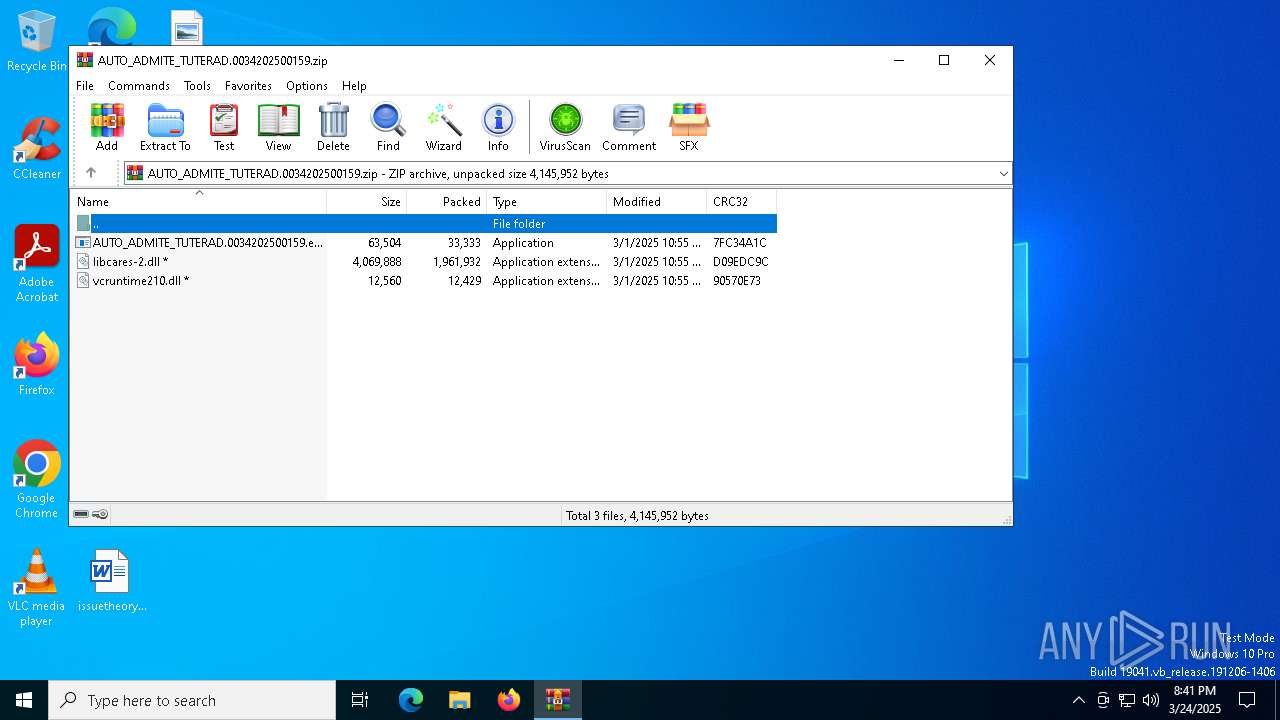
| File name: | AUTO_ADMITE_TUTERAD.0034202500159.zip |
| Full analysis: | https://app.any.run/tasks/70c1a14b-3de2-4f46-99fb-53b140deddb4 |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2025, 20:41:50 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 6127CC3F7F10EEBC7C1C7BAA28AB8123 |
| SHA1: | BC00D0437A00E340659FA82BAA75B3D198F85374 |
| SHA256: | E85D6FA126668CE8C6137CDB47699354C6E6B4F1EBE6E9C6C9AFCAFFAE7FB680 |
| SSDEEP: | 98304:DN5aaRdpsGMh0giYZCmn2Vt73d2ryMfIPfwhwo1vaYxlQtYcjmdWYEjKzRhYzA3l:s3 |
MALICIOUS
GENERIC has been found (auto)
- WinRAR.exe (PID: 2152)
- AUTO_ADMITE_TUTERAD.0034202500159.exe (PID: 2852)
Changes the autorun value in the registry
- AUTO_ADMITE_TUTERAD.0034202500159.exe (PID: 2852)
SUSPICIOUS
Executable content was dropped or overwritten
- AUTO_ADMITE_TUTERAD.0034202500159.exe (PID: 2852)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2152)
Connects to unusual port
- AddInProcess32.exe (PID: 1184)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2152)
Reads the computer name
- AUTO_ADMITE_TUTERAD.0034202500159.exe (PID: 2852)
- AddInProcess32.exe (PID: 1184)
Checks supported languages
- AddInProcess32.exe (PID: 1184)
Reads the machine GUID from the registry
- AddInProcess32.exe (PID: 1184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:03:01 05:55:24 |
| ZipCRC: | 0x7fc34a1c |
| ZipCompressedSize: | 33333 |
| ZipUncompressedSize: | 63504 |
| ZipFileName: | AUTO_ADMITE_TUTERAD.0034202500159.exe |
Total processes
139
