12020000000005000000CC0B120201000000C8E91F02C0E91F0200000000C8FDDE02C0FCDE0244E71F023DA9457600000000FBFFFF7F68E71F02987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF00000000000000000000000035EE190651EE190635EE1906000000000000000000000000080000002E006C006E006B0000005300630068006500640075006C00650072002E006C006E006B00000014000000140050000000070000000200060026030200A5863C750800000064021400E72F1B77B5863C753F030000CC04140000001400A86D150011000000B8451700B045170005000000F8F3DD0270E80000F28635BB20E81F028291457670E81F0224E81F022795457600000000ECD2DD024CE81F02CD944576ECD2DD02F8E81F0260CEDD02E19445760000000060CEDD02F8E81F0254E81F020200000002000000724300004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000120200000000CC0B120200000000CC0B12020400050005001F02280C12020800050005001F026CE71F020100000154001F0200000100B8139D75444812020C0003000300000000000500280C12020000000005000000CC0B120201000000C8E91F02C0E91F0200000000C8FDDE02C0FCDE0244E71F023DA9457600000000FBFFFF7F68E71F02987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF00000000000000000000000035EE190651EE190635EE1906000000000000000000000000080000002E006C006E006B0000005300630068006500640075006C00650072002E006C006E006B00000014000000140050000000070000000200060026030200A5863C750800000064021400E72F1B77B5863C753F030000CC04140000001400A86D150011000000B8451700B045170005000000F8F3DD0270E80000F28635BB20E81F028291457670E81F0224E81F022795457600000000ECD2DD024CE81F02CD944576ECD2DD02F8E81F0260CEDD02E19445760000000060CEDD02F8E81F0254E81F02 | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {S38OS404-1Q43-42S2-9305-67QR0O28SP23}\rkcybere.rkr |
