| File name: | eaa4a480208609b36ab83a9b65802143 |
| Full analysis: | https://app.any.run/tasks/7c88482b-6b94-409d-80ea-ca35a5148cbd |
| Verdict: | Malicious activity |
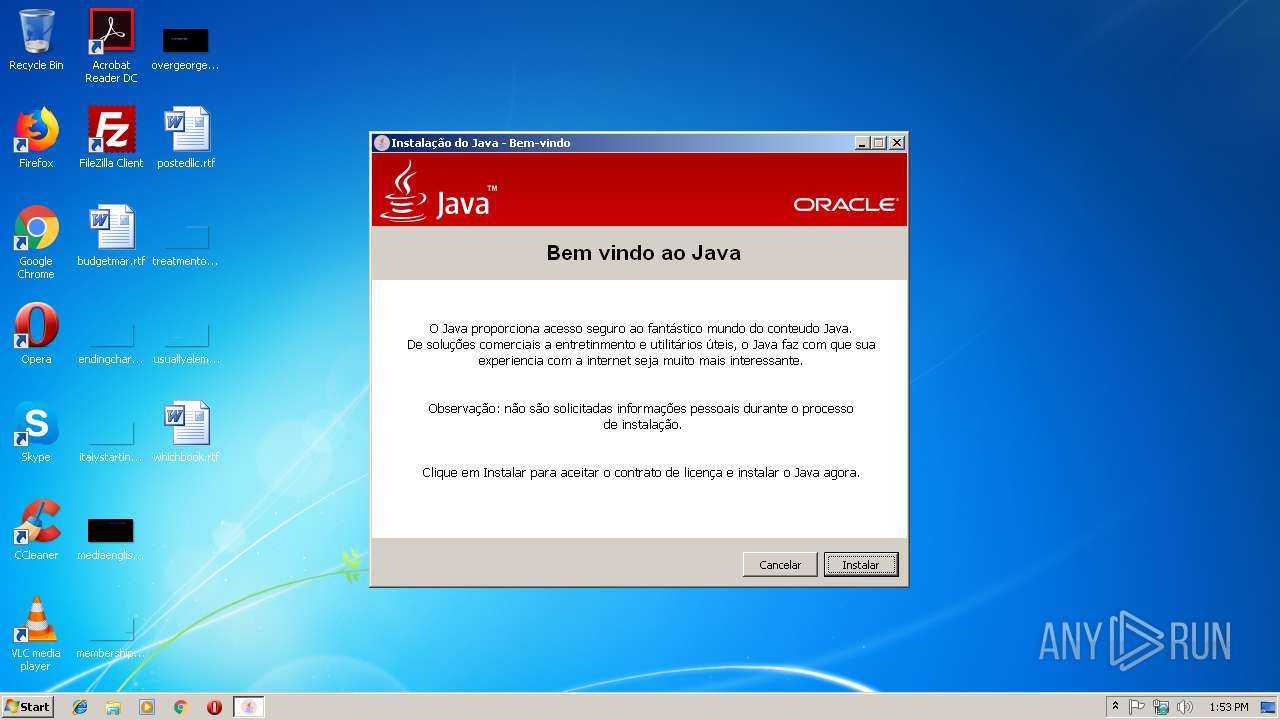
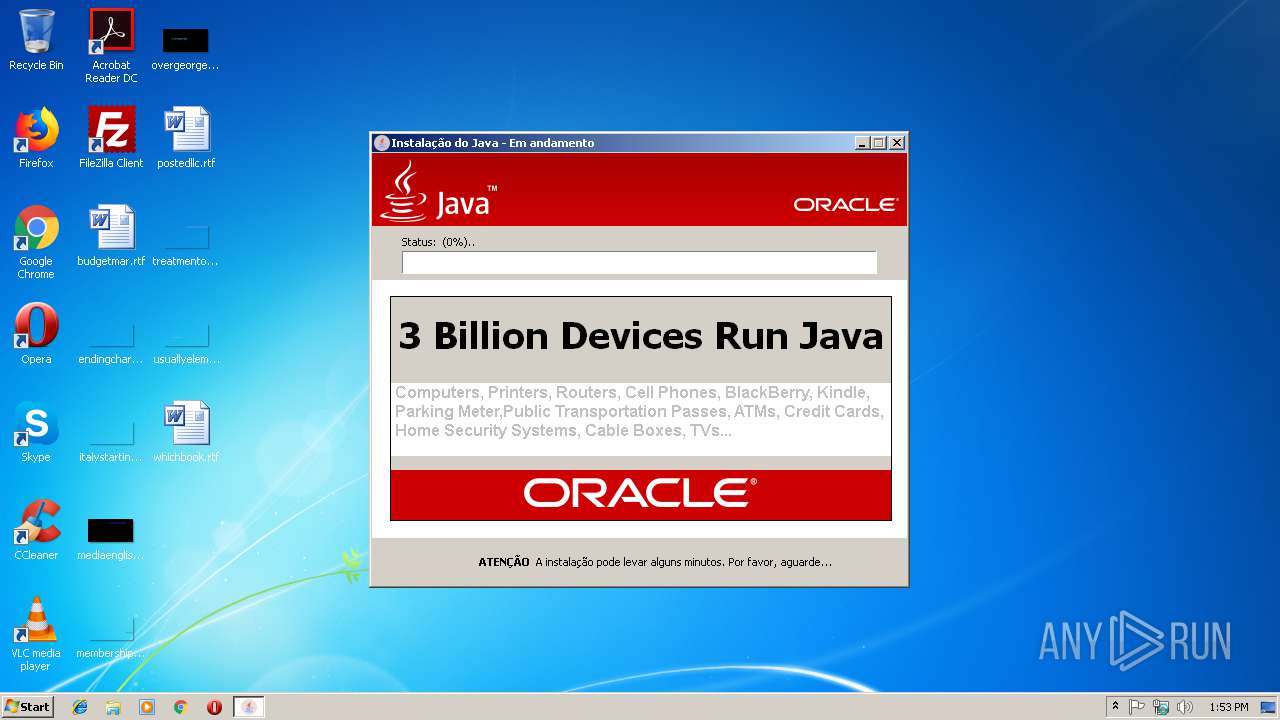
| Analysis date: | January 22, 2019, 13:53:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | EAA4A480208609B36AB83A9B65802143 |
| SHA1: | E62FC3C3957CC741798395BF1F04910ACFC7DC14 |
| SHA256: | E871ACC43E8BEF95B68C9BEFB3ADA8279D91068981AB1554051F8EC15740DFF8 |
| SSDEEP: | 49152:tGFWM51r5nPPoATGFaStAh7kDy+mXQYYTxC+5p:tGFXVR+Dy+mAiCp |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (79.7) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (8.6) |
| .exe | | | Win16/32 Executable Delphi generic (3.9) |
| .exe | | | Generic Win/DOS Executable (3.8) |
| .exe | | | DOS Executable Generic (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:01:15 15:01:35+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 2342400 |
| InitializedDataSize: | 415232 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x23d5c4 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| FileVersion: | 1.0.0.0 |
| ProductVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Jan-2019 14:01:35 |
| Detected languages: |
|
| FileVersion: | 1.0.0.0 |
| ProductVersion: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 11 |
| Time date stamp: | 15-Jan-2019 14:01:35 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0023A404 | 0x0023A600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.47552 |
.itext | 0x0023C000 | 0x00001618 | 0x00001800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.01256 |
.data | 0x0023E000 | 0x00008D0C | 0x00008E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.18175 |
.bss | 0x00247000 | 0x00005CA8 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0024D000 | 0x00004F04 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.33711 |
.didata | 0x00252000 | 0x000009A6 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.11145 |
.edata | 0x00253000 | 0x00000061 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.13506 |
.tls | 0x00254000 | 0x00000040 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00255000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.201539 |
.reloc | 0x00256000 | 0x00030F90 | 0x00031000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.72647 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.86531 | 714 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.47309 | 67624 | UNKNOWN | English - United States | RT_ICON |
3 | 4.49335 | 16936 | UNKNOWN | English - United States | RT_ICON |
4 | 4.8398 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 4.85263 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 4.99343 | 1128 | UNKNOWN | English - United States | RT_ICON |
7 | 2.91604 | 308 | UNKNOWN | English - United States | RT_CURSOR |
4073 | 3.2825 | 1856 | UNKNOWN | UNKNOWN | RT_STRING |
4074 | 3.26823 | 2840 | UNKNOWN | UNKNOWN | RT_STRING |