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1184 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe | AUTO_ADMITE_TUTERAD.0034202500159.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: AddInProcess.exe Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1348 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1812 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | AUTO_ADMITE_TUTERAD.0034202500159.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
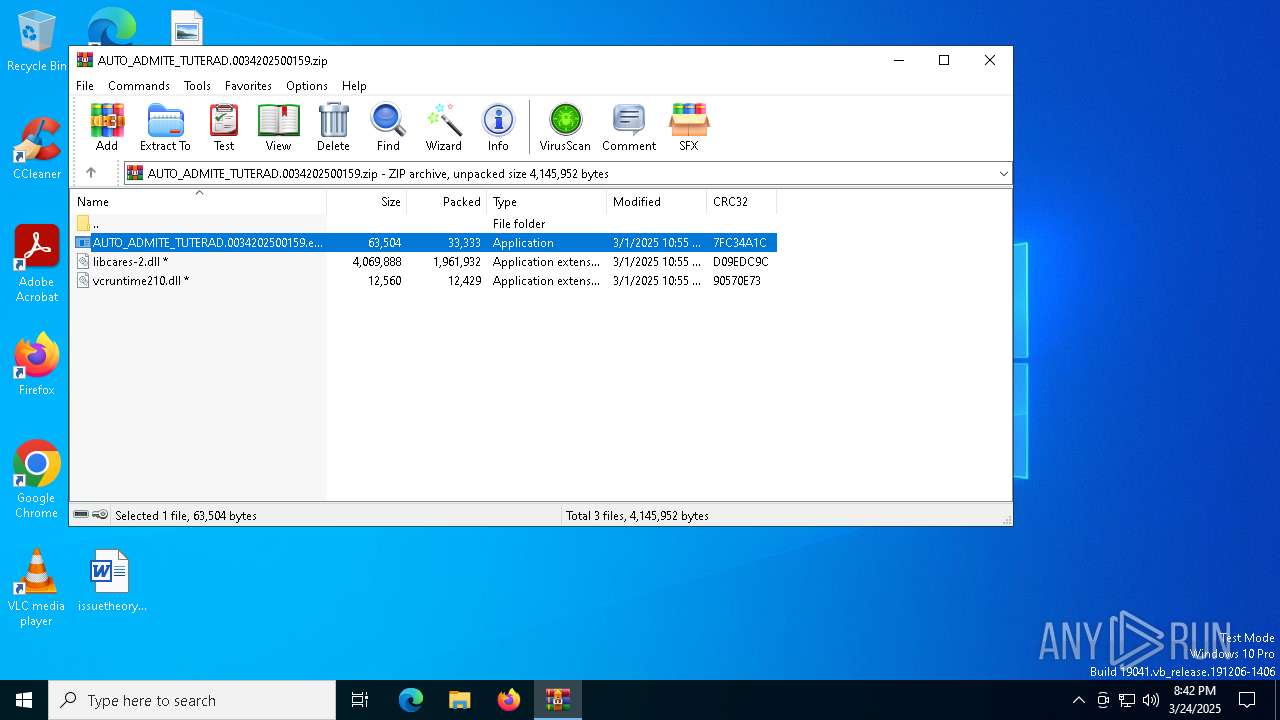
| 2152 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\AUTO_ADMITE_TUTERAD.0034202500159.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 2852 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb2152.23021\AUTO_ADMITE_TUTERAD.0034202500159.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb2152.23021\AUTO_ADMITE_TUTERAD.0034202500159.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
| |||||||||||||||
| 5256 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 383
Read events
2 372
Write events
11
Delete events
0
Modification events
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\AUTO_ADMITE_TUTERAD.0034202500159.zip | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
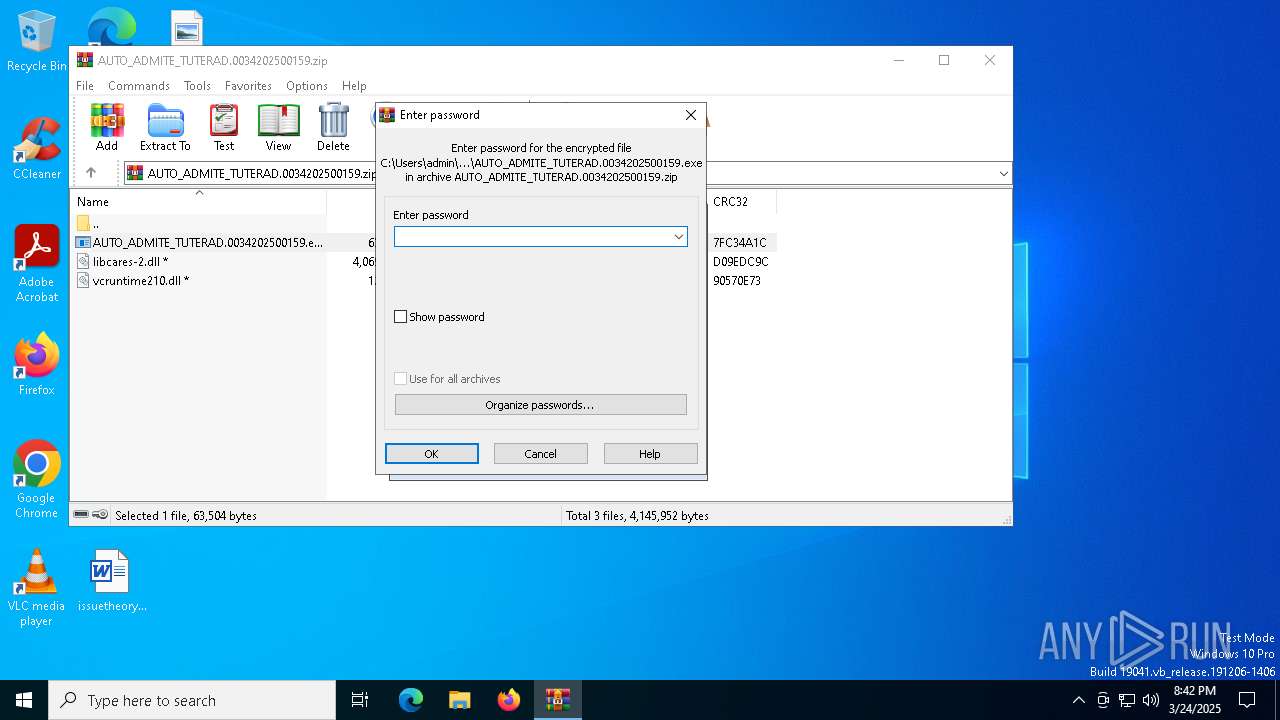
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2852) AUTO_ADMITE_TUTERAD.0034202500159.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | AUTO_ADMITE_TUTERAD.0034202500159 |
Value: cmd.exe /C "start "" /D "C:\Users\admin\SystemRootDoc" "C:\Users\admin\SystemRootDoc\AUTO_ADMITE_TUTERAD.0034202500159.exe"" | |||
Executable files
4
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2152 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2152.23021\vcruntime210.dll | binary | |
MD5:A64A3E2413DF50A77217410F6DAD32F8 | SHA256:9D19B043B0A14FFA675ECDC5EF378BA7154F43A41686ACD6C7F9C7FB085EC5AF | |||
| 2852 | AUTO_ADMITE_TUTERAD.0034202500159.exe | C:\Users\admin\SystemRootDoc\vcruntime210.dll | binary | |