Value: 00000000010000000000000000000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF60C8C21A2DFBD40100000000 | |||
Executable files
16
Suspicious files
3
Text files
83
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
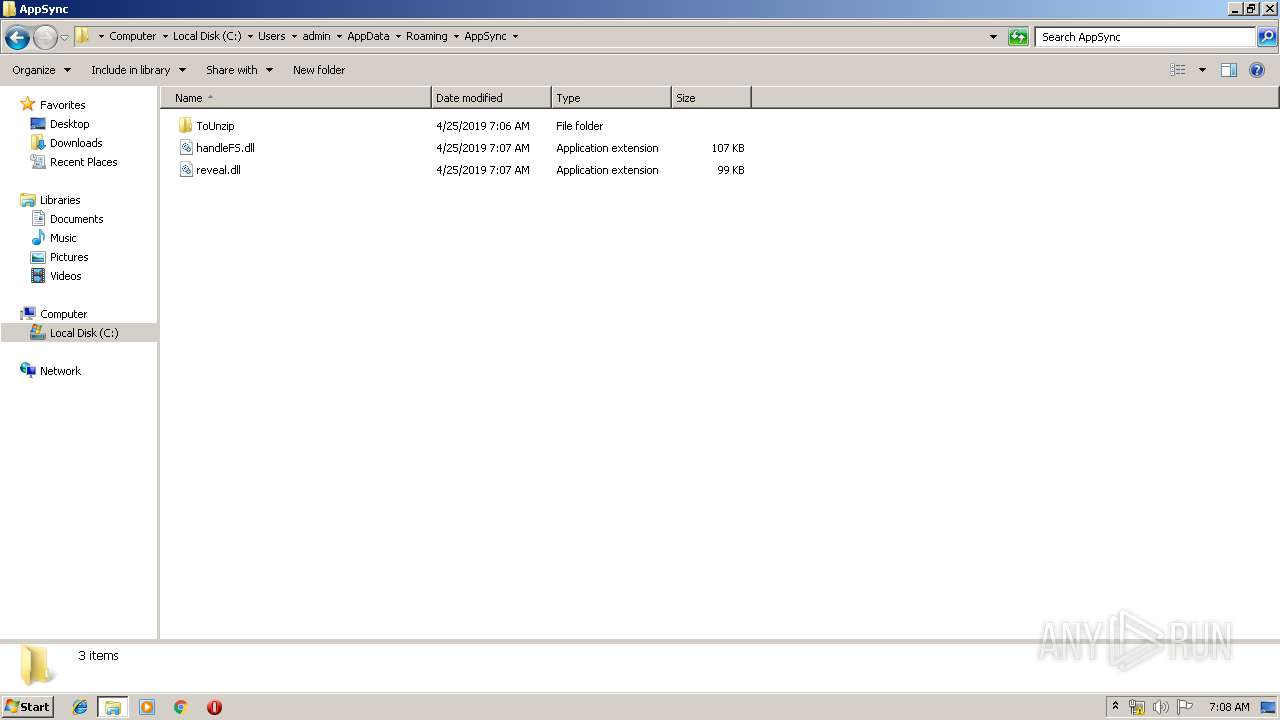
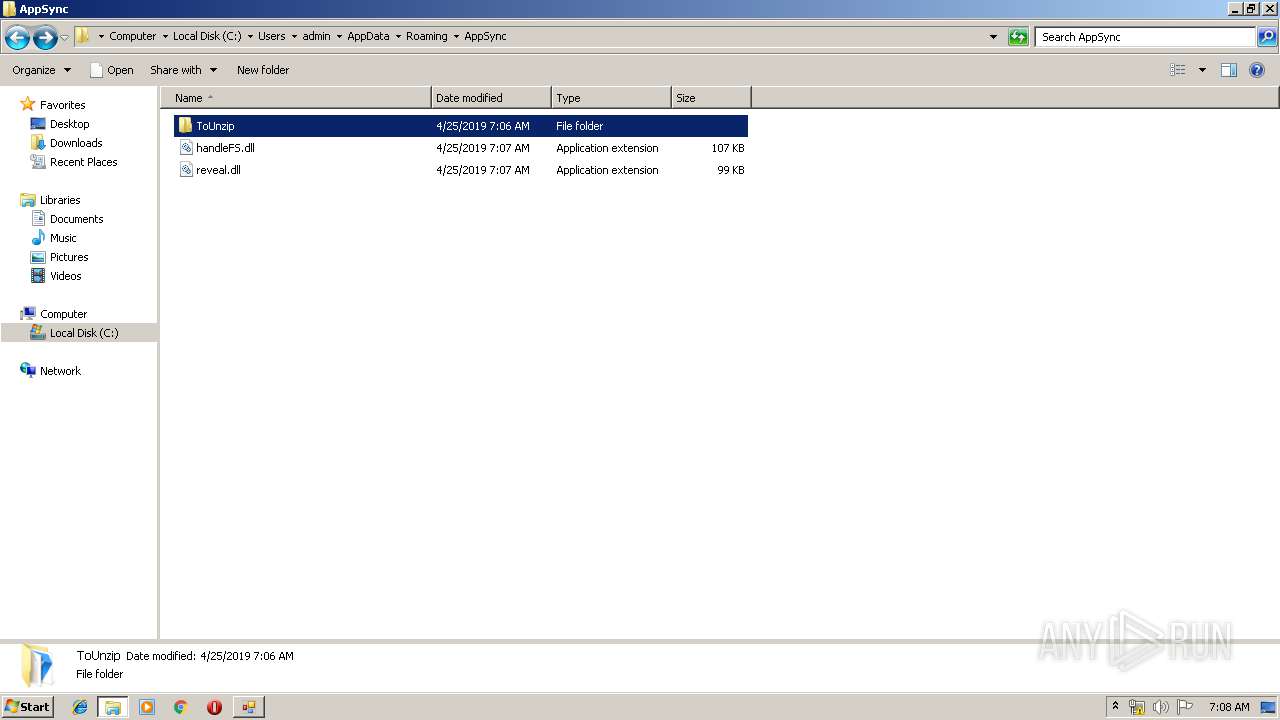
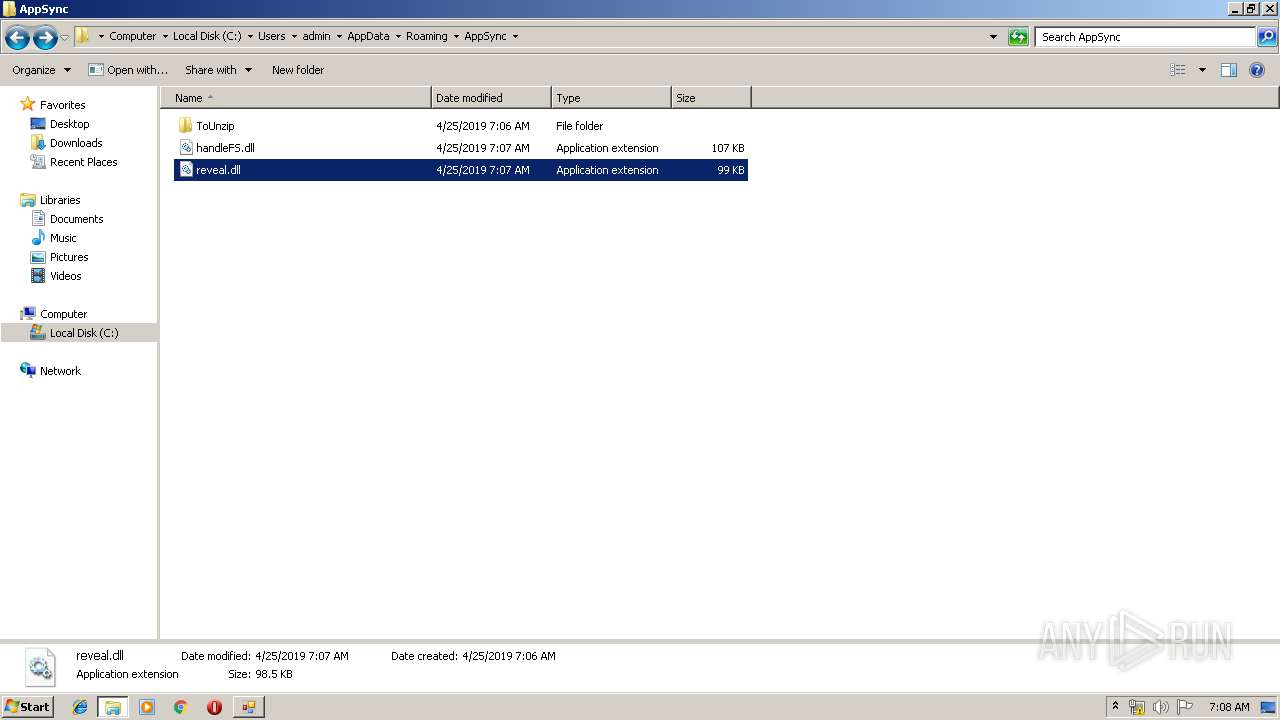
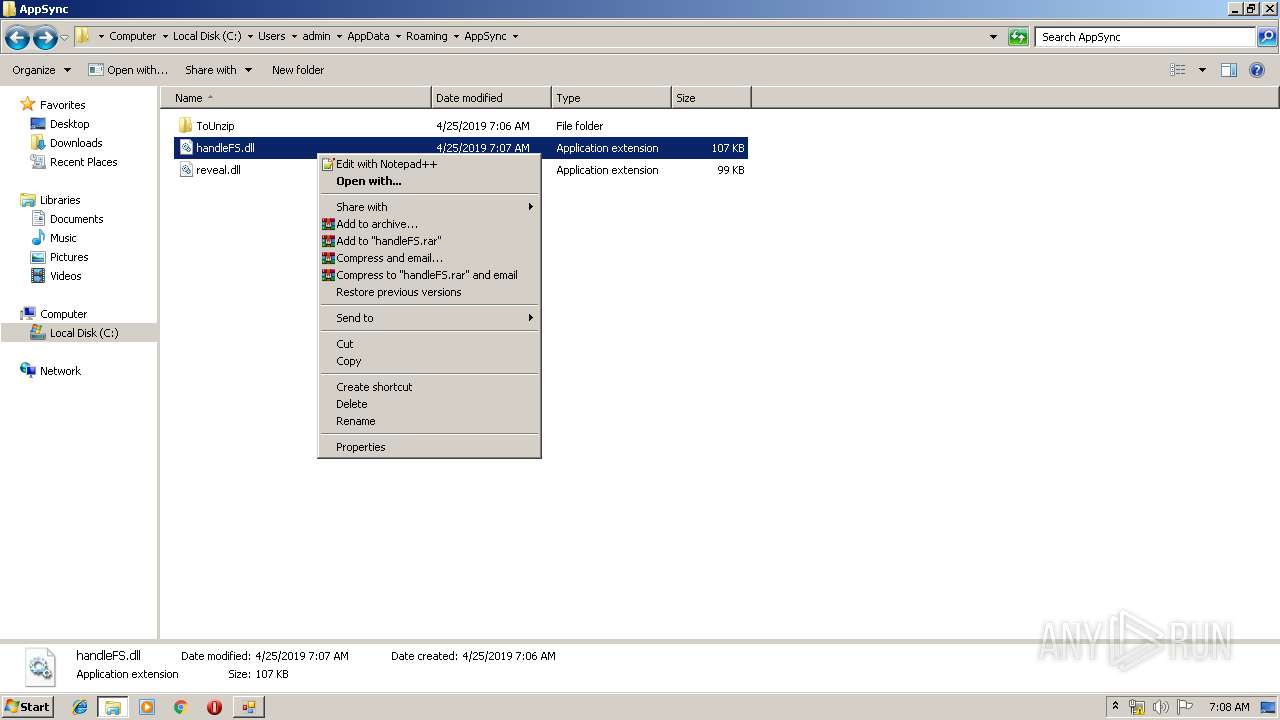
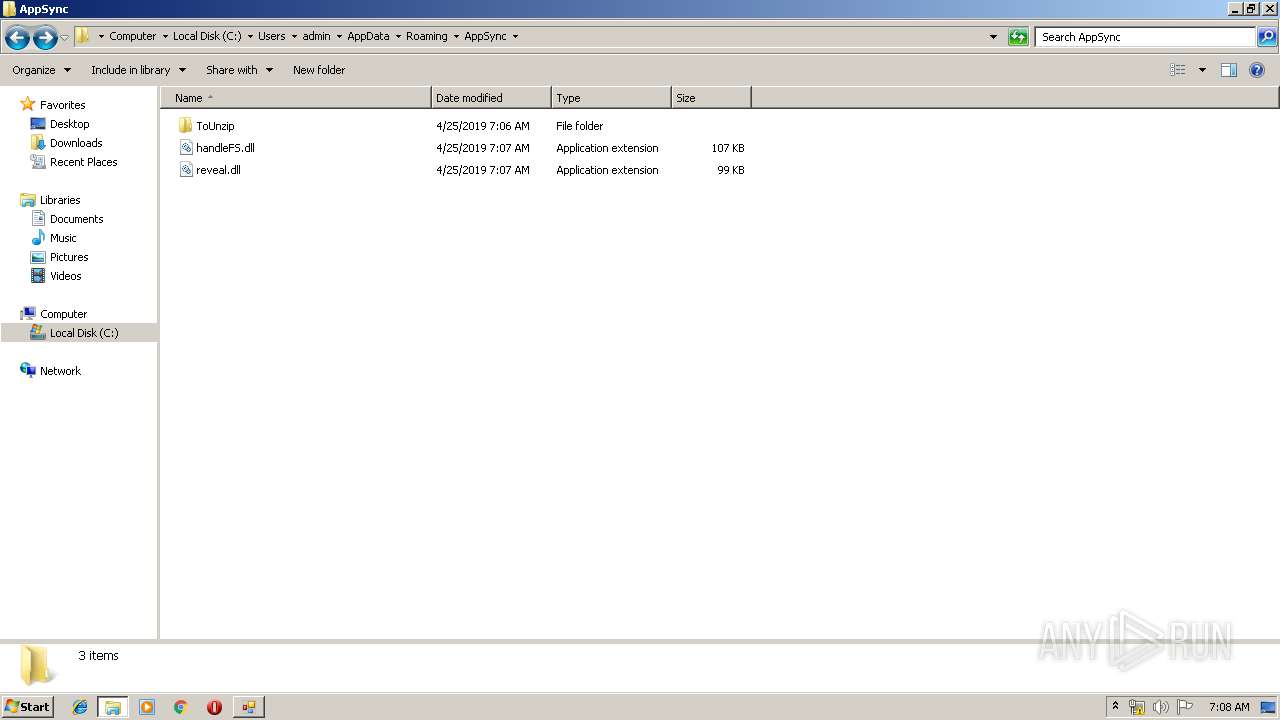
| 3092 | AppSync.exe | C:\Users\admin\AppData\Roaming\AppSync\reveal.dll | executable | |
MD5:— | SHA256:— | |||
| 3092 | AppSync.exe | C:\Users\admin\AppData\Local\Temp\reveal.dll | executable | |
MD5:— | SHA256:— | |||
| 3092 | AppSync.exe | C:\Users\admin\AppData\Roaming\AppSync\ToUnzip\AppMaster.exe.config | xml | |
MD5:— | SHA256:— | |||