4075 | 3.21033 | 904 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
gdi32.dll |
gdiplus.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
msvcrt.dll |
ole32.dll |
oleaut32.dll |
olepro32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
TMethodImplementationIntercept | 1 | 0x0005E420 |
Total processes
30
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3148 | "C:\Users\admin\AppData\Local\Temp\eaa4a480208609b36ab83a9b65802143.exe" | C:\Users\admin\AppData\Local\Temp\eaa4a480208609b36ab83a9b65802143.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
38
Read events
20
Write events
18
Delete events
0
Modification events
| (PID) Process: | (3148) eaa4a480208609b36ab83a9b65802143.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\eaa4a480208609b36ab83a9b65802143_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3148) eaa4a480208609b36ab83a9b65802143.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\eaa4a480208609b36ab83a9b65802143_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3148) eaa4a480208609b36ab83a9b65802143.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\eaa4a480208609b36ab83a9b65802143_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3148) eaa4a480208609b36ab83a9b65802143.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\eaa4a480208609b36ab83a9b65802143_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3148) eaa4a480208609b36ab83a9b65802143.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\eaa4a480208609b36ab83a9b65802143_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3148) eaa4a480208609b36ab83a9b65802143.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\eaa4a480208609b36ab83a9b65802143_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3148) eaa4a480208609b36ab83a9b65802143.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\eaa4a480208609b36ab83a9b65802143_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3148) eaa4a480208609b36ab83a9b65802143.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\eaa4a480208609b36ab83a9b65802143_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3148) eaa4a480208609b36ab83a9b65802143.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\eaa4a480208609b36ab83a9b65802143_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3148) eaa4a480208609b36ab83a9b65802143.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\eaa4a480208609b36ab83a9b65802143_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3148 | eaa4a480208609b36ab83a9b65802143.exe | GET | 502 | 189.1.158.193:8080 | http://valent.hopto.org:8080/valent/count/step/1/?os=Win7_32 | BR | html | 182 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3148 | eaa4a480208609b36ab83a9b65802143.exe | 189.1.158.193:8080 | valent.hopto.org | SILVA & SILVEIRA S/C LTDA - ME | BR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
valent.hopto.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3148 | eaa4a480208609b36ab83a9b65802143.exe | Potentially Bad Traffic | ET INFO HTTP Connection To DDNS Domain Hopto.org |