MD5:A64A3E2413DF50A77217410F6DAD32F8 | SHA256:9D19B043B0A14FFA675ECDC5EF378BA7154F43A41686ACD6C7F9C7FB085EC5AF | |||
| 2152 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2152.23021\libcares-2.dll | executable | |
MD5:685341E5347952DCC91726EF16D52FE8 | SHA256:C66EFD7693F67389D4FE5761657265214F1ECA398FA85742250EE7FA775D28C7 | |||
| 2852 | AUTO_ADMITE_TUTERAD.0034202500159.exe | C:\Users\admin\SystemRootDoc\libcares-2.dll | executable | |
MD5:685341E5347952DCC91726EF16D52FE8 | SHA256:C66EFD7693F67389D4FE5761657265214F1ECA398FA85742250EE7FA775D28C7 | |||
| 2152 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2152.23021\AUTO_ADMITE_TUTERAD.0034202500159.exe | executable | |
MD5:FD3C8166E7FBBB64D12C1170B8F4BACF | SHA256:A52E245DD7937094711B10C479274A2CCCEA2DFB89F7D4C9F22879214718F92B | |||
| 2852 | AUTO_ADMITE_TUTERAD.0034202500159.exe | C:\Users\admin\SystemRootDoc\AUTO_ADMITE_TUTERAD.0034202500159.exe | executable | |
MD5:FD3C8166E7FBBB64D12C1170B8F4BACF | SHA256:A52E245DD7937094711B10C479274A2CCCEA2DFB89F7D4C9F22879214718F92B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
48
DNS requests
13
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3884 | backgroundTaskHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5260 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5260 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.139:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 40.126.32.74:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3884 | backgroundTaskHost.exe | 20.223.35.26:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3884 | backgroundTaskHost.exe | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1184 | AddInProcess32.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 13 |