| 1692 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2004 | AppSync.exe | C:\Users\admin\AppData\Roaming\AppSync\ToUnzip\AppMaster.exe | executable | |
MD5:— | SHA256:— | |||
| 1692 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3092 | AppSync.exe | C:\Users\admin\AppData\Roaming\AppSync\handleFS.dll | executable | |
MD5:— | SHA256:— | |||
| 3092 | AppSync.exe | C:\Users\admin\AppData\Local\Temp\handleFS.dll | executable | |
MD5:— | SHA256:— | |||
| 3092 | AppSync.exe | C:\Users\admin\AppData\Roaming\AppSync\ToUnzip\AppMaster.exe | executable | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@bing[2].txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
10
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
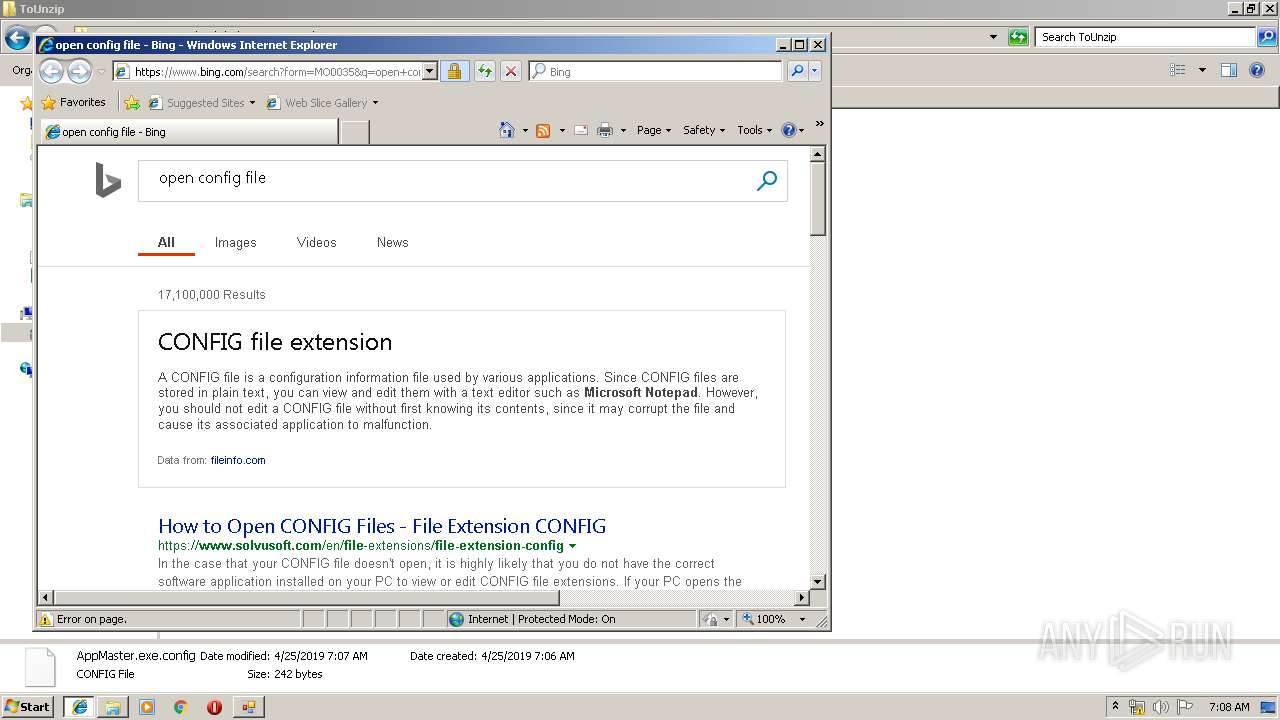
3964 | iexplore.exe | GET | 301 | 2.16.186.24:80 | http://shell.windows.com/fileassoc/fileassoc.asp?Ext=config | unknown | — | — | whitelisted |
3964 | iexplore.exe | GET | 302 | 23.38.36.63:80 | http://go.microsoft.com/fwlink/?LinkId=57426&Ext=config | NL | — | — | whitelisted |
1692 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3964 | iexplore.exe | 23.38.36.63:80 | go.microsoft.com | Akamai Technologies, Inc. | NL | whitelisted |
1692 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3964 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1692 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3964 | iexplore.exe | 2.16.186.24:80 | shell.windows.com | Akamai International B.V. | — | whitelisted |
3964 | iexplore.exe | 157.55.135.130:443 | login.live.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
shell.windows.com |
| whitelisted |
login.live.com |
| whitelisted |