| File name: | 47798_1918094.xlsm |
| Full analysis: | https://app.any.run/tasks/16abe5ab-200d-44bf-ac4d-f3c729c85008 |
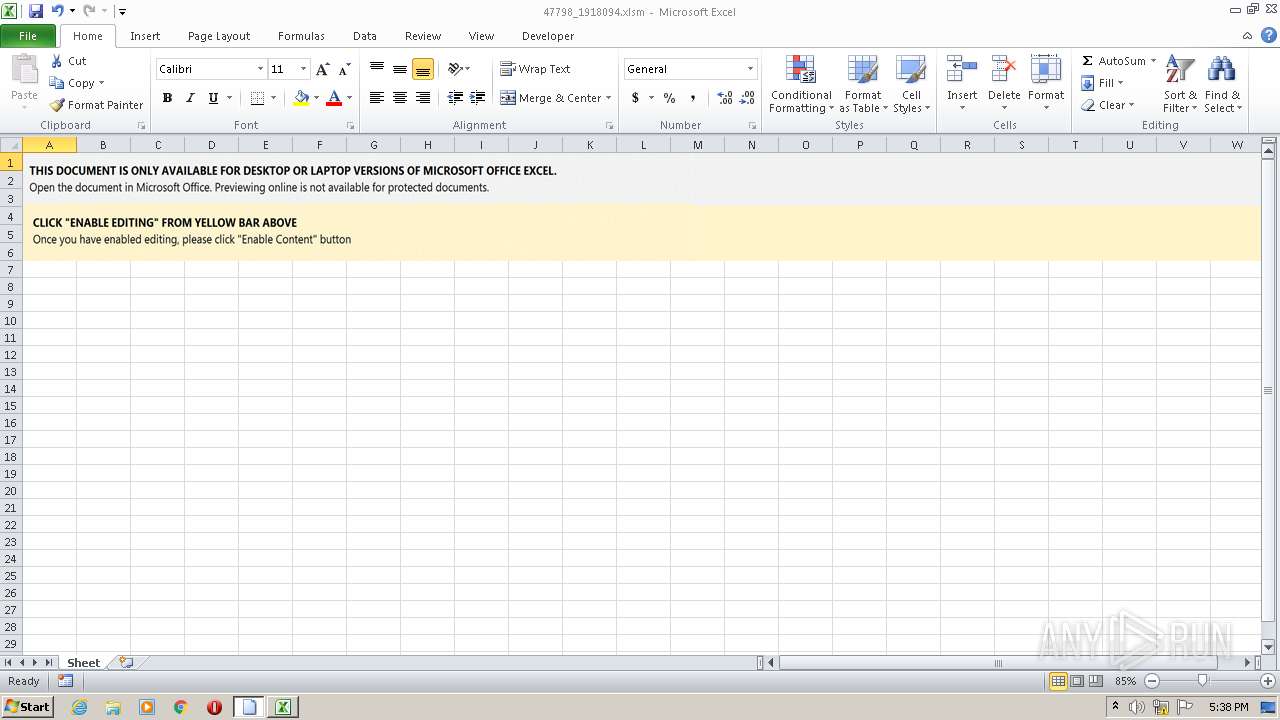
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 24, 2022, 17:38:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.spreadsheetml.sheet |
| File info: | Microsoft Excel 2007+ |
| MD5: | FF69AB8D7C4DE71325B9A6B5D4ACCF07 |
| SHA1: | 5E4BA073E2307D84F63AAB0A0A4808940F94EA31 |
| SHA256: | E869F1F1C15FC3635F603C1F201E91C4D4FC67E27D48FA526512922A2DFA61AC |
| SSDEEP: | 1536:/fRL8sqxG/+CbEcWeu3XDXeoiHwt/uE1d7mT6SrPag3HtQVASgVou:H1wG/+CbE9H78wt2E1d7e6STa6Sa |
MALICIOUS
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 3980)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- EXCEL.EXE (PID: 3980)
INFO
Checks supported languages
- EXCEL.EXE (PID: 3980)
- rundll32.exe (PID: 3732)
Reads the computer name
- EXCEL.EXE (PID: 3980)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 3980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xlsx | | | Excel Microsoft Office Open XML Format document (61.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (31.5) |
| .zip | | | ZIP compressed archive (7.2) |
EXIF
XML
| AppVersion: | 16.03 |
|---|---|
| HyperlinksChanged: | No |
| SharedDoc: | No |
| LinksUpToDate: | No |
| Company: | - |
| TitlesOfParts: |
|
| HeadingPairs: |
|
| ScaleCrop: | No |
| DocSecurity: | None |
| Application: | Microsoft Excel |
| ModifyDate: | 2022:01:14 16:14:12Z |
| CreateDate: | 2015:06:05 18:19:34Z |
| LastModifiedBy: | Admin |
XMP
| Creator: | Admin |
|---|
ZIP
| ZipFileName: | [Content_Types].xml |
|---|---|
| ZipUncompressedSize: | 1943 |
| ZipCompressedSize: | 457 |
| ZipCRC: | 0x332b8ba7 |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCompression: | Deflated |
| ZipBitFlag: | 0x0006 |
| ZipRequiredVersion: | 20 |
Total processes
37
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3732 | C:\Windows\SysWow64\rundll32.exe ..\erum.ocx,D"&"l"&"lR"&"egister"&"Serve"&"r | C:\Windows\SysWow64\rundll32.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3980 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 587
Read events
1 523
Write events
53
Delete events
11
Modification events
| (PID) Process: | (3980) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | :29 |
Value: 3A3239008C0F0000010000000000000000000000 | |||
| (PID) Process: | (3980) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3980) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3980) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3980) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3980) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3980) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3980) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3980) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3980) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3980 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRE69A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3980 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\suspendedpage[1].htm | html | |
MD5:— | SHA256:— | |||
| 3980 | EXCEL.EXE | C:\Users\admin\erum.ocx | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3980 | EXCEL.EXE | GET | 200 | 149.255.62.24:80 | http://rjmtel.com/cgi-sys/suspendedpage.cgi | GB | html | 7.47 Kb | suspicious |
3980 | EXCEL.EXE | GET | 302 | 149.255.62.24:80 | http://rjmtel.com/wp-content/bYAiTvGo635qKITG6/ | GB | html | 227 b | suspicious |
3980 | EXCEL.EXE | GET | 500 | 69.50.142.179:80 | http://www.crownpacificpartners.com/guglio/Rt4el/ | US | html | 7.14 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3980 | EXCEL.EXE | 69.50.142.179:80 | www.crownpacificpartners.com | NationalNet, Inc. | US | suspicious |
3980 | EXCEL.EXE | 157.7.44.226:80 | nbp-c.com | GMO Internet,Inc | JP | malicious |
3980 | EXCEL.EXE | 149.255.62.24:80 | rjmtel.com | Awareness Software Limited | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.crownpacificpartners.com |
| suspicious |
nbp-c.com |
| malicious |
rjmtel.com |
| suspicious |
dns.msftncsi.com |
| shared |